Abstract
The cube attack was proposed at the 2009 Eurocrypt. The attack derives linear polynomials for specific output bits of a BlackBox cipher. Cube attacks target recovery keys or secret states. In this paper, we present a cube attack on a 5-round Sycon permutation and a 6-round Sycon permutation with a 320-bit state, whose rate occupies 96 bits, and whose capacity is 224 bits. We found cube variables related to a superpoly with a secret state. Within the cube variables, we recovered 32 bits of the secret state. The target algorithm was Sycon with 5-round and 6-round versions of permutation. For the 5-round Sycon, we found a cube variable and recovered a state with a total of Sycon computations and bits of memory. For the 6-round Sycon, we found cube variables and recovered a state with a total of Sycon computations and bits of memory. When using brute force in a 5-round attack, operations were required, but the cube attack proposed in this paper had offline operations, and operations were required. When using brute force in a 6-round attack, operations were required, but the cube attack proposed in this paper required offline operations, and operations were required. For both attacks, offline could be used continuously after performing only once. To the best of our knowledge, this is the first cube attack on Sycon.
1. Introduction
Currently, wireless communication technology supports the high-speed communication of various devices, such as cellular phones, lightweight devices, and industrial sensors. In addition, wireless communication makes smart factories, smart cities, and self-driving cars possible and provides many conveniences for human beings. However, the importance of information security must be emphasized, because there are risks of being exposed to cyber security threat, manipulation or leakage of data and invasion of privacy during the transmission of data by wireless communication [1,2,3]. In wireless communication, information security may be provided through cryptographic algorithms [4,5]. However, since the security strength of cryptographic algorithms does not provide immutability, it must be continuously re-evaluated and reviewed for proper use.
A cube attack is the first type of attack to utilize existing linear, logarithmic, and correlation at the same time [6]. A cube attack can apply to block ciphers, stream ciphers, and MACs. With a cube attack, key recovery is possible. A cube attack creates a polynomial in GF(2) using a set of variables defined as a cube. A cube is the set of all cases with the given variables. The polynomial is associated with a cryptographic algorithm’s output treated as a black box, expressed with a quotient and a remainder. The goal is to find the coefficient of the quotient. Then, the secret data are recovered using the obtained coefficient of the quotient.
At Eurocrypt 2009, a cube attack against Trivium, a block cipher-based stream cipher suitable for wireless communication environments, was announced [6]. Trivium is a stream cipher using an 80-bit key and 1152 initializations [7]. Since then, it has been proven through several papers that a cube attack is possible for several cryptographic algorithms such as SIMON-64/96, Ascon, ACORN, MROUS, GILMI, and Keyak [8,9,10,11,12,13].
This paper proposes a cube attack on Sycon. Sycon is an AEAD cipher sponge construction with a 128-bit key. Sycon was submitted to the NIST Lightweight Cryptography Competition [14] and was selected among the ciphers for the first round of this project.
In this paper, Sycon using a rate of 96 was reduced to five rounds and six rounds. Based on the low algebraic degree of Sycon, we were able to construct a cube attack with a complexity of for the 5-round Sycon permutation, described in Section 4. A total operations and bits of memory were required to recover the 32-bit state in the 5-round Sycon. In Section 6, we describe the use of similar algebraic properties to construct a cube attack to obtain a state recovery attack for the 6-round Sycon permutation. We recovered the same 32-bit state on the 6-round Sycon with operations and bits of memory. To the best of our knowledge, this paper describes the first cube attack on Sycon. The main contributions of this paper are summarized as follows:
- The cube attack against Sycon shows the potential threat applicable to wireless communication. Sycon could be considered in wireless communication for confidentiality and integrity, since Sycon is a lightweight AEAD algorithm.
- This is the first known state recovery attack against Sycon. The time complexity to recover the state of the 5-round and 6-round Sycon was , faster than brute force. This paper shows the possibility of transmission data tampering or sniffing by an attacker.
This paper proceeds as follows. Section 3 introduces cube attacks and the Sycon cipher. Section 4 describes a cube attack on Sycon. The Results and Discussion section describes the complexity of the attacks. Conclusions are provided in Section 6 with a summary of the proposed attack and the results.
2. Related Work
A cube attack was proposed on Trivium with 672 initialization rounds with bits operations, 735 initialization rounds with bits operations, and 767 initialization rounds with bits operations. Since then, an improved attack with an MILP model on Trivium with 675/735/840/841/842 initialization rounds was proposed in 2021, and an attack on Trivium with 843 initialization rounds was proposed in 2022 [15,16].
Ascon was selected as a finalist in the NIST Lightweight AEAD Cryptography Contest in 2017, and the strongest attack at that time was a cube attack, which had the time complexity of under the nonce misuse condition in the 7-round Ascon initialization step [17]. However, for Ascon in 2022, an improved cube attack was also conducted under the condition of nonce misuse in the initialization phase [18]. The complexity of the key recovery for a full-round Ascon was .
In [19], Dinur et al. presented a cube-like attack against Keccak hash function-based message authentication codes, authenticated encryption, and stream cipher. The key recovery attack was performed for up to seven rounds. Key recovery and forgery attacks were proposed for AE based on the Keccak hash function. In the case of the key recovery, the attacks were performed up to six rounds under the nonce respected condition, and the attacks were performed up to seven rounds under the nonce reused condition. A key recovery attack and keystream prediction attack were proposed for the Keccak hash function-based stream cipher, and it was shown that six rounds of key recovery and key stream prediction could perform attacks for up to nine rounds.
In [20], Salam et al. proposed a cube attack against the authenticated encryption stream cipher ACORN. This attack recovered a 128-bit key with a complexity of in 477 initialization rounds in ACORN, a proposed candidate for NIST CAESAR (Competition for Authenticated Encryption: Security, Applicability, and Robustness). In addition, full-round ACORN showed that a state recovery attack could be performed with a complexity of using a linear equation associated with the initial state. In [12], Yang et al. proposed a method of measuring the algebraic order and numerical mapping in NFSR-based ciphers and a method of finding a cube based on a greedy algorithm. It was shown that a key could be recovered with a complexity of with cube variables using 123 variables for the 772 reduced-round ACORN.
In [21], Huang et al. introduced an efficient key recovery attack for the Keccak hash function-based MAC or Keccak hash function-based AE algorithm Keyak using a conditional cube attack. In [19], a MAC-based 7-round Keccak hash function was proposed. With times more data, the time complexity could be decreased to . An attack against Keyak was feasible with the time complexity of and a data complexity of for eight rounds.
3. Preliminaries
In this section, we briefly introduce the necessary background for this paper. Firstly, we provide the notations used in this paper. Then, we provide a brief description of Sycon and the concept of a cube attack.
3.1. Abbreviations and Notations
The abbreviations used in this paper are listed in Table 1.

Table 1.
Abbreviations.
The symbol notations used in this paper are listed in Table 2.

Table 2.
Notations.
3.2. Sycon Authenticated Encryption with the Associated Data Algorithm Specification
Sycon is an authenticated encryption with an associated data (AEAD) cipher [22]. AEAD is an encryption algorithm with a built-in integrity process using a secret key [23]. AEAD usually performs better than using two separate cryptographic processes with two different secret keys. Sycon provides two authenticated encryption algorithms with associated data and one hash algorithm in a sponge structure. In this section, we specify the Sycon whose rate is 96.
Sycon consists of initialization, related data processing, encryption/decryption, and finalization. The initialization phase loads 128-bit keys, a 128-bit nonce, and a 64-bit initialization vector into the 320-bit state variable. Then, it conducts two permutation calls, truncating the key by 64 bits and XORing it. The relevant data processing is applied after the initialization phase, if the related data are not empty. Relevant data processing performs the permutation with the associated data (AD) and the current state as input. The relevant data processing will not perform if the relevant data are empty. In encryption/decryption, the encryption algorithm generates the ciphertext with the same length as the input plaintext. In this case, the size of the plaintext is a multiple of 96, and padding is performed if it is less than 96 bits. Then, we conduct the permutation to update the state. This process is repeated until all 96 bits of plaintext are processed. The finalization absorbs the key back into the state via a ratio of two permutation calls, and a 128-bit tag is output. A tag is a value that concatenates the contents of S2 and S3 among the state variables.
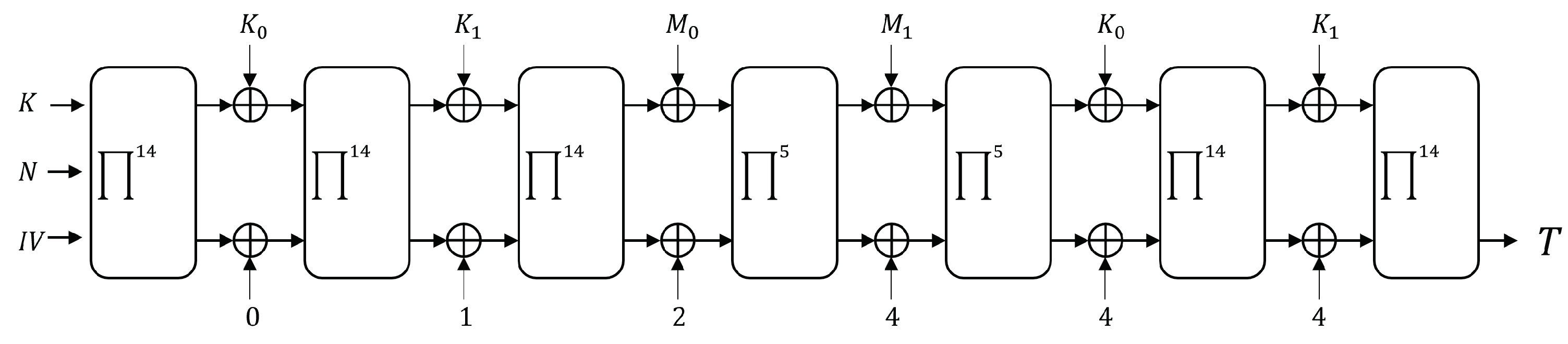
The state is XORed with a key or plaintext after permutation as shown in Figure 1. The LSB 224 bits of the state are XORed with a domain separator. The domain separator of Sycon is as follows: for initialization, for AD processing, for massage, and for tag generations. If the additional data are empty, is replaced by .
Figure 1.
Sycon -AEAD-96 (when the length of the associated data is 0).
Sycon permutation is an iterative computation in a round function. In the round function, Sycon uses a 320-bit state. In the state, the first 64/96 bits are user message bits along the rate. The round function (R) of the Sycon permutation consists of a sequence of three distinct transformations: SBox (SB), SubBlockDiffusion (SD), and AddRoundConstant (RC), i.e., . The -round permutation, denoted by , is constructed as .
The first layer is a nonlinear computation. Sycon’s round function is SPN. Thus, for nonlinear computation, Sycon uses 64 S-boxes. The process of the S-boxes in the equation is as follows:
The second layer is a diffusion layer that performs linear transformation on five 64-bit sub-blocks. The diffusion layer uses the following linear transformation:
The third layer is the add round constant layer. Round constants use a four-bit LFSR defined by the polynomial . The LFSR status is expressed as , where . Starting from the initial state , we generate a round constant, where each state of the LFSR is given as a unique constant. The four-bit LFSR with status is converted to a byte equal to . The round constants are given in Table 3.

Table 3.
The round constants .
3.3. Cube Attack
Let the cryptography algorithms be expressed with a polynomial f. The input of the cryptographic algorithm (e.g., plaintext, initial vector, nonce, associated authentication data) will be f’s input parameter, and the output of the cryptography algorithm (e.g., ciphertext, tag) will be the value of f’s computed result. If the block cipher has input as plaintext P, initial vector , and key K, and the output is ciphertext C, we can express the block cipher with , , , and , where , , and is a bit representation, respectively.
- Degree The dense polynomial f of degree d has possible polynomials over GF(2). To eliminate the nonlinear terms on the polynomials, the attack needs to eliminate . Thus, when the degree becomes higher, it is hard to eliminate the nonlinear terms.
- Cube Variables To eliminate the nonlinear terms from the polynomial f, an attacker needs to divide the polynomials f by the other polynomial t, whose degree is . If divided by , then f can be expressed as . In this term, t is bit cube variables.
- Superpolys We assume that dense polynomial f divided by , , as above. In this term, is a superpoly with degree 1. In order to obtain a superpoly, the attacker can compute .
In a cube attack, finding cube variables is important, because when the degree of the polynomial becomes higher, an attacker needs more polynomials to use Gaussian elimination. When the cube variables are larger, the attacker breaks more rounds. Moreover, f can be divided by variables, and the quotient will be a degree 1 polynomial. A cube attack should first formulate the polynomial f. If f is not a dense polynomial, superpoly Q’s degree will be changed along the chosen cube variables. For example, when we define cube variables as , and if A is bits that multiplied with bits, then f could be . That is, the polynomial Q degree is . Thus, in order to obtain Q, the attacker needs to use fewer cube variables .
To make m independent polynomials, the attacker needs to analyze where there are no multiplication values between the target bits and the input bits that the attacker can control. The attacker will select the control bits that do not have multiplication with the target bits. The attacker can know whether multiplication will be computed by analyzing the cryptographic algorithms’ process. A typical example that has a multiplication step in a cryptography algorithm is an S-box. After the attacker finds the proper cube variables from the polynomials, a cube attack can decide the round that an attacker can use. Then, the cube attack is presented as follows:
- Offline Phase The attacker computes and stores the . The targeted data bits can be expressed as linear polynomials . The attacker computes a linear polynomial from the Q values. The attacker assigns 0 except for the cube variables. Then, the attacker sets bit by bit on x. From the data, the attacker computes each coefficient of x.
- Online Phase Considering the oracle as given, the attacker derives the cube sum of the oracle query results . From the polynomials saved in the offline phase, the attacker recovers target bits A. If A has variables, the attacker needs an cube sum result. The attacker computes the Gaussian elimination to obtain the recovered target bits.
- Brute Force Phase If the cube variables are not enough to obtain all rounds or all target bits, the attacker performs a brute force attack on the remaining bits. For example, if the recovered bits are l bits and the targeted bits are m bits, the attacker performs a exhaustive search.
4. State Recovery Attack on a Reduced-Round Sycon
In this section, we focus on state recovery attacks. First, we analyze the round-reduced Sycon. Then, in the later part of the section, the cube attacks on five-round Sycon and six-round Sycon are described.
4.1. Idea and Scenario
We propose an attack idea and scenario to recover the secret state of Sycon. Sycon has a 320-bit state variable, as described in Section 3. In this paper, the state variable is expressed as a truncated form to 32-bit units as follows:
The polynomial of the output from the S-box has degree 2. After five rounds of the permutation are performed, the result has a polynomial of degree . Therefore, we require variables in the cube for an attack against the 5-round Sycon. In the same way, after six rounds, the degree of is . Thus, we need variables in the cube. We choose bits from the state variable that we have control over. We select , , and as the cube variables. The cube attack is feasible if the variables are uniquely multiplied by , , and . The variable with this characteristic in the S-box is . is only multiplied by and . Choosing as the cube variable allows us to recover . With the cube variables, we obtain the linear equations as follows:
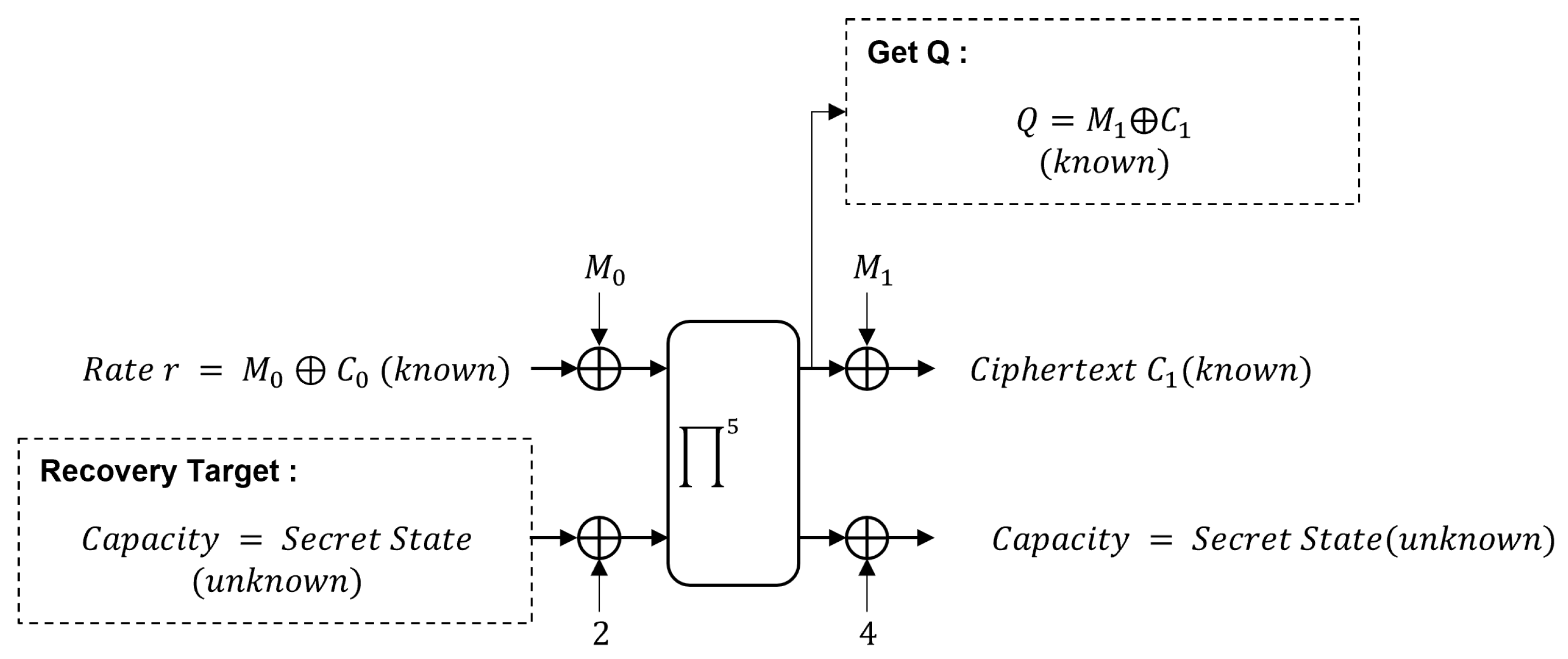
To construct , we obtain the result of the permutation by , and we choose the message bits that construct the cube variables. Figure 2 shows the attack scenario.
Figure 2.
State recovery attack scenario on the reduced-round Sycon.
4.2. Attack on the Five-Round Sycon
4.2.1. Offline Phase
Sycon encrypts plaintext by truncating it in units of 96 bits. We chose 96 bits of plaintext. The state variable S was concatenated as , , , , , , , and , where each size was 32 bits.
, , and were the plaintext values chosen. Ciphertext , , and were computed by performing XOR of the current state variables MSB 96 bits , , and and the plaintext , , and .
Since the ciphertext and the plaintext were known, we computed the XORing of the ciphertext and the plaintext to obtain , , .
We set the cube variables in . Since the degree of the S-box was 2, the result after five rounds had a polynomial of degree 16. The attacker chose a 15-bit cube in the 5-round Sycon state variable to obtain a polynomial of degree 1 and the rest of the values as constants. We recovered 16 bits of MSB and 16 bits of LSB of , respectively. Therefore, two cube variables were required, and each cube variable set had elements. The cube variable could be {0x0, 0x1, …, 0xffff} and {0x00000, 0x10000, …, 0xffff0000}. We assigned all the other variables to 0 except for the cube variable and used in the attack. was used in the attack as it was multiplied only by and , as described in Section 4.1.
Since depends only on , after five rounds, the polynomial could be expressed as a polynomial for the quotient of and .
We used the process shown in Table 4 to find the variable coefficients of a polynomial for . As a result, we obtained the following values. The results obtained were stored in the memory and used in the online phase.

Table 4.
Attack on the five-round Sycon: Offline phase process.
4.2.2. Online Phase
In the online phase, we implemented an oracle. The oracle allowed the choice of arbitrary plaintext and , and the cube variables were defined internally as a fixed set. The oracle computed for the plaintext chosen. We computed two times for the MSB 32 bits and LSB 32 bits of . The oracle calculated the superpolys as follows:
We explored the superpoly obtained by querying the oracle in the memory space stored during the offline phase. If the same value as was in the memory, we determined , because the memory stored for every . The that we explored in the memory was as follows:
4.2.3. Brute Force Phase
We recovered the remaining 192 bits of state by brute force. There was no memory required, but we needed computations.
4.3. Attack on the Six-Round Sycon
4.3.1. Offline Phase
We chose the 32-bit . With the chosen plaintext, we assigned the LSB 31 bits of as the cube variable 0xffffffff}. The cube variable of , , , , , and was fixed as , because was only multiplied with and . We used the process shown in Table 5 to find the variable coefficients of a polynomial for Q(S). could be rephrased as . was . For each , we computed the following:

Table 5.
Attack on the six-round Sycon: Offline phase process.
4.3.2. Online Phase
We implemented an oracle, where the cube variables were defined internally as a fixed set. The oracle computed for the plaintext chosen. The results calculated by the oracle were as follows for the online cube-sum:
We explored the value obtained through the oracle in the memory space stored during the offline phase. If the same value as was in the memory, we determined , because the memory stored for every . The that we explored in the memory was as follows:
4.3.3. Brute Force Phase
We recovered the remaining 192-bit state bits by brute force.
5. Results and Discussion
First, we analyze the complexity in the offline phase. Computing the equations for just one case in the memory required 5-round Sycon and 16 bits of memory. We performed the same process times repeatedly for each and . Therefore, in the offline phase, we required Sycon computations and bits of memory. In the online phase, we required computations to recover the target bits. The remaining 192 bits of state were recovered by brute force, so we required . In total, the attack needed a computational complexity of .
To recover the six-round Sycon permutation state, we needed an offline phase, an online phase, and a brute-force phase. In the offline phase, we precalculated the cube sum, and it needed a computation complexity of and 64 bits of memory. We performed this process times repeatedly for all cases in and . In total, in the offline phase, 6-round Sycon computations and bits of memory were required. In the online phase, we only needed to perform of six-round Sycon permutations. The remaining 192 bits of state were recovered by brute force. In the brute-force phase, there was no memory required, but we needed computations. Thus, in total, the attack required a computational complexity of (Table 6).

Table 6.
Complexity of the 224-bit secret state recovery attack.
The AEAD cipher encrypts the data to be transmitted and creates a tag for data integrity [24]. In order to give functions, Sycon has the following four phases: Initialization, associated data processing, encryption/decryption, and finalization. Each step should be analyzed in different ways [25]. In the future, we can extend the cube attack to the initialization or finalization phase of Sycon to recover the secret key.
6. Conclusions
In this paper, we proposed a state recovery attack against five-round and six-round Sycon. Sycon keeps 224 bits in secret and 96 bits as plaintext/ciphertext. With no information, we needed computations. From the attack we proposed, 32 bits of the state could be recovered against the 5-round Sycon, with a time complexity of . We also proposed an attack against the six-round Sycon. The attack recovered the same 32 bits with the time complexity of and of memory in the offline phase. The time complexity was . This was faster than brute force over the possible states by a factor of about .
Author Contributions
Methodology, M.C.; Writing—original draft, M.C.; Formal analysis, H.E. and E.T.; Writing—review and editing, H.E. and E.T.; Supervision, C.L.; All authors read and agreed to the published version of the manuscript.
Funding
This work was supported as part of the Military Crypto Research Center (UD210027XD) funded by the Defense Acquisition Program Administration (DAPA) and the Agency for Defense Development (ADD).
Data Availability Statement
Not applicable.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Abdalzaher, M.S.; Samy, L.; Muta, O. Non-zero-sum game-based trust model to enhance wireless sensor networks security for IoT applications. IET Wirel. Sens. Syst. 2019, 9, 218–226. [Google Scholar] [CrossRef]
- Abdalzaher, M.S.; Muta, O. A game-theoretic approach for enhancing security and data trustworthiness in IoT applications. IEEE Internet Things J. 2020, 7, 11250–11261. [Google Scholar] [CrossRef]
- Abdalzaher, M.S.; Seddik, K.; Muta, O. Using repeated game for maximizing high priority data trustworthiness in wireless sensor networks. In Proceedings of the 2017 IEEE Symposium on Computers and Communications (ISCC), Heraklion, Greece, 3–6 July 2017; pp. 552–557. [Google Scholar]
- Phuc, T.S.D.; Xiong, N.N.; Lee, C. Cryptanalysis of the XO-64 Suitable for Wireless Systems. Wirel. Pers. Commun. 2017, 93, 589–600. [Google Scholar] [CrossRef]
- Phuc, T.S.D.; Lee, C. Cryptanalysis on SDDO-Based BM123-64 Designs Suitable for Various IoT Application Targets. Symmetry 2018, 10, 353. [Google Scholar] [CrossRef]
- Dinur, I.; Shamir, A. Cube attacks on tweakable black box polynomials. In Proceedings of the Annual International Conference on the Theory and Applications of Cryptographic Techniques, Cologne, Germany, 26–30 April 2009; pp. 278–299. [Google Scholar]
- De Cannière, C.T.; Preneel, B. A stream cipher construction inspired by block cipher design principles. In Information Security; Katsikas, S.K., López, J., Backes, M., Gritzalis, S., Preneel, B., Eds.; Springer: Berlin/Heidelberg, Germany; pp. 171–186.
- Mroczkowski, P.; Szmidt, J. The cube attack on stream cipher Trivium and quadraticity tests. Fundam. Informaticae 2012, 114, 309–318. [Google Scholar] [CrossRef]
- Li, Z.; Dong, X.; Wang, X. Conditional Cube Attack on Round-Reduced ASCON. Cryptology ePrint Archive 2017. Available online: https://eprint.iacr.org/2017/160.pdf (accessed on 24 July 2022).
- Bi, W.; Li, Z.; Dong, X.; Li, L.; Wang, X. Conditional cube attack on round-reduced River Keyak. Des. Codes Cryptogr. 2018, 86, 1295–1310. [Google Scholar]
- Chen, S.; Xiang, Z.; Zeng, X.; Zhang, S. Cube attacks on round-reduced MORUS and GIMLI. Sci. China Inf. Sci. 2022, 65, 1–3. [Google Scholar] [CrossRef]
- Yang, J.; Liu, M.; Lin, D. Cube cryptanalysis of round-reduced ACORN. In Proceedings of the International Conference on Information Security, New York, NY, USA, 16–18 September 2019; pp. 44–64. [Google Scholar]
- He, Y.; Wang, G.; Li, W.; Ren, Y. Improved cube attacks on some authenticated encryption ciphers and stream ciphers in the Internet of Things. IEEE Access 2020, 8, 20920–20930. [Google Scholar] [CrossRef]
- Lightweight Cryptography Round 1. Available online: https://csrc.nist.gov/Projects/lightweight-cryptography/round-1-candidates (accessed on 22 August 2022).
- Sun, Y. Cube Attack against 843-Round Trivium. Cryptology ePrint Archive 2021. Available online: https://eprint.iacr.org/2021/547 (accessed on 24 July 2022).
- Delaune, S.; Derbez, P.; Gontier, A.; Prud’Homme, C. A Simpler Model for Recovering Superpoly on Trivium. In Proceedings of the International Conference on Selected Areas in Cryptography; Springer: Cham, Switzerland, 2022; pp. 266–285. [Google Scholar]
- Dobraunig, C.; Eichlseder, M.; Mendel, F.; Schläffer, M. Ascon v1. 2: Lightweight authenticated encryption and hashing. J. Cryptol. 2021, 34, 1–42. [Google Scholar] [CrossRef]
- Chang, D.; Hong, D.; Kang, J. Conditional Cube Attacks on Ascon-128 and Ascon-80pq in a Nonce-Misuse Setting. Cryptology ePrint Archive 2022. Available online: https://eprint.iacr.org/2022/544 (accessed on 24 July 2022).
- Dinur, I.; Morawiecki, P.; Pieprzyk, J.; Srebrny, M.; Straus, M. Cube attacks and cube-attack-like cryptanalysis on the round-reduced Keccak sponge function. In Proceedings of the Annual International Conference on the Theory and Applications of Cryptographic Techniques, Sofia, Bulgaria, 26–30 April 2015; pp. 733–761. [Google Scholar]
- Salam, M.I.; Bartlett, H.; Dawson, E.; Pieprzyk, J.; Simpson, L.; Wong, K.K.H. Investigating cube attacks on the authenticated encryption stream cipher ACORN. In Proceedings of the International Conference on Applications and Techniques in Information Security, Cairns, QLD, Australia, 26–28 October 2016; pp. 15–26. [Google Scholar]
- Huang, S.; Wang, X.; Xu, G.; Wang, M.; Zhao, J. Conditional cube attack on reduced-round Keccak sponge function. In Proceedings of the Annual International Conference on the Theory and Applications of Cryptographic Techniques, Paris, France, 30 April–4 May 2017; pp. 259–288. [Google Scholar]
- Mandal, K.; Saha, D.; Sarkar, S.; Todo, Y. Sycon: A new milestone in designing ASCON-like permutations. J. Cryptogr. Eng. 2022, 12, 305–327. [Google Scholar] [CrossRef]
- Frankel, S.E.; Kent, K.; Lewkowski, R.; Orebaugh, A.D.; Ritchey, R.W.; Sharma, S.R. SP 800-77. Guide to IPsec VPNs. 2005. Available online: https://csrc.nist.rip/library/alt-SP800-77.pdf (accessed on 24 July 2022).
- Seok, B.; Sicato, J.C.S.; Erzhena, T.; Xuan, C.; Pan, Y.; Park, J.H. Secure D2D communication for 5G IoT network based on lightweight cryptography. Appl. Sci. 2019, 10, 217. [Google Scholar] [CrossRef]
- Teng, W.L.; Salam, I.; Yau, W.C.; Pieprzyk, J.; Phan, R.C.W. Cube attacks on round-reduced TinyJAMBU. Sci. Rep. 2022, 12, 1–13. [Google Scholar]
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).