1. Introduction
In various graphics applications such as military, medicine, homeland security, etc., advanced image encryption techniques are increasingly needed for the safe transfer, storage, and recuperation of digital images. A well-designed image cryptosystem should meet the two principles: diffusion and confusion [
1]. Confusion indicates that all possible traces or information related to the plaintext or key are deleted from the ciphertext. Diffusion indicates that any tiny modification in either the plaintext or the key leads to a huge modification in the ciphertext. The substitution-box (S-box) is a nonlinear unit used in many cryptographic applications to guarantee the confusion characteristic [
2]. The diffusion feature can be checked with chaotic dynamical maps. In actuality, chaotic maps have numerous ultimate features, such as ergodicity, sensitivity to primary conditions. They show a random behavior that can cause confusion and diffusion in the plaintext to get secure ciphertext [
3].
Recently, various researchers have used chaotic maps in constructing S-boxes and designing image encryption mechanisms [
4,
5,
6,
7,
8,
9,
10,
11,
12,
13]. Chaotic systems play an important role in designing S-boxes. For example, Tang et al. [
14] presented a different scheme for constructing S-box using a 2D discretized chaotic system, and in [
7], a four-step strategy to construct S-boxes using a chaotic system is proposed. In [
15], Chen et al. developed the scheme presented in [
14] by utilizing 3D Backer system. In [
16], Fatih et al. introduced a new method for S-box constructions using chaotic Lorenz map. Furthermore, Khan et al. [
17] presented a new S-box construction scheme for block cipher using multi-chaotic maps. A popular characteristic of the above approaches is that they construct S-boxes using only the randomness properties of chaotic systems. This is why we need a new chaotic map with good randomness properties to build strong S-boxes. In [
18], Tlelo-Cuautle et al. presented a new 3D chaotic map with infinite numbers of equilibrium points and good effective performance. Based on the advantages of the presented map in [
18], we design a new chaos-based S-box that utilizes the randomness property of the chaotic map.
Data security performs a vital task in our daily life, in which chaotic systems are popularly utilized in the development of modern encryption mechanisms [
19,
20,
21]. Based on chaos, several image cryptosystems have been introduced. Most of them are dependent on a one-dimensional or multi-dimensional chaotic system to generate pseudorandom numbers for constructing the cipher image. For example, in [
22], a skew tent map is employed to design an image encryption approach, and in [
8], a 1D chaotic map is obtained through coupling sine and tent maps, which is then adjusted to encrypt the plain image. Hua et al. in [
23] employ a 2D Sine Logistic modulation system to produce an image cryptosystem, and Liu et al. [
24] suggest a color image cryptosystem by utilizing a hyper-chaotic map and Choquet fuzzy integral. In [
9], a chaos-based image block encryption approach is presented using S-box, and Wang et al. [
24] suggested an image cryptosystem in the form of block cipher using a chaotic map and dynamic random growth mechanism. In [
25], an image cryptosystem based on a 3D cat map is proposed. Although the previous schemes have some good results, they are not enough to raise the effectiveness of potential applications for the image encryption field. Most of them present vulnerabilities [
26,
27,
28].
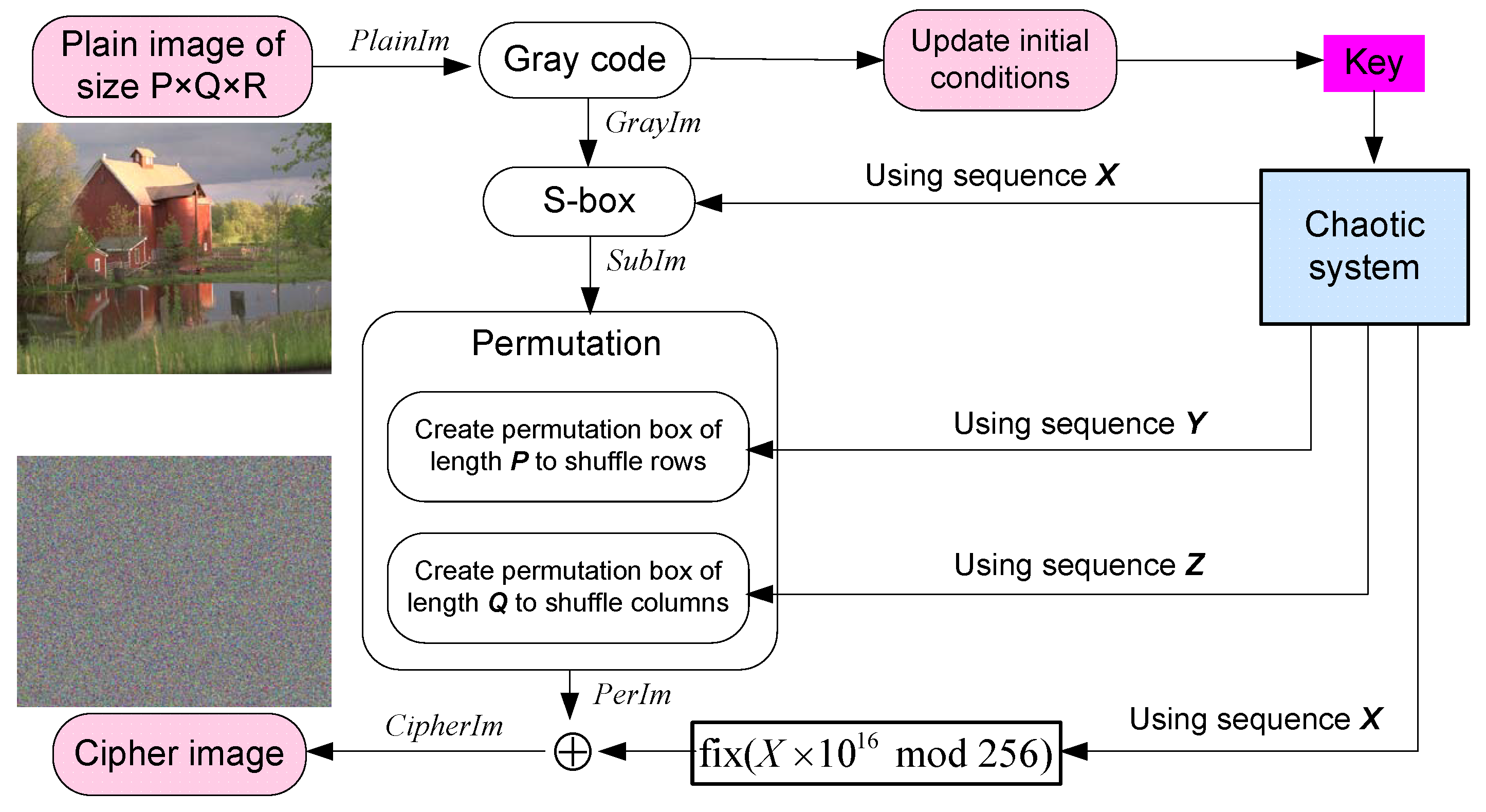
Based on the presented chaos-based substitution box efficiency, we present a new chaos-based image cryptosystem using Gray code, 3D chaotic map [
18], and the proposed substitution box strategy. The provided image cryptosystem can be implemented on both grey-scale and colored images. Experimental outcomes demonstrate that the presented approach posses high performance and security.
To clarify, the main contributions of our study are twofold, as follows:
Designing a new chaos-based S-box and validating its randomness property as required in efficient chaotic maps [
18].
Utilising the designed S-box as the fulcrum of a new image cryptosystem that also integrates the Gray code and the chaotic mapping [
18] to generate unique encryption signatures with high sensitivity for each image.
This work’s organization is as follows:
Section 2 gives the preliminary work for the suggested schemes. In
Section 3, the new approach of designing the S-box is illustrated, and the criteria for assessing the S-box and the performance evaluation of the suggested S-box are presented and compared with other chaos-based S-boxes. In
Section 4, a new chaos-based image cryptosystem is presented, while its performance evaluations are provided in
Section 5. Finally, a conclusion is given in
Section 6.
5. Performance and Security Analyses
In this part, various analyses are employed to evaluate the security and performance of the suggested encryption scheme. A dataset of images taken from Kodak [
33] of dimension
were employed to evaluate the proposed cryptosystem (see
Figure 3). The primary values and control parameter for acting the 3D chaotic map (
2) are given as (
,
,
, and
). These simulation results were obtained using Matlab software, which was performed on an Intel Core i5-2450M 2.5 CPU with 6 GB RAM.
5.1. Key Space Analysis
The key space is defined as the whole set of keys employed throughout the encryption process. It must be amply large to make brute-force attacks ineffective. The key space of the proposed cryptosystem consists of the initial conditions
of (
2). The computational precision of digital computers is assumed to be
. The possible values of
are
, as are the values of
,
, and
a. Therefore, the proposed scheme holds a
key space, which is enough to defend against potential brute-force-based attacks.
5.2. Statistical Analysis
In this part, various statistical analyses are utilized to evaluate the performance of the suggested cryptosystem, including correlation analysis, histogram analysis, global entropy, and local entropy.
5.2.1. Correlation Analysis
The correlation of neighboring pixels in the original images and their ciphered ones are displayed in this subsection. It is understood that the values of correlation for original images are very near to 1, whilst encrypted images with a good encryption mechanism are very near to 0. The correlations among each pair of two neighboring pixels can be measured as follows:
where
and
are gray-scale values of two selected adjacent pixels, and
N is the complete number of pairs
collected from the image. The correlation coefficients of 10,000 randomly selected pairs of neighboring pixels in the original image and its encrypted ones are provided in
Table 12. The correlation coefficients of original images are close to 1, whilst those of ciphered images are approximately equal to 0. Then, the adjacent pixels in the encrypted image are de-correlated in each direction. This feature is displayed graphically in
Figure 4,
Figure 5 and
Figure 6, which contains plots of the correlation distributions in each direction of the original Houses image and the Cipher-Houses image for each color component. Consequently, the presented encryption scheme fulfills zero correlation, and it has a high privilege towards statistical attacks.
5.2.2. Histogram Analysis
The histogram exposes the intensity of the grey level of an image. This information can be beneficial in the event of a histogram attack with an uneven distribution. Images created using a well-designed image cryptosystem should have identical histograms to increase resistance to statistical analysis. Histograms of plain images and their ciphered ones are shown in
Figure 7. Obviously, the histograms of the ciphered images are somewhat identical and differ significantly from the corresponding plain images. Therefore, we can deduce that the suggested encryption mechanism can withstand histogram attacks.
5.2.3. Global Entropy
Information entropy is a statistical examination of randomness. The entropy value can be measured as given in (
5).
where
denotes the appearance probability of each symbol
. The optimal entropy value (i.e.,
bits) is achieved if all the pixels appeared with equal probability, which implies that the pixel distribution is identical. The entropy values of experimented images are given in
Table 13, in which the entropy values for the presented cryptosystem are approximately equal to 8. Thus, the presented image cryptosystem has the ability to withstand entropy attacks.
5.2.4. Local Entropy
The global entropy is the average amount of information, so it does not reflect the randomness within each region of the image; i.e., the insufficiency of randomness inside some local regions of the image may be hidden. Therefore, it is recommended to apply another entropy analysis that works at the block level, namely, the local entropy [
34]. The local entropy computation is conducted following the steps reported in [
34]. The local entropy outcomes are listed in
Table 14, where the entropies are very close to the optimal empiric value
[
34].
5.3. Sensitivity Analysis
A well-designed cryptosystem must present a very high sensitivity of the ciphered image to slight modifications in either the key or the plain image. In this part, we present the suggested cryptosystem sensitivity analyses, including key sensitivity and plaintext sensitivity.
5.3.1. Key Sensitivity
A robust encryption scheme always warrants a high sensitivity to the secret key. That is, any slight change in such a key would provide a diametrically different encrypted image.
Figure 8 shows the outcomes of key sensitivity for the proposed image cryptosystem, in which it demonstrates a high sensitivity to the secret key. Consequently, the proposed cryptosystem is extremely sensitive to tiny changes in the secret key.
5.3.2. Plaintext Sensitivity
Like the key sensitivity, the plaintext sensitivity measures the rate of changes in the ciphertext when inducing a slight alteration to the plaintext. In this regard, two well-known quantitative tools were used: unified average changing intensity (UACI) and the number of pixel change rate (NPCR). We performed NPCR to calculate the number of different pixels between two ciphered images encrypted with one key and differing only in one bit of the plain image. Whereas the UACI criteria provide the average intensity variation. The NPCR and UACI are represented in (
6) and (
7), respectively.
where
W is the complete number of pixels in the image and
is obtained as:
where,
and
are two ciphered images; the
pixel of
and
are indicated as
and
, respectively; and
n is the number of bits utilized to form a greyscale pixel value. The results of NPCR and UACI values are provided in
Table 15. It can be observed from
Table 15 that all of the NPCR values are over than
, which confirms the high sensitivity of the encryption method, and UACI values for all experimented dataset are very near to
, which verifies that the degree of influence is very high. Accordingly, the proposed cryptosystem is immensely sensitive to minor changes in the original image, and no valuable information can be deduced from the algorithm.
5.4. Robustness Analysis
When transmitted over a communication channel, the encrypted images are susceptible to data losses, which causes degradations in the quality of the decrypted images. Furthermore, the transmission channels are noisy, and the encrypted images are susceptible to noise-based attacks. In this part, we present the robustness analyses of the suggested cryptosystem, including occlusion attack and noise attack.
5.4.1. Occlusion Attack
An occlusion attack generally tests an encryption scheme’s ability to retain the original image’s features when the corresponding encrypted image is subjected to a loss of information.
Figure 9a–d depict the encrypted images of Lighthouse under data losses of (a)
, (b)
, (c)
, and (d)
, respectively. Their decrypted images are displayed in
Figure 9e–h, respectively. Although half of the encrypted image information is lost, the corresponding decrypted image reserves enough visual information of the original image. As a result, the proposed cryptosystem can resist occlusion-based attacks.
5.4.2. Noise Attack
A strong encryption scheme should not be concerned with such noises. To check the robustness of the proposed cryptosystem to noise-based attacks, the encrypted image of the Lighthouse is tainted by the salt and pepper noise with several densities. The corresponding decrypted images are displayed in
Figure 10. It is shown that the image maintains the original image’s features, although the noise density is set to 0.3. Therefore, the proposed cryptosystem exhibits strong immunity against noise-based attacks.
5.5. Known-Plaintext and Chosen-Plaintext Attacks
The main task of cryptanalysis is to recover the entire secret key or some parts of it to completely or partially decipher the ciphertexts produced by a given encryption scheme. Moreover, in some attack scenarios, the attacker can retrieve the correct plaintext from a given ciphertext without needing the secret key. Indeed, he/she tries to find any similarities between plaintexts and ciphertexts. According to how the cryptanalyst performed such a search, four different attacks are presented and listed here from the hardest to the easiest attacks: the ciphertext-only attack, the known-plaintext attack, the chosen-plaintext attack, and the chosen-ciphertext attack. Among these attacks, the known-plaintext and chosen-plaintext attacks are considered the powerful ones, and if an encryption scheme can withstand them, it can resist the other attacks as well. In the proposed cryptosystem, the secret key is fully correlated to the input image, which leads to a unique key for each different image. Accordingly, the cryptanalyst cannot establish any link between plaintext/ciphertext pairs. The proposed cryptosystem has the power to hold facing known-plaintext and chosen-plaintext attacks.
5.6. Comparative and Speed Analysis
To appraise our image cryptosystem’s performance, its experimental outcomes are compared to other related encryption schemes.
Table 16 provides a comparison analysis, proving our encryption mechanism’s high performance. Apart from performance and security evaluations of the presented approach, a speed performance is also needed.
Table 17 provides the speed performance of our cryptosystem and the competitive image cryptosystem for various sizes of grey-scale of images as reported in [
35].
Table 16 and
Table 17 confirm the supremacy of our cryptosystem alongside those related image cryptosystems.

















.png)

