-
 E-Coin-Based Priced Oblivious Transfer with a Fast Item Retrieval
E-Coin-Based Priced Oblivious Transfer with a Fast Item Retrieval -
 NLU-V: A Family of Instruction Set Extensions for Efficient Symmetric Cryptography on RISC-V
NLU-V: A Family of Instruction Set Extensions for Efficient Symmetric Cryptography on RISC-V -
 Analysis of Biometric-Based Cryptographic Key Exchange Protocols—BAKE and BRAKE
Analysis of Biometric-Based Cryptographic Key Exchange Protocols—BAKE and BRAKE -
 Detour-RS: Reroute Attack Vulnerability Assessment with Awareness of the Layout and Resource
Detour-RS: Reroute Attack Vulnerability Assessment with Awareness of the Layout and Resource
Journal Description
Cryptography
Cryptography
is an international, scientific, peer-reviewed, open access journal on cryptography published quarterly online by MDPI.
- Open Access— free for readers, with article processing charges (APC) paid by authors or their institutions.
- High Visibility: indexed within Scopus, ESCI (Web of Science), dblp, and other databases.
- Journal Rank: CiteScore - Q2 (Applied Mathematics)
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 22 days after submission; acceptance to publication is undertaken in 2.9 days (median values for papers published in this journal in the second half of 2023).
- Recognition of Reviewers: reviewers who provide timely, thorough peer-review reports receive vouchers entitling them to a discount on the APC of their next publication in any MDPI journal, in appreciation of the work done.
Impact Factor:
1.6 (2022);
5-Year Impact Factor:
2.4 (2022)
Latest Articles
Constrained Device Performance Benchmarking with the Implementation of Post-Quantum Cryptography
Cryptography 2024, 8(2), 21; https://doi.org/10.3390/cryptography8020021 - 23 May 2024
Abstract
►
Show Figures
Advances in quantum computers may pose a significant threat to existing public-key encryption methods, which are crucial to the current infrastructure of cyber security. Both RSA and ECDSA, the two most widely used security algorithms today, may be (in principle) solved by the
[...] Read more.
Advances in quantum computers may pose a significant threat to existing public-key encryption methods, which are crucial to the current infrastructure of cyber security. Both RSA and ECDSA, the two most widely used security algorithms today, may be (in principle) solved by the Shor algorithm in polynomial time due to its ability to efficiently solve the discrete logarithm problem, potentially making present infrastructures insecure against a quantum attack. The National Institute of Standards and Technology (NIST) reacted with the post-quantum cryptography (PQC) standardization process to develop and optimize a series of post-quantum algorithms (PQAs) based on difficult mathematical problems that are not susceptible to being solved by Shor’s algorithm. Whilst high-powered computers can run these PQAs efficiently, further work is needed to investigate and benchmark the performance of these algorithms on lower-powered (constrained) devices and the ease with which they may be integrated into existing protocols such as TLS. This paper provides quantitative benchmark and handshake performance data for the most recently selected PQAs from NIST, tested on a Raspberry Pi 4 device to simulate today’s IoT (Internet of Things) devices, and provides quantitative comparisons with previous benchmarking data on a range of constrained systems. CRYSTALS-Kyber and CRYSTALS-Dilithium are shown to be the most efficient PQAs in the key encapsulation and signature algorithms, respectively, with Falcon providing the optimal TLS handshake size.
Full article
Open AccessArticle
A Provably Secure Anonymous Authentication Protocol for Consumer and Service Provider Information Transmissions in Smart Grids
by
Zahraa Abdullah Ali, Zaid Ameen Abduljabbar, Hamid Ali Abed AL-Asadi, Vincent Omollo Nyangaresi, Iman Qays Abduljaleel and Abdulla J. Y. Aldarwish
Cryptography 2024, 8(2), 20; https://doi.org/10.3390/cryptography8020020 - 9 May 2024
Abstract
►▼
Show Figures
Smart grids integrate information technology, decision support systems, communication networks, and sensing technologies. All these components cooperate to facilitate dynamic power adjustments based on received client consumption reports. Although this brings forth energy efficiency, the transmission of sensitive data over the public internet
[...] Read more.
Smart grids integrate information technology, decision support systems, communication networks, and sensing technologies. All these components cooperate to facilitate dynamic power adjustments based on received client consumption reports. Although this brings forth energy efficiency, the transmission of sensitive data over the public internet exposes these networks to numerous attacks. To this end, numerous security solutions have been presented recently. Most of these techniques deploy conventional cryptographic systems such as public key infrastructure, blockchains, and physically unclonable functions that have either performance or security issues. In this paper, a fairly efficient authentication scheme is developed and analyzed. Its formal security analysis is carried out using the Burrows–Abadi–Needham (BAN) logic, which shows that the session key negotiated is provably secure. We also execute a semantic security analysis of this protocol to demonstrate that it can resist typical smart grid attacks such as privileged insider, guessing, eavesdropping, and ephemeral secret leakages. Moreover, it has the lowest amount of computation costs and relatively lower communication overheads as well as storage costs.
Full article

Figure 1
Open AccessArticle
Auditable Anonymous Electronic Examination
by
Ádám Vécsi and Attila Pethő
Cryptography 2024, 8(2), 19; https://doi.org/10.3390/cryptography8020019 - 1 May 2024
Abstract
Ensuring security in electronic examination systems represents a significant challenge, particularly when practical considerations dictate that most involved parties cannot be fully trusted due to self-interest. To enhance the security, we introduce auditability to e-exam systems, enabling an auditing authority to verify the
[...] Read more.
Ensuring security in electronic examination systems represents a significant challenge, particularly when practical considerations dictate that most involved parties cannot be fully trusted due to self-interest. To enhance the security, we introduce auditability to e-exam systems, enabling an auditing authority to verify the system integrity. This auditability not only ensures system robustness but also creates an opportunity to grant communication between candidates and examiners, allowing for clarification on unclear questions during exams. Additionally, the implementation of attribute-based certifications ensures anonymity for both candidates and examiners throughout all stages of the exam, with the option for revocation in case of audit-detected fraud.
Full article
(This article belongs to the Special Issue Privacy-Enhancing Technologies for the Digital Age)
►▼
Show Figures

Figure 1
Open AccessArticle
An Efficient Homomorphic Argmax Approximation for Privacy-Preserving Neural Networks
by
Peng Zhang, Ao Duan and Hengrui Lu
Cryptography 2024, 8(2), 18; https://doi.org/10.3390/cryptography8020018 - 1 May 2024
Abstract
►▼
Show Figures
Privacy-preserving neural networks offer a promising solution to train and predict without user privacy leakage, and fully homomorphic encryption (FHE) stands out as one of the key technologies, as it enables homomorphic operations over encrypted data. However, only addition and multiplication homomorphisms are
[...] Read more.
Privacy-preserving neural networks offer a promising solution to train and predict without user privacy leakage, and fully homomorphic encryption (FHE) stands out as one of the key technologies, as it enables homomorphic operations over encrypted data. However, only addition and multiplication homomorphisms are supported by FHE, and thus, it faces huge challenges when implementing non-linear functions with ciphertext inputs. Among the non-linear functions in neural networks, one may refer to the activation function, the argmax function, and maximum pooling. Inspired by using a composition of low-degree minimax polynomials to approximate sign and argmax functions, this study focused on optimizing the homomorphic argmax approximation, where argmax is a mathematical operation that identifies the index of the maximum value within a given set of values. For the method that uses compositions of low-degree minimax polynomials to approximate argmax, in order to further reduce approximation errors and improve computational efficiency, we propose an improved homomorphic argmax approximation algorithm that includes rotation accumulation, tree-structured comparison, normalization, and finalization phases. And then, the proposed homomorphic argmax algorithm was integrated into a neural network structure. Comparative experiments indicate that the network with our proposed argmax algorithm achieved a slight increase in accuracy while significantly reducing the inference latency by
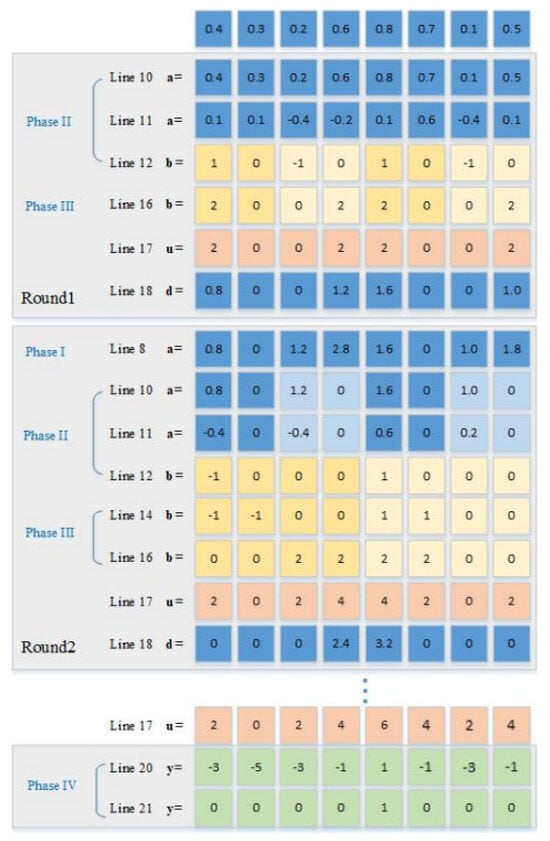
Figure 1
Open AccessArticle
Enhancing Smart Communication Security: A Novel Cost Function for Efficient S-Box Generation in Symmetric Key Cryptography
by
Oleksandr Kuznetsov, Nikolay Poluyanenko, Emanuele Frontoni and Sergey Kandiy
Cryptography 2024, 8(2), 17; https://doi.org/10.3390/cryptography8020017 - 25 Apr 2024
Abstract
In the realm of smart communication systems, where the ubiquity of 5G/6G networks and IoT applications demands robust data confidentiality, the cryptographic integrity of block and stream cipher mechanisms plays a pivotal role. This paper focuses on the enhancement of cryptographic strength in
[...] Read more.
In the realm of smart communication systems, where the ubiquity of 5G/6G networks and IoT applications demands robust data confidentiality, the cryptographic integrity of block and stream cipher mechanisms plays a pivotal role. This paper focuses on the enhancement of cryptographic strength in these systems through an innovative approach to generating substitution boxes (S-boxes), which are integral in achieving confusion and diffusion properties in substitution–permutation networks. These properties are critical in thwarting statistical, differential, linear, and other forms of cryptanalysis, and are equally vital in pseudorandom number generation and cryptographic hashing algorithms. The paper addresses the challenge of rapidly producing random S-boxes with desired cryptographic attributes, a task notably arduous given the complexity of existing generation algorithms. We delve into the hill climbing algorithm, exploring various cost functions and their impact on computational complexity for generating S-boxes with a target nonlinearity of 104. Our contribution lies in proposing a new cost function that markedly reduces the generation complexity, bringing down the iteration count to under 50,000 for achieving the desired S-box. This advancement is particularly significant in the context of smart communication environments, where the balance between security and performance is paramount.
Full article
(This article belongs to the Special Issue Advances in Authentication, Authorization and Privacy for Securing Smart Communications)
►▼
Show Figures
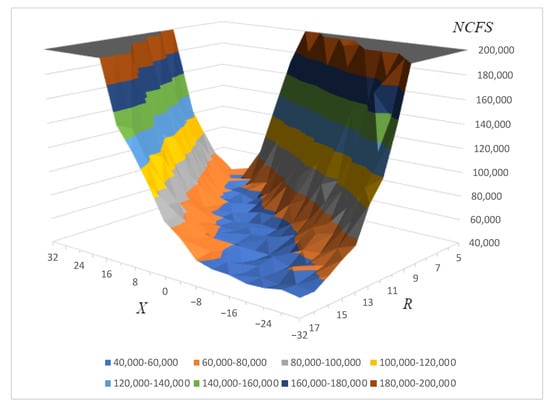
Figure 1
Open AccessArticle
An Engineered Minimal-Set Stimulus for Periodic Information Leakage Fault Detection on a RISC-V Microprocessor
by
Idris O. Somoye, Jim Plusquellic, Tom J. Mannos and Brian Dziki
Cryptography 2024, 8(2), 16; https://doi.org/10.3390/cryptography8020016 - 22 Apr 2024
Abstract
Recent evaluations of counter-based periodic testing strategies for fault detection in Microprocessor (μP) have shown that only a small set of counters is needed to provide complete coverage of severe faults. Severe faults are defined as faults that leak sensitive information,
[...] Read more.
Recent evaluations of counter-based periodic testing strategies for fault detection in Microprocessor (μP) have shown that only a small set of counters is needed to provide complete coverage of severe faults. Severe faults are defined as faults that leak sensitive information, e.g., an encryption key on the output of a serial port. Alternatively, fault detection can be accomplished by executing instructions that periodically test the control and functional units of the μP. In this paper, we propose a fault detection method that utilizes an ’engineered’ executable program combined with a small set of strategically placed counters in pursuit of a hardware Periodic Built-In-Self-Test (PBIST). We analyze two distinct methods for generating such a binary; the first uses an Automatic Test Generation Pattern (ATPG)-based methodology, and the second uses a process whereby existing counter-based node-monitoring infrastructure is utilized. We show that complete fault coverage of all leakage faults is possible using relatively small binaries with low latency to fault detection and by utilizing only a few strategically placed counters in the μP.
Full article
(This article belongs to the Special Issue Feature Papers in Hardware Security II)
►▼
Show Figures
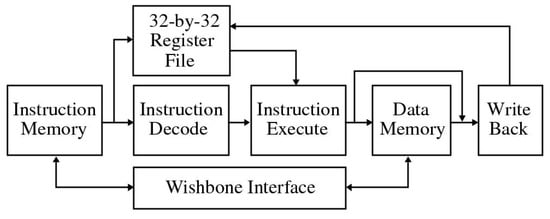
Figure 1
Open AccessArticle
Investigating CRYSTALS-Kyber Vulnerabilities: Attack Analysis and Mitigation
by
Maksim Iavich and Tamari Kuchukhidze
Cryptography 2024, 8(2), 15; https://doi.org/10.3390/cryptography8020015 - 19 Apr 2024
Abstract
►▼
Show Figures
Significant advancements have been achieved in the field of quantum computing in recent years. If somebody ever creates a sufficiently strong quantum computer, many of the public-key cryptosystems in use today might be compromised. Kyber is a post-quantum encryption technique that depends on
[...] Read more.
Significant advancements have been achieved in the field of quantum computing in recent years. If somebody ever creates a sufficiently strong quantum computer, many of the public-key cryptosystems in use today might be compromised. Kyber is a post-quantum encryption technique that depends on lattice problem hardness, and it was recently standardized. Despite extensive testing by the National Institute of Standards and Technology (NIST), new investigations have demonstrated the effectiveness of CRYSTALS-Kyber attacks and their applicability in non-controlled environments. We investigated CRYSTALS-Kyber’s susceptibility to side-channel attacks. In the reference implementation of Kyber512, additional functions can be compromised by employing the selected ciphertext. The implementation of the selected ciphertext allows the attacks to succeed. Real-time recovery of the entire secret key is possible for all assaults.
Full article
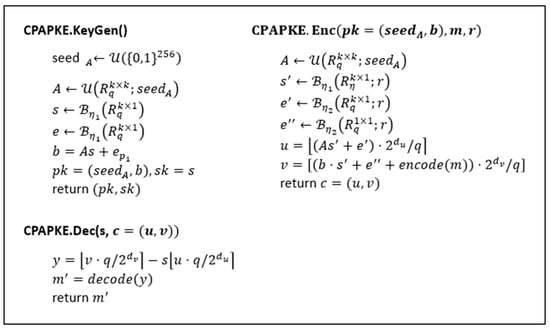
Figure 1
Open AccessArticle
Analysis of Biometric-Based Cryptographic Key Exchange Protocols—BAKE and BRAKE
by
Maksymilian Gorski and Wojciech Wodo
Cryptography 2024, 8(2), 14; https://doi.org/10.3390/cryptography8020014 - 6 Apr 2024
Abstract
Biometric authentication methods offer high-quality mechanisms to confirm the identity of individuals in security systems commonly used in the modern world, such as physical access control, online banking, or mobile device unlocking. They also find their application in cryptographic solutions, which allow the
[...] Read more.
Biometric authentication methods offer high-quality mechanisms to confirm the identity of individuals in security systems commonly used in the modern world, such as physical access control, online banking, or mobile device unlocking. They also find their application in cryptographic solutions, which allow the biometrically authenticated exchange of cryptographic keys between users and services on the internet, despite the fuzziness of biometric data. Such solutions are BAKE (biometrics-authenticated key exchange) and BRAKE (biometric-resilient authenticated key exchange) protocols, upon which our work is based. However, the direct application of fuzzy biometrics in cryptography, which relies heavily on the accuracy of single-bit secret values, is not trivial. Therefore, this paper is devoted to analyzing the security of this idea and the feasibility of implementing biometric AKE (authenticated key exchange) protocols, with an emphasis on the BRAKE protocol. As the results of our analysis, we discuss BRAKE’s limitations and vulnerabilities, which need to be appropriately addressed to implement the protocol in modern systems.
Full article
(This article belongs to the Topic Trends and Prospects in Security, Encryption and Encoding)
►▼
Show Figures
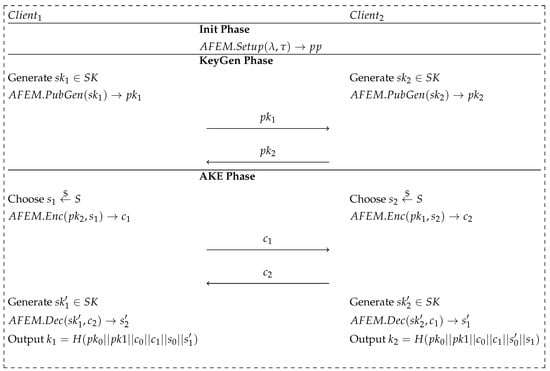
Figure 1
Open AccessArticle
Detour-RS: Reroute Attack Vulnerability Assessment with Awareness of the Layout and Resource
by
Minyan Gao, Liton Kumar Biswas, Navid Asadi and Domenic Forte
Cryptography 2024, 8(2), 13; https://doi.org/10.3390/cryptography8020013 - 6 Apr 2024
Abstract
Recent decades have witnessed a remarkable pace of innovation and performance improvements in integrated circuits (ICs), which have become indispensable in an array of critical applications ranging from military infrastructure to personal healthcare. Meanwhile, recent developments have brought physical security to the forefront
[...] Read more.
Recent decades have witnessed a remarkable pace of innovation and performance improvements in integrated circuits (ICs), which have become indispensable in an array of critical applications ranging from military infrastructure to personal healthcare. Meanwhile, recent developments have brought physical security to the forefront of concern, particularly considering the valuable assets handled and stored within ICs. Among the various invasive attack vectors, micro-probing attacks have risen as a particularly menacing threat. These attacks leverage advanced focused ion beam (FIB) systems to enable post-silicon secret eavesdropping and circuit modifications with minimal traceability. As an evolved variant of micro-probing attacks, reroute attacks possess the ability to actively disable built-in shielding measures, granting access to the security-sensitive signals concealed beneath. To address and counter these emerging challenges, we introduce a layout-level framework known as Detour-RS. This framework is designed to automatically assess potential vulnerabilities, offering a systematic approach to identifying and mitigating exploitable weaknesses. Specifically, we employed a combination of linear and nonlinear programming-based approaches to identify the layout-aware attack costs in reroute attempts given specific target assets. The experimental results indicate that shielded designs outperform non-shielded structures against reroute attacks. Furthermore, among the two-layer shield configurations, the orthogonal layout exhibits better performance compared to the parallel arrangement. Furthermore, we explore both independent and dependent scenarios, where the latter accounts for potential interference among circuit edit locations. Notably, our results demonstrate a substantial near 50% increase in attack cost when employing the more realistic dependent estimation approach. In addition, we also propose time and gas consumption metrics to evaluate the resource consumption of the attackers, which provides a perspective for evaluating reroute attack efforts. We have collected the results for different categories of target assets and also the average resource consumption for each via, required during FIB reroute attack.
Full article
(This article belongs to the Special Issue Feature Papers in Hardware Security II)
►▼
Show Figures
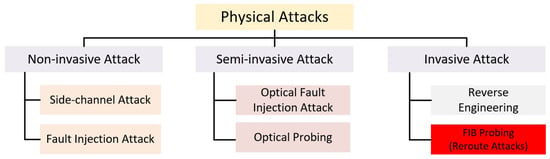
Figure 1
Open AccessArticle
A Survey of Consortium Blockchain and Its Applications
by
Xiaotong Chen, Songlin He, Linfu Sun, Yangxin Zheng and Chase Q. Wu
Cryptography 2024, 8(2), 12; https://doi.org/10.3390/cryptography8020012 - 22 Mar 2024
Abstract
Blockchain is a revolutionary technology that has reshaped the trust model among mutually distrustful peers in a distributed network. While blockchain is well-known for its initial usage in a public manner, such as the cryptocurrency of Bitcoin, consortium blockchain, which requires authentication of
[...] Read more.
Blockchain is a revolutionary technology that has reshaped the trust model among mutually distrustful peers in a distributed network. While blockchain is well-known for its initial usage in a public manner, such as the cryptocurrency of Bitcoin, consortium blockchain, which requires authentication of all involved participants, has also been widely adopted in various domains. Nevertheless, there is a lack of comprehensive study of consortium blockchain in terms of its architecture design, consensus mechanisms, comparative performance, etc. In this study, we aim to fill this gap by surveying the most popular consortium blockchain platforms and assessing their core designs in a layered fashion. Particularly, Byzantine fault tolerant (BFT) state machine replication (SMR) is introduced to act as a basic computational model of consortium blockchain. Then the consortium blockchain is split into the hardware layer, layer-0 (network layer), layer-I (data layer, consensus layer and contract layer), layer-II protocols, and application layer. Each layer is presented with closely related discussion and analysis. Furthermore, with the extraction of the core functionalities, i.e., robust storage and guaranteed execution, that a consortium blockchain can provide, several typical consortium blockchain-empowered decentralized application scenarios are introduced. With these thorough studies and analyses, this work aims to systematize the knowledge dispersed in the consortium blockchain, highlight the unsolved challenges, and also indicate the propitious avenues of future work.
Full article
(This article belongs to the Section Blockchain Security)
►▼
Show Figures
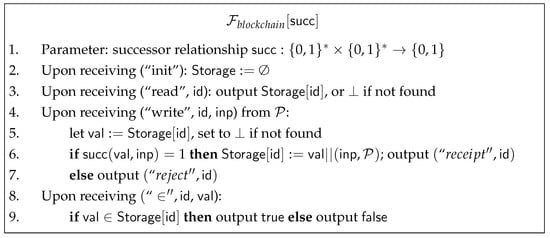
Figure 1
Open AccessArticle
Lookup Table-Based Design of Scalar Multiplication for Elliptic Curve Cryptography
by
Yan-Duan Ning, Yan-Haw Chen, Cheng-Sin Shih and Shao-I Chu
Cryptography 2024, 8(1), 11; https://doi.org/10.3390/cryptography8010011 - 18 Mar 2024
Abstract
►▼
Show Figures
This paper is aimed at using a lookup table method to improve the scalar multiplication performance of elliptic curve cryptography. The lookup table must be divided into two polynomials and requires two iterations of point doubling operation, for which negation operations are needed.
[...] Read more.
This paper is aimed at using a lookup table method to improve the scalar multiplication performance of elliptic curve cryptography. The lookup table must be divided into two polynomials and requires two iterations of point doubling operation, for which negation operations are needed. It is well known that an inversion operation requires a lot of multiplication time. The advantage of this paper is that we are able to reduce one inverse element calculation for this problem and also improve the basic operations of finite fields through segmentation methods. If the normal basis method is used in the design of the inverse element operation, it must be converted to the normal basis through the standard basis. However, the conversion process requires a lot of matrix operations. Though the anti-element operation has good speed performance, it also increases the computational complexity. Using number theory and grouping methods will greatly improve the performance of inverse element operations. With application of the two-time point doubling operation in the hardware implementation, the developed approach reduces the computing time by 48% as compared with the conventional approach. The computational time of the scalar multiplication using the presented method is further improved by 67% over the traditional algorithm with only an area increase of 12%. Finally, the proposed lookup table-based technique can be utilized for software and hardware implementation, as the developed arithmetic operations are simple and are consistent in their execution.
Full article
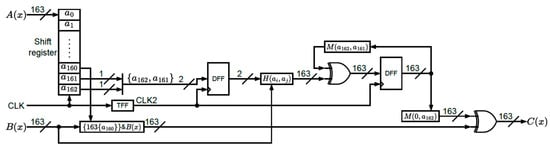
Figure 1
Open AccessArticle
E-Coin-Based Priced Oblivious Transfer with a Fast Item Retrieval
by
Francesc Sebé and Sergi Simón
Cryptography 2024, 8(1), 10; https://doi.org/10.3390/cryptography8010010 - 13 Mar 2024
Abstract
►▼
Show Figures
Priced oblivious transfer (POT) is a cryptographic protocol designed for privacy-preserving e-commerce of digital content. It involves two parties: the merchant, who provides a set of priced items as input, and a customer, who acquires one of them. After the protocol has run,
[...] Read more.
Priced oblivious transfer (POT) is a cryptographic protocol designed for privacy-preserving e-commerce of digital content. It involves two parties: the merchant, who provides a set of priced items as input, and a customer, who acquires one of them. After the protocol has run, the customer obtains the item they chose, while the merchant cannot determine which one. Moreover, the protocol guarantees that the customer gets the content only if they have paid the price established by the merchant. In a recent paper, the authors proposed a POT system where the payments employed e-coin transactions. The strong point of the proposal was the absence of zero-knowledge proofs required in preceding systems to guarantee the correctness of payments. In this paper, we propose a novel e-coin-based POT system with a fast item retrieval procedure whose running time does not depend on the number of items for sale. This is an improvement over the aforementioned existing proposal whose execution time becomes prohibitively long when the catalog is extensive. The use of zero-knowledge proofs is neither required.
Full article
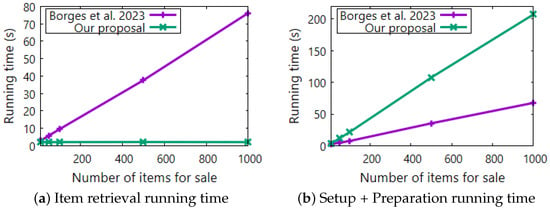
Figure 1
Open AccessArticle
NLU-V: A Family of Instruction Set Extensions for Efficient Symmetric Cryptography on RISC-V
by
Hakan Uzuner and Elif Bilge Kavun
Cryptography 2024, 8(1), 9; https://doi.org/10.3390/cryptography8010009 - 29 Feb 2024
Abstract
Cryptographic primitives nowadays are not only implemented in high-performance systems but also in small-scale systems, which are increasingly powered by open-source processors, such as RISC-V. In this work, we leverage RISC-V’s modular base instruction set and architecture to propose a generic instruction set
[...] Read more.
Cryptographic primitives nowadays are not only implemented in high-performance systems but also in small-scale systems, which are increasingly powered by open-source processors, such as RISC-V. In this work, we leverage RISC-V’s modular base instruction set and architecture to propose a generic instruction set extension (ISE) for symmetric cryptography. We adapt the work from Engels et al. in ARITH’13, the non-linear/linear instruction set extension (NLU), which presents a generic hardware/software co-design solution for efficient symmetric crypto implementations through a hardware unit extending the 8-bit AVR instruction set. These new instructions realize non-linear and linear layers, which are widely used to implement the block ciphers in symmetric cryptography. Our proposal modifies and extends the NLU instructions to a 32-bit RISC-V architecture; hence, we call the proposed ISE ‘NLU-V’. The proposed architecture is integrated into the open-source RISC-V implementation ‘Icicle’ and synthesized on a Xilinx Kintex-7 XC7K160T FPGA. The area overhead for the proposed NLU-V ISE is 1088 slice registers and 4520 LUTs. As case studies, the PRESENT and AES block ciphers are implemented using the new ISE on RISC-V in assembly. Our evaluation metric to showcase the performance gain, Z ‘time-area-product (TAP)’ (the execution time in clock cycles times code memory consumption), reflects the impact of the proposed family of instructions on the performance of the cipher implementations. The simulations show that the NLU-V achieves 89% gain for PRESENT and 68% gain for AES. Further, the NLU-V requires 44% less lines of code for the PRESENT and 23% less for the AES implementation.
Full article
(This article belongs to the Special Issue Feature Papers in Hardware Security II)
►▼
Show Figures
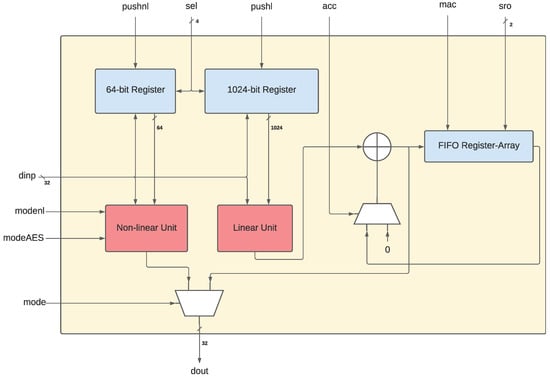
Figure 1
Open AccessArticle
FPGA-Based Acceleration of K-Nearest Neighbor Algorithm on Fully Homomorphic Encrypted Data
by
Sagarika Behera and Jhansi Rani Prathuri
Cryptography 2024, 8(1), 8; https://doi.org/10.3390/cryptography8010008 - 27 Feb 2024
Abstract
The suggested solution in this work makes use of the parallel processing capability of FPGA to enhance the efficiency of the K-Nearest Neighbor (KNN) algorithm on encrypted data. The suggested technique was assessed utilizing the breast cancer datasets and the findings indicate that
[...] Read more.
The suggested solution in this work makes use of the parallel processing capability of FPGA to enhance the efficiency of the K-Nearest Neighbor (KNN) algorithm on encrypted data. The suggested technique was assessed utilizing the breast cancer datasets and the findings indicate that the FPGA-based acceleration method provides significant performance improvements over software implementation. The Cheon–Kim–Kim–Song (CKKS) homomorphic encryption scheme is used for the computation of ciphertext. After extensive simulation in Python and implementation in FPGA, it was found that the proposed architecture brings down the computational time of KNN on ciphertext to a realistic value in the order of the KNN classification algorithm over plaintext. For the FPGA implementation, we used the Intel Agilex7 FPGA (AGFB014R24B2E2V) development board and validated the speed of computation, latency, throughput, and logic utilization. It was observed that the KNN on encrypted data has a computational time of 41.72 ms which is 80 times slower than the KNN on plaintext whose computational time is of 0.518 ms. The main computation time for CKKS FHE schemes is 41.72 ms. With our architecture, we were able to reduce the calculation time of the CKKS-based KNN to 0.85 ms by using 32 parallel encryption hardware and reaching 300 MHz speed.
Full article
(This article belongs to the Special Issue Applied Cryptography and Machine Learning for Security and Privacy Protection of Critical Infrastructures)
►▼
Show Figures
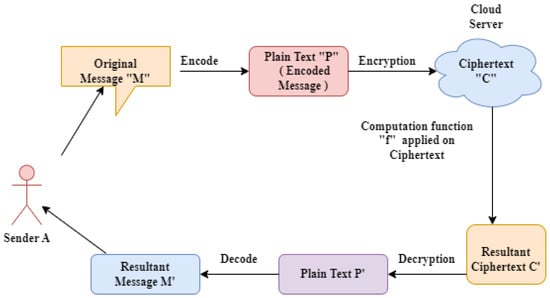
Figure 1
Open AccessArticle
Threats, Attacks, and Cryptography Frameworks of Cybersecurity in Critical Infrastructures
by
Kyriaki Tsantikidou and Nicolas Sklavos
Cryptography 2024, 8(1), 7; https://doi.org/10.3390/cryptography8010007 - 25 Feb 2024
Abstract
►▼
Show Figures
Critical Infrastructures (CIs), such as healthcare facilities, power grids, transportation systems, and financial institutions, are vital components of a functioning society, with the economy and safety being dependent on them. Nevertheless, they have become increasingly vulnerable to cyber threats and attacks in recent
[...] Read more.
Critical Infrastructures (CIs), such as healthcare facilities, power grids, transportation systems, and financial institutions, are vital components of a functioning society, with the economy and safety being dependent on them. Nevertheless, they have become increasingly vulnerable to cyber threats and attacks in recent years. The main reason is their inability to quickly adapt to technological changes, employ updated cryptographic frameworks, and implement a thoroughly secure architecture based on their characteristics. In this study, the unique complexities of these systems are highlighted. Various verified cyberattacks that were executed against CIs in recent years are analyzed. Moreover, the general framework of CIs is demonstrated together with the employed technologies and cryptographic primitives. A thorough architecture of said technologies is developed to better understand the targeted components and easily identify potentially hidden threats. Afterwards, threat, adversary, and attack models that target critical systems and services are designed. The purpose is a better comprehension of the systems’ vulnerabilities, attack structures, motives, and targets for assisting CIs’ designers in creating secure frameworks and mechanisms, with the ability to mitigate such threats. Lastly, security controls and cryptography frameworks are demonstrated together with efficient mitigation architectures and implementations from the research community.
Full article
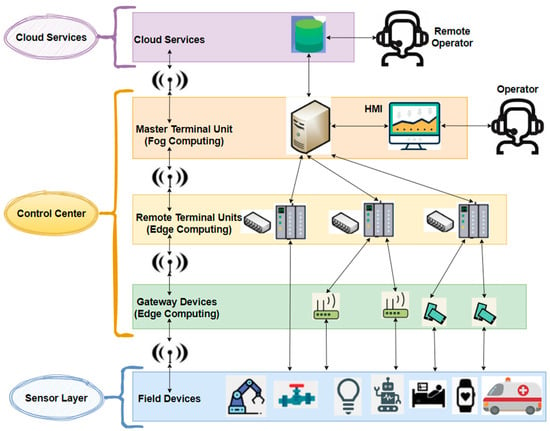
Figure 1
Open AccessArticle
Privacy-Preserving Multi-Party Cross-Chain Transaction Protocols
by
Chang Chen, Guoyu Yang, Zhihao Li, Fuan Xiao, Qi Chen and Jin Li
Cryptography 2024, 8(1), 6; https://doi.org/10.3390/cryptography8010006 - 4 Feb 2024
Abstract
Cross-chain transaction technologies have greatly promoted the scalability of cryptocurrencies, which then facilitates the development of Metaverse applications. However, existing solutions rely heavily on centralized middleware (notary) or smart contracts. These schemes lack privacy considerations, and users’ cross-chain transactions are easy to master
[...] Read more.
Cross-chain transaction technologies have greatly promoted the scalability of cryptocurrencies, which then facilitates the development of Metaverse applications. However, existing solutions rely heavily on centralized middleware (notary) or smart contracts. These schemes lack privacy considerations, and users’ cross-chain transactions are easy to master by other parties. Some signature-based payment schemes have good privacy but do not support multi-party cross-chain protocols or rely heavily on some time assumptions. The uncertainty of user behavior makes it difficult to design a secure multi-party cross-chain protocol. To solve these problems, we investigate how to design a secure multi-party cross-chain transaction protocol with offline tolerance. We propose a new signature algorithm called the pre-adaptor signature scheme, an extension of the adaptor signature scheme. The pre-adaptor signature scheme combines the multi-signature and adaptor signature schemes, which can realize the secret transmission channel between multiple parties. To provide offline tolerance, we encode our protocol into the P2SH script. Our protocol provides better privacy due to no dependence on smart contracts. The performance evaluation was conducted with ten participants. For each participant of our cross-chain protocol, the initialization and execution process can be performed in 3 milliseconds and with 6 k bytes of communication overhead at most. The cost increases linearly with the increase in the number of participants.
Full article
(This article belongs to the Section Blockchain Security)
►▼
Show Figures

Figure 1
Open AccessReview
Pervasive User Data Collection from Cyberspace: Privacy Concerns and Countermeasures
by
Yinhao Jiang, Mir Ali Rezazadeh Baee, Leonie Ruth Simpson, Praveen Gauravaram, Josef Pieprzyk, Tanveer Zia, Zhen Zhao and Zung Le
Cryptography 2024, 8(1), 5; https://doi.org/10.3390/cryptography8010005 - 31 Jan 2024
Abstract
The increasing use of technologies, particularly computing and communication paradigms, has significantly influenced our daily lives. Interconnecting devices and networks provides convenient platforms for information exchange and facilitates pervasive user data collection. This new environment presents serious privacy challenges. User activities can be
[...] Read more.
The increasing use of technologies, particularly computing and communication paradigms, has significantly influenced our daily lives. Interconnecting devices and networks provides convenient platforms for information exchange and facilitates pervasive user data collection. This new environment presents serious privacy challenges. User activities can be continuously monitored in both digital and physical realms. Gathered data can be aggregated and analysed, revealing aspects of user behaviour that may not be apparent from a single data point. The very items that facilitate connectivity simultaneously increase the risk of privacy breaches. The data gathered to provide services can also be used for monitoring and surveillance. This paper discerns three novel categories of privacy concerns relating to pervasive user data collection: privacy and user activity in cyberspace, privacy in personal cyber–physical systems, and privacy in proactive user-driven data collection. We emphasise the primary challenges, ranging from identity tracking in browsing histories to intricate issues in opportunistic networks, situating each within practical, real-world scenarios. Furthermore, we assess the effectiveness of current countermeasures, investigating their strengths and limitations. This paper explores the challenges in preserving privacy in user interactions with dynamic interconnected systems and suggests countermeasures to mitigate identified privacy risks.
Full article
(This article belongs to the Special Issue Recent Advances in Information Security and Privacy)
►▼
Show Figures
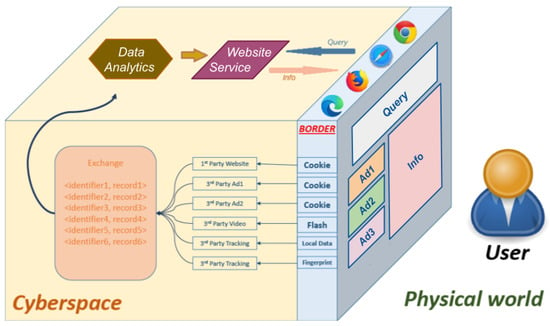
Figure 1
Open AccessArticle
Cryptanalysis of Two Conditional Privacy Preserving Authentication Schemes for Vehicular Ad Hoc Networks
by
Ahmad Mohamad Kabil, Heba Aslan and Marianne Azer
Cryptography 2024, 8(1), 4; https://doi.org/10.3390/cryptography8010004 - 24 Jan 2024
Cited by 1
Abstract
Conditional Privacy Preserving Authentication (CPPA) schemes are an effective way of securing communications in vehicular ad hoc networks (VANETs), as well as ensuring user privacy and accountability. Cryptanalysis plays a crucial role in pointing out the vulnerabilities in existing schemes to enable the
[...] Read more.
Conditional Privacy Preserving Authentication (CPPA) schemes are an effective way of securing communications in vehicular ad hoc networks (VANETs), as well as ensuring user privacy and accountability. Cryptanalysis plays a crucial role in pointing out the vulnerabilities in existing schemes to enable the development of more resilient ones. In 2019, Zhang proposed a CPPA scheme for VANET security (PA-CRT), based on identity batch verification (IBV) and Chinese Remainder Theorem (CRT). In this paper, we cryptanalyze Zhang’s scheme and point out its vulnerability to impersonation and repudiation attacks. In 2023, Zhang’s scheme was cryptanalyzed by Tao; however, we point out flaws in Tao’s cryptanalysis due to invalid assumptions; hence, we propose countermeasures to Tao’s attacks. Furthermore, in 2021, Xiong proposed a Certificateless Aggregate Signature (CLAS) scheme which is also cryptanalyzed in this paper. Finally, we analyze the causes and countermeasures by pointing out the vulnerabilities in each scheme that enabled us to launch successful attacks and proposing changes that would fortify these schemes against similar attacks in the future.
Full article
(This article belongs to the Special Issue Advances in Authentication, Authorization and Privacy for Securing Smart Communications)
►▼
Show Figures

Figure 1
Open AccessArticle
Novel and Efficient Privacy-Preserving Continuous Authentication
by
Ahmed Fraz Baig, Sigurd Eskeland and Bian Yang
Cryptography 2024, 8(1), 3; https://doi.org/10.3390/cryptography8010003 - 24 Jan 2024
Abstract
►▼
Show Figures
Continuous authentication enhances security by re-verifying a user’s validity during the active session. It utilizes data about users’ behavioral actions and contextual information to authenticate them continuously. Such data contain information about user-sensitive attributes such as gender, age, contextual information, and may also
[...] Read more.
Continuous authentication enhances security by re-verifying a user’s validity during the active session. It utilizes data about users’ behavioral actions and contextual information to authenticate them continuously. Such data contain information about user-sensitive attributes such as gender, age, contextual information, and may also provide information about the user’s emotional states. The collection and processing of sensitive data cause privacy concerns. In this paper, we propose two efficient protocols that enable privacy-preserving continuous authentication. The contribution is to prevent the disclosure of user-sensitive attributes using partial homomorphic cryptographic primitives and reveal only the aggregated result without the explicit use of decryption. The protocols complete an authentication decision in a single unidirectional transmission and have very low communication and computation costs with no degradation in biometric performance.
Full article

Figure 1
Open AccessArticle
Locking-Enabled Security Analysis of Cryptographic Circuits
by
Devanshi Upadhyaya, Maël Gay and Ilia Polian
Cryptography 2024, 8(1), 2; https://doi.org/10.3390/cryptography8010002 - 5 Jan 2024
Abstract
Hardware implementations of cryptographic primitives require protection against physical attacks and supply chain threats. This raises the question of secure composability of different attack countermeasures, i.e., whether protecting a circuit against one threat can make it more vulnerable against a different threat. In
[...] Read more.
Hardware implementations of cryptographic primitives require protection against physical attacks and supply chain threats. This raises the question of secure composability of different attack countermeasures, i.e., whether protecting a circuit against one threat can make it more vulnerable against a different threat. In this article, we study the consequences of applying logic locking, a popular design-for-trust solution against intellectual property piracy and overproduction, to cryptographic circuits. We show that the ability to unlock the circuit incorrectly gives the adversary new powerful attack options. We introduce LEDFA (locking-enabled differential fault analysis) and demonstrate for several ciphers and families of locking schemes that fault attacks become possible (or consistently easier) for incorrectly unlocked circuits. In several cases, logic locking has made circuit implementations prone to classical algebraic attacks with no fault injection needed altogether. We refer to this “zero-fault” version of LEDFA by the term LEDA, investigate its success factors in-depth and propose a countermeasure to protect the logic-locked implementations against LEDA. We also perform test vector leakage assessment (TVLA) of incorrectly unlocked AES implementations to show the effects of logic locking regarding side-channel leakage. Our results indicate that logic locking is not safe to use in cryptographic circuits, making them less rather than more secure.
Full article
(This article belongs to the Special Issue Feature Papers in Hardware Security II)
►▼
Show Figures
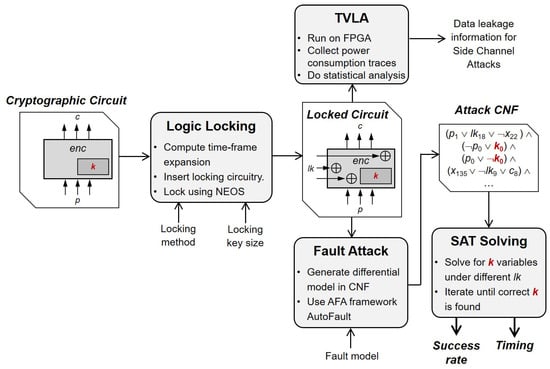
Figure 1
Highly Accessed Articles
Latest Books
E-Mail Alert
News
Topics
Topic in
Applied Sciences, Cryptography, JCP, JSAN, Sci, Symmetry
Trends and Prospects in Security, Encryption and Encoding
Topic Editors: Ki-Hyun Jung, Luis Javier García VillalbaDeadline: 31 December 2024

Conferences
Special Issues
Special Issue in
Cryptography
Hardware Security and Cryptographic Implementations
Guest Editors: Kris Gaj, Xiaofang Wang, Danai ChasakiDeadline: 30 June 2024
Special Issue in
Cryptography
Advances in Authentication, Authorization and Privacy for Securing Smart Communications
Guest Editors: Cheng-Chi Lee, Tuan-Vinh Le, Chun-Ta Li, Dinh-Thuan Do, Agbotiname Lucky ImoizeDeadline: 31 July 2024
Special Issue in
Cryptography
Privacy-Enhancing Technologies for the Digital Age
Guest Editors: Dou An, Hanlin Zhang, Zengpeng LiDeadline: 31 October 2024
Special Issue in
Cryptography
Role of Cryptography in Network Security
Guest Editors: Krzysztof Szczypiorski, Borislav StoyanovDeadline: 30 November 2024






