Journal Description
Journal of Sensor and Actuator Networks
Journal of Sensor and Actuator Networks
is an international, peer-reviewed, open access journal on the science and technology of sensor and actuator networks, published bimonthly online by MDPI.
- Open Access— free for readers, with article processing charges (APC) paid by authors or their institutions.
- High Visibility: indexed within Scopus, ESCI (Web of Science), dblp, Inspec, and other databases.
- Journal Rank: JCR - Q2 (Computer Science, Information Systems) / CiteScore - Q1 (Control and Optimization)
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 23.6 days after submission; acceptance to publication is undertaken in 3.8 days (median values for papers published in this journal in the second half of 2025).
- Recognition of Reviewers: reviewers who provide timely, thorough peer-review reports receive vouchers entitling them to a discount on the APC of their next publication in any MDPI journal, in appreciation of the work done.
- Journal Clusters of Network and Communications Technology: Future Internet, IoT, Telecom, Journal of Sensor and Actuator Networks, Network, Signals.
Impact Factor:
4.2 (2024);
5-Year Impact Factor:
3.7 (2024)
Latest Articles
UGV Path Optimization in UAV-Assisted Environments Using Visibility-Aware Path Simplification
J. Sens. Actuator Netw. 2026, 15(3), 41; https://doi.org/10.3390/jsan15030041 - 22 May 2026
Abstract
This study proposes a modular path optimization framework for uncrewed ground vehicles (UGVs) in uncrewed aerial vehicle (UAV)-assisted navigation environments to improve the efficiency, smoothness, and executability of paths generated by classical grid-based path planning algorithms. The principal innovation of this work is
[...] Read more.
This study proposes a modular path optimization framework for uncrewed ground vehicles (UGVs) in uncrewed aerial vehicle (UAV)-assisted navigation environments to improve the efficiency, smoothness, and executability of paths generated by classical grid-based path planning algorithms. The principal innovation of this work is the Visibility and Line-of-Sight Path Simplification (VLoSPS) algorithm, an algorithm-independent post-processing method that removes redundant waypoints through long-range axis-aligned visibility analysis while preserving path feasibility. VLoSPS is integrated with the Direction-Aware Path Planning Approach (DAPPA) to reduce angular deviations and improve directional continuity. The proposed framework is applicable to standard algorithms, including A*, Dijkstra, Breadth-First Search (BFS), and Depth-First Search (DFS), without modifying their internal search mechanisms. The main academic contributions comprise the formulation of a generalized post-processing architecture for UAV-derived occupancy maps, the introduction of a visibility-aware waypoint reduction strategy, and extensive validation using two synthetic maze datasets and three UAV-derived semantically segmented real-world datasets. On the Göttingen Maze Dataset, the VLoSPS and DAPPA pipeline reduced the average path lengths of A*, Dijkstra, BFS, and DFS by 5.42%, 9.46%, 10.44%, and 86.00%, respectively. The consistent improvements across real-world datasets demonstrate the effectiveness, computational feasibility, and general applicability of the proposed framework for UAV-assisted UGV path planning. The implementation code and benchmark resources developed in this study are publicly released to promote reproducibility and facilitate future research.
Full article
(This article belongs to the Special Issue Collaborative Integrated Sensing and Localization in Autonomous Systems)
►
Show Figures
Open AccessArticle
A Benchmark for Image Forgery Detection and Localization on Social Media Images
by
Md. Mehedi Rahman Rana, Md. Anisur Rahman, Kamrul Hasan Talukder, Syed Md. Galib and Nazmul Siddique
J. Sens. Actuator Netw. 2026, 15(3), 40; https://doi.org/10.3390/jsan15030040 - 19 May 2026
Abstract
The widespread manipulation of digital images on social media has significantly undermined public trust in visual content and created major challenges for automated forgery detection. These challenges are further intensified by platform-induced degradations such as compression, resizing, and filtering, which often obscure forensic
[...] Read more.
The widespread manipulation of digital images on social media has significantly undermined public trust in visual content and created major challenges for automated forgery detection. These challenges are further intensified by platform-induced degradations such as compression, resizing, and filtering, which often obscure forensic traces. This work develops FIDD-6000, a large-scale benchmark dataset for image forgery detection and localization, containing 6000 social media images, including 1000 authentic and 5000 manipulated samples, with pixel-level ground-truth masks annotated across three forgery categories, splicing, copy-move, and retouching, all created under realistic post-processing conditions. Each manipulated image is accompanied by a pixel-level ground-truth mask indicating the tampered regions. To assess the challenges posed by social media-based image manipulation, we evaluate 15 state-of-the-art image forgery localization methods on FIDD-6000, including approaches based on JPEG compression artifacts, sensor-noise analysis, and error level analysis. Experimental results show that these methods perform poorly on the proposed dataset, revealing their limited effectiveness in detecting forged images that have undergone social media-specific compression and transformation. This performance gap highlights the need for more robust and advanced machine learning and deep learning approaches capable of handling the complexity of modern image manipulations. Therefore, FIDD-6000 provides a valuable resource for researchers by offering a rigorous benchmark for developing, evaluating, and comparing next-generation forgery detection and localization methods.
Full article
(This article belongs to the Section Big Data, Computing and Artificial Intelligence)
►▼
Show Figures

Figure 1
Open AccessArticle
Evaluation of the Effectiveness of Distributed Antenna Systems for Improving Indoor Wireless Network Coverage
by
Kyrmyzy Taissariyeva, Zhuldyz Kalpeyeva, Yerlan Tashtay, Yermek Bekenov and Zhansaya Ayapbergen
J. Sens. Actuator Netw. 2026, 15(3), 39; https://doi.org/10.3390/jsan15030039 - 18 May 2026
Abstract
A pressing challenge of modern wireless networks is ensuring stable radio coverage inside buildings, where radio signal propagation is significantly complicated by the influence of building structures. Reinforced concrete walls, floor slabs, internal partitions, and energy-efficient windows with metallized coatings create substantial obstacles
[...] Read more.
A pressing challenge of modern wireless networks is ensuring stable radio coverage inside buildings, where radio signal propagation is significantly complicated by the influence of building structures. Reinforced concrete walls, floor slabs, internal partitions, and energy-efficient windows with metallized coatings create substantial obstacles to the propagation of electromagnetic waves, causing reflection, absorption, and scattering. As a result, areas with weakened coverage are formed inside buildings, leading to deterioration in mobile communication quality and reduced data transmission rates. This study presents an experimental investigation of the received signal strength of mobile operators inside a multi-storey residential complex. An analysis was conducted to evaluate the impact of building height, architectural features, and construction materials on radio signal propagation. In addition, the frequency bands used in 4G LTE and 5G networks by mobile operators were examined. It was found that LTE networks mainly operate in the 1.8–2.1 GHz frequency range, whereas 5G networks operate in the n77 band (3.6–3.7 GHz), which provides higher data throughput but is characterized by greater signal attenuation when propagating inside buildings. To address this issue, a Distributed Antenna System (DAS) based on GPON technology was implemented in the studied building. The placement of antenna equipment on the roof enabled the efficient reception of the signal from the base station and its subsequent distribution inside the building through an internal antenna network. The measurement results demonstrated that the deployment of a GPON-based DAS significantly improves the received signal level and ensures more uniform radio coverage inside indoor environments. The obtained results confirm that the use of distributed antenna systems is an effective solution for compensating signal losses caused by the shielding effect of building structures and can significantly improve the quality of mobile communications in dense urban environments. The results show that the RSRP level in indoor environments without DAS decreases to approximately −100 to −110 dBm, while after deployment of the GPON-based DAS, it improves to −45 to −75 dBm. This corresponds to a signal gain of up to 40–50 dB, ensuring stable connectivity and significantly improved data transmission performance.
Full article
(This article belongs to the Section Communications and Networking)
►▼
Show Figures

Figure 1
Open AccessReview
Fiber Bragg Grating-Based Deformation Monitoring in Space Infrastructure: A Comprehensive Review
by
Nurzhigit Smailov, Sauletbek Koshkinbayev, Kydyrali Yssyraiyl, Ainur Kuttybayeva, Gulbahar Yussupova, Askhat Batyrgaliyev and Akezhan Sabibolda
J. Sens. Actuator Netw. 2026, 15(3), 38; https://doi.org/10.3390/jsan15030038 - 15 May 2026
Abstract
►▼
Show Figures
The increasing complexity and extended operational lifetimes of modern space infrastructure have significantly intensified the demand for reliable structural health monitoring (SHM) systems. However, the extreme space environment, characterized by radiation exposure, microgravity, ultra-high vacuum, and severe thermal cycling, imposes critical limitations on
[...] Read more.
The increasing complexity and extended operational lifetimes of modern space infrastructure have significantly intensified the demand for reliable structural health monitoring (SHM) systems. However, the extreme space environment, characterized by radiation exposure, microgravity, ultra-high vacuum, and severe thermal cycling, imposes critical limitations on conventional electrical sensing technologies, leading to reduced measurement accuracy, instability, and long-term degradation. This review presents a comprehensive analysis of fiber Bragg grating (FBG)-based sensing technologies as a promising solution for deformation monitoring in space infrastructure. The study investigates the fundamental operating principles of FBG sensors under space conditions and systematically classifies existing FBG-based SHM architectures, including point-based, multiplexed, long-distance, and hybrid sensing systems. Furthermore, the advantages of FBG sensors—such as immunity to electromagnetic interference, passive operation, and high-resolution multipoint sensing—are critically evaluated in comparison with traditional electrical sensors. In addition, key challenges affecting the performance of FBG systems in space environments are analyzed, including radiation-induced wavelength drift, temperature–strain cross-sensitivity, signal attenuation, and long-term stability issues. The paper also highlights recent advances in interrogation techniques and network architectures that enable reliable in situ and real-time deformation monitoring of space structures. The results demonstrate that FBG-based sensing systems provide a scalable and robust framework for SHM in extreme environments while also revealing existing limitations and open research challenges. This work establishes a structured foundation for the development of next-generation intelligent monitoring systems for space infrastructure.
Full article

Figure 1
Open AccessArticle
Nonlinear Dynamics and Energy Harvesting Characteristics of Asymmetric Tristable Systems with an Elastic Magnifier
by
Devarajan Kaliyannan, Kadhiravan M J, Shree Vignesh Khumar Alampalayam Tamilselvan, Kughan S A, Hari Krishnan Babu and Mohanraj Thangamuthu
J. Sens. Actuator Netw. 2026, 15(3), 37; https://doi.org/10.3390/jsan15030037 - 12 May 2026
Abstract
Vibration energy harvesting has emerged as a sustainable solution for powering low-energy devices such as wireless sensors and wearable electronics. However, conventional vibration energy harvesters often suffer from narrow operational bandwidth and limited output performance under ultra-low excitation conditions. To overcome these limitations,
[...] Read more.
Vibration energy harvesting has emerged as a sustainable solution for powering low-energy devices such as wireless sensors and wearable electronics. However, conventional vibration energy harvesters often suffer from narrow operational bandwidth and limited output performance under ultra-low excitation conditions. To overcome these limitations, this study proposes an asymmetric tristable vibration energy harvester integrated with an elastic magnifier (EM), hereafter referred to as the asymmetric TVEH with EM, to enhance energy conversion efficiency under weak excitation. A nonlinear two-degree-of-freedom electromechanical model is developed to describe the coupled dynamics between the cantilever beam and the EM, incorporating nonlinear restoring forces and electromechanical coupling effects. The system performance is investigated using the harmonic balance method (HBM) and time-domain numerical simulations. In addition, parametric studies are conducted to examine the influence of the EM mass and stiffness ratios on the dynamic response and energy harvesting performance. The numerical results demonstrate that the inclusion of the EM significantly amplifies the system response under ultra-low excitation
(This article belongs to the Section Actuators, Sensors and Devices)
►▼
Show Figures

Figure 1
Open AccessArticle
Utilizing AoA for Decision Gathering in Optical Wireless Sensor Networks
by
Abdullah Alhasanat, Ahed Aleid, Abdelrahman Abushattal, Amal Alhasanat and Umar Raza
J. Sens. Actuator Netw. 2026, 15(3), 36; https://doi.org/10.3390/jsan15030036 - 8 May 2026
Abstract
Optical Wireless Sensor Networks (OWSNs) have emerged as a promising solution for energy-efficient and secure data collection in free-space optical (FSO) environments. A key challenge in such networks is minimizing the decision error rate (DER) during decision aggregation at the central entity (CE).
[...] Read more.
Optical Wireless Sensor Networks (OWSNs) have emerged as a promising solution for energy-efficient and secure data collection in free-space optical (FSO) environments. A key challenge in such networks is minimizing the decision error rate (DER) during decision aggregation at the central entity (CE). Building on earlier Time-Difference-of-Arrival (TDoA) reporting methods, this paper introduces an Angle-of-Arrival (AoA) framework for decision gathering. In the proposed scheme, sensor nodes equipped with Corner Cube Retro-reflectors (CCRs) passively communicate their local decisions, while the CE identifies such decisions based on AoA estimation. A closed-form expression for the DER is derived, incorporating false-alarm and missed-detection probabilities, and is validated through Monte Carlo simulations. Comparative evaluation against TDoA, Single Wavelength Parallel (SWP), and Multiple Wavelength Series (MWS) schemes shows that the AoA-based approach achieves consistently lower DERs, particularly in high-SNR regimes and larger node counts, closely approaching the theoretical lower bound. These results highlight AoA as a practical and scalable alternative to conventional decision-gathering methods in OWSNs.
Full article
(This article belongs to the Section Communications and Networking)
►▼
Show Figures
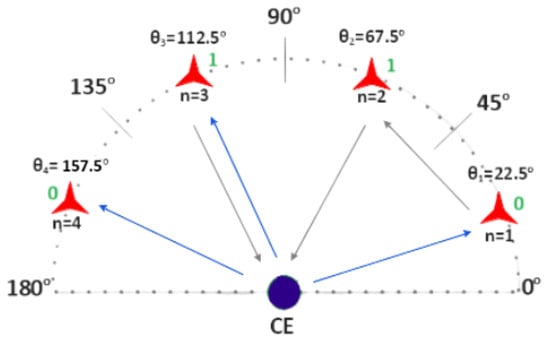
Figure 1
Open AccessArticle
Clinical Correlation and Postoperative Findings of Thigh-Based Electrocardiography in Aortic Stenosis
by
Aline dos Santos Silva, Miguel Velhote Correia, Andreia Gonçalves da Costa, Rui J. Cerqueira and Hugo Plácido da Silva
J. Sens. Actuator Netw. 2026, 15(3), 35; https://doi.org/10.3390/jsan15030035 - 28 Apr 2026
Abstract
Previous studies on healthy controls suggest the added value of thigh-based Electrocardiography (ECG), which collects data using sensors embedded in a toilet seat for unobtrusive signal acquisition. However, further evidence regarding its clinical feasibility is needed; with this work, we investigated three complementary
[...] Read more.
Previous studies on healthy controls suggest the added value of thigh-based Electrocardiography (ECG), which collects data using sensors embedded in a toilet seat for unobtrusive signal acquisition. However, further evidence regarding its clinical feasibility is needed; with this work, we investigated three complementary aspects: signal quality, morphological correlation with standard ECG leads, and the system’s potential for heart rate variability (HRV) analysis in patients undergoing aortic valve replacement. This work was divided into two main phases. In the first, 32 healthy volunteers underwent simultaneous ECG recordings using both a standard 12-lead ECG system and the thigh-based system. Signal Quality Index (SQI) analysis revealed that 56.25% of the experimental signals were classified as excellent, and over 62.5% of recordings showed a strong correlation with Lead I of the clinical ECG. These findings extend the state of the art by further characterising the quality and relevance of the captured signals. In the second phase, two patients with severe aortic stenosis were monitored before and after surgical valve replacement. HRV metrics derived from the thigh-based ECG captured distinct autonomic responses: one patient showed significant postoperative improvement in global and parasympathetic modulation (increased SDNN, RMSSD, and Sample Entropy), while the other exhibited reduced variability and complexity, potentially indicating impaired autonomic recovery. These results highlight the feasibility of thigh-based ECG data acquisition for passive, longitudinal cardiac health monitoring in everyday environments and its applicability for pre- and postoperative autonomic assessment.
Full article
(This article belongs to the Section Actuators, Sensors and Devices)
►▼
Show Figures

Figure 1
Open AccessArticle
Introducing the Slowloris E-DoS Attack: A Threat Arising from Vulnerabilities in the FTP and SSH Protocols
by
Nikola Gavric, Guru Bhandari and Andrii Shalaginov
J. Sens. Actuator Netw. 2026, 15(2), 34; https://doi.org/10.3390/jsan15020034 - 17 Apr 2026
Abstract
Slowloris is a well-known application-layer Denial of Service (DoS) attack that is challenging to detect due to its low-rate nature, allowing it to blend with legitimate traffic and remain unnoticed. Our hypothesis is that deliberate prolongation of the pre-authentication stage in stateful protocols
[...] Read more.
Slowloris is a well-known application-layer Denial of Service (DoS) attack that is challenging to detect due to its low-rate nature, allowing it to blend with legitimate traffic and remain unnoticed. Our hypothesis is that deliberate prolongation of the pre-authentication stage in stateful protocols induces unnecessary CPU utilization. In this study, we repurpose Slowloris as an energy-oriented (E-DoS) attack that exploits pre-authentication statefulness of the most prevalent remote access protocols, the Secure Shell Protocol (SSH) and File Transfer Protocol (FTP). We employ a Raspberry Pi-based experimental setup with different software implementations of the mentioned protocols to validate our hypothesis. Our experiments confirm the susceptibility of SSH and FTP to Slowloris E-DoS attacks, and we quantify the consequential impact on power consumption. We find that the Slowloris E-DoS attack exhibits an asymmetrical nature, causing a disproportionate computational demand on victim systems compared to the resources invested by the attacker. The results of this study indicate that battery-powered single-board computers (SBCs) are critically affected by these attacks due to their limited power availability. This research demonstrates the importance of understanding and mitigating Slowloris E-DoS vulnerabilities in the SSH and FTP protocols, offering valuable insights for enhancing security measures. Our findings show that millions of SBCs worldwide may be at risk and highlight a deeper structural weakness: the stateful design of widely deployed protocols can turn service availability into an energy liability. This systemic risk extends beyond SSH and FTP, with implications for IoT devices and backends that depend on stateful communication protocols.
Full article
(This article belongs to the Special Issue Feature Papers in the Section of Network Security and Privacy)
►▼
Show Figures

Figure 1
Open AccessArticle
Photogrammetry–Polarimetry Fusion for 3D Structural Edge Extraction and Physics-Guided Classification
by
Mohammad Saadatseresht, Hossein Arefi and Fatemeh Torkamandi
J. Sens. Actuator Netw. 2026, 15(2), 33; https://doi.org/10.3390/jsan15020033 - 16 Apr 2026
Abstract
►▼
Show Figures
The accurate interpretation of structural edges requires distinguishing geometry-driven discontinuities from reflectance- and illumination-induced variations. Conventional photogrammetric pipelines rely primarily on radiometric and geometric cues, which often lack physical interpretability under complex material and lighting conditions. This study proposes a photogrammetry–polarimetry fusion framework
[...] Read more.
The accurate interpretation of structural edges requires distinguishing geometry-driven discontinuities from reflectance- and illumination-induced variations. Conventional photogrammetric pipelines rely primarily on radiometric and geometric cues, which often lack physical interpretability under complex material and lighting conditions. This study proposes a photogrammetry–polarimetry fusion framework for physics-guided semantic classification of 3D structural edges. Radiometric, geometric, and polarimetric features are integrated within a noise-normalized representation to enable modality-independent interpretation. A rule-based classification scheme is introduced to assign edges to physically meaningful categories, including geometric, material, specular, illumination, and polarization-driven phenomena. The method is evaluated on a calibrated geometric object and a cultural heritage statue. Results show that polarization provides complementary information that reduces ambiguity between geometry-driven and reflectance-driven edge responses while preserving the underlying reconstructed geometry. On the calibrated dataset, edge detection achieves 88.4% precision, 95.5% recall, and an F1-score of approximately 0.92. Multi-view integration further improves the completeness of geometry-dominant 3D edges. The proposed framework introduces a physics-guided semantic sensing layer for multi-modal 3D perception, enabling more robust and interpretable structural analysis in photogrammetric workflows.
Full article

Graphical abstract
Open AccessArticle
An LLM-Based Agentic Network Traffic Incident-Report Approach Towards Explainable-AI Network Defense
by
Chia-Hong Chou, Arjun Sudheer and Younghee Park
J. Sens. Actuator Netw. 2026, 15(2), 32; https://doi.org/10.3390/jsan15020032 - 7 Apr 2026
Abstract
Traditional intrusion detection systems for IoT networks achieve high classification accuracy but lack interpretability and actionable incident-response capabilities, limiting their operational value in security-critical environments. This paper presents a graph-based multi-agent framework that integrates ensemble machine learning with Large Language Model (LLM)-powered incident
[...] Read more.
Traditional intrusion detection systems for IoT networks achieve high classification accuracy but lack interpretability and actionable incident-response capabilities, limiting their operational value in security-critical environments. This paper presents a graph-based multi-agent framework that integrates ensemble machine learning with Large Language Model (LLM)-powered incident report generation via Retrieval-Augmented Generation (RAG). The system employs a three-phase architecture: (1) a lightweight Random Forest binary pre-detection, achieving 99.49% accuracy with a 6 MB model size for edge deployment; (2) ensemble classification combining Multi-Layer Perceptron, Random Forest, and XGBoost with soft voting and SHAP-based feature attribution for explainability; and (3) a ReAct-based summary agent that synthesizes classification results with external threat intelligence from Web search and scholarly databases to generate evidence-grounded incident reports. To address the challenge of evaluating non-deterministic LLM outputs, we introduce custom RAG evaluation metrics—faithfulness and groundedness implemented via the LLM-as-Judge framework. Experimental validation on the ACI IoT Network Dataset 2023 demonstrates ensemble accuracy exceeding 99.8% across 11 attack classes; perfect groundedness scores (1.0), indicating all generated claims derive from the retrieved context; and moderate faithfulness (0.64), reflecting appropriate analytical synthesis. The ensemble approach mitigates individual model weaknesses, improving the UDP Flood F1 score from 48% (MLP alone) to 95% through soft voting. This work bridges the gap between high-accuracy detection and trustworthy, actionable security analysis for automated incident-response systems.
Full article
(This article belongs to the Special Issue Feature Papers in the Section of Network Security and Privacy)
►▼
Show Figures

Figure 1
Open AccessArticle
A Hybrid AVT-FVT Approach for Sensor Optimization in Structural Health Monitoring
by
Michele Paoletti, Giovanni Paragliola and Carmelo Mineo
J. Sens. Actuator Netw. 2026, 15(2), 31; https://doi.org/10.3390/jsan15020031 - 1 Apr 2026
Abstract
►▼
Show Figures
This study presents a structured methodology for optimizing the placement and selection of accelerometer sensors for structural health monitoring in civil infrastructures. The approach integrates both ambient and forced vibration testing data, followed by a unified analysis of sensor energy distribution through singular
[...] Read more.
This study presents a structured methodology for optimizing the placement and selection of accelerometer sensors for structural health monitoring in civil infrastructures. The approach integrates both ambient and forced vibration testing data, followed by a unified analysis of sensor energy distribution through singular value decomposition of the cross power spectral density. The energy associated with each sensor is normalized and decomposed into its vertical, longitudinal, and transversal components, allowing for detailed ranking and visualization across different structural elements such as the deck and supporting piers. A comparative analysis between the energy distributions obtained from ambient and forced vibrations is conducted to identify consistent sensor locations. The sensor configuration is then iteratively refined using a combination of global dynamic criteria and local spatial constraints to ensure both stability and optimal spatial distribution. The resulting framework enables the systematic design of sensor layouts that combine energy-based robustness with optimal spatial distribution across all three spatial components, while significantly reducing the number of required sensors, ensuring the preservation of damage detection capability and long-term structural health monitoring.
Full article

Figure 1
Open AccessArticle
Design Principles for a New Form of Bioelectrical Nanonetwork Based on Cellular Nanowires
by
Konstantinos F. Kantelis, Vassilis Asteriou, Aliki Papadimitriou-Tsantarliotou, Olga Tsave, Christos Liaskos, Christos A. Ouzounis, Lefteris Angelis, Ioannis S. Vizirianakis, Petros Nicopolitidis and Georgios I. Papadimitriou
J. Sens. Actuator Netw. 2026, 15(2), 30; https://doi.org/10.3390/jsan15020030 - 23 Mar 2026
Abstract
Nanotechnology continues to advance rapidly, revealing previously unexplored directions in nanoscale communications. Biological and electromagnetic nanonetworks—established communication paradigms at the nanoscale—have shifted interest toward the middle and higher levels of the nanonetworking protocol stack. Motivated by the discovery of Cable Bacteria (CB) and
[...] Read more.
Nanotechnology continues to advance rapidly, revealing previously unexplored directions in nanoscale communications. Biological and electromagnetic nanonetworks—established communication paradigms at the nanoscale—have shifted interest toward the middle and higher levels of the nanonetworking protocol stack. Motivated by the discovery of Cable Bacteria (CB) and their unique properties, we propose a theoretical model and framework for a new category of nanonetworks: bioelectrical nanonetworks (BioEN). This proposed framework combines the biocompatibility, sustainability and inherent nanodimensions of biological organisms with the networking performance of electromagnetic systems. Large-scale formations (e.g., 10,000 cells spanning nearly 2 cm), together with the electrical characteristics of CB, suggest the feasibility of guided electron-based transport that could complement diffusion-dominated nanonetworks, subject to resistive-capacitive (RC) constraints that remain to be quantified. Furthermore, we present a set of basic network architectures—such as star, ring, and tree—introducing a conceptual bio-multiplexer component, which utilizes CB to form a bioelectrical nanonetwork and illustrate core functionalities primarily at the network layer. Within this theoretical framework, BioEN is positioned as a potential enabler for diverse scientific, environmental, and technological applications, including health and ecosystem biosensing and bioremediation-oriented bioengineering. This work is conceptual and does not experimentally validate a deployed nanonetwork; instead, it establishes the design principles, abstractions, and architectural foundations intended to guide future implementation and experimental verification of bioelectrical nanonetworks.
Full article
(This article belongs to the Section Communications and Networking)
►▼
Show Figures

Figure 1
Open AccessArticle
Model Checking in Federated Learning-Based Smart Advertising
by
Rasool Seyghaly, Jordi Garcia and Xavi Masip-Bruin
J. Sens. Actuator Netw. 2026, 15(2), 29; https://doi.org/10.3390/jsan15020029 - 20 Mar 2026
Abstract
►▼
Show Figures
As social networks continue to expand, smart advertising increasingly depends on machine learning to deliver personalized and effective advertisements. Federated Learning (FL) is a distributed learning paradigm that supports privacy-preserving advertising by training models locally while avoiding direct sharing of raw user data.
[...] Read more.
As social networks continue to expand, smart advertising increasingly depends on machine learning to deliver personalized and effective advertisements. Federated Learning (FL) is a distributed learning paradigm that supports privacy-preserving advertising by training models locally while avoiding direct sharing of raw user data. However, ensuring the correctness, reliability, and operational robustness of FL-driven smart advertising systems remains a significant challenge, particularly in distributed and user-facing environments. In this study, we investigate the use of model checking as a formal verification technique for validating key properties of an FL-based smart advertising workflow in social networks. We combine a structured finite-state modeling approach with Linear Temporal Logic (LTL) specifications and model-checking tools to assess correctness, availability, and baseline privacy requirements. Using controlled simulation-based configurations, we show that, for a setup with 100 users and 20 edge servers, the system delivers advertisements to all users and the global model successfully processes 200 out of 200 requests. We further analyze verification overhead through detection-time measurements, observing an increase in average detection time from 10.05 s to 11.98 s as the number of users rises from 20 to 100. These results indicate that the proposed framework can provide practical assurance for FL-enabled smart advertising workflows, support more reliable deployment in distributed intelligent systems, and improve trustworthiness in real advertising applications.
Full article

Graphical abstract
Open AccessArticle
AI-Driven Dynamic Resource Allocation for Energy-Efficient Optical Fiber Communication Networks: Modeling, Algorithms, and Performance Evaluation
by
Askar Abdykadyrov, Gulzada Mussapirova, Nurzhigit Smailov, Zhanna Seissenbiyeva, Gulbakhar Yussupova, Ainur Tasieva, Ainur Kuttybayeva, Altyngul Turebekova, Rizat Kenzhegaliyev and Nurlan Kystaubayev
J. Sens. Actuator Netw. 2026, 15(2), 28; https://doi.org/10.3390/jsan15020028 - 17 Mar 2026
Abstract
►▼
Show Figures
The object of this research is resource management and energy consumption processes in optical fiber communication networks with access–metro–core architectures. The study addresses the problem that conventional static and semi-dynamic control methods are unable to simultaneously ensure energy efficiency and QoS stability under
[...] Read more.
The object of this research is resource management and energy consumption processes in optical fiber communication networks with access–metro–core architectures. The study addresses the problem that conventional static and semi-dynamic control methods are unable to simultaneously ensure energy efficiency and QoS stability under conditions of exponentially growing and highly variable traffic. To solve this problem, an AI-based integrated control model was developed that combines traffic prediction, dynamic resource allocation, spectrum management, and power optimization within a unified framework. Traffic prediction is performed using LSTM–BiRNN neural networks (1.2–1.8 million parameters, 300–500 thousand records), while control decisions are generated by an Actor–Critic reinforcement learning algorithm. Simulation results obtained in the Python 3.12 and OptiSystem 17.0 environments demonstrate that, in the Access segment (1–10 Gb/s), latency is stabilized within 1–10 ms; in the Metro segment (40–120 Gb/s), energy consumption is reduced by 18–27%; and in the Core segment (400–1000 Gb/s), the efficiency of RSA algorithms increases by 22–35%. When the EDFA output power is maintained within +17 to +23 dBm, amplifier power consumption decreases by 10–15%, resulting in overall network energy savings of 20–40%. The obtained results are explained by the synergy of accurate traffic prediction provided by the LSTM–BiRNN model and proactive real-time decision-making enabled by the Actor–Critic algorithm. The distinctive feature of the proposed approach is the simultaneous optimization of energy efficiency and QoS across all access, metro, and core segments within a single integrated architecture. The results can be practically applied in the design and modernization of optical fiber communication networks, as well as in the deployment of energy-efficient intelligent network management systems.
Full article

Figure 1
Open AccessArticle
Indoor Localization Based on IoT Crowdsensing Task Allocation
by
Bahareh Lashkari, Javad Rezazadeh and Reza Farahbakhsh
J. Sens. Actuator Netw. 2026, 15(2), 27; https://doi.org/10.3390/jsan15020027 - 17 Mar 2026
Abstract
Crowdsensing has been recently investigated as an incorporation of Human-Machine intelligence in which contribution of users is crucial. Indoor localization is one of the significant applications among divers applications that have been introduced in this area. Considering the slight infiltration of GPS signals
[...] Read more.
Crowdsensing has been recently investigated as an incorporation of Human-Machine intelligence in which contribution of users is crucial. Indoor localization is one of the significant applications among divers applications that have been introduced in this area. Considering the slight infiltration of GPS signals in indoor environments crowdsensing and its promising indoor localization schemes have been utilized for providing precise localization services. Precision of crowdsensing indoor localization schemes and elimination of erroneous data collection is strongly dependent on the underlying task allocation mechanism. In this work, we have approached the localization precision as a consequence of task allocation mechanism of crowd-powered indoor localization schemes. Hence, we have proposed to tackle this issue by applying GWO (Gray Wolf Optimizer) algorithm on participants of crowdsensing scheme. It is expected that the GWO algorithm implicitly performs the task allocation procedure in account of its crowd-powered nature. Accordingly, we have applied GWO algorithm on a proposed indoor localization scenario to undertake the requirements for discrete task allocation mechanism. Implementation results demonstrated that the population-centric structure of the GWO algorithm significantly increments the accuracy of fingerprint collection mechanism which maintains an exceptional localization precision.
Full article
(This article belongs to the Special Issue Recent Trends and Advancements in Location Fingerprinting)
►▼
Show Figures

Figure 1
Open AccessArticle
Research and Development of Intelligent Control Systems for High-Frequency Ozone Generators
by
Askar Abdykadyrov, Dina Ermanova, Maxat Mamadiyarov, Seidulla Abdullayev, Nurzhigit Smailov and Nurlan Kystaubayev
J. Sens. Actuator Netw. 2026, 15(2), 26; https://doi.org/10.3390/jsan15020026 - 3 Mar 2026
Abstract
This paper presents the development and investigation of an intelligent control system for a high-frequency ozone generator integrated into an IoT-based and telecommunication environment. A cyber-physical nonlinear mathematical model combining the electrical, thermal, gas-dynamic, and chemical subsystems of the ozone generation process is
[...] Read more.
This paper presents the development and investigation of an intelligent control system for a high-frequency ozone generator integrated into an IoT-based and telecommunication environment. A cyber-physical nonlinear mathematical model combining the electrical, thermal, gas-dynamic, and chemical subsystems of the ozone generation process is proposed. The model was implemented in discrete-time form and experimentally validated using the corona–discharge-based high-frequency ozonator ETRO-02. The deviation between simulation and experimental results did not exceed 5.3% for settling time, 6.7% for overshoot, 1.6% for steady-state ozone concentration, and 0.9% for gas temperature, confirming the adequacy of the proposed model. Based on this model, a hierarchical two-level intelligent control architecture is synthesized, consisting of a fast local control loop with a cycle time of 1–5 ms and a supervisory monitoring layer. The proposed adaptive state-feedback control law with online gain adjustment ensures stable real-time operation under nonlinear dynamics, ±20% parameter variations, network delays of 1–10 ms, and packet loss probabilities of up to 5%. As a result, the settling time is reduced from 420 ms to 160 ms, the overshoot from 12.5% to 3.1%, and the steady-state error from 6.5% to 1.6%, while the specific energy consumption decreases from 11.8 to 6.2 Wh/m3. The obtained results demonstrate that the integration of a cyber-physical model with a millisecond-level intelligent control system significantly improves the dynamic performance, robustness, and energy efficiency of high-frequency ozone generators compared to classical control and monitoring-oriented IoT systems. Unlike cloud-centric IoT monitoring architectures that operate at second-level update cycles, the proposed system closes the control loop locally at the millisecond scale, enabling stabilization of fast nonlinear electro-plasma dynamics. The results demonstrate that edge-intelligent adaptive control significantly enhances both dynamic performance and energy efficiency, confirming the feasibility of millisecond-level cyber-physical regulation for industrial ozone generation systems.
Full article
(This article belongs to the Section Big Data, Computing and Artificial Intelligence)
►▼
Show Figures

Figure 1
Open AccessArticle
Vehicle Communications: Sensitive Node Election SNE Algorithm Achieves Optimized QoS
by
Ayoob Ayoob, Mohd Faizal Ab Razak, Ghaith Khalil and Muammer Aksoy
J. Sens. Actuator Netw. 2026, 15(2), 25; https://doi.org/10.3390/jsan15020025 - 1 Mar 2026
Abstract
Vehicle networking is a new paradigm in wireless technology that facilitates communication between vehicles in close proximity and in-vehicle internet access. This technology paves the way for a variety of safety, convenience and entertainment applications, including safety message exchange, real-time traffic information sharing
[...] Read more.
Vehicle networking is a new paradigm in wireless technology that facilitates communication between vehicles in close proximity and in-vehicle internet access. This technology paves the way for a variety of safety, convenience and entertainment applications, including safety message exchange, real-time traffic information sharing and public internet access. The overall goal of vehicular networks is to create an efficient, safe and convenient environment for vehicles on the road. This paper presents a Sensitive Node Election (SNE) algorithm adapted to routing protocols in certain opportunistic network environments. The algorithm focuses on selecting the best agent for communication using an innovative approach for message forwarding. Quality of Service (QoS) metrics targeted for optimization include network end-to-end throughput and packet delivery, with the aim of improving the overall performance of the network. Our algorithm includes a stochastic rebroadcasting scheme that takes into account parameters, such as vehicle density, distance between vehicles and transmission distance, and adapts to various network conditions. Furthermore, the SNE algorithm uses a metric based on transmission distance and can dynamically adapt to application requirements, such as prioritization. It provides high throughput and minimizes delay. The results demonstrate the effectiveness of this approach in improving QoS in various vehicular ad hoc network (VANET) simulations and influencing the neural network ensemble (NNE Algorithm).
Full article
(This article belongs to the Special Issue Advances in Intelligent Transportation Systems (ITS))
►▼
Show Figures

Figure 1
Open AccessArticle
Image-Based Quantification of Boundary Uncertainty for Reliable Soymilk Solid Content Measurement
by
Taeyoon Kim, Minseo Lee, Sanghyun Cheong, Chunghwa Song and Han-Cheol Ryu
J. Sens. Actuator Netw. 2026, 15(2), 24; https://doi.org/10.3390/jsan15020024 - 26 Feb 2026
Abstract
Soymilk solid content (%) is a critical quality indicator that is directly related to product classification and regulatory compliance in food manufacturing. However, conventional optical refractometer-based measurements often suffer from blurred scale boundaries and subjective reading errors, leading to poor reproducibility under varying
[...] Read more.
Soymilk solid content (%) is a critical quality indicator that is directly related to product classification and regulatory compliance in food manufacturing. However, conventional optical refractometer-based measurements often suffer from blurred scale boundaries and subjective reading errors, leading to poor reproducibility under varying illumination conditions. This study proposes an image-based signal analysis framework that quantitatively interprets blurred liquid-scale boundaries by analyzing pixel intensity profiles, their gradients, and effective boundary widths. Instead of relying on human visual judgment, the proposed method characterizes boundary uncertainty using Gaussian-smoothed intensity signals and derivative-based feature extraction. Quantitative validation against ground-truth concentration values over 150 images demonstrates an overall mean absolute error (MAE) of 1.90 and a root mean squared error (RMSE) of 3.85. Illumination conditions yielding stable, single-peak derivative responses achieve an overall MAE of 0.23, whereas severe illumination conditions associated with unstable or distorted derivative patterns result in substantially higher errors (MAE = 8.57, RMSE = 8.60). These results quantitatively confirm that derivative-based boundary signal stability is directly linked to measurement accuracy. By transforming visual ambiguity into quantifiable signal features, this work provides a practical and reproducible alternative to subjective refractometer readings and offers a foundation for reliability-aware optical concentration measurement systems in industrial environments.
Full article
(This article belongs to the Section Actuators, Sensors and Devices)
►▼
Show Figures

Figure 1
Open AccessArticle
Temporal Attentive Graph Networks for Financial Surveillance: An Incremental Multi-Scale Framework
by
Wei Zhang, Yimin Shen, Hang Zhou, Bo Zhou, Xianju Zheng and Xiang Chen
J. Sens. Actuator Netw. 2026, 15(1), 23; https://doi.org/10.3390/jsan15010023 - 16 Feb 2026
Abstract
Systemic risk propagation in modern financial markets is characterized by non-linear contagion and rapid topological evolution, rendering traditional static monitoring methods ineffective. Existing Graph Neural Networks (GNNs) often struggle to capture “structural breaks” during crises due to their reliance on static adjacency assumptions
[...] Read more.
Systemic risk propagation in modern financial markets is characterized by non-linear contagion and rapid topological evolution, rendering traditional static monitoring methods ineffective. Existing Graph Neural Networks (GNNs) often struggle to capture “structural breaks” during crises due to their reliance on static adjacency assumptions and isotropic aggregation. To address these challenges, this study proposes the Temporal Attentive Graph Networks (TAGN), a dynamic framework designed for extreme volatility prediction and financial surveillance. TAGN constructs an incremental multi-scale graph by fusing high-frequency trading data, supply chain linkages, and institutional co-holdings to model heterogeneous risk transmission channels. Technically, it employs a deeply coupled GAT-GRU architecture, where the Graph Attention Network (GAT) dynamically assigns weights to contagion sources, and the Gated Recurrent Unit (GRU) memorizes the trajectory of structural evolution. Extensive experiments on the S&P 500 dataset (2018–2024) demonstrate that TAGN significantly outperforms state-of-the-art baselines, including WinGNN and PatchTST, achieving an AUC of 0.890 and a Precision at 50 of 61.5%. Notably, a risk early-warning index derived from TAGN exhibits a 1–2 week lead time over the VIX index during major market stress events, such as the Silicon Valley Bank collapse. This research facilitates a paradigm shift from historical statistical estimation to dynamic network-aware sensing, offering interpretable tools for RegTech applications.
Full article
(This article belongs to the Section Big Data, Computing and Artificial Intelligence)
►▼
Show Figures

Figure 1
Open AccessArticle
Enhanced MQTT Protocol for Securing Big Data/Hadoop Data Management
by
Ferdaous Kamoun-Abid and Amel Meddeb-Makhlouf
J. Sens. Actuator Netw. 2026, 15(1), 22; https://doi.org/10.3390/jsan15010022 - 16 Feb 2026
Abstract
Big data has significantly transformed data processing and analytics across various domains. However, ensuring security and data confidentiality in distributed platforms such as Hadoop remains a challenging task. Distributed environments face major security issues, particularly in the management and protection of large-scale data.
[...] Read more.
Big data has significantly transformed data processing and analytics across various domains. However, ensuring security and data confidentiality in distributed platforms such as Hadoop remains a challenging task. Distributed environments face major security issues, particularly in the management and protection of large-scale data. In this article, we focus on the cost of secure information transmission, implementation complexity, and scalability. Furthermore, we address the confidentiality of information stored in Hadoop by analyzing different AES encryption modes and examining their potential to enhance Hadoop security. At the application layer, we operate within our Hadoop environment using an extended, secure, and widely used MQTT protocol for large-scale data communication. This approach is based on implementing MQTT with TLS, and before connecting, we add a hash verification of the data nodes’ identities and send the JWT. This protocol uses TCP at the transport layer for underlying transmission. The advantage of TCP lies in its reliability and small header size, making it particularly suitable for big data environments. This work proposes a triple-layer protection framework. The first layer is the assessment of the performance of existing AES encryption modes (CTR, CBC, and GCM) with different key sizes to optimize data confidentiality and processing efficiency in large-scale Hadoop deployments. Afterwards, we propose evaluating the integrity of DataNodes using a novel verification mechanism that employs SHA-3-256 hashing to authenticate nodes and prevent unauthorized access during cluster initialization. At the third tier, the integrity of data blocks within Hadoop is ensured using SHA-3-256. Through extensive performance testing and security validation, we demonstrate integration.
Full article
(This article belongs to the Section Network Security and Privacy)
►▼
Show Figures

Figure 1

Journal Menu
► ▼ Journal Menu-
- JSAN Home
- Aims & Scope
- Editorial Board
- Reviewer Board
- Topical Advisory Panel
- Instructions for Authors
- Special Issues
- Topics
- Sections
- Article Processing Charge
- Indexing & Archiving
- Editor’s Choice Articles
- Most Cited & Viewed
- Journal Statistics
- Journal History
- Journal Awards
- Conferences
- Editorial Office
Journal Browser
► ▼ Journal BrowserHighly Accessed Articles
Latest Books
E-Mail Alert
News
Topics
Topic in
Electronics, Future Internet, Information, JSAN, Sensors, IoT
Privacy Challenges and Solutions in the Internet of Things
Topic Editors: Abdul Majeed, Safiullah KhanDeadline: 30 June 2026
Topic in
Applied Sciences, Electronics, JSAN, Photonics, Sensors, Telecom
Machine Learning in Communication Systems and Networks, 3rd Edition
Topic Editors: Yichuang Sun, Haeyoung Lee, Oluyomi SimpsonDeadline: 20 August 2026
Topic in
Computers, Electronics, Future Internet, IoT, Network, Sensors, JSAN, Technologies, BDCC
Challenges and Future Trends of Wireless Networks
Topic Editors: Stefano Scanzio, Ramez Daoud, Jetmir Haxhibeqiri, Pedro SantosDeadline: 30 September 2026
Topic in
Applied Sciences, Electronics, IoT, Sensors, Future Internet, JSAN, Telecom, Network
Applications of IoT in Multidisciplinary Areas
Topic Editors: Nurul Sarkar, Ivan CviticDeadline: 31 October 2026

Conferences
Special Issues
Special Issue in
JSAN
Feature Papers in the Section of Network Security and Privacy
Guest Editors: Jordi Mongay Batalla, Pascal Lorenz, Ioannis ChatzigiannakisDeadline: 31 May 2026
Special Issue in
JSAN
Remote Sensing and IoT Application for Smart Agriculture
Guest Editors: Xihai Zhang, Xiangyu Meng, Yuan RaoDeadline: 31 May 2026
Special Issue in
JSAN
Collaborative Integrated Sensing and Localization in Autonomous Systems
Guest Editors: Tanveer Ahmad, Xuejun Li, Muhammad Usman HadiDeadline: 31 May 2026
Special Issue in
JSAN
Advances in Intelligent Transportation Systems (ITS): 2nd Edition
Guest Editors: Hovannes Kulhandjian, Michel KulhandjianDeadline: 30 June 2026












