Journal Description
Cryptography
Cryptography
is an international, scientific, peer-reviewed, open access journal on cryptography published bimonthly online by MDPI.
- Open Access— free for readers, with article processing charges (APC) paid by authors or their institutions.
- High Visibility: indexed within Scopus, ESCI (Web of Science), dblp, and other databases.
- Journal Rank: JCR - Q2 (Computer Science, Theory and Methods) / CiteScore - Q1 (Applied Mathematics)
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 19.3 days after submission; acceptance to publication is undertaken in 3.9 days (median values for papers published in this journal in the second half of 2025).
- Recognition of Reviewers: reviewers who provide timely, thorough peer-review reports receive vouchers entitling them to a discount on the APC of their next publication in any MDPI journal, in appreciation of the work done.
- Journal Cluster of Information Systems and Technology: Analytics, Applied System Innovation, Cryptography, Data, Digital, Informatics, Information, Journal of Cybersecurity and Privacy and Multimedia.
Impact Factor:
2.1 (2024);
5-Year Impact Factor:
2.2 (2024)
Latest Articles
Moving-Skewness Preprocessing for Simple Power Analysis on Cryptosystems: Revealing Asymmetry in Leakage
Cryptography 2026, 10(2), 23; https://doi.org/10.3390/cryptography10020023 - 3 Apr 2026
Abstract
In side-channel analysis, simple power analysis (SPA) is a widely used technique for recovering secret information by exploiting differences between operations in traces. However, in realistic measurement environments, SPA is often hindered by noise, temporal misalignment, and weak or transient leakage, which obscure
[...] Read more.
In side-channel analysis, simple power analysis (SPA) is a widely used technique for recovering secret information by exploiting differences between operations in traces. However, in realistic measurement environments, SPA is often hindered by noise, temporal misalignment, and weak or transient leakage, which obscure secret-dependent features in single or very few power traces. In this paper, we provide a systematic analysis of moving-skewness-based trace preprocessing for enhancing asymmetric leakage characteristics relevant to SPA. The method computes local skewness within a moving window along the trace, transforming the original signal into a skewness trace that emphasizes distributional asymmetry while suppressing noise. Unlike conventional smoothing-based preprocessing techniques, the proposed approach preserves and can even amplify subtle leakage patterns and spike-like transient events that are often attenuated by low-pass filtering or moving-average methods. To further improve applicability under different leakage conditions, we introduce feature-driven window-selection strategies that align preprocessing parameters with various leakage characteristics. Both simulated datasets and real measurement traces collected from multiple cryptographic platforms are used to evaluate the effectiveness of the approach. The experimental results indicate that moving-skewness preprocessing improves leakage visibility and achieves higher SPA success rates compared to commonly used preprocessing methods.
Full article
(This article belongs to the Section Hardware Security)
►
Show Figures
Open AccessArticle
A Searchable Encryption Scheme Based on CRYSTALS-Dilithium
by
Minghui Zheng, Anqi Xiao, Shicheng Huang and Deju Kong
Cryptography 2026, 10(2), 22; https://doi.org/10.3390/cryptography10020022 - 27 Mar 2026
Abstract
►▼
Show Figures
With the advancement in quantum computing technology, the number theory-based hard problems underlying traditional searchable encryption algorithms are now vulnerable to efficient quantum attacks. To address this challenge, this paper proposes Dilithium-PAEKS (Dilithium-Public Authenticated Encryption with Keyword Search), a searchable encryption scheme based
[...] Read more.
With the advancement in quantum computing technology, the number theory-based hard problems underlying traditional searchable encryption algorithms are now vulnerable to efficient quantum attacks. To address this challenge, this paper proposes Dilithium-PAEKS (Dilithium-Public Authenticated Encryption with Keyword Search), a searchable encryption scheme based on the post-quantum cryptographic algorithm CRYSTALS-Dilithium. By transforming the verification relationship of digital signatures into a matching relationship between trapdoors and ciphertexts, the scheme not only meets the functional requirements of searchable encryption but also demonstrates quantum resistance. The implementation enhances algorithm efficiency through keyword-based signatures and dynamic matching testing mechanisms. The security of the scheme is defined by the MLWE and MSIS hard problems, with proofs of keyword ciphertext indistinguishability and trapdoor indistinguishability under the random oracle model. Additionally, the scheme provides strong resistance against both outside and insider keyword guessing attacks through sender–receiver binding mechanisms and trapdoor indistinguishability properties. Experimental results show that, compared to the post-quantum schemes CP-Absel and LB-FSSE, the proposed scheme demonstrates superior overall computational efficiency while maintaining stronger quantum resistance than the traditional scheme SM9-PAEKS.
Full article

Figure 1
Open AccessArticle
Homomorphic ReLU with Full-Domain Bootstrapping
by
Yuqun Lin, Yi Huang, Xiaomeng Tang, Jingjing Fan, Qifei Xu, Zoe-Lin Jiang, Xiaosong Zhang and Junbin Fang
Cryptography 2026, 10(2), 21; https://doi.org/10.3390/cryptography10020021 - 24 Mar 2026
Abstract
Fully homomorphic encryption (FHE) offers a promising solution for privacy-preserving machine learning by enabling arbitrary computations on encrypted data. However, the efficient evaluation of non-linear functions—such as the ReLU activation function over large integers—remains a major obstacle in practical deployments, primarily due to
[...] Read more.
Fully homomorphic encryption (FHE) offers a promising solution for privacy-preserving machine learning by enabling arbitrary computations on encrypted data. However, the efficient evaluation of non-linear functions—such as the ReLU activation function over large integers—remains a major obstacle in practical deployments, primarily due to high bootstrapping overhead and limited precision support in existing schemes. In this paper, we propose
(This article belongs to the Special Issue Information Security and Privacy—ACISP 2025)
►▼
Show Figures

Figure 1
Open AccessArticle
Securely Scaling Autonomy: The Role of Cryptography in Future Unmanned Aircraft Systems (UASs)
by
Paul Rochford, William J. Buchanan, Rich Macfarlane and Madjid Tehrani
Cryptography 2026, 10(2), 20; https://doi.org/10.3390/cryptography10020020 - 20 Mar 2026
Abstract
►▼
Show Figures
The decentralisation of autonomous Unmanned Aircraft Systems (UASs) introduces significant challenges in terms of establishing secure communication and consensus in contested, resource-constrained environments. This research addresses these challenges by conducting a comprehensive performance evaluation of two cryptographic technologies: Messaging Layer Security (MLS) for
[...] Read more.
The decentralisation of autonomous Unmanned Aircraft Systems (UASs) introduces significant challenges in terms of establishing secure communication and consensus in contested, resource-constrained environments. This research addresses these challenges by conducting a comprehensive performance evaluation of two cryptographic technologies: Messaging Layer Security (MLS) for group key exchange, and threshold signatures (FROST and BLS) for decentralised consensus. Seven leading open-source libraries were methodically assessed through a series of static, network-simulated, and novel bulk-signing benchmarks to measure their computational efficiency and practical resilience. This paper confirms that MLS is a viable solution, capable of supporting the group sizes and throughput requirements of a UAS swarm. It corroborates prior work by identifying the Cisco MLSpp library as unsuitable for dynamic environments due to poorly scaling group management functions, while demonstrating that OpenMLS is a highly performant and scalable alternative. Furthermore, the findings show that operating MLS in a ‘key management’ mode offers a dramatic increase in performance and resilience, a critical trade-off for UAS operations. For consensus, the benchmarks reveal a range of compromises for developers to consider, while identifying the Zcash FROST implementation as the most effective all-around performer for sustained, high-volume use cases due to its balance of security features and efficient verification.
Full article

Figure 1
Open AccessReview
A Scoping Analysis of the Literature on the Use of Hybrid Cryptographic Systems for Data Hiding in Cloud Storage
by
Luthando Mletshe, Mnoneleli Nogwina and Colin Chibaya
Cryptography 2026, 10(2), 19; https://doi.org/10.3390/cryptography10020019 - 13 Mar 2026
Abstract
Organizations have been moving on-premises data functionalities to cloud storage environments. The need for advanced hybrid cryptography is deemed a promising solution for securing data on cloud storage. This scoping review explores the application of hybrid cryptographic systems for data hiding in cloud
[...] Read more.
Organizations have been moving on-premises data functionalities to cloud storage environments. The need for advanced hybrid cryptography is deemed a promising solution for securing data on cloud storage. This scoping review explores the application of hybrid cryptographic systems for data hiding in cloud storage. It focuses on identifying global research trends, technological approaches, and contextual gaps in implementation. The review systematically examines the literature from major scholarly databases to identify existing models that combine traditional and modern cryptographic techniques to enhance data confidentiality, integrity, and authenticity against cloud-based security threats. Out of the 8250 eligible papers, 24 were included in the review. The findings reveal that the majority of scholarly contributions originate from Asia, averaging 87.5%, as reflected in the distribution of included articles by continent. Particularly, India and China dominate in the space, with a complete absence of studies from Africa, including South Africa. This geographical disparity underscores a significant research gap in the contextualization of hybrid cryptographic frameworks suited to Africa’s unique infrastructural and regulatory environments. The review further reveals a limited focus on the development of lightweight, scalable, and adaptable hybrid cryptographic schemes. Such approaches are essential for addressing challenges related to bandwidth limitations, computational efficiency, and regulatory compliance in developing regions. Consequently, this study contributes by establishing a comprehensive knowledge map of hybrid cryptography for cloud security, emphasizing the necessity for region-specific, context-aware frameworks. The findings provide a foundation for future investigations aimed at developing robust efficient hybrid cryptographic models that can strengthen data security in African cloud infrastructures.
Full article
(This article belongs to the Collection Survey of Cryptographic Topics)
►▼
Show Figures

Figure 1
Open AccessReview
Cryptographic Foundations of Pseudonymisation for Personal Data Protection
by
Konstantinos Limniotis
Cryptography 2026, 10(2), 18; https://doi.org/10.3390/cryptography10020018 - 11 Mar 2026
Abstract
Pseudonymisation constitutes an essential technical and organisational measure for implementing personal data-protection safeguards. Its main goal is to hide identities of individuals, thus reducing data protection and privacy risks through facilitating the fulfilment of several principles such as data minimisation and security. However,
[...] Read more.
Pseudonymisation constitutes an essential technical and organisational measure for implementing personal data-protection safeguards. Its main goal is to hide identities of individuals, thus reducing data protection and privacy risks through facilitating the fulfilment of several principles such as data minimisation and security. However, selecting and deploying appropriate pseudonymisation mechanisms in a risk-based approach, tailored to the specific data processing context, remains a non-trivial task. This survey paper aims to present especially how cryptography can be used at the service of pseudonymisation, putting emphasis not only on traditional approaches but also on advanced cryptographic techniques that have been proposed to address special pseudonymisation challenges. To this end, we systematically classify existing approaches according to a taxonomy that captures key design dimensions that are relevant to specific data-protection challenges. Finally, since the notion of pseudonymisation adopted in this work is grounded in European data-protection law, we also discuss recent legal developments, in particular the CJEU’s latest judgment, which refined the interpretation of pseudonymous data.
Full article
(This article belongs to the Collection Survey of Cryptographic Topics)
►▼
Show Figures

Figure 1
Open AccessReview
A Survey on Classical Lattice Algorithms
by
Tongchen Shen and Xiangxue Li
Cryptography 2026, 10(2), 17; https://doi.org/10.3390/cryptography10020017 - 6 Mar 2026
Abstract
The rapid advancement of quantum computing poses a severe threat to traditional public key cryptosystems. Lattice-based cryptography has emerged as a core candidate for post-quantum cryptography due to its presumed quantum resistance, robust security foundations, and functional versatility, with its concrete security relying
[...] Read more.
The rapid advancement of quantum computing poses a severe threat to traditional public key cryptosystems. Lattice-based cryptography has emerged as a core candidate for post-quantum cryptography due to its presumed quantum resistance, robust security foundations, and functional versatility, with its concrete security relying on the computational hardness of lattice problems. Existing lattice-based cryptography surveys mainly focus on cryptosystem design, scheme comparisons, and post-quantum cryptography standardization progress, with only cursory coverage of classical lattice algorithms that underpin the concrete security of lattice-based cryptography. We present the first systematic survey of classical lattice algorithms, focusing on two core categories of algorithms for solving lattice problems: approximate algorithms and exact algorithms. The approximate algorithms cover mainstream lattice basis reduction methods such as Lenstra–Lenstra–Lovász (LLL), Block Korkine–Zolotarev (BKZ), and General Sieve Kernel (G6K) algorithms, as well as alternative frameworks. The exact algorithms encompass dominant techniques like enumeration and sieving algorithms, along with alternative strategies. We systematically trace the evolutionary trajectory and inherent logical connections of various algorithms, clarify their core mechanisms, and identify promising future research directions. This survey not only serves as an introductory guide for beginners but also provides a valuable reference for seasoned researchers, facilitating the concrete security evaluation of lattice-based cryptosystems and the design of novel lattice algorithms.
Full article
(This article belongs to the Section Cryptography Reviews)
►▼
Show Figures

Figure 1
Open AccessArticle
A Robust Image Encryption Framework Using Deep Feature Extraction and AES Key Optimization
by
Sahara A. S. Almola, Hameed A. Younis and Raidah S. Khudeyer
Cryptography 2026, 10(2), 16; https://doi.org/10.3390/cryptography10020016 - 2 Mar 2026
Abstract
►▼
Show Figures
This article presents a novel framework for encrypting color images to enhance digital data security using deep learning and artificial intelligence techniques. The system employs a two-model neural architecture: the first, a Convolutional Neural Network (CNN), verifies sender authenticity during user authentication, while
[...] Read more.
This article presents a novel framework for encrypting color images to enhance digital data security using deep learning and artificial intelligence techniques. The system employs a two-model neural architecture: the first, a Convolutional Neural Network (CNN), verifies sender authenticity during user authentication, while the second extracts unique fingerprint features. These features are converted into high-entropy encryption keys using Particle Swarm Optimization (PSO), minimizing key similarity and ensuring that no key is reused or transmitted. Keys are generated in real time simultaneously at both the sender and receiver ends, preventing interception or leakage and providing maximum confidentiality. Encrypted images are secured using the Advanced Encryption Standard (AES-256) with keys uniquely bound to each user’s biometric identity, ensuring personalized privacy. Evaluation using security and encryption metrics yielded strong results: entropy of 7.9991, correlation coefficient below 0.00001, NPCR of 99.66%, UACI of 33.9069%, and key space of 2256. Although the final encryption employs an AES-256 key (key space of 2256), this key is derived from a much larger deep-key space of 28192 generated by multi-layer neural feature extraction and optimized via PSO, thereby significantly enhancing the overall cryptographic strength. The system also demonstrated robustness against common attacks, including noise and cropping, while maintaining recoverable original content. Furthermore, the neural models achieved classification accuracy exceeding 99.83% with an error rate below 0.05%, confirming the framework’s reliability and practical applicability. This approach provides a secure, dynamic, and efficient image encryption paradigm, combining biometric authentication and AI-based feature extraction for advanced cybersecurity applications.
Full article

Figure 1
Open AccessArticle
Performance Evaluation of NIST-Standardized Post-Quantum and Symmetric Ciphers for Mitigating Deepfakes
by
Mohammad Alkhatib
Cryptography 2026, 10(2), 15; https://doi.org/10.3390/cryptography10020015 - 26 Feb 2026
Abstract
►▼
Show Figures
Deepfake technology can produce highly realistic manipulated media which pose as significant cybersecurity threats, including fraud, misinformation, and privacy violations. This research proposes a deepfake prevention approach based on symmetric and asymmetric ciphers. Post-quantum asymmetric ciphers were utilized to perform digital signature operations,
[...] Read more.
Deepfake technology can produce highly realistic manipulated media which pose as significant cybersecurity threats, including fraud, misinformation, and privacy violations. This research proposes a deepfake prevention approach based on symmetric and asymmetric ciphers. Post-quantum asymmetric ciphers were utilized to perform digital signature operations, which offer essential security services, including integrity, authentication, and non-repudiation. Symmetric ciphers were also employed to provide confidentiality and authentication. Unlike classical ciphers that are vulnerable to quantum attacks, this study adopts quantum-resilient ciphers to offer long-term security. The proposed approach enables entities to digitally sign media content before public release on other platforms. End users can subsequently verify the authenticity of content using the public keys of the media creators. To identify the most efficient ciphers to perform cryptography operations required for deepfake prevention, the study explores the implementation of quantum-resilient symmetric and asymmetric ciphers standardized by NIST, including Dilithium, Falcon, SPHINCS+, and Ascon-80pq. Additionally, this research provides comprehensive comparisons between the various classical and post-quantum ciphers in both categories: symmetric and asymmetric. Experimental results revealed that Dilithium-5 and Falcon-512 algorithms outperform other post-quantum ciphers, with a time delay of 2.50 and 251 ms, respectively, for digital signature operations. The Falcon-512 algorithm also demonstrates superior resource efficiency, making it a cost-effective choice for digital signature operations. With respect to symmetric ciphers, Ascon-80pq achieved the lowest time consumption, taking just 0.015 ms to perform encryption and decryption operations. Also, it is a significant option for constrained devices, since it consumes fewer resources compared to standard symmetric ciphers, such as AES. Through comprehensive evaluations and comparisons of various symmetric and asymmetric ciphers, this study serves as a blueprint to identify the most efficient ciphers to perform the cryptography operations necessary for deepfake prevention.
Full article

Figure 1
Open AccessArticle
Strong Non-Transferability from Randomizable Universal Designated Verifier Signatures
by
Magdalena Bertram, Benjamin Zengin, Nicolas Buchmann and Marian Margraf
Cryptography 2026, 10(1), 14; https://doi.org/10.3390/cryptography10010014 - 18 Feb 2026
Abstract
In the context of digital certification systems, the demand for privacy-preserving authentication is increasingly vital, particularly for critical applications that involve sensitive personal data. Traditional digital signatures provide a robust means of implementing such systems. However, they raise significant privacy concerns due to
[...] Read more.
In the context of digital certification systems, the demand for privacy-preserving authentication is increasingly vital, particularly for critical applications that involve sensitive personal data. Traditional digital signatures provide a robust means of implementing such systems. However, they raise significant privacy concerns due to their public verifiability, which allows verifiers to prove the authenticity of the received sensitive data to third parties. Universal designated verifier signature (UDVS) schemes address these privacy risks by offering non-transferability, ensuring that only the specified verifier can confirm the validity of the designated verifier signature (DVS). However, despite their advantages, existing UDVS models exhibit vulnerabilities that may allow tracking of the user’s authentications among cooperating verifiers and enable third parties to be convinced of the authenticity of sensitive user data by retrieving DVSs from different, non-cooperating verifiers. This paper presents a strategy to achieve strong non-transferability, which effectively addresses these vulnerabilities, by being the first to extend the concept of randomizability to UDVS schemes and their security properties. Our findings demonstrate that a randomizable UDVS scheme can serve as a solid foundation for constructing strong non-transferable UDVS schemes. Finally, we propose an efficient, strong, non-transferable UDVS scheme as an instantiation of our strategy, utilizing state-of-the-art Type 3 pairings, significantly improving upon previous constructions.
Full article
Open AccessArticle
Secure and Efficient Block Cipher Mode Design for Parallel Processing and Reliable Security
by
Valli Kumari Vatsavayi and Dinesh Reddy Bommireddy
Cryptography 2026, 10(1), 13; https://doi.org/10.3390/cryptography10010013 - 13 Feb 2026
Abstract
Communication is defined as the process of transferring data and exchanging information between interconnected systems. Due to the increasing reliance on digital infrastructures by the military, financial, and healthcare sectors, it is important to ensure the confidential, authentication, and tamper-proof nature of communications.
[...] Read more.
Communication is defined as the process of transferring data and exchanging information between interconnected systems. Due to the increasing reliance on digital infrastructures by the military, financial, and healthcare sectors, it is important to ensure the confidential, authentication, and tamper-proof nature of communications. In addition, the increasing need for secure communications in the fields of network security and cryptography have led to the development of numerous systems. The basic requirement of these systems is that under the same key, identical plaintexts do not result in identical ciphertexts. The most significant contribution to this requirement has came from block cipher modes. There are many traditional modes of operation such as the Electronic Code Book (ECB) compromises between simplicity and security. Probabilistic Modes such as the Cipher Block Chaining Mode (CBC) provide a method to randomize data so that the potential for pattern analysis is eliminated, while Deterministic Modes such as ECB enable potential access to the patterns within the plaintexts. Conversely, since the randomization is in the Probabilistic Mode, there is no access to the patterns; however, the sequentiality of the blocks creates dependence and increases the computing overhead. To address these issues, a novel block cipher mode that provides the highest level of security and the most effective method for performing encryption and decryption will be proposed in this paper. It is anticipated that the improved security features and efficient encryption and decryption procedures will significantly improve confidentiality. The methods proposed will utilize compact key structures, parallel processing, a header generation based on multiple random values, and a Key-derived S Box. The experimental results show that SEBCM is more effective than CBC with respect to speed in both encryption and decryption.
Full article
(This article belongs to the Special Issue Advances in Provable and Practical Security—ProvSec 2025)
►▼
Show Figures

Figure 1
Open AccessReview
Post-Quantum Cryptography in Networking Protocols: Challenges, Solutions, and Future Directions
by
Sang-Yoon Chang and Qaiser Khan
Cryptography 2026, 10(1), 12; https://doi.org/10.3390/cryptography10010012 - 12 Feb 2026
Cited by 1
Abstract
Post-quantum cryptography (PQC) provides the essential cryptographic algorithms needed to secure digital networking systems against future adversaries equipped with quantum computing. This paper reviews the PQC research landscape and identifies open challenges and future directions for the critical transition to PQC in digital
[...] Read more.
Post-quantum cryptography (PQC) provides the essential cryptographic algorithms needed to secure digital networking systems against future adversaries equipped with quantum computing. This paper reviews the PQC research landscape and identifies open challenges and future directions for the critical transition to PQC in digital networking systems. Building on the NIST standardization process which has hardened the PQC cipher algorithm security, this paper analyzes and describes the recent research on PQC implementations and integrations into scalable and standardized networking systems (Internet, web and cellular networks). We review research on the security, side-channel threats, performances, overheads, and compatibility of PQC ciphers. We also study the research incorporating PQC into the standardized web and cellular networking protocols, ranging from testing the PQC feasibility to proposing protocol solutions and mechanisms to enable PQC. Our study highlights the PQC challenge of large parameter sizes, common across the PQC cipher algorithms, and the research proposing protocol- and system-level mechanisms to address them. Informed by the survey, this paper identifies and highlights the research gaps and future directions to facilitate further research and development for PQC and to secure next-generation digital networking systems.
Full article
(This article belongs to the Special Issue Advances in Post-Quantum Cryptography)
►▼
Show Figures

Figure 1
Open AccessReview
Post-Quantum PKI: A Survey of Applications and Benchmarking Practices
by
Maya Thabet, Antonia Tsili, Konstantinos Krilakis and Dimitris Syvridis
Cryptography 2026, 10(1), 11; https://doi.org/10.3390/cryptography10010011 - 12 Feb 2026
Abstract
Post-quantum cryptography (PQC) is, and should be, currently dominating the field of cybersecurity, with many works designing and evaluating the transition of communications security to quantum-safe solutions. As the security level and implementations of post-quantum algorithms become more mature, the research on their
[...] Read more.
Post-quantum cryptography (PQC) is, and should be, currently dominating the field of cybersecurity, with many works designing and evaluating the transition of communications security to quantum-safe solutions. As the security level and implementations of post-quantum algorithms become more mature, the research on their application to realistic conditions changes accordingly, especially their application to widely adopted network architectures and corresponding protocols such as the Public Key Infrastructure (PKI). In this survey, we identified articles presenting ways of integrating PQC algorithms to PKI and classified related work according to the employed methods and benchmarking choices. The main results from many evaluations converge to similar conclusions on the performance of the most popular PC digital signature algorithms; however, modeling choices concerning architecture variants, hardware and measurement metrics vary. The diversity of the results and experimental setups makes comparison difficult and arrival at an objective conclusion regarding PKI requirements almost impossible. Ultimately, this review reveals a fragmented landscape of benchmarking practices for post-quantum PKI systems. The absence of standardized evaluation frameworks and common test environments limits the comparability and reproducibility of the findings. We aim to provide reference implementations, which are essential to guide the transition of PKI infrastructures toward robust, scalable, and quantum-resistant deployments.
Full article
(This article belongs to the Special Issue Advances in Post-Quantum Cryptography)
►▼
Show Figures

Graphical abstract
Open AccessReview
Some Mathematical Problems Behind Lattice-Based Cryptography
by
Chuanming Zong
Cryptography 2026, 10(1), 10; https://doi.org/10.3390/cryptography10010010 - 12 Feb 2026
Abstract
In 1994, P. Shor discovered quantum algorithms that can break both the RSA cryptosystem and the ElGamal cryptosystem. In 2007, D-Wave demonstrated the first quantum computer. These events and further developments have brought a crisis to secret communication. In 2016, the National Institute
[...] Read more.
In 1994, P. Shor discovered quantum algorithms that can break both the RSA cryptosystem and the ElGamal cryptosystem. In 2007, D-Wave demonstrated the first quantum computer. These events and further developments have brought a crisis to secret communication. In 2016, the National Institute of Standards and Technology (NIST) launched a global project to solicit and select a handful of encryption algorithms with the ability to resist quantum computer attacks. In 2022, it announced four candidates, CRYSTALS-Kyber, CRYSTALS-Dilithium, Falcon, and Sphincs+, for post-quantum cryptography standards. The first three are based on lattice theory and the last on a hash function. The security of lattice-based cryptosystems relies on the computational complexity of the shortest vector problem (SVP), the closest vector problem (CVP), and their generalizations. As we will explain, the SVP is a ball-packing problem, and the CVP is a ball-covering problem. Furthermore, both the SVP and CVP are equivalent to arithmetic problems for positive definite quadratic forms. This paper will briefly describe the mathematical problems on which lattice-based cryptography is built so that cryptographers can extend their views and learn something useful.
Full article
(This article belongs to the Section Cryptography Reviews)
►▼
Show Figures

Figure 1
Open AccessFeature PaperArticle
MIND-Crypt: A Machine Learning Framework for Assessing the Indistinguishability of Lightweight Block Ciphers Across Multiple Modes of Operation
by
Jimmy Dani, Kalyan Nakka and Nitesh Saxena
Cryptography 2026, 10(1), 9; https://doi.org/10.3390/cryptography10010009 - 10 Feb 2026
Abstract
Indistinguishability is a fundamental principle of cryptographic security, crucial for securing data transmitted between Internet of Things (IoT) devices. This principle ensures that an attacker cannot distinguish between the encrypted data, also known as ciphertext, and random data or the ciphertexts of two
[...] Read more.
Indistinguishability is a fundamental principle of cryptographic security, crucial for securing data transmitted between Internet of Things (IoT) devices. This principle ensures that an attacker cannot distinguish between the encrypted data, also known as ciphertext, and random data or the ciphertexts of two messages encrypted with the same key. This research investigates the ability of machine learning (ML) to assess the indistinguishability property in encryption systems, with a focus on lightweight ciphers. As our first case study, we consider the SPECK32/64 and SIMON32/64 lightweight block ciphers, designed for IoT devices operating under significant energy constraints. In this research, we introduce MIND-Crypt (a Machine-learning-based framework for assessing the INDistinguishability of Cryptographic algorithms), a novel ML-based framework designed to assess the cryptographic indistinguishability of lightweight block ciphers, specifically the SPECK32/64 and SIMON32/64 encryption algorithms in CBC, CFB, OFB, and CTR modes, under Known Plaintext Attacks (KPAs). Our approach involves training ML models using ciphertexts from two plaintext messages encrypted with the same key to determine whether ML algorithms can identify meaningful cryptographic patterns or leakage. Our experiments show that modern ML techniques consistently achieve accuracy equivalent to random guessing, indicating that no statistically exploitable patterns exist in the ciphertexts generated by the considered lightweight block ciphers. Although some models exhibit mode-dependent bias (e.g., collapsing to a single-class prediction in CBC and CFB), their overall accuracy remains at random guessing levels, reinforcing that no meaningful distinguishing patterns are learned. Furthermore, we demonstrate that, when ML algorithms are trained on all possible combinations of ciphertexts for given plaintext messages, their behavior reflects memorization rather than generalization to unseen ciphertexts. Collectively, these findings suggest that existing block ciphers have secure cryptographic designs against ML-based indistinguishability assessments, reinforcing their security even under round-reduced conditions.
Full article
(This article belongs to the Special Issue Advances in Privacy, Security, and Trust: Cryptographic Perspectives from PST2025)
►▼
Show Figures

Figure 1
Open AccessArticle
On Tabu Search for Block Cyphers Cryptanalysis
by
Adrian Donatien-Charon, Mijail Borges-Quintana, Miguel A. Borges-Trenard, Omar Rojas and Guillermo Sosa-Gómez
Cryptography 2026, 10(1), 8; https://doi.org/10.3390/cryptography10010008 - 27 Jan 2026
Abstract
►▼
Show Figures
This article presents general methodologies for plaintext attacks on block ciphers using the Tabu Search algorithm. These methods treat the cipher as a black box, with the objective of finding the session key. The primary innovation of our approach is the division of
[...] Read more.
This article presents general methodologies for plaintext attacks on block ciphers using the Tabu Search algorithm. These methods treat the cipher as a black box, with the objective of finding the session key. The primary innovation of our approach is the division of the key space into subsets based on a divisor, enabling the attack to focus on a specific portion of the total space. The following investigation demonstrates the successful application of these methods to a member of a block cipher family that includes the Advanced Encryption Standard (AES) cipher. One of the proposed methodologies, the subregions path attack, enables navigation of the key session space by applying specific predetermined strategies within these subregions.
Full article

Figure 1
Open AccessArticle
Autopotency and Conjugacy of Non-Diagonalizable Matrices for Challenge–Response Authentication
by
Daniel Alarcón-Narváez, Luis Adrián Lizama-Pérez and Fausto Abraham Jacques-García
Cryptography 2026, 10(1), 7; https://doi.org/10.3390/cryptography10010007 - 18 Jan 2026
Abstract
►▼
Show Figures
We present an algebraic framework for constructing challenge–response authentication protocols based on powers of non-diagonalizable matrices over finite fields. The construction relies on upper triangular Toeplitz matrices with a single Jordan block and on their structured power expansions, which induce nonlinear relations between
[...] Read more.
We present an algebraic framework for constructing challenge–response authentication protocols based on powers of non-diagonalizable matrices over finite fields. The construction relies on upper triangular Toeplitz matrices with a single Jordan block and on their structured power expansions, which induce nonlinear relations between matrix parameters and exponents through an autopotency phenomenon. The protocol is built from a cyclic family of matrix products derived from secret matrices
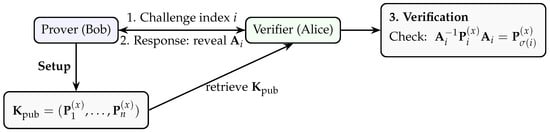
Figure 1
Open AccessArticle
Secure Implementation of RISC-V’s Scalar Cryptography Extension Set
by
Asmaa Kassimi, Abdullah Aljuffri, Christian Larmann, Said Hamdioui and Mottaqiallah Taouil
Cryptography 2026, 10(1), 6; https://doi.org/10.3390/cryptography10010006 - 17 Jan 2026
Abstract
Instruction Set Architecture (ISA) extensions, particularly scalar cryptography extensions (Zk), combine the performance advantages of hardware with the adaptability of software, enabling the direct and efficient execution of cryptographic functions within the processor pipeline. This integration eliminates the need to communicate with external
[...] Read more.
Instruction Set Architecture (ISA) extensions, particularly scalar cryptography extensions (Zk), combine the performance advantages of hardware with the adaptability of software, enabling the direct and efficient execution of cryptographic functions within the processor pipeline. This integration eliminates the need to communicate with external cores, substantially reducing latency, power consumption, and hardware overhead, making it especially suitable for embedded systems with constrained resources. However, current scalar cryptography extension implementations remain vulnerable to physical threats, notably power side-channel attacks (PSCAs). These attacks allow adversaries to extract confidential information, such as secret keys, by analyzing the power consumption patterns of the hardware during operation. This paper presents an optimized and secure implementation of the RISC-V scalar Advanced Encryption Standard (AES) extension (Zkne/Zknd) using Domain-Oriented Masking (DOM) to mitigate first-order PSCAs. Our approach features optimized assembly implementations for partial rounds and key scheduling alongside pipeline-aware microarchitecture optimizations. We evaluated the security and performance of the proposed design using the Xilinx Artix7 FPGA platform. The results indicate that our design is side-channel-resistant while adding a very low area overhead of 0.39% to the full 32-bit CV32E40S RISC-V processor. Moreover, the performance overhead is zero when the extension-related instructions are properly scheduled.
Full article
(This article belongs to the Topic Recent Advances in Security, Privacy, and Trust)
►▼
Show Figures
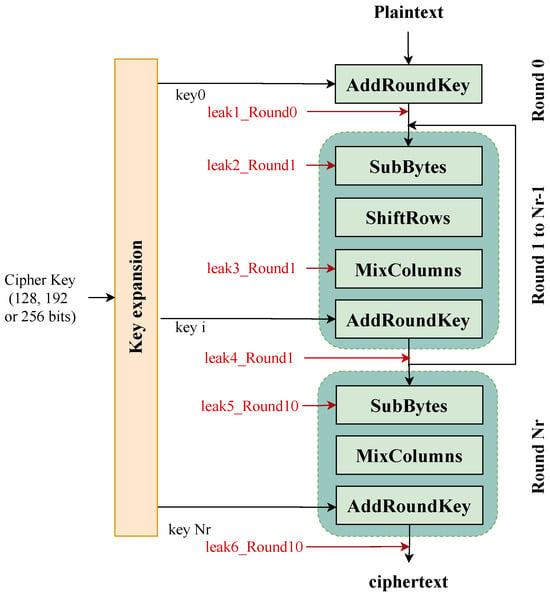
Figure 1
Open AccessFeature PaperArticle
Lower Bound on the Overlattice-Based Sieve Algorithm
by
Tongchen Shen, Xiangxue Li and Licheng Wang
Cryptography 2026, 10(1), 5; https://doi.org/10.3390/cryptography10010005 - 1 Jan 2026
Cited by 1
Abstract
►▼
Show Figures
Lattice-based cryptography stands as one of the most pivotal candidates in post-quantum cryptography. To configure the parameters of lattice-based cryptographic schemes, a thorough comprehension of their concrete security is indispensable. Lattice sieving algorithms represent among the most critical tools for conducting concrete security
[...] Read more.
Lattice-based cryptography stands as one of the most pivotal candidates in post-quantum cryptography. To configure the parameters of lattice-based cryptographic schemes, a thorough comprehension of their concrete security is indispensable. Lattice sieving algorithms represent among the most critical tools for conducting concrete security analysis. Currently, the state-of-the-art BDGL-sieve (SODA 2016) achieves a time complexity of

Figure 1
Open AccessArticle
Unbreakable QR Code Watermarks: A High-Robustness Technique for Digital Image Security Using DWT, SVD, and Schur Factorization
by
Bashar Suhail Khassawneh, Issa AL-Aiash, Mahmoud AlJamal, Omar Aljamal, Latifa Abdullah Almusfar, Bashair Faisal AlThani and Waad Aldossary
Cryptography 2026, 10(1), 4; https://doi.org/10.3390/cryptography10010004 - 30 Dec 2025
Abstract
In the digital era, protecting the integrity and ownership of digital content is increasingly crucial, particularly against unauthorized copying and tampering. Traditional watermarking techniques often struggle to remain robust under various image manipulations, leading to a need for more resilient methods. To address
[...] Read more.
In the digital era, protecting the integrity and ownership of digital content is increasingly crucial, particularly against unauthorized copying and tampering. Traditional watermarking techniques often struggle to remain robust under various image manipulations, leading to a need for more resilient methods. To address this challenge, we propose a novel watermarking technique that integrates the Discrete Wavelet Transform (DWT), Singular Value Decomposition (SVD), and Schur matrix factorization to embed a QR code as a watermark into digital images. Our method was rigorously tested across a range of common image attacks, including histogram equalization, salt-and-pepper noise, ripple distortions, smoothing, and extensive cropping. The results demonstrate that our approach significantly outperforms existing methods, achieving high normalized correlation (NC) values such as 0.9949 for histogram equalization, 0.9846 for salt-and-pepper noise (2%), 0.96063 for ripple distortion, 0.9670 for smoothing, and up to 0.9995 under 50% cropping. The watermark consistently maintained its integrity and scannability under all tested conditions, making our method a reliable solution for enhancing digital copyright protection.
Full article
(This article belongs to the Special Issue Advanced Techniques in Watermarking, Encryption and Steganography for Secure Communication)
►▼
Show Figures

Figure 1
Highly Accessed Articles
Latest Books
E-Mail Alert
News
Topics
Topic in
Applied Sciences, Cryptography, Mathematics, Symmetry, AI
Challenges and Solutions in Large Language Models
Topic Editors: Debiao He, Hu XiongDeadline: 30 June 2026
Topic in
Applied Sciences, Cryptography, Electronics, Mathematics, Information, Sci, Entropy, JCP
Recent Developments and Applications of Image Watermarking
Topic Editors: Frederic Ros, Pedro M. B. TorresDeadline: 31 July 2026
Topic in
AI, Future Internet, Micromachines, Symmetry, Cryptography
Cybersecurity Symmetry: Encryption, AI, and Attack Patterns
Topic Editors: Mobyen Uddin Ahmed, Azidine GuezzazDeadline: 31 March 2027
Topic in
Mathematics, Symmetry, Algorithms, Cryptography, IoT, Digital, Quantum Reports
Future-Proofing Digital Trust: From Classical to Quantum-Safe Security
Topic Editors: Saqib Ali, Raja Waseem AnwarDeadline: 30 April 2027

Special Issues
Special Issue in
Cryptography
Emerging Cryptographic Techniques in Watermarking and Steganography for Secure Communication and Privacy
Guest Editors: Mhamed Sayyouri, Mohamed Amine TahiriDeadline: 10 April 2026
Special Issue in
Cryptography
Information Security and Privacy—ACISP 2025
Guest Editors: Yudi Zhang, Zhen Zhao, Fuchun Guo, Josef PieprzykDeadline: 30 April 2026
Special Issue in
Cryptography
Advances in Privacy, Security, and Trust: Cryptographic Perspectives from PST2025
Guest Editors: Rongxing Lu, Ali GhorbaniDeadline: 30 April 2026
Special Issue in
Cryptography
Information and Communications Security—ICICS 2025
Guest Editors: Wanpeng Li, Rang Zhou, Jinguang HanDeadline: 30 April 2026









