A Double-Layer Blockchain Based Trust Management Model for Secure Internet of Vehicles
Abstract
1. Introduction
- 1.
- We propose a double-layer blockchain trust management system for the Internet of Vehicles, including vehicle and RSU blockchain. Our DLBTM can selectively store messages according to their importance and provide accurate message services for vehicles;
- 2.
- We propose a trust evaluation method for vehicle nodes, including the message trust value of vehicles, the evaluation trust value of vehicles, and the historical trust value of vehicles. Then use logistic regression to update the above three trust values;
- 3.
- We use simulation experiments to prove the safety and effectiveness of DLBTM, and show that DLBTM can effectively distinguish malicious nodes from normal nodes.
2. Related Work: A Critical Literature Review
2.1. Centralized Trust Management
2.2. Distributed Trust Management
2.3. Combination of Blockchain and Trust Management
2.4. Combination of Double-Layer Blockchain and Trust Management
3. Trust Management Mechanism of Double-Layer Blockchain: System Model, Design and Implementation
3.1. System Model
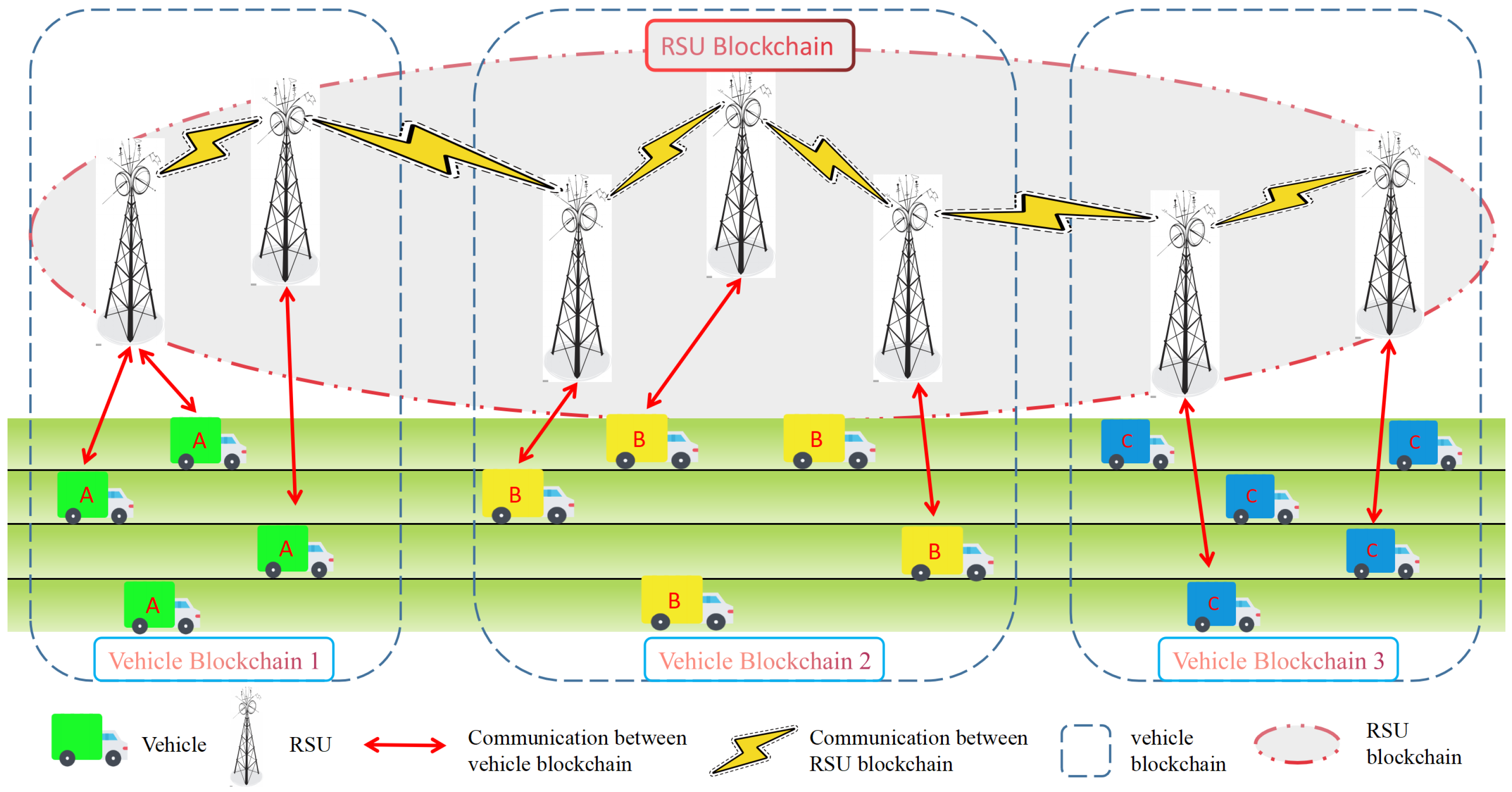
3.1.1. Double Layer Blockchain
- It can reduce the memory cost for RSUs. If the RSU blockchain stores these unimportant messages, it will cause a waste of storage resources;
- It can provide fast message sharing and speed up consensus process building. By storing these messages with no value to other regions, but value to the local region on the vehicle blockchain can help other vehicles in the same region receive the message faster, and help them reach a consensus more quickly.
3.1.2. Participants in the System Model
- RSUs: The RSUs are responsible for block generation, vehicle final trust calculation, offering messages to vehicles that send a request, storing summaries of important messages, and storing unimportant messages for a period of time;
- Vehicles: Responsible for message generation, message evaluation, and message requests.
3.2. System Design and Implementation
3.2.1. System Initialization
- RSU Registration: selects an elliptic curve , and randomly selects a point as the base point . selects a large number as the private key and generates the public key . sends public key to Certificate Authority (CA) for registration, and CA issues a certificate to .
- Vehicle Registration: selects an elliptic curve , and randomly selects a point as the base point . selects a large number as the private key and generates the public key . sends public key and private key to CA for registration, and CA issues certificate to .
3.2.2. Message Classification
| Algorithm 1 Message Classification on Type |
|
3.2.3. Selecting Message Evaluator
| Algorithm 2 Message Evaluator Selection |
|
3.2.4. Message Trust Value of Vehicle
3.2.5. Evaluation Trust Value of Vehicles
3.2.6. Vehicle Final Trust Value Update
3.3. Consensus Mechanism
3.3.1. Consensus Mechanism of Vehicle Blockchain
3.3.2. Consensus Mechanism of RSU Blockchain
- 1.
- The nodes of the vehicle blockchain participating in consensus are pre-selected RSUs, and the transactions of the vehicle blockchain are relatively less important data. Even if attackers know the leaders in advance, bribery attacks and DDOS attacks on them will have little impact on the stability of the DLBTM system;
- 2.
- The RSU blockchain stores important information and trust value shared by vehicles, so the identity information of the leader needs to be hidden. The nodes involved in mining in the RSU blockchain run verifiable random functions (VRFS) locally and only know who is the leader when other nodes receive the block, thus, reducing the impact of an attack on the DLBTM system.
3.4. Security Analysis
- 1.
- Resist malicious RSUs: Based on the Ouroboros protocol cluster, our DLBTM model can effectively defend against malicious RSUs. RSUs are important nodes in both the vehicle blockchain and the RSU blockchain. If normal RSUs are hacked and become malicious RSUs, they cannot construct a false block. This is because the consensus protocol used by the vehicle blockchain and RSU blockchain is the Ouroboros protocol cluster, and malicious RSUs as the leader can only create a blank block, since the transactions in the block are verified by multiple endorsement nodes and then sent to the leader. At the same time, according to the Ouroboros protocol cluster, the probability of becoming the leader is proportional to the proportion of the node’s stake, and even the RSU with a relatively high proportion of the intrusion stake cannot forge the block. If an attacker controls multiple RSUs to become malicious nodes, the Ouroboros protocol cannot issue fake blocks as long as the malicious RSUs do not hold more than of the blockchain;
- 2.
- Defense against false message attacks: Our DLBTM model can effectively defend against false message attacks. In false message attacks, an attacker may invade vehicle nodes, turning normal vehicle nodes into malicious ones. The malicious vehicle node then sends a false message to the RSU in an attempt to influence other nodes in the system. However, in DLBTM, other vehicle nodes will calculate the trust of false information, and, therefore, grant the malicious node a very low message trust value, so that when RSU updates the final trust value of the malicious node, the malicious node will receive a very low final trust value. Therefore, when other vehicle nodes request service later, RSU will choose the message provided by the vehicle node with a higher trust value. Therefore, false information published by malicious nodes will not be selected by RSUs, so the malicious nodes cannot affect other nodes in the system. In the end, malicious nodes that continue to publish false information will be excluded from the system;
- 3.
- Defence against false score attacks: Our DLBTM model system can effectively defend against false score attacks. In IoV, malicious nodes may be selected by RSUs as message evaluators according to their similarity, generating false scores for messages of normal vehicle nodes, thus, affecting the whole system. However, in our DLBTM, RSU selects multiple message evaluators when scoring the message. According to Equation (3), RSU will record the difference between the message score evaluated by the malicious node and the mean value, and identify the possible malicious nodes, reducing their final trust value. In this way, malicious nodes will be excluded from our system, and fail to undermine the system. Furthermore, the number of malicious nodes is often limited. Therefore, those malicious nodes are usually unable to evaluate the same message because RSUs select vehicles as message evaluators based on similarity. Therefore, our DLBTM can reduce the possibility of collusion attacks;
- 4.
- Data integrity: Our DLBTM model system can effectively prevent important data such as trust values and important message summaries of vehicles from being tampered with by malicious nodes to ensure data integrity. In DLBTM, both unimportant messages recorded in the vehicle blockchain and important message summaries and trust values recorded in the RSU blockchain are created by the leader and then completed by endorsement nodes that add legitimate transactions to the block, which become a consensus of all RSUs. The sequence and content of the blocks are protected using hash chains. The hash value of each block is unique. Once any content of any block is modified, the hash of the other blocks will be changed [26]. Therefore, a malicious RSU node that intends to tamper with the data and modify a vehicle’s trust value will have to modify the data in the current block and recalculate the previous block’s hash value on the chain, which is impossible in practice. Therefore, our DLBTM can effectively protect data integrity.
4. Experiment and Analysis
4.1. Time Complexity and Space Complexity Analysis
4.2. Simulation Results and Performance Evaluation
5. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Vaezi, M.; Azari, A.; Khosravirad, S.R.; Shirvanimoghaddam, M.; Azari, M.M.; Chasaki, D.; Popovski, P. Cellular, wide-area, and non-terrestrial IoT: A survey on 5G advances and the road toward 6G. IEEE Commun. Surv. Tutor. 2022, 24, 1117–1174. [Google Scholar] [CrossRef]
- Noor-A-Rahim, M.; Liu, Z.; Lee, H.; Khyam, M.O.; He, J.; Pesch, D.; Moessner, K.; Saad, W.; Poor, H.V. 6G for vehicle-to-everything (V2X) communications: Enabling technologies, challenges, and opportunities. Proc. IEEE 2022, 110, 712–734. [Google Scholar] [CrossRef]
- Mohanty, S.K.; Tripathy, S. SIoVChain: Time-Lock Contract Based Privacy-Preserving Data Sharing in SIoV. IEEE Trans. Intell. Transp. Syst. 2022, 23, 24071–24082. [Google Scholar] [CrossRef]
- Ahmad, F.; Kurugollu, F.; Kerrache, C.A.; Sezer, S.; Liu, L. Notrino: A novel hybrid trust management scheme for internet-of-vehicles. IEEE Trans. Veh. Technol. 2021, 70, 9244–9257. [Google Scholar] [CrossRef]
- Tian, Z.; Gao, X.; Su, S.; Qiu, J. Vcash: A novel reputation framework for identifying denial of traffic service in internet of connected vehicles. IEEE Internet Things J. 2019, 7, 3901–3909. [Google Scholar] [CrossRef]
- Mahmood, A.; Sheng, Q.Z.; Siddiqui, S.A.; Sagar, S.; Zhang, W.E.; Suzuki, H.; Ni, W. When trust meets the internet of vehicles: Opportunities, challenges, and future prospects. In Proceedings of the 2021 IEEE 7th International Conference on Collaboration and Internet Computing (CIC), Atlanta, GA, USA, 13–15 December 2021; IEEE: Piscataway, NJ, USA, 2021; pp. 60–67. [Google Scholar] [CrossRef]
- Yang, Z.; Wang, R.; Wu, D.; Yang, B.; Zhang, P. Blockchain-enabled trust management model for the Internet of Vehicles. IEEE Internet Things J. 2021. Early Access. [Google Scholar] [CrossRef]
- Singh, P.K.; Singh, R.; Nandi, S.K.; Ghafoor, K.Z.; Rawat, D.B.; Nandi, S. Blockchain-based adaptive trust management in internet of vehicles using smart contract. IEEE Trans. Intell. Transp. Syst. 2020, 22, 3616–3630. [Google Scholar] [CrossRef]
- Misra, N.; Dixit, Y.; Al-Mallahi, A.; Bhullar, M.S.; Upadhyay, R.; Martynenko, A. IoT, big data, and artificial intelligence in agriculture and food industry. IEEE Internet Things J. 2020, 9, 6305–6324. [Google Scholar] [CrossRef]
- Mahmoud, M.E.; Shen, X. An integrated stimulation and punishment mechanism for thwarting packet dropping attack in multihop wireless networks. IEEE Trans. Veh. Technol. 2011, 60, 3947–3962. [Google Scholar] [CrossRef]
- Bißmeyer, N.; Njeukam, J.; Petit, J.; Bayarou, K.M. Central misbehavior evaluation for vanets based on mobility data plausibility. In Proceedings of the Ninth ACM International Workshop on Vehicular Inter-Networking, Systems, and Applications, Low Wood Bay Lake District, UK, 25 June 2012; pp. 73–82. [Google Scholar] [CrossRef]
- Li, Q.; Malip, A.; Martin, K.M.; Ng, S.L.; Zhang, J. A reputation-based announcement scheme for VANETs. IEEE Trans. Veh. Technol. 2012, 61, 4095–4108. [Google Scholar] [CrossRef]
- Huang, X.; Yu, R.; Kang, J.; Zhang, Y. Distributed reputation management for secure and efficient vehicular edge computing and networks. IEEE Access 2017, 5, 25408–25420. [Google Scholar] [CrossRef]
- Oluoch, J. A distributed reputation scheme for situation awareness in vehicular ad hoc networks (VANETs). In Proceedings of the 2016 IEEE International Multi-Disciplinary Conference on Cognitive Methods in Situation Awareness and Decision Support (CogSIMA), San Diego, CA, USA, 21–25 March 2016; IEEE: Piscataway, NJ, USA, 2016; pp. 63–67. [Google Scholar] [CrossRef]
- Raya, M.; Papadimitratos, P.; Gligor, V.D.; Hubaux, J.P. On data-centric trust establishment in ephemeral ad hoc networks. In Proceedings of the IEEE INFOCOM 2008-The 27th Conference on Computer Communications, Phoenix, AZ, USA, 13–18 April 2008; IEEE: Piscataway, NJ, USA, 2008; pp. 1238–1246. [Google Scholar] [CrossRef]
- Yang, Z.; Yang, K.; Lei, L.; Zheng, K.; Leung, V.C. Blockchain-based decentralized trust management in vehicular networks. IEEE Internet Things J. 2018, 6, 1495–1505. [Google Scholar] [CrossRef]
- Zhang, H.; Liu, J.; Zhao, H.; Wang, P.; Kato, N. Blockchain-based trust management for internet of vehicles. IEEE Trans. Emerg. Top. Comput. 2020, 9, 1397–1409. [Google Scholar] [CrossRef]
- Kang, J.; Yu, R.; Huang, X.; Wu, M.; Maharjan, S.; Xie, S.; Zhang, Y. Blockchain for secure and efficient data sharing in vehicular edge computing and networks. IEEE Internet Things J. 2018, 6, 4660–4670. [Google Scholar] [CrossRef]
- Lee, S.; Seo, S.H. Design of a two layered blockchain-based reputation system in vehicular networks. IEEE Trans. Veh. Technol. 2021, 71, 1209–1223. [Google Scholar] [CrossRef]
- Kandah, F.; Huber, B.; Skjellum, A.; Altarawneh, A. A blockchain-based trust management approach for connected autonomous vehicles in smart cities. In Proceedings of the 2019 IEEE 9th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, USA, 7–9 January 2019; IEEE: Piscataway, NJ, USA, 2019; pp. 544–549. [Google Scholar] [CrossRef]
- Mihalcea, R.; Tarau, P. Textrank: Bringing Order into Text. In Proceedings of the 2004 Conference on Empirical Methods in Natural Language Processing, Barcelona, Spain, 25–26 July 2004; pp. 404–411. Available online: https://aclanthology.org/W04-3252.pdf (accessed on 2 May 2023).
- Manku, G.S.; Jain, A.; Das Sarma, A. Detecting near-duplicates for web crawling. In Proceedings of the 16th International Conference on World Wide Web, Banff, AL, Canada, 8–12 May 2007; pp. 141–150. [Google Scholar] [CrossRef]
- Wang, Y.; Lu, Y.C.; Chen, I.R.; Cho, J.H.; Swami, A.; Lu, C.T. LogitTrust: A Logit Regression-Based Trust Model for Mobile ad hoc Networks. In Proceedings of the 6th ASE International Conference on Privacy, Security, Risk and Trust, Boston, MA, USA; 2014; pp. 1–10. Available online: https://people.cs.vt.edu/~clu/Publication/2014/PASSAT-14.pdf (accessed on 2 May 2023).
- Kiayias, A.; Russell, A.; David, B.; Oliynykov, R. Ouroboros: A provably secure proof-of-stake blockchain protocol. In Proceedings of the Advances in Cryptology–CRYPTO 2017: 37th Annual International Cryptology Conference, Santa Barbara, CA, USA, 20–24 August 2017; pp. 357–388. [Google Scholar] [CrossRef]
- David, B.; Gaži, P.; Kiayias, A.; Russell, A. Ouroboros praos: An adaptively-secure, semi-synchronous proof-of-stake blockchain. In Proceedings of the Advances in Cryptology–EUROCRYPT 2018: 37th Annual International Conference on the Theory and Applications of Cryptographic Techniques, Tel Aviv, Israel, 29 April–3 May 2018; pp. 66–98. [Google Scholar] [CrossRef]
- Al-Jaroodi, J.; Mohamed, N. Blockchain in industries: A survey. IEEE Access 2019, 7, 36500–36515. [Google Scholar] [CrossRef]
- Chen, X.; Ding, J.; Lu, Z. A decentralized trust management system for intelligent transportation environments. IEEE Trans. Intell. Transp. Syst. 2020, 23, 558–571. [Google Scholar] [CrossRef]
- Liu, X.; Huang, H.; Xiao, F.; Ma, Z. A blockchain-based trust management with conditional privacy-preserving announcement scheme for VANETs. IEEE Internet Things J. 2019, 7, 4101–4112. [Google Scholar] [CrossRef]
- Zhong, S.; Chen, J.; Yang, Y.R. Sprite: A simple, cheat-proof, credit-based system for mobile ad-hoc networks. In Proceedings of the IEEE INFOCOM 2003. Twenty-Second Annual Joint Conference of the IEEE Computer and Communications Societies (IEEE Cat. No. 03CH37428), San Francisco, CA, USA, 30 March–3 April 2003; IEEE: Piscataway, NJ, USA, 2003; Volume 3, pp. 1987–1997. [Google Scholar] [CrossRef]







| Summary | Description |
|---|---|
| The single blockchain and double-layer blockchain have different participating nodes | The participating nodes of a single blockchain are vehicles and RSUs, and the miners may be vehicles or RSUs, while the participating nodes of a vehicle blockchain in a double-layer blockchain are vehicles and RSUs; the RSU blockchain only has RSU participating nodes, and the miners are RSUs. |
| The difference in functionality between the single blockchain and double-layer blockchain | We separate the three tasks of data storage, message evaluation, and trust value calculation. The vehicles in the vehicle blockchain perform message evaluation, while the RSU of the RSU blockchain performs data storage and trust value calculation. The nodes in the single blockchain need to complete the above three tasks |
| The length of time the single blockchain and double blockchain store data is different | The nodes in the single blockchain need to store all historical data. The vehicle blockchain in the double-layer blockchain is a temporary blockchain (deleted every hour, that is, creating a new Genesis block and deleting previously recorded blockchain data). The RSU blockchain is a permanent blockchain that stores important message summaries and vehicle trust values. |
| Trust Management Mechanism | Shortcoming |
|---|---|
| Centralized Trust Management | All data are stored and processed on a central server, which is generally located in the cloud and far from the vehicle, and may not meet the latency requirements of the IoV. At the same time, there are also the single points of failure, concurrency problems (at the same time, a large number of vehicles access the central server), big data (storage and transmission of massive data), and other problems. |
| Distributed Trust Management | In distributed trust management mechanisms, the task of managing and storing data is usually completed by vehicles or RSUs. However, vehicles and RSUs are usually distributed outdoors, and security measures are not as strict as central servers. RSUs have the possibility of failure, and security and reliability are not fully guaranteed. |
| Combination of Blockchain and Trust Management | Vehicles can query the trust data of another vehicle anytime and anywhere, which can cause privacy breaches of the vehicle. The current research does not have a reasonable plan for the collection, storage, and management of trust data. Vehicles need to store a complete blockchain ledger, which will increase the storage burden on vehicle nodes. Due to the varying importance of data generated by vehicles, the system does not differentiate the importance of messages and instead stores and shares data. |
| Combination of Double-layer Blockchain and Trust Management | The system model in reference [19] calculates the credibility of messages by voting on other vehicles but does not constrain the behavior of voters, making it easy to launch attacks on them. Reference [20] does not provide a specific method for evaluating vehicle trust values. |
| Notation | Description |
|---|---|
| The i-th RSU in IoV | |
| The j-th vehicle in IoV | |
| Point generator of an additive cyclic group | |
| A private key of | |
| A public key of | |
| A private key of | |
| A public key of | |
| M | Messages sent by RSU or vehicles |
| List of each message sent by each vehicle | |
| A two-dimensional list of messages grouped by type | |
| Message summary list generated from | |
| The m-th message reported by to the nearby RSU | |
| A list containing many vehicles | |
| List of vehicles selected for evaluated messages |
| Parameters | Settings |
|---|---|
| Simulation map area | 2500 m × 1500 m |
| Number of RSUs | 13 |
| Number of vehicles | 100 or 50 |
| Vehicle speed | 60 km/h |
| Vehicle communication distance | 300 m |
| RSU communication distance | 600 m |
| Vehicle transmit power | 10 mW |
| RSU transmit power | 30 mW |
| Mac protocol | IEEE802.11p |
| Model | Time Complexity | Space Complexity |
|---|---|---|
| DTMS | ||
| DLBTM |
| Model | Time Complexity | Space Complexity |
|---|---|---|
| DTMS | ||
| DLBTM |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ruan, W.; Liu, J.; Chen, Y.; Islam, S.M.N.; Alam, M. A Double-Layer Blockchain Based Trust Management Model for Secure Internet of Vehicles. Sensors 2023, 23, 4699. https://doi.org/10.3390/s23104699
Ruan W, Liu J, Chen Y, Islam SMN, Alam M. A Double-Layer Blockchain Based Trust Management Model for Secure Internet of Vehicles. Sensors. 2023; 23(10):4699. https://doi.org/10.3390/s23104699
Chicago/Turabian StyleRuan, Wenbo, Jia Liu, Yuanfang Chen, Sardar M. N. Islam, and Muhammad Alam. 2023. "A Double-Layer Blockchain Based Trust Management Model for Secure Internet of Vehicles" Sensors 23, no. 10: 4699. https://doi.org/10.3390/s23104699
APA StyleRuan, W., Liu, J., Chen, Y., Islam, S. M. N., & Alam, M. (2023). A Double-Layer Blockchain Based Trust Management Model for Secure Internet of Vehicles. Sensors, 23(10), 4699. https://doi.org/10.3390/s23104699





.png)

