Journal Description
Mathematics
Mathematics
is a peer-reviewed, open access journal which provides an advanced forum for studies related to mathematics, and is published semimonthly online by MDPI. The European Society for Fuzzy Logic and Technology (EUSFLAT) and International Society for the Study of Information (IS4SI) are affiliated with Mathematics and their members receive a discount on article processing charges.
- Open Access— free for readers, with article processing charges (APC) paid by authors or their institutions.
- High Visibility: indexed within Scopus, SCIE (Web of Science), RePEc, and other databases.
- Journal Rank: JCR - Q1 (Mathematics) / CiteScore - Q1 (General Mathematics)
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 16.9 days after submission; acceptance to publication is undertaken in 2.6 days (median values for papers published in this journal in the second half of 2023).
- Recognition of Reviewers: reviewers who provide timely, thorough peer-review reports receive vouchers entitling them to a discount on the APC of their next publication in any MDPI journal, in appreciation of the work done.
- Sections: published in 13 topical sections.
- Companion journals for Mathematics include: Foundations, AppliedMath, Analytics, International Journal of Topology, Geometry and Logics.
Impact Factor:
2.4 (2022);
5-Year Impact Factor:
2.3 (2022)
Latest Articles
A Theory of Functional Connections-Based hp-Adaptive Mesh Refinement Algorithm for Solving Hypersensitive Two-Point Boundary-Value Problems
Mathematics 2024, 12(9), 1360; https://doi.org/10.3390/math12091360 (registering DOI) - 29 Apr 2024
Abstract
This manuscript introduces the first hp-adaptive mesh refinement algorithm for the Theory of Functional Connections (TFC) to solve hypersensitive two-point boundary-value problems (TPBVPs). The TFC is a mathematical framework that analytically satisfies linear constraints using an approximation method called a constrained expression.
[...] Read more.
This manuscript introduces the first hp-adaptive mesh refinement algorithm for the Theory of Functional Connections (TFC) to solve hypersensitive two-point boundary-value problems (TPBVPs). The TFC is a mathematical framework that analytically satisfies linear constraints using an approximation method called a constrained expression. The constrained expression utilized in this work is composed of two parts. The first part consists of Chebyshev orthogonal polynomials, which conform to the solution of differentiation variables. The second part is a summation of products between switching and projection functionals, which satisfy the boundary constraints. The mesh refinement algorithm relies on the truncation error of the constrained expressions to determine the ideal number of basis functions within a segment’s polynomials. Whether to increase the number of basis functions in a segment or divide it is determined by the decay rate of the truncation error. The results show that the proposed algorithm is capable of solving hypersensitive TPBVPs more accurately than MATLAB R2021b’s bvp4c routine and is much better than the standard TFC method that uses global constrained expressions. The proposed algorithm’s main flaw is its long runtime due to the numerical approximation of the Jacobians.
Full article
(This article belongs to the Special Issue Dynamics and Control Using Functional Interpolation)
Open AccessArticle
Analysis of High-Order Bright–Dark Rogue Waves in (2+1)-D Variable-Coefficient Zakharov Equation via Self-Similar and Darboux Transformations
by
Hangwei Zhang, Jie Zong, Geng Tian and Guangmei Wei
Mathematics 2024, 12(9), 1359; https://doi.org/10.3390/math12091359 (registering DOI) - 29 Apr 2024
Abstract
This paper conducts an in-depth study on the self-similar transformation, Darboux transformation, and the excitation and propagation characteristics of high-order bright–dark rogue wave solutions in the (2+1)-dimensional variable-coefficient Zakharov equation. The Zakharov equation is instrumental for studying complex nonlinear interactions in these areas,
[...] Read more.
This paper conducts an in-depth study on the self-similar transformation, Darboux transformation, and the excitation and propagation characteristics of high-order bright–dark rogue wave solutions in the (2+1)-dimensional variable-coefficient Zakharov equation. The Zakharov equation is instrumental for studying complex nonlinear interactions in these areas, with specific implications for energy transfer processes in plasma and nonlinear wave propagation systems. By analyzing bright–dark rogue wave solutions—phenomena that are critical in understanding high-energy events in optical and fluid environments—this research elucidates the intricate dynamics of energy concentration and dissipation. Using the self-similar transformation method, we map the (2+1)-dimensional equation to a more tractable (1+1)-dimensional nonlinear Schrödinger equation form. Through the Lax pair and Darboux transformation, we successfully construct high-order solutions that reveal how variable coefficients influence rogue wave features, such as shape, amplitude, and dynamics. Numerical simulations demonstrate the evolution of these rogue waves, offering novel perspectives for predicting and mitigating extreme wave events in engineering applications.This paper crucially advances the practical understanding and manipulation of nonlinear wave phenomena in variable environments, providing significant insights for applications in optical fibers, atmospheric physics, and marine engineering.
Full article
(This article belongs to the Topic Advances in Nonlinear Dynamics: Methods and Applications)
Open AccessArticle
Two-Variable q-Hermite-Based Appell Polynomials and Their Applications
by
Mohammed Fadel, Maryam Salem Alatawi and Waseem Ahmad Khan
Mathematics 2024, 12(9), 1358; https://doi.org/10.3390/math12091358 (registering DOI) - 29 Apr 2024
Abstract
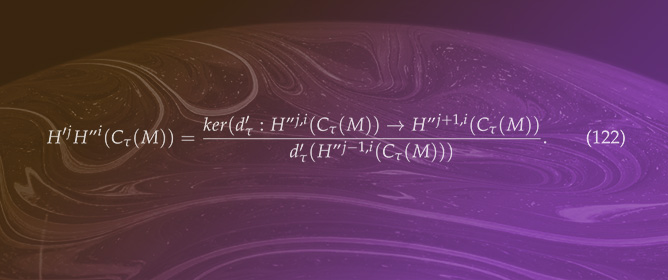
A noteworthy advancement within the discipline of q-special function analysis involves the extension of the concept of the monomiality principle to q-special polynomials. This extension helps analyze the quasi-monomiality of many q-special polynomials. This extension is a helpful tool for
[...] Read more.
A noteworthy advancement within the discipline of q-special function analysis involves the extension of the concept of the monomiality principle to q-special polynomials. This extension helps analyze the quasi-monomiality of many q-special polynomials. This extension is a helpful tool for considering the quasi-monomiality of several q-special polynomials. This study aims to identify and establish the characteristics of the 2-variable q-Hermite–Appell polynomials via an extension of the concept of monomiality. Also, we present some applications that are taken into account.
Full article
(This article belongs to the Special Issue Analytical and Computational Methods in Differential Equations, Special Functions, Transmutations and Integral Transforms, 2nd Edition)
►▼
Show Figures
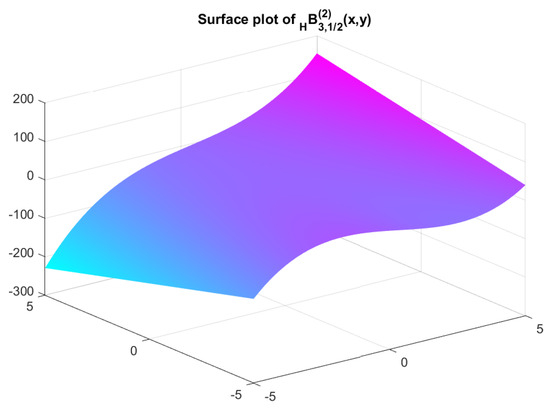
Figure 1
Open AccessArticle
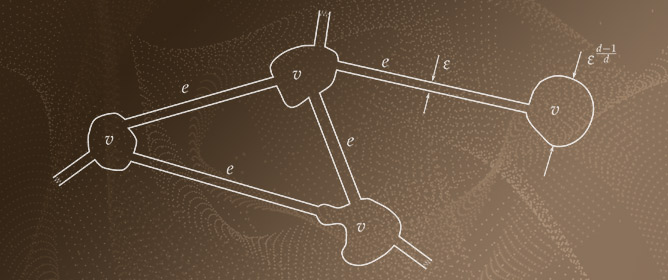
Extending Undirected Graph Techniques to Directed Graphs via Category Theory
by
Sebastian Pardo-Guerra, Vivek Kurien George, Vikash Morar, Joshua Roldan and Gabriel Alex Silva
Mathematics 2024, 12(9), 1357; https://doi.org/10.3390/math12091357 (registering DOI) - 29 Apr 2024
Abstract
We use Category Theory to construct a `bridge’ relating directed graphs with undirected graphs, such that the notion of direction is preserved. Specifically, we provide an isomorphism between the category of simple directed graphs and a category we call `prime graphs category’; this
[...] Read more.
We use Category Theory to construct a `bridge’ relating directed graphs with undirected graphs, such that the notion of direction is preserved. Specifically, we provide an isomorphism between the category of simple directed graphs and a category we call `prime graphs category’; this has as objects labeled undirected bipartite graphs (which we call prime graphs), and as morphisms undirected graph morphisms that preserve the labeling (which we call prime graph morphisms). This theoretical bridge allows us to extend undirected graph techniques to directed graphs by converting the directed graphs into prime graphs. To give a proof of concept, we show that our construction preserves topological features when applied to the problems of network alignment and spectral graph clustering.
Full article
Open AccessArticle
Practical Security of Continuous Variable Quantum Key Distribution Ascribable to Imperfect Modulator for Fiber Channel
by
Shengzhe Xu, Zicheng Zhou and Ying Guo
Mathematics 2024, 12(9), 1356; https://doi.org/10.3390/math12091356 - 29 Apr 2024
Abstract
An amplitude modulator plays an essential role in the implementation of continuous-variable quantum key distribution (CVQKD), whereas it may bring about a potential security loophole in the practical system. The high-frequency modulation of the actual transmitter usually results in the high rate of
[...] Read more.
An amplitude modulator plays an essential role in the implementation of continuous-variable quantum key distribution (CVQKD), whereas it may bring about a potential security loophole in the practical system. The high-frequency modulation of the actual transmitter usually results in the high rate of the system. However, an imperfect amplitude modulator (AM) can give birth to a potential information leakage from the modulation of the transmitter. To reveal a potential security loophole from the high-frequency AM embedded in the transmitter, we demonstrate an influence on the practical security of the system in terms of the secret key rate and maximal transmission distance. The results indicate the risk of this security loophole in the imperfect AM-embedded transmitter. Fortunately, the legal participants can trace back the potential information leakage that has been produced from the imperfect transmitter at high frequencies, which can be used for defeating the leakage attack in CVQKD. We find the limitations of the imperfect AM-embedded transmitter of the high-frequency quantum system, and hence, we have to trade off the practical security and the modulation frequency of the AM-embedded transmitter while considering its implementation in a practical environment.
Full article
(This article belongs to the Special Issue Quantum Cryptography and Encryption)
Open AccessArticle
Ride-Hailing Matching with Uncertain Travel Time: A Novel Interval-Valued Fuzzy Multi-Objective Linear Programming Approach
by
Sudradjat Supian, Subiyanto, Tubagus Robbi Megantara and Abdul Talib Bon
Mathematics 2024, 12(9), 1355; https://doi.org/10.3390/math12091355 - 29 Apr 2024
Abstract
This study introduces an innovative approach to tackle multi-objective linear programming (MOLP) problems amidst uncertainty, employing interval-valued fuzzy numbers. The method is tailored to resolve ride-hailing matching challenges encompassing uncertain travel times. Findings reveal that managing uncertainty parameters within interval-valued fuzzy MOLP is
[...] Read more.
This study introduces an innovative approach to tackle multi-objective linear programming (MOLP) problems amidst uncertainty, employing interval-valued fuzzy numbers. The method is tailored to resolve ride-hailing matching challenges encompassing uncertain travel times. Findings reveal that managing uncertainty parameters within interval-valued fuzzy MOLP is achieved through strategic reformulations, focusing on constraint coefficients, resulting in streamlined linear programming formulations conducive to solution simplicity. The efficacy of the proposed model in efficiently handling ride-hailing matching quandaries is demonstrated. Moreover, this study delves into the prospective applications of the developed method, including its potential for generalization to address non-linear programming (NLP) issues pertinent to the ride-hailing domain. This research advances decision-making processes under uncertainty and paves the way for broader applications beyond ride-hailing.
Full article
(This article belongs to the Section Fuzzy Sets, Systems and Decision Making)
Open AccessArticle
Dynamic Behavior and Bifurcation Analysis of a Modified Reduced Lorenz Model
by
Mohammed O. Al-Kaff, Ghada AlNemer, Hamdy A. El-Metwally, Abd-Elalim A. Elsadany and Elmetwally M. Elabbasy
Mathematics 2024, 12(9), 1354; https://doi.org/10.3390/math12091354 - 29 Apr 2024
Abstract
This study introduces a newly modified Lorenz model capable of demonstrating bifurcation within a specified range of parameters. The model demonstrates various bifurcation behaviors, which are depicted as distinct structures in the diagram. The study aims to discover and analyze the existence and
[...] Read more.
This study introduces a newly modified Lorenz model capable of demonstrating bifurcation within a specified range of parameters. The model demonstrates various bifurcation behaviors, which are depicted as distinct structures in the diagram. The study aims to discover and analyze the existence and stability of fixed points in the model. To achieve this, the center manifold theorem and bifurcation theory are employed to identify the requirements for pitchfork bifurcation, period-doubling bifurcation, and Neimark–Sacker bifurcation. In addition to theoretical findings, numerical simulations, including bifurcation diagrams, phase pictures, and maximum Lyapunov exponents, showcase the nuanced, complex, and diverse dynamics. Finally, the study applies the Ott–Grebogi–Yorke (OGY) method to control the chaos observed in the reduced modified Lorenz model.
Full article
(This article belongs to the Special Issue Applied Mathematics in Nonlinear Dynamics and Chaos)
►▼
Show Figures
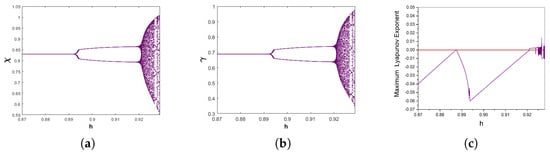
Figure 1
Open AccessEditorial
New Challenges in Mathematical Modelling and Control of COVID-19 Epidemics: Analysis of Non-Pharmaceutical Actions and Vaccination Strategies
by
Cristiano Maria Verrelli and Fabio Della Rossa
Mathematics 2024, 12(9), 1353; https://doi.org/10.3390/math12091353 (registering DOI) - 29 Apr 2024
Abstract
Since its official appearance in China in December 2019, COVID-19 (SARS-CoV-2)
immediately reached pandemic proportions on six continents and in over 195 countries [...] Full article
immediately reached pandemic proportions on six continents and in over 195 countries [...] Full article
(This article belongs to the Special Issue New Challenges in Mathematical Modelling and Control of COVID-19 Epidemics: Analysis of Non-pharmaceutical Actions and Vaccination Strategies)
Open AccessArticle
Group Doubly Coupled Designs
by
Weiping Zhou, Shigui Huang and Min Li
Mathematics 2024, 12(9), 1352; https://doi.org/10.3390/math12091352 - 29 Apr 2024
Abstract
Doubly coupled designs (DCDs) have better space-filling properties between the qualitative and quantitative factors than marginally coupled designs (MCDs) which are suitable for computer experiments with both qualitative and quantitative factors. In this paper, we propose a new class of DCDs, called group
[...] Read more.
Doubly coupled designs (DCDs) have better space-filling properties between the qualitative and quantitative factors than marginally coupled designs (MCDs) which are suitable for computer experiments with both qualitative and quantitative factors. In this paper, we propose a new class of DCDs, called group doubly coupled designs (GDCDs), and provide methods for constructing two forms of GDCDs, within-group doubly coupled designs and between-group doubly coupled designs. The proposed GDCDs can accommodate more qualitative factors than DCDs, when the subdesigns for the qualitative factors are symmetric. The subdesigns of qualitative factors are not asymmetric in the existing results on DCDs, and in this paper, we construct GDCDs with symmetric and asymmetric designs for the qualitative factors, respectively. Moreover, detailed comparisons with existing MCDs show that GDCDs have better space-filling properties between qualitative and quantitative factors. Finally, the methods are particularly easy to implement.
Full article
(This article belongs to the Special Issue Advances in Computational Statistics, Design of Experiments, and Its Applications)
►▼
Show Figures
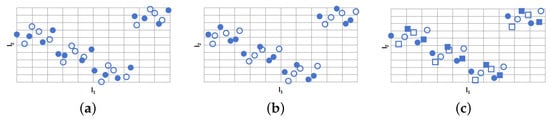
Figure 1
Open AccessArticle
Optimizing Cryptocurrency Returns: A Quantitative Study on Factor-Based Investing
by
Phumudzo Lloyd Seabe, Claude Rodrigue Bambe Moutsinga and Edson Pindza
Mathematics 2024, 12(9), 1351; https://doi.org/10.3390/math12091351 - 29 Apr 2024
Abstract
This study explores cryptocurrency investment strategies by adapting the robust framework of factor investing, traditionally applied in equity markets, to the distinctive landscape of cryptocurrency assets. It conducts an in-depth examination of 31 prominent cryptocurrencies from December 2017 to December 2023, employing the
[...] Read more.
This study explores cryptocurrency investment strategies by adapting the robust framework of factor investing, traditionally applied in equity markets, to the distinctive landscape of cryptocurrency assets. It conducts an in-depth examination of 31 prominent cryptocurrencies from December 2017 to December 2023, employing the Fama–MacBeth regression method and portfolio regressions to assess the predictive capabilities of market, size, value, and momentum factors, adjusted for the unique characteristics of the cryptocurrency market. These characteristics include high volatility and continuous trading, which differ markedly from those of traditional financial markets. To address the challenges posed by the perpetual operation of cryptocurrency trading, this study introduces an innovative rebalancing strategy that involves weekly adjustments to accommodate the market’s constant fluctuations. Additionally, to mitigate issues like autocorrelation and heteroskedasticity in financial time series data, this research applies the Newey–West standard error approach, enhancing the robustness of regression analyses. The empirical results highlight the significant predictive power of momentum and value factors in forecasting cryptocurrency returns, underscoring the importance of tailoring conventional investment frameworks to the cryptocurrency context. This study not only investigates the applicability of factor investing in the rapidly evolving cryptocurrency market, but also enriches the financial literature by demonstrating the effectiveness of combining Fama–MacBeth cross-sectional analysis with portfolio regressions, supported by Newey–West standard errors, in mastering the complexities of digital asset investments.
Full article
(This article belongs to the Special Issue Applications of Quantitative Analysis in Financial Markets)
►▼
Show Figures
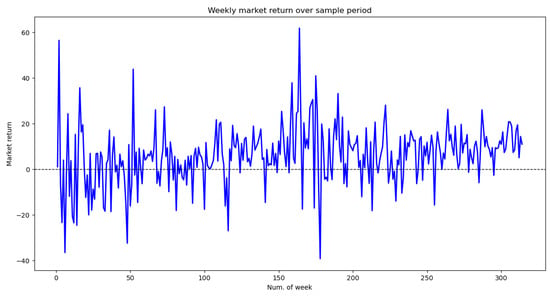
Figure 1
Open AccessArticle
Sideslip Angle Estimation for Distributed Drive Electric Vehicles Based on Robust Unscented Particle Filter
by
Jie Hu, Feiyue Rong, Pei Zhang and Fuwu Yan
Mathematics 2024, 12(9), 1350; https://doi.org/10.3390/math12091350 - 29 Apr 2024
Abstract
►▼
Show Figures
An accurate and reliable sideslip angle is crucial for active safety control systems and advanced driver-assistance systems (ADAS). The direct measurement method of the sideslip angle suffers from challenges of high costs and environmental sensitivity, so sideslip angle estimation has always been a
[...] Read more.
An accurate and reliable sideslip angle is crucial for active safety control systems and advanced driver-assistance systems (ADAS). The direct measurement method of the sideslip angle suffers from challenges of high costs and environmental sensitivity, so sideslip angle estimation has always been a significant research issue. To improve the precision and robustness of sideslip angle estimation for distributed drive electric vehicles (DDEV) in extreme maneuvering scenarios, this paper presents a novel robust unscented particle filter (RUPF) algorithm based on low-cost onboard sensors. Firstly, a nonlinear dynamics model of DDEV is constructed, providing a theoretical foundation for the design of the RUPF algorithm. Then, the RUPF algorithm, which incorporates the unscented Kalman filter (UKF) to update importance density and utilizes systematic random resampling to mitigate particle degradation, is designed for estimation. Eventually, the availability of the proposed RUPF algorithm is validated on the co-simulation platform with non-Gaussian noises. Simulation results demonstrate that RUPF algorithm attains a higher precision and stronger robustness compared with the traditional PF and UKF algorithms.
Full article
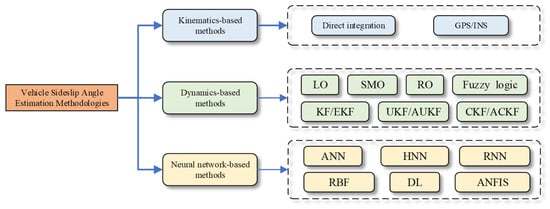
Figure 1
Open AccessArticle
A Graph-Based Keyword Extraction Method for Academic Literature Knowledge Graph Construction
by
Lin Zhang, Yanan Li and Qinru Li
Mathematics 2024, 12(9), 1349; https://doi.org/10.3390/math12091349 - 29 Apr 2024
Abstract
In this paper, we construct an academic literature knowledge graph based on the relationship between documents to facilitate the storage and research of academic literature data. Keywords are an important type of node in the knowledge graph. To solve the problem that there
[...] Read more.
In this paper, we construct an academic literature knowledge graph based on the relationship between documents to facilitate the storage and research of academic literature data. Keywords are an important type of node in the knowledge graph. To solve the problem that there are no keywords in some documents for several reasons in the process of knowledge graph construction, an improved keyword extraction algorithm called TP-CoGlo-TextRank is proposed by using word frequency, position, word co-occurrence frequency, and a word embedding model. By combining the word frequency and position in the document, the importance of words is distinguished. By introducing the GloVe word-embedding model, which brings the external knowledge of documents into the TextRank algorithm, and combining the internal word co-occurrence frequency in the documents, the word-adjacency relationship is transferred non-uniformly. Finally, the words with the highest scores are combined into phrases if they are adjacent in the original text. The validity of the TP-CoGlo-TextRank algorithm is verified by experiments. On this basis, the Neo4j graph database is used to store and display the academic literature knowledge graph, to provide data support for research tasks such as text clustering, automatic summarization, and question-answering systems.
Full article
(This article belongs to the Special Issue Advances in Machine Learning and Applications)
►▼
Show Figures
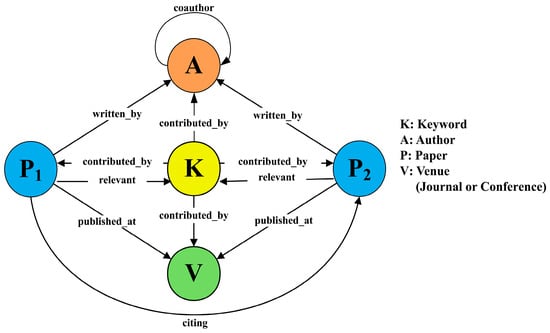
Figure 1
Open AccessArticle
The Approximation Characteristics of Weighted Band-Limited Function Space
by
Yue Li, Guanggui Chen, Yanyan Xu and Xiangyu Pan
Mathematics 2024, 12(9), 1348; https://doi.org/10.3390/math12091348 - 29 Apr 2024
Abstract
This article primarily investigates the width problem within weighted band-limited function space in a uniform setting. Through an analysis of the properties of s-numbers, we establish a connection between the widths of weighted band-limited function spaces and the s-numbers of infinite-dimensional diagonal operators.
[...] Read more.
This article primarily investigates the width problem within weighted band-limited function space in a uniform setting. Through an analysis of the properties of s-numbers, we establish a connection between the widths of weighted band-limited function spaces and the s-numbers of infinite-dimensional diagonal operators. Furthermore, employing the discretization method, we estimate the exact asymptotic orders of Kolmogorov n-width and linear n-width in the weighted band-limited function space, which is characterized by the weight
Open AccessArticle
Adaptive Parallel Scheduling Scheme for Smart Contract
by
Wenjin Yang, Meng Ao, Jing Sun, Guoan Wang, Yongxuan Li, Chunhai Li and Zhuguang Shao
Mathematics 2024, 12(9), 1347; https://doi.org/10.3390/math12091347 - 29 Apr 2024
Abstract
With the increasing demand for decentralized systems and the widespread usage of blockchain, low throughput and high latency have become the biggest stumbling blocks in the development of blockchain systems. This problem seriously hinders the expansion of blockchain and its application in production.
[...] Read more.
With the increasing demand for decentralized systems and the widespread usage of blockchain, low throughput and high latency have become the biggest stumbling blocks in the development of blockchain systems. This problem seriously hinders the expansion of blockchain and its application in production. Most existing smart contract scheduling solutions use static feature analysis to prevent contract conflicts during parallel execution. However, the conflicts between transactions are complex; static feature analysis is not accurate enough. In this paper, we first build the dependency between smart contracts by analyzing the features. After numerous experiments, we propose a conflict model to adjust the relationship between threads and conflict to achieve high throughput and low latency. Based on these works, we propose adaptive parallel scheduling for smart contracts on the blockchain. Our adaptive parallel scheduling can distinguish conflicts between smart contracts and dynamically adjust the execution strategy of smart contracts based on the conflict factors we define. We implement our scheme on ChainMaker, one of the most popular open-source permissioned blockchains, and build experiments to verify our solution. Regarding latency, our solution demonstrates remarkable efficiency compared with the fully parallel scheme, particularly in high-conflict transaction scenarios, where our solution achieves latency levels just one-twentieth of the fully parallel scheme. Regarding throughput, our solution significantly outperforms the fully parallel scheme, achieving 30 times higher throughput in high-conflict transaction scenarios. These results highlight the superior performance and effectiveness of our solution in addressing latency and throughput challenges, particularly in environments with high transaction conflicts.
Full article
(This article belongs to the Special Issue New Advances in Coding Theory and Cryptography, 2nd Edition)
►▼
Show Figures
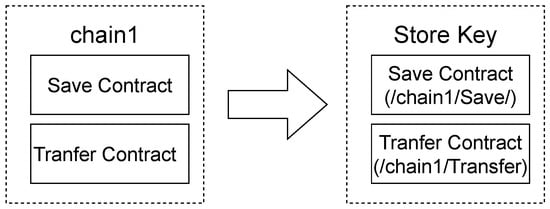
Figure 1
Open AccessArticle
Exploring Dynamic Spalling Behavior in Rock–Shotcrete Combinations: A Theoretical and Numerical Investigation
by
Lin Luo, Yichao Rui, Jiadong Qiu, Chongjin Li, Xiong Liu and Cong Chen
Mathematics 2024, 12(9), 1346; https://doi.org/10.3390/math12091346 - 29 Apr 2024
Abstract
►▼
Show Figures
Spalling is a widespread dynamic disaster during blasting excavation in underground engineering. To clarify the coupled dynamic response and spalling behavior of an underground tunnel with a spray anchor, an investigation based on the rock–shotcrete combination was conducted using theoretical and numerical methods.
[...] Read more.
Spalling is a widespread dynamic disaster during blasting excavation in underground engineering. To clarify the coupled dynamic response and spalling behavior of an underground tunnel with a spray anchor, an investigation based on the rock–shotcrete combination was conducted using theoretical and numerical methods. The mathematical representation of stress wave propagation between rock and shotcrete was deduced based on the elastic stress wave theory. A novel method for predicting the location and time of initial spalling in a rock–shotcrete combination was proposed. A numerical simulation was conducted to verify the validity of the proposed theoretical method. In addition, the effect of the material’s tensile strength, the loading amplitude, and the thickness of shotcrete on the stress evolution and spalling characteristics was studied. The results demonstrate that the initial spalling locations are sensitive to the relationship between the normalized tensile strength of the rock, shotcrete, and interface. A high incident amplitude can cause the initial spalling in rock, and the shotcrete or rock–shotcrete interface can cause initial spalling due to a low incident amplitude. The stress evolution and spalling characteristics are sensitive to the thickness of shotcrete. The location of the initial spalling failure changes with the thickness of the shotcrete. An appropriate increment in thickness and normalized strength of the shotcrete is beneficial to the dynamic stability of underground engineering.
Full article
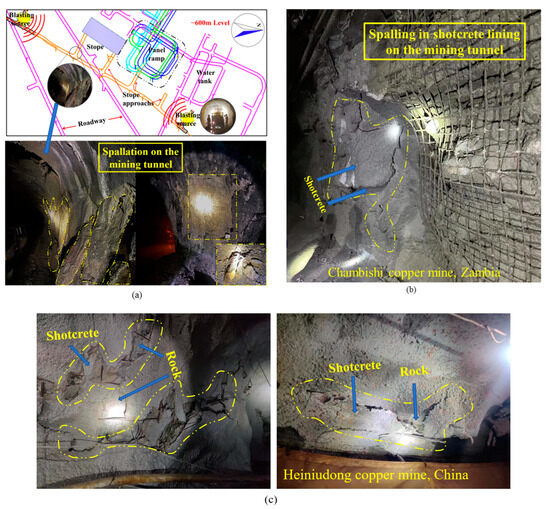
Figure 1
Open AccessArticle
Abnormal Monitoring Data Detection Based on Matrix Manipulation and the Cuckoo Search Algorithm
by
Zhenzhu Meng, Yiren Wang, Sen Zheng, Xiao Wang, Dan Liu, Jinxin Zhang and Yiting Shao
Mathematics 2024, 12(9), 1345; https://doi.org/10.3390/math12091345 - 29 Apr 2024
Abstract
Structural health monitoring is an effective method to evaluate the safety status of dams. Measurement error is an important factor which affects the accuracy of monitoring data modeling. Processing the abnormal monitoring data before data analysis is a necessary step to ensure the
[...] Read more.
Structural health monitoring is an effective method to evaluate the safety status of dams. Measurement error is an important factor which affects the accuracy of monitoring data modeling. Processing the abnormal monitoring data before data analysis is a necessary step to ensure the reliability of the analysis. In this paper, we proposed a method to process the abnormal dam displacement monitoring data on the basis of matrix manipulation and Cuckoo Search algorithm. We first generate a scatter plot of the monitoring data and exported the matrix of the image. The scatter plot of monitoring data includes isolate outliers, clusters of outliers, and clusters of normal points. The gray scales of isolated outliers are reduced using Gaussian blur. Then, the isolated outliers are eliminated using Ostu binarization. We then use the Cuckoo Search algorithm to distinguish the clusters of outliers and clusters of normal points to identify the process line. To evaluate the performance of the proposed data processing method, we also fitted the data processed by the proposed method and by the commonly used 3-
(This article belongs to the Special Issue Anomaly and Novelty Detection and Explainability)
►▼
Show Figures
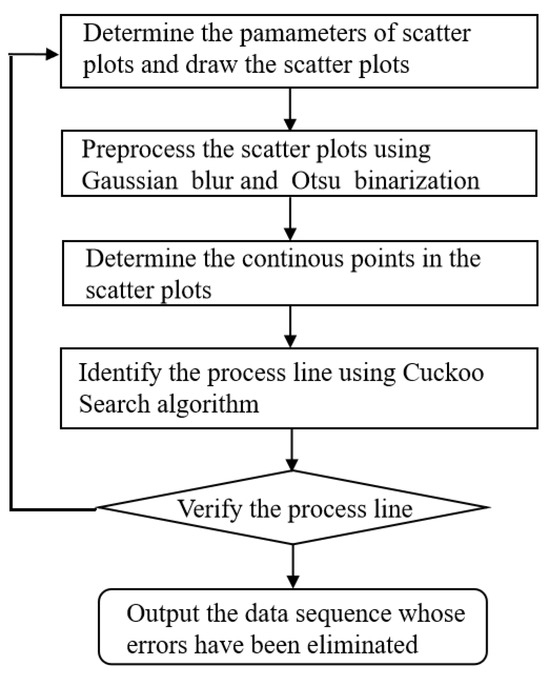
Figure 1
Open AccessArticle
On Intersections of B-Spline Curves
by
Ying-Ying Yu, Xin Li and Ye Ji
Mathematics 2024, 12(9), 1344; https://doi.org/10.3390/math12091344 - 28 Apr 2024
Abstract
Bézier and B-spline curves are foundational tools for curve representation in computer graphics and computer-aided geometric design, with their intersection computation presenting a fundamental challenge in geometric modeling. This study introduces an innovative algorithm that quickly and effectively resolves intersections between Bézier and
[...] Read more.
Bézier and B-spline curves are foundational tools for curve representation in computer graphics and computer-aided geometric design, with their intersection computation presenting a fundamental challenge in geometric modeling. This study introduces an innovative algorithm that quickly and effectively resolves intersections between Bézier and B-spline curves. The number of intersections between the two input curves within a specified region is initially determined by applying the resultant of a polynomial system and Sturm’s theorem. Subsequently, the potential region of the intersection is established through the utilization of the pseudo-curvature-based subdivision scheme and the bounding box detection technique. The projected Gauss-Newton method is ultimately employed to efficiently converge to the intersection. The robustness and efficiency of the proposed algorithm are demonstrated through numerical experiments, demonstrating a speedup of 3 to 150 times over traditional methods.
Full article
(This article belongs to the Section Computational and Applied Mathematics)
►▼
Show Figures
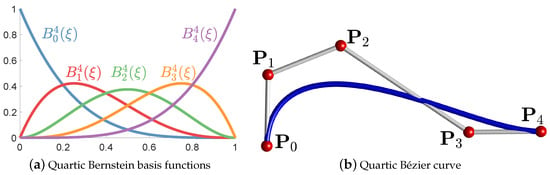
Figure 1
Open AccessArticle
Improving Oriented Object Detection by Scene Classification and Task-Aligned Focal Loss
by
Xiaoliang Qian, Shaoguan Gao, Wei Deng and Wei Wang
Mathematics 2024, 12(9), 1343; https://doi.org/10.3390/math12091343 - 28 Apr 2024
Abstract
Oriented object detection (OOD) can precisely detect objects with arbitrary direction in remote sensing images (RSIs). Up to now, the two-stage OOD methods have attracted more attention because of their high detection accuracy. However, the two-stage methods only rely on the features of
[...] Read more.
Oriented object detection (OOD) can precisely detect objects with arbitrary direction in remote sensing images (RSIs). Up to now, the two-stage OOD methods have attracted more attention because of their high detection accuracy. However, the two-stage methods only rely on the features of each proposal for object recognition, which leads to the misclassification problem because of the intra-class diversity, inter-class similarity and clutter backgrounds in RSIs. To address the above problem, an OOD model combining scene classification is proposed. Considering the fact that each foreground object has a strong contextual relationship with the scene of the RSI, a scene classification branch is added to the baseline OOD model, and the scene classification result of input RSI is used to exclude the impossible categories. To focus on the hard instances and enhance the consistency between classification and regression, a task-aligned focal loss (TFL) which combines the classification difficulty with the regression loss is proposed, and TFL assigns lager weights to the hard instances and optimizes the classification and regression branches simultaneously. The ablation study proves the effectiveness of scene classification branch, TFL and their combination. The comparisons with 15 and 14 OOD methods on the DOTA and DIOR-R datasets validate the superiority of our method.
Full article
(This article belongs to the Special Issue Advances in Computer Vision and Machine Learning, 2nd Edition)
►▼
Show Figures
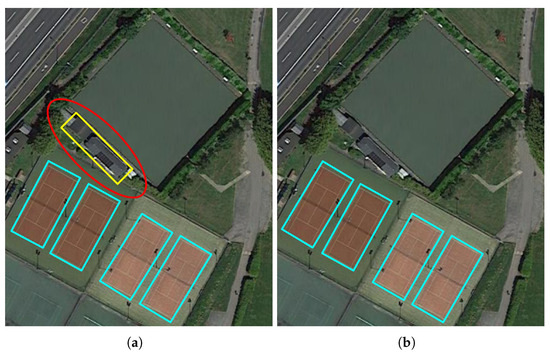
Figure 1
Open AccessArticle
New Results on the Ulam–Hyers–Mittag–Leffler Stability of Caputo Fractional-Order Delay Differential Equations
by
Osman Tunç
Mathematics 2024, 12(9), 1342; https://doi.org/10.3390/math12091342 - 28 Apr 2024
Abstract
The author considers a nonlinear Caputo fractional-order delay differential equation (CFrDDE) with multiple variable delays. First, we study the existence and uniqueness of the solutions of the CFrDDE with multiple variable delays. Second, we obtain two new results on the Ulam–Hyers–Mittag–Leffler (UHML) stability
[...] Read more.
The author considers a nonlinear Caputo fractional-order delay differential equation (CFrDDE) with multiple variable delays. First, we study the existence and uniqueness of the solutions of the CFrDDE with multiple variable delays. Second, we obtain two new results on the Ulam–Hyers–Mittag–Leffler (UHML) stability of the same equation in a closed interval using the Picard operator, Chebyshev norm, Bielecki norm and the Banach contraction principle. Finally, we present three examples to show the applications of our results. Although there is an extensive literature on the Lyapunov, Ulam and Mittag–Leffler stability of fractional differential equations (FrDEs) with and without delays, to the best of our knowledge, there are very few works on the UHML stability of FrDEs containing a delay. Thereby, considering a CFrDDE containing multiple variable delays and obtaining new results on the existence and uniqueness of the solutions and UHML stability of this kind of CFrDDE are the important aims of this work.
Full article
(This article belongs to the Special Issue Qualitative Analysis of Differential Equations: Theory and Applications)
Open AccessArticle
Shortage Policies for a Jump Process with Positive and Negative Batch Arrivals in a Random Environment
by
Yonit Barron
Mathematics 2024, 12(9), 1341; https://doi.org/10.3390/math12091341 - 28 Apr 2024
Abstract
We study a continuous-review stock management of a retailer for a single item in a limited storage (buffer) in a random environment. The stock level fluctuates according to two independent compound Poisson processes with discrete amounts of items (batches) that enter and leave
[...] Read more.
We study a continuous-review stock management of a retailer for a single item in a limited storage (buffer) in a random environment. The stock level fluctuates according to two independent compound Poisson processes with discrete amounts of items (batches) that enter and leave the storage facility. The storage facility is controlled by a three-parameter base-stock replenishment policy. All items exceeding the storage capacity are transferred to an unlimited foreign facility. In addition, a restricted backlogging possibility is permitted; additional demands for items are lost sales. We further assume a random shelf life, the possibility of total inventory collapse, and a random lead time. Applying Markov theory, we derive the optimal control parameters minimizing the long-run expected total cost. A sensitivity analysis is conducted focusing on the comparison between the pure lost-sales policy and a partial backordering policy. Accordingly, we identify cases where one policy is cost effective compared to the other, particularly with respect to the batch patterns (sign, rate, average, and variability), and the associated costs.
Full article
(This article belongs to the Special Issue Theoretical and Applied Mathematics in Supply Chain Management)

Journal Menu
► ▼ Journal Menu-
- Mathematics Home
- Aims & Scope
- Editorial Board
- Reviewer Board
- Topical Advisory Panel
- Instructions for Authors
- Special Issues
- Topics
- Sections & Collections
- Article Processing Charge
- Indexing & Archiving
- Editor’s Choice Articles
- Most Cited & Viewed
- Journal Statistics
- Journal History
- Journal Awards
- Society Collaborations
- Conferences
- Editorial Office
Journal Browser
► ▼ Journal BrowserHighly Accessed Articles
Latest Books
E-Mail Alert
News
Topics
Topic in
Axioms, Computation, MCA, Mathematics, Symmetry
Mathematical Modeling
Topic Editors: Babak Shiri, Zahra AlijaniDeadline: 31 May 2024
Topic in
Algorithms, Axioms, Fractal Fract, Mathematics, Symmetry
Fractal and Design of Multipoint Iterative Methods for Nonlinear Problems
Topic Editors: Xiaofeng Wang, Fazlollah SoleymaniDeadline: 30 June 2024
Topic in
Algorithms, Computation, Information, Mathematics
Complex Networks and Social Networks
Topic Editors: Jie Meng, Xiaowei Huang, Minghui Qian, Zhixuan XuDeadline: 31 July 2024
Topic in
Algorithms, Future Internet, Information, Mathematics, Symmetry
Research on Data Mining of Electronic Health Records Using Deep Learning Methods
Topic Editors: Dawei Yang, Yu Zhu, Hongyi XinDeadline: 31 August 2024

Conferences
Special Issues
Special Issue in
Mathematics
Advances in the Mathematics of Ecological Modelling
Guest Editors: Dmitrii O. Logofet, Larisa Khanina, Pavel GrabarnikDeadline: 30 April 2024
Special Issue in
Mathematics
Advances in Linear Recurrence System
Guest Editors: Lorentz Jäntschi, Virginia NiculescuDeadline: 15 May 2024
Special Issue in
Mathematics
New Trends on Boundary Value Problems
Guest Editors: Miklós Rontó, András Rontó, Nino Partsvania, Bedřich Půža, Hriczó KrisztiánDeadline: 31 May 2024
Special Issue in
Mathematics
Applications of Fuzzy Modeling in Risk Management
Guest Editors: Edit Toth-Laufer, László PokorádiDeadline: 20 June 2024
Topical Collections
Topical Collection in
Mathematics
Topology and Foundations
Collection Editors: Lorentz Jäntschi, Dušanka Janežič
Topical Collection in
Mathematics
Multiscale Computation and Machine Learning
Collection Editors: Yalchin Efendiev, Eric Chung
Topical Collection in
Mathematics
Theoretical and Mathematical Ecology
Collection Editor: Yuri V. Tyutyunov