1. Introduction
Recent technological advances have enabled the inexpensive development of sensor nodes which, despite their relatively small size, have extremely powerful sensing, processing and communication capabilities. The benefits arising from the collaborative use of such sensor nodes which are wirelessly interconnected, find an ever growing number of applications. A group of spatially distributed sensor nodes which are interconnected without the use of any wires constitutes a WSN [
1,
2].
The typical configuration of such a sensor node in a WSN includes single or multiple sensing elements, a data processor, communicating components and a power source of limited energy capacity. The sensing elements of such a sensor node perform measurements related to the conditions existing at its surrounding environment. These measurements are transformed into corresponding electric signals and are processed by the processing unit. A sensor node makes use of its communication components in order to transmit the data, over a wireless channel, to a designated sink point, referred to as a base station. The base station collects all the data transmitted to it in order to act as a supervisory control processor or an access point for a human interface or even as a gateway to other networks.
By using such a configuration as that described above and through the collaborative use of a large number of sensor nodes, a WSN is able to perform concurrent data acquisition of ambient conditions at various spots of interest located over wide areas. Nowadays, WSNs support an ever growing variety of applications including environment and habitat monitoring, surveillance and reconnaissance, home automation, biomedical applications, object tracking, traffic control, fire detection, inventory control, agriculture, machine failure diagnosis and energy management [
1–
7].
Despite however the profound advantages that the utilization of WSNs offers, it is strictly limited due to energy constraints. In fact, the most of energy expenditure of a sensor node takes place during wireless communication and the rest whilst sensing and data processing. Therefore, there is a need for eradication of energy inefficiencies at all layers of the protocol stack of sensor nodes [
1]. More specifically, research on the network layer of the protocol stack focuses on the achievement of energy efficient route setup and consistent data communication from the sensor nodes to the base station in order to extend the network lifetime and thus prolong network connectivity [
5]; this is why routing protocols in WSNs aim mainly at the attainment of power conservation.
However, the routing protocols developed for wired communication networks, which mainly aim at high Quality of Service (QoS), are considered to be inappropriate for WSNs for many reasons. Firstly, IP based schemes cannot `easily’ be applied in WSNs. Secondly, contrary to wired networks, most of the data flow in WSNs is directed from many sources to one single sink. Moreover, given that multiple sensor nodes located within the vicinity of a phenomenon may generate similar data, routing protocols in a WSN need to tackle the redundancy associated with the data traffic generated by similar measurements. Furthermore, sensor nodes are strictly constrained in terms of on board energy, storage and processing capacity.
For these reasons, many new protocols have been proposed for data routing in sensor networks. These protocols can be classified in several categories [
8,
9]. This article deals with ‘Hierarchical Routing’. The main idea in hierarchical schemes is that nodes are grouped into squads and perform data aggregation and multi hop communication. In this way, the number of transmitted messages to the base station is reduced for the benefit of system scalability and energy efficiency. On the other hand, the detrimental effect of all hierarchical routing protocols is the increase of the computational overhead and the corresponding delay.
Moreover, no matter which the routing protocol selected is, the power efficiency of the data routing process is affected by the route selection policy adopted at local level, i.e., the policy used in order to find the most appropriate path to route data from one node to another.
The rest of this work is organized as follows. In Section 2, a discussion on some of the most popular hierarchical routing protocols and route selection policies is offered. In Section 3, the system model adopted in the proposed SHPER protocol is described. In Section 4, the initialization and steady state phases of SHPER protocol are explained. The performance evaluation of SHPER takes place in Section 5 through the description of the simulation scenarios and the corresponding results. Finally, Section 6 concludes the article.
2. WSN Routing Protocols
This article aims at presenting in detail and thoroughly validating the enhanced work performed on the development of a hierarchical routing protocol for WSNs named SHPER (Scaling Hierarchical Power Efficient Routing), which was first introduced by Kandris
et al. [
10]. This section presents the most widely used protocols which have similar features with SHPER, when compared according to specific metrics such as classification, power usage, data aggregation ability, localization and scalability.
2.1. Hierarchical Routing Protocols
The LEACH protocol, which was introduced by Heizelman
et al., is one of the most popular energy efficient hierarchical routing protocols proposed for sensor networks and has been utilized as the basis for many other subsequent protocols of such a kind [
11]. In this protocol neighboring nodes dynamically form clusters in a distributed manner. One node per cluster is randomly chosen to be the cluster head. Each cluster head collects and aggregates all data it receives from its cluster nodes and forwards the aggregated data directly to the base station. The election of cluster heads is rotated among the cluster nodes and it is based on the determined
a priori suggested proportion of cluster heads for the network and the number of times a node has been a cluster head so far. After the end of each round, the new elected cluster head sends to each one of the rest of its cluster nodes a consequent notification.
Given that in LEACH data collection is performed periodically, this protocol is supposed to be more suitable when there is a need for constant proactive monitoring by the WSN. However, in several cases, periodic data transmissions are needless, thus causing ineffectual expenditure of energy. Additionally, LEACH supposes that all nodes contain the same quantity of energy capacity at every election round. Furthermore, it is also presumed that every node has an adequate amount of transmission power in order to directly get in touch with the base station if required. Nevertheless, in most cases these hypotheses are unlikely.
A protocol which is considered to be an enhanced descendant of LEACH is PEGASIS, which was introduced by Lindsey and Raghavendra [
12]. In this protocol the nodes are not grouped into clusters. Instead, chains of nodes are formed in a greedy way so that each node transmits and receives from a neighbor and eventually one node is selected to transmit to the base station. Although, PEGASIS achieves higher energy conservation when compared to LEACH, it suffers however from certain drawbacks. One of them is the excessive delay which is caused by distant nodes on the chain. Another weakness of the protocol has to do with the fact that the single leader can become a bottleneck for the network.
Hierarchical-PEGASIS, introduced by Lindsey
et al, is an extension to PEGASIS [
13]. It achieves a notable decrease of the delay incurred for packets during transmission to the base station by enabling simultaneous transmissions of data. However, both PEGASIS and Hierarchical-PEGASIS, like LEACH, are based on some unrealistic assumptions such as that all nodes have the same level of energy and are able to communicate with the BS directly.
TEEN is another widely referenced and extensively used energy efficient hierarchical routing protocol, proposed by Manjeshwar and Agrawal [
14]. TEEN makes use of a hierarchical scheme along with a data centric mechanism. More precisely, in a way akin to that adopted by LEACH, adjacent nodes are dynamically grouped into clusters. Within every cluster, one of the cluster nodes is elected in turn to be the cluster head for a time interval called cluster period. At the beginning of every cluster period, each new elected cluster head broadcasts, to its cluster nodes, the values of two relative to the sensed attribute thresholds. The first of them is the so called hard threshold. It is the minimum value of the sensed attribute required to force a sensor node to activate its transmitter and transmit to the cluster head. The use of the hard threshold minimizes the number of transmissions for the reason that the nodes transmit only when the sensed attribute exceeds a critical value. The second one is the so called soft threshold. It represents a small alteration in the value of the sensed attribute that prompts the node to turn on its transmitter and transmit. The use of the soft threshold reduces further the number of transmissions, for the reason that in the presence of little or no change in the sensed attribute the sensor nodes do not transmit. Each cluster head collects and aggregates all data it receives from its cluster nodes and forwards the aggregated data either directly or indirectly to the base station.
TEEN has been designed so as to react to sudden alterations of the sensed attributes. Therefore, it is appropriate for reactive networks and time critical applications. However, TEEN is not suitable for applications which require periodic reports since the nodes may not transmit and thus the user may not get any data at all from the network if the thresholds are not reached.
APTEEN is an extension of TEEN, also proposed by Manjeshwar and Agrawal [
15]. Although APTEEN makes use of a hierarchical scheme similar to that adopted by TEEN, it is however a hybrid protocol given that it enables both reactive and proactive ways of operation. More precisely, in APTEEN sensor nodes are required not only to respond instantly to time critical situations but to periodically send data too. The periodicity and the values of thresholds are adapted to the user needs and the type of the application.
APTEEN incorporates query handling in an efficient way. Three different query types are supported: historical, in order to explore past data, one-time, to take a snapshot view of the network and persistent, to observe an event for a period of time. Experimentally has been shown that APTEEN surpasses LEACH in terms of energy dissipation and network lifetime. However, the same simulation results proved that TEEN outperforms both protocols [
15].
Many other hierarchical routing protocols have been proposed either in the past [
8,
9] or more recently [
16,
17]. Similarly, many alternative approaches have been proposed for energy conservation in WSNs, for instance through optimized clustering [
18], or collaborative sensing and adaptive target estimation [
19]. However, any reference to them is out of the scope of this article due to their dissimilarities from SHPER when compared according to specific features of classification.
2.2. Route Selection Schemes
Although a routing protocol may indicate the source and destination nodes associated with the routing procedures, it may not however specify the path through which a transmitting node should route its data to the receiving node. One of the main factors which influence the power awareness of a routing procedure is the selection of the most energy efficient route. In wired networks, where there are not any energy limitations, the hop count or/and the delay can be considered as suitable metrics for route selection. However, in WSNs the energy issue should be taken into account in order to find the most appropriate paths.
It is for this reason why many energy efficient route selection policies have been suggested. Singh
et al. proposed the MBCR and MMBCR algorithms [
20]. According to MBCR, the route having the maximum residual energy is selected. The main drawback of this scheme is that it can lead to decreased fairness among the WSN nodes since one node may be used extensively. The MMBCR algorithm suggests the selection of the path having the maximum residual energies of the nodes. The weakness of this algorithm is that it may lead to extremely lengthy paths.
Scott and Bambos proposed the MTPR algorithm, which recommends the selection of the route having the minimum total energy consumption during transmission [
21]. The disadvantage of MTPR is that it cannot assure the life extension of each individual node because it does not take into consideration its residual energy.
Chang and Tassioulas proposed the MREPsum and MREPcap algorithms [
22]. The first of them considers a cost function which represents the reciprocal of the residual energy of a node after the transmission of a packet, while the second uses as a cost function the energy expenditure per bit transmission divided by the residual energy.
Finally, Vergados
et al. propose xMBCR and xMREPsum [
23]. In these two schemes the cost functions proposed by MBCR and MREPsum correspondingly are raised to the power of a parameter, the value of which is adjusted in order to improve the performance of the two parent algorithms.
3. SHPER Protocol Model Description
This article proposes the enhanced integration of a hierarchical reactive routing protocol named SHPER, which aims at the achievement of energy conservation through the use of both an energy efficient routing strategy and a power aware route selection scheme.
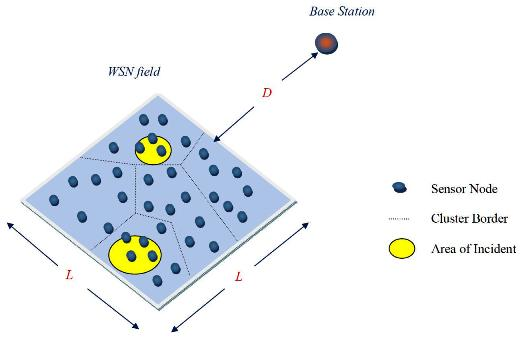
The model of the SHPER protocol supposes the coexistence of a base station and a set of homogeneous sensor nodes which are randomly distributed within a delimited area of interest. The base station is located at a distant position away from the sensor field. Both the base station and the set of the sensor nodes are supposed to be immobile (stationary). It is further assumed that the base station is able to transmit with high enough power to all the network nodes, due to its unlimited power supply. However, the network nodes are supposed to be energy constrained. All the network nodes are dynamically grouped into clusters. One of the nodes within every cluster is elected to be the cluster head. The cluster heads located close enough to the network base station are capable of direct transmission to the base station with reasonable energy expenditure. These cluster heads are supposed to be the
Upper Level cluster heads. In a similar way, cluster heads located far away from the network base station, are considered to be the
Lower Level cluster heads. This architecture scheme is illustrated in
Figure 1. The adoption of such a scheme ensures the network scalability i.e., the ability of the routing procedures to sustain their performance unaffected by the increase of the overall network size. This is achieved because even nodes located at the most distant positions of the network field are able to route their messages to the base station by multihop routing via other neighboring nodes of the Lower Level and nodes of the Upper Level.
Moreover, contrary to other hierarchical protocols as those described in Section 2, the SHPER protocol specifies that the election of the cluster heads is not randomized. More precisely, the node elected to be the cluster head within each cluster is the one having the maximum residual energy. Furthermore, the route selection policy proposed takes into consideration both the residual energy of nodes and the energy consumption for all possible paths.
4. Protocol Operation Description
The operation of SHPER protocol, which is analytically explained in the rest of this section, consists of two phases, which namely are the initialization phase and the steady state phase.
At the very first round of the initialization phase, all nodes have to keep their receivers on (step 1). This is because the base station creates a TDMA (Time Division Multiple Access) schedule and requests the nodes to advertise themselves (step 2). The size of this schedule is equal to the number of the existing network nodes. In fact, this is the unique piece of information that the base station needs to have about the network field.
When the TDMA schedule is broadcasted, all nodes, during their allocated time slots, transmit their advertisement messages using the same transmission energy. In this way, each time a node advertises itself, the other nodes which receive this advertisement message estimate their comparative distance from this node, according to the power of the advertisement signal received (step 3).
As soon as the node advertisement procedure is accomplished, the base station chooses in a random way some of the nodes from which it has received an advertisement message to be the high level cluster heads. Similarly, the base station elects some of the nodes from which it has not received any advertisement message to be the low level cluster heads. The overall number of nodes which are assigned to be cluster heads is considered to be predefined (step 4).
After that, the base station broadcasts the identities (IDs) of the newly elected cluster heads. It also broadcasts the values of soft and hard thresholds (step 5). The use of these thresholds is explained in detail later on.
Next, each non cluster head node selects for the current round to participate into the cluster of the cluster head, whose advertisement message had been received before with the largest signal strength (step 6).
Since lower level cluster head nodes cannot transmit directly to the base station, it is necessary for them to route their messages via a path consisting of an upper level cluster head node and possibly other lower level cluster head nodes which are located closer to the network upper level. In this way however, there are various alternative paths that may me followed.
According to SHPER algorithm, each path
p = (
c1,
c2,…,
cn) between a lower level cluster head node
c1 and the base station
cn that spans
n − 2 intermediate cluster head nodes
c2,…,
cn−1, is assigned with a corresponding value of the Routing Index
RI(p), which is shown in
Equation (1):
where
Eri denotes the residual energy of the cluster head node
ci, and
E(
ci,
ci+1) denotes the energy consumed for a message to be routed between two sequential cluster head nodes c
i and
ci+1.
If
A is the set of all possible paths
pl that can be followed for the transmission of the messages of a lower level cluster head to the base station, then the path
pk selected is the one which satisfies the property given in
Equation (2):
By using
Equations (1) and
(2) each lower level cluster head defines the mostly energy efficient path to route its messages to the base station and selects the upper level cluster to belong to (step 7).
After each node has decided which cluster it belongs to, it informs its corresponding cluster head that is going to be a member of its cluster. Each node transmits this information back to its corresponding cluster head using a CSMA (Carrier-Sense Multiple Access) MAC protocol (step 8). That is why, cluster head nodes have to keep their receivers on during this specific step.
Each cluster head receives in this way all the messages from the nodes that want to be included in its cluster and creates, according to their quantity, a TDMA schedule of corresponding size (step 9).
Then each cluster head broadcasts this schedule back to the nodes in its cluster, in order to inform each node when it can transmit (step 10).
Next, the data transmission may start. Thus, during its allocated transmission time, each node sends to its cluster head quantitative data concerning the sensed events. In a way similar to that proposed in TEEN hard and soft thresholds are utilized in the SHPER protocol too. Thus, data are transmitted by a node to its cluster head within its corresponding time slot only when the presence of a sensed event is detected. This happens only when this node measures a value of the sensed attribute which is equal or greater than the hard threshold or when this value changes by an amount equal to or greater than the soft threshold. Along with the data concerning the sensed attributes the node transmits the current value of its residual energy. The radio of each non cluster head node can be turned off until the node’s allocated transmission time comes, thus minimizing energy dissipation in these nodes (step 11).
Each cluster head collects the data transmitted to it by the nodes of its own cluster (step 12). When all the data have been received, each cluster head performs signal processing functions to aggregate the data it has received along with its own data into a single composite message. This message contains the ID of the node having the highest residual energy among the cluster nodes, along with the most excessive (e.g., maximum) value of the sensed variable and the id of the node that has sensed it (step 13).
After each cluster head has created its aggregate message, it waits until its own time slot in order to transmit this aggregate message to the base station either directly, if this is possible, or via intermediate upper level cluster heads according to the path suggested by the use of
Equations (1) and
(2) (step 14).
Next, the base station collects all the messages transmitted to it (step 15).
After this step is completed, the initialization phase is ended and the steady state phase begins.
Hence, the base station determines the new cluster heads by using the data of the received messages. More specifically, the node having the highest residual energy in each cluster is elected to be the new cluster head. Moreover, the new values of soft and hard thresholds are defined (step16).
After that, all nodes switch their receivers on (step 17).
Finally, the base station broadcasts the ids of the new cluster heads along with the values of the thresholds (step 18).
Subsequently, each non cluster head node chooses the cluster it intends to belong to. The steady state phase is further carried on as a continuously recurrent execution of the procedures described above from step 6 to step 18.
A synoptic overview of the SHPER protocol algorithm is graphically depicted in
Figure 2.
6. Conclusions
This work focused on hierarchical routing in WSNs through the use of a new enhanced reactive protocol, named SHPER, which aims at the achievement of power conservation through energy efficient routing.
Contrary to other popular routing protocols, SHPER performs the cluster leadership in a non randomized way, but by taking into account the residual energy of nodes. Thus, energy balance is achieved and the power depletion among the nodes is performed in a more even way.
Moreover, the data routing is based on a route selection policy which takes into consideration both the energy reserves of the nodes and the communication cost associated with the potential paths. A consequence of this is that optimal routes are selected and significant power conservation is achieved.
Furthermore, many other protocols are based on single hop routing. This kind of routing is impractical in networks deployed over wide regions. In contradiction to this, SHPER adopts both multihop routing and hierarchical architecture. In this way, the network scalability is retained.
An extended set of simulation tests were performed, comparing SHPER against TEEN, which is considered to be one of the most advanced hierarchical WSN protocols. The simulation comparison of these two protocols took place over several network configurations for various locations of the base station both with and without uniform distribution of node initial energy. Simulation tests compared the two protocols with reference to the number of nodes remaining alive over time, the first node depletion time, the last node depletion time and the average consumption.
Simulation results showed that SHPER outperforms TEEN concerning all of the energy performance metrics. Moreover, it was shown that the beneficial results offered by the use of SHPER are further increased when a non uniform initial node energy distribution is adopted. This makes SHPER even more preferable in real life applications where imbalance in energy distribution is the common case.