Secure and Privacy-Preserving Authentication Scheme Using Decentralized Identifier in Metaverse Environment
Abstract
:1. Introduction
1.1. Contributions
- In the metaverse environment, users are exposed to threats, such as fraud through fake avatars and the risk of personal information leakage during data transmission through open channels. We propose a secure authentication method for the metaverse environment to ensure security against various threats arising from fake avatars or vulnerabilities in wireless communication channels, and provide forward secrecy, anonymity, and privacy preservation.
- The proposed scheme utilizes decentralized identifiers and verifiable credentials to enhance user privacy protection. Metaverse users can provide only the necessary identity information to stakeholders without disclosing their information to external parties, thereby safeguarding their personal information.
- We perform an informal analysis to ensure that the proposed scheme can provide security against various attacks, including impersonation, session key disclosure, replay, man-in-the-middle, and insider attacks. Additionally, we show that the proposed scheme can achieve mutual authentication, perfect forward secrecy, anonymity and privacy preservation.
- The security of the proposed scheme is analyzed by performing informal and formal analyses, such as Burrows–Abadi–Nikoogadam (BAN) logic, the real-or-random (RoR) model, and the automated validation of internet security protocols and applications (AVISPA) simulation tool. We also compare the performance and security features with the related works to show that the proposed scheme is superior.
1.2. Organization
2. Related Work
3. Preliminaries
3.1. Fuzzy Extractor
- : The user’s biometric information is accepted as an input parameter to the algorithm. Then, the secret value r is output along with the public reproduction parameter .
- : The algorithm accepts a noisy user biometric from the user, controlling the noise using the public reproduction parameter . Then, reproduces the original biometric secret value r.
3.2. Decentralized Identifier and Verifiable Credential
- 1.
- Decentralized identifier creation: Users or entities generate DIDs. DIDs are unique and can be created by users themselves, not centralized authentication authorities.
- 2.
- Integration with blockchain: DIDs are stored in conjunction with a blockchain. This ensures that DIDs are stored in a distributed registry, making duplication or alteration difficult.
- 3.
- Digital identity verification: To log in to digital services or applications using their DID, users create a signature using their private key.
- 4.
- Distributed identity management: Users manage their DIDs and identity information in a distributed network. This information is stored on the blockchain, ensuring immutability, and users share it only when necessary.
- 1.
- Creation of VCs: Users process their identity-related data to generate VCs. These VCs include the user’s identity information and the user’s signature using the elliptic curve-based signature algorithm.
- 2.
- Issuer of VCs: VCs are created by the party or institution that issues the information. The issuer verifies the source of the information and signs the VC to ensure its integrity.
- 3.
- Storage and transmission of VCs: VCs are stored in a digital format, and users share them only when necessary. VCs are securely transmitted and stored, often in encrypted form.
- 4.
- Verification of VCs: When presenting VCs to a verifier, the verifier uses the issuer’s public key to verify the signature of the VC and validate the accuracy of the information. This confirms the authenticity of the VC.
- 5.
- Selective sharing of VCs: Users can share only the necessary information through VCs, enhancing personal data protection. They provide minimal information to third parties and perform required identity verification.
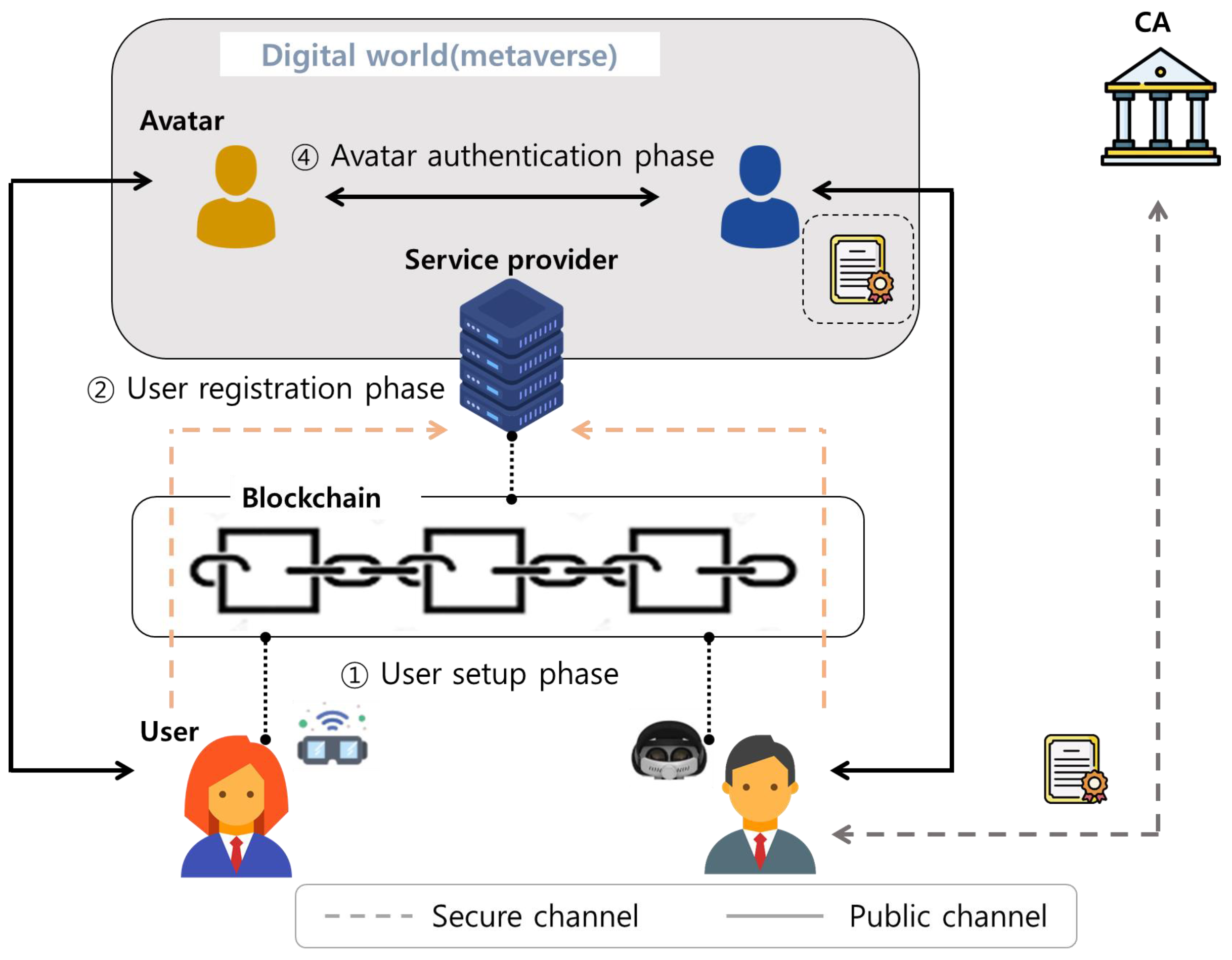
4. System Model
- Certificate authority (): serves as a fully trusted entity that initializes and publishes system parameters. receives the user’s decentralized identifier and personal information, which require verification. Then, verifies both and issues a credential to the user proving the user’s personal information (occupation, age, etc.). The credential values must be authenticated between the users/avatars in the metaverse environment.
- Service provider (): s offer services that enable users to engage in various activities in virtual spaces, such as education, gaming, healthcare, and more. The user first registers on the using the decentralized identifier. If a user attempts to access the , verifies the correct identity of the user. In addition, the is responsible for forwarding request and response messages that occur in its own virtual space during the avatar authentication phase.
- User: The user creates his/her own decentralized identifier on the blockchain. The user sends his/her decentralized identifier and personal information to to receive credentials to prove their personal information. Then, the user registers with the to participate in the metaverse environment. At this time, the user transmits only minimal information to register with the , and no other personal information is transmitted. The user can interact with other users by using avatars created in the virtual world, such as exchanging information with other users for various purposes. The user uses DID, public key, and verifiable credentials in the virtual space to mutually authenticate with other users’ avatars to achieve secure interaction between avatars and avatars.
- Blockchain: In the proposed authentication scheme, we adopt the public blockchain, which is a fully decentralized infrastructure. In the public blockchain network, every node can easily join blockchain networks without the need for a trusted authority. All blockchain members can read the ledger and upload transitions to the blockchain. To ensure that all entities participating in the system agree on a single source of truth, the public blockchain adopts proof-based consensus algorithms, including proof of work and proof of stake. In our system, the blockchain is adopted to store the information required for authentication, and it does not contain any other information other than DID documents. In the proposed scheme, we assume that the consensus process of the blockchain operates correctly and reliably.
- User setup phase: The user generates their own decentralized identifier. The issues a verifiable credential to the user that proves the user’s personal information.
- User registration phase: The user registers with the using his/her own decentralized identifier. The verifies that the user’s decentralized identifier is valid, and then the user’s avatar is generated in virtual space.
- Login phase: When the user attempts to access the , the user and authenticate each other. If the mutual authentication between the user and is completed and the session key is agreed upon, the user and establish a secure communication channel through the session key.
- Avatar authentication phase: In the virtual space, the user can interact with other avatars. For secure avatar-to-avatar interactions, the user provides verifiable credentials, proving the personal information needed to perform the avatar authentication phase.
4.1. Adversary Model
- An adversary can eavesdrop, intercept, modify, expunge, and forge the transmitted messages through a public channel.
- An adversary can conjecture about either the identity or the password of a legitimate user, but it is incapable of conjecturing about both simultaneously.
- An adversary can attempt to launch various attacks, including impersonation, replay attacks, and man-in-the-middle attacks.
- An adversary can be an insider in the .
5. Proposed Scheme
5.1. Initialization Phase
5.2. User Setup
- US-1: User inputs a unique , password and biometric information . Then, selects a random number as a private key and computes , , . Then, generates the ’s own that indicates the location of the DID document on the blockchain.
- US-2: requests to issue a credential by sending , personal information . checks a ’s personal information and , and issues a verifiable credential that vouches for ’s personal information, such as occupation, age, etc. Then, sends to . After checking , computes and stores in the device.
5.3. User Registration Phase
- UR-1: inputs a identity , password , and imprints a biomatic information . Then, computes , , , , and send to .
- UR-2: checks the validity of and retrieves from the blockchain. If it is valid, computes , and verifies . If the equation is correct, selects a random nonce and calculates , . After that, dispatches to and stores in a secure database.
- UR-3: computes , , and stores in ’s XR devices.
5.4. Login Phase
- LA-1: User first enters , , and . Then, computes , , , , , , and checks the . If the equation is correct, selects a random nonce and a current timestamp , and computes , . After that, sends to .
- LA-2: generates a current timestamp and checks the freshness of the timestamp. Next, retrieves from the database using , and calculates , . checks the , and selects a random nonce and calculates , , , . After that, transmits to .
- LA-3: After reception of the messages, checks the freshness of and computes , , . Then, checks the validity of , calculates , and updates with .
5.5. Avatar Authentication Phase
- AA-1: first sends a request including to . After reception of the request, retrieves using , and selects a random nonce and a current timestamp . Next, computes , , , , and sends to .
- AA-2: After receiving the message , checks the validity of , and retrieves from the blockchain using . Then, computes , , and verifies the equation and the signature of the . Next, selects a random nonce and calculates , , , . And transmits to .
- AA-3: Upon reception of message , checks the freshness of and computes , , . Finally, checks that is correct and verifies ’s signature .
6. Security Analysis
6.1. Informal Security Analysis
6.1.1. Stolen XR Device Attack
6.1.2. Offline Password-Guessing Attack
6.1.3. Impersonation Attack
6.1.4. Avatar Impersonation Attack
6.1.5. Session Key Disclosure Attack
6.1.6. Perfect Forward Secrecy
6.1.7. Replay Attack and MITM Attack
6.1.8. Insider Attack
6.1.9. Ephemeral Secret Leakage Attack
6.1.10. Mutual Authentication
6.1.11. Anonymity
6.1.12. Privacy-Preservation
6.1.13. Untraceability
6.1.14. Denial-of-Service (DoS) Attack
6.2. Security Analysis Using BAN Logic
BAN Logic Rules
- Message meaning rule:
- Nonce verification rule:
- Jurisdiction rule:
- Freshness rule:
- Belief rule:
6.3. Goals
- Goal 1:
- Goal 2:
- Goal 3:
- Goal 4:
6.3.1. Idealized Forms
- Msg1:
- :
- Msg2:
- :
6.3.2. Assumptions
- :
- :
- :
- :
- :
- :
- :
- :
6.3.3. Proof Using BAN Logic
- Step 1:
- From ,
- Step 2:
- Upon the message meaning rule with and ,
- Step 3:
- Using the freshness rule with ,
- Step 4:
- Using the nonce verification rule with and ,
- Step 5:
- Since the session key , from and ,
- Step 6:
- Upon the jurisdiction rule with and ,
- Step 7:
- Using the ,
- Step 8:
- From the message meaning rule with and ,
- Step 9:
- Using the freshness rule with ,
- Step 10:
- Upon the nonce verification rule with and ,
- Step 11:
- Since the session key , from and ,
- Step 12:
- Utilizing the jurisdiction rule with and ,
6.4. ROR Model
- Game 0: presents the ’s real attacks against our proposed scheme in the ROR model. selects the bit c at the starting of . is as follows.
- Game 1: is modeled such that implements an eavesdropping attack. In this game, executes the query to steal the communicated messages and between and . At the end of this game, executes and queries to check whether the derived session key is an actual or random key. needs the long-term secret values (such as the private keys and ), and the short-term secret values (such as the random nonces and ) to extract the . However, it is impracticable for to obtain these secret values, even if obtains all communicated messages. As shown, the eavesdropping messages , and do not increase the probability of a winning game . Therefore, because games and are indistinguishable, we obtain
- Game 2: is modeled as an active attack. In this game, executes the and queries to guess the hash collision. However, all exchanged messages are protected using the one-way hash function and consist of secret credentials and random numbers. Moreover, it is difficult for to derive secret credentials and a random nonce because it is a computationally infeasible problem depending on the properties of . So, using the birthday paradox, we obtain the following inequality:
- Game 3: is modeled such that an active attack is implemented by . In this game, executes the query to extract the secret values from the user’s XR devices. Subsequently, to derive credential and ’s secret key , must guess the unknown password through operating the query. However, it is computationally infeasible for to guess the password through the query without ’s identity and secret nonce . In the absence of password-guessing attacks, games and are identical. The probability of winning the game using Zip’s law is
6.5. Avispa Simulation Tool
7. Performance Analysis
7.1. Analysis of Computation Cost
7.2. Analysis of Communication Cost
7.3. Security and Functionality Comparison
8. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Xu, M.; Ng, W.C.; Lim, W.Y.B.; Kang, J.; Xiong, Z.; Niyato, D.; Yang, Q.; Shen, X.; Miao, C. A full dive into realizing the edge-enabled metaverse: Visions, enabling technologies, and challenges. IEEE Commun. Surv. Tutor. 2023, 25, 656–700. [Google Scholar] [CrossRef]
- Yang, Q.; Zhao, Y.; Huang, H.; Xiong, Z.; Kang, J.; Zheng, Z. Fusing blockchain and AI with metaverse: A survey. IEEE Open J. Comput. Soc. 2022, 3, 122–136. [Google Scholar] [CrossRef]
- Huynh-The, T.; Gadekallu, T.R.; Wang, W.; Yenduri, G.; Ranaweera, P.; Pham, Q.V.; Costa, D.B.; Liyanage, M. Blockchain for the metaverse: A review. Futur. Gener. Comp. Syst. 2023, 143, 401–419. [Google Scholar] [CrossRef]
- Bansal, G.; Rajgopal, K.; Chamola, V.; Xiong, Z.; Niyato, D. Healthcare in metaverse: A survey on current metaverse applications in healthcare. IEEE Access 2022, 10, 119914–119946. [Google Scholar] [CrossRef]
- Park, S.; Kim, Y. A metaverse: Taxonomy, components, applications, and open challenges. IEEE Access 2022, 10, 4209–4251. [Google Scholar] [CrossRef]
- A Researcher’s Avatar was Sexually Assaulted on a Metaverse Platform Owned by Meta, Making Her the Latest Victim of Sexual Abuse on Meta’s Platforms, Watchdog Says. Available online: https://www.businessinsider.com/researcher-claims-her-avatar-was-raped-on-metas-metaverse-platform-2022-5 (accessed on 20 September 2023).
- Wang, Y.; Su, Z.; Zhang, N.; Xing, R.; Liu, D.; Luan, T.H.; Shen, X. A survey on metaverse: Fundamentals, security, and privacy. IEEE Commun. Surv. Tutor. 2023, 25, 319–352. [Google Scholar] [CrossRef]
- Falchuck, B.; Loeb, S.; Neff, R. The social metaverse: Battle for privacy. IEEE Technol. Soc. Mag. 2018, 37, 52–61. [Google Scholar] [CrossRef]
- Li, Y.; Cheng, Y.; Meng, W.; Li, Y.; Deng, R.H. Designing leakage-resilient password entry on head-mounted smart wearable glass devices. IEEE Trans. Inf. Forensic Secur. 2020, 16, 307–321. [Google Scholar] [CrossRef]
- Sayeed, S.; Pitropakis, N.; Buchanan, W.J.; Markakis, E.; Papatsaroucha, D.; Politis, I. TRUSTEE: Towards the creation of secure, trustworthy and privacy-preserving framework. In Proceedings of the 18th International Conference on Availability, Reliability and Security, Benevento, Italy, 29 August–1 September 2023; pp. 1–10. [Google Scholar]
- Tu, S.; Yu, H.; Badshah, A.; Waqas, M.; Halim, Z.; Ahmad, I. Secure internet of vehicles (IoV) with decentralized consensus blockchain mechanism. IEEE Trans. Veh. Technol. 2023, 72, 11227–11236. [Google Scholar] [CrossRef]
- Sayeed, S.; Marco-Gisbert, H. Assessing blockchain consensus and security mechanisms against the 51% attack. IEEE Commun. Surv. Tutor. 2019, 9, 1788. [Google Scholar] [CrossRef]
- Truong, V.T.; Le, L.; Niyato, D. Blockchain meets metaverse and digital asset management: A comprehensive survey. IEEE Access 2023, 11, 26258–26288. [Google Scholar] [CrossRef]
- Patwe, S.; Mane, S. Blockchain enabled architecture for secure authentication in the metaverse environment. In Proceedings of the 2023 IEEE 8th International Conference for Convergence in Technology (I2CT), Lonavla, India, 7–9 April 2023; pp. 1–8. [Google Scholar]
- Huang, Y.; Li, Y.J.; Cai, Z. Security and privacy in metaverse: A comprehensive survey. Big Data Min. Anal. 2023, 6, 234–247. [Google Scholar] [CrossRef]
- Panda, P.K.; Chattopadhyay, S. A secure mutual authentication protocol for IoT environment. J. Reliable Intell. Environ. 2020, 6, 79–94. [Google Scholar] [CrossRef]
- Li, Y.; Xu, M.; Xu, G. Blockchain-based mutual authentication protocol without CA. J. Supercomput. 2022, 78, 17261–17283. [Google Scholar] [CrossRef]
- Ryu, J.; Son, S.; Lee, J.; Park, Y.; Park, Y. Design of secure mutual authentication scheme for metaverse environments using blockchain. IEEE Access 2022, 10, 98944–98958. [Google Scholar] [CrossRef]
- Dodis, Y.; Reyzin, L.; Smith, A. Fuzzy extractors: How to generate strong keys from biometrics and other noisy data. In Proceedings of the International Conference on the Theory and Applications of Cryptographic Techniques, Interlaken, Switzerland, 2–6 May 2004; pp. 523–540. [Google Scholar]
- Decentralized Identifiers (DIDs) v1.0 Core Architecture, Data Model, and Representations. Available online: https://www.w3.org/TR/did-core/ (accessed on 22 August 2023).
- Verifiable Credentials Data Model 1.1. Available online: https://www.w3.org/TR/vc-data-model/ (accessed on 22 August 2023).
- Dolev, D.; Yao, A. On the security of public key protocols. IEEE Trans. Inf. Theory 1983, 29, 198–208. [Google Scholar] [CrossRef]
- Masud, M.; Gaba, G.S.; Choudhary, K.; Hossain, M.S.; Alhamid, M.F.; Muhammad, G. Lightweight and anonymity-preserving user authentication scheme for IoT-based healthcare. IEEE Internet Things J. 2022, 9, 2649–2656. [Google Scholar] [CrossRef]
- Kim, M.; Lee, J.; Oh, J.; Kwon, D.; Park, K.; Park, Y.; Park, K.H. A secure batch authentication scheme for multiaccess edge computing in 5G-enabled intelligent transportation system. IEEE Access 2022, 10, 96224–96238. [Google Scholar] [CrossRef]
- Bhattacharya, M.; Roy, S.; Chattopadhyay, S.; Das, A.K.; Jamal, S.S. ASPA-MOSN: An efficient user authentication scheme for phishing attack detection in mobile online social networks. IEEE Syst. J. 2023, 17, 234–245. [Google Scholar] [CrossRef]
- Kocher, P.; Jaffe, J.; Jun, B. Differential power analysis. In Proceedings of the Annual International Cryptology Conference (CRYPTO), Santa Barbara, CA, USA, 15–19 August 1999; pp. 388–397. [Google Scholar]
- Son, S.; Kwon, D.; Lee, S.; Jeon, Y.; Das, A.K.; Park, Y. Design of secure and lightweight authentication scheme for UAV-enabled intelligent transportation systems using blockchain and PUF. IEEE Access 2023, 11, 60240–60253. [Google Scholar] [CrossRef]
- Kim, M.; Lee, J.; Park, K.; Park, Y.; Park, K.H.; Park, Y. Design of secure decentralized car-sharing system using blockchain. IEEE Access 2021, 9, 54796–54810. [Google Scholar] [CrossRef]
- Canetti, R.; Krawczyk, H. Universally composable notions of key exchange and secure channels. In Proceedings of the International Conference on the Theory and Applications of Cryptographic Techniques, Amsterdam, The Netherlands, 28 April–2 May 2002; pp. 337–351. [Google Scholar]
- Soni, P.; Pardhan, J.; Pal, A.K.; Islam, S.K.H. Cybersecurity attack-resilience authentication mechanism for intelligent healthcare system. IEEE Trans. Ind. Inform. 2023, 19, 830–840. [Google Scholar] [CrossRef]
- Oh, J.; Yu, S.; Lee, J.; Son, S.; Kim, M.; Park, Y. A secure and lightweight authentication protocol for IoT-based smart homes. Sensors 2021, 21, 1488. [Google Scholar] [CrossRef] [PubMed]
- Hosseinzadeh, M.; Ahmed, O.H.; Ahmed, S.H.; Trinh, C.; Bagheri, N.; Kumari, S.; Lansky, J.; Huynh, B. An enhanced authentication protocol for RFID systems. IEEE Access 2020, 8, 126977–126987. [Google Scholar] [CrossRef]
- Lee, J.; Kim, G.; Das, A.K.; Park, Y. Secure and efficient honey list-based authentication protocol for vehicular ad hoc networks. IEEE Trans. Netw. Sci. Eng. 2021, 8, 2412–2425. [Google Scholar] [CrossRef]
- Chen, C.M.; Chen, Z.; Kumari, S.; Lin, M.C. LAP-IoHT: A lightweight authentication protocol for the internet of health things. Sensors 2022, 22, 5401. [Google Scholar] [CrossRef]
- Wang, D.; Cheng, H.; Wang, P.; Huang, X.; Jian, G. Zipf’s law in passwords. IEEE Trans. Inf. Forensics Secur. 2017, 12, 2776–2791. [Google Scholar] [CrossRef]
- AVISPA. Automated Validation of Internet Security Protocols and Applications. Available online: http://www.avispa-project.org/ (accessed on 22 August 2023).
- SPAN: A Security Protocol Animator for AVISPA. Available online: https://people.irisa.fr/Thomas.Genet/span/ (accessed on 22 August 2023).
- Yu, S.; Lee, J.; Park, Y.; Park, Y.; Lee, S.; Chung, B. A secure and efficient three-factor authentication protocol in global mobility networks. Appl. Sci. 2020, 10, 3565. [Google Scholar] [CrossRef]
- Kilinc, H.H.; Yanik, T. A survey of SIP authentication and key agreement schemes. IEEE Commun. Surv. Tutor. 2013, 16, 1005–1023. [Google Scholar] [CrossRef]
- Ravanbakhsh, N.; Nazari, M. An efficient improvement remote user mutual authentication and session key agreement scheme for E-health care systems. Multimed. Tools Appl. 2018, 77, 55–88. [Google Scholar] [CrossRef]
- Gope, P.; Sikdar, B. Lightweight and privacy-preserving two-factor authentication scheme for IoT devices. IEEE Internet Things J. 2019, 6, 580–589. [Google Scholar] [CrossRef]







| Symbol | Description |
|---|---|
| i-th user | |
| The service provider | |
| A certificate authority | |
| Identity and password of | |
| Secret key and public key of entity x | |
| Decentralized identity of entity x | |
| Hash function | |
| T | Timestamp |
| Random nonces | |
| ⊕ | XOR operation |
| Concatenation operation |
| Notation | Description |
|---|---|
| believes statement X | |
| #X | Statement X is fresh |
| sees statement X | |
| controls statement X | |
| once said X | |
| X is encrypted under key K | |
| Formula X is combined with formula Y | |
| and may use shared key K to communicate | |
| has K as a public key | |
| Session key used in the current session |
| Query | Description |
|---|---|
| using this query to tap the communication messages transmitted between and . | |
| sends a messages to the and receives a response messages from . | |
| gets a current session key between and its partner. | |
| guesses the probabilistic outcome for a flipped unbiased coin C. If the session key is fresh, receives . If the session key is not fresh, receives . Otherwise, obtains null value (⊥). | |
| This query presumes an active attack. extracts secret values stored in the XR devices by executing a power analysis. |
| Schemes | User | Service Provider |
|---|---|---|
| Panda and Chattopadhyay [16] | ms | ms |
| Li et al. [17] | ms | ms |
| Ryu et al. [18] | ms | ms |
| The proposed scheme | ms | ms |
| Schemes | Costs |
|---|---|
| Panda and Chattopadhyay [16] | 1440 bits |
| Li et al. [17] | 1888 bits |
| Ryu et al. [18] | 1344 bits |
| Our scheme | 1024 bits |
| Panda and Chattopadhyay [16] | Li et al. [17] | Ryu et al. [18] | Our Scheme | |
|---|---|---|---|---|
| Stolen IoT devices(XR) attack | − | − | √ | √ |
| Offline password guessing attack | √ | − | √ | √ |
| Impersonation attack | √ | √ | √ | √ |
| Avatar impersonation attack | − | − | √ | √ |
| Session key disclosure attack | √ | √ | √ | √ |
| Perfect forward secrecy | √ | √ | √ | √ |
| Replay attack | √ | √ | √ | √ |
| MITM attack | √ | √ | √ | √ |
| Insider attack | √ | − | √ | √ |
| Ephemeral secret leakage attack | × | √ | √ | √ |
| Mutual authentication | × | √ | √ | √ |
| Anonymity | √ | × | √ | √ |
| Privacy-preservation | − | − | × | √ |
| Untraceability | √ | × | √ | √ |
| Denial-of-Service (DoS) Attack | × | √ | × | √ |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kim, M.; Oh, J.; Son, S.; Park, Y.; Kim, J.; Park, Y. Secure and Privacy-Preserving Authentication Scheme Using Decentralized Identifier in Metaverse Environment. Electronics 2023, 12, 4073. https://doi.org/10.3390/electronics12194073
Kim M, Oh J, Son S, Park Y, Kim J, Park Y. Secure and Privacy-Preserving Authentication Scheme Using Decentralized Identifier in Metaverse Environment. Electronics. 2023; 12(19):4073. https://doi.org/10.3390/electronics12194073
Chicago/Turabian StyleKim, Myeonghyun, Jihyeon Oh, Seunghwan Son, Yohan Park, Jungjoon Kim, and Youngho Park. 2023. "Secure and Privacy-Preserving Authentication Scheme Using Decentralized Identifier in Metaverse Environment" Electronics 12, no. 19: 4073. https://doi.org/10.3390/electronics12194073
APA StyleKim, M., Oh, J., Son, S., Park, Y., Kim, J., & Park, Y. (2023). Secure and Privacy-Preserving Authentication Scheme Using Decentralized Identifier in Metaverse Environment. Electronics, 12(19), 4073. https://doi.org/10.3390/electronics12194073









