Hyperledger for IoT: A Review of Reconstruction Diagrams Perspective
Abstract
:1. Introduction
2. Introduction to Hyperledger
2.1. Fabric
2.2. Sawtooth
2.3. Iroha
2.4. Indy
2.5. Aries
2.6. Besu
3. Introduction to the IoT
3.1. Overview of the IoT and the IIoT
3.2. Convergence Point of Hyperledger with IoT and IIoT
- (1)
- Distributed storage and collaboration ensures tamper resistance for large volumes of data and decisions.
- (2)
- Fine-grained permission control enhances privacy protection between enterprises and consumers.
- (3)
- Hyperledger supports multiple chaincode authoring languages and provides channel-oriented chaincode lifecycle management, enhancing the efficiency of system collaboration.
- (4)
- The fine-grained state-based endorsement strategy enhances the security of enterprise transactions.
- (5)
- The efficient consensus mechanism effectively reduces network latency for device or large appliance collaboration and enables faster node state agreement, which can provide millisecond response time for the industrial IoT.
- (6)
- Peer-to-peer authentication ensures high portability of identities and provides great convenience for portable IoT device identification.
- (7)
- The highly modular framework and support for diverse chaincode writing languages enables Hyperledger to be quickly integrated with any IoT and industrial IoT system.
- (8)
- The dynamic network makes the system highly flexible and robust to meet the basic business requirements of the IoT.
4. Hyperledger Applications in the IoT
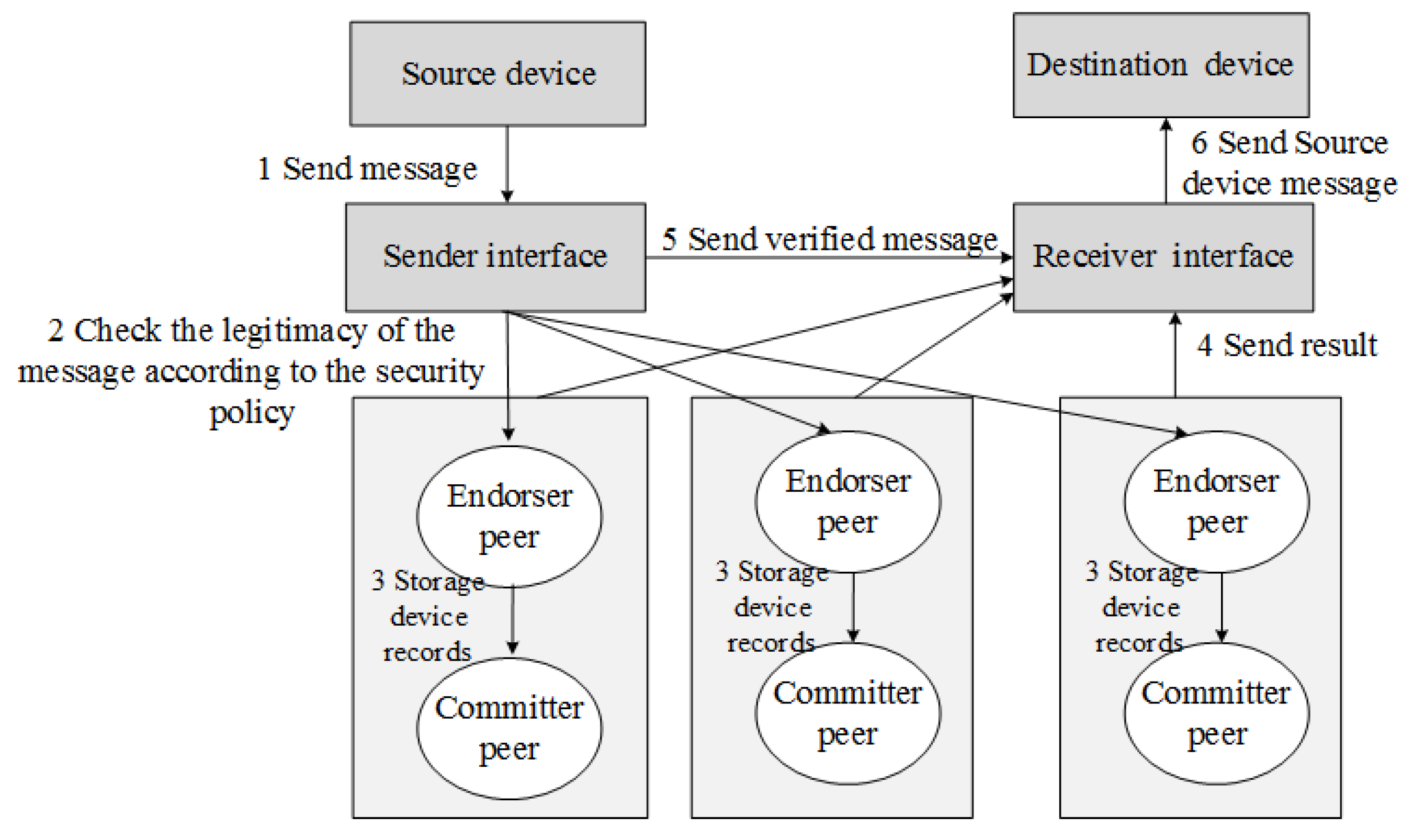
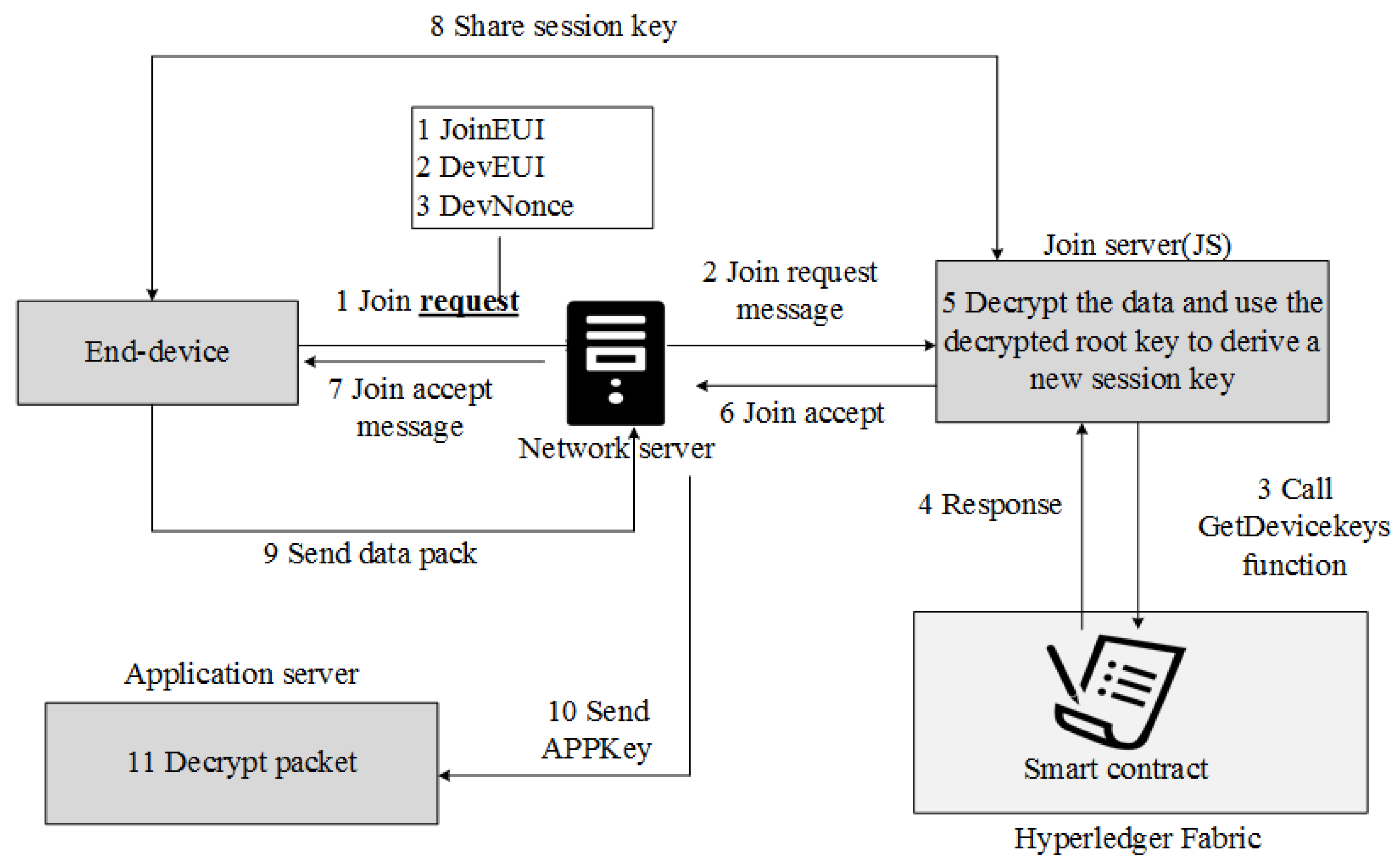
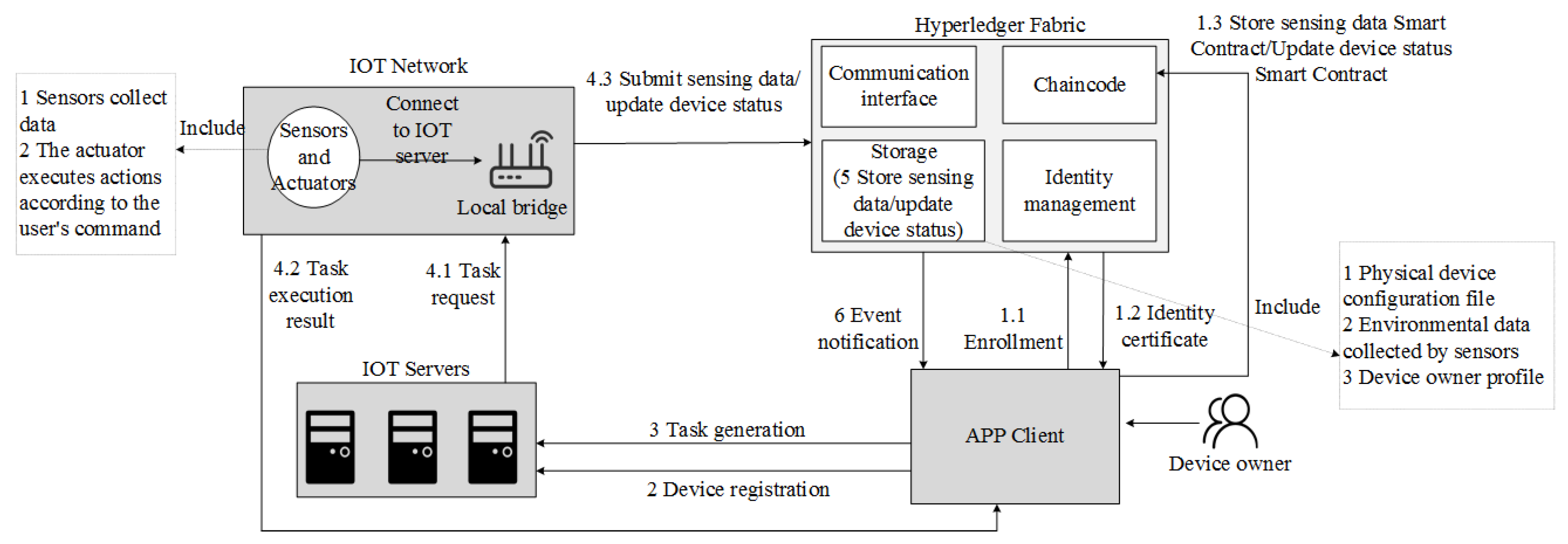
4.1. IoT Security
4.2. Smart Fisheries and Smart Agriculture
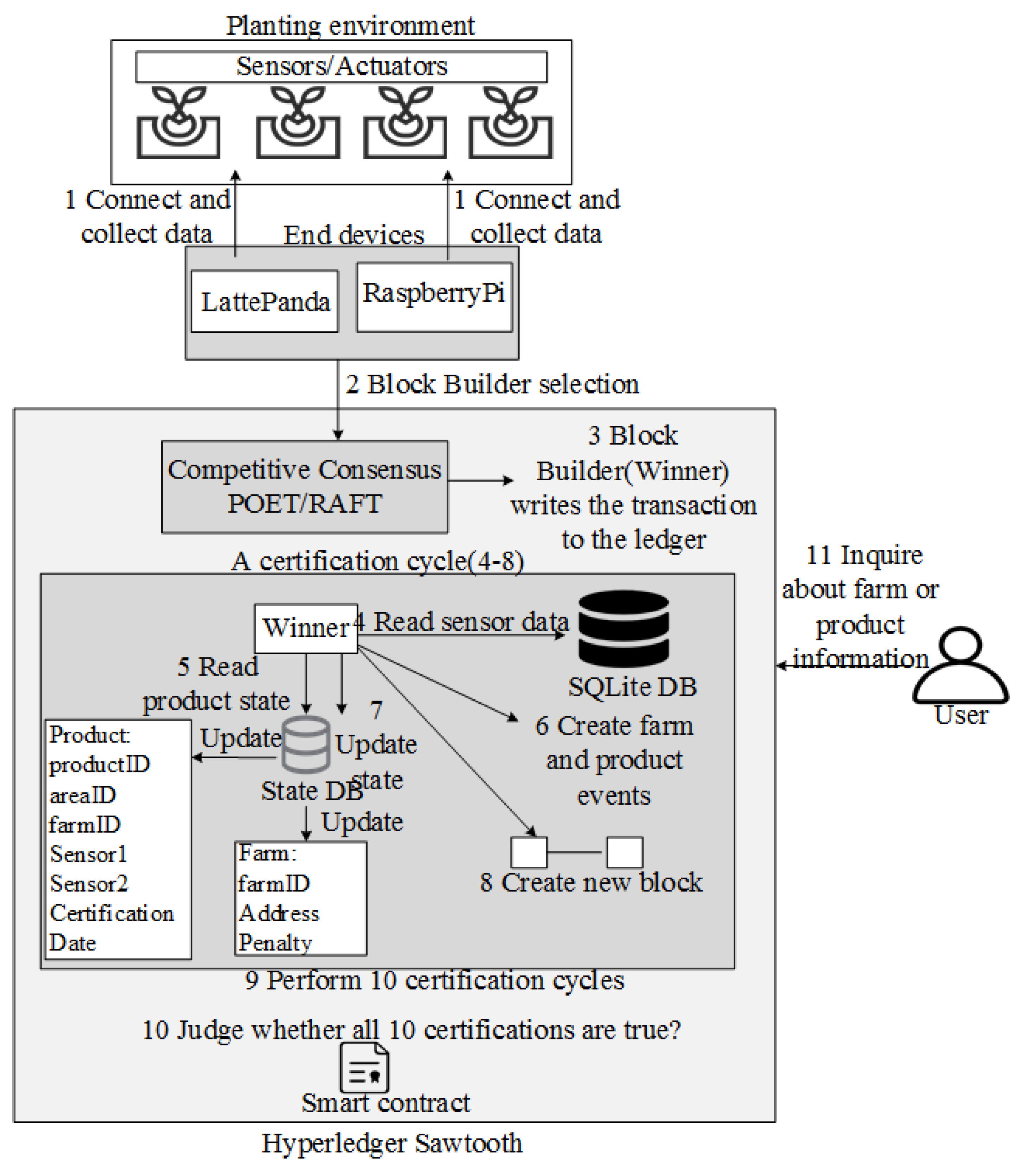
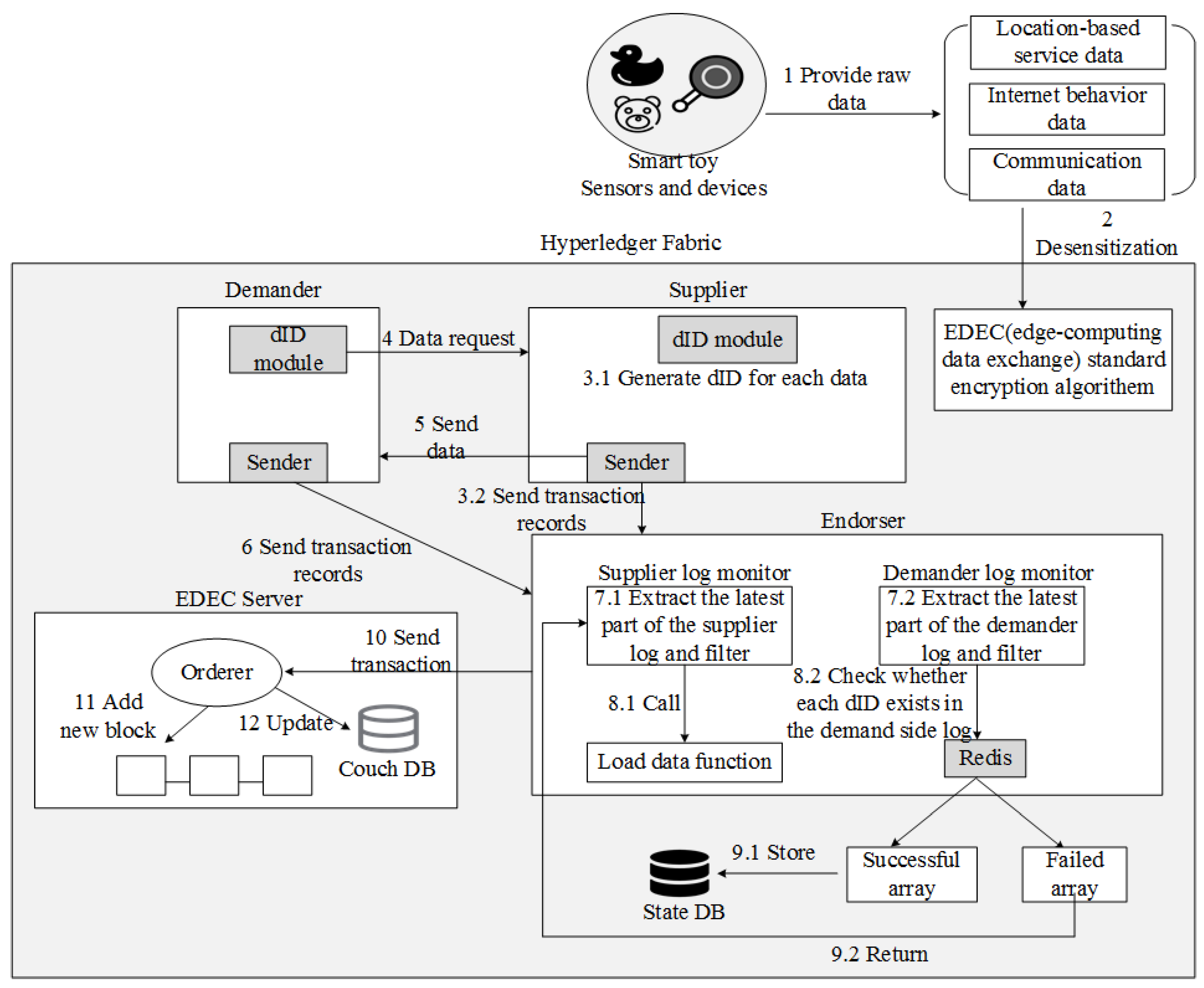
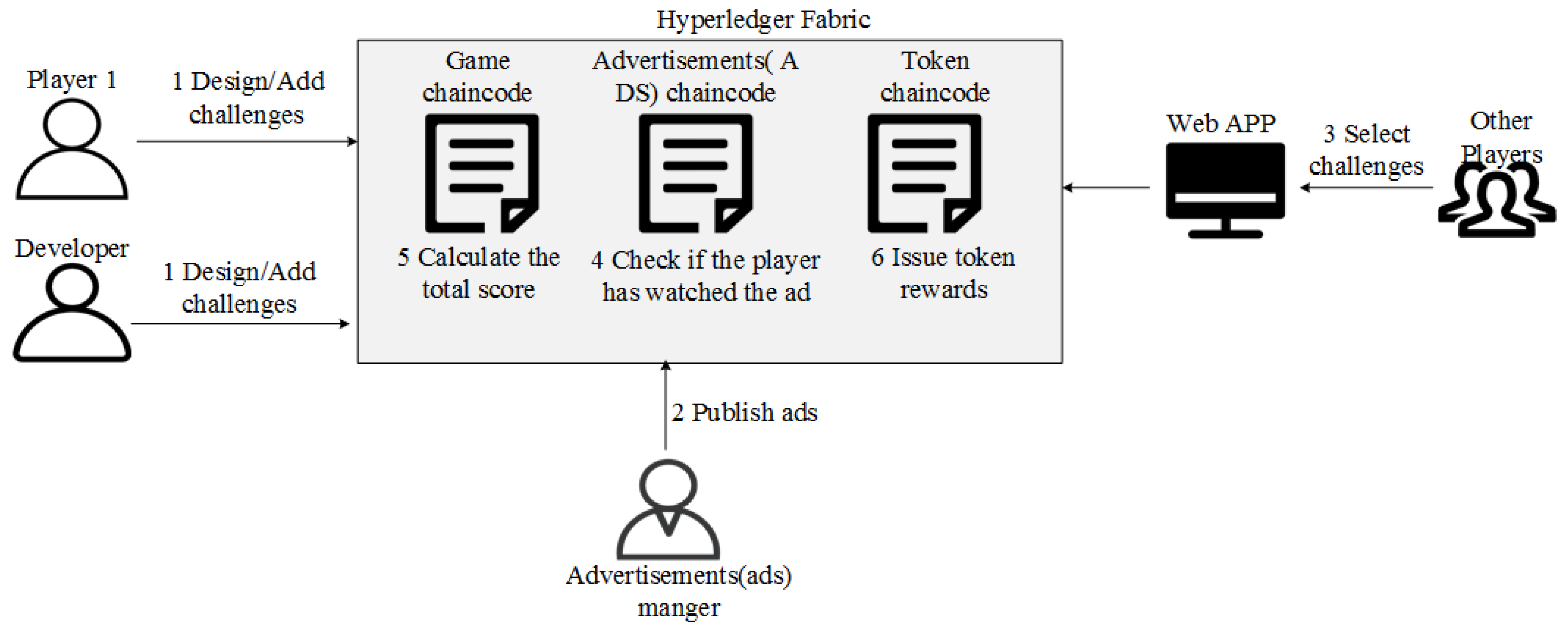
4.3. Smart Toys and IoT Games
4.4. Smart Fitness
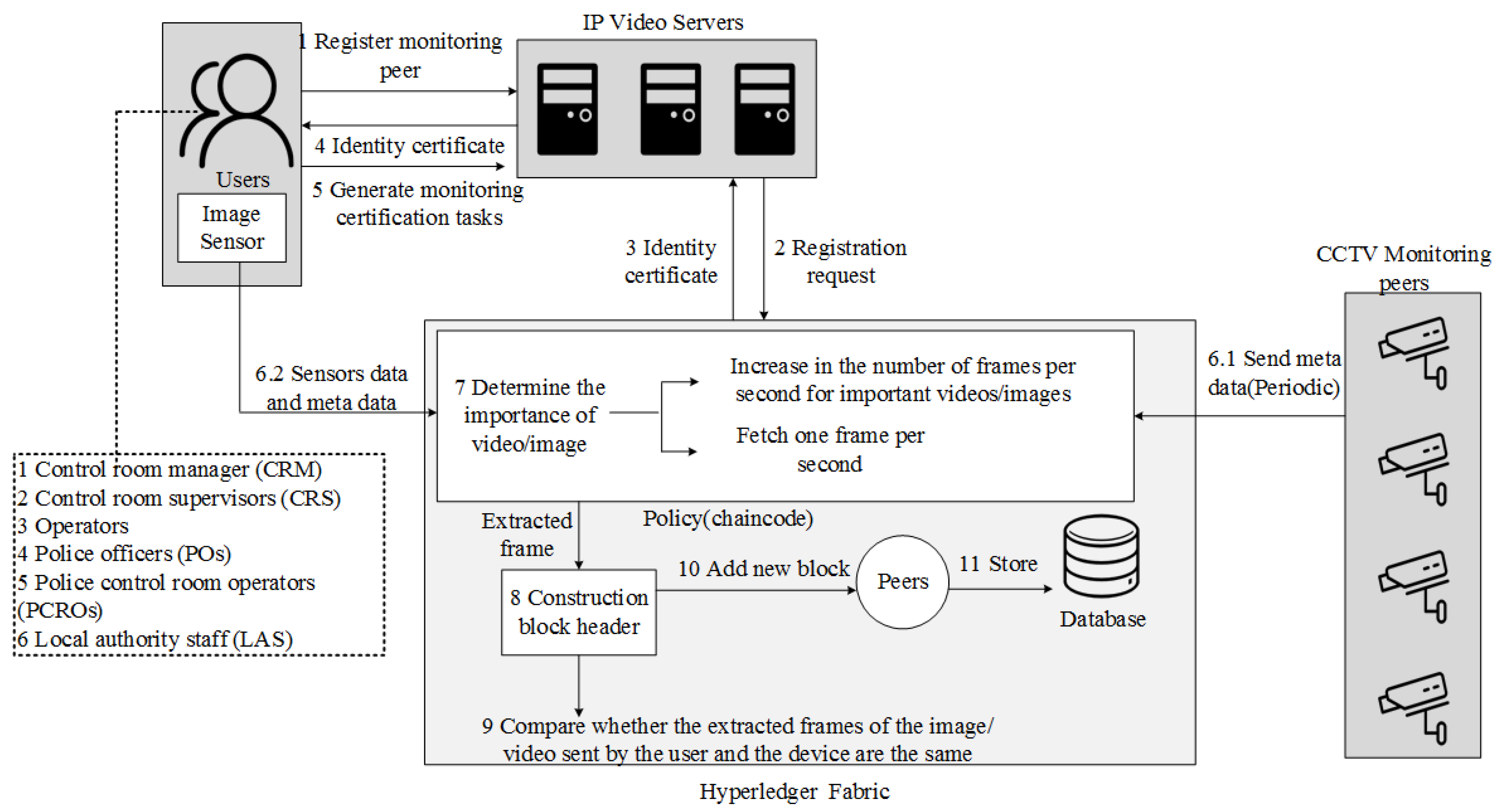
4.5. Smart Urban Monitoring
4.6. Smart Grid
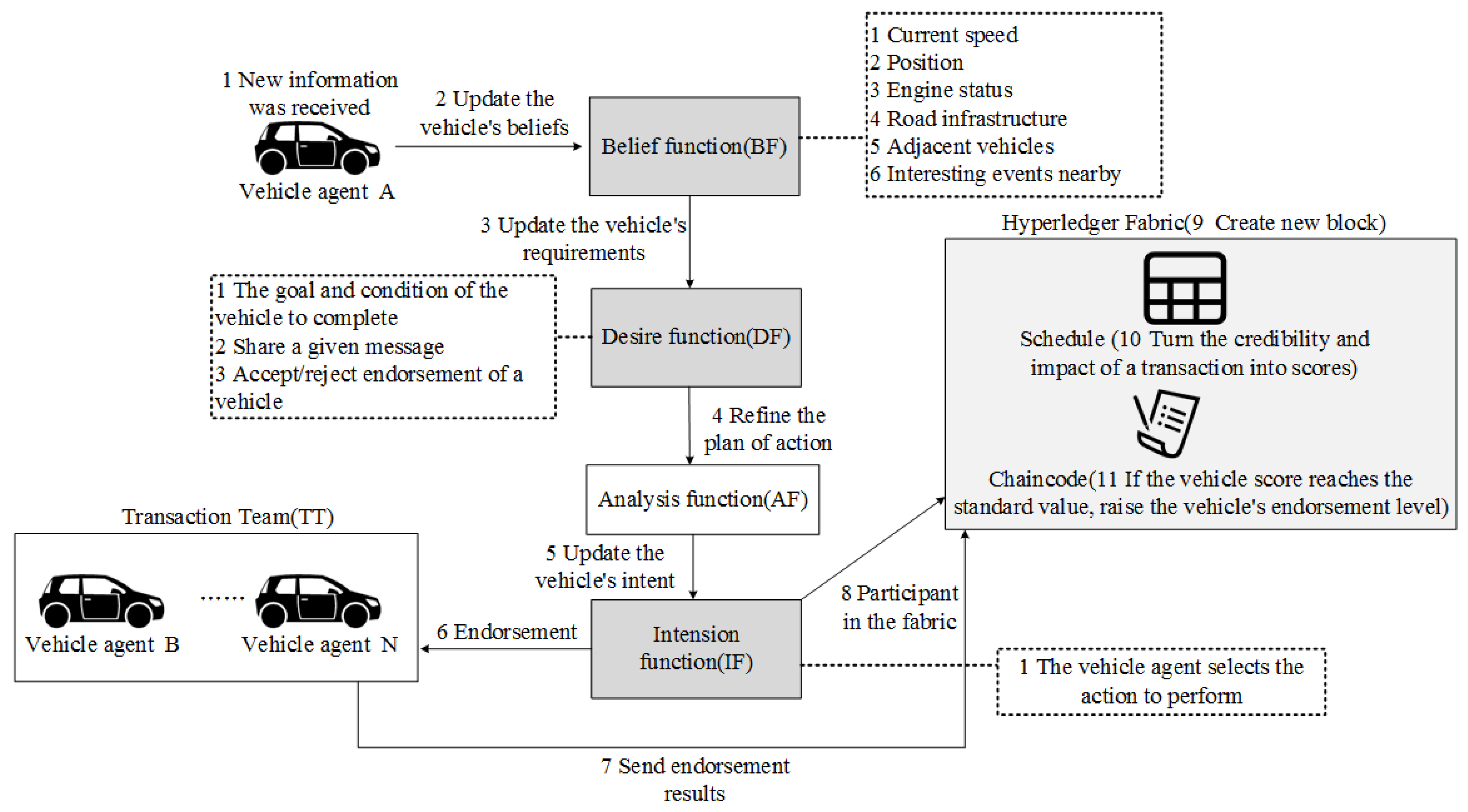
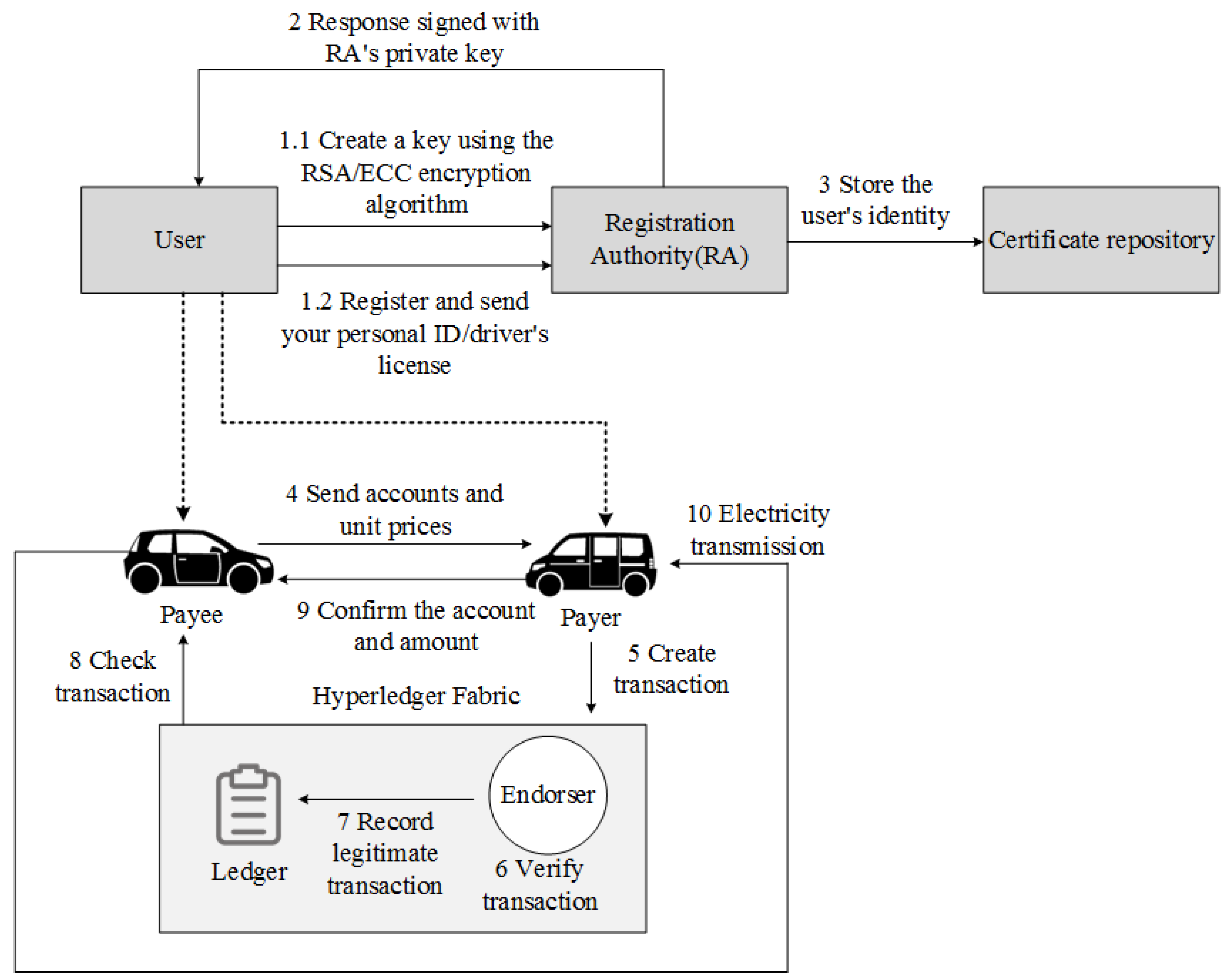
4.7. Smart Transportation
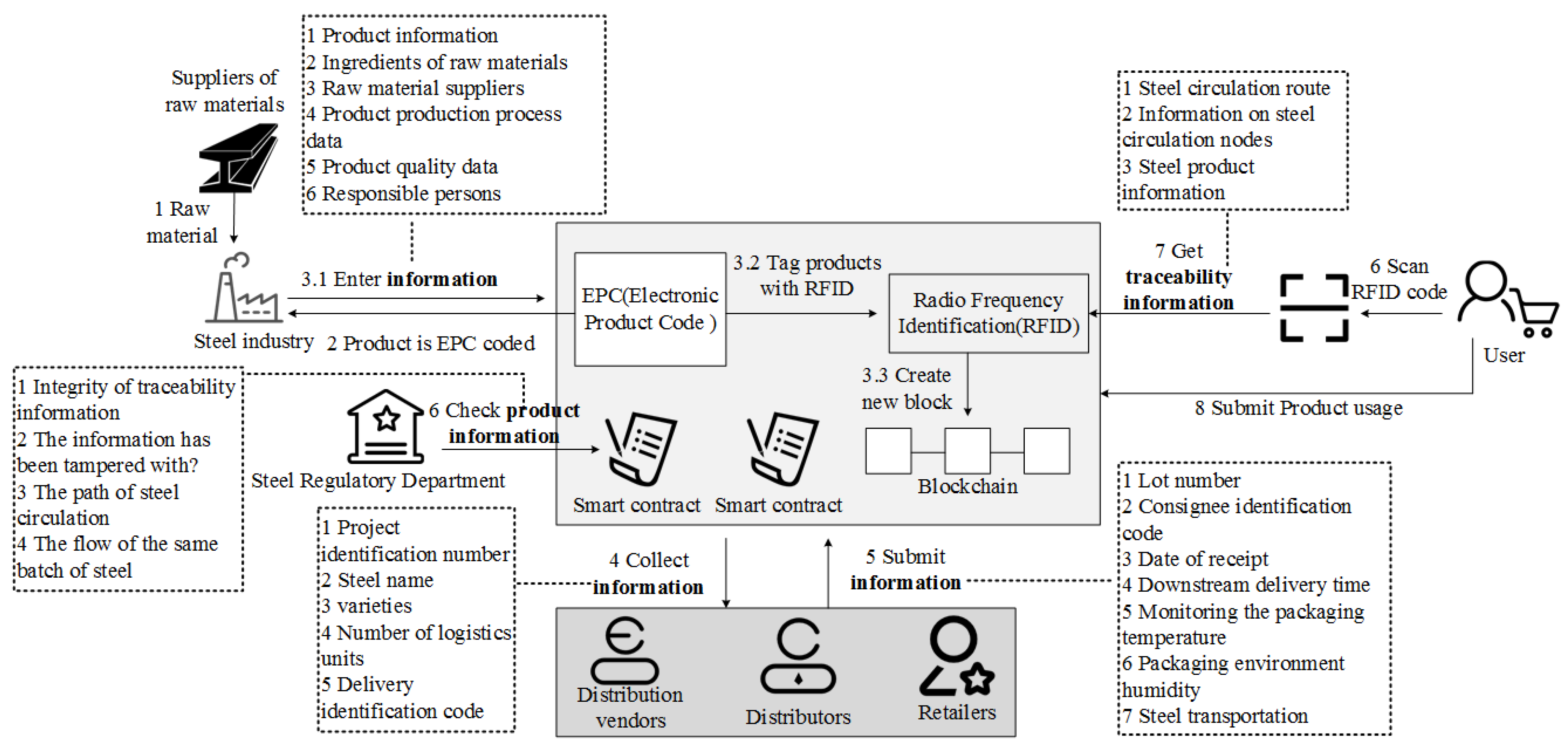
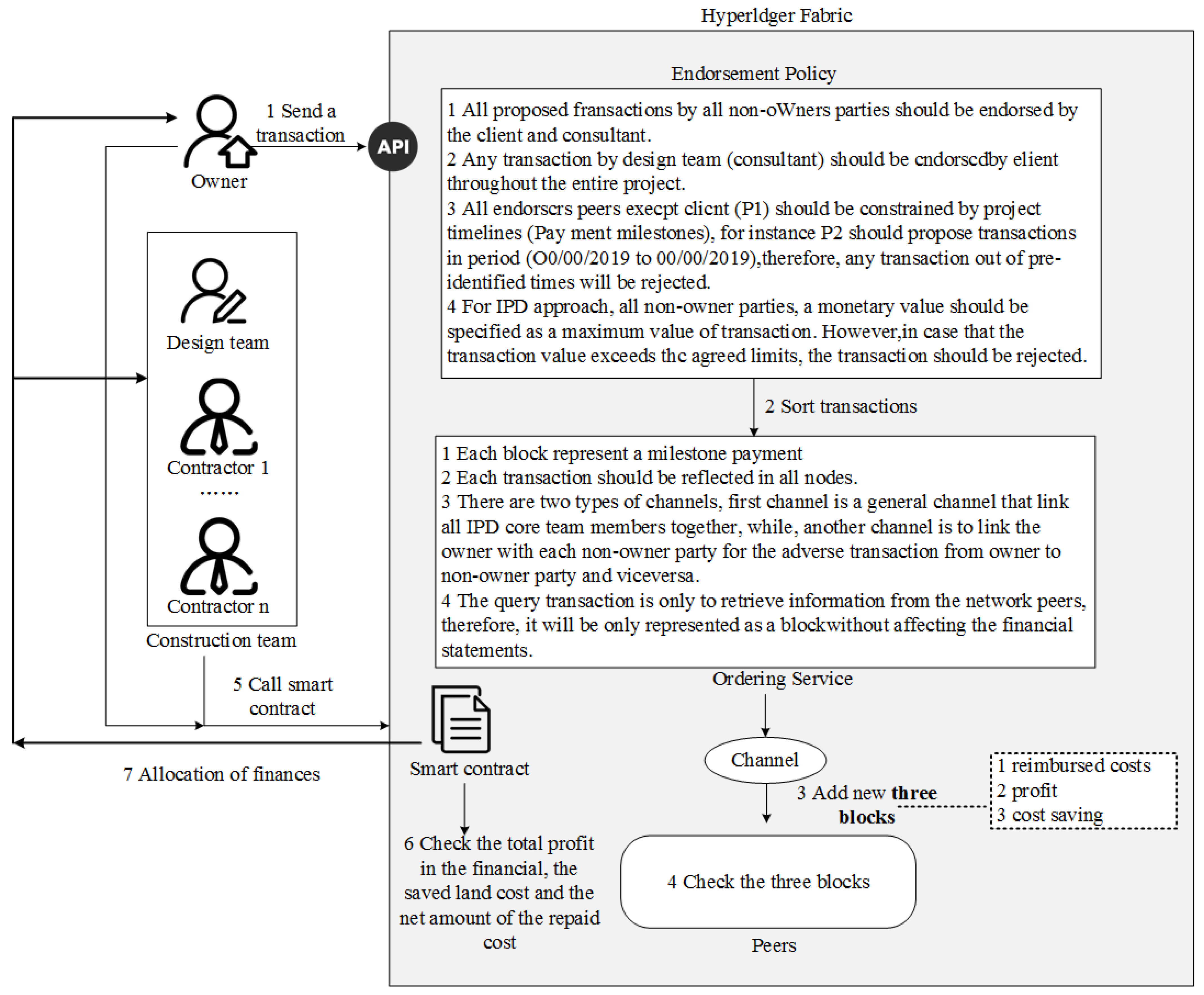
4.8. Smart Construction Project
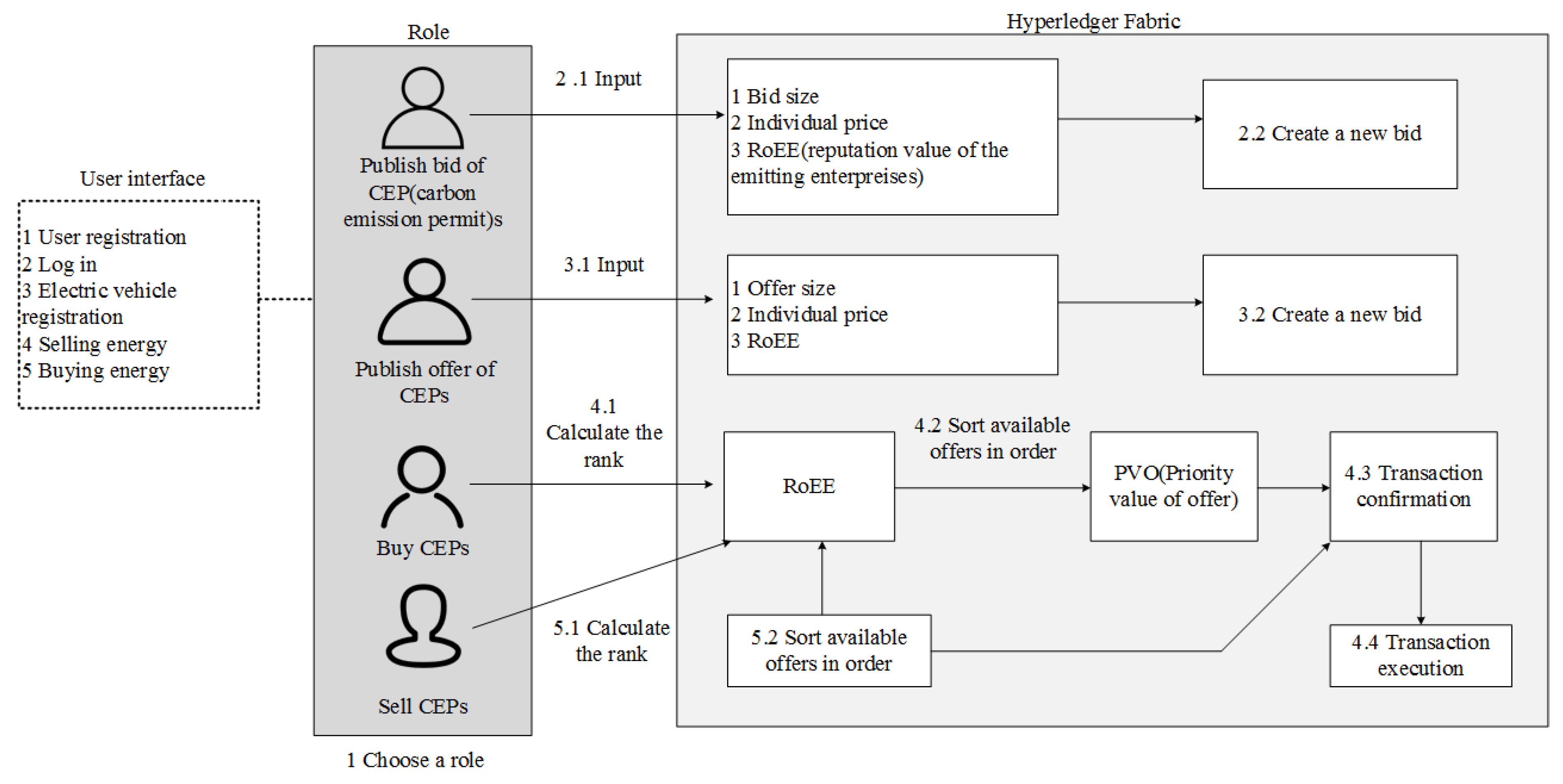
4.9. Smart Energy (Energy Saving Direction)
5. Future Trends and Prospects
- 1.
- Low-power consensus mechanism
- 2.
- Intelligent transaction validation
- 3.
- Mixed on-chain and off-chain storage
- 4.
- Customized incentives
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Khan, M.A.; Salah, K. IoT security: Review, blockchain solutions, and open challenges. Future Gener. Comput. Syst. 2018, 82, 395–411. [Google Scholar] [CrossRef]
- Cachin, C. Architecture of the hyperledger blockchain fabric. In Proceedings of the Workshop on Distributed Cryptocurrencies and Consensus Ledgers, Chicago, IL, USA, 25 July 2016; Volume 310, pp. 1–4. [Google Scholar]
- Elrom, E. Hyperledger. In The Blockchain Developer; Apress: Berkeley, CA, USA, 2019; pp. 299–348. [Google Scholar]
- Aggarwal, S.; Kumar, N. Hyperledger. In Advances in Computers; Elsevier: Amsterdam, The Netherlands, 2021; Volume 121, pp. 323–343. [Google Scholar]
- Blummer, T.; Sean, M.; Cachin, C. An Introduction to Hyperledger; Hyperledger Organization: San Francisco, CA, USA, 2018; Available online: https://www.hyperledger.org/wp-content/uploads/2018/08/HL_Whitepaper_IntroductiontoHyperledger.pdf (accessed on 18 December 2021).
- Leng, Z.; Tan, Z.; Wang, K. Application of Hyperledger in the Hospital Information Systems: A Survey. IEEE Access 2021, 9, 128965–128987. [Google Scholar] [CrossRef]
- Hyperledger, S. Introduction. Available online: https://sawtooth.hyperledger.org/docs/core/releases/latest/introduction.html (accessed on 17 March 2019).
- Ampel, B.; Patton, M.; Chen, H. Performance modeling of hyperledger sawtooth blockchain. In Proceedings of the 2019 IEEE International Conference on Intelligence and Security Informatics (ISI), Shenzhen, China, 1–3 July 2019; pp. 59–61. [Google Scholar]
- Moriggl, P.; Asprion, P.M.; Schneider, B. Blockchain technologies towards data privacy—hyperledger sawtooth as unit of analysis. In New Trends in Business Information Systems and Technology; Springer: Cham, Switzerland, 2021; pp. 299–313. [Google Scholar]
- Vlachou, V.; Kontzinos, C.; Markaki, O.; Kokkinakos, P.; Karakolis, V.; Psarras, J. Leveraging Hyperledger Iroha for the Issuance and Verification of Higher-Education Certificates. Int. J. Educ. Pedagog. Sci. 2020, 14, 755–763. [Google Scholar]
- Iushkevich, N.; Lebedev, A.; Šketa, R.; Takemiya, M. D3ledger: The decentralized digital depository platform for asset management based on hyperledger iroha. In Proceedings of the OTS 2019 Advanced Information Technology and Services, Maribor, Slovenia, 18–19 June 2019; pp. 29–36. [Google Scholar] [CrossRef]
- Available online: https://github.com/hyperledger/iroha/blob/main/README.md (accessed on 5 January 2022).
- Dunphy, P. A Note on the Blockchain Trilemma for Decentralized Identity: Learning from Experiments with Hyperledger Indy. arXiv 2022, arXiv:2204.05784. [Google Scholar]
- Bhattacharya, M.P.; Zavarsky, P.; Butakov, S. Enhancing the security and privacy of self-sovereign identities on hyperledger indy blockchain. In Proceedings of the 2020 International Symposium on Networks, Computers and Communications (ISNCC), Montreal, QC, Canada, 16–18 June 2020; pp. 1–7. [Google Scholar]
- Available online: https://www.edx.org/course/identity-in-hyperledger-aries-indy-and-ursa (accessed on 5 January 2022).
- Abramson, W.; Hall, A.J.; Papadopoulos, P.; Pitropakis, N.; Buchanan, W.J. A distributed trust framework for privacy-preserving machine learning. In Proceedings of the International Conference on Trust and Privacy in Digital Business, Bratislava, Slovakia, 3 June 2020; pp. 205–220. [Google Scholar]
- Dalla Palma, S.; Pareschi, R.; Zappone, F. What is your distributed (hyper) ledger? In Proceedings of the 2021 IEEE/ACM 4th International Workshop on Emerging Trends in Software Engineering for Blockchain (WETSEB), Madrid, Spain, 31 May 2021; pp. 27–33. [Google Scholar]
- Available online: https://besu.hyperledger.org/en/stable/ (accessed on 6 January 2022).
- Keramidas, G.; Voros, N.; Hübner, M. Components and Services for IoT Platforms; Springer International Publishing: Cham, Switzerland, 2016. [Google Scholar]
- Olson, K.; Bowman, M.; Mitchell, J.; Amundson, S.; Middleton, D.; Montgomery, C. Sawtooth: An introduction. The Linux Foundation, Jan, 2018. Available online: https://www.hyperledger.org/wp-content/uploads/2018/01/Hyperledger_Sawtooth_WhitePaper.pdf (accessed on 6 January 2022).
- Lee, I.; Lee, K. The Internet of Things (IoT): Applications, investments, and challenges for enterprises. Bus. Horizons. 2015, 58, 431–440. [Google Scholar] [CrossRef]
- Wang, H.; Zhang, J. Blockchain based data integrity verification for large-scale IoT data. IEEE Access 2019, 7, 164996–165006. [Google Scholar] [CrossRef]
- Yang, H.; Yuan, J.; Yao, H.; Yao, Q.; Yu, A.; Zhang, J. Blockchain-based hierarchical trust networking for JointCloud. IEEE Internet Things J. 2019, 7, 1667–1677. [Google Scholar] [CrossRef]
- Dib, O.; Huyart, C.; Toumi, K. A novel data exploitation framework based on blockchain. Pervasive Mob. Comput. 2020, 61, 101104. [Google Scholar] [CrossRef]
- Cao, Y.; Jia, F.; Manogaran, G. Efficient traceability systems of steel products using blockchain-based industrial Internet of Things. IEEE Trans. Ind. Inform. 2019, 16, 6004–6012. [Google Scholar] [CrossRef]
- Seshadri, S.S.; Rodriguez, D.; Subedi, M.; Choo, K.-K.R.; Ahmed, S.; Chen, Q.; Lee, J. Iotcop: A blockchain-based monitoring framework for detection and isolation of malicious devices in internet-of-things systems. IEEE Internet Things J. 2020, 8, 3346–3359. [Google Scholar] [CrossRef]
- Kim, J.H.; Lee, S.; Hong, S. Autonomous Operation Control of IoT Blockchain Networks. Electronics 2021, 10, 204. [Google Scholar] [CrossRef]
- Košťál, K.; Helebrandt, P.; Belluš, M.; Ries, M.; Kotuliak, I. Management and monitoring of IoT devices using blockchain. Sensors 2019, 19, 856. [Google Scholar] [CrossRef] [Green Version]
- Mbarek, B.; Jabeur, N.; Pitner, T.; Yasar, A.-U.-H. Mbs: Multilevel blockchain system for IoT. Pers. Ubiquit. Comput. 2021, 25, 247–254. [Google Scholar] [CrossRef]
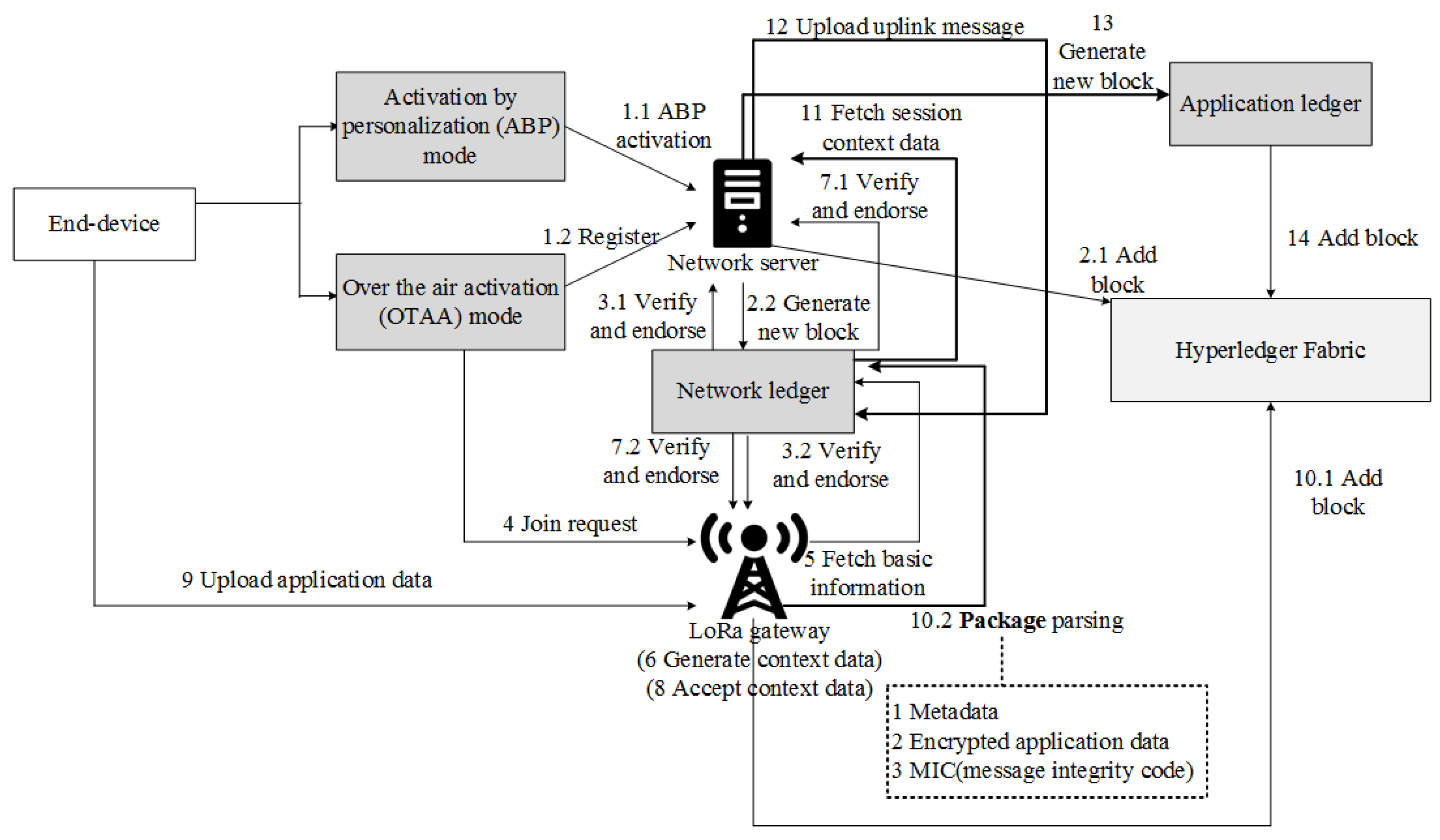
- Ribeiro, V.; Holanda, R.; Ramos, A.; Rodrigues, J.J.P.C. Enhancing key management in LoRaWAN with permissioned blockchain. Sensors 2020, 20, 3068. [Google Scholar] [CrossRef]
- Hang, L.; Kim, D.H. Design and implementation of an integrated iot blockchain platform for sensing data integrity. Sensors 2019, 19, 2228. [Google Scholar] [CrossRef] [Green Version]
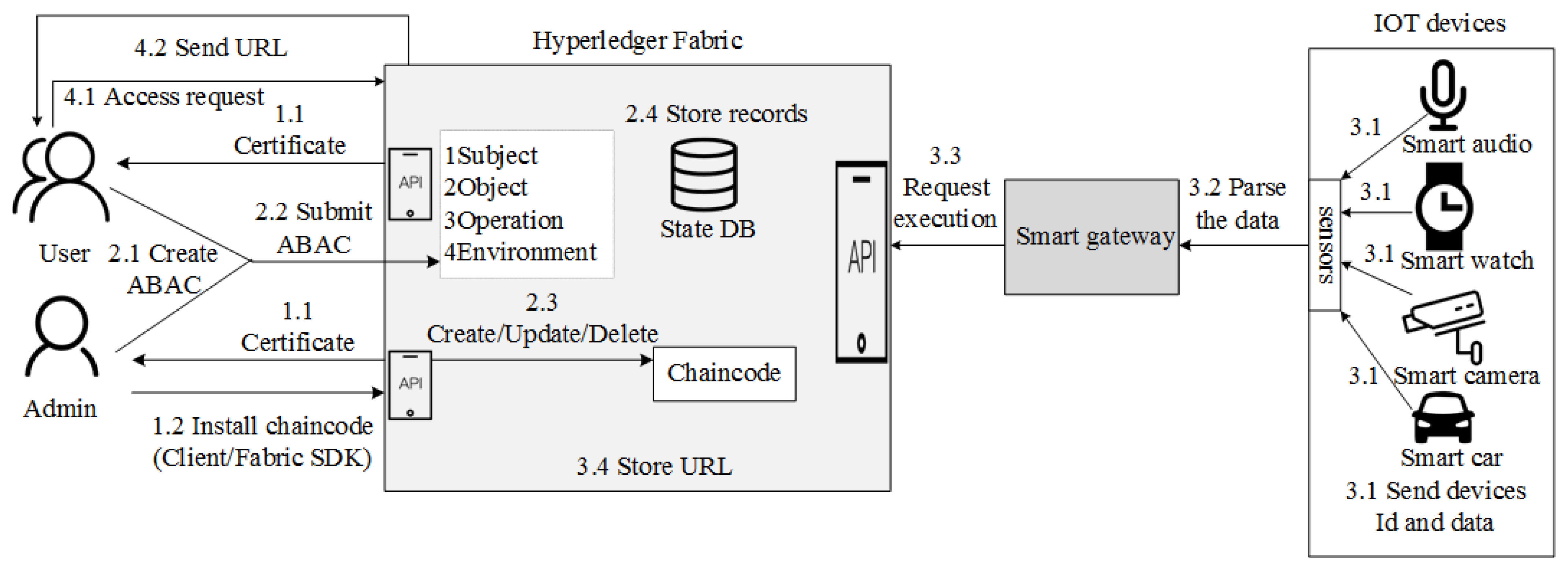
- Liu, H.; Han, D.; Li, D. Fabric-IoT: A blockchain-based access control system in IoT. IEEE Access 2020, 8, 18207–18218. [Google Scholar] [CrossRef]
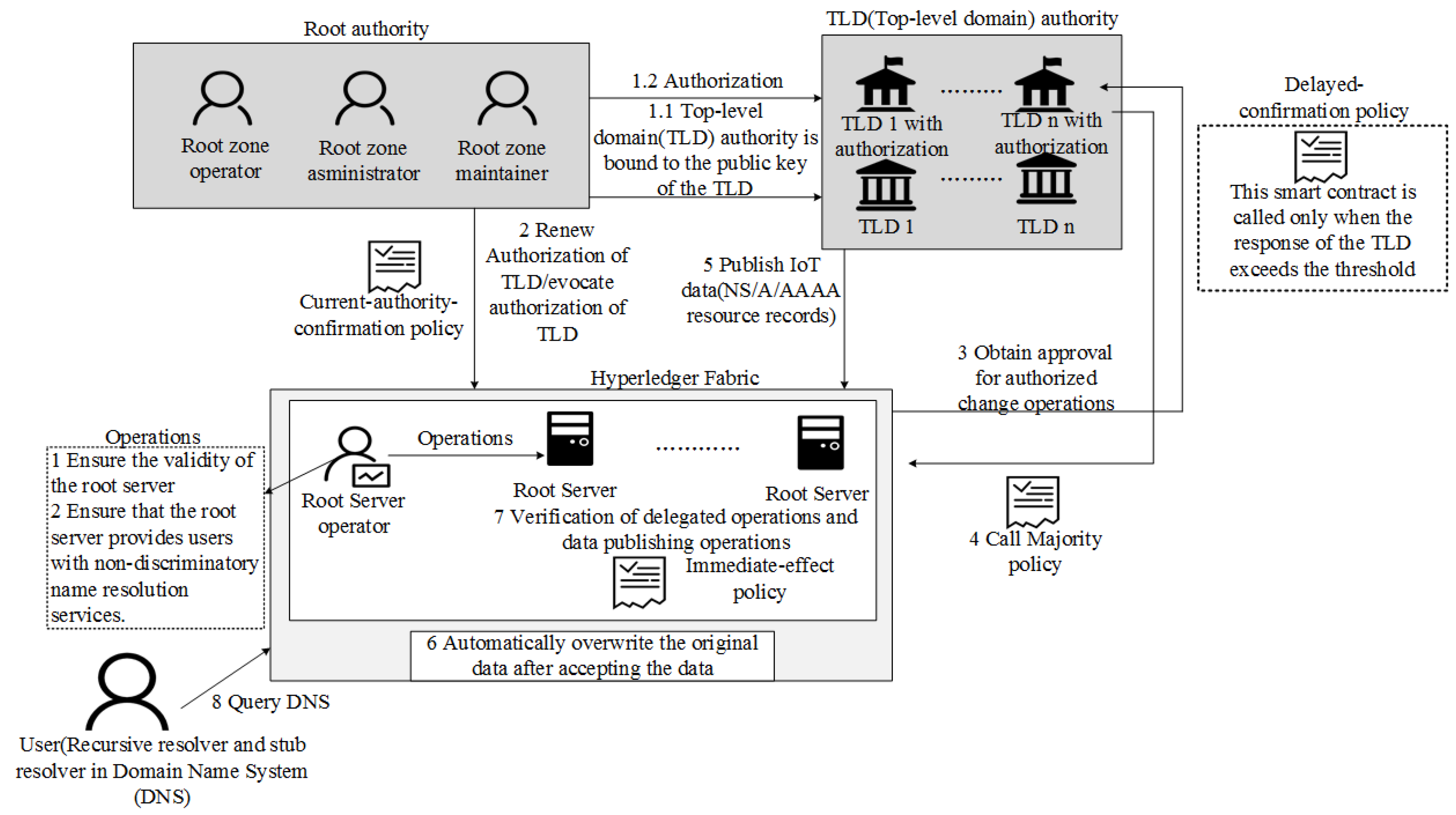
- Zhang, Y.; Liu, W.; Xia, Z.; Wang, Z.; Liu, L.; Zhang, W.; Zhang, H.; Fang, B. Blockchain-Based DNS Root Zone Management Decentralization for Internet of Things. Wirel. Commun. Mob. Comput. 2021, 2021, 6620236. [Google Scholar] [CrossRef]
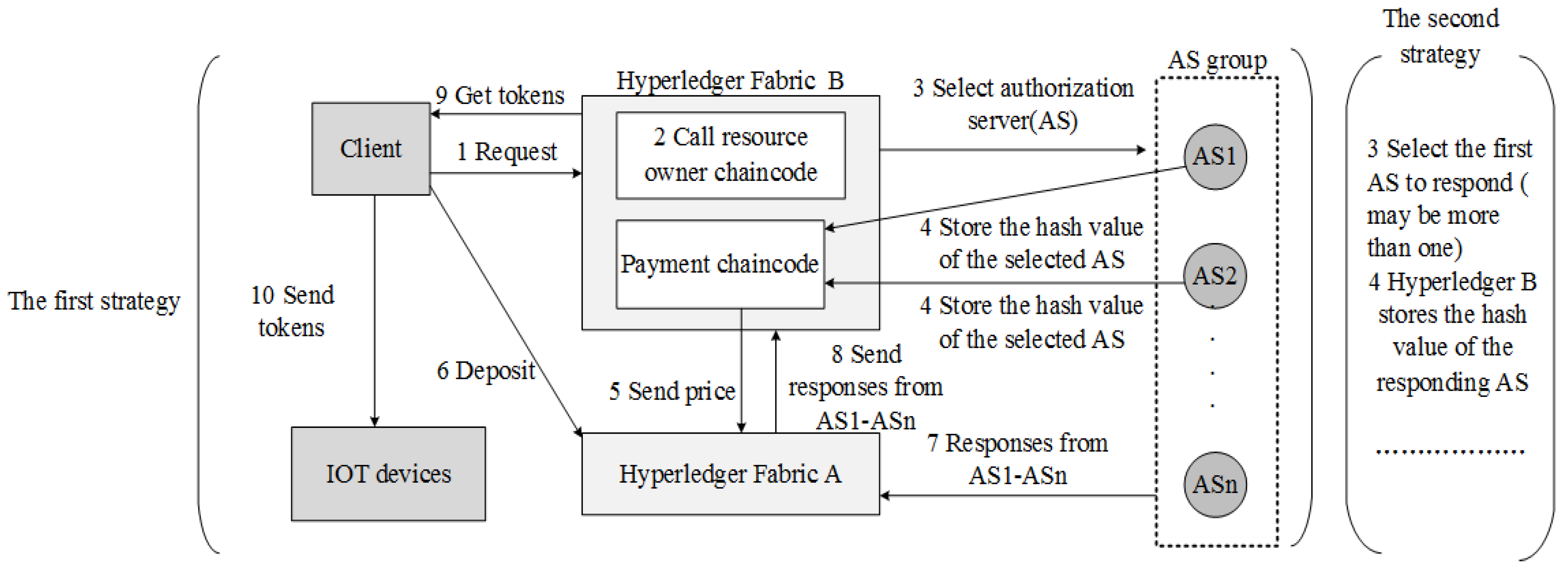
- Chi, J.; Li, Y.; Huang, J.; Liu, J.; Jin, Y.; Chen, C.; Qiu, T. A secure and efficient data sharing scheme based on blockchain in industrial Internet of Things. J. Netw. Comput. Appl. 2020, 167, 102710. [Google Scholar] [CrossRef]
- Yu, D.; Liu, G.; Guo, M.; Liu, X. An improved K-medoids algorithm based on step increasing and optimizing medoids. Expert Syst. Appl. 2018, 92, 464–473. [Google Scholar] [CrossRef]
- Fauzi, M.A.; Utomo, D.C.; Setiawan, B.D.; Pramukantoro, E.S. Automatic essay scoring system using n-gram and cosine similarity for gamification based e-learning. In Proceedings of the International Conference on Advances in Image Processing, Bangkok, Thailand, 25–27 August 2017; pp. 151–155. [Google Scholar]
- Siris, V.A.; Dimopoulos, D.; Fotiou, N.; Voulgaris, S.; Polyzos, G.C. Decentralized authorization in constrained IoT environments exploiting interledger mechanisms. Comput. Commun. 2020, 152, 243–251. [Google Scholar] [CrossRef]
- Kakei, S.; Shiraishi, Y.; Mohri, M.; Nakamura, T.; Hashimoto, M.; Saito, S. Cross-certification towards distributed authentication infrastructure: A case of hyperledger fabric. IEEE Access 2020, 8, 135742–135757. [Google Scholar] [CrossRef]
- Pajooh, H.; Rashid, M.; Alam, F.; Demidenko, S. Multi-layer blockchain-based security architecture for internet of things. Sensors 2021, 21, 772. [Google Scholar] [CrossRef]
- Zhou, L.; Wang, L.; Ai, T.; Sun, Y. BeeKeeper 2.0: Confidential blockchain-enabled IoT system with fully homomorphic computation. Sensors 2018, 18, 3785. [Google Scholar] [CrossRef] [Green Version]
- Hou, L.; Zheng, K.; Liu, Z.; Xu, X.; Wu, T. Design and prototype implementation of a blockchain-enabled LoRa system with edge computing. IEEE Internet Things J. 2020, 8, 2419–2430. [Google Scholar] [CrossRef]
- Yang, X.; Zhang, S.; Liu, J.; Gao, Q.; Dong, S.; Zhou, C. Deep learning for smart fish farming: Applications, opportunities and challenges. Rev. Aquac. 2021, 13, 66–90. [Google Scholar] [CrossRef]
- Feng, Y.; Niu, H.; Wang, F.; Ivey, S.J.; Wu, J.J.; Qi, H.; Almeida, R.A.; Eda, S.; Cao, Q. SocialCattle: IoT-based Mastitis Detection and Control through Social Cattle Behavior Sensing in Smart Farms. IEEE Internet Things J. 2021, 9, 10130–10138. [Google Scholar] [CrossRef]
- Hang, L.; Ullah, I.; Kim, D.H. A secure fish farm platform based on blockchain for agriculture data integrity. Comput. Electron. Agric. 2020, 170, 105251. [Google Scholar] [CrossRef]
- Lee, S.; Lee, J.; Hong, S.; Kim, J.-H. Lightweight end-to-end blockchain for IoT applications. KSII Trans. Internet Inf. Syst. 2020, 14, 3224–3242. [Google Scholar]
- Kara, N.; Cagiltay, K. Smart toys for preschool children: A design and development research. Electron. Commer. Res. Appl. 2020, 39, 100909. [Google Scholar] [CrossRef]
- Yang, J.; Lu, Z.; Wu, J. Smart-toy-edge-computing-oriented data exchange based on blockchain. J. Syst. Archit. 2018, 87, 36–48. [Google Scholar] [CrossRef]
- Manzoor, A.; Samarin, M.; Mason, D.; Ylianttila, M. Scavenger Hunt: Utilization of Blockchain and IoT for a location-based Game. IEEE Access 2020, 8, 204863–204879. [Google Scholar] [CrossRef]
- Pittaras, I.; Fotiou, N.; Siris, V.; Polyzos, G. Beacons and blockchains in the mobile gaming ecosystem: A feasibility analysis. Sensors 2021, 21, 862. [Google Scholar] [CrossRef]
- Farrokhi, A.; Farahbakhsh, R.; Rezazadeh, J.; Minerva, R. Application of Internet of Things and artificial intelligence for smart fitness: A survey. Comput. Netw. 2021, 189, 107859. [Google Scholar] [CrossRef]
- Jamil, F.; Iqbal, N.; Imran; Ahmad, S.; Kim, D. Peer-to-peer energy trading mechanism based on blockchain and machine learning for sustainable electrical power supply in smart grid. IEEE Access 2021, 9, 39193–39217. [Google Scholar] [CrossRef]
- Khan, P.W.; Byun, Y.C.; Park, N. A data verification system for CCTV surveillance cameras using blockchain technology in smart cities. Electronics 2020, 9, 484. [Google Scholar] [CrossRef] [Green Version]
- Dileep, G. A survey on smart grid technologies and applications. Renew. Energy 2020, 146, 2589–2625. [Google Scholar] [CrossRef]
- Li, F.; Qiao, W.; Sun, H.; Wan, H.; Wang, J.; Xia, Y.; Xu, Z.; Zhang, P. Smart transmission grid: Vision and framework. IEEE Trans. Smart Grid. 2010, 1, 168–177. [Google Scholar] [CrossRef]
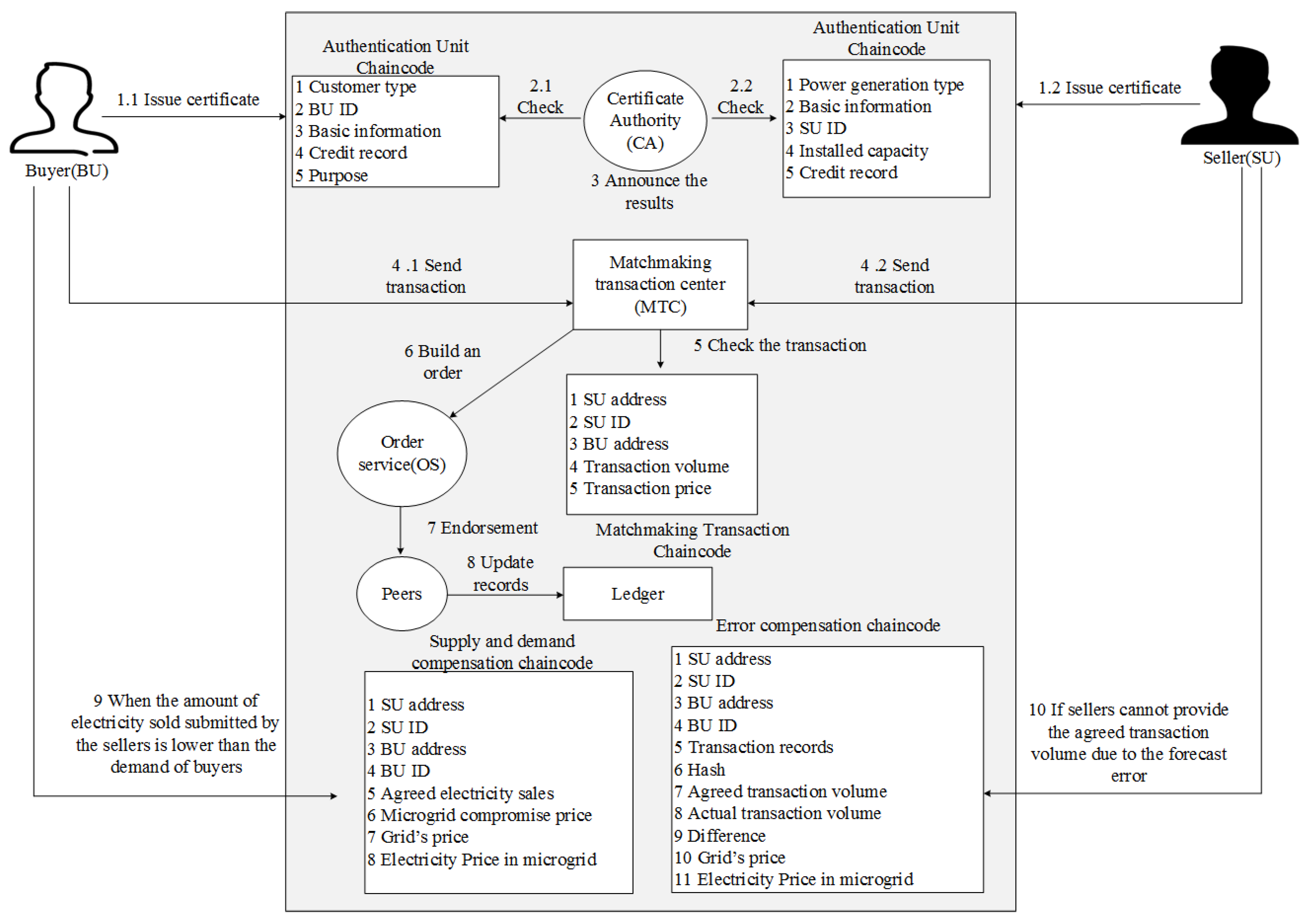
- Zhao, W.; Lv, J.; Yao, X.; Zhao, J.; Jin, Z.; Qiang, Y.; Che, Z.; Wei, C. Consortium Blockchain-Based microgrid market transaction research. Energies 2019, 12, 3812. [Google Scholar] [CrossRef] [Green Version]
- Li, Y.; Hu, B. An iterative two-layer optimization charging and discharging trading scheme for electric vehicle using consortium blockchain. IEEE Trans. Smart Grid 2019, 11, 2627–2637. [Google Scholar] [CrossRef]
- Li, Y.; Hu, B. A consortium blockchain-enabled secure and privacy-preserving optimized charging and discharging trading scheme for electric vehicles. IEEE Trans. Ind. Inform. 2020, 17, 1968–1977. [Google Scholar] [CrossRef]
- Yu, Y.; Guo, Y.; Min, W.; Zeng, F. Trusted transactions in micro-grid based on blockchain. Energies 2019, 12, 1952. [Google Scholar] [CrossRef] [Green Version]
- Lohachab, A.; Garg, S.; Kang, B.H.; Amin, M.B. Performance evaluation of Hyperledger Fabric-enabled framework for pervasive peer-to-peer energy trading in smart Cyber–Physical Systems. Future Gener. Comput. Syst. 2021, 118, 392–416. [Google Scholar] [CrossRef]
- Jamil, F.; Kahng, H.K.; Kim, S.; Kim, D.-H. Towards Secure Fitness Framework Based on IoT-Enabled Blockchain Network Integrated with Machine Learning Algorithms. Sensors 2021, 21, 1640. [Google Scholar] [CrossRef]
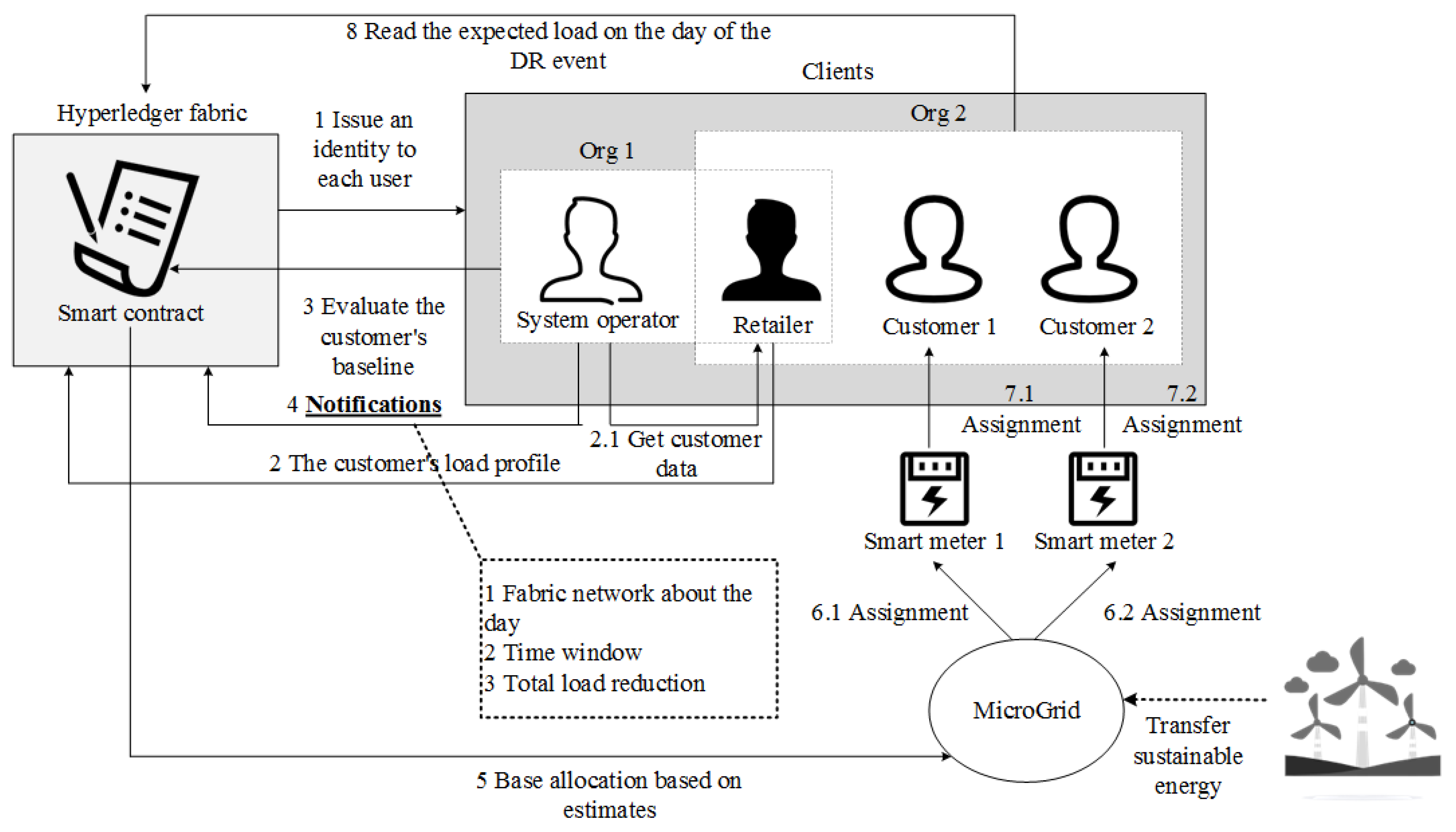
- Sciume, G.; Palacios-Garcia, E.J.; Gallo, P.; Sanseverino, E.R.; Vasquez, J.C.; Guerrero, J.M. Demand response service certification and customer baseline evaluation using blockchain technology. IEEE Access 2020, 8, 139313–139331. [Google Scholar] [CrossRef]
- Wang, L.; Jiao, S.; Xie, Y.; Mubaarak, S.; Zhang, D.; Liu, J.; Jiang, S.; Zhang, Y.; Li, M. A Permissioned Blockchain-Based Energy Management System for Renewable Energy Microgrids. Sustainability 2021, 13, 1317. [Google Scholar] [CrossRef]
- Nallaperuma, D.; Nawaratne, R.; Bandaragoda, T.; Adikari, A.; Nguyen, S.; Kempitiya, T.; De Silva, D.; Alahakoon, D.; Pothuhera, D. Online incremental machine learning platform for big data-driven smart traffic management. IEEE Trans. Intell. Transp. Syst. 2019, 20, 4679–4690. [Google Scholar] [CrossRef]
- Djahel, S.; Doolan, R.; Muntean, G.-M.; Murphy, J. A communications-oriented perspective on traffic management systems for smart cities: Challenges and innovative approaches. IEEE Commun. Surv. Tutor. 2014, 17, 125–151. [Google Scholar] [CrossRef]
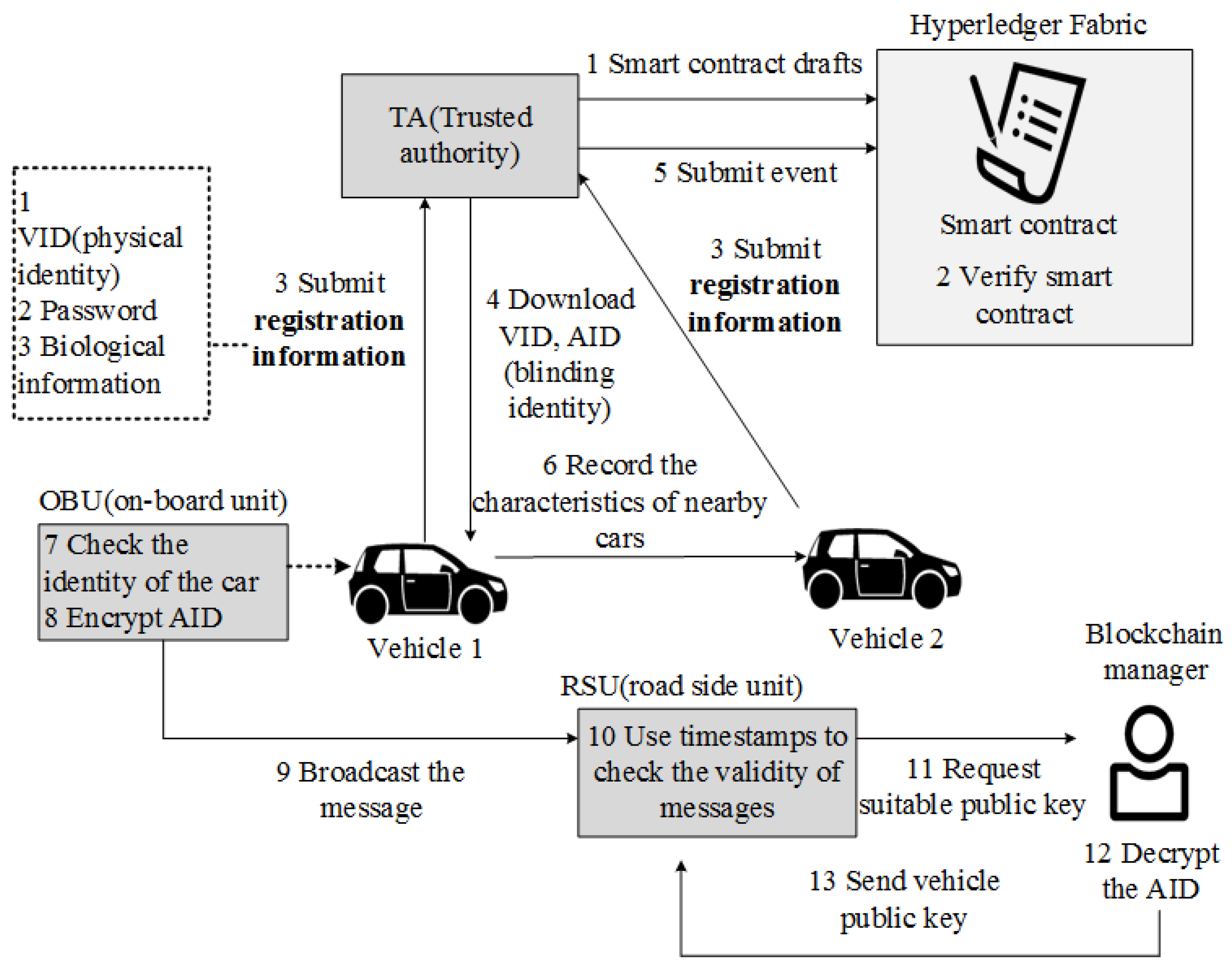
- Feng, Q.; He, D.; Zeadally, S.; Liang, K. BPAS: Blockchain-Assisted Privacy-Preserving Authentication System for Vehicular Ad Hoc Networks. IEEE Trans. Ind. Inform. 2020, 16, 4146–4155. [Google Scholar] [CrossRef]
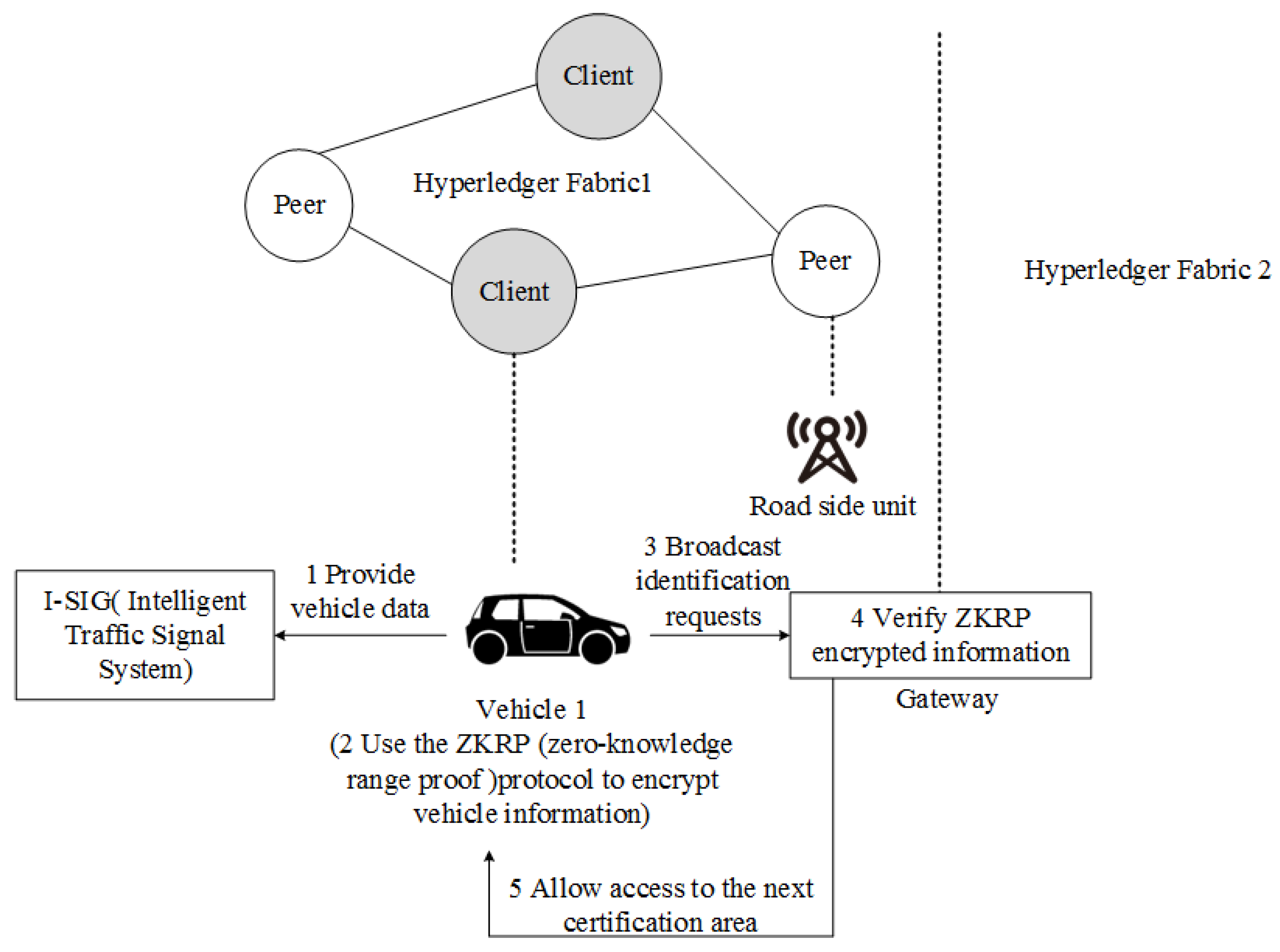
- Li, W.; Guo, H.; Nejad, M.; Shen, C.-C. Privacy-preserving traffic management: A blockchain and zero-knowledge proof inspired approach. IEEE Access 2020, 8, 181733–181743. [Google Scholar] [CrossRef]
- Luo, G.; Shi, M.; Zhao, C.; Shi, Z. Hash-Chain-Based Cross-Regional Safety Authentication for Space-Air-Ground Integrated VANETs. Appl. Sci. 2020, 10, 4206. [Google Scholar] [CrossRef]
- Buzachis, A.; Celesti, A.; Galletta, A.; Fazio, M.; Fortino, G.; Villari, M. A multi-agent autonomous intersection management (MA-AIM) system for smart cities leveraging edge-of-things and Blockchain. Inf. Sci. 2020, 522, 148–163. [Google Scholar] [CrossRef]
- Mbarek, B.; Jabeur, N.; Pitner, T.; Yasar, A.-U.-H. Empowering communications in vehicular networks with an intelligent blockchain-based solution. Sustainability 2020, 12, 7917. [Google Scholar] [CrossRef]
- Xiao, Y.; Liu, Y.; Li, T. Edge computing and blockchain for quick fake news detection in IoV. Sensors 2020, 20, 4360. [Google Scholar] [CrossRef]
- Chen, W.; Chen, Y.; Chen, X.; Zheng, Z. Toward secure data sharing for the IoV: A quality-driven incentive mechanism with on-chain and off-chain guarantees. IEEE Internet Things J. 2019, 7, 1625–1640. [Google Scholar] [CrossRef]
- Gao, F.; Zhu, L.; Shen, M.; Sharif, K.; Wan, Z.; Ren, K. A blockchain-based privacy-preserving payment mechanism for vehicle-to-grid networks. IEEE Network 2018, 32, 184–192. [Google Scholar] [CrossRef]
- Chiu, W.Y.; Meng, W. EdgeTC-a PBFT blockchain-based ETC scheme for smart cities. Peer Peer Netw. Appl. 2021, 14, 2874–2886. [Google Scholar] [CrossRef]
- Bartolomeu, P.C.; Vieira, E.; Ferreira, J. Pay as You Go: A Generic Crypto Tolling Architecture. IEEE Access 2020, 8, 196212–196222. [Google Scholar] [CrossRef]
- Lee, Y.; Jeong, S.; Masood, A.; Park, L.; Dao, N.-N.; Cho, S. Trustful Resource Management for Service Allocation in Fog-Enabled Intelligent Transportation Systems. IEEE Access 2020, 8, 147313–147322. [Google Scholar] [CrossRef]
- Lee, D.; Lee, S.H.; Masoud, N.; Krishnan, M.S.; Li, V.C. Integrated digital twin and blockchain framework to support accountable information sharing in construction projects. Autom. Constr. 2021, 127, 103688. [Google Scholar] [CrossRef]
- Haaskjold, H.; Andersen, B.; Langlo, J.A. Dissecting the project anatomy: Understanding the cost of managing construction projects. Prod. Plan. Control. 2021, 1–22. [Google Scholar] [CrossRef]
- Suliyanti, W.N.; Sari, R.F. Blockchain-Based Implementation of Building Information Modeling Information Using Hyperledger Composer. Sustainability 2021, 13, 321. [Google Scholar] [CrossRef]
- Elghaish, F.; Abrishami, S.; Hosseini, M.R. Integrated project delivery with blockchain: An automated financial system. Autom. Constr. 2020, 114, 103182. [Google Scholar] [CrossRef]
- Yang, R.; Wakefield, R.; Lyu, S.; Jayasuriya, S.; Han, Y.; Yi, X.; Yang, X.; Amarasinghe, G.; Chen, S. Public and private blockchain in construction business process and information integration. Autom. Constr. 2020, 118, 103276. [Google Scholar] [CrossRef]
- Sheng, D.; Ding, L.; Zhong, B.; Love, P.E.; Luo, H.; Chen, J. Construction quality information management with blockchains. Autom. Constr. 2020, 120, 103373. [Google Scholar] [CrossRef]
- Yuan, P.; Xiong, X.; Lei, L.; Zheng, K. Design and implementation on hyperledger-based emission trading system. IEEE Access 2018, 7, 6109–6116. [Google Scholar] [CrossRef]
- Hu, Z.; Du, Y.; Rao, C.; Goh, M. Delegated Proof of Reputation Consensus Mechanism for Blockchain-Enabled Distributed Carbon Emission Trading System. IEEE Access 2020, 8, 214932–214944. [Google Scholar] [CrossRef]
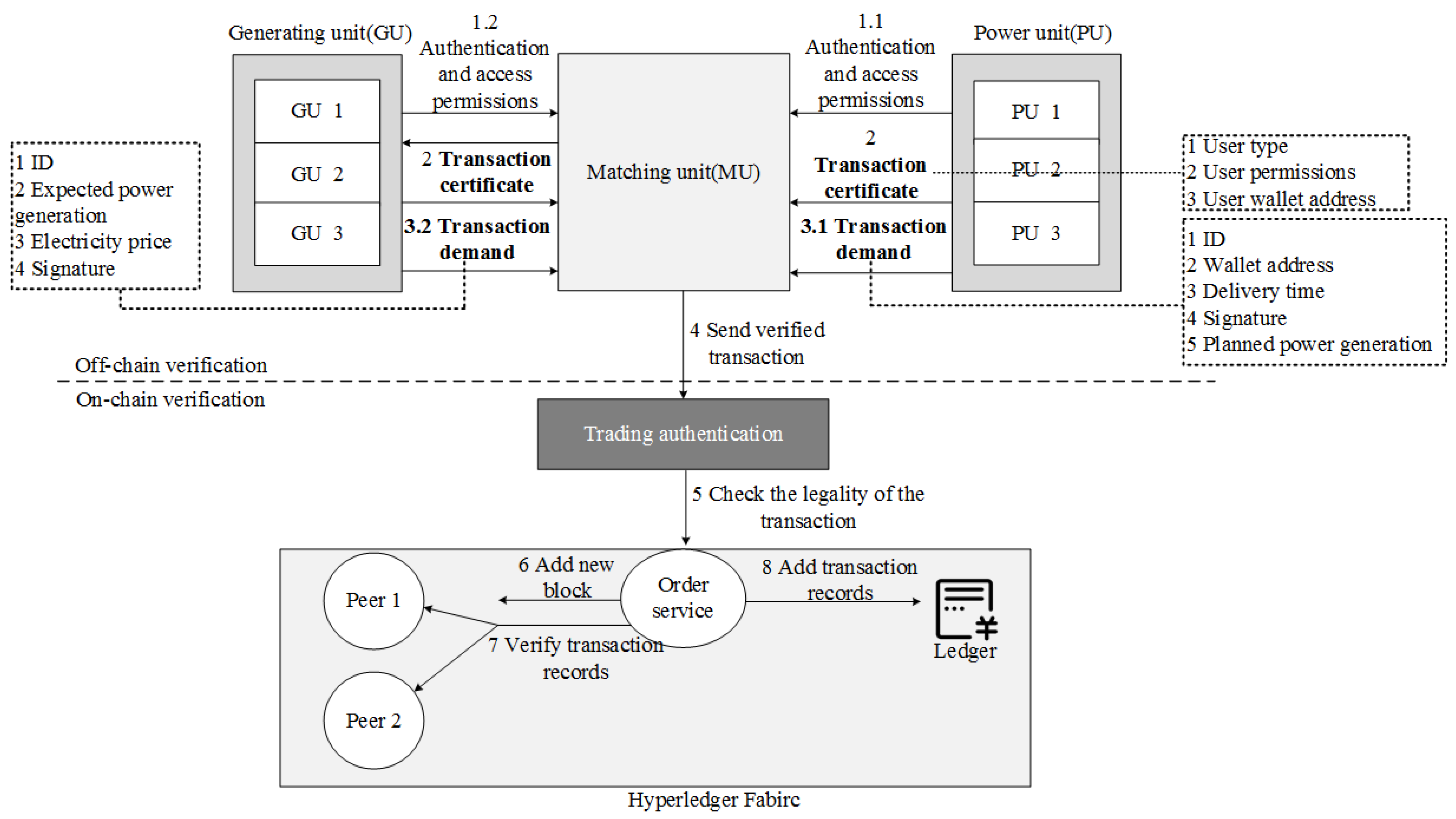
- Che, Z.; Wang, Y.; Zhao, J.; Qiang, Y.; Ma, Y.; Liu, J. A distributed energy trading authentication mechanism based on a consortium blockchain. Energies 2019, 12, 2878. [Google Scholar] [CrossRef] [Green Version]
- Silva, F.C.; Ahmed, M.A.; Martínez, J.M.; Kim, Y.-C. Design and implementation of a blockchain-based energy trading platform for electric vehicles in smart campus parking lots. Energies 2019, 12, 4814. [Google Scholar] [CrossRef] [Green Version]






























| Authors | Year | Consensus Algorithm | Incentive Mechanism | Application Domain | Issue Addressed | Performance Evaluation |
|---|---|---|---|---|---|---|
| Wang et al. | 2019 | NM | × | IoT data | Integrity verification for large-scale IoT data | The number of fragments of data is 200,300,400 and 500, the time cost is about 20 s, 26.5 s, 42.5 s, and 59 s. |
| Yang et al. | 2020 | NM | × | JointCloud | Secure transactions | The transactions are 100, 1000, and 2000, the latency time is about 0.18 s, 2.01 s, and 5.23 s. |
| DIb et al. | 2019 | Solo | × | IOT data | Intelligent data exploitation | The transaction sending rate is 50,100,500, the average latency is 0.98 s, 3.14 s, and 5.25 s |
| Cao et al. | 2020 | Proof of concept (PoC) | × | Steel products | Quality traceability | System response time is less than 10 ms at 1000 users |
| Rodriguez et al. | 2015 | PBFT | × | IOT devices | Security | The average committed latency for the four networks configured by the system is 298.62 ms, 514.42 ms, 514.32 ms, and 730.11 ms |
| Kim et al. | 2021 | Proof of elapsed time | × | IOT networks | Communication efficiency | The minimum convergence time for the final solution obtained by the genetic algorithm is 2600 ms, the maximum convergence time is 4300 ms. |
| Helebrandt et al. | 2019 | NM | √ | IOT networks | Security | The profiles is 2, 5, 10, the processing time is 4.2 ms, 407 ms, and 402 ms. |
| Authors | Year | Consensus Algorithm | Incentive Mechanism | Application Domain | Issued Addressed | Performance Evaluation |
|---|---|---|---|---|---|---|
| Mbarek et al. | 2019 | NM | × | IOT devices | Device security | The number of nodes is 200, 600, 800, and 1200, the average latency is about 2.4 ms, 2.6 s, 3.5 ms, and 5 ms. |
| Ribeiro et al. | 2020 | NS: lightweight consensus algorithms | × | Low-power wide-area network (LPWAN) | Efficiency, security | The number of requests is 1000, 3000, 5000, and the average system latency is about 13 s, 35 s, and 59.24 s. |
| Hang et al. | 2019 | NS: byzantine fault tolerant (BFT)/crash fault tolerant (CFT)/PBFT | × | IOT platforms | Data accessing | The records is 500, 250, 5000 and 10,000, the average latency is 271 ms, 559 ms, m656 ms, and 752 ms. |
| Liu et al. | 2017 | PoW | × | IoT data | Access control | The requests are 50, 200, 500 and 1000, the average time is about 0.12 s, 0.075 s, 0.065 s, and 0.062 s. |
| Zhang et al. | 2021 | NM | × | Domain name system | Root zone management | The TPS of write data is 100,200,250, the average latency is about 100 ms, 1450 ms and 10,000 ms. Read data TPS is 100,200,250, the average latency is about 10 ms, 15 ms, and 30 ms. |
| Chi et al. | 2020 | NM | × | IIOT | Efficiency of data sharing | The query tag is 6, when the query request reaches 200, 300, and 400, the time cost of the system is 12 s, 17 s, and 24 s. |
| Authors | Year | Consensus Algorithm | Incentive Mechanism | Application Domain | Issued Addressed | Performance Evaluation |
|---|---|---|---|---|---|---|
| Siris et al. | 2020 | Proof-of-work (POW), Proof-of-authority (POA) | × | Constrained IOT devices | Decentralized authorization | The latency for the request event is approximately 4.2 s. |
| Kakei et al. | 2010 | NM | × | Public key infrastructure | Distributed CA | The average processing time for initialization, participation, deployment, and validation is 2215.6 ms, 2366.7 ms, 2463.3 ms, 2404.8 ms, 65.7 ms. |
| Pajooh et al. | 2021 | Proposed | × | 5G-enabled IoT networks | Security | The transaction sending rate is 100,200,400, and 500, the average delay is about 0.5 s, 1.6 s, 5.7 s, and 9.8 s |
| Zhou et al. | 2018 | NM | × | IoT data | Data security | The number of sending transactions per second is 100, 200,300, the average latency is 2.4 s, 5.8 s, and 6.4 s. |
| Hou et al. | 2020 | PBFT | × | Long range (LoRa) system | Security, availability | The application package is 500, 1000, and 2000, the average processing time is about 12 s, 20 s, 25 s. The number of requests is 400, 1200, 2200, the system connection is about 3.5 s, 3.7 s, 6.3 s. |
| Authors | Year | Consensus Algorithm | Incentive Mechanism | Application Domain | Issued Addressed | Performance Evaluation |
|---|---|---|---|---|---|---|
| Hang et al. | 2020 | NS:BFT/CFT/PBFT | × | Smart fish farming | Data quality | The average throughput of the system is 800 tps, 850 tps, and 875 s when the number of transactions reaches 200, 400, 500. |
| Lee et al. | 2020 | PoET, RAFT | × | Smart food farming | Monitoring, certification | - |
| Yang et al. | 2018 | NM | × | Smart toy | Security of data exchange | When the number of blocks is 50,100,416, the response time of the system is 130 s, 165 s, and 239 s. |
| Manzoor et al. | 2020 | NM | √ | IOT mobile games | Incentives transparency | When the number of transactions is 10,000, the creation time is 250 tps, the query time is 500 tps, and the update time is 250 tps. |
| Pittaras et al. | 2021 | BFT | √ | IOT mobile games | Cost and transaction delay | When the number of challenges is 60,100,140, the system response time is 0.3 s, 0.5 s, and 0.7 s. |
| Jamil et al. | 2021 | PBFT | × | Smart fitness | Intelligence, security | When the sending rate is 400,600,1000, the system throughput is 400 tps, 590 tps, and 950 tps. |
| Khan et al. | 2020 | NM | × | Smart city | Data security for CCTV (closed-circuit television camera) cameras | - |
| Authors | Year | Consensus Algorithm | Incentive Mechanism | Application Domain | Issued Addressed | Performance Evaluation |
|---|---|---|---|---|---|---|
| Zhao et al. | 2019 | NS: Kafka/SBFT(simple Byzantine fault tolerance)/Solo | × | Microgrid trading | Pricing strategy | When the transmission rate is 100,300,460, the average system delay is 3000 s, 5900 s, and 8000 s. |
| Li et al. | 2020 | Kafka | × | Power trading for charge and discharge | Transaction scheduling, mixed-integerprogramming (MIP) | When the number of concurrent transactions per second is 350, the system’s minimum transaction confirmation time is 366 ms. |
| Li et al. | 2021 | Kafka | × | Power trading for charge and discharge | Security and privacy, MIP | With 1000 concurrent transactions per second, the system has a throughput of 500 tps or more, outperforming Ethereum and Bitcoin systems. |
| Yu et al. | 2019 | NM | × | Peer-to-peer (P2P) power trading | Competitive trading | When the power demand is 160 MW, the revenue is around USD 443.77. |
| Lohachab | 2021 | NS: Kafka/Raft/Solo | √ | Power transactions supported by CPS (Cyber-Physical Systems) | Performance issues and optimized configuration | When the asset size is 1000 bytes, 8000, 32,000, the system query performance is around 570 tps, 400 tps, and 200 tps. |
| Jamil et al. | 2021 | PBFT | √ | Trading for distributed energy resources | Predict short-term energy consumption | Maximum throughput of 43 tps, 68 tps, and 95 tps for user groups of 500, 1000, and 1500. |
| Sciume et al. | 2020 | Solo | √ | Power consumption demand response | Network load | The average system downloading energy file is 10.2 s, the average query downloading files is 0.065 s, and the average time to get the reward is 2.3 s. |
| Wang | 2021 | NS: Kafka/SBFT/Solo | × | Microgrid energy management | Privacy protection of microgrid | The annual staff salary cost is approximately USD 15,000 and the staff cost savings from the energy management approach is USD 30,000/year. |
| Authors | Year | Consensus Algorithm | Incentive Mechanism | Application Domain | Issued Addressed | Performance Evaluation |
|---|---|---|---|---|---|---|
| Feng et al. | 2019 | PBFT (Practical Byzantine Fault Tolerance) | × | Vehicular ad hoc networks (VANETs) | Automatic authentication | Point addition, scalar multiplication, multiplication, the average time of these three operations are 0.184 ms, 64.99 ms, and 0.179 ms. |
| Li et al. | 2020 | NM | × | Traffic management systems | Privacy protection | Proof generation time and validation time remain at 98 ms and 97 ms. |
| Luo et al. | 2020 | PBFT, Kafka | × | Space–air–ground integrated network (SAGIN) | Cross-regional certification | Maximum request delay for Kafka message packaging, maximum number of packaged messages, maximum block capacity, and maximum message size are 2 s, 100, 99 mb, and 512 kb. |
| Buzachis et al. | 2020 | NM | × | Autonomous Intersection Management (AIM) | Collisions of AVs(Autonomous Vehicles) and traffic congestion | Response latency is about 0.7 s, average latency of about 0.72 s. |
| Mbarek et al. | 2020 | Proposed | × | Vehicular Ad-hoc Network (V ANET) | Communication overheads | For 250 transactions, the total execution time is 14 s, average execution time for transactions is 0.056 s. |
| Authors | Year | Consensus Algorithm | Incentive Mechanism | Application Domain | Issued Addressed | Performance Evaluation |
|---|---|---|---|---|---|---|
| Xiao et al. | 2020 | POA | × | Vehicular ad hoc networks (VANETs) | Information security detection | When the batch size reaches 1000, the trading time is 20.246 s. |
| Chen et al. | 2019 | PoS(Proof of stake) | √ | Internet of vehicles (IoV) | Incentive mechanism, data quality | For data vendors, USD 0.03045839 is required for a data sharing round. |
| Gao et al. | 2018 | Byzantine | × | V2G (vehicle-to-grid) networks | Privacy preserving payment mechanism | The saturation value of the system throughput is 300 TPS. |
| Chiu et al. | 2021 | PBFT | × | Electronic Toll Collection (ETC) system | Data storage, trustworthiness and transparency | 1M of records has a trading time of 6 s. |
| Vieira et al. | 2020 | Proposed | × | 5G C-V2X (cellular Vehicle-to-everything) communication | Privacy protection | The average time taken by the system is 1090.3 s and the certificate verification is 465.9 ms. |
| lee et al. | 2020 | Proposed | √ | Vehicle-to-everything (V2X) communications | Service stability, data integrity | 100 nodes, 200 nodes, and 300 nodes out of the block time is about 7.5 s. |
| Authors | Year | Consensus Algorithm | Incentive Mechanism | Application Domain | Issued Addressed | Performance Evaluation |
|---|---|---|---|---|---|---|
| Widya Nita Suliyanti et al. | 2020 | NM | × | Building information modeling (BIM) | Information interaction, monitoring status | The average response has a table value of about 8000 ms. |
| Faris Elghaish et al. | 2020 | NM | × | Integrated project delivery (IPD) | Automated financial | - |
| Rebecca Yang et al. | 2020 | NM | × | Construction projects | Efficiency, synergy | Transaction time is between 30 s and 60 s. |
| Da Sheng et al. | 2020 | Kafka | × | Construction projects | Management of quality information | The upload average latencies are 53.3 ms and the query average latencies are 57.8 ms. |
| Authors | Year | Consensus Algorithm | Incentive Mechanism | Application Domain | Issued Addressed | Performance Evaluation |
|---|---|---|---|---|---|---|
| Pu Yuan et al. | 2018 | NM | × | Emission trading | Security | The saturation point for throughput is approximately 340 RPS (requests per second). |
| Zhou Hu et al. | 2020 | Delegated Proof of Reputation | √ | Carbon emission trading | Trading scheme and consensus mechanism | - |
| Zheng Che et al. | 2019 | Solo | × | Distributed renewable energy transaction | Transaction authentication | 250 TPS (transactions per second) |
| Felipe Condon Silva et al. | 2019 | NM | × | Energy trading for electric vehicles in smart campus | Intelligence, security | - |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Leng, Z.; Wang, K.; Zheng, Y.; Yin, X.; Ding, T. Hyperledger for IoT: A Review of Reconstruction Diagrams Perspective. Electronics 2022, 11, 2200. https://doi.org/10.3390/electronics11142200
Leng Z, Wang K, Zheng Y, Yin X, Ding T. Hyperledger for IoT: A Review of Reconstruction Diagrams Perspective. Electronics. 2022; 11(14):2200. https://doi.org/10.3390/electronics11142200
Chicago/Turabian StyleLeng, Zeqi, Kunhao Wang, Yuefeng Zheng, Xiangyu Yin, and Tingting Ding. 2022. "Hyperledger for IoT: A Review of Reconstruction Diagrams Perspective" Electronics 11, no. 14: 2200. https://doi.org/10.3390/electronics11142200
APA StyleLeng, Z., Wang, K., Zheng, Y., Yin, X., & Ding, T. (2022). Hyperledger for IoT: A Review of Reconstruction Diagrams Perspective. Electronics, 11(14), 2200. https://doi.org/10.3390/electronics11142200






