Abstract
The literature on probabilistic hazard and risk assessment shows a rich and wide variety of modeling strategies tailored to specific perils. On one hand, catastrophe (CAT) modeling, a recent professional and scientific discipline, provides a general structure for the quantification of natural (e.g., geological, hydrological, meteorological) and man-made (e.g., terrorist, cyber) catastrophes. On the other hand, peril characteristics and related processes have yet to be categorized and harmonized to enable adequate comparison, limit silo effects, and simplify the implementation of emerging risks. We reviewed the literature for more than 20 perils from the natural, technological, and socio-economic systems to categorize them by following the CAT modeling hazard pipeline: (1) event source → (2) size distribution → (3) intensity footprint. We defined the following categorizations, which are applicable to any type of peril, specifically: (1) point/line/area/track/diffuse source, (2) discrete event/continuous flow, and (3) spatial diffusion (static)/threshold (passive)/sustained propagation (dynamic). We then harmonized the various hazard processes using energy as the common metric, noting that the hazard pipeline’s underlying physical process consists of some energy being transferred from an energy stock (the source), via an event, to the environment (the footprint).
1. Introduction
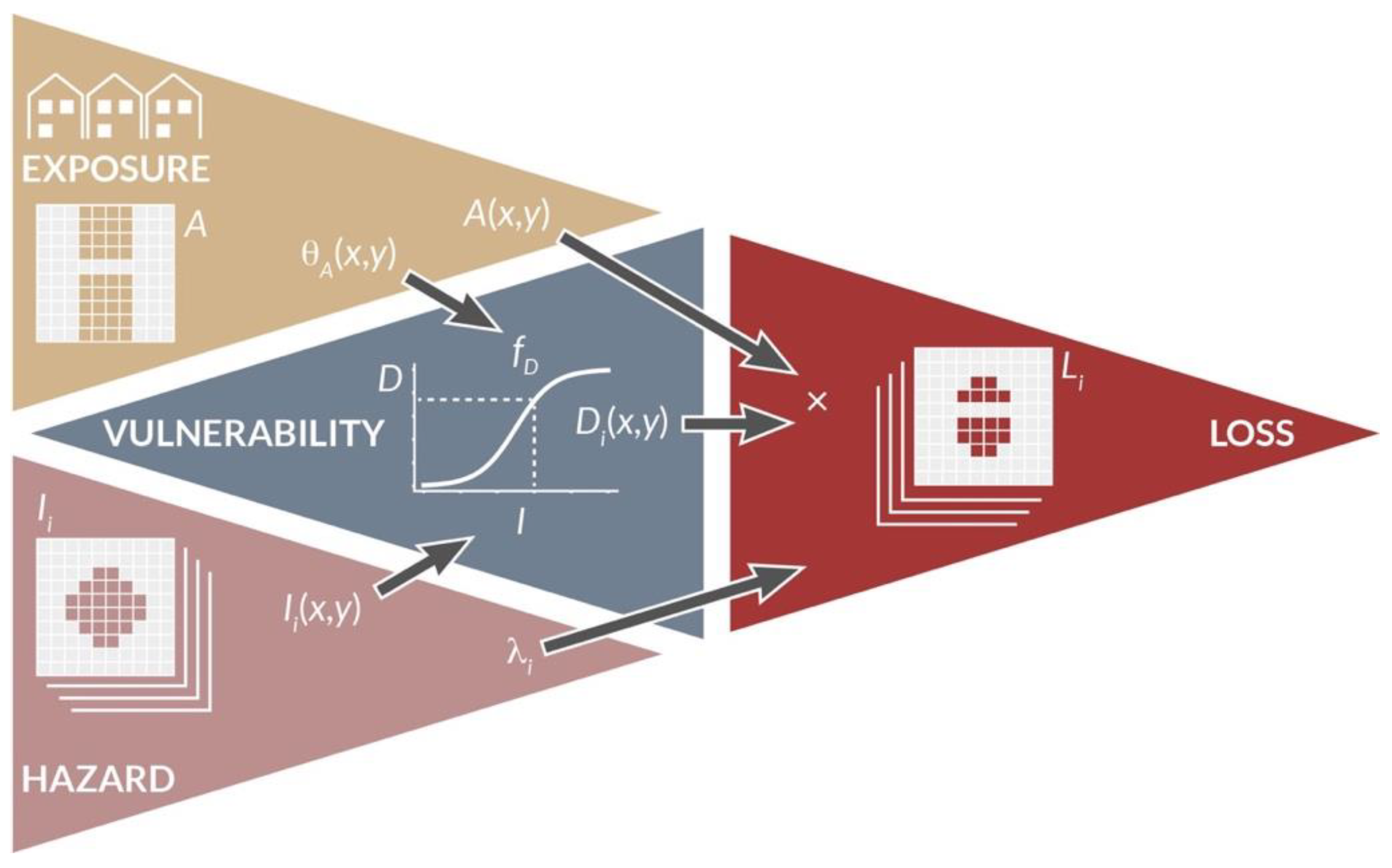
Catastrophe (CAT) modeling has developed in the past 40 years from pilot applications [1] to the standard that it is today, used by insurers and reinsurers, public agencies, and corporations [2,3,4]. The process is a computational pipeline (Figure 1) where a mapping is performed between hazard intensity and loss via a vulnerability function . It is defined as
where is the exposed asset value, the asset exposure characteristics, and the damage level, such as the mean damage ratio (MDR). Equation (1) represents the Risk Triangle with depending on the following three elements: exposure , vulnerability , and hazard [5]. For a given event , losses are aggregated for all the geographical locations of coordinates impacted by the event, with the total event loss. This mapping is repeated for each event for a specific region and peril, typically an earthquake, a storm, or a flood. Considering a set of stochastic events yields the event loss table (ELT) that lists the event identifier , its rate , and its loss . Risk metrics can then be computed from the ELT using various actuarial methods for portfolio analysis, including the average annual loss (AAL) and exceedance probability (EP) curves [2,4]. At each step of the process, uncertainties can be implemented via various statistical distributions. Site effects and other correcting factors can also be added at any location . The Monte Carlo method can also be used to simulate a year loss table (YLT) which provides more flexibility in the treatment of uncertainties, the aggregation of losses, and the inclusion of processes beyond the homogeneous Poisson process (e.g., clustering [6], seasonality [7], cascading effects and other loss amplifying factors [8]). For the interested reader, more details can be found in [4].
Figure 1.
The CAT modeling framework. The binary grids represent the different spatial footprints for the exposed assets and for the stochastic events . See text for details and notation.
The probabilistic risk assessment part is standardizable across different perils since a common damage metric can consistently be used (e.g., the MDR). Moreover, vulnerability functions could, in theory, be developed following similar engineering methods independently of the hazard stressor type [9]. It is only the probabilistic hazard assessment component that remains peril-specific and requires expert knowledge—for example in seismology, meteorology, or hydrology. Hence, the only heterogeneous, silo-type, parts of the CAT modeling pipeline are all the steps leading to the assessment of the hazard intensity footprint and of its rate . While the most common perils in CAT models [10,11,12] remain earthquakes [13,14], tropical and extratropical cyclones [15,16], and floods [17,18], others have been progressively added, such as convective storms with hail and tornados [19,20], cyber-attacks [21,22], epidemics [23,24], terrorist attacks [25,26], and wildfires [27]. Secondary perils, also included in some CAT models, include fire-following earthquakes [28], storm surges [29], and business interruption [30]. Other perils, primary or secondary, also recently considered in the CAT modeling framework include landslides, tsunamis, and volcanic eruptions [4,12]. Others have yet to be fully integrated in the CAT modeling paradigm, such as heatwaves [31], crop failures [32], and asteroid impacts [33,34]. Social unrest and war, to only cite a few additional perils, have yet to be implemented to the best of the author’s knowledge, although computational methods are already available [35,36]. A peril is often not implemented if not yet demonstrated to be insurable, which is most commonly due to a lack of data or models to assess risk and set premiums [26]. It has also been argued that some man-made risks are not calculable [37] or simply too costly to insure.
For each peril considered, a different set of terms, concepts, and models is employed. This hampers comparisons and makes the implementation of any new peril in the CAT modeling framework a challenge. To improve comparability and find equivalences in physically different hazard processes, this article reviews the different steps involved in probabilistic hazard assessment for more than 20 perils and categorizes them in terms of event source (Section 2.2), event size distribution (Section 2.3), and hazard intensity footprint (Section 2.4). Finally, the hazard process is harmonized in terms of energy transfer since it is applicable to any peril (Section 3). This review serves several purposes. Pedagogical and encyclopedic in nature, it first illustrates the richness of the space of potential hazards faced by society. Second, by treating and quantifying all perils and their hazards in a common way, it provides the basic knowledge needed to develop CAT modeling as an independent scientific discipline. Finally, this review can be viewed as a preliminary step to developing multi-risk models that would consider all the interconnections between the natural, technological, and socio-economic systems, within the context of CAT accumulation risk.
2. Review of Hazard Modeling Parameterization per Peril
We reviewed the literature on CAT modeling, as well as other works which can provide inputs to CAT models. We attempted to cover as many perils as possible for the three hazard steps (Section 2.2, Section 2.3 and Section 2.4). Note that we distinguish peril, a potential cause of damage, from hazard, the danger arising from a peril [4]. In other words, a peril can be an earthquake, a storm, or an industrial explosion, while their matching hazards (in terms of intensity) are ground shaking, strong wind, and blast overpressure, respectively. The term event then represents one instance from a given peril (one earthquake, one storm, etc.). To make this review tractable, we only consider first-order processes and mention seminal studies and reviews for the reader to explore each peril in more detail. For each step of the probabilistic hazard assessment procedure, peril characteristics are listed in alphabetical order. Some perils can display different hazardous phenomena, in which case each phenomenon is associated to a sub-peril. Not all perils are described systematically in Section 2.2, Section 2.3 and Section 2.4. Note that the proposed categorization is aimed at facilitating peril comparison, not at forcing them into strict boxes. For convenience, Table A1 of Appendix A provides a list of the variables and parameters mentioned in this review.
2.1. Data
To illustrate some of the possible models (mainly for source-type description and size distribution parameterization—see Section 2.2 and Section 2.3), the following databases were used:
- Asteroid impacts (fireballs): The Fireballs Reported by US Government Sensors [38] dataset for the period 15 April 1988–21 August 2022, available online: https://cneos.jpl.nasa.gov/fireballs/ (accessed on 31 August 2022).
- Blackouts: Dataset of numbers of customers affected in electrical blackouts in the United States between 1984 and 2002 [39], available online: https://aaronclauset.github.io/powerlaws/data/blackouts.txt (accessed on 31 August 2022).
- Cyber-attacks: The 2005–2018 Privacy Rights Clearinghouse (PRC) catalogue [40] for category hacking/malware, available online: https://privacyrights.org/data-breaches (accessed on 31 August 2022).
- Earthquakes: The 1900–2012 International Seismological Centre-Global Earthquake Model (ISC-GEM) Global Instrumental Earthquake Catalogue [41], available online: http://www.isc.ac.uk/iscgem/ (accessed on 31 August 2022); the fault source model of the 2013 European Seismic Hazard Model (ESHM13) [42], available online: http://hazard.efehr.org/en/Documentation/specific-hazard-models/europe/overview/active-faults/ (accessed on 31 August 2022).
- Epidemics: The Global Epidemics Dataset [43], available online: https://zenodo.org/record/4626111 (accessed on 31 August 2022).
- Heatwaves: Temperature data for July 2022 in France from the Météo-France data portal [44], available online: https://donneespubliques.meteofrance.fr/donnees_libres/Txt/Synop/Archive/synop.202207.csv.gz (accessed on 31 August 2022).
- Landslides: Inventory of events triggered by the 2008 Wenchuan, China, earthquake, courtesy of Dr. G. Li and Prof. J. West [45].
- River flooding: Dataset of flood peaks at the Potomac River between 1895 and 1986, provided in Table 1 of [46], a textbook example.
- Terrorism: Dataset of the severity of terrorist attacks worldwide from 1968 to 2006, measured as the number of directly resulting deaths [39,47], available online: https://aaronclauset.github.io/powerlaws/data/terrorism.txt (accessed on 31 August 2022).
- Tropical (and extra-tropical) cyclones: The International Best Track Archive for Climate Stewardship (IBTrACS) [48], available online: https://www.ncei.noaa.gov/products/international-best-track-archive?name=ibtracs-data (accessed on 31 August 2022).
- Tsunamis: The NCEI/WDS Global Historical Tsunami Database [49], here for the selected period 1900–2022, available online: https://www.ngdc.noaa.gov/hazard/tsu_db.shtml (accessed on 31 August 2022).
- Volcanic eruptions: The global database on large magnitude explosive volcanic eruptions (LaMEVE) [50], available online: https://www2.bgs.ac.uk/vogripa/view/controller.cfc?method=lameve (accessed on 31 August 2022).
- Wildfires: The FRY global database of fire patches [51], available online: https://data.oreme.org/doi/view/0e999ffc-e220-41ac-ac85-76e92ecd0320#FRY (accessed on 31 August 2022).
While most datasets are global, the others go from regional to local. Different time periods are also represented. These spatiotemporal heterogeneities have, however, no significant impact on the present review since the data are mainly used for illustration purposes with no quantitative comparison being provided. Moreover, most datasets are annualized. A color scheme has been developed to distinguish between different peril categories in the next figures. The scheme is given in Table A2 of Appendix A.
2.2. Event Source and Event Size
The size of an event is constrained by the source from which it originates. A source is here defined as the energy stock that drives the event. Each source represents a unique object with peril-specific characteristics. For instance, a tropical cyclone manifests itself from an atmospheric low-pressure system that moves along a track, while an earthquake corresponds to the rupture of a fault plane under tectonic loading—two very different objects. We define five categories of sources: point sources (Section 2.2.1), line sources (Section 2.2.2), area sources (Section 2.2.3), track sources (Section 2.2.4), and diffuse sources (Section 2.2.5). For each peril, we use the most common size metrics and, of those, preferentially the one most closely related to energy (see Section 3). We only list one model per peril to estimate the event size as a function of the source parameters, based on first principles and other simple empirical relationships. References to more sophisticated models are given for completeness.
2.2.1. Point Source
The point source of coordinates is the simplest source type. The event size depends on the energy stock implicitly encoded in that point.
- Asteroid (or comet) impacts: The source is the impact site, which is random and uniform in space (Figure 2). The stored energy is defined by the characteristics of the impactor and the event size is directly expressed in terms of kinetic energy [J],with [kg] the mass of the body and [m/s] its velocity. The typical characteristics of the impactor are a density of 3 g/cm3 (stony asteroid), 8 g/cm3 (iron asteroid), or 0.5 g/cm3 (comet) and a velocity of 20 km/s (asteroid) or 50 km/s (comet) [52]. Equation (2) is an oversimplification of the process and does not consider atmospheric deceleration, disruption, or ablation processes, nor ground penetration [34,52,53].
- Explosions (accidental): The source is a container of explosive material. Sources of severe accidental explosions are located at industrial sites, so-called Seveso sites. The size of the event is defined by the blast energy [kJ], which is a function of the mass and chemical characteristics of the explosive substance. It is usually described in TNT mass equivalent [kg]. For a vapor cloud explosion (VCE), or fuel-air explosion, we havewhere is the explosion efficiency, or fraction of available combustion energy participating in blast wave generation, [kJ/kg] is the heat of combustion of the material, and [kg] is the mass of flammable vapor release, itself a percentage of the total mass of hazardous material. 4200 kJ/kg is the heat of combustion of TNT. For an explosion at a fuel storage site or refinery, 46.4 MJ/kg and [54,55] can be used as an example. Another type of explosion is the boiling liquid-expanding vapor explosion (BLEVE), resulting from the sudden vaporization of a liquid [56]. Related perils include fire and toxic material release [57,58].
- Explosions (armed conflicts, terrorism): The source is a bomb, whose size is known by design. For conventional blasts, Equation (3) can be used with high explosives considered as source material (e.g., TNT). For non-conventional blasts, such as a nuclear explosion, a simple equation of the yield iswhere is the total mass of the spherical bomb (core + tamper), is the difference between the expanded radius and the initial radius of the sphere, is the time required for a neutron born in a fission to subsequently strike and fission another nucleus, and is the number of neutrons liberated per fission ( for Uranium 235 and for Plutonium 239) [59]. In contrast to accidental explosions, sources of intended explosions are mobile and correlate with population density and specific (critical) infrastructure targets [26]. It can be considered a sub-peril of armed conflicts and terrorist attacks, which have a diffuse source (see Section 2.2.5). A related peril is radiation in the case of a nuclear attack.
- River floods: The source is a river system associated to a catchment basin. It can, however, be represented by (or concentrated at) a point source characterized by the peak discharge [m3/s] at a point of the river. For a small basin (1 km2), it is estimated with the Rational Formulawith the runoff coefficient (which depends on soil conditions and surface characteristics, such as asphalt versus grass), [m] the critical rainfall, the concentration time [s] (function of flow distance and terrain slope), and the catchment area [m2] [60,61]. If is defined as the duration of the rainfall event, then represents the rainfall intensity with the role of slope included in . For greater basins, non-linearities must be included, such as the topography and the non-stationary flow observed on hydrographs [60]. An empirical relationship approximating the process can otherwise be used withwhere is the expected annual peak discharge [m3/s], [km2] the catchment area, the annual average rainfall in the catchment [mm], the upstream catchment slope [m/km], and to empirical parameters [62].
- Volcanic eruptions: An active volcano transfers heat and matter from the Earth’s interior to outside the volcanic edifice. Most eruptions occur along the Ring of Fire (Figure 2). The event size is the volume of matter ejected [km3], which is also the main parameter of the Volcanic Explosivity Index (VEI) [63]. Other characteristics of the magma, such as temperature , allow the thermal energy released during the eruption to be estimated [64] (see Section 3).
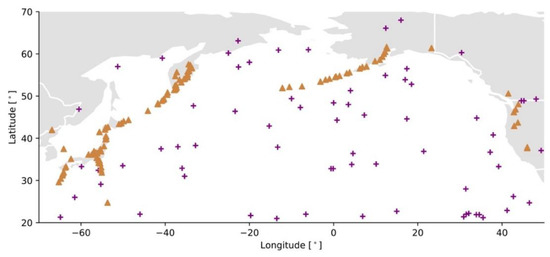
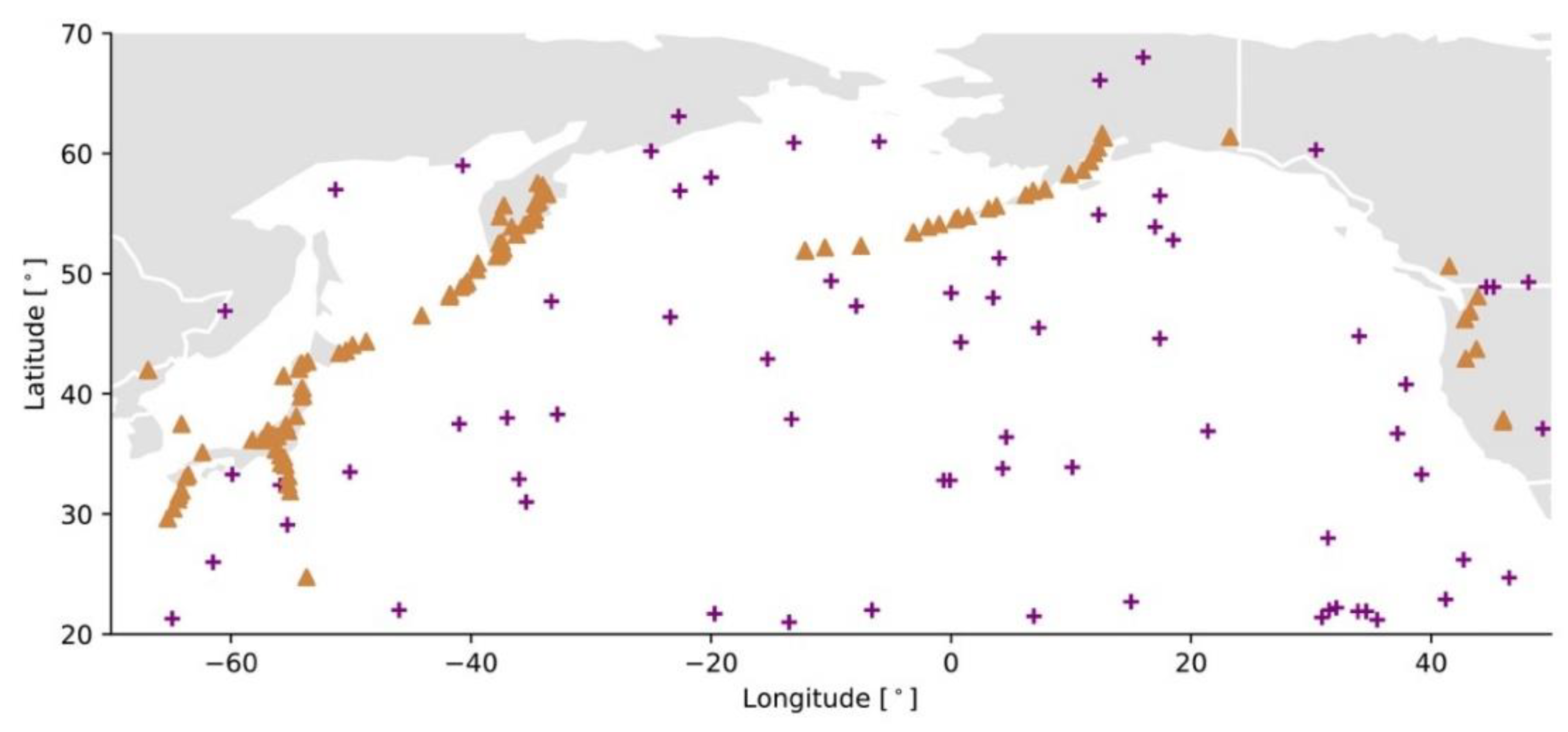
Figure 2.
Examples of point sources (asteroid impact and volcanic eruption cases) in the North Pacific region. Fireball locations (plus signs) in the dataset of Fireballs Reported by US Government Sensors [38]. Active volcanoes (triangles) represented by the eruptions that occurred in the past 10,000 years in the LaMEVE database [50].
Figure 2.
Examples of point sources (asteroid impact and volcanic eruption cases) in the North Pacific region. Fireball locations (plus signs) in the dataset of Fireballs Reported by US Government Sensors [38]. Active volcanoes (triangles) represented by the eruptions that occurred in the past 10,000 years in the LaMEVE database [50].
2.2.2. Line Source
The line source is composed of segments with coordinates . For a “line source” with a time stamp, see Section 2.2.4 on track sources. Various source characteristics can be associated to each point or segment.
- Earthquakes: The source is a fault, i.e., a planar rock fracture which shows evidence of relative movement. There is often no need to explicitly define an area source as the line carries dip and width information (Figure 3a). The seismic energy released by an earthquake is proportional to the seismic moment [N·m], with Pa the rock shear modulus, [m2] the rupture surface area, and [m] the average displacement on the fault. The earthquake’s size is, however, commonly described in terms of moment magnitude [65]Usually, empirical relationships linking magnitude and fault geometry are used instead of the other physical characteristics of the rupture, such aswith the surface rupture length and and fitting parameters as a function of the fault mechanism (normal, reverse, or strike-slip) [66] (Figure 3b).
- Storm surges: The source is a storm, and more precisely the low-pressure region above the water mass combined with strong winds. It may be considered a line source since the event size is defined in terms of the water height along the coastline [29]. The storm surge can be related to storm maximum windspeed , for example with a polynomial function of the formwhere the empirical parameters , , and are site-specific [67]. Although the match between hurricane windspeed and storm surge height ranges is given on the Saffir–Simpson Hurricane Wind Scale, the indicator is often not sufficient for estimating the actual storm surge [68].
- Tornados: The simplified source of a tornado track is a line with no intensity variability along its length [20] (otherwise it is modelled as a track source—Section 2.2.4). The event size is defined in terms of maximum wind speed , which is the main parameter of the Enhanced Fujita Scale [69]. Additional parameters of the source, such as location, length, and width (or maximum radius), are sampled from historical data [70].
- Tsunamis (triggered by an earthquake): In this case, the source is an underwater fault line. The size of the event is commonly defined by both wave velocity and wave height at arrival on the coast, which is equivalent to the hazard intensity footprint. This applies also to tsunamis generated by other non-meteorological sources, including asteroid impacts, landslides, and volcanic eruptions. For an earthquake trigger, the initial size of the tsunami above the rupture can be estimated in terms of potential energy [J] (following the box-shaped ‘waterberg’ method) bywith kg/m3 the water density, the gravitational acceleration, the earthquake rupture length [m], the wavelength or width of the area displaced [m], and the upward rupture displacement [m] [71]. For other formulations, see [72].
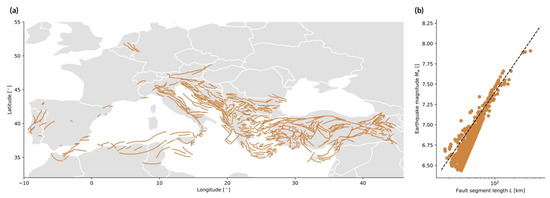 Figure 3. Example of line sources (earthquake case). (a) Fault segments in the 2013 European Seismic Hazard Model (ESHM13) [42]; (b) mean magnitude versus effective fault segment length in the ESHM13, compared to Equation (8) (dashed line) with and [66].Figure 3. Example of line sources (earthquake case). (a) Fault segments in the 2013 European Seismic Hazard Model (ESHM13) [42]; (b) mean magnitude versus effective fault segment length in the ESHM13, compared to Equation (8) (dashed line) with and [66].
Figure 3. Example of line sources (earthquake case). (a) Fault segments in the 2013 European Seismic Hazard Model (ESHM13) [42]; (b) mean magnitude versus effective fault segment length in the ESHM13, compared to Equation (8) (dashed line) with and [66].Figure 3. Example of line sources (earthquake case). (a) Fault segments in the 2013 European Seismic Hazard Model (ESHM13) [42]; (b) mean magnitude versus effective fault segment length in the ESHM13, compared to Equation (8) (dashed line) with and [66].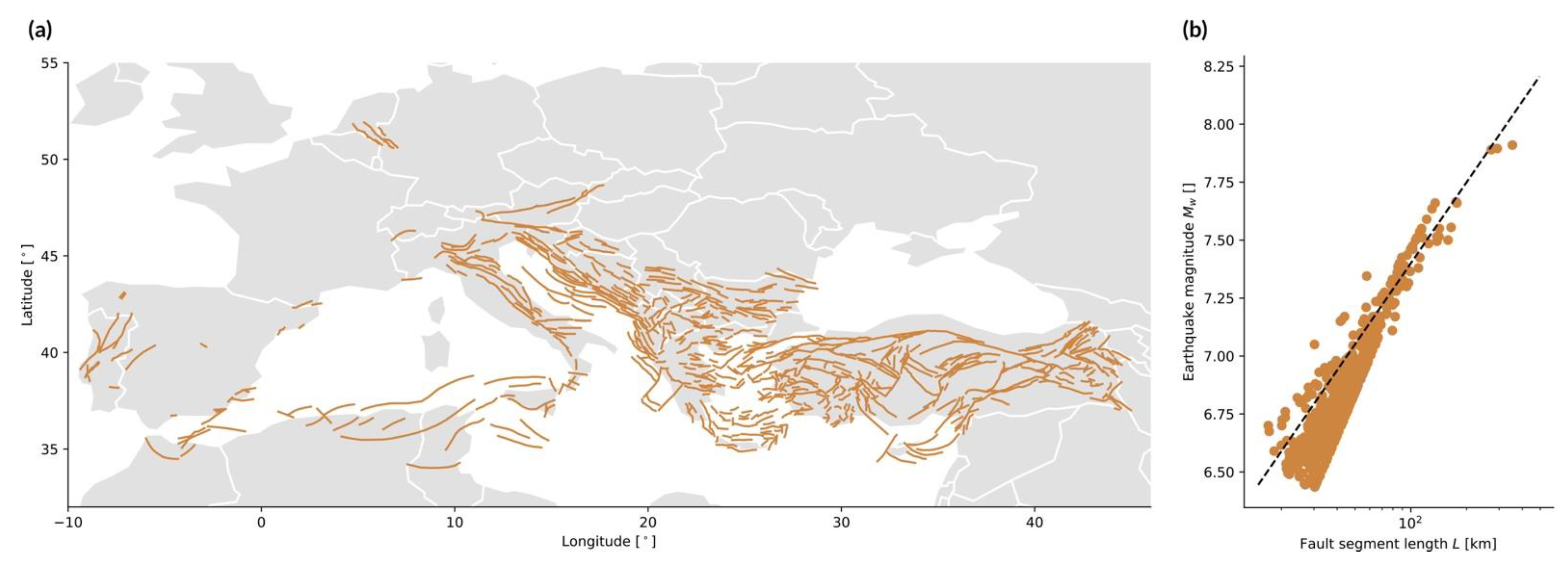
2.2.3. Area Source
An area source is a localized surface large enough that it cannot be simplified by a point source (Section 2.2.1) and small enough that it is not a diffuse environmental source (Section 2.2.5). There is no strict definition of an area source. It can be characterized by a geometrical shape, such as a rectangle or an ellipse, or by an irregular patch defined by the coordinates of its contour. All physical characteristics are assumed to be spatially homogeneous within the source. An area source, such as a large warehouse stocked with explosive material, is commonly simplified by a point source [73]. An area source may represent a region in which the peril process is kept hidden, such as a territorial division in a compartmental epidemic model (with integration method). However, the heterogeneity of the real-world environment makes the use of a diffuse source more realistic in many cases (e.g., landslides—see Section 2.2.5). Finally, an area source can also represent uncertainty on a fault line [42], while a line source may suffice to characterize an area (e.g., an earthquake rupture plane or tornado path, as previously shown). Perils for which an area source is most common are:
- Hail: The source is a convective storm, with hail as a sub-peril alongside strong winds, tornados, lightning, and heavy rain. It is described by the area in which hailstones are found, with the size of the event defined in terms of the maximum hailstone diameter [cm] [19]. Hail cells have been approximated by so-called storm boxes [19] or ellipses [74]. Their location, size, and shape are constrained by meteorological observations [74]. The temporal evolution during an event can also be considered, in which case a track source should be used [74]. Note that it is a case where event source and hazard footprint cover the same area (see Section 2.4.2).
- Urban fires and wildfires: Fires in both wildland and urban areas were originally modelled as ellipses, with the fire spread rate [m/min] defined aswith the spread rate on flat terrain and without wind as a function of the combustible characteristics (i.e., the source), the direction of maximum slope, the wind direction, the eccentricity function of windspeed and terrain slope, and an arbitrary direction [75,76]. Despite its simplicity, Equation (11) produces reasonable estimates of fire spread in a uniform environment. It is now more common to use cellular automata to model fires by considering diffuse sources instead [28] (see Section 2.2.5 and Section 2.4.3). Yet, ellipses can be used to define the seed events from which greater fires can propagate [76].
2.2.4. Track Source
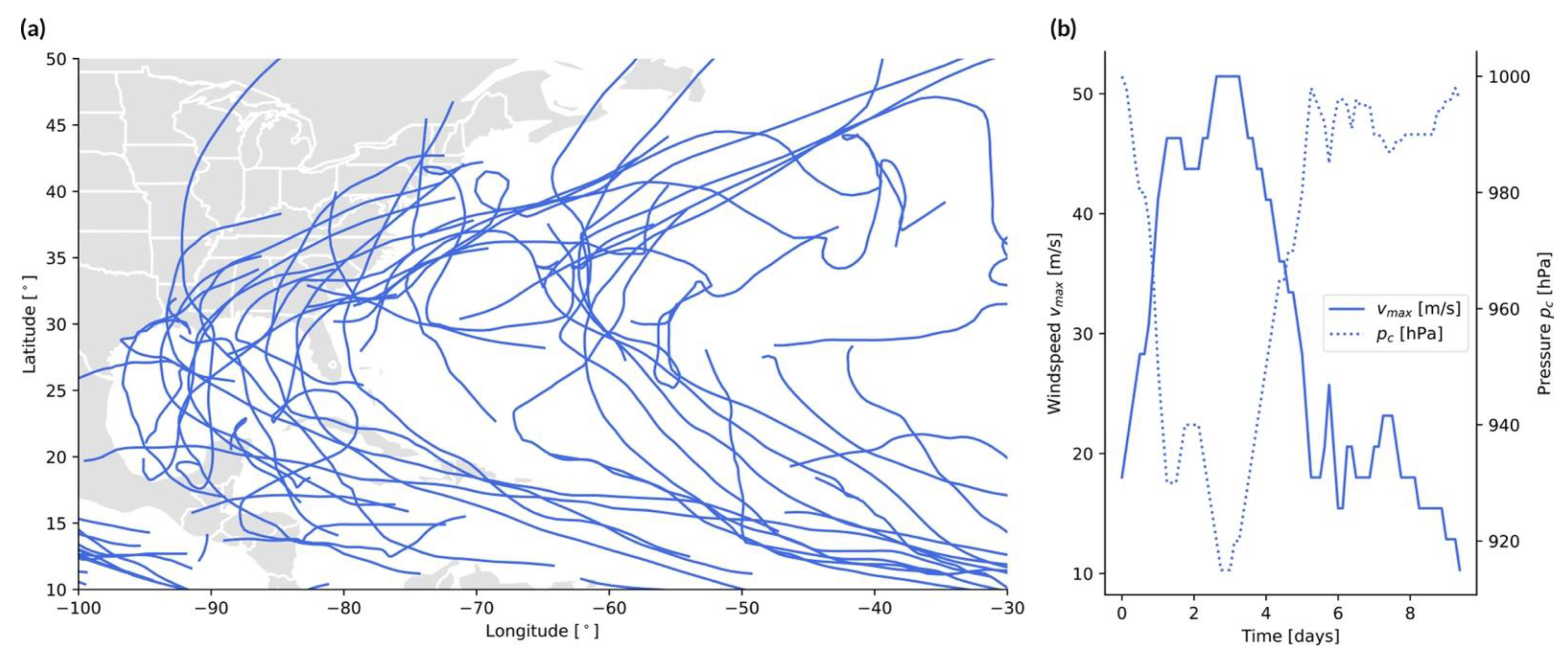
The track source is the combination of a point source and of a line source, with the event footprint defined at any given time from a point along the line, i.e., the track . This applies to storms, such as windstorms, tropical cyclones, and other related perils (note that the point source could be replaced by an area source, for example in the case of hail). Examples of hurricane tracks are shown in Figure 4a.
- Tropical cyclones: The source is an area of low pressure over a large water surface, which moves along a track over time . The genesis point, trajectory, and end point of the storm are stochastic and derived from past observations [77]. The event size at any given time is defined by the maximum wind speedwith [Pa] the cyclone’s central pressure, [Pa] the ambient pressure outside the cyclone, 1.15 kg/m3 the air density, the Holland parameter, and Euler’s number [78]. Notice the anticorrelation between and in Figure 4b, in agreement with Equation (12). The windspeed can then be used to estimate the event size on the Saffir–Simpson Hurricane Wind Scale. Along the track, the windspeed progressively increases, as the tropical cyclone grows, and then decreases, as the storm makes landfall, weakens, and dies off (Figure 4b). One can define the size of an individual storm in terms of total power dissipation by integrating over the wind profile along the entire track [79] (see Figure 5 and Section 3).
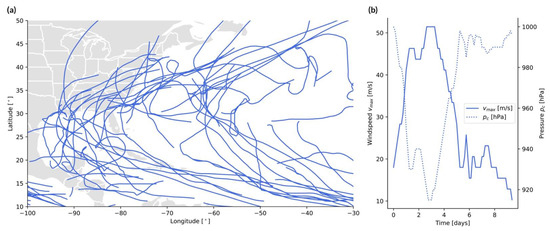
Figure 4.
Example of track sources (tropical cyclone case). (a) Tracks of recent Atlantic hurricanes (2020–2022) in the IBTrACS database [48]; (b) windspeed versus central pressure along the track of 1992’s Typhoon Yvette, based on IBTrACS data as shown in [48].
Figure 4.
Example of track sources (tropical cyclone case). (a) Tracks of recent Atlantic hurricanes (2020–2022) in the IBTrACS database [48]; (b) windspeed versus central pressure along the track of 1992’s Typhoon Yvette, based on IBTrACS data as shown in [48].
2.2.5. Diffuse Source
The diffuse source is the part of the environment—natural, technological, or socio-economic—which acts as a spatially extended energy stock. The environment, or system, can be defined on an geographical grid with coordinates . It may also be represented as a graph composed of nodes with spatial coordinates and links defined in an adjacency matrix (as, for example, in the case of connected infrastructures). It could finally be a set of moving agents with coordinates . Each element of the diffuse source has additional characteristics necessary for the estimation of event size. In contrast to other source types, the event size is not well constrained without dynamical modeling, except for the maximum possible size often being the size of the system itself. This section describes the source of a seed event, which can be a point or an area which does not characterize the event in its entirety. The event size depends on how the event grows, which is described in Section 2.4.3 on hazard footprint modeling. In some of those cases, event size and footprint intensity can be indistinguishable and described by the same metric.
- Armed conflicts (incl. terrorism): The source is a hierarchical group of individuals, ranging from small terrorist organizations to large (trans)national armies. The size of the seed event is constrained by the funds and people power at the disposal of the attacker, as well as by the group’s network structure and utility function. The process is highly dynamic, as the various agents are mobile and opponents can allocate resources to defend against an attack [25,26]. The size of an event depends directly on the type and number of weapons. It can be a group of fighters (with firearms or non-firearms—see Section 2.4.3), conventional weapons (expressed as a TNT-equivalent, e.g., Equation (3)), or non-conventional weapons, including chemical, biological (see epidemic), radiological, nuclear (e.g., Equation (4)), and cyber- attacks. Those weapon types, which require different hazard modeling strategies, can be considered different sub-perils of an armed conflict. The event size is commonly defined in terms of the fatality count summed over all attacks taking place during the conflict ( then directly represents the human loss in the risk component of the CAT model).
- Blackouts: The source of a blackout is a current overload due to a local disturbance in the power grid. This system is composed of generator nodes (i.e., power plants), transmission nodes, and distribution nodes connected via transmission lines. A seed event can correspond to the tripping of several lines due to tree contact for example, which can be caused by lack of tree trimming or by a storm [80]. The event is only called a blackout if a relatively large number of consumers is affected by the loss of electricity. The event size can also be defined in terms of unsupplied energy [MWh]. The event size depends on how the overload propagates through the power grid through cascading failures.
- Business interruptions: The source is any business that is shut down due to direct damage by some natural or man-made event. Although a business location can be represented by a point source or extended area source, a catastrophic event consists of the aggregation of disruptions at many locations in the built environment, which may include a supply chain network in the case of contingent business interruption. The event size is directly defined in terms of revenue loss [30].
- Crop failures (due to pest): The source is a pest, such as an insect, a virus, a grazing animal, or some other invasive species that damages the crops. The size of an event depends on the complex interactions between the pest and crop growth within the crop production system where natural predators and/or pesticides may also participate [32]. Note that crop failure can also be due to climatic stress, represented by extreme temperature changes, droughts, as well as meteorological (hail), hydrological (flood), and ecological (field fire) events. In those cases, crops only represent the exposure layer of the CAT model. The event size is commonly defined in economic terms, such as farming production yield loss. However, it could, in theory, be defined by pest biomass before any consideration of crop damage.
- Cyber-attacks: The source of a cyber-attack is a malicious agent (a hacker) acting for personal gain or on behalf of a governing entity. Cyber-attacks can include theft of data or currency, ransoms, business interruption, or some other forms of system destabilization. The attack occurs, by definition, via electronic communication networks and virtual reality [21]. One particularity of cyber-attacks is that they are not geographically bound. They can cascade into greater events [22] via highly dynamic processes [21]. Their size is defined in terms of the number of data breaches in the common case of data exfiltration. However, this depends on how the initial attack propagates through the IT system. Since is often the number of actual breaches and not of attempted breaches, the event size directly reflects the loss in the risk domain after considering the level of vulnerability of the exposed system. Hazard and risk are intertwined since both the type and size of a cyber-attack depend on the attacked system. For example, a cyber-heist on a banking system is different from a distributed denial of service (DDoS) attack (with here expressed in gigabits per second [Gbps]), itself different from a cyber-attack on a power grid or other connected critical infrastructure. Many other types of events exist which could go as far as a cyber-war [22].
- Epidemics: The source of an epidemic is the first infection in the human population. This requires the pathogen and susceptible hosts to be in contact in adequate numbers. The size of an event can be the number of infections , which depends on how the epidemic propagates, as a function of the basic reproduction numberwhere is the transmission parameter, the recovery delay, and the total population. The parameters and depend on the vector, which can be a virus, bacterium, fungus, or parasite [24]. When an epidemic spreads to multiple continents, it becomes a pandemic. The total number of fatalities, which is the number of infections times the mortality rate, is the final loss. However, it may also be considered as the event size since the mortality rate also depends on the pathogen, and not only on the human vulnerability (function of age, gender, and health condition).
- Landslides: The source is the set of terrain patches with an unstable slope , which is controlled by topographic and soil characteristics. The size of the seed event can be the area [km2] or volume [km3] of each patch or set of patches. The area that is unstable is defined by a Factor of Safety () lower than 1, since it is the ratio of resisting forces to driving forces. A simple formulation iswhere [m] is the depth perpendicular to surface (or thickness) of the soil, is the gravitational acceleration, [N/m2] is the soil cohesion, [kg/m3] is the soil density, 1000 kg/m3 is the unit weight of water, is the slope angle, is the internal friction angle of the soil, and is the relative wetness representing the ratio between water column height and soil height . For additional formulations, see [81,82]. An increase of due to heavy rain further decreases , making previously stable slopes unstable [82]. is also involved in landslide triggering by earthquake ground shaking [83].
- Social unrest: The source of social unrest is the part of the population which has a high level of grievance against the governing entity [35]. The first individuals turning violent, who can be anyone in the system, can lead to a riot, i.e., an aggregate act of violence against individuals and property, which includes looting and setting fires as sub-perils [84]. The event can, however, be avoided if enough security is at the disposal of the government [35]. The dynamics is reminiscent of what can occur during an armed conflict (see above), with an extreme social unrest event potentially turning into a revolution. The event size could, in theory, be defined in terms of the number of rioters .
- Urban fires (accidental or malicious): Fire can be considered a sub-peril of industrial accidents [58], armed conflicts [85], and social unrest [84], as well as a secondary peril of earthquakes [28]. The source is some combustible material that is set alight. The event size, defined in terms of burnt area , depends on how the fire propagates in the environment, as in the case of a wildfire (see below). If an elliptical event is realistic in a uniform environment (Equation (11)), it is not in most real-world situations.
- Wildfires: The source of a wildfire has two components: a trigger for ignition and some combustible material (i.e., vegetation). The main cause of wildfires globally is anthropogenic, with fires started intentionally or accidentally. This ranges from power line ignition to arson via a forgotten cigarette butt [86]. Lightning strikes are the most important natural ignition trigger for wildfires [87]. In this case, the occurrence of a seed event depends on the continental lightning rate [flashes/min]A function of the convective cloud top height [km] and a resolution- and model-dependent scaling factor [87,88]. The size of the event, described in terms of burnt area , depends on the propagation process, a function of the characteristics of the environment, such as terrain, fuel, and meteorological conditions (see Equation (11)). Conditions are more favorable for a wildfire during a drought [89]. In the CAT modeling context, losses occur in the wildland–urban interface, defined as an area covered by more than 50% vegetation with more than one housing unit per 1.62 ha [27]. An ignition index can be calculated to map the potential size of an event as a function of dead fuel moisture, temperature, and vegetation species flammability among other parameters [90].
2.3. Event Size Distribution
The probabilistic nature of a hazard is described by the rate of events as a function of the event size (or by the return period ). There are two main statistical approaches, commonly the power-law distribution [39,91,92], for discrete events, and the Generalized Extreme Value (GEV) distribution and Generalized Pareto distribution (GPD) [93], for events derived from continuous flows. Figure 5 shows the size distribution of the perils from Section 2.1 that can be fitted by a power-law, GEV, or GPD. Any peril can, however, be described by various statistical distributions, with the choice often depending on the discipline’s most accepted approach for event definition and event count [94,95,96]. We here assume the independence of events as well as the stationarity of event occurrences over time.
2.3.1. Power-Law Distribution
The complementary cumulative distribution function (CCDF) of a power-law is
with the event size, the minimum event size threshold, and the power exponent [39]. The size distribution of a hazard is most often described by the annual rate
generally expressed in the following empirical form
with and the slope of the size distribution in a log–log plot (also called the shape parameter of the classical Pareto distribution). We will consistently use (i.e., cumulative form) in the following review.
- Armed conflicts (incl. terrorism): The size distribution follows Equation (18), with as the number of fatalities [97]. In Ref. [97], a value of was obtained for various types of conflicts (war, banditry, gang warfare). In Ref. [98], a value of was obtained for interstate wars taking place between 1820 and 1997 and the 1465–1965 European great power wars. In Ref. [39], a value of was calculated for wars between 1816 and 1980. In the case of terrorism worldwide from 1968 to 2006, we obtain and (Figure 5), close to the value of found by [39,47] for the same dataset.
- Asteroid impacts: The flux of small near-Earth objects colliding with our planet follows a power-law in the form of Equation (18), with [kton] as the energy and 0.5677 and 0.90 globally [99]. In Ref. [92], a value of was obtained when including more recent data. Considering data up to 2022, we obtained 0.468 and 0.99 (Figure 5).
- Blackouts: The size distribution follows Equation (18), with as the number of customers affected. In Ref. [100], the range was observed for different countries. For data from the United States, Ref. [39] obtained , while we obtained and (Figure 5) for the same dataset.
- Cyber-attacks: The size distribution follows Equation (18), with the number of personal identity losses or data breach volume (used as the example in this case). In Ref. [101], a value of was obtained when using data from the Open Security Foundation for the 2000–2008 period. Considering hacking events from the public dataset published by the Privacy Rights Clearinghouse [40], we obtained and for the 2005–2018 period.
- Earthquakes: Although the size distribution of earthquakes also follows a power-law in the seismic energy domain with (Equation (18), as with the and values shown in Figure 5, and with ) [102], the Gutenberg–Richter (exponential) law is used in virtually all cases [103], as a function of the magnitude . It yields a Gutenberg–Richter slope of globally [41] which is close to unity, known as the standard value for tectonic earthquakes.
- Landslides: The size distribution follows Equation (18), with [km2] the landslide area or [km3] the landslide volume. Conversion from area to volume can be performed with the empirical scaling relationship [104]. For , a review of more than 20 analyses provides [105]. For landslides triggered by the 2008 Wenchuan earthquake for instance [45], we find at the tail of the distribution (Figure 5), which is in agreement with [106] who obtained .
- Tsunamis: The size distribution follows Equation (18), with the maximum wave height (i.e., tsunami runup). Ref. [107] obtained for different locations along Japan. For global data [49], we find and (Figure 5).
- Volcanic eruptions: The size distribution follows Equation (18), with [km3] as the erupted volume. Considering all volcanic eruptions which occurred after the year 1000 in the LaMEVE database [50], we obtain −1.156 and 0.66 (Figure 5). A recent review of large VEI eruptions indicates that VEI-7 events recur every 500–1000 years [108]. Our parameters lead to 300–1300 years for the range of VEI-7 events.
- Wildfires: The size distribution follows Equation (18), with [km2] as the size of the wildfire as defined by the burned area . Ref. [109] reviewed the literature and mentioned for China and the United States. Ref. [39] calculated for U.S. federal land. Ref. [92] found for fires in Angola and for fires in Canada. For the FRY catalogue [51], we obtained 8.553 and 1.23 (Figure 5).
2.3.2. Generalized Extreme Value (GEV) Distribution
Events such as storms and floods, which originate from continuous flows (wind and water discharge, respectively), must be defined as extreme instances. To define an event, a threshold or maximum estimate is then considered, following the rules of Extreme Value Theory [93]. When considering the maximum value over a fixed period (i.e., the block maxima approach), the Generalized Extreme Value (GEV) family of distributions applies which, in CDF form, is
with the “size” termed the return level (“”) in GEV parlance, the location parameter, the scale parameter, and the shape parameter. corresponds to the Fréchet distribution, to the Weibull distribution, and to the Gumbel distribution [93]. Considering the probability of exceedance instead,
where is the return period. Inverting Equation (20) gives the so-called return level plot
Introducing (i.e., a return period) in Equation (21) yields [110]
(see flood case below).
An alternative representation of extremes that uses more of the available data consists of analyzing excesses over a high threshold (the so-called Peak-Over-Threshold, POT, method). In this case, the Generalized Pareto distribution (GPD), a type of power-law [91], applies. Its CCDF takes the form
with the location parameter (i.e., the chosen high threshold), the scale parameter, and the shape parameter, which is related to the power exponent of Equation (16) via . If , the distribution has the upper bound . For the case , the exponential distribution is retrieved [93]. It follows that
where “size” is exceeded on average once every observations (i.e., a return period) and where is naturally estimated as the sample proportion of observations (or “events”) exceeding . The return level plot of the GPD is [93]
(see epidemic case below).
Since extreme values are commonly retrieved from individual sensors, the parameter set is usually site-specific. Parameter values are only provided below when associated to regional or global datasets (e.g., epidemics) and/or when a fit is provided in Figure 5:
- Epidemics: Considering a global dataset, [43] showed that epidemic sizes (per mil/year) follow a GPD (Equation (25)), with ‰/yr and for a fixed ‰/yr in addition to . We retrieved ‰/yr and (i.e., or ) for the same data and threshold (Figure 5).
- River floods: With the event size defined from the maximum discharge observed in a year of daily measurements, flood sizes are described by the GEV distribution [111,112]. Taking the Potomac River dataset [46] as a textbook example, we obtained m3/s, m3/s, and (Figure 5). A power-law behavior has also been proposed [95].
- Storms (tropical cyclones and other windstorms): Both GEV and GPD distributions have been used to describe the size distribution of storms () and related perils. Parameterizations for specific cities and coastline segments can be found in the literature [113,114,115,116]. It can be noted that defining storm size in terms of total dissipation of power yields a power-law distribution with a relatively high exponent [92]. Using such a proxy by summing over the cube of records per interval for each track duration , i.e., [m3/s2] [79,92], we obtain for global data [48] (Figure 5).
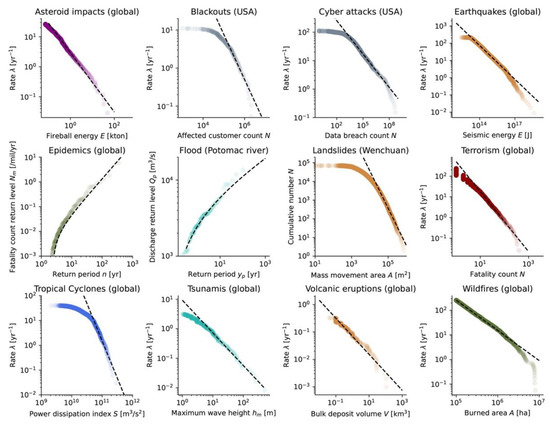
Figure 5.
Size distribution of various perils, fitted by a simple power-law (most perils), a GEV distribution (river flooding), or a GPD (epidemics). Note that the results are sensitive to the choice of minimum size threshold, with fitted parameters to be used carefully when extrapolating. Data sources (Section 2.1): asteroid impacts [38], blackouts [39], cyber-attacks [40], earthquakes [41] (with [117]), epidemics [43], landslides [45], flooding [46], terrorism [39], tropical cyclones [48], tsunamis [49], volcanic eruptions [50], and wildfires [51]. See the text within Section 2.3 for the values of the fitting parameters.
Figure 5.
Size distribution of various perils, fitted by a simple power-law (most perils), a GEV distribution (river flooding), or a GPD (epidemics). Note that the results are sensitive to the choice of minimum size threshold, with fitted parameters to be used carefully when extrapolating. Data sources (Section 2.1): asteroid impacts [38], blackouts [39], cyber-attacks [40], earthquakes [41] (with [117]), epidemics [43], landslides [45], flooding [46], terrorism [39], tropical cyclones [48], tsunamis [49], volcanic eruptions [50], and wildfires [51]. See the text within Section 2.3 for the values of the fitting parameters.
2.4. Hazard Intensity Footprint
Once the size distribution is defined for a given peril, the impact of each event on the environment must be assessed. We use the term intensity to describe the physical quantity that leads to damage (i.e., a variable of the vulnerability function ). The area impacted by said intensity is known as the event footprint. A hazard intensity footprint can be modelled by following three main approaches: (i) an analytical expression of spatial diffusion with the value of decreasing away from the event source (Section 2.4.1); (ii) a threshold model with as a passive function of the variability on the underlying environment layer that is sliced (Section 2.4.2); or (iii) a numerical model of dynamic propagation of the event with potentially increasing in the diffuse source (Section 2.4.3).
2.4.1. Analytical Expressions of Static Event Spatial Diffusion
Although every hazard process is dynamical in nature, the process can be simplified to a static footprint where the event source is localized in most cases. For both point- and line-sources, the footprint is
with the spatial coordinates, the event size, and the distance to the event source. For track-sources, we can define
which takes the maximum intensity observed at a given location over all timelapses . For a point source, with as the source coordinates. For both line- and track-sources, with as the source coordinates (for an area source, these could correspond to the surface’s contour). Modifications may be applied to describe second-order variations in the footprint. Site-specific conditions can be modeled by simply adding a modifying factor to , as a function of . All the equations listed below are empirical relationships which are parameterized for some generic conditions. Epistemic uncertainties are not assessed but can be assumed to be large as only the simplest models are considered in this review. The reader is referred to the articles mentioned below for other functions, parameterizations, and calibrations.
- Asteroid (and comet) impacts: The kinetic energy of the celestial body transforms into destructive explosive energy at impact, which is described by peak overpressure [psi]. The simplest approach consists of defining a binary intensity footprint, for instancewith the 4-psi overpressure radius [km], [Mton] the event impact energy, and [km] the burst altitude [34]. Due to lack of data for calibration, the blast footprint formula is usually calibrated to data from nuclear tests [33,52,118] (see also the comparison between Equation (28) and the industrial explosion footprint case below and in Figure 6). Damage can also occur due to thermal radiation [34].
- Earthquakes: The general formulation of a ground motion prediction equation (GMPE) iswith the earthquake magnitude and [km] the distance to the source [119,120]. The intensity is often taken as the peak ground acceleration but can also be peak ground velocity, peak ground displacement, or spectral acceleration of felt intensity [121]. One of the simplest parameterizations is , , , and , with as the PGA [g] and [km], being the distance to the surface projection of the fault rupture, and the fault depth [122] (Figure 6).
- Explosions (accidental or malicious): A simple empirical relationship linking blast overpressure [kPa] to the explosive mass [kg] iswith as the dimensional scaled distance according to Hopkinson–Cranz law and with [m] as the distance to the source [123]. This is, for example, consistent with the binary footprint model (Equation (28)) proposed for asteroid impact CAT modeling (for an impact on the ground with and 1 psi = 6.89476 kPa). This is illustrated in Figure 6. The overpressure field for very large yields is calibrated to nuclear tests [118] and therefore also applicable to the blast component of nuclear explosions.
- Tornados: The mean wind field for a stationary tornado is calculated as the sum of the tangential and radial velocities and , with both wind velocity components based on the Rankine vortex model,with the distance from the tornado origin, the maximum (tangential or radial) velocity, and the radius of the maximum (tangential or radial) velocity. An example of parameterization is m/s, m/s, and m [124]. The intensity footprint of the tornado is obtained by adding the forward motion velocity to the wind field (e.g., m/s).
- Tropical cyclones: The wind profile of a tropical cyclone can be described bywhere [km] is the distance to the cyclone center, [km] the radius of maximum winds, and [rad/s] the Coriolis parameter function of the latitude (see Equation (12) for the definition of , , , and ) [78] (Figure 6). Nowadays, more sophisticated models are preferred [125], although Equation (32) remains important in CAT modeling conditional on the proper estimation of [126].
- Volcanic eruptions: Apart from pyroclastic and lava flows, the principal hazard arises from the fall of airborne debris, ranging from blocks to ash, collectively known as tephra. The ash load is calculated by the pressure [Pa], where 900 kg/m3 is the density of dry ash and is the ash layer thickness [m]. The ash thickness can be estimated from the exponential thinning lawwhere [m] is the maximum thickness and [m] is the half-distance (Figure 6). For a circular footprint,where is the volume of tephra [127]. We remain unaware of any simple model to estimate .
2.4.2. Threshold Models of Passive Event Emergence
Some hazard intensity footprints can be generated by applying a threshold on an environment layer, such as a water level relative to sea surface on topography (storm surge case) or a temperature limit on the regional wet-bulb temperature (heatwave case). A threshold model may have binary outcomes in which a value above threshold means potential harm and a value below none. The threshold defines the spatial contour of the hazard footprint.
- Business interruptions: There exists a lower damage threshold of ~5–10% that must be breeched to result in a business interruption, and an upper threshold, often as low as 50%, to cause the facility to completely shut down for repair or demolition [30]. This depends on the hazard intensity footprint of the trigger event.
- Hail: The contour of a convective storm is estimated from meteorological indicators. A hailfall footprint (often elliptical—see Section 2.2.3) then exists if the hailstone size (often assumed uniform in space) can exceed the threshold above which damage can occur (usually 2 cm in diameter) [128]. The hazard intensity is then defined as the kinetic energy [J/m2]with the maximum hailstone diameter [mm] and empirical parameters of and in [128].
- Heatwaves: Heat stress can be quantified by the wet-bulb temperature , measured by covering a standard thermometer bulb with a wetter cloth and fully ventilating it. If exceeds a 35 °C threshold, hyperthermia follows [129]. The heat stress footprint can be derived from the temperature map (which could be considered an unbounded area source; Figure 6) with the empirical expressionwhere is the relative humidity [130].
- Storm surges: The so-called “bathtub” model defines a flooded area as all the locations below a certain elevation that are hydrologically connected to the coast, with the threshold based on the size of the storm surge event. In other words, it is a projection of a horizontal flood surface onto the topography (Figure 6). This model tends to overestimate flood extents [131]. More realistic models are based on hydrodynamics, a simplification of which are cellular automata (see Section 2.4.3). In this case, the discharge [m3/s] must be used as input, defined fromwhere [m] is the height of water above the ground, [m] the breach width, and [m/s] the velocity of the water following the weir equation [29]. The breaching of a natural or man-made defense must also be modelled, which involves defense vulnerability analysis between event size assessment and flood modeling [29].
2.4.3. Numerical Models of Dynamic Event Propagation
Some hazard processes cannot easily be simplified. This is especially true for perils with a diffuse source (see Section 2.2.5). Numerical modeling is then required to describe the dynamical process through time. In this case, energy does not dissipate but propagates through the extended source (and it is assumed that the event is extinguished immediately at the border of the source). A static footprint can still be defined with . For the sake of simplicity and transparency, we here only consider cellular automata (CA) and their extension to agent-based models (ABM). Only their basic principles are explained. Other numerical methods could be used but cannot be condensed in this review. Most CA represent variants of the Sandpile model [132].
It should be noted that the intensity footprint of an event occurring on a diffuse source usually matches the event size . The intensity is often binary: burned/not-burned in a wildfire, electricity off/on in a blackout, or people infected/not-infected in an epidemic, in which cases the intensity is a count or an area. When the assets at risk are also equivalent to the source, there is no convolution operation needed between hazard and exposure. Modeling the hazard footprint is not required in this case, a good example being compartmental modeling for epidemics [133] where exposure, hazard, and losses are people. However, the hazard footprint remains a critical element for some other perils, for example landslides and river floods for which the intensity is defined as the soil thickness and water level at , respectively. For those specific cases, numeric modeling is required to describe how mass movement occurs on an irregular surface (in disregard of the surface representing a diffuse source or not).
Numerical modeling of hazard footprints is necessary or often recommended for the following perils:
- Armed conflicts (ABM): A war is a cumulation of attacks and counterattacks, whose dynamics can be explained with Game Theory [36]. Although highly complex and heterogeneous in nature, some basic rules can be mentioned. The simplest model of attrition warfare is a set of ordinary differential equations (ODEs) defined aswhere is the number of soldiers in the A army, each with offensive firepower (i.e., number of enemy soldiers killed per soldier from A), and is the number of enemy soldiers in the B army, each with offensive fire power (called Lanchester equations after F.W. Lanchester’s 1916 work) [134]. Solving Equation (38) indicates that the effectiveness of an army rises proportionally to the square of the number of its soldiers, but only linearly with their fighting ability. While Equation (38) is relevant for static trench warfare (see other ODEs in [135]), agent-based models can include spatial variations of forces, decision making, and psychology [136]. Agents are then combat units with a mission and situational awareness, among other characteristics. Their possible states are alive, injured, or killed. The battlefield is the geographical lattice. However, the rules would be too numerous to list here [136,137]. A much simpler ABM for social unrest will later be provided that illustrates how different groups of individuals may act against each other [35]. The hazard footprint of an armed conflict would, in theory, be the sum of a heterogenous set of sub-footprints (e.g., explosion footprints—Equation (26), agents’ individual acts of violence—see social unrest and terrorist attack cases below, fires, etc.).
- Blackouts (CA): Cascading power failures can be modeled as a Sandpile on a network, instead of on a regular lattice. In the simplest generic configuration [138], each power line and generator have a region of safe operation, characterized by a load in a node. Links between nodes define the neighbors to which or from which a load increment is randomly transferred withwhen the power load exceeds the margin at node , then units of load are transferred (and distributed randomly) to the failed node’s neighbors :with the condition . The Sandpile network self-organizes, with cascading failures potentially leading to large-scale blackouts [138]. The footprint of the blackout is then defined as all the nodes that failed in one event (Figure 6).
- Crop failures (due to pests, ABM): Pest dynamics can be described by a set of ODEs that describes inter-species interactions. They can be multiple and play at different spatiotemporal scales in an ecosystem. The simplest model is the predator–prey Lotka–Volterra model [139,140]where is the prey density (e.g., the crops) and the predator density (e.g., the pest). Note the resemblance to the model of attrition warfare (Equation (38)). A far more complex model is the seminal ‘insect outbreak system’ of [141], which—in its simplest form—describes interactions between a pest (the spruce budworm), its predator (some birds), and the exposed vegetation (the forest). Several CA and ABM have been developed for insect pest assessment [32]. Simple agent rules can be derived from Equation (41) by, for instance, adding a spatial component, random agent movement, and a contact radius. The intensity of an event could be defined by the aggregate size of the pest on the crops, , or the direct damage, .
- Cyber-attacks (various): Cyber-catastrophes propagate via cascading effects within IT systems and networks. For data exfiltration cases, the final event size, or event footprint extent, can be defined on a data breach severity scale function of the number of lost personal records (P3, for the range 1000–10,000, to P9, for 1 billion [22]). Cyber-attacks may also cascade into critical infrastructure failures (e.g., blackout—see above) and socio-economic events [22]. Their footprints (both virtual and physical) are highly scenario-dependent. However, [22] indicated a 1.6 economic multiplier when considering loss increase due to cascades in a trading network of companies. The dynamics of a cyber-attack is mainly governed by the principle of least action, i.e., striking targets with inferior security, and follows the rules of Game Theory [22]. Various statistical models have been proposed [21,142] which are outside the scope of this paper. On the physical side, epidemic models, for example (see below), have been modified to quantify the spread of a piece of malware [143].
- Epidemics (ABM): The simplest epidemic model is the Susceptible-Infectious-Recovered (SIR) model [133]. Many more sophisticated models exist [144,145] that derive from the SIR set of ODEs:where is the susceptible stock, the infected stock, the recovered stock, and (see Section 2.2.5 and Equation (13) for the definition of and ). The controlling parameter is the basic reproduction number (Equation (13)); a feedback loop leading to an epidemic occurs for . While Equation (42) can be solved by numerical integration, agent-based models attempt to capture the real-world heterogeneous mixing of agents [146,147]. Each stock, or compartment, then represents a state. In the simplest configuration, agents move randomly and, if an infected agent is within infection range of a susceptible agent, . after (Figure 6). Such a model can incorporate local knowledge of demographic data, the healthcare system, and human contact networks [24].
- Floods (river flood, storm surge, tsunami—CA): Flood intensity usually refers to the inundation depth . Although depends on the peak discharge and the shape of the valley [148], modeling is required to properly consider the variations in topography. A simple CA can be defined with the following rules:
- Define the absolute height (or motion cost) as the sum of the altitude and water height ;
- Calculate the gradient (or weight) between the central cell and von Neumann neighbor cells (zero weight for neighbors with equal or greater );
- Discharge the central cell with (some of) the water distributed to the neighbor cells, depending on their weight.
The first discharge occurs at the source of the flood, with where is the time interval between two steps and the cell width. The motion cost can include soil characteristics, such as roughness and infiltration potential. The weights for water distribution are a function of the motion cost at the central and neighbor cells [149], which, in the simplest case, is proportional to the normalized gradients. A similar CA strategy can apply to tsunamis [150]. - Landslides (CA): The propagation of a landslide can be modelled as a Sandpile with the environment—or diffuse source—defined by the topography and the soil thickness . The simplest case consists of initiating mass movement in cells of unstable slope, which is defined by (i.e., seed event, see Equation (14)) [151]. The mass is transferred downward to the Moore neighbor of maximum gradient , so thatand with mass movement defined, for example, bywith the maximum slope angle for which . Since increases, can cross the instability threshold, hence further propagating the landslide (Figure 6). Many model variants exist [152,153,154,155]. Note that the landslide source was previously defined as diffuse instead of an area source because part of the soil outside the seed event may participate in landslide propagation (Equation (43)).
- Social unrest (ABM): A simple model of civil violence [35] consists of two types of agents: population and cops. Population agents can be in one of three states (quiet , active , or jailed ). They have a fixed degree of grievance , a fixed degree of risk aversion , and a vision radius . Cops have a vision radius . All agents are also characterized by their location . There are three rules:
- General rule: Move to an empty cell (or where someone is jailed);
- Population rule: If , become active (), otherwise stay quiet ();
- Cop rule: arrest a random active agent located within ()
where is the net risk and a threshold for rebellion.is the arrest probability, which depends on the number of cops and the number of active agents observed within (and with as a normalization constant). For each jailed agent, the jail term is random and uniform in the range , with once released. Due to the form of Equation (45), a contagion process can occur, leading to a large-scale riot [35] whose intensity could, in theory, be defined by the total number of violent individuals . The duration of the riot could be a second measure of hazard intensity. - Terrorist attacks (ABM): Large-scale terrorist attacks generally infer the use of explosives (see above). The choice of location for an attack can be explained by Game Theory, but the modeling of agents is not required. In other types of attacks, such as a group of terrorists attacking civilians with knifes, an ABM can be formulated. Ref. [156], for example, combined the effect of such an attack with the risk of stampede in a closed environment. Terrorists search targets in their radius of vision, while civilians attempt to flee with direction and speed depending on the amount of blood lost and collisions with other agents. Variants are too numerous to mention any specific model in the context of this review.
- Wildfires (incl. urban fires, CA): The so-called Forest Fire model is defined by four rules:
- An empty space fills with a tree with probability (i.e., tree growth);
- A tree ignites due to a lightning strike of probability ;
- A tree burns if at least one von Neumann neighbor is burning;
- A burning cell turns into an empty cell.
A binary footprint is defined from the clusters of burned cells (Figure 6). Standard models will include wind direction and windspeed, relative humidity, fuel moisture content, air temperature, and topography [157,158,159]. More sophisticated physics-based models will also include radiation, convection, conduction, and other processes, which can, for example, describe the pyrocumulus phenomenon associated to some mega-fires [160]. The general rules previously described can also apply to urban fires under different parameterizations [28].
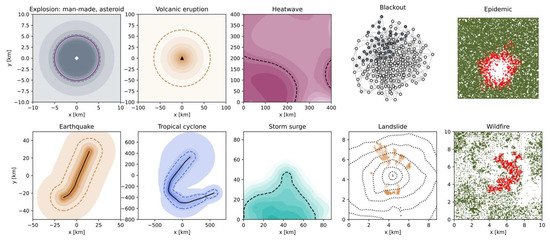
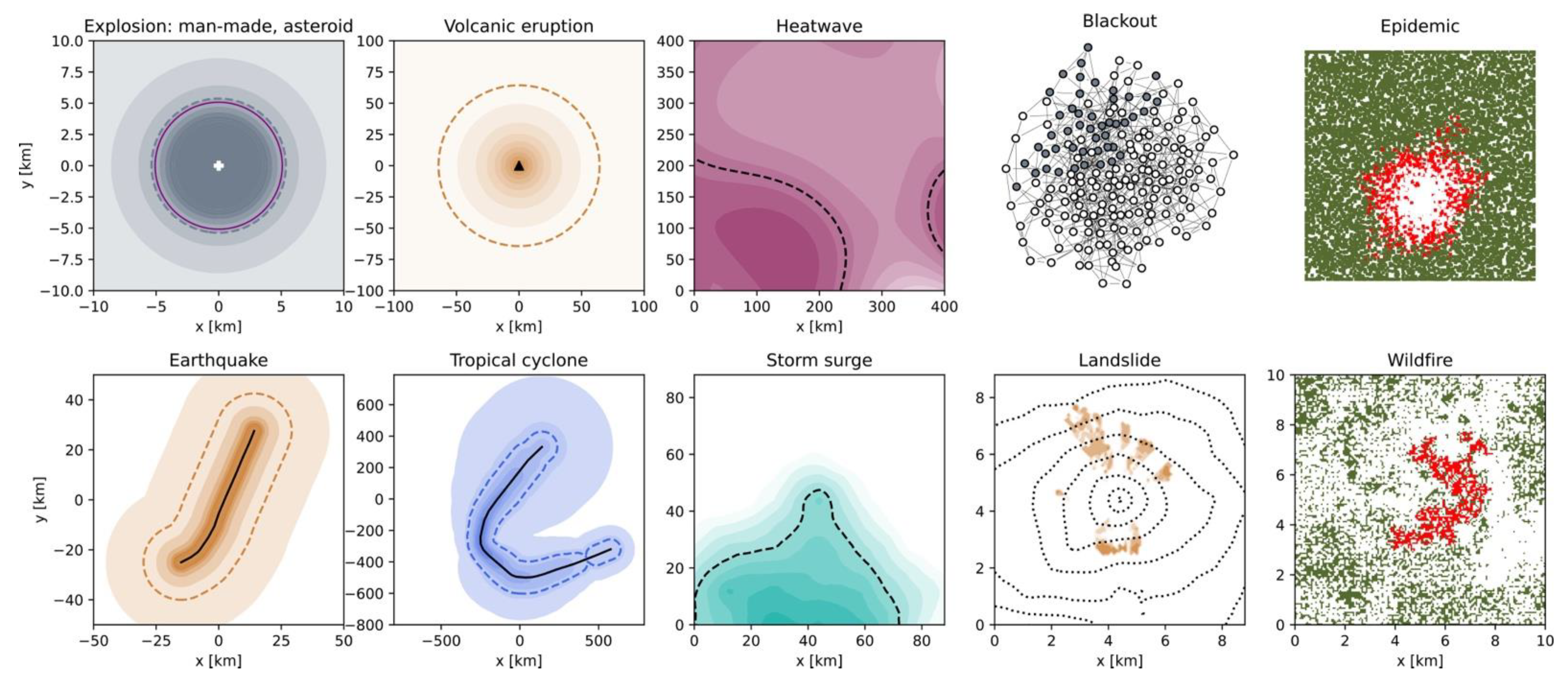
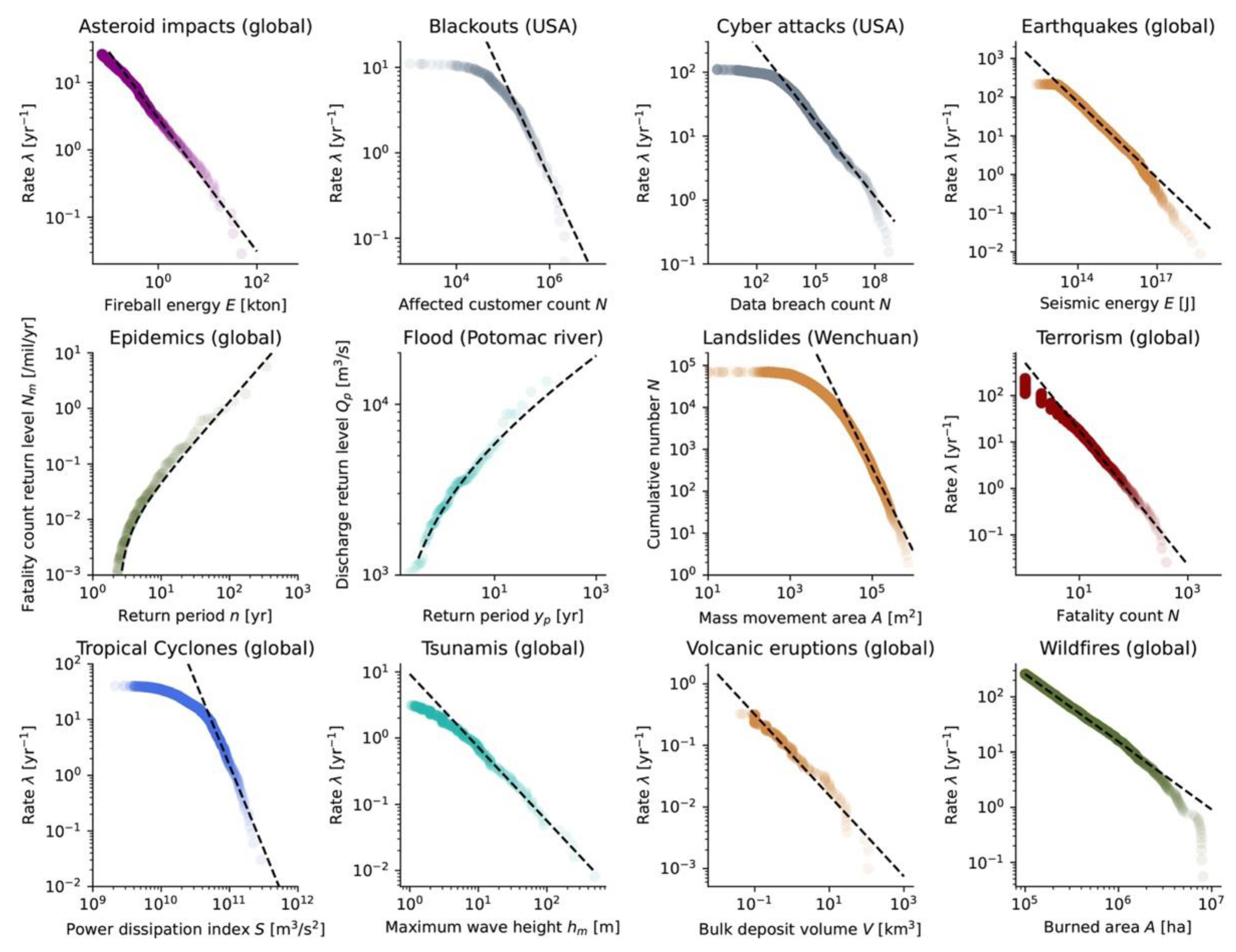
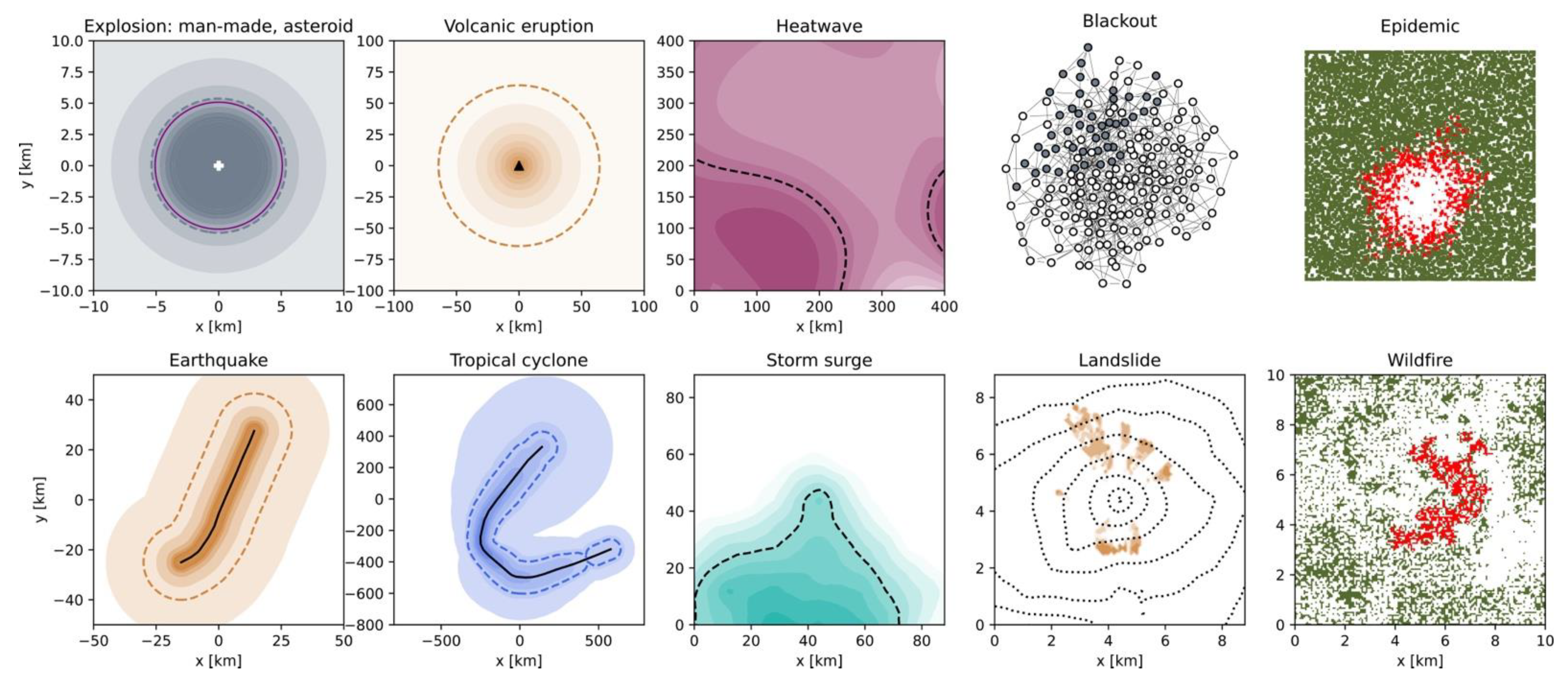
Figure 6.
Examples of hazard intensity footprints based on analytical expressions (first two columns, Section 2.4.1), threshold models (central column, Section 2.4.2), and numerical models (last two columns, Section 2.4.3). DIFFUSION (POINT SOURCES)—Explosion (incl. asteroid impact): overpressure field for an ad-hoc Mton event (Equation (30)) with a 4-psi dashed contour in grey and matching 4-psi contour from Equation (28) in purple. Volcanic eruption: Ash depth map for a km3 (e.g., 1980, Mt St. Helens) and m event (Equation (33)) with a 5-cm dashed contour in orange. DIFFUSION (LINE SOURCES)—Earthquake: Peak ground acceleration footprint of an event on the ESHM13 fault segment ITCS073 with depth km (Equation 29) and a dashed 0.1-g contour in dark orange. DIFFUSION (TRACK SOURCES)—Tropical cyclone: Windspeed map for the IBTrACS 2005 Hurricane Katrina track (Equation (32) with mb and [161]) with a dashed 35-m/s wind speed contour in dark blue. THRESHOLD (AREA SOURCE)—Heatwave: Temperature map of Southwestern France at 3 pm on 17 July 2022 [44] with a dashed 35°-contour in dark magenta as (ad-hoc) proxy to the heatwave. THRESHOLD (LINE SOURCE)—Storm surge: Inundation map on a random topography (with fractal dimension [162]) with dashed 0-m altitude level as a coastline marker. DYNAMIC PROPAGATION (DIFFUSE SOURCES)—Blackout: Ring network with each node (power node or transmission line) connected to four others and with grey nodes as failed (i.e., blackout) following the rules of Equations (39) and (40). Epidemic: Infected and susceptible individuals colored in red and green, respectively, following the rules of Equation (42). Landslide: Event footprint formed of several patches, following the rules of Equations (43) and (44), on a random fractal topography (dotted contours with fractal dimension [162]). Wildfire: Burned areas and vegetation represented in red and green, respectively, following the rules of the Forest Fire model.
Figure 6.
Examples of hazard intensity footprints based on analytical expressions (first two columns, Section 2.4.1), threshold models (central column, Section 2.4.2), and numerical models (last two columns, Section 2.4.3). DIFFUSION (POINT SOURCES)—Explosion (incl. asteroid impact): overpressure field for an ad-hoc Mton event (Equation (30)) with a 4-psi dashed contour in grey and matching 4-psi contour from Equation (28) in purple. Volcanic eruption: Ash depth map for a km3 (e.g., 1980, Mt St. Helens) and m event (Equation (33)) with a 5-cm dashed contour in orange. DIFFUSION (LINE SOURCES)—Earthquake: Peak ground acceleration footprint of an event on the ESHM13 fault segment ITCS073 with depth km (Equation 29) and a dashed 0.1-g contour in dark orange. DIFFUSION (TRACK SOURCES)—Tropical cyclone: Windspeed map for the IBTrACS 2005 Hurricane Katrina track (Equation (32) with mb and [161]) with a dashed 35-m/s wind speed contour in dark blue. THRESHOLD (AREA SOURCE)—Heatwave: Temperature map of Southwestern France at 3 pm on 17 July 2022 [44] with a dashed 35°-contour in dark magenta as (ad-hoc) proxy to the heatwave. THRESHOLD (LINE SOURCE)—Storm surge: Inundation map on a random topography (with fractal dimension [162]) with dashed 0-m altitude level as a coastline marker. DYNAMIC PROPAGATION (DIFFUSE SOURCES)—Blackout: Ring network with each node (power node or transmission line) connected to four others and with grey nodes as failed (i.e., blackout) following the rules of Equations (39) and (40). Epidemic: Infected and susceptible individuals colored in red and green, respectively, following the rules of Equation (42). Landslide: Event footprint formed of several patches, following the rules of Equations (43) and (44), on a random fractal topography (dotted contours with fractal dimension [162]). Wildfire: Burned areas and vegetation represented in red and green, respectively, following the rules of the Forest Fire model.
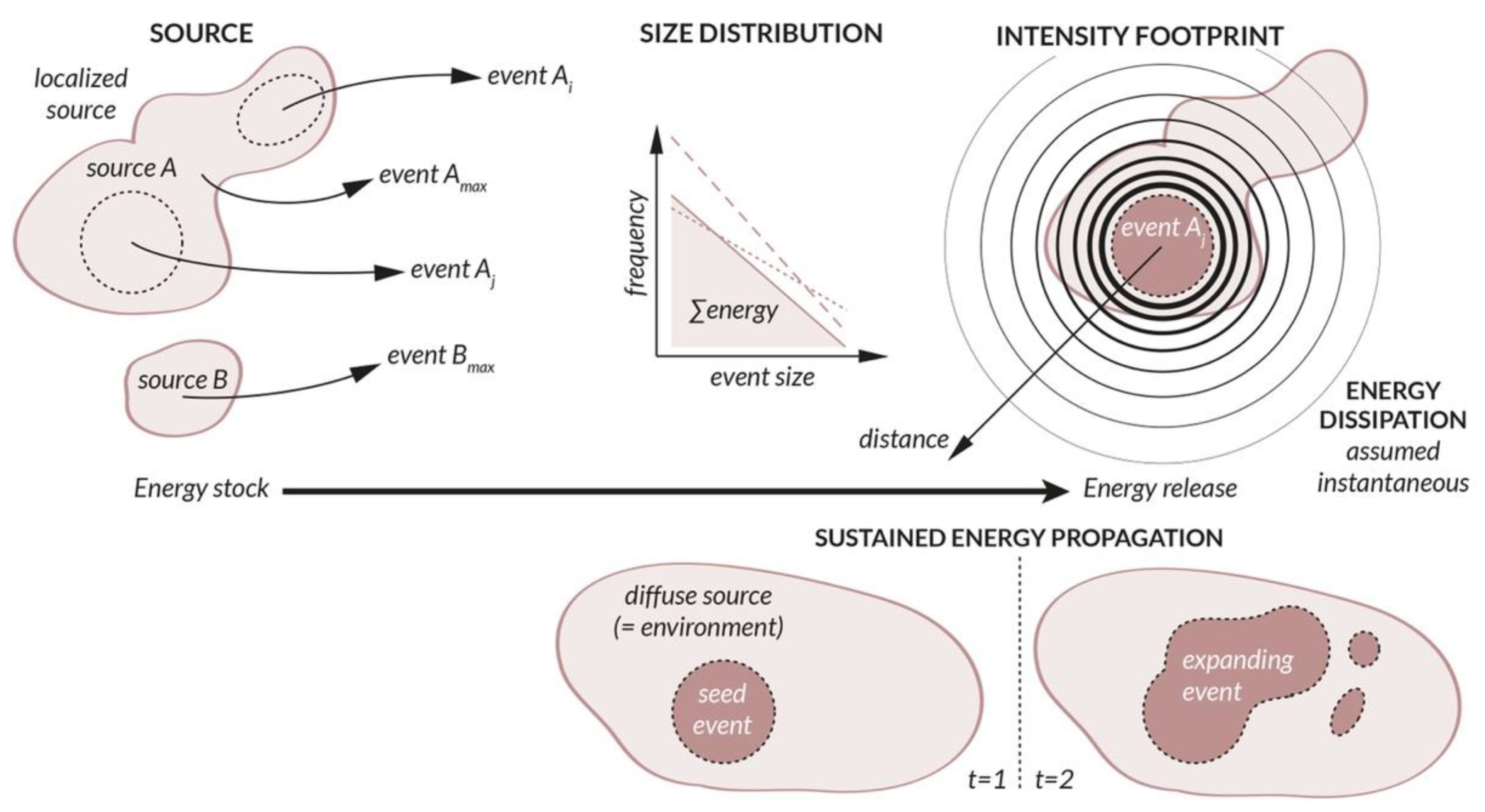
3. Peril Harmonization via the Concept of Energy Transfer
The present review illustrated the heterogeneity of the physical processes involved in the occurrence of different perils (e.g., Figure 6). Although they can be grouped by source type (Section 2.2), size distribution type (Section 2.3), and intensity footprint type (Section 2.4), event size metrics are not intelligibly exchangeable. An obvious choice for a common size measure is the energy being released by an event [163,164]. We can indeed describe the hazard process in terms of energy transfer, as illustrated in Figure 7 (note that power could be another option). Following the hazard pipeline of standard CAT modeling, the source represents the energy stock, the size distribution indicates how energy is released via the emergence of events, and the intensity footprint characterizes how energy dissipates in the environment. For a localized source, the energy released can only diffuse in space from the region of high energy concentration that is the source to the surrounding environment. For a diffuse source, the energy released by the initial event (or seed event) can transfer to the environment, which acts as a continuous energy stock promoting sustained energy propagation. In this case, event size and intensity footprint are virtually indistinguishable. Nonlinear dissipative systems are known to release energy sporadically by following a power-law size distribution (Figure 5). This is a property of systems in the state of self-organized criticality, which is exemplified in the Sandpile CA [132] and believed to occur for many perils [154,165,166].
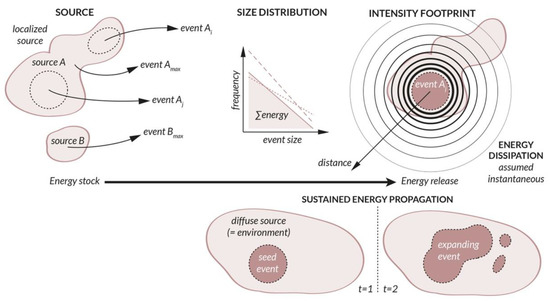
Figure 7.
Sketch describing the hazard process in terms of energy transfer, applicable to any peril. See text for details.
Johnston [164] devised a ranking of selected historical events using energy as a common metric, comparing past earthquakes, volcanic eruptions, tropical cyclones, tornadoes, landslides, and nuclear explosions, as well as a lightning bolt on the low-energy side and a hypothetical 10-km asteroid impact on the high-energy side. Despite the importance of such a comparison, this work has only been cited 10 times over the past 30 years (August 2022 Google Scholar search), suggesting that peril harmonization via energy has yet to be addressed.
Energy can take many forms, which can all be categorized as kinetic energy (motion) or potential energy (stored). Kinetic energy includes radiant (electromagnetic) energy, thermal (heat) energy, motion energy, wave energy, and electrical energy. Potential energy includes chemical energy, mechanical energy, nuclear energy, and gravitational energy. For natural perils, and some man-made ones, damage is due to destructive energy. However, for some man-made perils, the damage can be a lack of energy that is needed for the functioning of society [167], since energy is fundamentally the ability to work. The energy transforms from when it is stored in an event source to when it is released in the environment, with part of the original energy always converted to heat. Table 1 lists the perils considered in this study and the main energy form(s) they take. This is indicative in nature, as a review of the proportion of energy types per peril is outside the scope of the present invited article. For example, for asteroid impacts, a thermal radiation model can be coupled to the blast model [34], consistent with models of nuclear explosions [118]. For floods, both water height (potential energy) and flow velocity (kinetic energy) lead to damage, which can be combined with the formula [168]. For volcanic eruptions, thermal energy depends on mass erupted, which is proportional to the volume [64], etc.


Table 1.
Energy types per peril (indicative only, non-exhaustive).
Table 1.
Energy types per peril (indicative only, non-exhaustive).
| Peril | Event Size (Section 2.2) → Intensity (Section 2.4) | Matching Energy Types |
|---|---|---|
| Armed conflicts | Various, so far aggregated in terms of loss (Equation (38)) | Various, aggregation TBD 1 |
| Asteroid impacts | Kinetic energy (Equation (2)) → overpressure (Equation (28)) | Motion → wave (air) (+radiant, thermal) |
| Blackouts | E.g., unsupplied electrical energy (Equation (40)) | Electrical (lack of) |
| Business interruption | Revenue loss | Work done (lack of) |
| Crop failures | So far in terms of farming production yield loss (Equation (41)) | Chemical (food) (lack of) |
| Cyber-attacks | E.g., number of data breaches | Stored information (lack of) |
| Earthquakes | Magnitude (Equations (7) and (8)) → PGA (Equation (29)) | Mechanical (elastic) → wave (seismic) |
| Epidemics | Infection count (Equation (42)) | TBD 1 |
| Explosions (nuclear) | Explosive yield (Equation (4)) → overpressure (Equation (30)) | Nuclear → wave (air) (+radiant, thermal) |
| Explosions (other) | TNT mass (Equation (3)) → overpressure (Equation (30)) | Chemical → wave (air) (+thermal) |
| Floods | Discharge (Equations (5) and (37)) → water depth | Motion + gravitational → gravitational (+motion) |
| Hail | Hailstone diameter → kinetic energy (Equation (35)) | Gravitational → motion |
| Heatwaves | Temperature | Thermal |
| Landslides | Area or volume → soil height | Gravitational → gravitational (+motion) |
| Social unrest | Number of violent individuals as possible proxy | Various (thermal via arson, mechanical) |
| Storms | Windspeed (Equation (12)) → Equation (32)) | Motion (+water latent heat) → motion |
| Tsunamis | Potential energy (Equation (10)) → Water height | Gravitational → wave (water) (+motion) |
| Volcanic eruptions | Erupted volume → ash depth (Equation (33)) | Thermal → gravitational (+thermal) |
| Wildfires (incl. urban) | Burnt area | Thermal (+radiant) |
1 Debatable when size and/or intensity are defined in terms of human losses—see text below for a discussion.
Human losses may be used to describe the size and/or intensity of an event, for example the number of people infected in an epidemic (which is proportional to fatalities in the risk component of a CAT model). Heterogeneous types of destructive energy in armed conflicts, terrorism, and social unrest are also aggregated in terms of human losses in practice. Relating human loss to energy is, however, tricky. The metabolic heat of a resting human body could represent the lower bound of the energy loss (~100 W of power × lifespan [129]). If individuals are considered as workers in a society, their loss could be defined in terms of lack of work related to muscle power or to their amplified power by machines [169]. Their role may not be actual physical work but intellectual work, with a connection to be made between information (as entropy) and energy [169,170]. Note that an information-based metric could also be used to describe energy loss in a cyber-attack (Table 1). A life has obviously far more value, which might also be related to information content, such as memories defining part of an individual’s identity and character. These considerations significantly stretch the idea of using energy as a simple metric to compare different perils, but they are worth pointing out.
We already defined event size or hazard intensity in terms of energy for several perils (see Equations (2)–(4), (10) and (35) and Table 1). A dimensional analysis shows how different physical parameters of a hazard process can be combined to define or in terms of energy, which has dimension [M1L2T−2]. Ref. [79] did so for hurricanes, considering power instead of energy. Ref. [72] reviewed methods to assess the energy released by tsunamis and used dimensional analysis to calculate their power. For wildfires, the Stefan–Boltzmann constant shows that it must be multiplied by burning area and the fourth power of temperature, , to connect to a radiative energy measure [171]. The reader can do such an analysis for many of the perils physically described in this review. Although the standard International System of Units for energy is the Joule, it is convenient for catastrophes to instead use the explosive power equivalent to one ton of TNT (trinitrotoluene) (e.g., Equation (3)), which converts to about Joules.
4. Conclusions
This review is the first to consider so many perils while providing all the equations necessary for basic hazard assessment in the context of CAT risk modeling. By categorizing perils per event source type (Section 2.2), size distribution (Section 2.3), and intensity footprint modeling strategy (Section 2.4), we were able to describe a heterogeneous collection of physical and environmental processes within a common scheme. Different perils can now be considered different flavors of what we may refer to as the catastrophe object (Figure 7). This ontological analysis shall help with the development of CAT modeling as a distinct scientific discipline [4]. By describing any peril in terms of event size , size distribution , and intensity footprint , peril-specific jargon and methods can be minimized, and silo effects hence reduced. It should also facilitate the implementation of emergent risks by directly following the CAT modeling paradigm.
One of the main goals of this study was to describe as many perils as possible, but some are still missing. Those include droughts, toxic release, and financial crises among others. They could, however, be implemented within the proposed classification strategy in the future. Although most of the presented models remain very simple, they can be used as a basis for the development of more sophisticated and more realistic models. These hazard pipeline templates should help the student of risk to create new CAT models from the fundamental concepts and laws of CAT risk science. This study has also the potential to foster multi-risk modeling [172,173]. Ready-made models for basic hazard assessment indeed provide the inputs necessary to implement more peril interactions than are usually performed. In regard to global warming, the availability of simple models for many climate-related perils should also facilitate the implementation of more of them in climate risk modeling frameworks [16,174] and related system dynamics models [175]. Since global warming means more energy being transferred into the atmosphere, our approach of peril harmonization via the concept of energy transfer remains fully valid. Overall, the results of this review will be helpful for the prototyping of more complex risk problems.
Funding
This research was mainly funded by the National Natural Science Foundation of China, grant number 42074054, and was also supported in part by the Shenzhen Science and Technology Innovation Commission, grant number GJHZ20210705141805017.
Institutional Review Board Statement
Not applicable.
Informed Consent Statement
Not applicable.
Data Availability Statement
All the data used in this study are publicly available, or otherwise available upon request from their authors (as per the given references).
Acknowledgments
The author thanks three anonymous reviewers for their valuable comments.
Conflicts of Interest
The author declares no conflict of interest.
Appendix A

Table A1.
List of symbols used in the present article.
Table A1.
List of symbols used in the present article.
| Symbol | Dimension | Description |
|---|---|---|
| various | Productivity parameter of the power-law | |
| [L2] | Area | |
| [1] | Power-law exponent in cumulative form () | |
| [1] | Holland parameter for tropical cyclones | |
| [1] | Empirical parameter, scaling factor | |
| [ML−1T−2] | Soil cohesion | |
| [L] | Distance | |
| [1] | Damage, e.g., mean damage ratio | |
| [1] | Euler’s number () | |
| [ML2T−2] | Energy | |
| - | Damage function | |
| - | Intensity function | |
| - | Frequency function | |
| [1] | Factor of safety for landslides | |
| [LT−2] | Gravitational acceleration ( m/s2) | |
| [L] | Height, depth | |
| various | Intensity of event | |
| [L] | Length, diameter | |
| various | Loss (e.g., economic, human) | |
| [M] | Mass | |
| [1] | Magnitude of earthquake | |
| [ML2T−2] | Seismic moment | |
| [1] | Number, count | |
| [ML−1T−2] | Pressure, overpressure | |
| [1] | Probability (non-cumulative, cumulative) | |
| [L3T−1] | Water discharge | |
| [L] | Radius, radial distance | |
| [1] | Epidemic basic reproduction number | |
| various | Size of event | |
| [T] | Time increment | |
| [Q] | Temperature | |
| [L] | Displacement | |
| [LT−1] | Velocity | |
| [L3] | Volume | |
| [L] | Width | |
| [L] | Geographical coordinates | |
| various | Random variable | |
| various | Electricity load | |
| [1] | Power-law exponent () | |
| [T−1] | Infectious disease transmission parameter | |
| [L] | Thickness | |
| [L2T−2] | Heat of combustion | |
| [T] | Return period, time interval | |
| [1] | Eccentricity | |
| [1] | in GPD | |
| [1] | Fraction, ratio | |
| various | Parameter set | |
| [T−1] | Rate of occurrence | |
| various | GEV and GPD location parameter | |
| [1] | GEV and GPD shape parameter | |
| [ML−3] | Density | |
| various | GEV and GPD scale parameter | |
| [T] | Time | |
| [1] | Angle | |
| various | Characteristics of an agent | |
| - | State of an agent | |
| various | Threshold |

Table A2.
Color scheme per peril category.
Table A2.
Color scheme per peril category.
| Color | Category | Perils |
|---|---|---|
| ■ | Climatological | Heatwave |
| ■/■1 | Ecological | Crop failure, epidemic, wildfire |
| ■ | Extraterrestrial | Asteroid and comet impact |
| ■ | Geophysical | Earthquake, landslide, volcanic eruption |
| ■ | Hydrological | River flood, storm surge, tsunami |
| ■ | Meteorological | Convective storm (incl. hail, tornado, lightning), (extra-)tropical cyclone, other storms |
| ■ | Socio-economic | Armed conflict, social unrest, terrorism |
| ■ | Technological | Blackout, cyber-attack, explosion, fire |
1. For footprints, ecological environment in dark olive green and active footprint in red (see Figure 6).
References
- Friedman, D.G. Natural Hazard Risk Assessment for an Insurance Program. Geneva Pap. Risk Insur. 1984, 9, 57–128. [Google Scholar] [CrossRef]
- Grossi, P.; Kunreuther, H.; Patel, C.C. Catastrophe Modeling: A New Approach to Managing Risk; Springer: Boston, MA, USA, 2005. [Google Scholar]
- Smolka, A. Natural disasters and the challenge of extreme events: Risk management from an insurance perspective. Phil. Trans. R. Soc. A 2006, 364, 2147–2165. [Google Scholar] [CrossRef] [PubMed]
- Mitchell-Wallace, K.; Jones, M.; Hillier, J.; Foote, M. Natural Catastrophe Risk Management and Modelling, A Practitioner’s Guide; John Wiley & Sons Ltd.: Chichester, UK, 2017. [Google Scholar]
- Crichton, D. The Risk Triangle. In Natural Disaster Management; Ingleton, J., Ed.; Tudor Rose: London, UK, 1999; pp. 102–103. [Google Scholar]
- Mailier, P.J.; Stephenson, D.B.; Ferro, C.A.T. Serial Clustering of Extratropical Cyclones. Mon. Weather Rev. 2006, 134, 2224–2240. [Google Scholar] [CrossRef]
- Matos, J.P.; Mignan, A.; Schleiss, A.J. Vulnerability of large dams considering hazard interactions, Conceptual application of the Generic Multi-Risk framework. In Proceedings of the 13th ICOLD Benchmark Workshop on the Numerical Analysis of Dams, Lausanne, Switzerland, 9–11 September 2015. [Google Scholar]
- Mignan, A.; Danciu, L.; Giardini, D. Considering large earthquake clustering in seismic risk analysis. Nat. Hazards 2018, 91, S149–S172. [Google Scholar] [CrossRef]
- Douglas, J. Physical vulnerability modelling in natural hazard risk assessment. Nat. Hazards Earth Syst. Sci. 2007, 7, 283–288. [Google Scholar] [CrossRef]
- Grünthal, G.; Thieken, A.H.; Schwarz, J.; Radtke, K.S.; Smolka, A.; Merz, B. Comparative Risk Assessments for the City of Cologne—Storms, Floods, Earthquakes. Nat. Hazards 2006, 38, 21–44. [Google Scholar] [CrossRef]
- Schneider, P.J.; Schauer, B.A. HAZUS—Its Development and Ist Future. Nat. Haz. Rev. 2006, 7, 40–44. [Google Scholar] [CrossRef]
- Schmidt, J.; Matcham, I.; Reese, S.; King, A.; Bell, R.; Henderson, R.; Smart, G.; Cousins, J.; Smith, W.; Heron, D. Quantitative multi-risk analysis for natural hazards: A framework for multi-risk modelling. Nat. Hazards 2011, 58, 1169–1192. [Google Scholar] [CrossRef]
- Cardona, O.D.; Ordaz, M.G.; Yamin, L.E.; Marulanda, M.C.; Barbat, A.H. Earthquake Loss Assessment for Integrated Disaster Risk Management. J. Earthq. Eng. 2008, 12 (Suppl. S2), 48–59. [Google Scholar] [CrossRef]
- Tseng, C.-P.; Chen, C.-W. Natural disaster management mechanisms for probabilistic earthquake loss. Nat. Hazards 2012, 60, 1055–1063. [Google Scholar] [CrossRef]
- Vickery, P.J.; Masters, F.J.; Powell, M.D.; Wadhera, D. Hurricane hazard modeling: The past, present, and future. J. Wind Eng. Ind. Aerodyn. 2009, 97, 392–405. [Google Scholar] [CrossRef]
- Aznar-Signan, G.; Bresch, D.N. CLIMADA v1: A global weather and climate risk assessment platform. Geosci. Model Dev. 2019, 12, 3085–3097. [Google Scholar] [CrossRef]
- Ermolieva, T.; Filatova, T.; Ermoliev, Y.; Obersteiner, M.; de Bruijn, K.M.; Jenken, A. Flood Catastrophe Model for Designing Optimal Flood Insurance Program: Estimating Location-Specific Premiums in the Netherlands. Risk Anal. 2017, 37, 82–98. [Google Scholar] [CrossRef]
- Palán, L.; Matyás, M.; Válková, M.; Kovacka, V.; Pazourková, E.; Puncochár, P. Accessing Insurance Flood Losses Using a Catastrophe Model and Climate Change Scenarios. Climate 2022, 10, 67. [Google Scholar] [CrossRef]
- Hohl, R.; Schiesser, H.-H.; Knepper, I. The use of weather radars to estimate hail damage to automobiles: An exploratory study in Switzerland. Atmos. Res. 2002, 61, 215–238. [Google Scholar] [CrossRef]
- Romanic, D.; Refan, M.; Wu, C.-H.; Michel, G. Oklahoma tornado risk and variability: A statistical model. Int. J. Disaster Risk Reduct. 2016, 16, 19–32. [Google Scholar] [CrossRef]
- Eling, M.; Schnell, W. What do we know about cyber risk and cyber risk insurance? J. Risk Financ. 2016, 17, 474–491. [Google Scholar] [CrossRef]
- Coburn, A.; Leverett, E.; Woo, G. Solving Cyber Risk; John Wiley & Sons: Hoboken, NJ, USA, 2019. [Google Scholar]
- Fullam, D.; Madhav, N. Quantifying Pandemic Risk. Actuar. Mag. 2015, 12, 29–34. [Google Scholar]
- Smith, D. Pandemic Risk Modelling. In The Palgrave Handbook of Unconventional Risk Transfer; Pompella, M., Scordis, N.A., Eds.; Palgrave Macmillan Cham: London, UK, 2017; pp. 463–495. [Google Scholar]
- Woo, G. Quantitative Terrorism Risk Assessment. J. Risk Financ. 2002, 4, 7–14. [Google Scholar] [CrossRef]
- Kunreuther, H.; Michel-Kerjan, E.; Porter, B. Chapter 10—Extending Catastrophe Modeling To Terrorism. In Catastrophe Modeling: A New Approach to Managing Risk; Grossi, P., Kunreuther, H., Patel, C.C., Eds.; Springer: Boston, MA, USA, 2005; pp. 209–233. [Google Scholar]
- Murnane, R.J. Catastrophe Risk Models for Wildfires in the Wildland-Urban Interface: What Insurers Need. Nat. Hazards Rev. 2006, 7, 150–156. [Google Scholar] [CrossRef]
- Lee, S.; Davidson, R.; Ohnishi, N.; Scawthorn, C. Fire Following Earthquake—Reviewing the State-of-the-Art of Modeling. Earthq. Spectra 2008, 24, 933–967. [Google Scholar] [CrossRef]
- Muir-Wood, R.; Drayton, M.; Berger, A.; Burgess, P.; Wright, T. Catastrophe loss modelling of storm-surge flood risk in eastern England. Phil. Trans. R. Soc. A 2005, 363, 1407–1422. [Google Scholar] [CrossRef] [PubMed]
- Rose, A.; Huyck, C.K. Improving Catastrophe Modeling for Business Interruption Insurance Needs. Risk Anal. 2016, 36, 1896–1915. [Google Scholar] [CrossRef] [PubMed]
- Tomlinson, C.J.; Chapman, L.; Thornes, J.E.; Baker, C.J. Including the urban heat island in spatial heat health risk assessment strategies: A case study for Birmingham, UK. Int. J. Health Geogr. 2011, 10, 42. [Google Scholar] [CrossRef]
- Tonnang, H.E.; Hervé, B.D.; Biber-Freudenberger, L.; Salifu, D.; Subramanian, S.; Ngowi, V.B.; Guimapi, R.Y.; Anani, B.; Kakmeni, F.M.; Affognon, H.; et al. Advances in crop insect modelling methods—Towards a whole system approach. Ecol. Model. 2017, 354, 88–103. [Google Scholar] [CrossRef]
- Mignan, A.; Grossi, P.; Muir-Wood, R. Risk assessment of Tunguska-type airbursts. Nat. Hazards 2011, 56, 869–880. [Google Scholar] [CrossRef][Green Version]
- Mathias, D.L.; Wheeler, L.F.; Dotson, J.L. A probabilistic asteroid impact risk model: Assessment of sub-300 m impacts. Icarus 2017, 289, 106–119. [Google Scholar] [CrossRef]
- Epstein, J.M. Modeling civil violence: An agent-based computational approach. Proc. Natl. Acad. Sci. USA 2002, 99, 7243–7250. [Google Scholar] [CrossRef]
- Kress, M. Modeling Armed Conflicts. Science 2012, 336, 865–869. [Google Scholar] [CrossRef]
- Beck, U. The Terrorist Threat, World Risk Society Revisited. Theory Cult. Soc. 2002, 19, 39–55. [Google Scholar] [CrossRef]
- Center for Near Earth Object Studies, Fireball and Bolide Data. Available online: https://cneos.jpl.nasa.gov/fireballs/ (accessed on 31 August 2022).
- Clauset, A.; Shalizi, C.R.; Newman, M.E.J. Power-Law Distributions in Empirical Data. SIAM Rev. 2009, 51, 661–703. [Google Scholar] [CrossRef]
- Privacy Rights, Data Breaches. Available online: https://privacyrights.org/data-breaches (accessed on 31 August 2022).
- Storchak, D.A.; Di Giacomo, D.; Bondár, I.; Engdahl, E.R.; Harris, J.; Lee, W.H.K.; Villasenor, A.; Bormann, P. Public Release of the ISC-GEM Global Instrumental Earthquake Catalogue (1900-2009). Seismol. Res. Lett. 2013, 84, 810–815. [Google Scholar] [CrossRef]
- Woessner, J.; The SHARE Consortium; Laurentiu, D.; Giardini, D.; Crowley, H.; Cotton, F.; Grünthal, G.; Valensise, G.; Arvidsson, R.; Basili, R.; et al. The 2013 European Seismic Hazard Model: Key components and results. Bull. Earthq. Eng. 2015, 13, 3553–3596. [Google Scholar] [CrossRef]
- Marani, M.; Katul, G.G.; Pan, W.K.; Parolari, A.J. Intensity and frequency of extreme novel epidemics. Proc. Natl. Acad. Sci. USA 2021, 118, e2105482118. [Google Scholar] [CrossRef]
- Météo-France, Données Publiques. Available online: https://donneespubliques.meteofrance.fr/ (accessed on 31 August 2022).
- Li, G.; West, A.J.; Densmore, A.L.; Jin, Z.; Parker, R.N.; Hilton, R.G. Seismic mountain building: Landslides associated with the 2008 Wenchuan earthquake in the context of a generalized model for earthquake volume balance. Geochem. Geophys. Geosyst. 2014, 15, 833–844. [Google Scholar] [CrossRef]
- Smith, J.A. Estimating the Upper Tail of Flood Frequency Distributions. Water Resour. Res. 1987, 23, 1657–1666. [Google Scholar] [CrossRef]
- Clauset, A.; Young, M.; Gleditsch, K.S. On the Frequency of Severe Terrorist Events. J. Confl. Resolut. 2007, 51, 58–87. [Google Scholar] [CrossRef]
- Knapp, K.R.; Kruk, M.C.; Levinson, D.H.; Diamond, H.J.; Neumann, C.J. The International Best Track Archive for Climate Stewardship (IBTrACS), Unifying Tropical Cyclone Data. Bull. Am. Meteo. Soc. 2010, 91, 363–376. [Google Scholar] [CrossRef]
- National Geophysical Data Center / World Data Service: NCEI/WDS Global Historical Tsunami Database. In NOAA National Centers for Environmental Information. Available online: https://www.ngdc.noaa.gov/hazard/tsu_db.shtml (accessed on 31 August 2022). [CrossRef]
- Crosweller, H.S.; Arora, B.; Brown, S.; Cottrell, E.; Deligne, N.; Guerrero, N.O.; Hobbs, L.; Kiyosugi, K.; Loughlin, S.; Lowndes, J.; et al. Global database on large magnitude explosive volcanic eruptions (LaMEVE). J. Appl. Volc. 2012, 1, 4. [Google Scholar] [CrossRef]
- Laurent, P.; Mouillot, F.; Yue, C.; Ciais, P.; Moreno, M.V.; Nogueira, J.M.P. Data Descriptor: FRY, a global database of fire patch functional traits derived from space-borne burned area products. Sci. Data 2018, 5, 180132. [Google Scholar] [CrossRef]
- Hills, J.G.; Goda, M.P. The Fragmentation of Small Asteroids in the Atmosphere. Astron. J. 1993, 105, 1114–1144. [Google Scholar] [CrossRef]
- Bland, P.A.; Artemieva, N.A. The rate of small impacts on Earth. Meteorit. Planet. Sci. 2006, 41, 607–631. [Google Scholar] [CrossRef]
- Maremonti, M.; Russo, G.; Salzano, E.; Tufano, V. Post-Accident Analysis of Vapour Cloud Explosions in Fuel Storage Areas. Trans. IChemE 1999, 77, 360–365. [Google Scholar] [CrossRef]
- Ottemöller, L.; Evers, L.G. Seismo-acoustic analysis of the Buncefield oil depot explosion in the UK, 2005 December 11. Geophys. J. Int. 2008, 172, 1123–1134. [Google Scholar] [CrossRef]
- Abbasi, T.; Abbasi, S.A. The boiling liquid expanding vapour explosion (BLEVE): Mechanism, consequence assessment, management. J. Hazard. Mater. 2007, 141, 489–519. [Google Scholar] [CrossRef]
- Alileche, N.; Cozzani, V.; Reniers, G.; Estel, L. Thresholds for domino effects and safety distances in the process industry: A review of approaches and regulations. Reliab. Eng. Syst. Saf. 2015, 143, 74–84. [Google Scholar] [CrossRef]
- Mignan, A.; Spada, M.; Burgherr, P.; Wang, Z.; Sornette, D. Dynamics of severe accidents in the oil & gas energy sector derived from the authoritative Energy-related severe accident database. PLoS ONE 2022, 17, e0263962. [Google Scholar]
- Reed, B.C. A toy model for the yield of a tamped fission bomb. Am. J. Phys. 2018, 86, 105–109. [Google Scholar] [CrossRef]
- Grimaldi, S.; Petroselli, A. Do we still need the Rational Formula? An alternative empirical procedure for peak discharge estimation in small and ungauged basins. Hydrol. Sci. J. 2015, 60, 67–77. [Google Scholar] [CrossRef]
- Gericke, O.J.; Smithers, J.C. Review of methods used to estimate catchment response time for the purpose of peak discharge estimation. Hydrol. Sci. J. 2014, 59, 1935–1971. [Google Scholar] [CrossRef]
- Meigh, J.R.; Farquharson, F.A.K.; Sutcliffe, J.V. A worldwide comparison of regional flood estimation methods and climate. Hydrol. Sci. J. 1997, 42, 225–244. [Google Scholar] [CrossRef]
- Newhall, C.G.; Self, S. The Volcanic Explosivity Index (VEI): An Estimate of Explosive Magnitude for Historical Volcanism. J. Geophys. Res. 1982, 87, 1231–1238. [Google Scholar] [CrossRef]
- Pyle, D.M. Mass and energy budgets of explosive volcanic eruptions. Geophys. Res. Lett. 1995, 22, 563–566. [Google Scholar] [CrossRef]
- Hanks, T.C.; Kanamori, H. A Moment Magnitude Scale. J. Geophys. Res. 1979, 84, 2348–2350. [Google Scholar] [CrossRef]
- Wells, D.L.; Coppersmith, K.J. New Empirical Relationships among Magnitude, Rupture Length, Rupture Width, Rupture Area, and Surface Displacement. Bull. Seismol. Soc. Am. 1994, 84, 974–1002. [Google Scholar]
- Lin, N.; Emanuel, K.A.; Smith, J.A.; Vanmarcke, E. Risk assessment of hurricane storm surge for New York City. J. Geophys. Res. 2010, 115, D18121. [Google Scholar] [CrossRef]
- Camelo, J.; Mayo, T. The lasting impacts of the Saffir-Simpson Hurricane Wind Scale on storm surge risk communication: The need for multidisciplinary research in addressing a multidisciplinary challenge. Weather Clim. Extrem. 2021, 33, 100335. [Google Scholar] [CrossRef]
- Edwards, R.; DaDue, J.G.; Ferree, J.T.; Scharfenberg, K.; Maier, C.; Coulbourne, W.L. Tornado Intensity Estimation, Past, Present, and Future. Bull. Am. Meteo. Soc. 2013, 94, 641–653. [Google Scholar] [CrossRef]
- Standohar-Alfano, C.D.; van de Lindt, J.W. Empirically Based Probabilistic Tornado Hazard Analysis of the United States Using 1973–2011 Data. Nat. Hazards Rev. 2015, 16, 04014013. [Google Scholar] [CrossRef]
- Halif, M.N.A.; Sabki, S.N. The Physics of Tsunami: Basic understanding of the Indian Ocean disaster. Am. J. Appl. Sci. 2005, 2, 1188–1193. [Google Scholar] [CrossRef]
- Ghasemi, S. Study of Tsunamis by Dimensional Analysis. Engineering 2011, 3, 905–910. [Google Scholar] [CrossRef]
- Rigby, S.E.; Lodge, T.J.; Alotaibi, S.; Barr, A.D.; Clarke, S.D.; Langdon, G.S.; Tyas, A. Preliminary yield estimation of the 2020 Beirut explosion using video footage from social media. Shock Waves 2020, 30, 671–675. [Google Scholar] [CrossRef]
- Hering, A.M.; Germann, U.; Boscacci, M.; Sénési, S. Operational nowcasting of thunderstorms in the Alps during MAP D-PHASE. In Proceedings of the 5th European Conference on Radar in Meteorology and Hydrology, Helsinki, Finland, 30 June–4 July 2008. [Google Scholar]
- Rothermal, R.C. Predicting Fire Spread in Wildland Fuels. USDA For. Serv. Res. Pap. 1972, INT-115, 1–40. [Google Scholar]
- Trunfio, G.A. Predicting Wildfire Spreading Through a Hexagonal Cellular Automata Model. In ACRI 2004, LNCS 3305; Sloot, P.M.A., Chopard, B., Hoekstra, A.G., Eds.; Springer: Berlin, Germany, 2004; pp. 385–394. [Google Scholar]
- Bloemendaal, N.; Haigh, I.D.; de Moel, H.; Muis, S.; Haarsma, R.J.; Aerts, J.C.J.H. Generation of a global synthetic tropical cyclone hazard dataset using STORM. Sci. Data 2020, 7, 40. [Google Scholar] [CrossRef]
- Holland, G.J. An Analytic Model of the Wind and Pressure Profiles in Hurricanes. Mon. Weather Rev. 1982, 108, 1212–1218. [Google Scholar] [CrossRef]
- Emanuel, K.A. The power of a hurricane: An example of reckless driving on the information superhighway. Weather 1998, 54, 107–108. [Google Scholar] [CrossRef]
- Andersson, G.; Donalek, P.; Farmer, R.; Hatziargyriou, N.; Kamwa, I.; Kundur, N.; Martins, J.; Paserba, P.; Pourbeik, J.; Sanchez-Gasca, R.; et al. Causes of the 2003 Major Grid Blackouts in North America and Europe, and Recommended Means to Improve System Dynamic Performance. IEEE Trans. Power Syst. 2005, 20, 1922–1928. [Google Scholar] [CrossRef]
- Crosta, G. Regionalization of rainfall thresholds: An aid to landslide hazard evaluation. Env. Geol. 1998, 35, 131–145. [Google Scholar] [CrossRef]
- Iverson, R.M. Landslide triggering by rain infiltration. Water Res. Res. 2000, 36, 1897–1910. [Google Scholar] [CrossRef]
- Jibson, R.W. Predicting Earthquake-Induced Landslide Displacements Using Newmark’s Sliding Block Analysis. Transp. Res. Rec. 1993, 1411, 9–17. [Google Scholar]
- McPhail, C.; Wohlstein, R.T. Individual and Collective Behaviors within Gatherings, Demonstrations, and Riots. Ann. Rev. Sociol. 1983, 9, 579–600. [Google Scholar] [CrossRef]
- Atiyeh, B.S.; Gunn, S.W.A.; Hayek, S.N. Military and civilian burn injuries during armed conflicts. Ann. Burn. Fire Disasters 2007, XX, 203–215. [Google Scholar]
- Syphard, A.D.; Keeley, J.E. Location, timing and extent of wildfire vary by cause of ignition. Int. J. Wildland Fire 2015, 24, 37–47. [Google Scholar] [CrossRef]
- Krause, A.; Kloster, S.; Wilkenskjeld, S.; Paeth, H. The sensitivity of global wildfires to simulated past, present, and future lightning frequency. J. Geophys. Res. Biogeosci. 2014, 119, 312–322. [Google Scholar] [CrossRef]
- Price, C.; Rind, D. A Simple Lightning Parameterization for Calculating Global Lightning Distributions. J. Geophys. Res. 1992, 97, 9919–9933. [Google Scholar] [CrossRef]
- Littell, J.S.; Peterson, D.L.; Riley, K.L.; Liu, Y.; Luce, C.H. A review of the relationships between drought and forest fire in the United States. Glob. Chang. Biol. 2016, 22, 2353–2369. [Google Scholar] [CrossRef]
- Molina, J.R.; Martín, T.; Silva, F.R.Y.; Herrera, M.Á. The ignition index based on flammability of vegetation improves planning in the wildland-urban interface: A case study in Southern Spain. Landsc. Urban Plan. 2017, 158, 129–138. [Google Scholar] [CrossRef]
- Newman, M.E.J. Power laws, Pareto distributions and Zipf’s law. Contemp. Phys. 2005, 46, 323–351. [Google Scholar] [CrossRef]
- Corral, Á.; González, Á. Power law size distributions in geoscience revisited. Earth Space Sci. 2019, 6, 673–697. [Google Scholar] [CrossRef]
- Coles, S. An Introduction to Statistical Modeling of Extreme Values; Springer: London, UK, 2001. [Google Scholar]
- Harris, I. Generalised Pareto methods for wind extremes. Useful tool or mathematical mirage? J. Wind Eng. 2005, 93, 341–360. [Google Scholar] [CrossRef]
- Malamud, B.D.; Turcotte, D.L. The applicability of power-law frequency statistics to floods. J. Hydro. 2006, 322, 168–180. [Google Scholar] [CrossRef]
- Chen, L.; Guo, S. Copulas and Its Applications in Hydrology and Water Resources; Springer Nature: Singapore, 2019. [Google Scholar]
- Richardson, L.F. Variation of the Frequency of Fatal Quarrels With Magnitude. J. Am. Stat. Assoc. 1948, 43, 523–546. [Google Scholar] [CrossRef]
- Cederman, L.-E. Modeling the Size of Wars: From Billiard Balls to Sandpiles. Am. Political Sci. Rev. 2003, 97, 135–150. [Google Scholar] [CrossRef]
- Brown, P.; Spalding, R.E.; ReVelle, D.O.; Tagliaferri, E.; Worden, S.P. The flux of small near-Earth objects colliding with the Earth. Nature 2002, 420, 294–296. [Google Scholar] [CrossRef]
- Dobson, I.; Carreras, B.A.; Lynch, V.E.; Newman, D.E. Complex systems analysis of series of blackouts: Cascading failure, critical points, and self-organization. Chaos 2007, 17, 026103. [Google Scholar] [CrossRef]
- Maillart, T.; Sornette, D. Heavy-tailed distribution of cyber-risks. Eur. Phys. J. B 2010, 75, 357–364. [Google Scholar] [CrossRef]
- Utsu, T. Representation and Analysis of the Earthquake Size Distribution: A Historical Review and Some New Approaches. Pure Appl. Geophys. 1999, 155, 509–535. [Google Scholar] [CrossRef]
- Gutenberg, B.; Richter, C.F. Frequency of Earthquakes in California. Bull. Seismol. Soc. Am. 1944, 34, 185–188. [Google Scholar] [CrossRef]
- Malamud, B.D.; Turcotte, D.L.; Guzzetti, F.; Reichenbach, P. Landslides, earthquakes, and erosion. Earth Planet. Sci. Lett. 2004, 229, 45–59. [Google Scholar] [CrossRef]
- Van Den Eeckhaut, M.; Poesen, J.; Govers, G.; Verstraeten, G.; Demoulin, A. Characteristics of the size distribution of recent and historical landslides in a populated hilly region. Earth Planet. Sci. Lett. 2007, 256, 588–603. [Google Scholar] [CrossRef]
- Xu, C.; Xu, X.; Yao, X.; Dai, F. Three (nearly) complete inventories of landslides triggered by the May 12, 2008 Wenchuan Mw 7.9 earthquake of China and their spatial distribution statistical analysis. Landslides 2014, 11, 441–461. [Google Scholar] [CrossRef]
- Burroughs, S.M.; Tebbens, S.F. Power-law Scaling and Probabilistic Forecasting of Tsunami Runup Heights. Pure Appl. Geophys. 2005, 162, 331–342. [Google Scholar] [CrossRef]
- Newhall, C.; Self, S.; Robock, A. Anticipating future Volcanic Explosivity Index (VEI) 7 eruptions and their chilling impacts. Geosphere 2018, 14, 572–603. [Google Scholar] [CrossRef]
- Cui, W.; Perera, A.H. What do we know about forest fire size distribution, and why is this knowledge useful for forest management? Int. J. Wildland Fire 2008, 17, 234–244. [Google Scholar] [CrossRef]
- Gilleland, E.; Katz, R.W. extRemes 2.0: An Extreme Value Analysis Package in R. J Stat. Soft. 2016, 72, 1–39. [Google Scholar] [CrossRef]
- Katz, R.W.; Parlange, M.B.; Naveau, P. Statistics of extremes in hydrology. Adv. Water Resour. 2002, 25, 1287–1304. [Google Scholar] [CrossRef]
- Morrison, J.E.; Smith, J.A. Stochastic modelling of flood peaks using the generalized extreme value distribution. Water Resour. Res. 2002, 38, 1305. [Google Scholar] [CrossRef]
- Jagger, T.H.; Elsner, J.B. Climatology Models for Extreme Hurricane Winds near the United States. J. Clim. 2006, 19, 3220–3236. [Google Scholar] [CrossRef]
- Della-Marta, P.M.; Mathis, H.; Frei, C.; Liniger, M.A.; Kleinn, J.; Appenzeller, C. The return period of wind storms over Europe. Int. J. Climatol. 2009, 29, 437–459. [Google Scholar] [CrossRef]
- Hofherr, T.; Kunz, M. Extreme wind climatology of winter storms in Germany. Clim. Res. 2010, 41, 105–123. [Google Scholar] [CrossRef][Green Version]
- Malmstadt, J.C.; Elsner, J.B.; Jagger, T.H. Risk of Strong Hurricane Winds to Florida Cities. J. Appl. Meteo. Clim. 2010, 49, 2121–2132. [Google Scholar] [CrossRef]
- Bath, M. The energies of seismic body waves and surface waves. Contr. Geophys. 1958, 1, 1–16. [Google Scholar]
- Glasstone, S.; Dolan, P.J. The Effects of Nuclear Weapons, 3rd ed.; US Department of Defense and Department of Energy: Washington, DC, USA, 1977.
- Ambraseys, N.N.; Simpson, K.A.; Bommer, J.J. Prediction of Horizontal Response Spectra in Europe. Earthq. Eng. Struct. Dyn. 1996, 25, 371–400. [Google Scholar] [CrossRef]
- Youngs, R.R.; Chiou, S.-J.; Silva, W.J.; Humphrey, J.R. Strong Ground Motion Attenuation Relationships for Subduction Zone Earthquakes. Seismol. Res. Lett. 1997, 68, 58–73. [Google Scholar] [CrossRef]
- Douglas, J.; Edwards, B. Recent and future developments in earthquake ground motion estimation. Earth-Sci. Rev. 2016, 160, 203–219. [Google Scholar] [CrossRef]
- Ambraseys, N.N.; Bommer, J.J. The attenuation of ground accelerations in Europe. Earthq. Eng. Struct. Dyn. 1991, 20, 1179–1202. [Google Scholar] [CrossRef]
- Mills, C. The design of concrete structures to resist explosions and weapon effects. In Proceedings of the 1st International Conference on Concrete for Hazard Protections, Edinburgh, UK, 27–30 September 1987. [Google Scholar]
- Holland, A.P.; Riordan, A.J.; Franklin, E.C. A Simple Model for Simulating Tornado Damage in Forests. J. App. Meteo. Climatol. 2006, 45, 1597–1611. [Google Scholar] [CrossRef]
- Willoughby, H.E.; Darling, R.W.R.; Rahn, M.E. Parametric Representation of the Primary Hurricane Vortex. Part II: A New Family of Sectionally Continuous Profiles. Mon. Weather Rev. 2006, 134, 1102–1120. [Google Scholar] [CrossRef]
- Vickery, P.J.; Wadhera, D. Statistical Models of Holland Pressure Profile Parameter and Radius to Maximum Winds of Hurricanes from Flight-Level Pressure and H*Wind Data. J. Appl. Meteo. Climatol. 2008, 47, 2497–2517. [Google Scholar] [CrossRef]
- Pyle, D.M. The Thickness, volume and grainsize of tephra fall deposits. Bull. Volcanol. 1989, 51, 1–15. [Google Scholar] [CrossRef]
- Grieser, J.; Hill, M. How to Express Hail Intensity—Modeling the Hailstone Size Distribution. J. Appl. Meteo. Climatol. 2019, 58, 2329–2345. [Google Scholar] [CrossRef]
- Sherwood, S.C.; Huber, M. An adaptability limit to climate change due to heat stress. Proc. Natl. Acad. Sci. USA 2010, 107, 9552–9555. [Google Scholar] [CrossRef]
- Stull, R. Wet-Bulb Temperature from Relative Humidity and Air Temperature. J. Appl. Meteo. Climatol. 2011, 50, 2267–2269. [Google Scholar] [CrossRef]
- Ramirez, J.A.; Lichter, M.; Coulthard, T.J.; Skinner, C. Hyper-resolution mapping of regional storm surge and tide flooding: Comparison of static and dynamic models. Nat. Hazards 2016, 82, 571–590. [Google Scholar] [CrossRef]
- Bak, P.; Tang, C.; Wiesenfeld, K. Self-Organized Criticality: An Explanation of 1/f Noise. Phys. Rev. Lett. 1987, 59, 381–384. [Google Scholar] [CrossRef]
- Kermack, W.O.; McKendrick, A.G. A Contribution to the Mathematical Theory of Epidemics. Proceed. R. Soc. A 1927, 115, 700–721. [Google Scholar]
- Kress, M. Lanchester Models for Irregular Warfare. Mathematics 2020, 8, 737. [Google Scholar] [CrossRef]
- MacKay, N.J. When Lanchester Met Richardson, the Outcome Was Stalemate: A Parable for Mathematical Models of Insurgency. In OR, Defence and Security; Forder, R.A., Ed.; Palgrave Macmillan: London, UK, 2015; pp. 124–147. [Google Scholar]
- Ilachinski, A. Irreducible Semi-Autonmous Adaptive Combat (ISAAC): An Artificial-Life Approach to Land Combat. Mil. Oper. Res. 2000, 5, 29–46. [Google Scholar] [CrossRef]
- Epstein, J.M. Agent-Based Computational Models And Generative Social Science. Complexity 1999, 4, 41–60. [Google Scholar] [CrossRef]
- Sachtjen, M.L.; Carreras, B.A.; Lynch, V.E. Disturbances in a power transmission system. Phys. Rev. E 2000, 61, 4877–4882. [Google Scholar] [CrossRef]
- Lotka, A.J. Contribution to the Theory of Periodic Reactions. J. Phys. Chem. 1910, 14, 271–274. [Google Scholar] [CrossRef]
- Volterra, V. Variations and Fluctuations of the Number of Individuals in Animal Species living together. ICES J. Mar. Sci. 1928, 3, 3–51. [Google Scholar] [CrossRef]
- Ludwig, D.; Jones, D.D.; Holling, C.S. Qualitative Analysis of Insect Outbreak Systems: The Spruce Budworm and Forest. J. Anim. Ecol. 1978, 47, 315–332. [Google Scholar] [CrossRef]
- Eling, M. Cyber risk research in business and actuarial science. Eur. Actuar. J. 2020, 10, 303–333. [Google Scholar] [CrossRef]
- Liu, W.; Zhong, S. Web malware spread modelling and optimal control strategies. Sci. Rep. 2017, 7, 42308. [Google Scholar] [CrossRef]
- Hethcore, H.W. The Mathematics of Infectious Diseases. SIAM Rev. 2000, 42, 599–653. [Google Scholar] [CrossRef]
- Wang, Z.; Broccardo, M.; Mignan, A.; Sornette, D. The dynamics of entropy in the COVID-19 outbreaks. Nonlinear Dyn. 2020, 101, 1847–1869. [Google Scholar] [CrossRef]
- Rahmandad, H.; Sterman, J. Heterogeneity and Network Structure in the Dynamics of Diffusion: Comparing Agent-Based and Differential Equation Models. Manag. Sci. 2008, 54, 998–1014. [Google Scholar] [CrossRef]
- Epstein, J.M. Modelling to contain pandemics. Nature 2009, 460, 687. [Google Scholar] [CrossRef]
- Merz, B.; Elmer, F.; Thicken, A.H. Significance of “High probability/low damage” versus “low probability/high damage” flood events. Nat. Hazards Earth Syst. Sci. 2009, 9, 1033–1046. [Google Scholar] [CrossRef]
- Issermann, M.; Chang, F.-J.; Jia, H. Efficient Urban Inundation Model for Live Flood Forecasting with Cellular Automata and Motion Cost Fields. Water 2020, 12, 1997. [Google Scholar] [CrossRef]
- Mohamed, E.S.; Rajasekaran, S. Tsunami Wave Simulation Models Based on Hexagonal Cellular Automata. WSEAS Transac. Fluid Mech. 2013, 8, 91–101. [Google Scholar]
- Piegari, E.; Cataudella, V.; Di Maio, R.; Milano, L.; Nicodemi, M. A cellular automaton for the factor of safety field in landslides modeling. Geophys. Res. Lett. 2006, 33, L01403. [Google Scholar] [CrossRef]
- Segre, E.; Deangeli, C. Cellular automaton for realistic modelling of landslides. Nonlinear Proc. Geophys. 1995, 2, 1–15. [Google Scholar] [CrossRef]
- Di Gregorio, S.; Rongo, R.; Siciliano, C.; Sorriso-Valvo, M.; Spataro, W. Mount Ontake Landslide Simulation by the Cellular Automata Model SCIDDICA-3. Phys. Chem. Earth 1999, 24, 131–137. [Google Scholar] [CrossRef]
- Guthrie, R.H.; Deadman, P.J.; Cabrera, A.R.; Evans, S.G. Exploring the magnitude-frequency distribution: A cellular automata model for landslides. Landslides 2008, 5, 151–159. [Google Scholar] [CrossRef]
- Avolio, M.V.; Di Gregorio, S.; Lupiano, V.; Mazzanti, P. SCIDDICA-SS3: A new version of cellular automata model for simulating fast moving landslides. J. Supercomput. 2013, 65, 682–696. [Google Scholar] [CrossRef]
- Lu, P.; Zhang, Z.; Li, M.; Chen, D.; Yang, H. Agent-based modeling and simulations of terrorist attacks combined with stampedes. Knowl.-Based Syst. 2020, 205, 106291. [Google Scholar] [CrossRef]
- Clarke, K.C.; Brass, J.A.; Riggan, P.J. A Cellular Automaton Model of Wildfire Propagation and Extinction. Photogramm. Eng. Remote Sens. 1994, 60, 1355–1367. [Google Scholar]
- Alexandridis, A.; Vakalis, D.; Siettos, C.I.; Bafas, G.V. A cellular automata model for forest fire spread prediction: The case of the wildfire that swept through Spetses Island in 1990. Appl. Math. Comput. 2008, 204, 191–201. [Google Scholar] [CrossRef]
- Trunfio, G.A.; D’Ambrosio, D.; Rongo, R.; Spataro, W.; Di Gregorio, S. A New Algorithm for Simulating Wildfire Spread through Cellular Automata. ACM Trans. Model. Comput. Simul. 2011, 22, 6. [Google Scholar] [CrossRef]
- Liu, Y.; Kochanski, A.; Baker, K.R.; Mell, W.; Linn, R.; Paugam, R.; Mandel, J.; Fournier, A.; Jenkins, M.A.; Goodrick, S.; et al. Fire behaviour and smoke modelling: Model improvement and measurement needs for next-generation smoke research and forecasting systems. Int. J. Wildland Fire 2019, 28, 570–588. [Google Scholar] [CrossRef]
- Fang, P.; Ye, G.; Yu, H. A parametric wind field model and its application in simulating historical typhoons in the western North Pacific Ocean. J. Wind Eng. Ind. Aerodyn. 2020, 199, 104131. [Google Scholar] [CrossRef]
- Fournier, A.; Fussell, D.; Carpenter, L. Computer Rendering of Stochastic Models. Comm. ACM 1982, 25, 371–384. [Google Scholar] [CrossRef]
- Woo, G. Calculating Catastrophe; Imperial College Press: London, UK, 2011. [Google Scholar]
- Johnston, A.C. An earthquake strength scale for the media and the public. Earthq. Volcanoes 1990, 22, 214–216. [Google Scholar]
- Malamud, B.D.; Morein, G.; Turcotte, D.L. Forest Fires: An Example of Self-Organized Critical Behavior. Science 1998, 281, 1840–1842. [Google Scholar] [CrossRef]
- Turcotte, D.L.; Malamud, B.D. Landslides, forest fires, and earthquakes: Examples of self-organized critical behavior. Physica A 2004, 340, 580–589. [Google Scholar] [CrossRef]
- Dincer, I.; Dost, S. Energy and GDP. Int. J. Energy Res. 1997, 21, 153–167. [Google Scholar] [CrossRef]
- Kreibich, H.; Piroth, K.; Seifert, I.; Maiwald, H.; Kunert, U.; Schwarz, J.; Merz, B.; Thicken, A.H. Is flow velocity a significant parameter in flood damage modelling? Nat. Hazards Earth Syst. Sci. 2009, 9, 1679–1692. [Google Scholar] [CrossRef]
- Tribus, M.; McIrvine, E.C. Energy and Information. Sci. Am. 1971, 225, 179–190. [Google Scholar] [CrossRef]
- Koski, J.V.; Maisi, V.F.; Pekola, J.P.; Averin, D.V. Experimental realization of a Szilard engine with a single electron. Proc. Natl. Acad. Sci. USA 2014, 111, 13786–13789. [Google Scholar] [CrossRef]
- Wooster, M.J.; Zhukov, B.; Oertel, D. Fire radiative energy for quantitative study of biomass burning: Derivation from the BIRD experimental satellite and comparison to MODIS fire products. Remote Sens. Environ. 2003, 86, 83–107. [Google Scholar] [CrossRef]
- Mignan, A.; Wiemer, S.; Giardini, D. The quantification of low-probability–high-consequences events: Part I. A generic multi-risk approach. Nat. Hazards 2014, 73, 1999–2022. [Google Scholar] [CrossRef]
- Mignan, A.; Wang, Z. Exploring the Space of Possibilities in Cascading Disasters with Catastrophe Dynamics. Int. J. Environ. Res. Public Health 2020, 17, 7317. [Google Scholar] [CrossRef]
- Bloemendaal, N.; de Moel, H.; Martinez, A.B.; Muis, S.; Haigh, I.D.; van der Wiel, K.; Haarsma, R.J.; Ward, P.J.; Roberts, M.J.; Dullaart, J.C.M.; et al. A globally consistent local-scale assessment of future tropical cyclone risk. Sci. Adv. 2022, 8, eabm8438. [Google Scholar] [CrossRef]
- Randers, J.; Golüke, U.; Wenstop, F.; Wenstop, S. A user-friendly earth system model of low complexity: The ESCIMO system dynamics model of global warming towards 2100. Earth Syst. Dynam. 2016, 7, 831–850. [Google Scholar] [CrossRef]
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).