Pinicorn: Towards Automated Dynamic Analysis for Unpacking 32-Bit PE Malware
Abstract
1. Introduction
- Contributions: This paper makes the following contributions:
- We provide an analysis of packers and their role in hindering reverse-engineering of programs.
- We propose an automated dynamic analysis approach for de-obfuscating and unpacking programs.
- We introduce an Emulator-based Obfuscated Code Execution method, demonstrating its efficacy in identifying and analyzing trampoline code in packed programs.
1.1. The Impact of General Packers on Binaries
1.2. Anti-Analysis Techniques
1.3. OEP Finding
1.4. Import Table Reconstruction
1.5. OEP and API Obfuscation Techniques
1.6. OEP Obfuscation: A Deep Insight
1.7. API Obfuscation: A Deep Insight
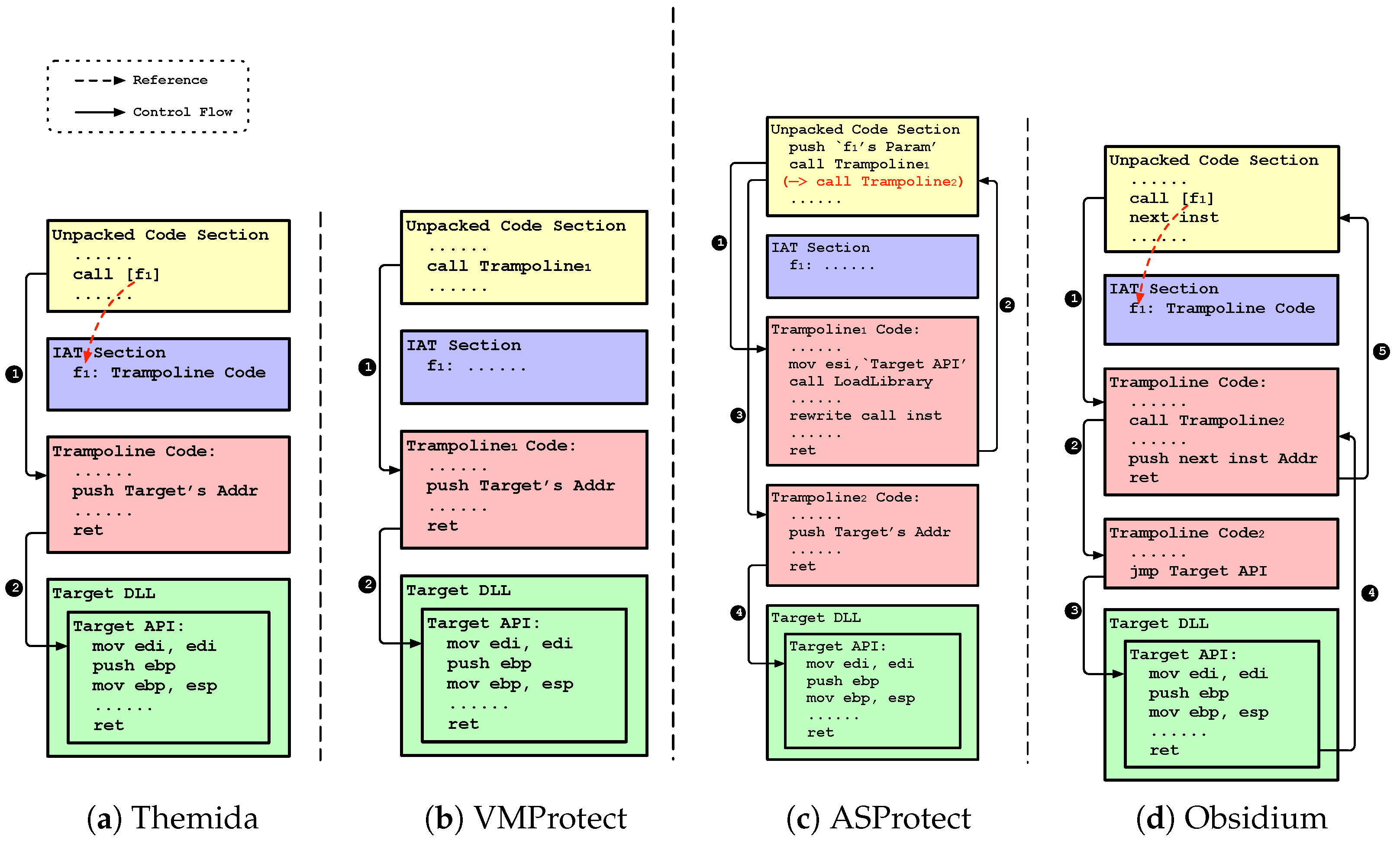
- Indirect Calls: Packers such as Themida use the IAT to bind trampoline codes at runtime, redirecting API calls to these codes (Figure 4a,d).
- Direct Calls: Alternatively, packers like VMProtect and ASProtect modify API call instructions to point directly to trampoline codes, bypassing the IAT (Figure 4b,c).
1.8. Summary of Related Works on Malware Unpacking and Analysis Techniques
2. Design
2.1. Overview
2.1.1. Scope
2.1.2. Challenges
- Counteracting Anti-analysis Techniques: Commercial protectors often deploy evasion techniques such as Anti-Debug and Anti-VM, probing memory structures and system settings. The straightforward nature of these techniques enables obfuscated software, especially malware, to efficiently detect analyis tools. This critical aspect is often overlooked in previous research.
- Trampoline Code Analysis Problem: Obfuscated binaries contain multiple trampoline codes in both original and bootstrap sections. Our goal is to list APIs and track how the Instruction Pointer branches from the OEP, requiring accurate execution and detailed analysis of each trampoline code.
2.1.3. Strategy
- Anti-analysis: Packers use evasion techniques like debugger and virtual machine detection, complicating the analysis of packed malware. Our approach started with an in-depth study of well-known anti-analysis methods, summarized in Table 2. We aimed to adapt the execution context to evade detection by monitoring specific instructions and API calls.
- Study of Anti-analysis Methods: We systematically reviewed various anti-analysis techniques used by popular packers. This included methods like API hooking and environmental checks.
- Execution Context Adaptation: By tracking specific instructions and API calls, we developed strategies to adapt the execution environment dynamically, ensuring our analysis bypasses detection mechanisms.
- OEP obfuscation: Packers disguise the OEP using complex bootstrap code patterns, posing unique challenges during unpacking. To address this, we studied commercial protectors to understand their methods, focusing on trampoline code that could lead to errors during unpacking. Our deobfuscation system is based on these findings, employing OEP detection algorithms, analyzing trampoline calls, and tracing the flow back to the original code.
- Commercial Protector Analysis: We examined the techniques used by commercial protectors to obfuscate the OEP, with particular focus on their bootstrap code and trampoline patterns.
- Deobfuscation Algorithm Development: Based on our analysis, we detected the OEP, identified trampoline calls, and traced them back to the original code flow.
- API obfuscation: Packers frequently eliminate the import table from the original program, which makes the analysis of APIs more challenging. Our approach involves identifying the IAT through trampoline codes and rebuilding it. Modern packers, such as Themida and Obsidium, obfuscated APIs using trampoline code addresses in the IAT. Our method examines blocks containing trampoline codes and employs a basic block-level emulation approach to unveil obfuscated APIs.
- IAT Reconstruction: We designed a method to reconstruct the IAT by analyzing and deobfuscating trampoline codes.
- Basic Block Emulation: Utilizing basic block-level emulation, our approach reveals obfuscated API calls, enabling accurate identification of the APIs used by the program through the reconstruction of the IAT.
| Packer | Version | Anti-Debug | Anti-VM |
|---|---|---|---|
| Themida | 3.0.7 | PEB (NtGlobalFlag), NtQueryInformationProcess, NtUserGetForegroundWindows | Registry Key and Value Checks, GeySystemFirmwareTable |
| VMProtect | 3.0.9, 3.4.0 | PEB (BeingDebugged), NtQueryInformationProcess, NtClose, Single-Step Exception | CPUID |
| ASProtect | 2.7.8 | PEB (BeingDebugged) | |
| Obsidium | 1.6.7 | PEB (BeingDebugged), NtQueryInformationProcess, NtClose | GeySystemFirmwareTable, IN |
2.2. Proposed Scheme
2.2.1. DBI-Based Obfuscated Program Execution
- Why DBI? Dynamic program analysis tools such as debuggers, emulators, and DBIs vary in their objectives and applications. For Pinicorn, the goal is to execute obfuscated programs until they restore the original program, capturing this state. Despite various studied techniques, the Intel Pin, a DBI framework, is preferred for its resilience against anti-analysis techniques [16]. However, to avoid detection by some obfuscation tools, we developed a PinTool-based bypass module, enabling the analysis of programs by bypassing anti-analysis techniques.
- Roles of DBI. Intel Pin dynamically instruments binary code using JIT (Just-In-Time) compilation [26]. Its plugin, PinTool, facilitates specific program analyses, allowing us to inject code for targeted analysis. The primary role here is to execute the obfuscated program while avoiding anti-analysis and to capture a memory snapshot when the OEP is reached. This memory dump includes sections with trampoline code addresses and setup data for emulator-based analysis in subsequent stages.
2.2.2. Emulator-Based Trampoline Code Execution
- Pre-Process. The DBI module captures process memory, including the original code and data (e.g., import table). The trampoline code’s location depends on the specific OEP and API obfuscation techniques employed. For instance, in Themida’s OEP obfuscation, the trampoline code is located at the OEP, as depicted in Figure 3. Similarly, for API obfuscation, Themida stores trampoline code addresses in the IAT, while VMProtect and ASProtect patch the API call to directly invoke the trampoline code, as shown in Figure 4. Pinicorn identifies these trampoline code locations to ensure they can be executed during emulation.
- Why Emulator? The secondary aim of Pinicorn is to execute detected trampoline codes to decode obfuscated details. The emulator, using the memory dump as a reference, replicates the environment from the first module, allowing targeted execution of trampoline codes to decode obfuscated information.
- Roles of Emulator. Unicorn [27], a CPU emulator built upon QEMU, facilitates direct binary code execution, making it ideal for reverse engineering tasks. Using Unicorn, Pinicorn focuses on specific program segments, detecting trampoline code locations and executing them via the emulator to pinpoint obfuscated data. This data is then used to reconstruct the deobfuscated binary.
3. Evaluation
3.1. Dataset
3.1.1. Experiment Setup
3.1.2. Comparison Models
3.2. Comparison of Deobfuscation Results
3.2.1. Evaluation of PinDemonium
3.2.2. Evaluation of Unipacker
3.2.3. Evaluation of Pinicorn
3.3. Malware Case Study
3.3.1. Themida Malware Case Study
3.3.2. VMProtect Malware Case Study
3.4. Performance Evaluation
4. Discussion
4.1. Role of DBI and Emulators in Malware Analysis
4.2. Overcoming Limitations of Existing Systems
- Detection Evasion: Advanced malware employs anti-analysis techniques to detect and evade previous analysis environments, rendering many tools ineffective.
- Dynamic Analysis Limitations: Dynamic analysis tools cannot execute or monitor all behaviors of a binary code. This limitation can prevent the analysis of certain obfuscated code, making them impractical for unpacking some malware. Specifically, dynamic analysis may miss code paths that are rarely executed or require specific triggers to activate. By not capturing all possible execution paths, these tools might fail to fully unpack or understand the malware’s functionality, reducing their effectiveness in thorough malware analysis.
4.3. Integration with Existing Systems
4.4. Potential Attacks and Measures
4.4.1. DBI Detection Attacks
4.4.2. Anti-Debugging Attacks in Trampoline Code
4.5. Limitation
4.5.1. Context Dump Problem
- We utilized PinDemonium’s OEP detection to recognize when the program’s original state is restored. Pinicorn identifies trampoline code from several OEP candidates. Analyzing multiple candidates and performing memory dumps for each significantly impacts performance.
- Operating in a virtual machine with a 30-min runtime limit, Pinicorn faced resource allocation challenges for malware dumping across 15 virtual machines. This occasionally resulted in restoring virtual machine snapshots before executing the packed malware’s original code.
- In experiments with malware, issues may arise from anti-analysis techniques in unknown versions of known packers, which cannot be completely bypassed. To improve this, there is a need to analyze as many versions of packers as possible and implement additional bypass modules.
4.5.2. Stolen Function
4.5.3. Unknown Argument-Sensitive Trampoline Code for API Obfuscation
4.5.4. Problems of Deobfuscation Approaches
4.5.5. Deobfuscation Challenges with Obfuscated Malware by ASProtect
4.5.6. Obsidium Malware Sample Were Not Found
4.5.7. Application to Other Operating Systems
4.6. Out-of-Scope
4.6.1. Limited Scope of Examined Commercial Protectors
4.6.2. Macro-Based Source Code Obfuscation
5. Conclusions
Limitations and Future Works
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- AV-TEST—The Independent IT-Security Institute. Malware Statistics and Trends Report. 2024. Available online: https://www.av-test.org/en/statistics/malware (accessed on 1 April 2023).
- FireEye. M-Trends 2020 Report. 2021. Available online: https://www.mandiant.com/sites/default/files/2021-09/mtrends-2020.pdf (accessed on 1 April 2023).
- FireEye. M-Trends 2021 Report. 2022. Available online: https://services.google.com/fh/files/misc/rpt-mtrends-2021-en.pdf (accessed on 1 April 2023).
- FireEye. M-Trends 2022 Report. 2023. Available online: https://services.google.com/fh/files/misc/m-trends-report-2022-en.pdf (accessed on 1 April 2023).
- Suk, J.; Lee, J.; Jin, H.; Kim, I.; Lee, D. UnThemida: Commercial obfuscation technique analysis with a fully obfuscated program. Softw. Pract. Exp. 2018, 48, 2331–2349. [Google Scholar] [CrossRef]
- Cheng, B.; Li, P. BareUnpack: Generic Unpacking on the Bare-Metal Operating System. IEICE Trans. Inf. Syst. 2018, 101, 3083–3091. [Google Scholar] [CrossRef]
- Choi, S.; Chang, T.; Kim, C.; Park, Y. X64Unpack: Hybrid emulation unpacker for 64-bit windows environments and detailed analysis results on VMProtect 3.4. IEEE Access 2020, 8, 127939–127953. [Google Scholar] [CrossRef]
- Cheng, B.; Ming, J.; Leal, E.; Zhang, H.; Fu, J.; Peng, G.; Marion, J. Obfuscation-Resilient Executable Payload Extraction From Packed Malware. In Proceedings of the 30th USENIX Security Symposium (USENIX Security 21), Virtual event, 11–13 August 2021; pp. 3451–3468. [Google Scholar]
- VMProtect Software. VMProtect Software Protection. 2003–2023. Available online: https://vmpsoft.com/ (accessed on 1 April 2023).
- Oreans Technologies. Themida Overview—Oreans Technologies. 2004–2023. Available online: https://www.oreans.com/Themida.php (accessed on 1 April 2023).
- Obsidium Software. Obsidium Software Protection System. 2023. Available online: https://www.obsidium.de/ (accessed on 1 April 2023).
- StartForge. ASProtect. 2007–2023. Available online: http://www.aspack.com/asprotect32.html/ (accessed on 1 April 2023).
- Roundy, K.A.; Miller, B.P. Binary-code obfuscations in prevalent packer tools. ACM Comput. Surv. (CSUR) 2013, 46, 1–32. [Google Scholar] [CrossRef]
- Korczynski, D. Repeconstruct: Reconstructing binaries with self-modifying code and import address table destruction. In Proceedings of the 2016 11th International Conference on Malicious and Unwanted Software (MALWARE), Fajardo, PR, USA, 18–21 October 2016; pp. 1–8. [Google Scholar]
- Microsoft. PE Format—Win32 Apps. 2023. Available online: https://learn.microsoft.com/en-us/windows/win32/debug/pe-format/ (accessed on 1 April 2023).
- Park, J.; Jang, Y.H.; Hong, S.; Park, Y. Automatic detection and bypassing of anti-debugging techniques for microsoft windows environments. Adv. Electr. Comput. Eng. 2019, 19, 23–29. [Google Scholar] [CrossRef]
- Lee, Y.; Suk, J.; Lee, D. Bypassing Anti-Analysis of Commercial Protector Methods Using DBI Tools. IEEE Access 2021, 9, 7655–7673. [Google Scholar] [CrossRef]
- D’Alessio, S.; Mariani, S. PinDemonium: A DBI-Based Generic Unpacker for Windows Executables; Black Hat: Las Vegas, NV, USA, 2016. [Google Scholar]
- Kim, G.M.; Park, Y.S. Improved Original Entry Point Detection Method Based on PinDemonium. KIPS Trans. Comput. Commun. Syst. 2018, 7, 155–164. [Google Scholar]
- Isawa, R.; Inoue, D.; Nakao, K. An original entry point detection method with candidate-sorting for more effective generic unpacking. IEICE Trans. Inf. Syst. 2015, 98, 883–893. [Google Scholar] [CrossRef]
- Kang, M.; Poosankam, P.; Yin, H. Renovo: A hidden code extractor for packed executables. In Proceedings of the 2007 ACM Workshop on Recurring Malcode, Alexandria, VA, USA, 2 November 2007; pp. 46–53. [Google Scholar]
- Yadegari, B.; Johannesmeyer, B.; Whitely, B.; Debray, S. A generic approach to automatic deobfuscation of executable code. In Proceedings of the 2015 IEEE Symposium on Security and Privacy, San Jose, CA, USA, 17–21 May 2015; pp. 674–691. [Google Scholar]
- Ugarte-Pedrero, X.; Balzarotti, D.; Santos, I.; Bringas, P.G. SoK: Deep packer inspection: A longitudinal study of the complexity of run-time packers. In Proceedings of the 2015 IEEE Symposium on Security and Privacy, San Jose, CA, USA, 17–21 May 2015; pp. 659–673. [Google Scholar]
- Cheng, B.; Ming, J.; Fu, J.; Peng, G.; Chen, T.; Zhang, X.; Marion, J. Towards paving the way for large-scale windows malware analysis: Generic binary unpacking with orders-of-magnitude performance boost. In Proceedings of the 2018 ACM SIGSAC Conference on Computer and Communications Security, Toronto, ON, Canada, 15–19 October 2018; pp. 395–411. [Google Scholar]
- Cheng, B.; Leal, E.A.; Zhang, H.; Ming, J. On the feasibility of malware unpacking via hardware-assisted loop profiling. In Proceedings of the 32nd USENIX Security Symposium (USENIX Security 23), Anaheim, CA, USA, 9–11 August 2023; pp. 7481–7498. [Google Scholar]
- Levi, O.; Pin—A Dynamic Binary Instrumentation Tool. 2007–2023. Available online: https://www.intel.com/content/www/us/en/developer/articles/tool/pin-a-dynamic-binary-instrumentation-tool.html (accessed on 1 April 2023).
- Quynh, N.; Vu, D. Unicorn—The Ultimate CPU Emulator. 2015–2023. Available online: https://www.unicorn-engine.org/ (accessed on 1 April 2023).
- National Institute of Standards and Technology. Juliet Test Suites. 2006–2023. Available online: https://samate.nist.gov/SARD/test-suites/ (accessed on 1 April 2023).
- VirusShare. 2012–2022. Available online: https://virusshare.com/ (accessed on 1 April 2023).
- PyPackerDetect. 2018–2023. Available online: https://github.com/cylance/PyPackerDetect (accessed on 1 April 2023).
- Scylla—x64/x86 Imports Reconstruction. 2011–2015. Available online: https://github.com/NtQuery/Scylla (accessed on 1 April 2023).
- Unipacker. 2019–2023. Available online: https://github.com/unipacker/unipacker (accessed on 1 April 2023).
- The UPX Team. UPX—The Ultimate Packer for eXecutables. 1996–2023. Available online: https://upx.github.io/ (accessed on 1 April 2023).
- StarForge. ASPACK Software. 2007–2023. Available online: http://www.aspack.com/aspack.html (accessed on 1 April 2023).






| Related Work | Research Design | Methodology | Contribution | Result |
|---|---|---|---|---|
| [21] | Comparative analysis | Uses emulation to extract hidden code. | Accurate hidden code extraction solution. | Successfully extracted original binaries from most executables. |
| [13] | Analytical study | Uses manual and automated analysis with Dyninst. | Detailed taxonomy of obfuscation techniques. | Enhanced analysis of obfuscated binaries. |
| [22] | Theoretical study | Uses taint propagation and code transformations. | Generalized deobfuscation technique. | Reconstructed logic of obfuscated programs. |
| [23] | Longitudinal study | Develops a framework and taxonomy for packer complexity. | Insights into evolution and sophistication of packers. | Revealed trends and increased complexity in packing. |
| [14] | Tool development | Uses DynamoRIO for static and dynamic analysis. | Accurate reconstruction of unpacked binaries. | Effective against self-modifying code and IAT destruction. |
| [5] | Empirical study | Uses static and dynamic analysis with Intel PIN. | First to deobfuscate Themida 2.4.5.0 version. | Reduced analysis time and enhanced deobfuscation techniques. |
| [24] | Experimental study | BinUnpack uses kernel-level DLL hijacking. | High-performance solution for multi-layered malware. | Completed unpacking within 0.5 s. |
| [6] | Comparative study | Utilizes packed IAT hooking on bare-metal OS. | Effective unpacking without simulated environments. | Outperformed existing approaches for environment-sensitive packers. |
| [16] | Evaluative study | Uses Pin tool to detect and bypass anti-debugging techniques. | Automatic detection and bypassing scheme. | 100% success rate in tested protectors. |
| [7] | Hybrid analysis | Combines instruction emulation and direct execution. | Specialized tool for anti-reverse engineering techniques. | Unpacked all tested binaries and provided detailed logs. |
| [17] | Experimental study | Uses DBI tools to bypass anti-analysis techniques. | Demonstrates DBI tools’ effectiveness. | Bypassed anti-analysis in various commercial protectors. |
| [8] | Experimental study | API-Xray uses hardware-assisted tracing and dynamic/static analysis. | Robust method for import table reconstruction. | Rebuilt import tables for 174,285 samples. |
| [25] | Experimental study | Uses HPCs and loop profiling with machine learning. | Novel hardware-assisted malware unpacking. | Successfully unpacked malware with selected hardware events. |
| Packer | 2021 1 | 2022 |
|---|---|---|
| Themida | 39 | 4376 |
| VMProtect | 432 | 8667 |
| ASProtect | 166 | 3328 |
| Obsidium 2 | 0 | 0 |
| Packer | 2021 1 | 2022 |
|---|---|---|
| Themida | 29 | 767 |
| VMProtect | 59 | 1386 |
| ASProtect 2 | 0 | 0 |
| Obsidium 2 | 0 | 0 |
| Packers | API Obfuscation | OEP Obfuscation | ||||
|---|---|---|---|---|---|---|
| PinDemonium | Unipacker | Pinicorn | PinDemonium | Unipacker | Pinicorn | |
| Themida | 0/100 | 0/100 | 100/100 | 0/100 | 0/100 | 100/100 |
| VMProtect | 0/100 | 0/100 | 100/100 | 0/100 | 0/100 | 100/100 |
| ASProtect | N/A 1 | 0/100 | 100/100 | N/A1 | 0/100 | N/A 2 |
| Packers | API Obfuscation | OEP Obfuscation |
|---|---|---|
| Themida | 9/43 | 37/43 |
| VMProtect | 10/27 | 11/27 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Lee, G.; Kim, M.; Yi, J.H.; Cho, H. Pinicorn: Towards Automated Dynamic Analysis for Unpacking 32-Bit PE Malware. Electronics 2024, 13, 2081. https://doi.org/10.3390/electronics13112081
Lee G, Kim M, Yi JH, Cho H. Pinicorn: Towards Automated Dynamic Analysis for Unpacking 32-Bit PE Malware. Electronics. 2024; 13(11):2081. https://doi.org/10.3390/electronics13112081
Chicago/Turabian StyleLee, Gwangyeol, Minho Kim, Jeong Hyun Yi, and Haehyun Cho. 2024. "Pinicorn: Towards Automated Dynamic Analysis for Unpacking 32-Bit PE Malware" Electronics 13, no. 11: 2081. https://doi.org/10.3390/electronics13112081
APA StyleLee, G., Kim, M., Yi, J. H., & Cho, H. (2024). Pinicorn: Towards Automated Dynamic Analysis for Unpacking 32-Bit PE Malware. Electronics, 13(11), 2081. https://doi.org/10.3390/electronics13112081






