Attacking IEC 61850 Substations by Targeting the PTP Protocol
Abstract
:1. Introduction
1.1. Purpose and Objective
1.2. Contributions
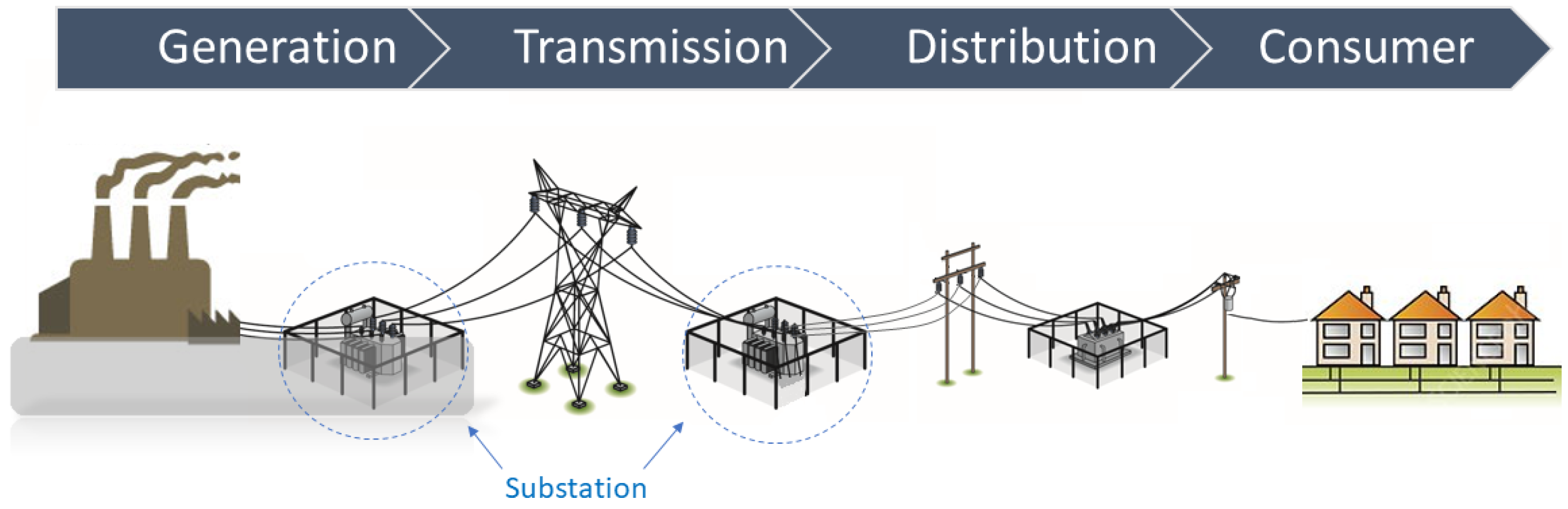
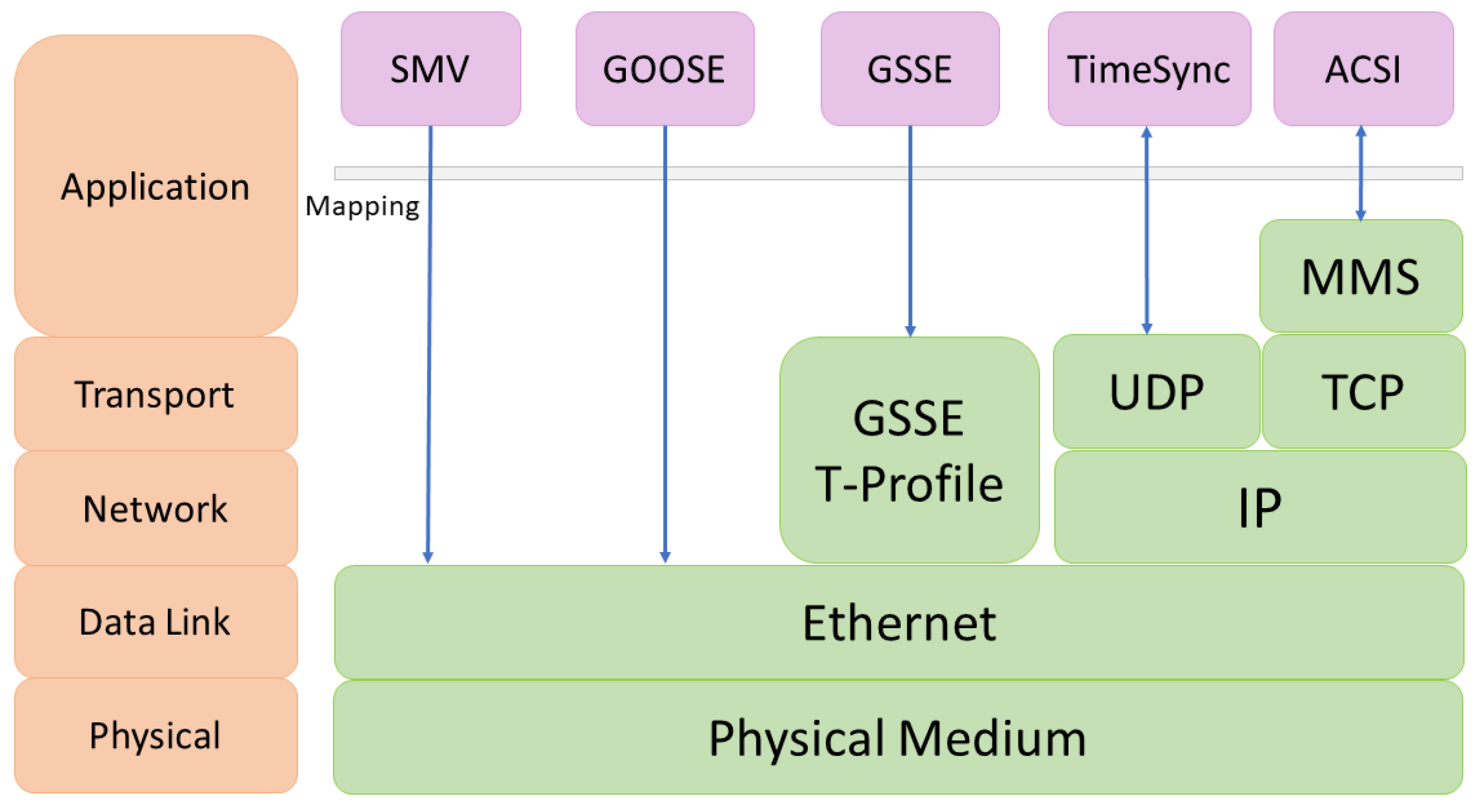
2. IEC 61850 and Time Synchronization
3. Related Work
| Authors | Year | Focus | Types of Attack(s) | Description and Drawback |
|---|---|---|---|---|
| Moradi et al. [50] | 2021 | Mitigation | Delay attack detection | Utilizing Simulator (OMNeT++) for evaluation |
| Alghamdi et al. [39] | 2020 | Attack | Packet propagation attack and time source attack | Laboratory testbed |
| Ullmann et al. [40] | 2009 | Attack | Delay Attacks | Mathematically abstract analysis |
| Lisova et al. [51] | 2016 | Attack | Delay attack | Utilizing high level Protocol simulator |
| Annessi et al. [41] | 2018 | Attack | Delay attack | No experimental validation |
| Han and Crossley [42] | 2019 | Attack | Packet modification, spoofing, traffic injection, and delay attacks | No experimental validation |
4. Digital Station Enclave Setup
5. Implementation and Testing of Cyber-Attacks on PTP
- Confidentiality: Obtaining the PTP messages in the network, including the current master time, the current master clock, and the network latencies based on the delays;
- Integrity: Adding a new time source to the network, changing the master clock, and changing the time;
- Availability: Stopping a time source and preventing a device from receiving the time.
- The best master clock with its MAC address and the main characteristics (priority numbers);
- The time of the best master clock;
- The leg of the switch where the attacker’s computer is connected;
- The settings of the switch (TC or BC).
- Create an inventory of the devices in the substation;
- Obtain the MAC addresses of the devices, which might ease their identification;
- Obtain the time sources of the digital substation devices.
- Adding a new master clock to the station bus network;
- Changing the time of the network.
- The network latency could not be calculated from the fake time source, resulting in the switch not being able to update the messages with its timestamps.
- The switch might compare the time with its own time and anomalies might have be detected, preventing the forwarding from being executed.
6. Discussion
- An unauthorized user/device attempts to access the digital station by VPN/physically connecting to switches or to IEDs in the network.
- An infected USB drive or malware like Stuxnet can propagate in the SCADA system via removable USB drives.
- The laptop of an employee/maintenance engineer is connected to one of the smart switches in the digital station, and due to the employee/maintenance engineer’s unintended or intended misuse, the attacker gains unauthorized access to the IEDs through the laptop.
- During the maintenance process of the digital station, the maintenance engineer might access the internet in order to download related updates or access the system to perform remote maintenance. An attacker may utilize this situation to penetrate the digital substation system.
6.1. Potential Mitigation Strategies
7. Conclusions and Future Works
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Gutierrez, S.; Botero, J.F.; Gaviria, N.; Fletscher, L.A.; Leal, E.A. Next-Generation Power Substation Communication Networks: IEC 61850 Meets Programmable Networks; IEEE: Piscataway, NJ, USA, 2022. [Google Scholar]
- EPRI. Report to NIST on the Smart Grid Interoperability Standards Roadmap; Technical Report; EPRI: Washington, DC, USA, 2009. [Google Scholar]
- Liang, Y.; Campbell, R.H. Understanding and Simulating the IEC 61850 Standard; Technical Report; University of Illinois: Champaign, IL, USA, 2008. [Google Scholar]
- Ten, C.W.; Manimaran, G.; Liu, C.C. Cybersecurity for critical infrastructures: Attack and defense modeling. IEEE Trans. Syst. Man Cybern.-Part A Syst. Hum. 2010, 40, 853–865. [Google Scholar] [CrossRef]
- Shrestha, A.; Silveira, M.; Yellajosula, J.; Kumar Mutha, S. Understanding the Impacts of Time Synchronization and Network Issues on Protection in Digital Secondary Systems. In Proceedings of the PAC World Global Conference 2021, Prague, Czech Republic, 31 August–1 September 2021; Schweitzer Engineering Laboratories, Inc.: Pullman, WA, USA, 2021; p. 12. [Google Scholar]
- Ridwan, M.; Tambunan, H.; Mangunkusumo, K.; Habibie, A.; Pramana, P. Review of digital substation equipment and technical specification in Indonesia. In Proceedings of the IOP Conference Series: Materials Science and Engineering, High Tatras, Slovakia, 13–15 October 2021; IOP Publishing: Bristol, UK, 2021; Volume 1098, p. 042053. [Google Scholar]
- Baumgartner, B.; Riesch, C.; Rudigier, M. IEEE 1588/PTP: The future of time synchronization in the electric power industry. In Proceedings of the PAC World Conference, Budapest, Hungary, 25–28 June 2012. [Google Scholar]
- Haapoja, S. Study and Design of Inter-Range Instrumentation Group Time Code B Synchronization of IEC 61850 Sampled Values. Master’s Thesis, University of Vaasa, Vaasa, Finland, 2018. [Google Scholar]
- Mackiewicz, R.E. Overview of IEC 61850 and Benefits. In Proceedings of the 2006 IEEE Power Engineering Society General Meeting, Montreal, QC, Canada, 18–22 June 2006; IEEE: Piscataway, NJ, USA, 2006; p. 8. [Google Scholar]
- Ozansoy, C.R.; Zayegh, A.; Kalam, A. Object modeling of data and datasets in the international standard IEC 61850. IEEE Trans. Power Deliv. 2009, 24, 1140–1147. [Google Scholar] [CrossRef]
- Sagen, E.; Workman, K. Methods of time synchronization. In Proceedings of the 63rd Annual Georgia Tech Protective Relaying Conference, Atlanta, GA, USA, 20–21 April 2009; pp. 1–8. [Google Scholar]
- Andersson, G.; Donalek, P.; Farmer, R.; Hatziargyriou, N.; Kamwa, I.; Kundur, P.; Martins, N.; Paserba, J.; Pourbeik, P.; Sanchez-Gasca, J.; et al. Causes of the 2003 major grid blackouts in North America and Europe, and recommended means to improve system dynamic performance. IEEE Trans. Power Syst. 2005, 20, 1922–1928. [Google Scholar] [CrossRef]
- Matson, J. Choosing the Correct Time Synchronization Protocol and Incorporating the 1756-Time Module into Your Application; Rockwell Automation: Milwaukee, WI, USA, 2013. [Google Scholar]
- Mills, D.L. Internet time synchronization: The network time protocol. IEEE Trans. Commun. 1991, 39, 1482–1493. [Google Scholar] [CrossRef]
- Mills, D. Simple Network Time Protocol (SNTP) Version 4 for IPv4, IPv6 and OSI. Technical Report. 2006. Available online: https://www.rfc-editor.org/rfc/rfc4330.html (accessed on 3 March 2023).
- Schweitzer, E.; Whitehead, D.; Achanta, S.; Skendzic, V. Implementing robust time solutions for modern power systems. In Proceedings of the 14th Annual Western Power Delivery Automation Conference, Spokane, WA, USA, 27–29 March 2012. [Google Scholar]
- IEEE Std 1588-2008; IEEE Standard for a Precision Clock Synchronization Protocol for Networked Measurement and Control Systems. IEEE: Piscataway, NJ, USA, 2008; pp. 1–269. [CrossRef]
- Watt, S.T.; Achanta, S.; Abubakari, H.; Sagen, E.; Korkmaz, Z.; Ahmed, H. Understanding and applying precision time protocol. In Proceedings of the 2015 Saudi Arabia Smart Grid (SASG), Jeddah, Saudi Arabia, 7–9 December 2015; IEEE: Piscataway, NJ, USA, 2015; pp. 1–7. [Google Scholar]
- EC61850-90-4; Network Engineering Guideline for Communication Networks and Systems in Substations. IEC: Geneva, Switzerland, 2013.
- Jones, T.; Arnold, D.; Tuffner, F.; Cummings, R.; Lee, K. Recent advances in precision clock synchronization protocols for power grid control systems. Energies 2021, 14, 5303. [Google Scholar] [CrossRef]
- Marrero, L.M.; Merlano-Duncan, J.C.; Querol, J.; Kumar, S.; Krivochiza, J.; Sharma, S.K.; Chatzinotas, S.; Camps, A.; Ottersten, B. Architectures and Synchronization Techniques for Distributed Satellite Systems: A Survey. IEEE Access 2022, 10, 45375–45409. [Google Scholar] [CrossRef]
- Wright, J.G.; Wolthusen, S.D. Stealthy Injection Attacks Against IEC61850’s GOOSE Messaging Service. In Proceedings of the 2018 IEEE PES Innovative Smart Grid Technologies Conference Europe (ISGT-Europe), Sarajevo, Bosnia and Herzegovina, 21–25 October 2018; IEEE: Piscataway, NJ, USA, 2018; pp. 1–6. [Google Scholar]
- Chlela, M.; Joos, G.; Kassouf, M.; Brissette, Y. Real-time testing platform for microgrid controllers against false data injection cybersecurity attacks. In Proceedings of the 2016 IEEE Power and Energy Society General Meeting (PESGM), Boston, MA, USA, 17–21 July 2016; IEEE: Piscataway, NJ, USA, 2016; pp. 1–5. [Google Scholar]
- Kabir-Querrec, M.; Mocanu, S.; Thiriet, J.M.; Savary, E. A test bed dedicated to the study of vulnerabilities in IEC 61850 power utility automation networks. In Proceedings of the 2016 IEEE 21st International Conference on Emerging Technologies and Factory Automation (ETFA), Berlin, Germany, 1–6 September 2016; IEEE: Piscataway, NJ, USA, 2016; pp. 1–4. [Google Scholar]
- Chattopadhyay, A.; Ukil, A.; Jap, D.; Bhasin, S. Toward threat of implementation attacks on substation security: Case study on fault detection and isolation. IEEE Trans. Ind. Inform. 2017, 14, 2442–2451. [Google Scholar] [CrossRef]
- Hoyos, J.; Dehus, M.; Brown, T.X. Exploiting the GOOSE protocol: A practical attack on cyber-infrastructure. In Proceedings of the 2012 IEEE Globecom Workshops, Anaheim, CA, USA, 3–7 December 2012; IEEE: Piscataway, NJ, USA, 2012; pp. 1508–1513. [Google Scholar]
- Kabir-Querrec, M.; Mocanu, S.; Bellemain, P.; Thiriet, J.M.; Savary, E. Corrupted goose detectors: Anomaly detection in power utility real-time ethernet communications. In Proceedings of the GreHack 2015, Grenoble, France, 20–22 November 2015. [Google Scholar]
- Noce, J.; Lopes, Y.; Fernandes, N.C.; Albuquerque, C.V.; Muchaluat-Saade, D.C. Identifying vulnerabilities in smart gric communication networks of electrical substations using geese 2.0. In Proceedings of the 2017 IEEE 26th International Symposium on Industrial Electronics (ISIE), Edinburgh, UK, 19–21 June 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 111–116. [Google Scholar]
- Da Silva, L.E.; Coury, D.V. A new methodology for real-time detection of attacks in IEC 61850-based systems. Electr. Power Syst. Res. 2017, 143, 825–833. [Google Scholar] [CrossRef]
- Zhang, F.; Mahler, M.; Li, Q. Flooding attacks against secure time-critical communications in the power grid. In Proceedings of the 2017 IEEE International Conference on Smart Grid Communications (SmartGridComm), Dresden, Germany, 23–26 October 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 449–454. [Google Scholar]
- Li, Q.; Ross, C.; Yang, J.; Di, J.; Balda, J.C.; Mantooth, H.A. The effects of flooding attacks on time-critical communications in the smart grid. In Proceedings of the 2015 IEEE Power & Energy Society Innovative Smart Grid Technologies Conference (ISGT), Washington, DC, USA, 17–20 February 2015; IEEE: Piscataway, NJ, USA, 2015; pp. 1–5. [Google Scholar]
- Elbez, G.; Keller, H.B.; Hagenmeyer, V. A cost-efficient software testbed for cyber-physical security in iec 61850-based substations. In Proceedings of the 2018 IEEE International Conference on Communications, Control, and Computing Technologies for Smart Grids (SmartGridComm), Aalborg, Denmark, 29–31 October 2018; IEEE: Piscataway, NJ, USA, 2018; pp. 1–6. [Google Scholar]
- Strobel, M.; Wiedermann, N.; Eckert, C. Novel weaknesses in IEC 62351 protected smart grid control systems. In Proceedings of the 2016 IEEE International Conference on Smart Grid Communications (SmartGridComm), Sydney, Australia, 6–9 November 2016; IEEE: Piscataway, NJ, USA, 2016; pp. 266–270. [Google Scholar]
- Subramaniam Rajkumar, V.; Tealane, M.; Stefanov, A.; Palensky, P. Cyber Attacks on Protective Relays in Digital Substations and Impact Analysis. In Proceedings of the 8th Workshop on Modeling and Simulation of Cyber-Physical Energy Systems, MSCPES 2020-Proceedings, Sydney, Australia, 21 April 2020; IEEE: Piscataway, NJ, USA, 2020. [Google Scholar]
- Kang, B.; Maynard, P.; McLaughlin, K.; Sezer, S.; Andrén, F.; Seitl, C.; Kupzog, F.; Strasser, T. Investigating cyber-physical attacks against IEC 61850 photovoltaic inverter installations. In Proceedings of the 2015 IEEE 20th Conference on Emerging Technologies & Factory Automation (ETFA), Luxembourg, 8–11 September 2015; IEEE: Piscataway, NJ, USA, 2015; pp. 1–8. [Google Scholar]
- Zhang, J.; Chen, Y.; Jin, N.; Hou, L.; Zhang, Q. OPNET based simulation modeling and analysis of DoS attack for digital substation. In Proceedings of the 2017 IEEE Power & Energy Society General Meeting, Chicago, IL, USA, 16–20 July 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 1–5. [Google Scholar]
- Gaderer, G.; Treytl, A.; Sauter, T. Security aspects for IEEE 1588 based clock synchronization protocols. In Proceedings of the IEEE International Workshop on Factory Communication Systems (WFCS), Torino, Italy, 28–30 June 2006; pp. 247–250. [Google Scholar]
- Tsang, J.; Beznosov, K. A security analysis of the precise time protocol (short paper). In Proceedings of the International Conference on Information and Communications Security, Raleigh, NC, USA, 4–7 December 2006; Springer: Berlin/Heidelberg, Germany, 2006; pp. 50–59. [Google Scholar]
- Alghamdi, W.; Schukat, M. Cyber Attacks on Precision Time Protocol Networks—A Case Study. Electronics 2020, 9, 1398. [Google Scholar] [CrossRef]
- Ullmann, M.; Vögeler, M. Delay attacks—Implication on NTP and PTP time synchronization. In Proceedings of the 2009 International Symposium on Precision Clock Synchronization for Measurement, Control and Communication, Brescia, Italy, 12–16 October 2009; IEEE: Piscataway, NJ, USA, 2009; pp. 1–6. [Google Scholar]
- Annessi, R.; Fabini, J.; Iglesias, F.; Zseby, T. Encryption is futile: Delay attacks on high-precision clock synchronization. arXiv 2018, arXiv:1811.08569. [Google Scholar]
- Han, M.; Crossley, P. Vulnerability of IEEE 1588 under time synchronization attacks. In Proceedings of the 2019 IEEE Power & Energy Society General Meeting (PESGM), Atlanta, GA, USA, 4–8 August 2019; IEEE: Piscataway, NJ, USA, 2019; pp. 1–5. [Google Scholar]
- Finkenzeller, A.; Wakim, T.; Hamad, M.; Steinhorst, S. Feasible Time Delay Attacks Against the Precision Time Protocol. In Proceedings of the GLOBECOM 2022-2022 IEEE Global Communications Conference, Rio de Janeiro, Brazil, 4–8 December 2022; IEEE: Piscataway, NJ, USA, 2022; pp. 3375–3380. [Google Scholar]
- Treytl, A.; Hirschler, B. Security flaws and workarounds for IEEE 1588 (transparent) clocks. In Proceedings of the 2009 International Symposium on Precision Clock Synchronization for Measurement, Control and Communication, Brescia, Italy, 12–16 October 2009; IEEE: Piscataway, NJ, USA, 2009; pp. 1–6. [Google Scholar]
- Zhang, Z.; Gong, S.; Dimitrovski, A.D.; Li, H. Time synchronization attack in smart grid: Impact and analysis. IEEE Trans. Smart Grid 2013, 4, 87–98. [Google Scholar] [CrossRef]
- Moussa, B.; Debbabi, M.; Assi, C. A detection and mitigation model for PTP delay attack in an IEC 61850 substation. IEEE Trans. Smart Grid 2016, 9, 3954–3965. [Google Scholar] [CrossRef]
- Li, Z.; Ma, R.; Xie, Y.; Lu, L. Overview of Intrusion Detection in Smart Substation. In Proceedings of the 2022 IEEE 10th Joint International Information Technology and Artificial Intelligence Conference (ITAIC), Chongqing, China, 8–10 December 2022; Volume 10, pp. 2377–2384. [Google Scholar] [CrossRef]
- Narula, L.; Humphreys, T.E. Requirements for secure clock synchronization. IEEE J. Sel. Top. Signal Process. 2018, 12, 749–762. [Google Scholar] [CrossRef]
- Alghamdi, W.; Schukat, M. Advanced methodologies to deter internal attacks in PTP time synchronization networks. In Proceedings of the 2017 28th Irish Signals and Systems Conference (ISSC), Killarney, Ireland, 20–21 June 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 1–6. [Google Scholar]
- Moradi, M.; Jahangir, A.H. A new delay attack detection algorithm for PTP network in power substation. Int. J. Electr. Power Energy Syst. 2021, 133, 107226. [Google Scholar] [CrossRef]
- Lisova, E.; Uhlemann, E.; Steiner, W.; Åkerberg, J.; Björkman, M. Risk evaluation of an ARP poisoning attack on clock synchronization for industrial applications. In Proceedings of the 2016 IEEE International Conference on Industrial Technology (ICIT), Taipei, Taiwan, 14–17 March 2016; IEEE: Piscataway, NJ, USA, 2016; pp. 872–878. [Google Scholar]
- Jørgensen, P.A.; Waltoft-Olsen, A.; Houmb, S.H.; Toppe, A.L.; Soltvedt, T.G.; Muggerud, H.K. Building a hardware-in-the-loop (HiL) digital energy station infrastructure for cyber operation resiliency testing. In Proceedings of the 3rd International Workshop on Engineering and Cybersecurity of Critical Systems, Pittsburgh, PA, USA, 16 May 2022; pp. 9–16. [Google Scholar]
- Erdődi, L.; Kaliyar, P.; Houmb, S.H.; Akbarzadeh, A.; Waltoft-Olsen, A.J. Attacking Power Grid Substations: An Experiment Demonstrating How to Attack the SCADA Protocol IEC 60870-5-104. In Proceedings of the 17th International Conference on Availability, Reliability and Security, Vienna, Austria, 23–26 August 2022; pp. 1–10. [Google Scholar]
- Rocchetto, M.; Tippenhauer, N.O. On attacker models and profiles for cyber-physical systems. In Proceedings of the European Symposium on Research in Computer Security, Heraklion, Greece, 26–30 September 2016; Springer: Berlin/Heidelberg, Germany, 2016; pp. 427–449. [Google Scholar]









| Attack | Consequence |
| Denial of service (DoS) | Service Unavailable |
| Selective packet delay | Offset up to sync cycle |
| Packet manipulation | Loss of control |
| Byzantine master | Loss of control |
| Packet Removal from Control Loop | Deviation depends on clock precision |
| Control Loop Disruption | Deviation depends on clock precision |
| Packet injection | Offsets vary based on sync cycle implementation |
| Attack Step | Attacker Action | Attack Technique | Outcome |
|---|---|---|---|
| Step 1 (start) | Attacker collects information regarding the clock sources (Meinberg and Siemens). | Passive reconnaissance. | Attacker obtains information that is used in later attack stages. |
| Step 2 | Attacker takes over as the master clock | Manipulation—Rough master clock emulation. | Multiple clocks in the network (more than what is configured). |
| Step 3 | Attacker maintains the status with the master clock emulation (repeating the message every second). | Manipulation—Rough master clock emulation with broadcast messages. | Both real clock sources stopped working. No PTP time synchronization was available in the network. IEDs start using their internal clock and flagging missing time synchronization on SVMs. |
| Step 4 | Attacker maintains the status with the master clock emulation (repeating the message every second). | Manipulation—Rough master clock emulation with broadcast messages. | Real clocks are not operating any longer. No PTP time synchronization was available in the network. IEDs continued using their internal clock source. |
| Step 5 | Attacker sends time synchronization messages. | Manipulation—Rough master clock emulation with broadcast messages and link layer messages. | The network switch does not forward time synchronization to IEDs. IEDs continue to use their internal clock source. |
| Step 6 (stop) | Attacker stops sending PTP messages. | Passive reconnaissance. | Real clock sources start to operate again after a time delay. IEDs are synchronized again after a time delay. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Akbarzadeh, A.; Erdodi, L.; Houmb, S.H.; Soltvedt, T.G.; Muggerud, H.K. Attacking IEC 61850 Substations by Targeting the PTP Protocol. Electronics 2023, 12, 2596. https://doi.org/10.3390/electronics12122596
Akbarzadeh A, Erdodi L, Houmb SH, Soltvedt TG, Muggerud HK. Attacking IEC 61850 Substations by Targeting the PTP Protocol. Electronics. 2023; 12(12):2596. https://doi.org/10.3390/electronics12122596
Chicago/Turabian StyleAkbarzadeh, Aida, Laszlo Erdodi, Siv Hilde Houmb, Tore Geir Soltvedt, and Hans Kristian Muggerud. 2023. "Attacking IEC 61850 Substations by Targeting the PTP Protocol" Electronics 12, no. 12: 2596. https://doi.org/10.3390/electronics12122596







