A Lightweight Messaging Protocol for Internet of Things Devices
Abstract
:1. Introduction
2. Related Works
3. Research Motivation
- The proposal of a lightweight messaging protocol based on CoAP for D2D communication, and
- The proposal of a mechanism to detect message spoofing with reduced header parsing complexity.
4. Methodology
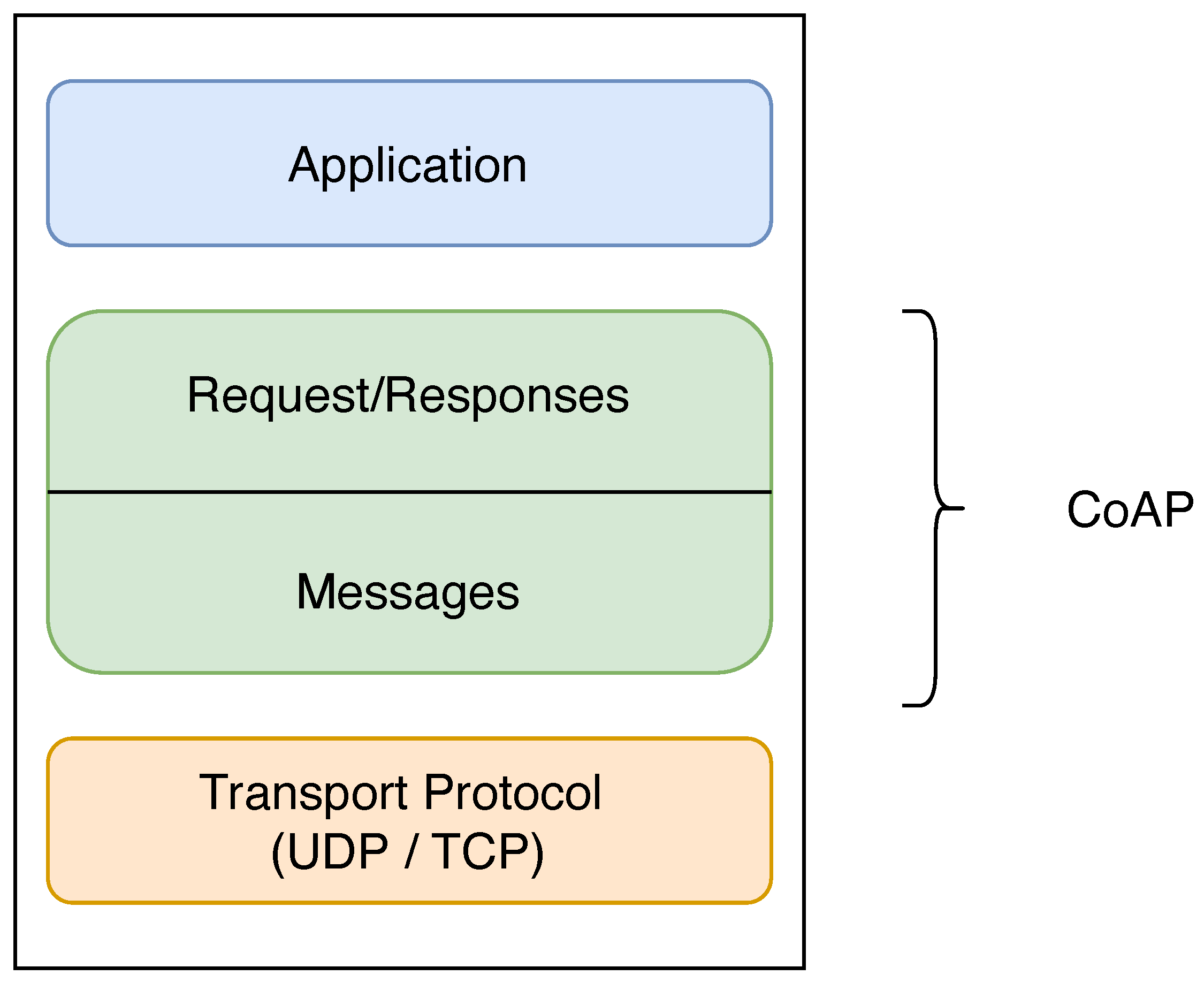
4.1. CoAP Stack
4.2. Analysis of the CoAP Stack
4.3. LiMP Stack
- Version (VER): VER is a 2-bit unsigned integer. Indicates the LiMP version number. The default value is set to 1 (01 in binary) to indicate its initial release.
- Type (T): The T field is a 2-bit unsigned integer. Indicates of the message is of the type Confirmable (0), Non-confirmable (1), Acknowledgement (2), or Reset (2).
- Code: This field stores a 2-bit unsigned integer. Indicates the request and response Method Codes. GET (0), POST (1), BadRequest (2), ServiceUnavailable (3). Detailed responses to requests can be included in the message payload.
- Content-Format (CF): The CF is a 2-bit unsigned integer. It indicates the type of encoding of the payload contents. It was narrowed down to two(2) most common content-formats; AppXML (XML format)—0 and AppJSON (JSON format)—1.
- Message-ID: The Message-ID portion is an 8-bit unsigned integer in network byte order. It is used to match requests to responses. This is 8-bits lesser than CoAP’s implementation. To deal with request/response replays by an attacker or a malicious device, an ETag is included in the message payload to detect such attacks since 8-bit or 16-bit (in the case of CoAP) message-IDs are computationally easy for an attacker to compute. The ETag is a hexadecimal value resulting from a bitwise operation of the Message-ID and a current timestamp embedded in the message payload. Further details are provided in Section 5.1.
4.4. Benchmark Test and Analysis
- The PDU sizes and
- The RTT of requests/responses of the application layer messaging protocols
5. Results and Discussion
5.1. Security Analysis of LiMP
- the ease of spoofing both 16 and 8-bit message-ID, and
- how LiMP uses a simple ETag generation mechanism to prevent message spoofing.
| Algorithm 1 ETag Generation Algorithm. |
| 1: procedure generate(seed, timestamp) |
| 2: % seed (bounded between 0, 255 inclusive), timestamp (time in milliseconds) |
| 3: ← bin2hex(bin(seed) + bin(timestamp)) |
| 4: end procedure |
| 5: procedure bin2hex(binary_data) |
| 6: ← hex(int(binary_data)) |
| 7: end procedure |
| 8: procedure hex2bin(hex_data) |
| 9: ← bin(int(hex_data)) |
| 10: end procedure |
| 11: procedure is_valid(e_tag, timestamp, seed) |
| 12: if generate(seed, timestamp) == e_tag then |
| 13: ← True |
| 14: else |
| 15: ← False |
| 16: end if |
| 17: end procedure |
6. Conclusions and Recommendation
7. Patents
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Abbreviations
| IoT | Internet of Things |
| D2D | Device-to-Device |
| LAN | Local Area Network |
| M2M | Machine-to-Machine |
| MQTT | Message Queueing Telemetry Transport |
| AMQP | Advanced Message Queuing Protocol |
| CoAP | Constrained Application Protocol |
| eUtility | External Utility |
| BLE | Bluetooth Lower Energy |
| NFC | Near Field Communication |
| LPWAN | Low Power Wide Area Network |
| WSN | Wireless Sensor Networks |
| 6LoWPAN | IPv6 over Low-Power Wireless Personal Area Networks |
| RPL | Routing Protocol for Low-Power and Lossy Networks |
| TLS | Transport Layer Security |
| DTLS | Datagram Transport Layer Security |
| TCP | Transmission Control Protocol |
| UDP | User Datagram Protocol |
| HTTP | HyperText Transfer Protocol |
| LiMP | Lightweight Messaging Protocol |
| DDS | Data Distribution Service |
| XMPP | eXtensible Messaging and Presence Protocol |
| REST | Representational State Transfer |
| CoRE | Constrained RESTful Environments |
| IP | Internet Protocol |
| IPv6 | IP version 6 |
| API | Application Programming Interface |
| QoS | Quality of Service |
| XML | eXtensible Markup Language |
| SCTP | Stream Control Transmission Protocol |
| UTF | Unicode Transformation Format |
| JSON | JavaScript Object IoTation |
| ETag | Entity Tag |
| PDU | Packet Data Unit |
| RTT | Round-Trip Time |
| ARM | Advanced RISC Machines |
References
- Laghari, A.A.; Wu, K.; Laghari, R.A.; Ali, M.; Khan, A.A. A Review and State of Art of Internet of Things (IoT). In Archives of Computational Methods in Engineering; Springer: Berlin/Heidelberg, Germany, 2021. [Google Scholar] [CrossRef]
- Malhotra, P.; Singh, Y.; Anand, P.; Bangotra, D.K.; Singh, P.K.; Hong, W.C. Internet of Things: Evolution, Concerns and Security Challenges. Sensors 2021, 21, 1809. [Google Scholar] [CrossRef] [PubMed]
- Wang, J.; Lim, M.K.; Wang, C.; Tseng, M.L. The evolution of the Internet of Things (IoT) over the past 20 years. Comput. Ind. Eng. 2021, 155, 107174. [Google Scholar] [CrossRef]
- Hanes, D.; Salgueiro, G.; Grossetete, P.; Barton, R.; Henry, J. IoT Fundamentals: Networking Technologies, Protocols, and Use Cases for the Internet of Things; Cisco Press: Indianapolis, IN, USA, 2017. [Google Scholar]
- Sicari, S.; Rizzardi, A.; Grieco, L.; Coen-Porisini, A. Security, privacy and trust in Internet of Things: The road ahead. Comput. Netw. 2015, 76, 146–164. [Google Scholar] [CrossRef]
- Mosenia, A.; Jha, N.K. A Comprehensive Study of Security of Internet-of-Things. IEEE Trans. Emerg. Top. Comput. 2017, 5, 586–602. [Google Scholar] [CrossRef]
- Khan, M.A.; Salah, K. IoT security: Review, blockchain solutions, and open challenges. Future Gener. Comput. Syst. 2018, 82, 395–411. [Google Scholar] [CrossRef]
- Voas, J. Networks of ‘Things’. NIST Spec. Publ. 2016, 800, 183–800. [Google Scholar]
- Di Martino, B.; Rak, M.; Ficco, M.; Esposito, A.; Maisto, S.; Nacchia, S. Internet of things reference architectures, security and interoperability: A survey. Internet Things 2018, 1–2, 99–112. [Google Scholar] [CrossRef]
- Radoglou Grammatikis, P.I.; Sarigiannidis, P.G.; Moscholios, I.D. Securing the Internet of Things: Challenges, threats and solutions. Internet Things 2019, 5, 41–70. [Google Scholar] [CrossRef]
- binti Mohamad Noor, M.; Hassan, W.H. Current research on Internet of Things (IoT) security: A survey. Comput. Netw. 2019, 148, 283–294. [Google Scholar] [CrossRef]
- Yousuf, O.; Mir, R.N. A survey on the Internet of Things security: State-of-art, architecture, issues and countermeasures. Inf. Comput. Secur. 2019, 27, 292–323. [Google Scholar] [CrossRef]
- Aly, M.; Khomh, F.; Haoues, M.; Quintero, A.; Yacout, S. Enforcing security in Internet of Things frameworks: A Systematic Literature Review. Internet Things 2019, 6, 100050. [Google Scholar] [CrossRef]
- Bhabad, M.A.; Bagade, S.T. Article: Internet of Things: Architecture, Security Issues and Countermeasures. Int. J. Comput. Appl. 2015, 125, 1–4. [Google Scholar]
- HaddadPajouh, H.; Dehghantanha, A.; Parizi, R.M.; Aledhari, M.; Karimipour, H. A survey on Internet of Things security: Requirements, challenges, and solutions. Internet Things 2021, 14, 100129. [Google Scholar] [CrossRef]
- Ogonji, M.M.; Okeyo, G.; Wafula, J.M. A survey on privacy and security of Internet of Things. Comput. Sci. Rev. 2020, 38, 100312. [Google Scholar] [CrossRef]
- Lombardi, M.; Pascale, F.; Santaniello, D. Internet of Things: A General Overview between Architectures, Protocols and Applications. Information 2021, 12, 87. [Google Scholar] [CrossRef]
- Lin, J.; Yu, W.; Zhang, N.; Yang, X.; Zhang, H.; Zhao, W. A Survey on Internet of Things: Architecture, Enabling Technologies, Security and Privacy, and Applications. IEEE Internet Things J. 2017, 4, 1125–1142. [Google Scholar] [CrossRef]
- Shelby, Z.; Hartke, K.; Bormann, C. The Constrained Application Protocol (CoAP). RFC 7252. 2014. Available online: https://iottestware.readthedocs.io/en/master/coap_rfc.html (accessed on 10 December 2021).
- Postel, J. User Datagram Protocol STD 6. RFC 768, The Request for Comments (RFC) Series. 1980. Available online: https://www.hjp.at/doc/rfc/rfc768.html (accessed on 10 December 2021).
- Saint-Andre, P.; Loreto, S.; Salsano, S.; Wilkins, G. Known Issues and Best Practices for the Use of Long Polling and Streaming in Bidirectional HTTP. RFC 6202. 2011. Available online: https://www.hjp.at/doc/rfc/rfc6202.html (accessed on 10 December 2021). [CrossRef] [Green Version]
- Melnikov, A.; Fette, I. The WebSocket Protocol. RFC 6455, The Request for Comments (RFC) Series. 2011. Available online: https://www.hjp.at/doc/rfc/rfc6455.html (accessed on 10 December 2021). [CrossRef]
- Message Queueing Telemetry Transport Protocol. v3.1.1. 2014. OASIS Standard. Available online: https://docs.oasis-open.org/mqtt/mqtt/v3.1.1/os/mqtt-v3.1.1-os.html (accessed on 10 December 2021).
- Saint-Andre, P. Extensible Messaging and Presence Protocol (XMPP): Core. RFC 6120, The Request for Comments (RFC) Series. 2011. Available online: https://www.hjp.at/doc/rfc/rfc6120.html (accessed on 10 December 2021). [CrossRef] [Green Version]
- Saint-Andre, P. Extensible Messaging and Presence Protocol (XMPP): Address Format. RFC 6122, The Request for Comments (RFC) Serie. 2011. Available online: https://www.hjp.at/doc/rfc/rfc7622.html (accessed on 10 December 2021). [CrossRef]
- Data Distribution Service. v1.4. 2015. Object Management Group (OMG). Available online: https://www.omg.org/spec/DDS/1.4/About-DDS (accessed on 10 December 2021).
- Naik, N. Choice of effective messaging protocols for IoT systems: MQTT, CoAP, AMQP and HTTP. In Proceedings of the 2017 IEEE International Systems Engineering Symposium (ISSE), Vienna, Austria, 11–13 October 2017; pp. 1–7. [Google Scholar]
- Al-Masri, E.; Kalyanam, K.R.; Batts, J.; Kim, J.; Singh, S.; Vo, T.; Yan, C. Investigating Messaging Protocols for the Internet of Things (IoT). IEEE Access 2020, 8, 94880–94911. [Google Scholar] [CrossRef]
- Huh, J.H. Reliable User Datagram Protocol as a Solution to Latencies in Network Games. Electronics 2018, 7, 295. [Google Scholar] [CrossRef] [Green Version]
- Thangavel, D.; Ma, X.; Valera, A.; Tan, H.X.; Tan, C.K.Y. Performance evaluation of MQTT and CoAP via a common middleware. In Proceedings of the 2014 IEEE Ninth International Conference on Intelligent Sensors, Sensor Networks and Information Processing (ISSNIP), Singapore, 21–24 April 2014; pp. 1–6. [Google Scholar]
- Tan, E.K.; Chong, Y.W.; Setyawan, R.A.; Niswar, M.; Mya, K.T. Lightweight messaging protocol for precision agriculture. In Proceedings of the 2021 International Conference on Information Networking (ICOIN), Jeju Island, Korea, 13–16 January 2021; pp. 403–407. [Google Scholar]
- Thota, P.; Kim, Y. Implementation and Comparison of M2M Protocols for Internet of Things. In Proceedings of the 2016 4th Intl Conf on Applied Computing and Information Technology/3rd Intl Conf on Computational Science/Intelligence and Applied Informatics/1st Intl Conf on Big Data, Cloud Computing, Data Science Engineering (ACIT-CSII-BCD), Las Vegas, NV, USA, 12–14 December 2016; pp. 43–48. [Google Scholar]























| Criteria | CoAP | WebSocket | MQTT | DDS | XMPP | AMQP |
|---|---|---|---|---|---|---|
| Architecture | Client/Server or Client Broker | Client/Server or Client/Broker | Client/Broker | Client/Server | Client/Server | Client/Broker or Client/Server |
| Header Size | 4 Bytes | 4 Bytes | 2 Bytes | 124 Bytes | Undefined | 8 Bytes |
| Transport Protocol | UDP (default), TCP, SCTP | TCP | TCP, UDP (Some Implementations) | UDP, TCP, SCTP | TCP | TCP, SCTP |
| Encoding Format | Binary | Text (UTF-8) | Binary | Binary | Binary | XML |
| Field | Number of Bits | Details |
|---|---|---|
| Version (VER) | 2-bit unsigned integer | Indicates the CoAP version number. The default value is set to 1 (01 in binary). |
| Type (T) | 2-bit unsigned integer | Indicates if the message is of type Confirmable (0), Non-confirmable (1), Acknowledgement (2), or Reset (3). |
| Token Length (TKL) | 4-bit unsigned integer | Indicates the length of the variable-length Token field (0–8) bytes. Lengths 9–15 are reserved and processed as a message format error. |
| Code | 8-bit unsigned integer | Divided into 3-bit class (most significant bits) and 5-bit detail (least significant bits), which are used to indicate requests and responses format. |
| Message-ID | 16-bit unsigned integer | It is used to detect message duplication and further match messages of type Acknowledgement/Reset to messages of Confirmable/Non-confirmable. |
| CoAP-TCP | LiMP-TCP | CoAP-UDP | LiMP-UDP | |
|---|---|---|---|---|
| PDU (bytes) | 81 | 68 | 57 | 44 |
| Device | 16-bit (Time/ms) | 8-bit (Time/ms) |
|---|---|---|
| Nvidia Jetson Nano | 8.037 | 0.022 |
| Nvidia Tegra | 12.989 | 0.032 |
| Raspberry Pi | 20.946 | 0.063 |
| iPhone 7 | 1.891 | 0.005 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Agyemang, J.O.; Kponyo, J.J.; Gadze, J.D.; Nunoo-Mensah, H.; Yu, D. A Lightweight Messaging Protocol for Internet of Things Devices. Technologies 2022, 10, 21. https://doi.org/10.3390/technologies10010021
Agyemang JO, Kponyo JJ, Gadze JD, Nunoo-Mensah H, Yu D. A Lightweight Messaging Protocol for Internet of Things Devices. Technologies. 2022; 10(1):21. https://doi.org/10.3390/technologies10010021
Chicago/Turabian StyleAgyemang, Justice Owusu, Jerry John Kponyo, James Dzisi Gadze, Henry Nunoo-Mensah, and Dantong Yu. 2022. "A Lightweight Messaging Protocol for Internet of Things Devices" Technologies 10, no. 1: 21. https://doi.org/10.3390/technologies10010021
APA StyleAgyemang, J. O., Kponyo, J. J., Gadze, J. D., Nunoo-Mensah, H., & Yu, D. (2022). A Lightweight Messaging Protocol for Internet of Things Devices. Technologies, 10(1), 21. https://doi.org/10.3390/technologies10010021









