Design of a Cyberattack Resilient 77 GHz Automotive Radar Sensor
Abstract
1. Introduction
- (A)
- False cyberattack alarm rate, , must be low
- (B)
- Cyberattack miss rate, , must be low
- (C)
- The radar DSP output must be robust against undetected cyberattacks
2. Review of FMCW AV Radars
Review of the Texas Instruments 77GHz Automotive Radar
3. Cyberattack Detection System
Mathematical Notation
- In every measurement cycle, a random signature is selected randomly.
- Throughout the measurement cycle, there will be total M chirps with index .
- If , the ramp generator outputs a positive slope ramp resulting in an up-chirp. Otherwise, the ramp generator outputs a negative slope ramp resulting in a down-chirp.
| Algorithm 1: Detector (a.k.a. Detection DSP) |
 |
| Algorithm 2: AV Sensor (a.k.a. Radar DSP) |
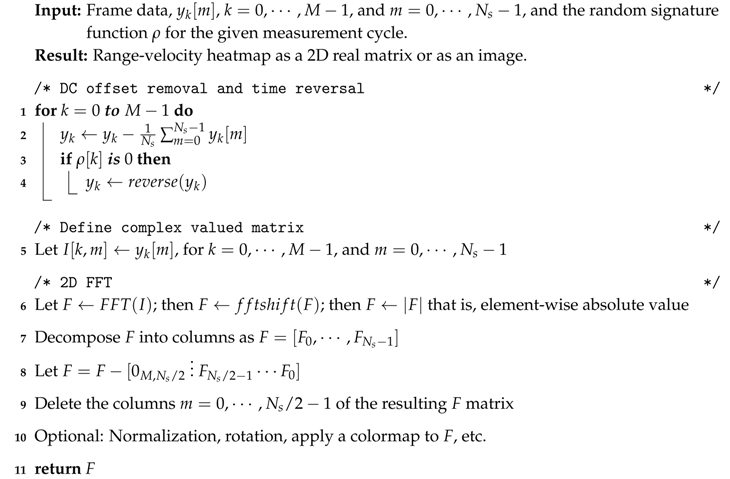 |
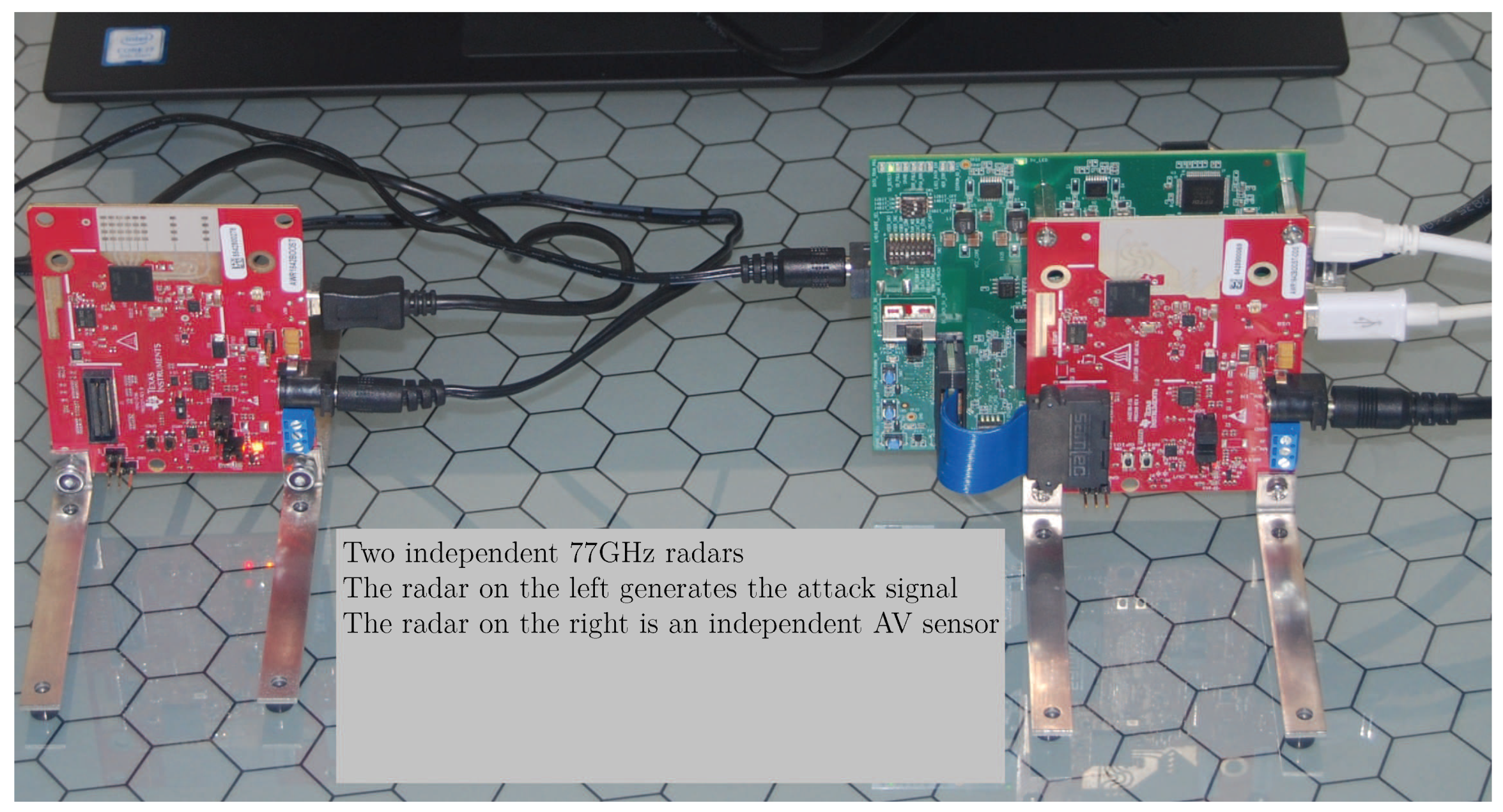
4. Experimental Setup and Measurements
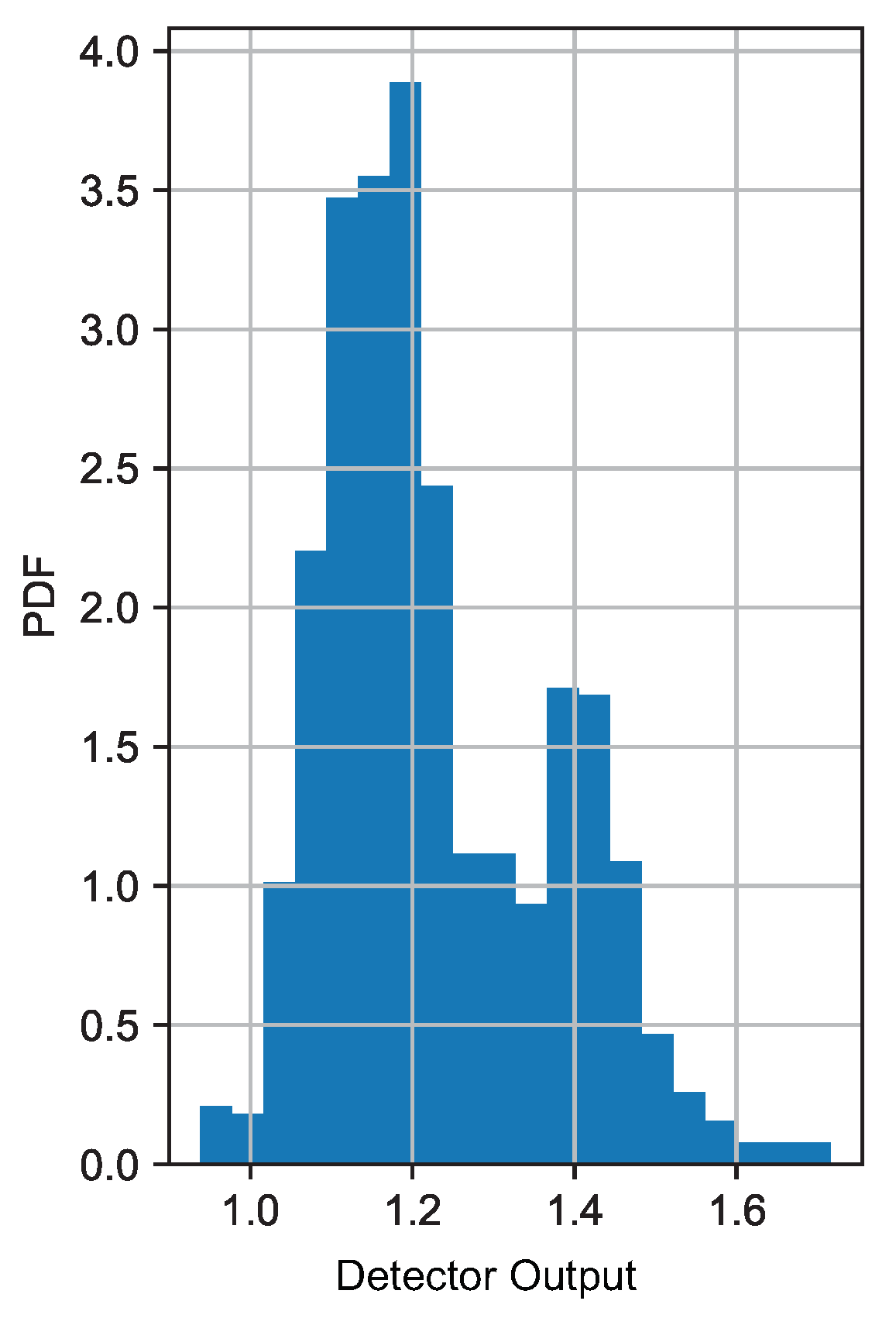
5. Analysis of System Noise
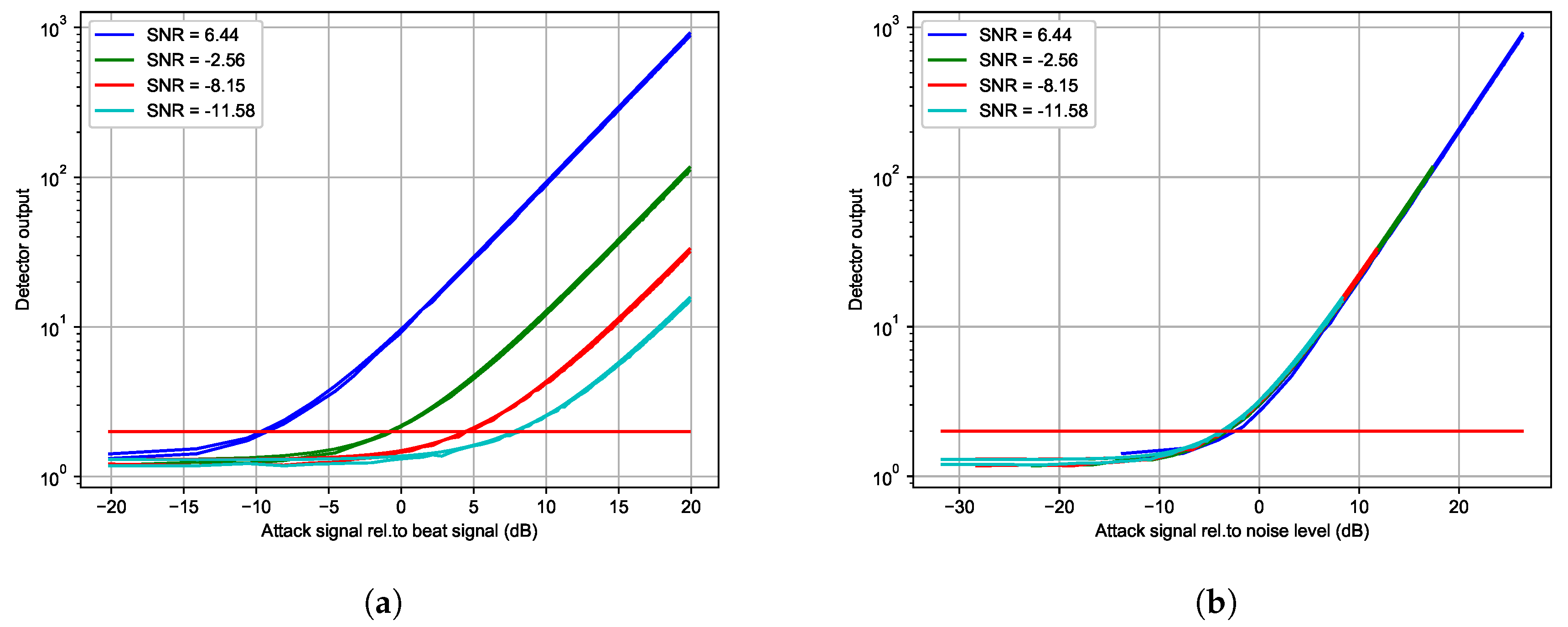
6. Analysis of the cyberattack Detection DSP
- (1)
- For a recorded system noise, , all transmitters are off (a.k.a. Type I measurement), so that we capture only the system noise,
- (2)
- For a recorded radar data, , the Attack Radar TX is off (a.k.a. Type II measurement), so we capture only the signal reflected from a target (A car or a pedestrian),
- (3)
- For a recorded attack signal, , Attack Radar TX is on, but AV Radar TX is off (a.k.a. Type III measurement). In this case, we capture only the effect of the attack signal.
6.1. Analysis of False Alarms
6.2. eWGN Cyberattack Test Case
6.3. eTX2 Cyberattack Test Case
6.4. eTX2R Cyberattack Test Case
6.5. eTX1 Cyberattack Test Case
6.6. eTX1R Cyberattack Test Case
6.7. Detector Performance When There Is No Target
7. Radar Performance under Cyberattacks: Analysis of Radar DSP
8. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Kala, R. On-Road Intelligent Vehicles, Motion Planning for Intelligent Transportation Systems; Butterworth-Heinemann: Oxford, UK, 2016. [Google Scholar] [CrossRef]
- Jimenez, F. Intelligent Vehicles, Enabling Technologies and Future Developments; Butterworth-Heinemann: Oxford, UK, 2018. [Google Scholar] [CrossRef]
- Patole, S.M.; Torlak, M.; Wang, D.; Ali, M. Automotive radars: A review of signal processing techniques. IEEE Signal Proc. Mag. 2017, 34, 22–35. [Google Scholar] [CrossRef]
- Ramasubramanian, K.; Ramaiah, K.; Aginskiy, A. Moving from legacy 24 GHz to state-of-the-art 77 GHz radar. ATZelektronik Worldw. 2018, 13. Available online: http://www.ti.com/lit/wp/spry312/spry312.pdf (accessed on 22 March 2020). [CrossRef]
- Bhat, C. Cybersecurity Challenges and Pathways in the Context of Connected Vehicle Systems; Technical Report 134; Data-Supported Transportation Operations & Planning Center (D-STOP): Austin, TX, USA, 2018; Available online: https://ctr.utexas.edu/wp-content/uploads/134.pdf (accessed on 22 March 2020).
- Alland, S.; Stark, W.; Ali, M.; Hegde, M. Interference in Automotive Radar Systems: Characteristics, Mitigation Techniques, and Current and Future Research. IEEE Signal Proc. Mag. 2019, 36, 45–59. [Google Scholar] [CrossRef]
- Ye, N.; Farley, T. A scientific approach to cyberattack detection. Computer 2005, 38, 55–61. [Google Scholar] [CrossRef]
- Pham, V.; Nguyen, N.; Li, J.; Hass, J.; Chen, Y.; Dang, T. MTSAD: Multivariate Time Series Abnormality Detection and Visualization. In Proceedings of the 2019 IEEE International Conference on Big Data (Big Data), Los Angeles, CA, USA, 9–12 December 2019. [Google Scholar] [CrossRef]
- Xu, L.; Liu, H.; Zhou, S.; Liu, J.; Yan, J. Colocated MIMO Radar Waveform Design Against Repeat Radar Jammers. In Proceedings of the 2018 International Conference on Radar (RADAR), Brisbane, Australia, 27–31 August 2018. [Google Scholar] [CrossRef]
- Chen, H.; Himed, B. Analyzing and improving MIMO radar detection performance in the presence of cybersecurity attacks. In Proceedings of the 2016 IEEE Radar Conference (RadarConf), Pacific Grove, CA, USA, 6–9 November 2016. [Google Scholar] [CrossRef]
- Yang, C.; Feng, L.; Zhang, H.; He, S.; Shi, Z. A Novel Data Fusion Algorithm to Combat False Data Injection Attacks in Networked Radar Systems. IEEE Trans. Signal Inf. Process. Over Netw. 2018, 4, 125–136. [Google Scholar] [CrossRef]
- Kordestani, M.; Chibakhsh, A.; Saif, M. A Control Oriented Cyber-Secure Strategy Based on Multiple Sensor Fusion. In Proceedings of the 2019 IEEE International Conference on Systems, Man and Cybernetics (SMC), Bari, Italy, 6–9 October 2019. [Google Scholar] [CrossRef]
- Ye, N.; Farley, T. Resilient Tracking Control of Networked Control Systems Under Cyber Attacks. IEEE Trans. Cybern. 2019, 1–13. [Google Scholar] [CrossRef]
- Mo, Y.; Sinopoli, B. False Data Injection Attacks in Control Systems. First Workshop on Secure Control Systems, CPS Week. 2010. Available online: https://www.researchgate.net/publication/228859026_False_data_injection_attacks_in_control_systems (accessed on 22 March 2020).
- Shoukry, Y.; Martin, P.; Yona, Y.; Diggavi, S.; Srivastava, M. Attack Resilience and Recovery using Physical Challenge Response Authentication for Active Sensors Under Integrity Attacks. arXiv 2016, arXiv:1605.02062v2. Available online: https://arxiv.org/pdf/1605.02062 (accessed on 22 March 2020).
- Dutta, R.G.; Guo, X.; Zhang, T.; Kwiat, K.; Kamhoua, C.; Njilla, L.; Jin, Y. Estimation of safe sensor measurements of autonomous system under attack. In Proceedings of the 54th ACM/EDAC/IEEE Design Automation Conference, Austin, TX, USA, 19–23 June 2017. [Google Scholar] [CrossRef]
- Kapoor, P.; Vora, A.; Kang, K.D. Detecting and Mitigating Spoofing Attack against an Automotive Radar. In Proceedings of the 2018 IEEE Vehicular Technology Conference, Chicago, IL, USA, 27–30 August 2018. [Google Scholar] [CrossRef]
- Toker, O.; Alsweiss, S.; Vargas, J.; Razdan, R. Design of an Automotive Radar Sensor Firmware Resilient to Cyberattacks. In Proceedings of the 2020 IEEE SoutheastCon, Raleigh, NC, USA, 11–15 March 2020. [Google Scholar]
- Toker, O.; Alsweiss, S.; Abid, M. A Computer Vision Based Testbed for 77 GHz mmWave Radar Sensors. In Proceedings of the 2020 IEEE SoutheastCon, Raleigh, NC, USA, 11–15 March 2020. [Google Scholar]
- Toker, O.; Alsweiss, S. mmWave Radar Based Approach for Pedestrian Identification in Autonomous Vehicles. In Proceedings of the 2020 IEEE SoutheastCon, Raleigh, NC, USA, 11–15 March 2020. [Google Scholar]
- Toker, O.; Kuhn, B. A Python Based Testbed for Real-Time Testing and Visualization using TI’s 77 GHz Automotive Radars. In Proceedings of the 2019 IEEE Vehicular Networking Conference, Los Angeles, CA, USA, 4–6 December 2019. [Google Scholar]
- Brinkmann, M. Design and Implementation of Improved Nonlinearity Correction Algorithms for FMCW Radar Sensors. Master’s Thesis, Florida Polytechnic University, Lakeland, FL, USA, 2019. [Google Scholar]
- Toker, O.; Brinkmann, M. A Novel Nonlinearity Correction Algorithm for FMCW Radar Systems for Optimal Range Accuracy and Improved Multitarget Detection Capability. Electronics 2019, 11, 1290. [Google Scholar] [CrossRef]
- Iovescu, C.; Rao, S. The Fundamentals of Millimeter Wave Sensors. Texas Instruments Technical Document. 2017. Available online: http://www.ti.com/lit/wp/spyy005/spyy005.pdf (accessed on 22 March 2020).
- Rao, S. Introduction to mmWave Sensing: FMCW Radars. Texas Instruments Training Document. 2017. Available online: https://training.ti.com/node/1139153 (accessed on 22 March 2020).
- Ash, M.; Ritchie, M.; Chetty, K. On the Application of Digital Moving Target Indication Techniques to Short-Range FMCW Radar Data. IEEE Sens. J. 2018, 18, 4167–4175. [Google Scholar] [CrossRef]
- Park, J.; Hong, Y.; Lee, H.; Jang, C.; Yun, G.; Lee, H.; Yook, J. Noncontact RF Vital Sign Sensor for Continuous Monitoring of Driver Status. IEEE Trans. Boimed. Circuits Syst. 2019, 13, 493–502. [Google Scholar] [CrossRef]
- Aalizadeh, M.; Shaker, G.; Almeida, J.C.M.; Morita, P.P.; Safavi-Naeini, S. Remote Monitoring of Human Vital Signs Using mm-Wave FMCW Radar. IEEE Access 2019, 7, 54958–54968. [Google Scholar] [CrossRef]
- Toker, O. REAL-time 2D Radar Heatmap Demo Using the TI 77 GHz Radar. YouTube Video. Available online: https://www.youtube.com/watch?v=jNuBgl6KMCs (accessed on 22 March 2020).

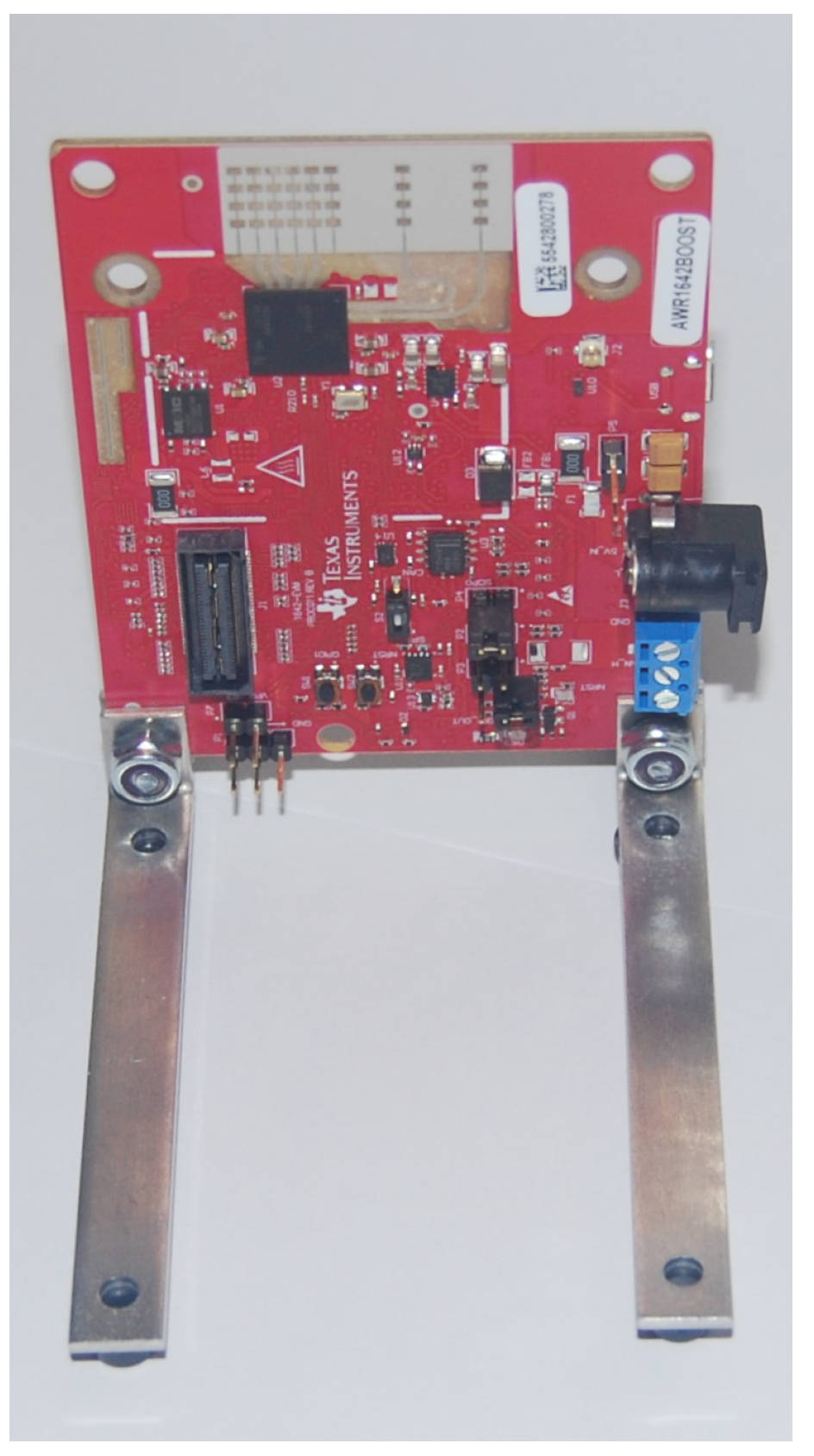













| Model Number | Details |
|---|---|
| AWR1642BOOST | 76-GHz to 81-GHz automotive radar |
| (Texas Instruments AWR1642 chip based) | |
| AWR1642BOOST-ODS | 76-GHz to 81-GHz automotive radar |
| (Texas Instruments AWR1642 chip based, wide field of view antenna) | |
| DCA1000 EVM | FPGA board for real-time data-capture |
| (Lattice LFE5UM-85F-8BG381I chip based) | |
| HostPC | Laptop, 16GB RAM, i7-8750H CPU @ 2.20 GHz, 64-bit Windows 10, |
| NVIDIA GeForce GTX 1050 Ti graphics accelerator | |
| Other | Two 5 V power supplies, two USB 2.0 cables (for configuration), |
| and a Gigabit Ethernet cable (for high speed data) |
| Name | Details |
|---|---|
| TI mmWave Studio | Version 2.1.0.0 |
| TI mmWave Visualizer | Version 3.3.0 |
| Type | Details |
|---|---|
| Type I: Noise only | Attack Radar TX = Off; AV Radar TX = Off, RX = On |
| Type II: Normal mode | Attack Radar TX = Off; AV Radar TX = On, RX = On |
| Type III: Attack mode | Attack Radar TX = On; AV Radar TX = Off, RX = On |
| Attack Scenario | Details |
|---|---|
| eWGN | Attack signal is white noise |
| eTX2 | Attack signal is the signal generated |
| by the second radar unit | |
| eTX2R | Attack signal is the signal generated |
| by the second radar unit with random | |
| frequency slope selection | |
| eTX1 | Attacker has full VCO sync information |
| eTX1R | Attacker has full VCO sync information, |
| and selects the frequency slope randomly |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Toker, O.; Alsweiss, S. Design of a Cyberattack Resilient 77 GHz Automotive Radar Sensor. Electronics 2020, 9, 573. https://doi.org/10.3390/electronics9040573
Toker O, Alsweiss S. Design of a Cyberattack Resilient 77 GHz Automotive Radar Sensor. Electronics. 2020; 9(4):573. https://doi.org/10.3390/electronics9040573
Chicago/Turabian StyleToker, Onur, and Suleiman Alsweiss. 2020. "Design of a Cyberattack Resilient 77 GHz Automotive Radar Sensor" Electronics 9, no. 4: 573. https://doi.org/10.3390/electronics9040573
APA StyleToker, O., & Alsweiss, S. (2020). Design of a Cyberattack Resilient 77 GHz Automotive Radar Sensor. Electronics, 9(4), 573. https://doi.org/10.3390/electronics9040573





