An Examination of Multi-Key Fully Homomorphic Encryption and Its Applications
Abstract
1. Introduction
Multi-Key Fully Homomorphic Encryption
2. MKFHE Scheme Classification
2.1. MKFHE Classified by Improvement Steps
2.2. Security Assumptions
2.3. Key Generation
2.4. MKFHE for Multi-Bit Encryption
2.5. MKFHE with Cipher Processing Optimization
3. Optimization Techniques for MKFHE
3.1. LinkAlgo Algorithm for the KLP18 Scheme
3.1.1. Notion of LinkAlgo
3.1.2. LinkAlgo Algorithm
| Algorithm 1 LinkAlgo algorithms. |
|
- 1.
- 2.
- Compute [t]. The extended ciphertext is:
3.2. SWC21 Ciphertext Compression Algorithm
Notion of SWC21
- has small entries ()
- = 0(mod q), i.e., all row vectors of can generate a kernel space of mod q;
- is full-rank over .
- Let k be the security parameter for a large module q with an error distribution = (k,N) bounded by . Additionally, taken for the step.Let , and (where and , , , , and ), choose .Output params = .
- (params): Choose and . Let , and , noticed that . Output , .
- (, ): Input a plaintext bit , choose , let ciphertext be . will be divided as follows for the step:Let .Notice that .Attached information is needed to successfully execute the Exp step.where , . The complete ciphertext tuple is
- : extended ciphertext is:Fresh ciphertext does not support compression. Therefore, the ciphertext of different users needs to be pre-processed before compression, which is similar to the traditional GSW-expand step.(1) Generate components required for extended ciphertext:where and only the intersection of column b and row is 1; all others are 0.Let(2) Generate auxiliary ciphertext :
- (params,): Compress one or some ciphertext into ciphertext of a smaller size. Let , where and only the intersection of the u-th row and v-th column are 1; all others are 0. Let compressed ciphertext be:The compressing algorithm is the same as Gentry’s GH19 scheme; all the cipher processing is to meet the requiements of this algorithm.
- (params, f, , , ⋯, ): Input N and circuit and a string of ciphertext , , ⋯, ; output the ciphertext after homomorphism.Eval.addEval.mult
- (, ): Input the private key of N participants; let be the extended private key. Decrypting a compressed cipher involves the following four steps:
- ;
- , is the open trapdoor matrix;
- ( is full-rank and ).
4. Application of MKFHE
4.1. Medical Applications
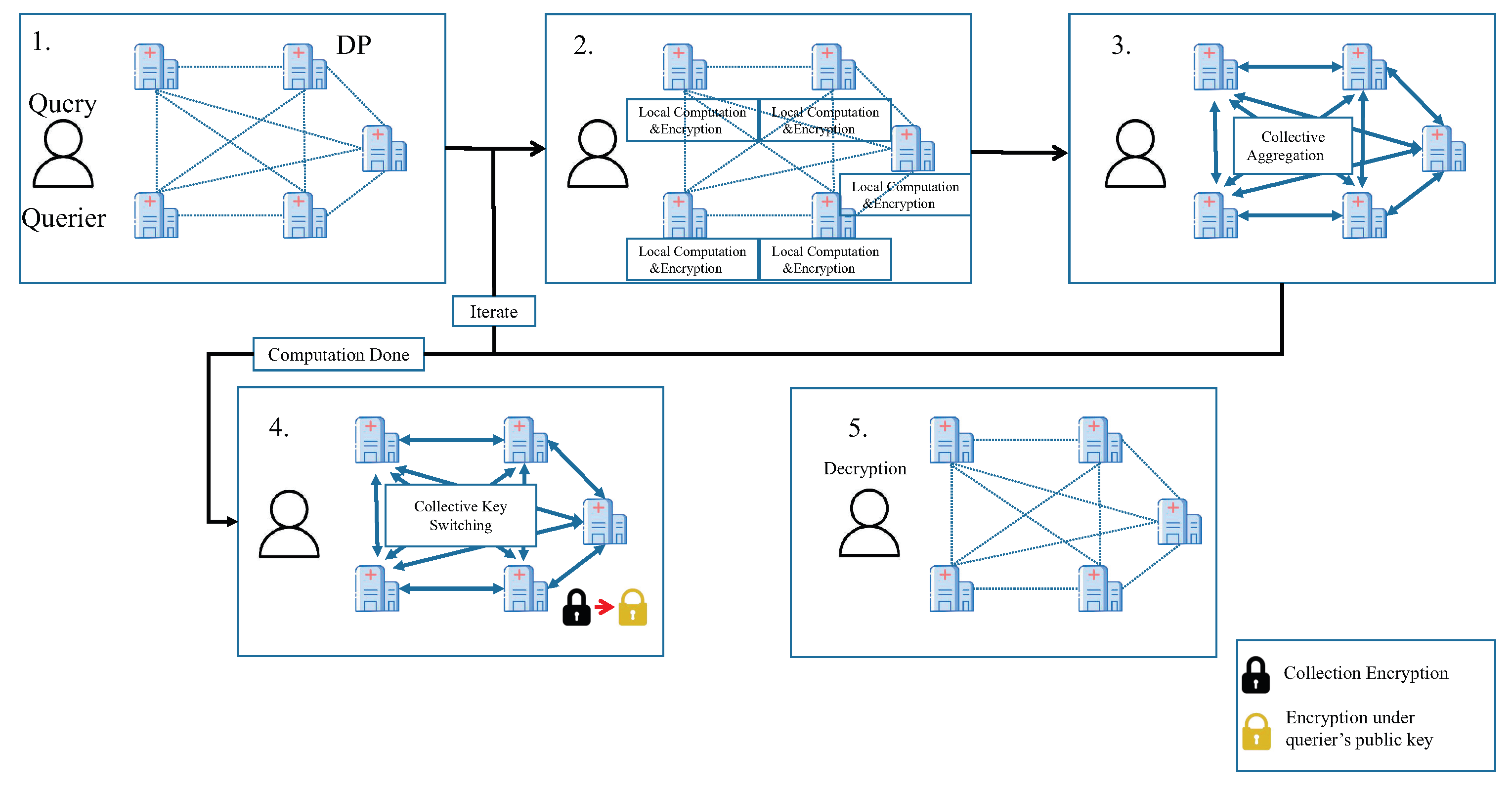
Model of MKFHE’s Application to Medical Data
- After each medical institution receives the request, locally compute the result of query; then encrypt the result and broadcast.
- Each medical institution aggregates encrypted results locally. For iterative tasks, each medical institution repeats the process until the requirements are met.
- The public key of the final result switched from collective public key to the public key of querier through collective key switching.
- The querier decrypts the final result.
4.2. Financial Scenarios
Model of MKFHE’s Application to Financial Data
- Each bank in the group trains the model on the local data and encrypts the obtained gradient using the public key of MKFHE. After signing the encrypted gradient, it is sent to other users.
- After receiving the information, each user verifies the validity of the information via digital signature. If valid, then the local model is obtained by training together with the local gradient.
- The local model is sent to the AS (aggregation server), and the corresponding block is generated in the blockchain for record keeping. The AS aggregates all the models and broadcasts them to the users within the group.
- Each user updates the local model with the global model. We repeat steps three and four until the accuracy condition is met. Then, each user performs partial decryption of MKFHE to obtain the plaintext result.
4.3. IoT
Model of MKFHE’s Application on IoT
- Each device uses the downloaded global model to train the local data to get the local model and uses its own public key to encrypt the local model parameter; then, it sends the encrypted parameter to the aggregation server.
- After receiving the encrypted model parameters of all parties, the aggregation server uses the aggregation algorithm to get the average model. The aggregation server sends the average model parameter to all parties.
- After receiving the average model parameter, all parties use it to update the local model.
4.4. Service Recommendation
4.5. Research Innovation
5. Conclusions
Author Contributions
Funding
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Ren, Y.; Leng, Y.; Qi, J.; Sharma, P.K.; Tolba, A. Multiple cloud storage mechanism based on blockchain in smart homes. Future Gener. Comput. Syst. 2021, 115, 304–313. [Google Scholar] [CrossRef]
- Rivest, R.L.; Adleman, L.M.; Dertouzos, M.L. On data banks and privacy homomorphisms. Found. Secur. Comput. 1978, 4, 169–179. [Google Scholar]
- Gentry, C. Fully homomorphic encryption using ideal lattices. In Proceedings of the forty-first annual ACM symposium on Theory of Computing, Bethesda, MD, USA, 1–2 June 2009; pp. 169–178. [Google Scholar]
- Ren, Y.; Yan, L.; Cheng, Y.; Jin, W. Secure data storage based on blockchain and coding in edge computing. Math. Biosci. Eng. MBE 2019, 16, 1874–1892. [Google Scholar] [CrossRef] [PubMed]
- Tang, D.H.; Zhu, S.X.; Wang, L.; Yang, H.M.; Fan, J. Fully homomorphic encryption scheme from rlwe. J. Commun. 2014, 35, 173–182. [Google Scholar]
- Brakerski, Z.; Vaikuntanathan, V. Efficient fully homomorphic encryption from (standard) lwe. SIAM J. Comput. 2014, 43, 831–871. [Google Scholar] [CrossRef]
- Ren, Y.; Huang, D.; Wang, W.H.; Yu, X.F. BSMD: A blockchain-based secure storage mechanism for big spatio-temporal data. Future Gener. Comput. Syst. 2023, 138, 328–338. [Google Scholar] [CrossRef]
- Lopez-Alt, A.; Tromer, E.; Vaikuntanathan, V. On-the-fly multiparty computation on the cloud via multikey fully homomorphic encryption. In Proceedings of the Forty-Fourth the Annual ACM Symposium on Theory of Computing 2012, New York, NY, USA, 19–22 May 2012. [Google Scholar]
- Che, X.; Zhou, T.; Li, N.; Zhou, H.; Chen, Z. Modified multi-key fully homomorphic encryption based on ntru cryptosystem without key-switching. Tsinghua Sci. Technol. 2020, 25, 14–28. [Google Scholar] [CrossRef]
- Kim, E.; Lee, H.S.; Park, J. Towards round-optimal secure multiparty computations: Multikey fhe without a crs. In Proceedings of the Australasian Conference on Information Security and Privacy, Wollongong, NSW, Australia, 11–13 July 2018; Springer: Cham, Switzerland, 2018; pp. 101–113. [Google Scholar]
- Mukherjee, P.; Wichs, D. Two round multiparty computation via multi-key fhe. In Proceedings of the Annual International Conference on the Theory and Applications of Cryptographic Techniques, Vienna, Austria, 8–12 May 2016; Springer: Berlin/Heidelberg, Germany, 2016; pp. 735–763. [Google Scholar]
- Long, C.; Zhang, Z.; Wang, X. Batched multi-hop multi-key fhe from ring-lwe with compact ciphertext extension. In Proceedings of the Theory of Cryptography Conference, Baltimore, MD, USA, 12–15 November 2017; Springer: Cham, Switzerland, 2017; Volume 10678, pp. 597–627. [Google Scholar]
- Brakerski, Z.; Gentry, C.; Vaikuntanathan, V. (Leveled) fully homomorphic encryption without bootstrapping. ACM Trans. Comput. Theory (TOCT) 2014, 6, 309–325. [Google Scholar] [CrossRef]
- Shen, T.; Wang, F.; Chen, K.; Shen, Z.; Zhang, R. Compressible multikey and multi-identity fully homomorphic encryption. Secur. Commun. Netw. 2021, 2021, 6619476. [Google Scholar] [CrossRef]
- Albrecht, M.; Bai, S.; Ducas, L. A subfield lattice attack on overstretched ntru assumptions. In Proceedings of the Annual International Cryptology Conference, Santa Barbara, CA, USA, 14–18 August 2016; Springer: Berlin/Heidelberg, Germany, 2016; pp. 153–178. [Google Scholar]
- Zhou, H.; Li, N.; Che, X.; Yang, X. Multi-key fully homomorphic encryption scheme over prime cyclotomic rings. IET Inf. Secur. 2021, 15, 472–486. [Google Scholar] [CrossRef]
- Yu, Y.; Xu, G.; Wang, X. Provably Secure NTRU Instances over Prime Cyclotomic Rings. In Proceedings of the IACR International Workshop on Public Key Cryptography, Amsterdam, The Netherlands, 28–31 March 2017; Springer: Berlin/Heidelberg, Germany, 2017; Volume 10174, pp. 409–434. [Google Scholar]
- Huang, Y.; Wu, K.; Chen, M. Fully dynamic multi-key fhe without gaussian noise. IEEE Access 2021, 9, 50639–50645. [Google Scholar] [CrossRef]
- Liu, F.H.; Wang, Z. Rounding in the rings. In Proceedings of the Annual International Cryptology Conference, Santa Barbara, CA, USA, 17–21 August 2020; Springer: Cham, Switzerland, 2020; Volume 12171, pp. 296–326. [Google Scholar]
- Brakerski, Z.; Perlman, R. Lattice-based fully dynamic multi-key fhe with short ciphertexts. In Proceedings of the Annual International Cryptology Conference, Santa Barbara, CA, USA, 14–18 August 2016; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2016; Volume 9814, pp. 190–213. [Google Scholar]
- Li, X.; Tang, C.; Hu, Y. Multi key fully homomorphic encryption system that supports multi-bit encryption. J. Cryptol. Res. 2022, 9, 248–256. [Google Scholar]
- Li, Z.; Ma, C.; Zhou, H. Multi-key fhe for multi-bit messages. Sci. China Inf. Sci. 2018, 61, 266–277. [Google Scholar] [CrossRef]
- Tang, C.; Hu, Y.; Li, X. Three round secure multiparty computation based on multi-key full-homomorphic encryption without crs. J. Cryptologic Res. 2021, 2, 273–281. [Google Scholar]
- Biswas, C.; Dutta, R. Dynamic multi-key fhe in symmetric key setting from lwe without using common reference matrix. J. Ambient Intell. Humaniz. Comput. 2022, 13, 1241–1254. [Google Scholar] [CrossRef]
- Peikert, C.; Shiehian, S. Multi-key fhe from lwe, revisited. In Proceedings of the Theory of Cryptography Conference, Tel Aviv, Israel, 10–13 January 2016; Springer: Berlin/Heidelberg, Germany, 2016; Volume 9986, pp. 217–238. [Google Scholar]
- Chen, H.; Chillotti, I.; Song, Y. Multi-key homomorphic encryption from tfhe. In Proceedings of the International Conference on the Theory and Application of Cryptology and Information Security, Kobe, Japan, 8–12 December 2019; Lecture Notes in Computer Science. Springer: Cham, Switzerland, 2019; Volume 11922, pp. 446–472. [Google Scholar]
- Clear, M.; Mcgoldrick, C. Multi-identity and multi-key leveled fhe from learning with errors. In Proceedings of the Annual Cryptology Conference, Santa Barbara, CA, USA, 16–20 August 2015; Springer: Berlin/Heidelberg, Germany, 2015; Volume 9216, pp. 630–656. [Google Scholar]
- Li, N.; Zhou, T.P.; Yang, X.Y.; Han, Y.L.; Tu, G.S. Efficient multi-key fhe with short extended ciphertexts and directed decryption protocol. IEEE Access 2019, 7, 56724–56732. [Google Scholar] [CrossRef]
- Chen, H.; Dai, W.; Kim, M.; Song, Y. Efficient multi-key homomorphic encryption with packed ciphertexts with application to oblivious neural network inference. In Proceedings of the 2019 ACM SIGSAC Conference on Computer and Communications Security, London, UK, 11–15 November 2019; pp. 395–412. [Google Scholar]
- Yang, X.; Zheng, S.; Zhou, T.; Liu, Y.; Che, X. Optimized relinearization algorithm of the multikey homomorphic encryption scheme. Tsinghua Sci. Technol. 2022, 27, 642–652. [Google Scholar] [CrossRef]
- Wang, X.; Xu, G.; Wang, M.; Meng, X. Mathematical Foundations of Public Key Cryptography; CRC Press: Boca Raton, FL, USA, 2015. [Google Scholar]
- Smart, N.P.; Vercauteren, F. Fully homomorphic simd operations. Des. Cryptogr. 2014, 71, 57–81. [Google Scholar] [CrossRef]
- Li, R.Q.; Jia, C.F. A multi-key homomorphic encryption scheme based on ntru. J. Cryptologic Res. 2020, 7, 683–697. [Google Scholar]
- Micciancio, D.; Peikert, C. Trapdoors for lattices: Simpler, tighter, faster, smaller. In Proceedings of the Annual International Conference on the Theory and Applications of Cryptographic Techniques, Cambridge, UK, 15–19 April 2012; Springer: Berlin/Heidelberg, Germany, 2012; Volume 7237, pp. 700–718. [Google Scholar]
- Gentry, C.; Sahai, A.; Waters, B. Homomorphic encryption from learning with errors: Conceptually-simpler, asymptotically-faster, attribute-based. In Proceedings of the Annual Cryptology Conference, Santa Barbara, CA, USA, 18–22 August 2013; Lecture Notes in Computer Science. Springer: Berlin/Heidelberg, Germany, 2013; Volume 8042, pp. 75–92. [Google Scholar]
- Zhou, T.; Zhang, Z.; Chen, L.; Che, X.; Liu, W.; Yang, X. Multi-key fully homomorphic encryption scheme with compact ciphertext. Cryptology ePrint Archive. 2021. Available online: https://eprint.iacr.org/2021/1131 (accessed on 6 September 2021).
- Gentry, C.; Halevi, S. Compressible fhe with applications to pir. In Proceedings of the Theory of Cryptography Conference, Nuremberg, Germany, 1–5 December 2019; Springer: Cham, Switzerland, 2019; Volume 11892, pp. 438–464. [Google Scholar]
- Chen, Y.; Dong, S.; Li, T.; Wang, Y.; Zhou, H. Dynamic multi-key fhe in asymmetric key setting from lwe. IEEE Trans. Inf. Forensics Secur. 2021, 16, 5239–5249. [Google Scholar] [CrossRef]
- Ren, Y.; Zhu, F.; Sharma, P.K.; Wang, T.; Wang, J.; Alfarraj, O.; Tolba, A. Data query mechanism based on hash computing power of blockchain in internet of things. Sensors 2020, 20, 207. [Google Scholar] [CrossRef] [PubMed]
- Wu, Q.; Han, Z.; Mohiuddin, G.; Ren, Y. Distributed timestamp mechanism based on verifiable delay functions. Comput. Syst. Sci. Eng. 2023, 44, 1633–1646. [Google Scholar] [CrossRef]
- Zhou, T.; Liu, W.; Li, N.; Yang, X.; Han, Y.; Zheng, S. Secure scheme for locating disease-causing genes based on multi-key homomorphic encryption. Tslnghua Sci. Technol. 2022, 27, 333–343. [Google Scholar] [CrossRef]
- Liu, J.; He, X.; Sun, R.; Du, X.; Guizani, M. Privacy-preserving data sharing scheme with fl via mpc in financial permissioned blockchain. In Proceedings of the ICC 2021-IEEE International Conference on Communications, Montreal, QC, Canada, 14–23 June 2021; IEEE: Piscataway, NJ, USA, 2021; pp. 1–6. [Google Scholar] [CrossRef]
- Matsumoto, M.; Oguchi, M. Speeding up sensor data encryption with a common key cryptosystem combined with fully homomorphic encryption on smartphones. In Proceedings of the 2020 Fourth World Conference on Smart Trends in Systems, Security and Sustainability (WorldS4), London, UK, 27–28 July 2020; IEEE: Piscataway, NJ, USA, 2020; pp. 500–505. Available online: https://ieeexplore.ieee.org/document/9210393/ (accessed on 1 October 2020).
- Kolsch, J.; Ratzke, A.; Grimm, C.; Heinz, C.; Nandagopal, G. Simulation based validation of a smart energy use case with homomorphic encryption. In Proceedings of the 2019 15th International Conference on Distributed Computing in Sensor Systems, Santorini Island, Greece, 29–31 May 2019; IEEE: Piscataway, NJ, USA, 2019; pp. 255–262. [Google Scholar] [CrossRef]
- Qiu, F.; Yu, J.; Zheng, F.; Liang, L.; Li, Y. Electric iot perception layer data privacy-preserving using multi identity-based fully homomorphic encryption. In Proceedings of the 2020 IEEE 3rd International Conference on Automation, Electronics and Electrical Engineering, Shenyang, China, 20–22 November 2020; IEEE: Piscataway, NJ, USA, 2020; pp. 30–34. [Google Scholar] [CrossRef]
- Ma, J.; Naas, S.A.; Sigg, S.; Lyu, X. Privacy-preserving federated learning based on multi-key homomorphic encryption. Int. J. Intell. Syst. 2022, 37, 5880–5901. [Google Scholar] [CrossRef]
- Xiang, K. Location-Preserving Matching Protocol for Ride-Hailing Service Based on Multi-Key Fully Homomorphic Encryption. Master’s Thesis, Harbin Institute of Technology, Harbin, China, 2020. [Google Scholar]
- Guo, H. Research and Implementation of Federated Learning That Supports Aggregation under Multiple Keys. Master’s Thesis, Harbin Institute of Technology, Harbin, China, 2020. [Google Scholar]
- Liu, Y. Research on Efficient Communication and Multi-Key Homomorphic Encryption Technology in Hierarchical Federated Learning Environment. Master’s Thesis, Beijing Jiaotong University, Beijing, China, 2021. [Google Scholar]
- Wang, H.; Feng, Y.; Zhao, L.; Tang, S. A secure multi-party computation protocol on the basis of multi key homomorphism. J. South China Univ. Technol. Sci. Ed. 2017, 45, 69–76. [Google Scholar]
- Ping, L.; Li, j.; Huang, Z.; Li, T.; Gao, C.Z.; Yiu, S.M.; Chen, K. Multi-key privacy-preserving deep learning in cloud computing. Future Gener. Comput. Syst. 2017, 74, 76–85. [Google Scholar]
- Kwabena, O.; Qin, Z.; Zhuang, T.; Qin, Z. Mscryptonet: Multi-scheme privacy-preserving deep learning in cloud computing. IEEE Access 2019, 7, 29344–29354. [Google Scholar] [CrossRef]
- Ren, Y.; Zhu, F.; Wang, J.; Sharma, P.K.; Ghosh, U. Novel vote scheme for decision-making feedback based on blockchain in internet of vehicles. IEEE Trans. Intell. Transp. Syst. 2022, 23, 1639–1648. [Google Scholar] [CrossRef]
- Huang, L.; Xu, L.; Zhu, L.; Gai, K. A blockchain-assisted privacy-preserving cloud computing method with multiple keys. In Proceedings of the 2021 IEEE 6th International Conference on Smart Cloud, Newark, NJ, USA, 6–8 November 2021; IEEE: Piscataway, NJ, USA; pp. 19–25. [Google Scholar] [CrossRef]




| Scheme | Technology | Function | Emphasis |
|---|---|---|---|
| CZL20 | LBD and DEC | reduce the ciphertext size | cost and efficient |
| ZLC20 | prime power cyclotomic polynomial ring | resist subdomain attacks | security |
| HWC21 | learning-with-rounding (LWR) | avoid gaussion sampling | efficient and security |
| Scheme | Technology | Function | Emphasis |
|---|---|---|---|
| KLP18 | LinkAlgo | convert single key to multi-key scheme | decentralization |
| LTH21 | combined KLP18 and LMZ18 | similar to above but multi-bit encryption | efficient and decentralization |
| THL21 | MKFHE.Expand (Encode, Link, Decode) | convert single key to multi-key scheme | efficient and decentralization |
| BD21 | symmetric key setting without CRS | similar to above but more efficient | efficient and decentralization |
| Scheme | Technology | Function | Emphasis |
|---|---|---|---|
| CZW17 | first BGV MKFHE | encrypt ring plaintext | efficient |
| LMZ18 | ciphertext packing | build a plaintext matrix | efficient |
| LJ20 | gadget vector and bit decomposition | remain ciphertext size unchanged | efficient and cost |
| Scheme | Technology | Function | Emphasis |
|---|---|---|---|
| CZW17 | zero-padded ciphertext vector | reduce complexity of ciphertext expansion | efficient |
| LZY+19 | nested ciphertext extension | reduce extended ciphertext size | efficient and cost |
| CCS19 | a new ciphertext multiplication | reduce evaluated ciphertext size | efficient and cost |
| ZZC20 | compact ciphertexts | reduce ciphertext size | efficient and cost |
| SWC21 | compressible ciphertexts | compress multiple ciphertexts into one | cost |
| CDL21 | distributed ciphertext extension | efficient and cost | |
| YZZ22 | rescaling techniques | reduce the complexity of relinearization | efficient |
| Scheme | Assumption | pk | CT | CRM | Dynamic | Bootstrap | Batch |
|---|---|---|---|---|---|---|---|
| CM15 | LWE | yes | no | no | no | ||
| CM15 | RLWE | yes | no | no | no | ||
| BP16 | LWE | yes | yes | yes | no | ||
| MW16 | LWE | yes | no | yes | |||
| PS16 1 | LWE | yes | yes | no | no | ||
| PS16 2 | LWE/KDM | yes | yes | no | no | ||
| KLP18 | LWE | no | no | yes | no | ||
| CCS19 | RLWE&Circular Security | yes | no | yes | no | ||
| CZL20 | RLWE | nk (K + d) | no | no | no | no | |
| BD21 | LWE | no | yes | no | no | ||
| CZW17 | LWE | yes | yes | no | no | ||
| CZW17 | RLWE | yes | yes | no | yes | ||
| CDL21 | LWE | yes | yes | no | no | ||
| CDKS19 | RLWE | yes | yes | yes | |||
| LZY+19 | GLWE | yes | no | yes | yes | ||
| ZZC20 | GLWE | yes | yes | ||||
| HWC21 | LWR | yes | yes | no | |||
| YZZ22 | RLWE | yes | no | yes | no | ||
| CZY21 | RLWE | yes | yes | no | |||
| LJ20 | RLWE&DSPR | yes | yes |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Yuan, M.; Wang, D.; Zhang, F.; Wang, S.; Ji, S.; Ren, Y. An Examination of Multi-Key Fully Homomorphic Encryption and Its Applications. Mathematics 2022, 10, 4678. https://doi.org/10.3390/math10244678
Yuan M, Wang D, Zhang F, Wang S, Ji S, Ren Y. An Examination of Multi-Key Fully Homomorphic Encryption and Its Applications. Mathematics. 2022; 10(24):4678. https://doi.org/10.3390/math10244678
Chicago/Turabian StyleYuan, Minghao, Dongdong Wang, Feng Zhang, Shenqing Wang, Shan Ji, and Yongjun Ren. 2022. "An Examination of Multi-Key Fully Homomorphic Encryption and Its Applications" Mathematics 10, no. 24: 4678. https://doi.org/10.3390/math10244678
APA StyleYuan, M., Wang, D., Zhang, F., Wang, S., Ji, S., & Ren, Y. (2022). An Examination of Multi-Key Fully Homomorphic Encryption and Its Applications. Mathematics, 10(24), 4678. https://doi.org/10.3390/math10244678






