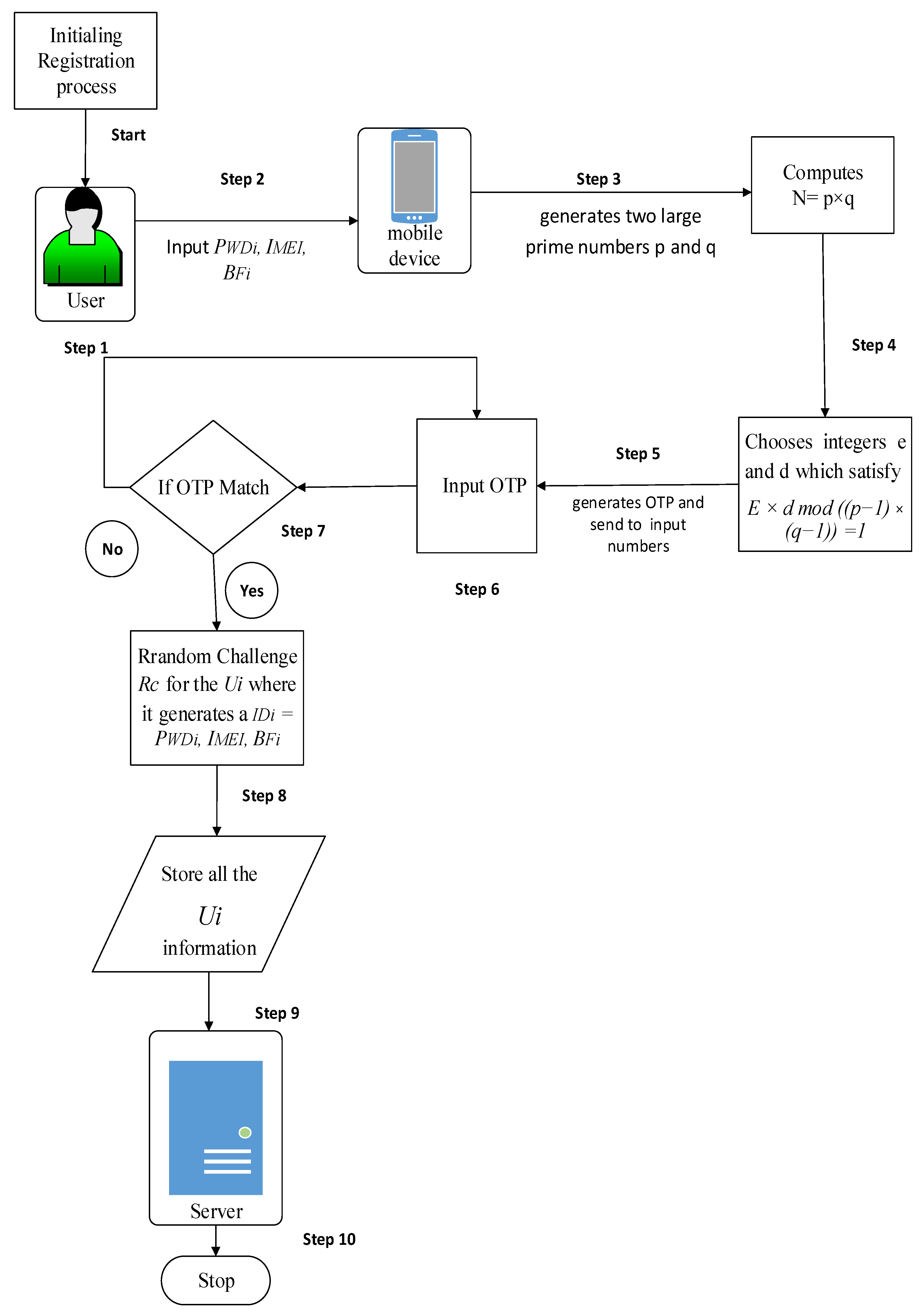
Figure 1.
The framework for the proposed technique.
Figure 1.
The framework for the proposed technique.
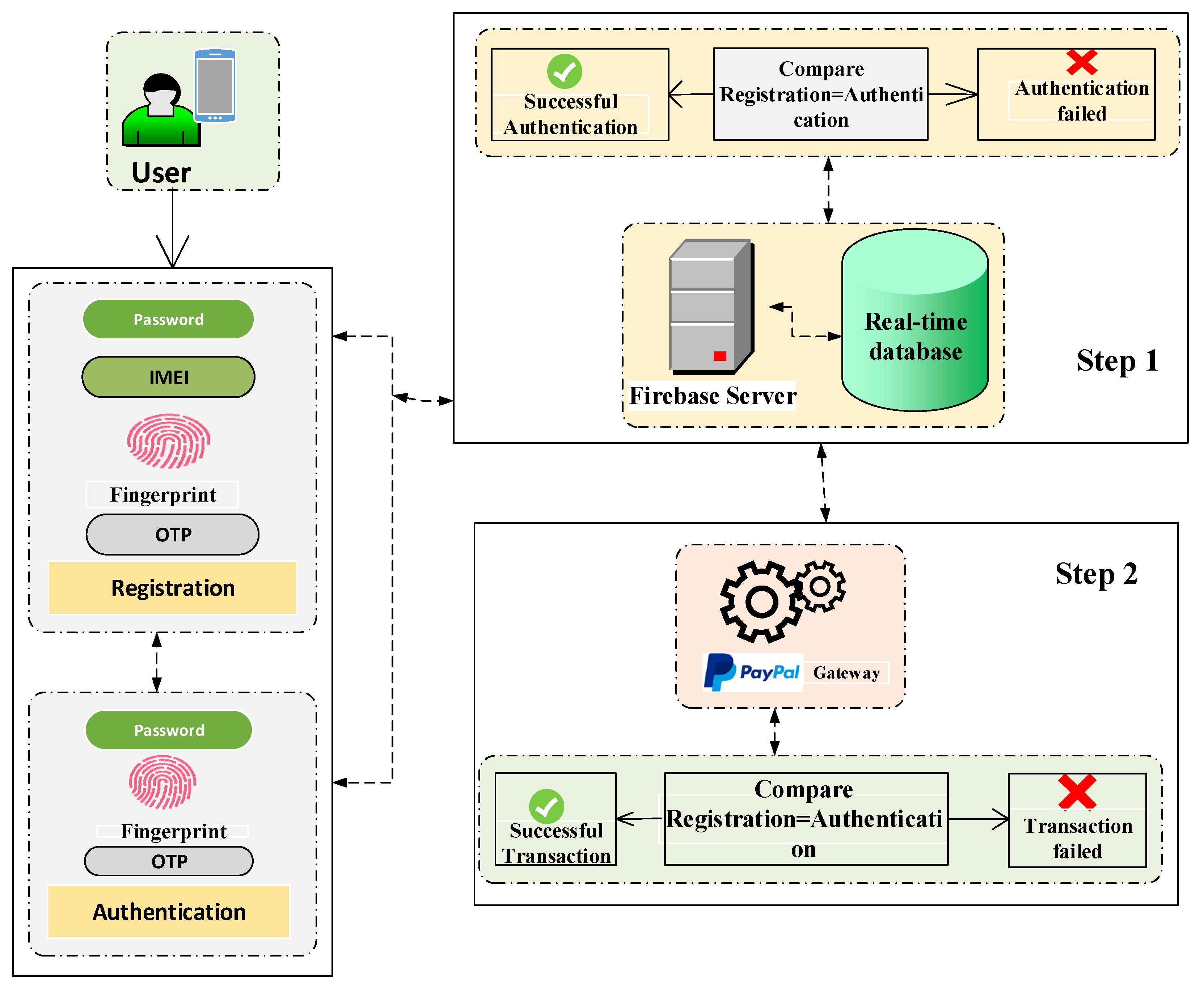
Figure 4.
Component diagram of the proposed method.
Figure 4.
Component diagram of the proposed method.
Figure 5.
Class diagram of the entire proposed method.
Figure 5.
Class diagram of the entire proposed method.
Figure 6.
(a): Register activity of proposed method and (b): Register OTP activity of proposed method. In (a), Step 1.1: The RegisterActivity will hide the keyboard in the CommonUtil (where util functions are stored) and return a message to the RegisterActivity. Step 1.2: The EncrptData function is the process in RsaAlgorithmUtil, which waits for the user input data to process the message. Step 1.2.1: The user input data encrypts into RsaUtil. Step 1.2.1.1: Then, user input data encrypt using RSA string to public key in RSAUtil and send return message from the RsaAlgorithmUtil to RegisterActivity. Step 1.3: Finally, the register activity sends a message to the UserModel to create an account and wait for the RegisterActivity to respond. In (b), Step 1.1: The RegisterOtpActivity will hide the keyboard in the CommonUtil and return a message to the RegisterOtpActivity. Step 1.2: The verifyOtp code starts, ends with RegisterOtpActivity, and waits for the response. Step 1.2.1: Once OTP is verified, the onComplete function then waits for the anonymous (where Utils functions are stored) response to process the request. Step 1.2.1.1: Anonymous responds to the RegisterOtpActivity request and confirms that sing up has been successful. Step 1.2.1.1.1: Then, RegisterOtpActivity sends request ondataChange (real-time database) to anonymous. Step 1.2.1.1.1.1: The onDataChange function starts and ends with the same lifeline (i.e., anonymous). Step 1.2.1.1.1.1.1: Then, anonymous sends a request to the UserModel to create a user profile in the real-time database. Step 1.2.1.1.1.1.2: UserModel sends response to the anonymous onComplete response. Step 1.2.1.1.1.1.2.1: Then, anonymous sends a response to the RegisterOtpActivity for successful registration.
Figure 6.
(a): Register activity of proposed method and (b): Register OTP activity of proposed method. In (a), Step 1.1: The RegisterActivity will hide the keyboard in the CommonUtil (where util functions are stored) and return a message to the RegisterActivity. Step 1.2: The EncrptData function is the process in RsaAlgorithmUtil, which waits for the user input data to process the message. Step 1.2.1: The user input data encrypts into RsaUtil. Step 1.2.1.1: Then, user input data encrypt using RSA string to public key in RSAUtil and send return message from the RsaAlgorithmUtil to RegisterActivity. Step 1.3: Finally, the register activity sends a message to the UserModel to create an account and wait for the RegisterActivity to respond. In (b), Step 1.1: The RegisterOtpActivity will hide the keyboard in the CommonUtil and return a message to the RegisterOtpActivity. Step 1.2: The verifyOtp code starts, ends with RegisterOtpActivity, and waits for the response. Step 1.2.1: Once OTP is verified, the onComplete function then waits for the anonymous (where Utils functions are stored) response to process the request. Step 1.2.1.1: Anonymous responds to the RegisterOtpActivity request and confirms that sing up has been successful. Step 1.2.1.1.1: Then, RegisterOtpActivity sends request ondataChange (real-time database) to anonymous. Step 1.2.1.1.1.1: The onDataChange function starts and ends with the same lifeline (i.e., anonymous). Step 1.2.1.1.1.1.1: Then, anonymous sends a request to the UserModel to create a user profile in the real-time database. Step 1.2.1.1.1.1.2: UserModel sends response to the anonymous onComplete response. Step 1.2.1.1.1.1.2.1: Then, anonymous sends a response to the RegisterOtpActivity for successful registration.
![Electronics 11 00004 g006a Electronics 11 00004 g006a]()
![Electronics 11 00004 g006b Electronics 11 00004 g006b]()
Figure 7.
(a): Login activity of proposed method and (b): Login OTP activity of proposed method. In (a), Step 1.1: The LoginActivity will hide the keyboard in the CommonUtil and return to the LoginActivity. Step 1.2: The signing starts and ends with LoginActivity and waits for the response. Step 1.2.1: Then, loginactivity sends a request onDataChange to anonymous. Step 1.2.1.1: Then, anonymous sent a request to decrytData into the RsaAlgorithmUtil. Step 1.2.1.1.1: User input data decrypt and sent to the RsaUtil. Step 1.2.1.1.1.1: Then, user input data decrypt using RSA string to private key in RSAUtil and send a return message to the RsaAlgorithmUtil to anonymous. Step 1.2.1.2: Then, anonymous sends a response to the LoginActivity and goes to the login page. Step 1.2.1.3: Finally, LoginActivity onCancelled. In (b), Step 1.1: The LoginOtpActivity will hide the keyboard in the CommonUtil and return to the LoginOtpActivity. Step 1.2: The verifyOtp code starts and ends with LoginOtpActivity and waits for the response. Step 1.2.1: Once OTP is verified, then the onComplete function waits for the anonymous response to process the request. Step 1.2.1.1: anonymous responds to the LoginOtpActivity and goes to the DashboardPage.
Figure 7.
(a): Login activity of proposed method and (b): Login OTP activity of proposed method. In (a), Step 1.1: The LoginActivity will hide the keyboard in the CommonUtil and return to the LoginActivity. Step 1.2: The signing starts and ends with LoginActivity and waits for the response. Step 1.2.1: Then, loginactivity sends a request onDataChange to anonymous. Step 1.2.1.1: Then, anonymous sent a request to decrytData into the RsaAlgorithmUtil. Step 1.2.1.1.1: User input data decrypt and sent to the RsaUtil. Step 1.2.1.1.1.1: Then, user input data decrypt using RSA string to private key in RSAUtil and send a return message to the RsaAlgorithmUtil to anonymous. Step 1.2.1.2: Then, anonymous sends a response to the LoginActivity and goes to the login page. Step 1.2.1.3: Finally, LoginActivity onCancelled. In (b), Step 1.1: The LoginOtpActivity will hide the keyboard in the CommonUtil and return to the LoginOtpActivity. Step 1.2: The verifyOtp code starts and ends with LoginOtpActivity and waits for the response. Step 1.2.1: Once OTP is verified, then the onComplete function waits for the anonymous response to process the request. Step 1.2.1.1: anonymous responds to the LoginOtpActivity and goes to the DashboardPage.
![Electronics 11 00004 g007 Electronics 11 00004 g007]()
Figure 8.
(a): Authentication activity of proposed method, (b): Authentication OTP activity of proposed method, and (c): Authentication successful activity of proposed method. In (a), Step 1.1: The AuthenticateActivity will hide the keyboard in the CommonUtil and return to the AuthenticateActivity. Step 1.2: AuthenticateActivity sends a message to the AuthenticationModel to create an account and waits for AuthenticateActivity to respond. Step 1.3: Finally, AuthenticationModel creates and sends a response to AuthenticateActivity. In (b), Step 1.1: The AuthenticateOtpActivity will hide the keyboard in the CommonUtil and return a message to the AuthenticateOtpActivity. Step 1.2: The verifyOtp code starts, ends with AuthenticateOtpActivity, and waits for the response. Step 1.2.1: Once OTP is verified, the onComplete function waits for anonymous response to process the request. Step 1.2.1.1: Anonymous sends a response to AuthUserData and sends it back to the AuthenticateOtpActivity. Step 1.2.1.1.1: Then, AuthenticateOtpActivity sends a request ondataChange to anonymous. Step 1.2.1.1.1.1: Then, anonymous sends a request to decrytData into the RsaAlgorithmUtil. Step 1.2.1.1.1.1.1: User input data decrypted and sent to the RsaUtil. Step 1.2.1.1.1.1.1.1: Then, user input data decrypted using RSA string to private key in RSAUtil and sends a return message to the RsaAlgorithmUtil to anonymous. Step 1.2.1.1.1.2: Then, anonymous sends a response to the AuthenticateOtpActivity and goes to the SuccessPage. Step 1.2.1.1.1.3: Once AuthenticateOtpActivity succeeds, the request sent to the PaymentGateway. Step 1.2.1.1.1.4: Finally, AuthenticateOtpActivity onCancelled. In (c), Step 1.1: The UpdateTransactionDb will start and return a message to the AuthenticateSuccessActivity. Step 1.1.1: The AuthenticateSuccessActivity creates an amount in the TransactionModel and sends it back to the AuthenticateSuccessActivity. Step 1.1.2: The updateDbBalance starts and ends with AuthenticateSuccessActivity and waits for the response. Step 1.1.2.1: Then, AuthenticateSuccessActivity sends a request ondataChange to anonymous. Step 1.1.2.1.1: Then, onCancelled starts and ends with anonymous and sends a request to the AuthenticateSuccessActivity. Step 1.1.3: The AuthenticateSuccessActivity creates an amount in the TransactionModel and sends it back to the AuthenticateSuccessActivity. Step 1.1.4: The updateDbBalance starts and ends with, AuthenticateSuccessActivity and waits for the response. Step 1.1.4.1: Then, AuthenticateSuccessActivity sends a request ondataChange to anonymous. Step 1.1.4.1.1: Then, onCancelled starts and ends with anonymous and sends a request to the AuthenticateSuccessActivity. Step 1.1.5: Then, onComplete request sent to anonymous. Step 1.1.5.1: Then, anonymous sends UpdateOtherUserBalance to the AuthenticateSuccessActivity. The next steps process the same flow.
Figure 8.
(a): Authentication activity of proposed method, (b): Authentication OTP activity of proposed method, and (c): Authentication successful activity of proposed method. In (a), Step 1.1: The AuthenticateActivity will hide the keyboard in the CommonUtil and return to the AuthenticateActivity. Step 1.2: AuthenticateActivity sends a message to the AuthenticationModel to create an account and waits for AuthenticateActivity to respond. Step 1.3: Finally, AuthenticationModel creates and sends a response to AuthenticateActivity. In (b), Step 1.1: The AuthenticateOtpActivity will hide the keyboard in the CommonUtil and return a message to the AuthenticateOtpActivity. Step 1.2: The verifyOtp code starts, ends with AuthenticateOtpActivity, and waits for the response. Step 1.2.1: Once OTP is verified, the onComplete function waits for anonymous response to process the request. Step 1.2.1.1: Anonymous sends a response to AuthUserData and sends it back to the AuthenticateOtpActivity. Step 1.2.1.1.1: Then, AuthenticateOtpActivity sends a request ondataChange to anonymous. Step 1.2.1.1.1.1: Then, anonymous sends a request to decrytData into the RsaAlgorithmUtil. Step 1.2.1.1.1.1.1: User input data decrypted and sent to the RsaUtil. Step 1.2.1.1.1.1.1.1: Then, user input data decrypted using RSA string to private key in RSAUtil and sends a return message to the RsaAlgorithmUtil to anonymous. Step 1.2.1.1.1.2: Then, anonymous sends a response to the AuthenticateOtpActivity and goes to the SuccessPage. Step 1.2.1.1.1.3: Once AuthenticateOtpActivity succeeds, the request sent to the PaymentGateway. Step 1.2.1.1.1.4: Finally, AuthenticateOtpActivity onCancelled. In (c), Step 1.1: The UpdateTransactionDb will start and return a message to the AuthenticateSuccessActivity. Step 1.1.1: The AuthenticateSuccessActivity creates an amount in the TransactionModel and sends it back to the AuthenticateSuccessActivity. Step 1.1.2: The updateDbBalance starts and ends with AuthenticateSuccessActivity and waits for the response. Step 1.1.2.1: Then, AuthenticateSuccessActivity sends a request ondataChange to anonymous. Step 1.1.2.1.1: Then, onCancelled starts and ends with anonymous and sends a request to the AuthenticateSuccessActivity. Step 1.1.3: The AuthenticateSuccessActivity creates an amount in the TransactionModel and sends it back to the AuthenticateSuccessActivity. Step 1.1.4: The updateDbBalance starts and ends with, AuthenticateSuccessActivity and waits for the response. Step 1.1.4.1: Then, AuthenticateSuccessActivity sends a request ondataChange to anonymous. Step 1.1.4.1.1: Then, onCancelled starts and ends with anonymous and sends a request to the AuthenticateSuccessActivity. Step 1.1.5: Then, onComplete request sent to anonymous. Step 1.1.5.1: Then, anonymous sends UpdateOtherUserBalance to the AuthenticateSuccessActivity. The next steps process the same flow.
Figure 9.
Top-up money activity of proposed method. Step 1.1: The InitSpinner will start and return a message to the TopUpMoneyActivity. Step 1.1.1: The TopUpMoneyActivity sends request BankListData to the DataUtil and waits for the response. Step 1.1.2: The TopUpMoneyActivity sends request OnItemSelect to anonymous and waits for the response. Step 1.1.2.1: Anonymous sends the response loadMoney to the TopUpMoneyActivity and waits for the request. Step 1.1.2.1.1: The TopUpMoneyActivity creates an amount in the AuthenticationModel and sends it back to the TopUpMoneyActivity.
Figure 9.
Top-up money activity of proposed method. Step 1.1: The InitSpinner will start and return a message to the TopUpMoneyActivity. Step 1.1.1: The TopUpMoneyActivity sends request BankListData to the DataUtil and waits for the response. Step 1.1.2: The TopUpMoneyActivity sends request OnItemSelect to anonymous and waits for the response. Step 1.1.2.1: Anonymous sends the response loadMoney to the TopUpMoneyActivity and waits for the request. Step 1.1.2.1.1: The TopUpMoneyActivity creates an amount in the AuthenticationModel and sends it back to the TopUpMoneyActivity.
Figure 10.
Transfer money activity of proposed method. Step 1.1: The TransferMoneyActivity sends request getProfileDetails to the DataUtil and waits for the response. Step 1.1.1: The DataUtil sends a request onDataChange to anonymous and waits for the response. Step 1.1.1.1: Anonymous sends a request onDataProfileDetails to the UserDetailscallback and sends the response to anonymous. Step 1.2: The InitAmmountList will start and return a message to the TransferMoneyActivity. Step 1.2.1: The TransferMoneyActivity sends request AmountData to the DataUnit and waits for the response. Step 1.2.1.1: The DataUtil creates an amount in the TransferMoneyModel and sends it back to the DataUtil. Step 1.2.2: The TransferMoneyActivity sends a request onViewEvent to anonymous and waits for the response. Step 1.2.2.1: The anonymous request created in the TransferMoneyModel is sent back to anonymous and waits for the response.
Figure 10.
Transfer money activity of proposed method. Step 1.1: The TransferMoneyActivity sends request getProfileDetails to the DataUtil and waits for the response. Step 1.1.1: The DataUtil sends a request onDataChange to anonymous and waits for the response. Step 1.1.1.1: Anonymous sends a request onDataProfileDetails to the UserDetailscallback and sends the response to anonymous. Step 1.2: The InitAmmountList will start and return a message to the TransferMoneyActivity. Step 1.2.1: The TransferMoneyActivity sends request AmountData to the DataUnit and waits for the response. Step 1.2.1.1: The DataUtil creates an amount in the TransferMoneyModel and sends it back to the DataUtil. Step 1.2.2: The TransferMoneyActivity sends a request onViewEvent to anonymous and waits for the response. Step 1.2.2.1: The anonymous request created in the TransferMoneyModel is sent back to anonymous and waits for the response.
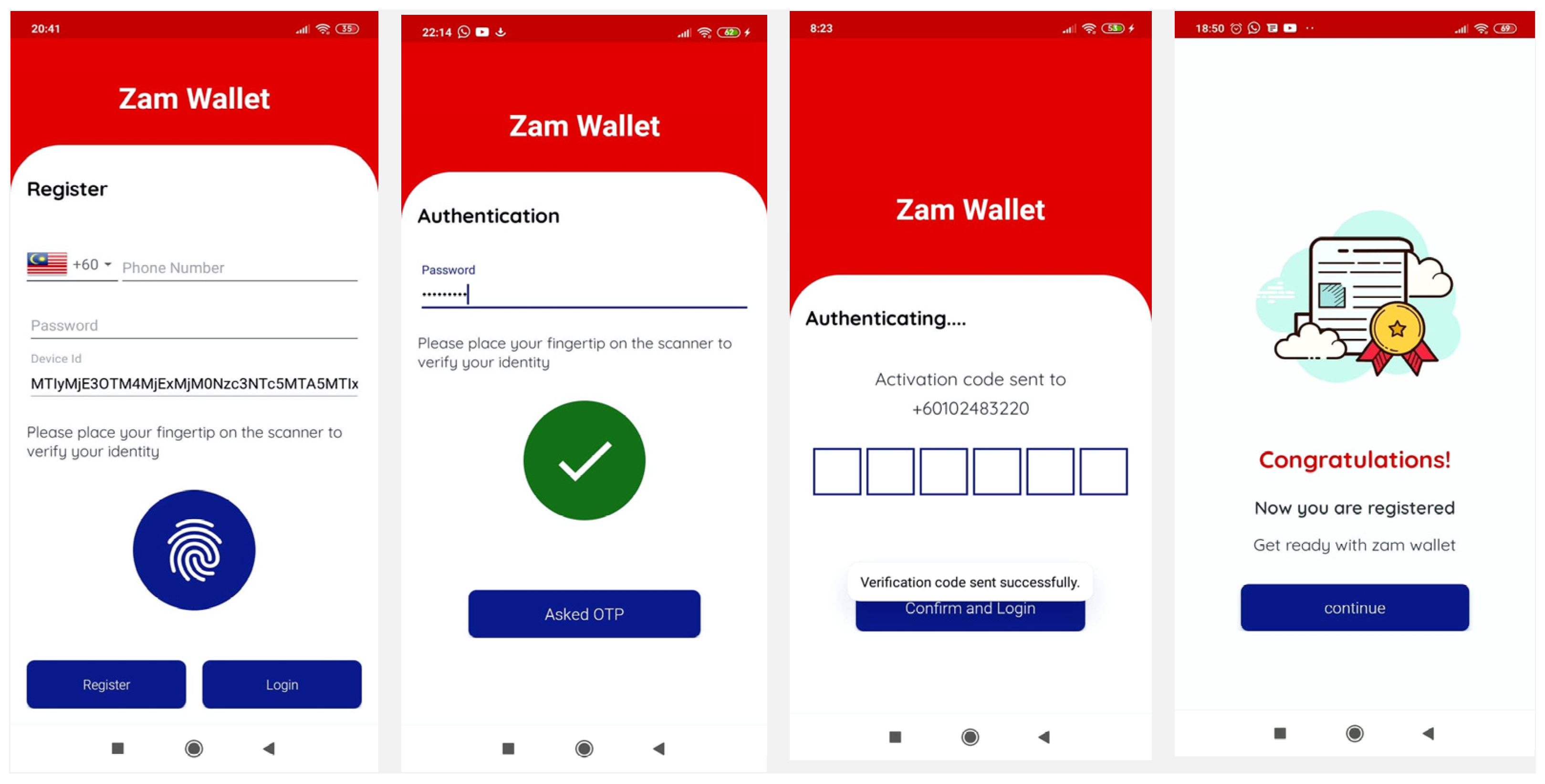
Figure 11.
Registration activity proposed method.
Figure 11.
Registration activity proposed method.
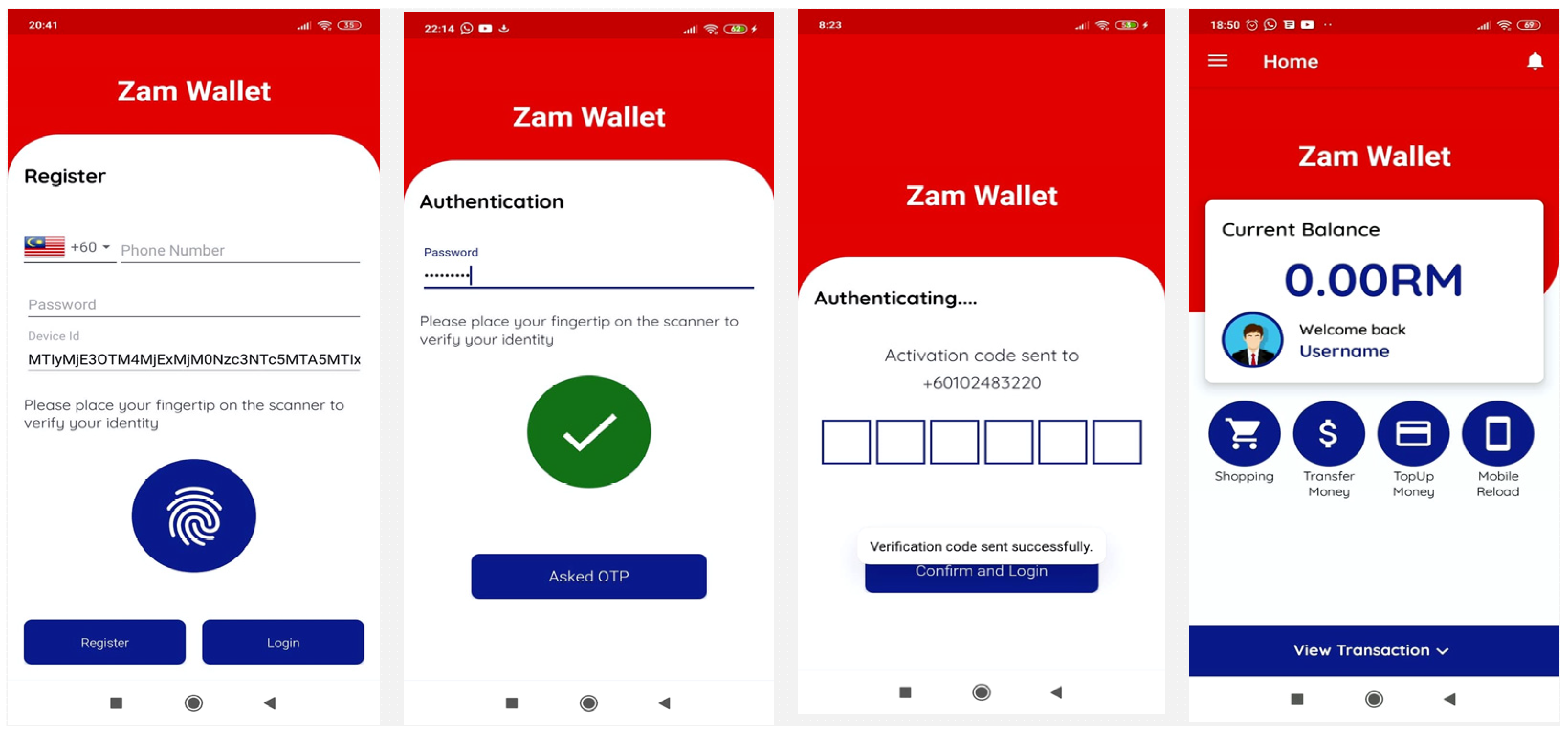
Figure 12.
Login process of Zamwallet.
Figure 12.
Login process of Zamwallet.
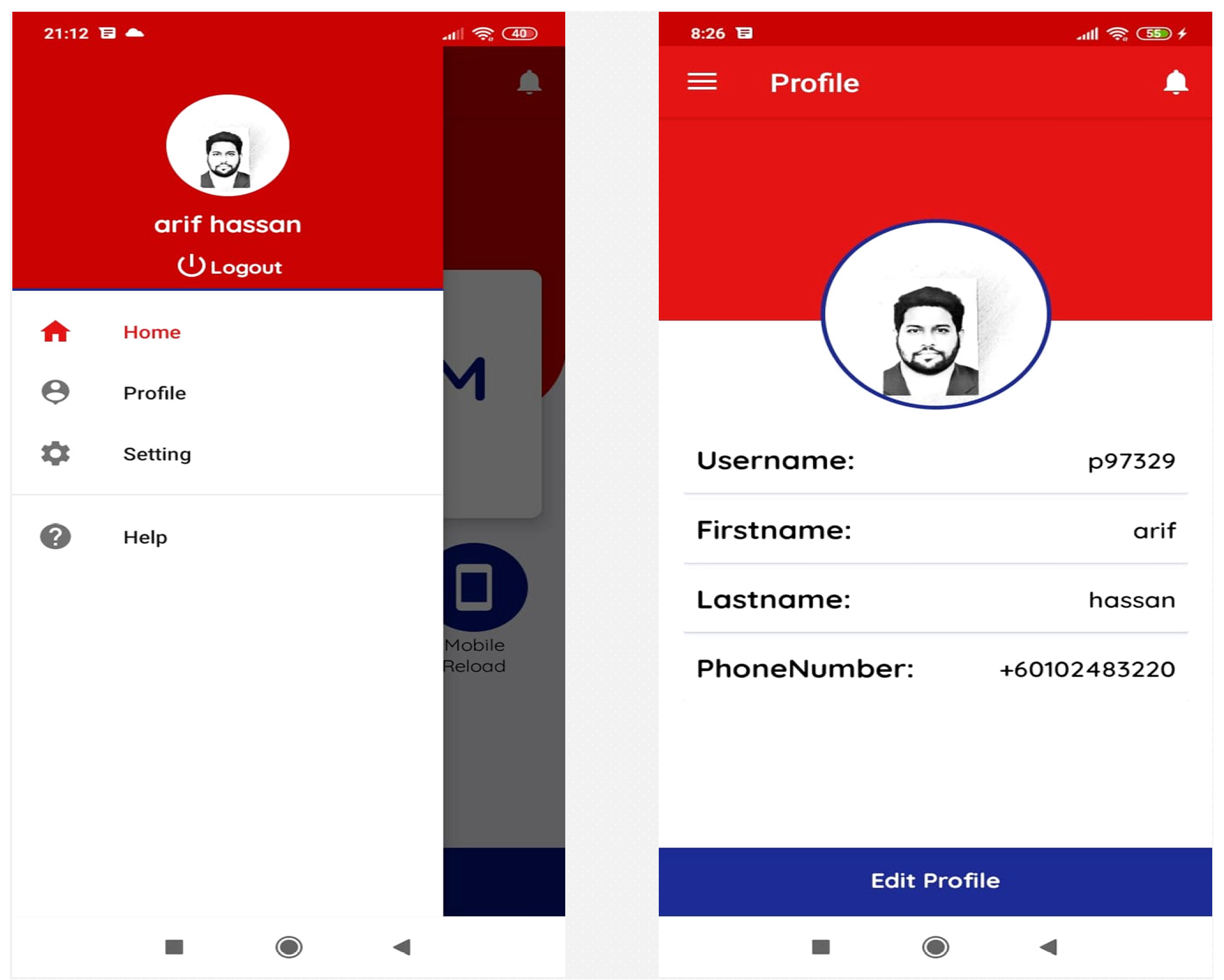
Figure 13.
Profile page and dashboard activity of Zamwallet.
Figure 13.
Profile page and dashboard activity of Zamwallet.
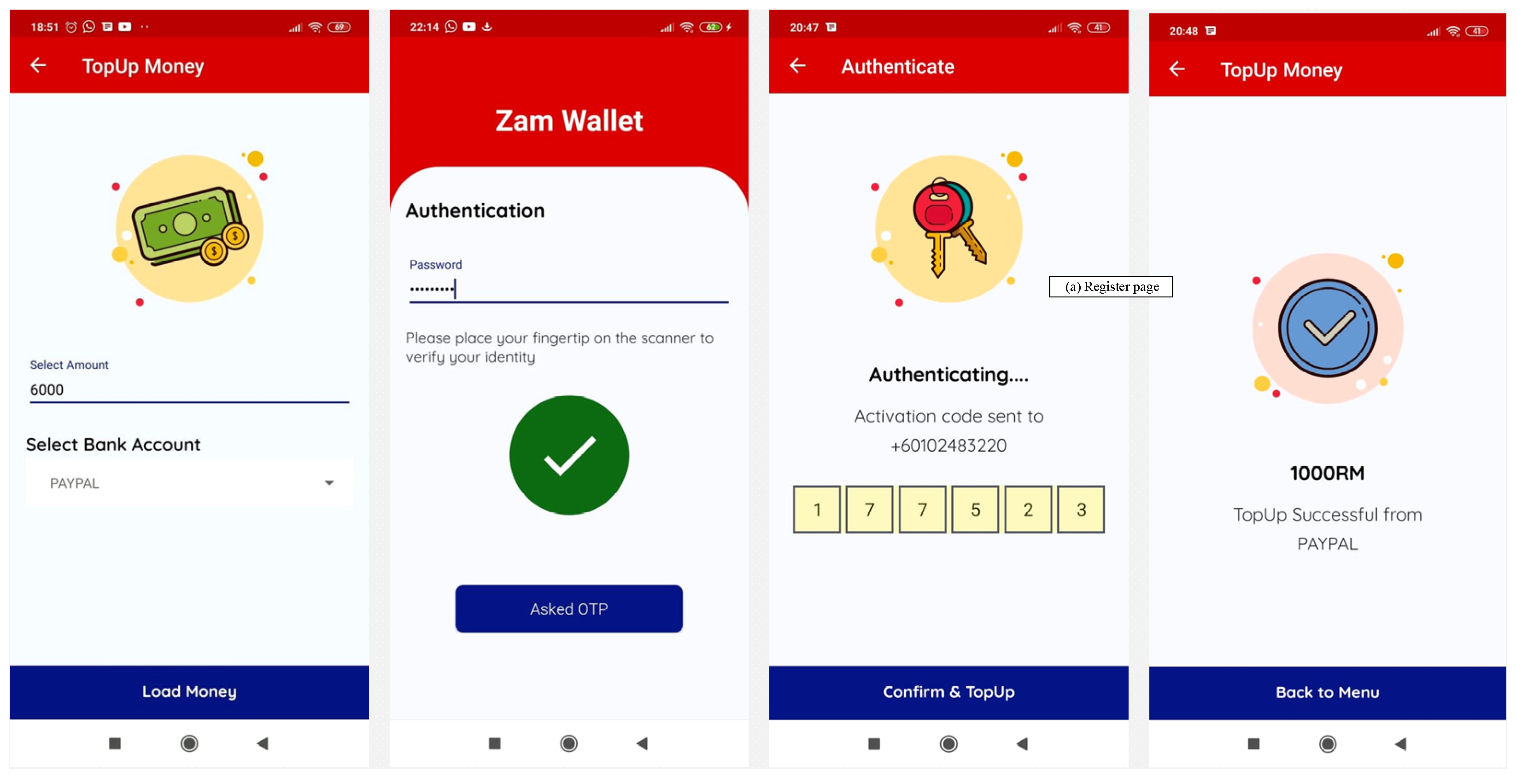
Figure 14.
Top-up money activity in Zamwallet.
Figure 14.
Top-up money activity in Zamwallet.
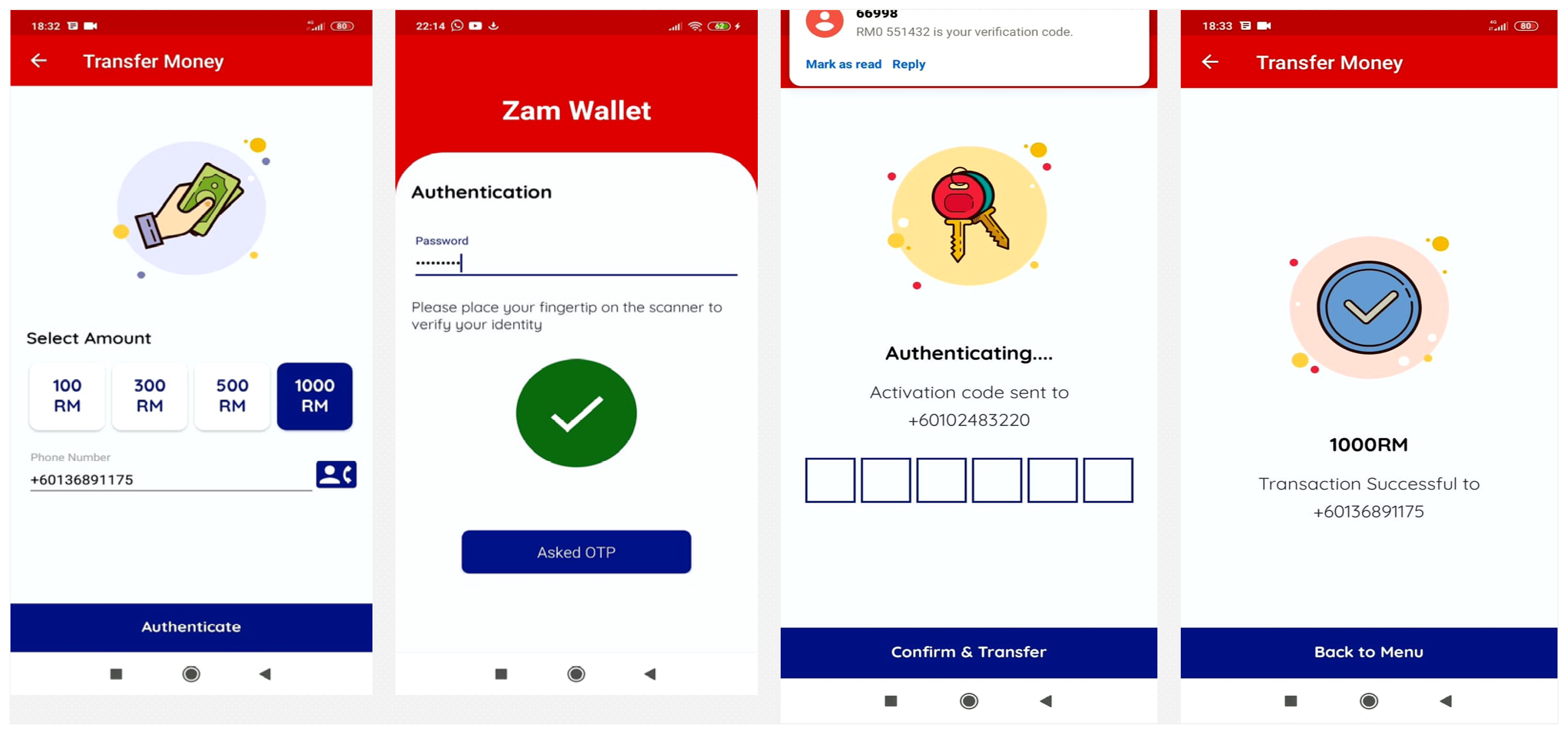
Figure 15.
Money transfer activity in Zamwallet.
Figure 15.
Money transfer activity in Zamwallet.
Figure 16.
View transaction activity of Zamwallet.
Figure 16.
View transaction activity of Zamwallet.
Figure 17.
Overview of real-time database activities. (a): User information on Firebase database and (b): user transaction details on Firebase database.
Figure 17.
Overview of real-time database activities. (a): User information on Firebase database and (b): user transaction details on Firebase database.
Figure 18.
Screenshot of performance of Zamwallet.
Figure 18.
Screenshot of performance of Zamwallet.
Figure 19.
Screenshot of the overview of Zamwallet in the real-time database.
Figure 19.
Screenshot of the overview of Zamwallet in the real-time database.
Table 1.
Work related to e-wallets.
Table 1.
Work related to e-wallets.
| Authors | Methods and Models | Technical Feature | Finding/Weakness | Evaluation
Approach |
|---|
| [9] | Biometric authentication | | The prototype tries to ensure the captured fingerprint is consistent and the process is repeatable (usability). Facial recognition does not work well under poor conditions such as poor lighting | Likert-5, VeriFinger’s software development kit (SDK) |
| [11] | WinAuth/Google Authenticator | Fingerprints One time password
| Shared secrets—regular renewal to keep security due to deterministic function of storing password | Framework |
| [43] | Biometric authentication | | This study requires additional hardware | RSA |
| [45] | Biometric authentication | | Does not work well under poor conditions such as poor lighting | Framework |
| [46] | cryptographic algorithm | | Pattern lock is vulnerable to side-channel, smudge, and shoulder surfing attacks | Framework |
| [51] | Biometric Authentication | Username Password Fingerprint
| This study approach user ID, password, and fingerprint. In order to continue to grow, the security and the privacy aspects need to be improved | Android studio |
| [52] | Biometric authentication | | This study requires an extra device to authentication fingerprint. Costly and single elements | Public key cryptosystem |
| [53] | Biometric authentication | | Poor practicality, unable to distinguish iris colors by ethnic features, the issue of financial difficulty is thus high market price, and therefore, the decrease in general utility is difficult to miniaturize. Requires extra hardware | Mat lab |
Table 2.
List of the symbols used.
Table 2.
List of the symbols used.
| Notations | Description |
|---|
| Ui | User |
| IDi | Unique Identifier of User |
| PWDi | Password of the User |
| BFi | Biometric feature of User |
| IMEI | International Mobile Station Equipment Identity of user |
| d | Private key in RSA |
| e | Public key in RSA |
| n | Computed as product of chosen prime numbers (p and q) |
| RC | Random Challenge (in this context—One Time Password) |
| CS | Concatenated String (Ui) |
| ESQ | Encrypted String |
| PKP | Plain Private Key |
| PKE | Encrypted Private Key |
| E (Data, Encryption Key) | Encryption Function |
| RF | Result of Comparison Function (PWDi, IMEI, BFi) |
| D (Data, Encryption Key) | Decryption Function |
Table 3.
The OTP results of the Redmi user.
Table 3.
The OTP results of the Redmi user.
| User 1-Redmi | No | OTP | Status |
| 1 | 984913 | Successful |
| 2 | 224264 | Successful |
| 3 | 845862 | Successful |
| 4 | 584132 | Successful |
| 5 | 112617 | Successful |
| 6 | 248980 | Successful |
Table 4.
The OTP results of the Vivo user.
Table 4.
The OTP results of the Vivo user.
| User 2- Vivo | No | OTP | Status |
| 1 | 884713 | Successful |
| 2 | 639264 | Successful |
| 3 | 389202 | Successful |
| 4 | 184033 | Successful |
| 5 | 714668 | Successful |
| 6 | 297947 | Successful |
Table 5.
The OTP results of the Neffos user.
Table 5.
The OTP results of the Neffos user.
| User 3-Neffos | No | OTP | Status |
| 1 | 232975 | Successful |
| 2 | 638645 | Successful |
| 3 | 800352 | Successful |
| 4 | 492469 | Successful |
| 5 | 985624 | Successful |
| 6 | 382478 | Successful |
Table 6.
Top-up transaction results.
Table 6.
Top-up transaction results.
| Currency MYR | Transaction ID | Item Title | Status |
|---|
| 5000 | 3YC06329A41446107 | Top-up | Completed |
| 300 | 4JM153463M403735T | Top-up | Completed |
| 500 | 50B06205AB1105831 | Top-up | Completed |
| 1000 | 9UD61707CH4090247 | Top-up | Completed |
| 700 | 4SB80386FE0038111 | Top-up | Completed |
| 1000 | 16D61116V0923694H | Top-up | Completed |
| 100 | 50C8271251302894N | Top-up | Completed |
Table 7.
Money transaction results.
Table 7.
Money transaction results.
| Number | Currency MYR | Status |
|---|
| +60777888999 | 500 | Completed |
| +60777888999 | 300 | Completed |
| +60777888999 | 1000 | Completed |
| +60149635 *** | 300 | Completed |
| +60136891 *** | 1000 | Completed |
| +60136891 *** | 500 | Completed |
| +60136891 *** | 500 | Completed |
| +60136891 *** | 300 | Completed |
| +60136891 *** | 500 | Completed |
| +60136891 *** | 1000 | Completed |
| +60112126 *** | 500 | Completed |
Table 8.
Functionality test of Zamwallet.
Table 8.
Functionality test of Zamwallet.
| Test | Test Case | Result |
|---|
| Functionality | Registration | Passed |
| Authentication | Passed |
| Top-up | Passed |
| Transaction | Passed |
| Profile/View Transaction | Passed |
| Device Cloning prevention | Passed |
Table 9.
Comparison of authentication categories within the proposed scheme and existing scheme.
Table 9.
Comparison of authentication categories within the proposed scheme and existing scheme.
| Authors | Authentication Catagories | Total Point |
|---|
| Knowledge | Ownership | Biometrics | Device ID |
|---|
| U | Pas | Pi | Pat | O | S | H | Fi | Fa | I | IMEI | |
|---|
| Harish et al., 2019 | | | | | | 1 | | | 1 | | | 2 |
| Vengatesan et al., 2020 | | | 1 | | | 1 | | | | | | 2 |
| Benli et al., 2017 | | | 1 | | | | | | 1 | | | 2 |
| Okpara and Bekaroo, 2017 | | | | | | | | 1 | 1 | | | 2 |
| L. Sharma and Mathuria, 2018 | 1 | | 1 | | | | | | 1 | | | 3 |
| K. Tiwari, 2016 | | | | | | | | | 1 | | | 1 |
| Gupta et al., 2020 | | | | | | | | | | 1 | | 1 |
| Houngbo et al., 2019 | | | | | | | | | 1 | | | 1 |
| Proposed Zamwallet | | | 1 | | | 1 | | 1 | | | 1 | 4 |