Complementary Cooperation of CCTV and UAV Systems for Tourism Security and Sustainability
Abstract
:1. Introduction
2. Related Studies
3. CCTV and UAV Security System in Tourism Destination
3.1. Characteristics of CCTV and UAV Systems
3.1.1. CCTV Security Systems
3.1.2. UAV Security System
- Mixing tethered drones and deployable drones help security respond to all situations quickly and efficiently.
- Intruder Responses.
- Using drones help security forces get closer to intruders without alerting them.
- UAV’s can run a perimeter route faster and more easily.
- Drones can be used to search blind spots and corners, minimizing risk to people.
- Tracking the intruders just became easier.
- With drones, response time is much faster.
- Drone can access to the inaccessible area and provide surveillance task
3.2. Tourist Flow of Tourists
3.3. Installation and Operation Issues
4. Mathematical Models
4.1. Mathematical Model 1: CCTV Security System
4.1.1. Notations of Model 1
4.1.2. Mathematical Formulations of Model 1
4.2. Mathematical Model 2: CCTV and UAV Security System
4.2.1. New Notations of Model 2
4.2.2. Mathematical Formulations of Model 2
4.3. Solution Approach
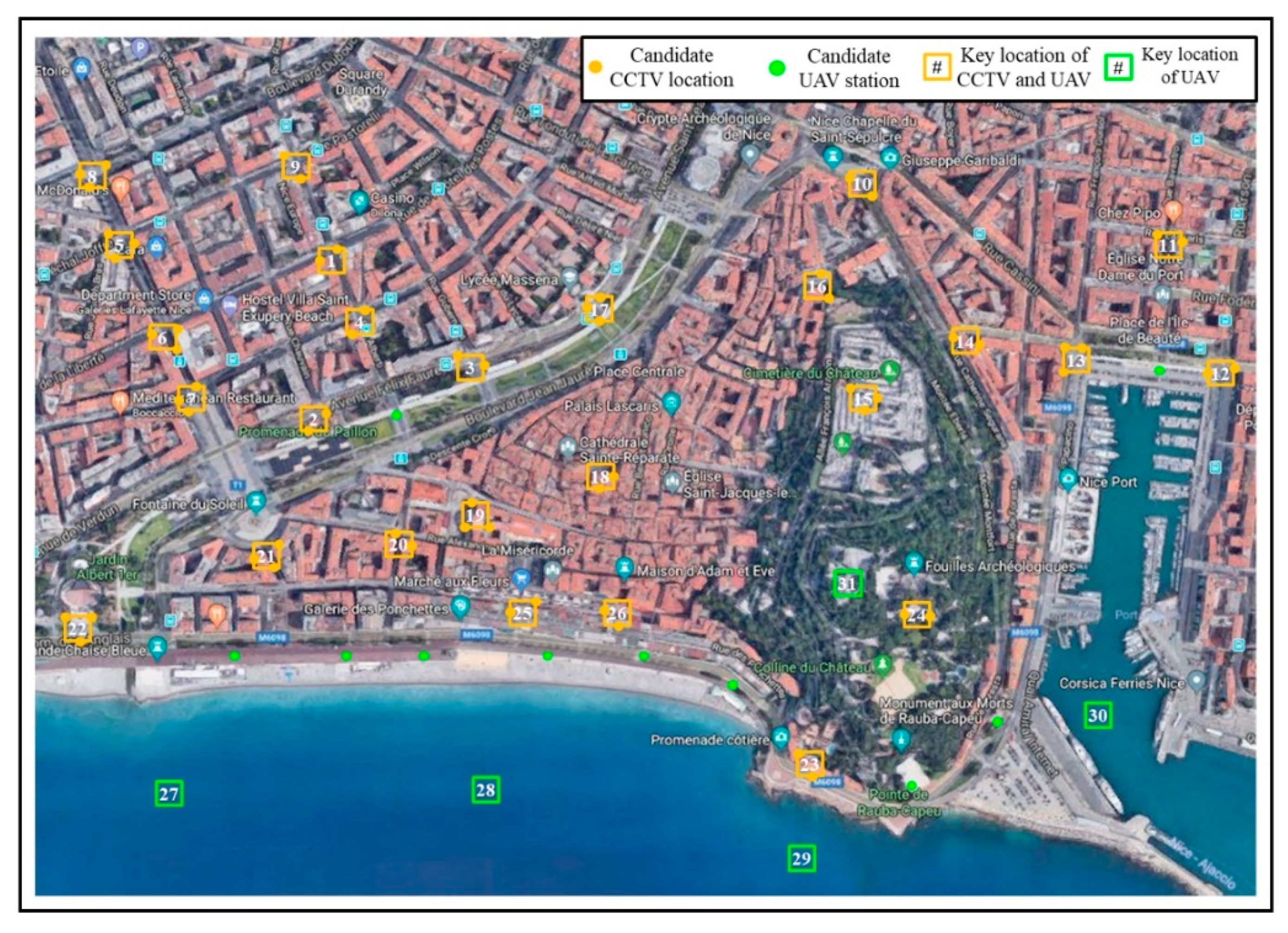
5. Case Study
5.1. Case Study Details
5.1.1. Cases Study Parameters for Situation 1
5.1.2. Cases Study Parameters for Situation 2
5.2. Results of the Case Study
5.2.1. Results of the Situation 1
5.2.2. Results of the Situation 2
6. Concluding Remarks
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- World Summit Outcome. United Nations 2005 World Summit Outcome A/60/L.1. Available online: http://www.un-documents.net/uncsd-docs.pdf (accessed on 19 August 2021).
- Lane, B. Sustainable rural tourism strategies: A tool for development and conservation. J. Sustain. Tour. 1994, 2, 102–111. [Google Scholar] [CrossRef]
- Baker, K.; Coulter, A. Terrorism and tourism: The vulnerability of beach vendors’ livelihoods in Bali. J. Sustain. Tour. 2007, 15, 249–266. [Google Scholar] [CrossRef]
- Rodríguez Díaz, M.; Espino Rodríguez, T.F. Determining the sustainability factors and performance of a tourism destination from the stakeholders’ perspective. Sustainability 2016, 8, 951. [Google Scholar] [CrossRef] [Green Version]
- Paraskevas, A.; Arendell, B. A strategic framework for terrorism prevention and mitigation in tourism destinations. Tour. Manag. 2007, 28, 1560–1573. [Google Scholar] [CrossRef]
- The National. Tourist Industry Worldwide Shows Resilience to Terror. Available online: https://www.thenational.ae/business/travel-and-tourism/tourist-industry-worldwide-shows-resilience-to-terror-1.677541 (accessed on 19 August 2021).
- The Local. France to Spend Big in Effort to Win Back Scared Tourists. Available online: https://www.thelocal.fr/20161107/more-cctv-and-mobile-units-france-moves-to-reassure-tourists (accessed on 19 August 2021).
- Sönmez, S.F.; Graefe, A.R. Influence of terrorism risk on foreign tourism decisions. Ann. Tour. Res. 1998, 25, 112–144. [Google Scholar] [CrossRef] [Green Version]
- Kozak, M.; Crotts, J.C.; Law, R. The impact of the perception of risk on international travellers. Int. J. Tour. Res. 2007, 9, 233–242. [Google Scholar] [CrossRef]
- Araña, J.E.; León, C.J. The impact of terrorism on tourism demand. Ann. Tour. Res. 2008, 35, 299–315. [Google Scholar] [CrossRef]
- Rittichainuwat, B.N.; Chakraborty, G. Perceived travel risks regarding terrorism and disease: The case of Thailand. Tour. Manag. 2009, 30, 410–418. [Google Scholar] [CrossRef]
- Pizam, A.; Smith, G. Tourism and terrorism: A quantitative analysis of major terrorist acts and their impact on tourism destinations. Tour. Econ. 2000, 6, 123–138. [Google Scholar] [CrossRef]
- Bonham, C.; Edmonds, C.; Mak, J. The impact of 9/11 and other terrible global events on tourism in the United States and Hawaii. J. Travel. Res. 2006, 45, 99–110. [Google Scholar] [CrossRef]
- Feridun, M. Impact of terrorism on tourism in Turkey: Empirical evidence from Turkey. Appl. Econ. 2011, 43, 3349–3354. [Google Scholar] [CrossRef]
- Long, N.T.; Nguyen, T.L. Sustainable development of rural tourism in an Giang Province, Vietnam. Sustainability 2018, 10, 953. [Google Scholar] [CrossRef] [Green Version]
- Southeast Asia GLOBE. Singapore Backs Crime-Fighting Security Drones. Available online: http://sea-globe.com/real-life-robocops-singapore-backs-crime-fighting-security-drones/ (accessed on 19 August 2021).
- Hussain, Z. India Uses Drones to Fight Rhino Poaching. The Sydney Morning Herald. Available online: http://www.smh.com.au/technology/sci-tech/india-uses-drones-to-fightrhino-poaching-20130408-2hi1c.html (accessed on 19 August 2021).
- Faulkner, B. Towards a framework for tourism disaster management. Tour. Manag. 2001, 22, 135–147. [Google Scholar] [CrossRef]
- Prideaux, B. The need to use disaster planning frameworks to respond to major tourism disasters: Analysis of Australia’s response to tourism disasters in 2001. J. Travel Tour. Mark. 2004, 15, 281–298. [Google Scholar] [CrossRef]
- Evans, N.; Elphick, S. Models of crisis management: An evaluation of their value for strategic planning in the international travel industry. Int. J. Tour. Res. 2005, 7, 135–150. [Google Scholar] [CrossRef]
- Song, B.D.; Ko, Y.D. Quantitative approaches for economic use of emerging technology in the tourism industry: Unmanned aerial vehicle systems. Asia Pac. J. Tour. Res. 2017, 22, 1207–1220. [Google Scholar] [CrossRef]
- Ko, Y.D.; Song, B.D. Application of UAVs for tourism security and safety. Asia Pac. J. Mark. Logist. 2021, 33, 1829–1843. [Google Scholar] [CrossRef]
- Yin, L.; Zhang, N.; Tang, C. On-demand UAV base station deployment for wireless service of crowded tourism areas. Pers. Ubiquitous. Comput. 2021, 1–13. [Google Scholar]
- Tsai, C.Y.; Chang, H.T.; Kuo, R.J. An ant colony based optimization for RFID reader deployment in theme parks under service level consideration. Tour. Manag. 2017, 58, 1–14. [Google Scholar] [CrossRef]
- Öztayşi, B.; Baysan, S.; Akpinar, F. Radio frequency identification (RFID) in hospitality. Technovation 2009, 29, 618–624. [Google Scholar] [CrossRef]
- Business Insider. The Most Staggering Part about Amazon’s Upcoming Drone Delivery Service. Available online: https://www.businessinsider.com/cost-savings-from-amazon-drone-deliveries-2016-6/ (accessed on 19 August 2021).
- Flyguys. Drone Security Services for Event Surveillance and Intruder Response. Available online: https://flyguys.com/drone-services/drone-security/ (accessed on 19 August 2021).
- Jun, S.; Chang, T.W.; Jeong, H.; Lee, S. Camera placement in smart cities for maximizing weighted coverage with budget limit. IEEE Sensors J. 2017, 17, 7694–7703. [Google Scholar] [CrossRef]
- Eun, J.; Song, B.D.; Lee, S.; Lim, D.E. Mathematical investigation on the sustainability of UAV logistics. Sustainability 2019, 11, 5932. [Google Scholar] [CrossRef] [Green Version]
- IBM Documentation, ILOG CPLEX Optimization Studio 20.1—Types of Problems Solved. Available online: https://www.ibm.com/docs/en/icos/20.1.0?topic=cplex-types-problems-solved (accessed on 19 August 2021).





| System Variables | |
| I | Set of key locations for monitoring |
| J | Set of candidate CCTV locations |
| T | Set of time periods |
| pit | Security priority of key location i at time t |
| dij | Distance between location i and j |
| ccctv | Purchase cost of CCTV |
| rcctv | Service range of a CCTV |
| kit | Service requirement of key location i and time t. It represents the number of required security equipment to monitor key location i at time t |
| b | Available budget (USD) for system installation |
| Decision Variables | |
| Xijt | Binary decision variable, it is equal to 1 if key location i is monitored by CCTV at j in time t; otherwise, 0. |
| Yj | Binary decision variable, it is equal to 1 if CCTV is located at candidate location j; otherwise, 0. |
| Wit | Binary decision variable, it is equal to 1 if key location i is fully monitored by CCTV with the number of required security equipment at time t; otherwise, 0. |
| System Variables | |
| S | Set of candidate UAV stations |
| dis | Distance between location i and s |
| uit | Mandatory UAV service request of key location i (usually, area where installation of CCTV is limited)at time t. It is equal to 1 if key location i should be monitored by UAV at time t; otherwise, 0. |
| cstation | Installation cost of UAV station |
| cuav | Purchase cost of UAV |
| nuav | Number of UAVs that requires to monitor a key location using UAVs |
| ruav | Service range of a UAV station |
| Decision Variables | |
| Zs | Binary decision variable, it is equal to 1 if UAV station is installed at s; otherwise, 0. |
| Uist | Binary decision variable, it is equal to 1 if key location i is served by UAV station s at time t; otherwise, 0. |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ko, Y.D.; Song, B.D. Complementary Cooperation of CCTV and UAV Systems for Tourism Security and Sustainability. Sustainability 2021, 13, 10693. https://doi.org/10.3390/su131910693
Ko YD, Song BD. Complementary Cooperation of CCTV and UAV Systems for Tourism Security and Sustainability. Sustainability. 2021; 13(19):10693. https://doi.org/10.3390/su131910693
Chicago/Turabian StyleKo, Young Dae, and Byung Duk Song. 2021. "Complementary Cooperation of CCTV and UAV Systems for Tourism Security and Sustainability" Sustainability 13, no. 19: 10693. https://doi.org/10.3390/su131910693






