In this section, we use tiled orders associated with suitable posets to generate emerging images from fixed templates. Such templates are obtained after applying some novel matrix operations.
3.1. Matrix Operations
In this section, we define algorithms which will allow obtaining emerging images via partially ordered sets.
Given two
-tiled orders
,
and
then the
joining matrix of
and
is such that its entries satisfy the following identities (modulo
):
where,
denotes that the value of the entry
in a matrix
is precisely
(in matrices, we will write
to denote the corresponding entry
). In the case of tiled orders
(
) indicates that points
i and
j in
are comparable (incomparable).
and
are said to be
complementary to each other.
As an example consider the following 01-tiled orders
,
, and
The following is the identity associated with the corresponding posets.
If
is a
-tiled order then the
completion of
is a
-tiled order whose entries satisfy the following identities:
For example, if
then
The aforementioned definitions of , , and prove the following results.
Proposition 1. If is the poset of then , where denotes a sub-poset of the poset dual .
Proposition 2. If Λ is a -tiled order then is a -tiled order for all the possible values of r and s.
The
reduction of a
-tiled order
is defined by the following identities:
As for Propositions 1 and 2, the following result holds by definition.
Proposition 3. If and Λ is a 01-tiled order then is a -tiled order.
For example, if
then
In [
12] several templates or masters (see
Figure 4) were used in order to generate a repository of emerging images, in this work we obtain such templates by using joining (of tiled orders
and
shown in
Figure 5 and
Figure 6), completion and reduction operations.
3.4. The Algorithm ATGEI
The algorithm to generate emerging images (Algorithm ATGEI) embraces Algorithm 1, whose application assumes that a boundary of a model has been already detected. In this section, we introduce an algorithm to detect such a boundary. The starting step consists of fixing some suitable markers, which are clusters with 0 as pixel value (including those after the application of a completion process).
Markers are denoted as , , or . Arrows, in this case denote which clusters in will be changed by using some type of transformation (reduction or completion). For instance, notation () means that any cluster is transformed for any (). We let denote the ordered set of markers associated with a model of an image ().
Algorithm 2 detects clusters in the boundary of . Then applies reduction to any cluster in the direction of the arrow associated with the marker. In this way, the sequence M determines the closure of . Let us describe some details associated with closure recognition.
For the development of the Algorithm 2 the following three procedures are carried out:
Movement;
Appendix removal;
Cropping.
| Algorithm 2: Closure detection |
- 1.
If and are consecutive markers with then both and belong to the boundary of T and have pixel value . - 2.
Compute the -distance
where is the ith row of and let the cluster such that then belongs to the boundary of T.
- 3.
If two clusters and satisfy the minimal condition then is given by the orientation of the arrow associated with the marker. Its pixel value, i.e., satisfy the minimal condition and has the minimal pixel value. - 4.
Apply reduction. - 5.
Repeat the process until the marker is reached.
|
Movement
In this step, Algorithm 2 goes through the array from the markers and it selects a temporal border for the model . By symmetry, it suffices to describe the behavior of the algorithm in vertical direction. We will assume that there is a partition of into suitable blocks denoted , , for some suitable . Thus, . Algorithm 2 is applied block by block.
is arcwise-connected if for any pair of clusters
, with pixel values
there exists a set of consecutive clusters
With the taxicab distance d, such that for all the possible values of i and v (taking into account the symmetry of the procedure). Henceforth, the set will be called a path. Consecutive clusters in the boundary of a model constitute a path from the initial marker to the (temporal) final marker.
The path , with initial cluster and final cluster , can be written , whereas the set of admissible paths connecting with is denoted as . We let denote the length of .
A cluster with pixel value is said to be a bridge. Bridges allow that the boundary of a model be arcwise-connected.
Note that the application of a movement generates a path . However, such automatic movement does not guarantee the minimality of . That is, it is possible to generate undesired clusters, the process for which such undesired clusters are deleted is called appendix removal. This process can be carried out by a suitable reduction.
Once a movement is applied in a given orientation of a suitable marker, it is necessary to clean the transformed block by deleting all the clusters in the exterior of via reductions. Such a procedure is said to be cropping.
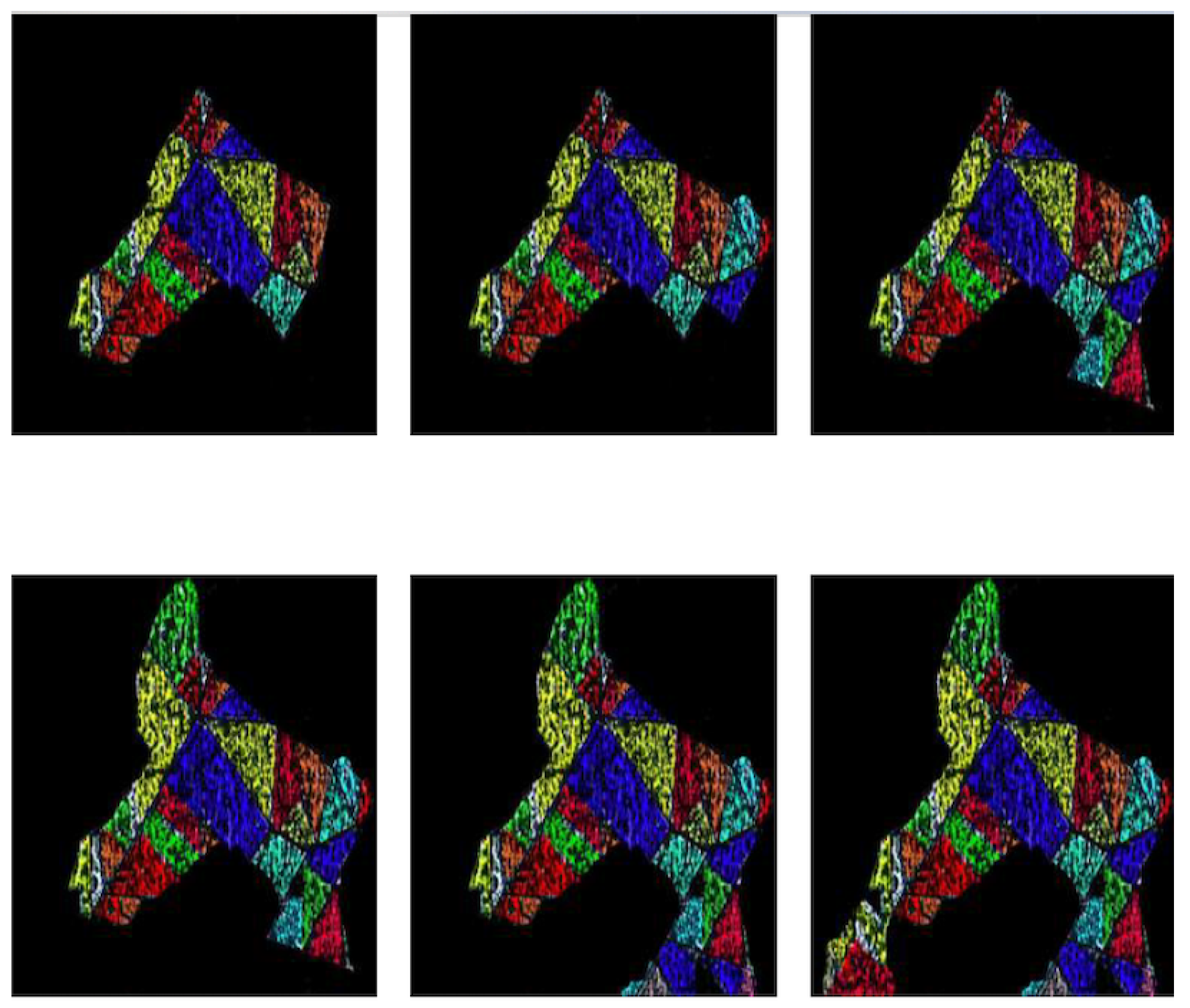
Joining, rotation by suitable angles (of a model ), completion, reduction, and a suitable filtering allow obtaining all the models associated with an image-repository , such a set of models is also a set of emerging images whose parts are given by clusters.
The following Algorithm 3 summarizes the process for which an emerging image based on clusters is obtained.
| Algorithm 3: Algorithm ATGEI |
| 1. Apply steps 1–3 of Algorithm 1. |
| 2. Apply step 4 of Algorithm 1 via Algorithm 2. |
| 3. Apply step 5 of Algorithm 1 (including cropping and appendix removal). |
The following
Figure 12 and
Figure 13 give an example of closure detection via the software REIADT.
The following are markers and bridges used to obtain
Figure 13:
, , , ,, ,, , , , , , , , ,, , , , , , , , , , .