1. Introduction
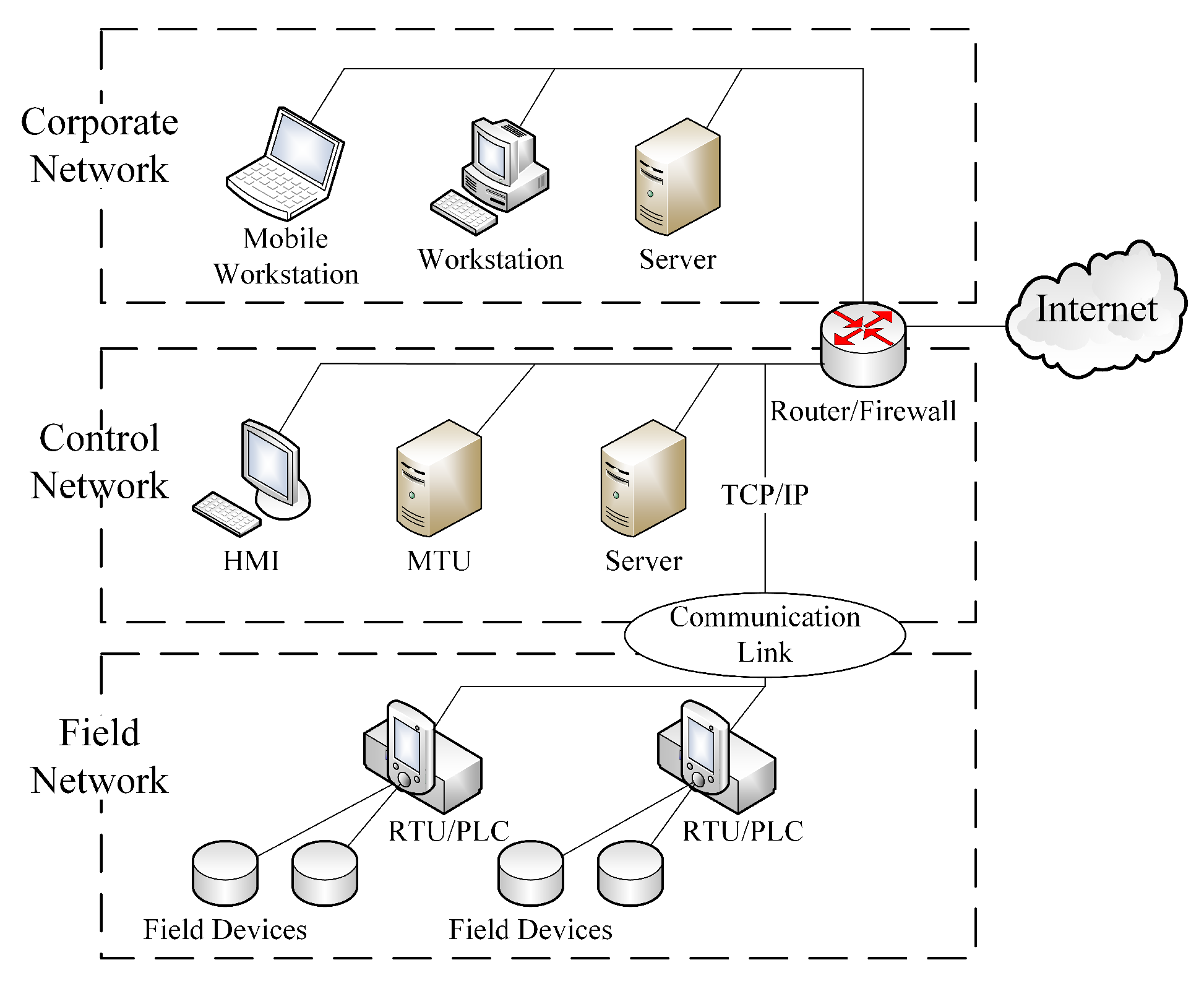
Cyber-physical systems (CPS) are integrations of computation, networking, and physical processes, which have tremendously stimulated the development of contemporary critical infrastructures in different domains, such as energy, health care, communication, transportation, and manufacturing [
1,
2]. However, these integrations have unintentionally entailed new vulnerabilities, threats and challenges in safety and security [
3,
4]. The growing count of security-related incidents has drawn the increased focus on securing CPS.
Since advanced persistent threat (APT) attacks are usually well-planned and highly-customized, they have become a major and challenging threat for CPS defenders [
5]. Specifically, the attackers carry out a long-term campaign with repeated attempts under the support of a highly organized and well-resourced malicious group who provides stealthy and evasive techniques; hence they are capable to adopt a series of advanced actions stealthily, persistently and detrimentally aiming at specific targets in critical infrastructures [
5,
6,
7]. The computer worm Stuxnet, which was the first discovered malware to intelligently damage a nuclear power station, is the epitome of APT attacks [
8], as well as other ensuing reported APT malware specimens, i.e., Duqu, Flame, Gauss [
9], etc. Owing to the use of stealthy and evasive techniques (e.g., zero-day exploits, obfuscation techniques), these stealth malwares play a vital role in the attack process.
However, the existing security solutions for CPS usually make some of the following flawed assumptions which hinder themselves [
10,
11]: (i) the security problem is modeled as an one-shot attack-and-defense scenario, violating the feature of persistent actions in the stealth malware propagation; (ii) attackers only possess the ability of using a limited set of fixable exploits for relatively isolated attacks, which is far from the real practice for the stealth malware propagation where different types of stealthy and evasive techniques are used by attackers; and (iii) defenders’ response is confined to cleaning the detected threats and recovering the compromised nodes, neglecting the fact that unknown threats might be undetected, propagated, injected, and updated persistently by APT attackers to pursue long-term gains. Thus, conventional countermeasures, such as intrusion detection systems, enterprise-wide patching, and anti-virus techniques, usually fail to mitigate the risk and damage posed by stealth malwares.
More specifically, there is always a time-span of
unprotected exposure when the defenders only adopt conventional countermeasures. Here, the unprotected exposure, which is accompanied by the attack-and-defense process, refers to the time-span between the detection of a certain intrusion and the complete deployment of a specified heavy-weight countermeasure (e.g., exploits patching, specialized anti-malware program). For defenders, their reaction duration towards newly detected threats directly determines the length of unprotected exposure. On the other hand, this unprotected exposure is crucial for the propagation of stealth malwares, since most valuable actions (e.g., updating, packing, targeting, propagating [
12,
13]) can be smoothly implemented in these time-spans. Given the fragility of CPS [
14], attackers’ exploitation of unprotected exposure can bring them profitable returns and thus pose irreversible damages to the system. Unfortunately, the unprotected exposure is almost inevitable and it is difficult to reduce the time-span to a tolerable scale in complex CPS. The reason lies on the fact that a diversity of tools (e.g., zero-day exploits, public exploits) and techniques (e.g., polymorphism, metamorphism) are utilized in persistent actions by attackers, while defenders have to confront the complexity and bear the time-consuming nature of detecting threats accurately, as well as developing and deploying specified heavy-weight treatment countermeasures properly. As a consequence, traditional security approaches which ignore the unprotected exposure provide readily exploitable opportunities for APT attackers to propagate malwares persistently and then achieve malicious goals.
Light-weight countermeasures, on the other hand, can help retard the spread of malwares during the time-span of unprotected exposure, thereby mitigating overall damages and offering additional time for the development and deployment of heavy-weight treatment countermeasures [
15,
16]. Unfortunately, light-weight countermeasures are likely to incur safety risk because they are usually cursory and sometimes inaccurate; hence, the ensuing side effects are still inherent shortcomings of these countermeasures, especially for the CPS with both safety and security requirements. Safety and security which share identical goals of protecting systems from failures are two key properties of CPS [
17]. Safety is protection against unintentional accidents, while security focuses on protecting systems from deliberate cyber attacks. For instance, containment techniques, such as firewalls, content filters, and routing blacklists [
18,
19], can be implemented to obstruct the propagation of worms whereas some legitimate communication which is necessary for systems’ normal operation might be blocked, as well. That is, when we try to maintain the security of a system using light-weight countermeasures, the safety requirements may be violated. This side effect is usually bearable in traditional information systems; however, the blockage of a critical legitimate control signal which is a safety requirement may lead to a catastrophic cascading in CPS [
20]. However, very little research has studied the optimal allocating and scheduling strategy of light-weight countermeasures taking the safety requirement into consideration.
Since security and safety are interdependent with the requirements of one having effects on the other, the satisfaction of fail-secure and fail-safe ability requires a collaborative approach [
20]. Here,
fail-secure means that access or data will not fall into the wrong or malicious hands in a security failure, while
fail-safe indicates that devices in a system will not endanger human lives or property when they fail. Hence, there is an urgent need for defenders to find an optimal trade-off between the gain and loss of deploying light-weight countermeasures in CPS, thereby achieving a balance between fail-secure and fail-safe ability. To address this problem, we model the persistent attack-and-defense process between the CPS defender and the attacker as a dynamic Stackelberg game. The attacker aims to stealthily penetrate the CPS at the lowest cost (e.g., time, effort) by selecting optimal network links to spread. On the other hand, the defender who has limited capabilities to detect stealth malwares aims to maximize the fail-secure ability, i.e., retarding the malware epidemic as much as possible by optimally allocating light-weight countermeasures until the development and deployment of heavy-weight countermeasures. Meanwhile, safety requirements of CPS are considered in the form of constraints in the defender’s decision model, which reflects the primary importance of fail-safe ability. The main contributions of this paper are:
- 1)
We propose the static shortest-path tree interdiction (SSPTI) game, model it as a bi-level integer program (BLIP), and prove its NP-hardness. A Benders decomposition algorithm (S-BD) is then developed to achieve its Stackelberg equilibrium.
- 2)
We extend the SSPTI to a multi-stage dynamic shortest-path tree interdiction (DSPTI) game to support the of real-time decision-making in the persistent attack-and-defense process, and design a model predictive control (MPC) strategy for the defender. An approximation algorithm is proposed for the defender to achieve local optimality, thereby expanding the solvable scale of the problem.
- 3)
The evaluation results demonstrate that the proposed approximation algorithm can enlarge the solvable scale of problems with an order of magnitude improvement (reporting an increase from less than 100 nodes to more than 3000 nodes) and reduce the resources consumption by .
- 4)
The performance of proposed MPC strategy is better than existing strategies on both simulated and real-case-based CPS networks. A lower steady infection rate and a higher ratio of giant component can be achieved by MPC strategy simultaneously, which means it can help retard the spread of malwares and the cascade of devices failure at the same time.
The reminder of this paper is organized as follows.
Section 2 provides the related work, and
Section 3 introduces the network model of CPS and the Stackelberg game model between the defender and the attacker aiming to penetrate the CPS. In
Section 4, SSPTI game is formulated as a BLIP, and an exact algorithm is designed for it. The game is then extended to a dynamic version in
Section 5, and an MPC strategy is designed for DSPTI.
Section 6 reveals the performance of proposed algorithms and strategies.
Section 7 concludes this paper.
5. Dynamic Shortest-Path Tree Interdiction Game
In the model setting of SSPTI game, both players adopt stationary strategies which sometimes violate the fact that a cunning attacker is likely to adjust its propagation plan according to the dynamic environment thereby achieving a better payoff. The defender, on the other hand, needs to take actions in an observe-and-react loop rather than take an one-shot defense because of the exist of unprotected exposure and forthcoming malicious events. The model of SSPTI obviously cannot meet those dynamic and adaptive needs of the interdictor. In order to meet the fact of real-time defense-and-attack decision-making, this section extends SSPTI to a multi-stage dynamic shortest-path tree interdiction (DSPTI) game, which can be modeled as an extensive-form game.
5.1. Extending SSPTI to the Dynamic Game
In contrast to the SSPTI game, both players can adopt an observe-and-response action rather than an once-and-for-all decision in real cyber-combat. That is, once newly infectious devices are detected, the defender will allocate certain light-weight countermeasures to certain links. Similarly, the attacker can redesign its propagating tree based on the observation of its opponent’s actions. Based on this practical realization, we propose the following DSPTI game.
The DSPTI game in extensive form is an ordered vector,
where
is a finite set of players (i.e., defender and attacker).
denotes a tree called the game tree from root
, which is determined by the initial infected vertex
, the graph
G and the functional assurance Constraints (5) and (6).
is a partition of the set of vertexes that are not leaves, denoting the decision vertex of player
i, and in this game the attacker and the defender make decisions in an alternating manner. Let
be the number of decisions that each player has to make during this game.
O denotes the set of possible game outcomes and
u is a function associating every leaf of the tree with a game outcome in the set
O, i.e., the utility function that accumulates all path lengths from infected root
to all each vertex for each game outcome. We can also demonstrate that the DSPTI game is NP-hard shown in Theorem 3.
Theorem 3. The DSPTI game is NP-hard.
Proof of Theorem 3. Firstly, we introduce a problem of finding a sequence of subsets (for ) of links such that and whose removal from G sequentially results in the largest increase in the length of the shortest-path tree from root to each vertex, called dynamic k-most-vital-links problem (DKMVP). It is clear that DKMVP is a special case of DSPTI problem.
We then prove that DKMVP is NP-hard by showing that a dynamic k-most-vital-links recognition problem (DKRP) related to it is NP-complete. The DKRP is:
INPUT: A undirected graph ; , ; ; .
OUTPUT: Yes, if there exists a sequence of subsets (for ) such that and the accumulated traversing length of the shortest-path tree from in for is ; no, otherwise.
Hence, we then demonstrate that DKRP is NP-complete by reducing the knapsack problem (KNAP) in Theorem 1 to it. The reduction process is as follows.
We reuse the graph shown in
Figure 3. Similarly, we consider the problem DKRP defined on this graph with
,
, and
. It is observed that none of links
and
for
can be members of any
for
. Therefore, we may assume that only links
for
are removed. For convenience, link
is simply denoted by index
j, and let
be any sequence of sets of removed links in the time period from 1 to
that does not violate the budget constraint
. It is obvious that
,
; hence,
, and the total length of the shortest-path tree from vertex 0 becomes
. That is, there is a one to one correspondence between solutions of DKRP and solutions of KNAP. □
5.2. A Model Predictive Control Strategy for DSPTI
In addition to its NP-hardness, it is impossible to achieve the Stackelberg equilibrium for the defender before the end of the game due to the uncertainty from incomplete malware detection and the lack of future data. Traditional exponential-state backward recursion approaches to other kinds of multi-stage interdiction games, such as the dynamic-programming algorithm for dynamic shortest-path interdiction game [
49], are not capable of tackling the real-time problem in which no future observation information could be obtained in advance and then used in the backward recursion procedure. To address this, drawing on ideas of modern control theory and methodology, we propose a MPC strategy for DSPTI game with respect to the requirement of real-time decision-making. The idea of MPC strategy derive from the advanced approach of process control, i.e., Model Predictive Control, which allows the current stage to be optimized while keeping the future stages in account [
50]. The detection system of malwares serves as the system model in this MPC strategy, and the optimizer is defined to solve a local-greedy SSPTI problem (LG-SSPTI) in a rolling horizon manner.
Once newly infectious devices are detected, a new decision round
t will be started by the defender and its opponent. According to the idea of MPC, we need to optimally solve the SSPTI at this round
t, and only implements decisions on the neighbor links of
. However, this simple idea is wasteful in the use of computing resource since useless decisions on non-neighbor links of
are made and SSPTI itself is NP-hard. Therefore, we introduce the local-greedy SSPTI problem first. The approximate decision of the defender at stage
t is made by solving the following LG-SSPTI problem:
where
,
is the Stackelberg equilibrium of this game, and
is the set of links directly connected to
. Constraint (
14) denotes that the propagation of malwares should follow a tree-structure pattern. Constraints (15) and (16) are functional assurance constraints at stage
t, where
and
denotes the available total and individual resources left after stage
. Constraint (17) denotes a local-greedy allocation constraint that only links connected to vertex
can be selected to allocate light-weight countermeasures at stage
t.
Theorem 4. The LG-SSPTI problem is NP-hard.
Proof of Theorem 4. Different from the SSPTI problem, Constraint (17) introduces new features. Hence, we first introduce a problem of finding a subset K of links which connected to such that and whose removal from G results in the largest increase in the length of the shortest-path tree from root to each vertex, called local greedy k-most-vital-links problem (LG-KMVP). It is clear that LG-KMVP is a special case of LG-SSPTI problem. Due to the reason in the proof of Theorem 1, we omit the Constraint (16) in the proof.
We then prove that LG-KMVP is NP-hard by showing that a local greedy k-most-vital-links recognition problem (LG-KRP) related to it is NP-complete. The LG-KRP is:
INPUT: A undirected graph ; , ; ; .
OUTPUT: Yes, if there exists a set such that and the total length of the shortest-path tree from in is ; no, otherwise.
The existence of a polynomial algorithm for LG-KMVP would imply the existence of a polynomial algorithm for LG-KRP. Hence, we then demonstrate that LG-KRP is NP-complete by reducing the above-mentioned NP-complete problem, i.e., knapsack problem (KNAP) in Theorem (1), to it.
The reduction process is as follows. Since links
for
, they cannot belong to
K. Thus, we can still reuse the graph shown in
Figure 3 though the removal cost of links
for
can be set as any value Then, we consider the problem LG-KRP defined on this graph with
,
, and
. It is observed that none of links
for
can be members of
K. Therefore, we may assume that only links
for
are removed. For convenience, link
is simply denoted by index
j, and let
K be any set of removed links that does not violate the budget constraint
. Then,
and the total length of the shortest-path tree from vertex 0 becomes
. That is, there is a one to one correspondence between solutions of LG-KRP and solutions of KNAP. □
Let
be the set of infected vertexes at stage
t, and
denote the newly detected set of infected vertexes at
t. The MPC strategy for DSPTI problem is shown in Algorithm 2, named as MPC-DSPTI strategy.
| Algorithm 2 MPC-DSPTI: MPC Strategy for DSPTI |
- 1:
Initialize , , , , - 2:
whiledo - 3:
Malware Detection: obtain a set - 4:
if then - 5:
Defender’s Decision: solve LG-SSPTI(t) for - 6:
Malware Interdiction: allocate countermeasures according to - 7:
Attacker’s Decision: solve [Sub()] for - 8:
Malware propagation: penetrate the CPS based on - 9:
|
Although LG-SSPTI problem is still NP-hard, two benefits are brought by introducing the local-greedy allocation constraint. (1) The number of decision variables is reduced a lot and will not increase directly as the growth of graph G, thereby expanding the solvable scale of the problem. (2) Since only urgent interdiction demands at current stage (i.e., the needs to allocate countermeasures to links that may be penetrated immediately by the attacker) are satisfied, and most resources remain available for future interdiction actions. That is, using this MPC strategy the defender can adopt an observe-and-response decision adaptively. This helps the defender reduce the decision-making risk due to the uncertainty of the distribution of malwares which is essential for avoiding countermeasures resources waste and achieving more robust decisions.
Due to the similarity between LG-SSPTI and SSPTI, the proposed algorithm S-BD can be used to solve LG-SSPTI optimally by adding the Constraint (17) to the the [Master(
)] in
Section 4. In this MPC strategy, the solution of any instance of LG-SSPTI can be viewed as a kind of approximate solution of the SSPTI with the same constraints except the Constraint (17). Let
, and the approximate performance analysis is shown in Theorem 5, which proves that LG-SSPTI holds an
approximation for SSPTI.
Theorem 5. The solution of LG-SSPTI can achieve the approximation for the corresponding SSPTI problem.
Proof of Theorem 5. Without loss of generality, we omit the superscript “
t” in [LG-SSPTI(
t)] during this proof. Let
and
be the feasible region of
and
determined by Constraints (
14)–(17) in LG-SSPTI, respectively. The optimal solution of SSPTI is
, and let
be the optimal solution of LG-SSPTI.
Firstly, it is clear that
, and
; thus,
Then, we define
. For the fixed
,
; hence, for the specific
, we have
Let
, where
, else
. For the fixed
, we have the explicit expression of
as follows:
Since
,
, we have
, i.e.,
On the other hand, item
in Equation (22) is the sum of added path lengths on tree
except the added path length of links
. Since each link can only be interdicted once at most, by assuming that all the links on tree
could be interdicted by the defender, we could obtain a upper bound:
Meanwhile, it is clear that
Finally, we conclude that
, i.e.,
□
6. Performance Evaluation
This section first introduces several defense strategies, including existing strategies and the proposed strategy. Then, we introduce the performance metrics for both static and dynamic strategies, and the evaluation settings in the experiment are given including simulation methods of networks and information of the real-case CPS network. After that, we evaluate our proposed algorithms and strategies through extensive experiments with static and dynamic settings.
6.1. Defense Strategies
We first evaluate two static defense strategies, i.e., SSPTI and LG-SSPTI. The defender who adopts static strategies allocates all available defense resources in an once-and-for-all manner, once infected devices are detected. Then, three different dynamic strategies are considered as follows for evaluation with respect to the pay-off between CPS security and safety.
- 1)
We propose the static shortest-path tree interdiction (SSPTI) game, model it as a bi-level integer p A fail-safe strategy (FSA): when a device is infected and detected during the unprotected exposure, it will be isolated from the CPS. Although its neighbors may have been infected, as well, no light-weight countermeasures will be taken on them such that fail-safe ability can be maintained as much as possible.
- 2)
A fail-secure strategy (FSE): when a device is infected and detected during the unprotected exposure, the device itself and its neighbors will be isolated at the same time so as to avoid further infections deriving from possible infected neighbors. Hence, fail-secure ability is the first priority for the defender.
- 3)
The MPC strategy (MPC): as mentioned in
Section 5, when a device is infected and detected during the unprotected exposure, it will be isolated and then light-weight countermeasures will be allocated optimally to its neighbors by solving a LG-SSPTI problem. In fact, this strategy intends to achieve a balance between fail-safe ability and fail-secure ability in CPS defense.
6.2. Performance Metrics and Evaluation Settings
We first use the following metrics for performance comparison in the evaluation of static strategies on different types of networks:
- 1)
The achieved objective u under different static strategies. That is, the shortest-path three length which the attacker can achieved under the situation of defenders’ countermeasure implementation. The larger u the attacker gains, the more effectively the defender defends in the malware propagation. We mainly compare the achieved u of SSPTI and LG-SSPTI, and analyze the impact of on the actual approximate ratio.
- 2)
The algorithm running time. We compare the running time of SSPTI and LG-SSPTI by changing the scale of the problem.
In the experiments, we select three representative types of CPS networks for evaluation, i.e., square-lattice networks, standard Erd
s-Rényi (ER) networks [
51] and scale-free networks [
52]. Lattice networks, where each vertex has the same number of links, have been used to model physical systems [
2], such as water supply systems, power grid systems, etc. ER network is the original model of networks based on random graph theory, which has a Poisson degree distribution. Many more real-life networks obey a power-law form in degree distribution, such as the Internet [
53], mobile communication networks [
54], and airline networks [
55]. These systems can be approximately modeled as scale-free networks.
For evaluation, 100 instances of square-lattice networks, ER networks and scale-free networks with 50 vertexes, 85, 178 (in average), and 144 links are generated, respectively, in the evaluation of static strategies. An initial infectious device is randomly generated to evaluate the performance of static strategies. In each instance, link attributes , are randomly generated and uniformly distributed on . Node attributes is uniformly distributed on . Let interdiction delay so as to analyse the impact of . Then, a set of square-lattice networks, ER networks and scale-free networks of different size (from 50 vertexes to 1600 vertexes) are generated with the same link attributes setting to compare the running time. Here, the upper bound of total loss R is set as , and is set as to consider the impact of network size on static strategies.
Additionally, the followings metrics are used to evaluate the performance of different dynamic defense strategies, which cares for the gain and loss of deploying light-weight countermeasures against stealth malware propagation in CPS.
- 1)
The speed and scale of malware propagation, which represents the security situation of the CPS during the defense process.
- 2)
The size of giant component of the CPS during the defense process, which is a major indicator of safety situation for networked systems.
According to the features of stealth malware detection [
12], we can simply assume that the probability that an infected vertex can be detected by the defender grows linearly as the increase of its infection duration, and after a given duration
it can be certainly detected. The initial ratio of infection is set to be 2% in the experiments that obtain the metrics versus time curves, and then varies from 1% to 100% in order to test the difference of steady infection state (i.e., the final scope of infection) under different initial infection ratios. Here, 100 instances of square-lattice networks, ER networks and scale-free networks with 300 vertexes are generated, respectively, with the same link attributes setting (e.g.,
,
,
), and let
. We set the upper bound of total loss
, and the individual upper bound of loss
so as to meet the safety requirement of CPS. Moreover, a practical CPS case is used to evaluate the dynamic strategies, i.e., Italian coupled communication and power grid network [
56]. There are 39 vertexes and 102 links in the control and communication network, 310 vertexes and 361 links in the power grid network, and 169 coupled links between them. We execute the evaluation 100 times adopting the above link attributes setting and average the numerical results.
We program our algorithms using YALMIP toolbox [
57] and Gurobi version 7.0.2 callable library for exact solution for master problems. Computation is performed on a Windows10 (64) computer with 2.40 GHz Intel(R) Core i5 CPU and 4.0G RAM.
6.3. Evaluation Results of Static Strategies
6.3.1. Comparison of Achieved Objective u
The performance comparison of static strategies SSPTI and LG-SSPTI on 100 instances of three types of networks with 50 vertexes is shown in
Table 2. It is obvious that as the increase of
from 0.2 to 1.0 the average actual approximation ratio
on square-lattice networks rises from 1.08 to 1.33, whereas that on ER networks and scale-free networks grows slightly from 1.03 to 1.13 and 1.11, respectively. That is, LG-SSPTI strategy can actually achieve a better approximation ratio, though the approximation ratio given by Theorem 5 is
, especially on scale-free networks. The length of shortest-path tree for malware propagation on square-lattice networks is noticeably larger than that on ER and scale-free networks with the same nodes scale. Besides, the consumed resources
when adopting SSPTI strategy is nearly 3 times of that when adopting LG-SSPTI strategy on ER and scale-free networks, and around 7 times of that on square-lattice networks. The result demonstrates that LG-SSPTI strategy can save interdiction resources in a large amount compared with SSPTI, and these saved resources can be used in the future shots of defense thereby bringing extra payoffs.
In summary, the defender who adopts LG-SSPTI strategy can achieve at most approximation of SSPTI strategy and consume quite fewer resources compared with SSPTI strategy in the meantime on square-lattice networks, ER networks and scale-free networks. Additionally, a malware can be spread faster in the manner of shortest-path tree on ER and scale-free networks compared with square-lattice networks, deriving from the structure difference between them.
6.3.2. Comparison of Algorithm Running Time
In
Table 3, we compare the algorithm running time of SSPTI and LG-SSPTI on three types of networks. For each number of vertexes
, 10 instances are generated for evaluation. With the enlargement of the scale of a problem especially the number of links
, the average running time of both strategies increases by various extents. When the scale of networks increase to over 200 links, SSPTI cannot solve all instances optimally in the given time (1800 CPU seconds) on three kinds of networks. However, compared with SSPTI, the solvable scale of LG-SSPTI has increased to 6268, 1479, and 4794 links on square-lattice, ER, and scale-free networks, respectively, and LG-SSPTI is faster than SSPTI by a wide margin. The superiority of LG-SSPTI is rooted in the fact that its decision variables will not increase directly as the growth of network. Since the number of an infected node’s neighbors on square-lattice network is a constant except that of edge nodes, the running time increases slowly as the rise of network size, and the average number of iterations in the decomposition procedure keeps nearly the same. The degree distribution of scale-free networks follows a power low asymptotically, and randomly selected initial infectious nodes usually have a low degree in statistical; hence, the LG-SSPTI running time on scale-free networks is lower than its counterpart on ER networks, which approximately holds Poisson degree distributions.
Therefore, we conclude that LG-SSPTI expands the solvable scale of the problem to a large extent on three kinds of generated networks. Besides, the running time of LG-SSPTI on square-lattice networks and scale-free networks is lower than it counterpart on ER networks.
6.4. Evaluation Results of Dynamic Strategies
6.4.1. Performance on Generated Networks
The propagation performances of three dynamic defense strategies on square-lattice networks, ER networks and scale-free networks are shown in
Figure 4,
Figure 5 and
Figure 6. From the security situation results in subplot (a), our proposed strategy MPC and the fail-secure strategy FSE can effectively retard and mitigate the propagation of malwares and all the ratios of infected vertexes are suppressed fewer than 20%, while the fail-safe strategy FSA cannot prevent malware penetration effectively resulting a higher propagation speed and a larger scope of infection. Meanwhile, scale-free networks tend to be more fragile towards malware propagation no matter which defense strategies the defender adopts. From the safety situation results in subplot (b), the proposed MPC strategy slows the collapse of giant component ratio
down and maintains the highest ratio of giant component among three dynamic strategies. At the beginning of the infection, FSA holds a lower collapse rate of
compared with that of FSE; however, due to the challenge of stealth malware quick detection, the propagation cannot be controlled in the short term resulting the outbreak of newly infected vertexes in the medium term. Hence, safety cannot be guaranteed as expected without active actions on system security, due to the interdependence between safety and security in CPS. The FSE strategy, on the other hand, can control the propagation of malware, while it gives rise to a sharp drop in
at early stages (lower than 60% in
Figure 6b). Althougfh, FSE outperforms in maintaining the security situation of CPS before the implementation of heavy-weight countermeasures, the high collapse rate of
of FSE at the beginning of infection is likely to make a large loss on safety assurance.
Therefore, among these three strategies, our proposed MPC strategy can align CPS security and safety properly. Although the FSA strategy aims to maintain safety and reduce the loss on system functionalities as much as possible, more vertexes will be infected in the future due to the undetected threats and the unprotected exposure, resulting worse performance on both safety and security maintenance. FSE, on the other hand, can achieve a low infected ratio but fail to maintain the connectivity and safety of CPS.
6.4.2. Performance on Real CPS Cases
The simulation results on Italian coupled communication and power grid network are shown in
Figure 7,
Figure 8 and
Figure 9. From the results in
Figure 7, the performances of three strategies are similar to the above conclusions on generated networks, and MPC strategy performs better than the other two strategies in both security and safety assurance. When
, the practical CPS network tends to be less fragile than the generated networks due to the difference in network structures. However, as the increase of
, i.e., the rise of detection difficulty, the performance of all strategies degenerates (see in
Figure 8 and
Figure 9). Both MPC and FSE strategy have a slight rise in the ratio of infected vertexes, while the spread of malwares cannot be effectively controlled by FSA strategy. The
when adopting MPC strategy decreases at the lowest speed and can be controlled in a relatively higher level among three strategies.
As a result, the performance of all strategies degenerates as the increase of detection difficulty. However, the proposed MPC strategy still outperforms other strategies, and it can help retard the spread of malwares and the cascade of devices failure during the time-span of unprotected exposure, thereby achieving a balance between security and safety.
6.4.3. Discussion of Steady Infection State
We then consider the extreme case that no heavy-weight countermeasures are developed and deployed until the steady infection state, i.e., the unprotected exposure is relatively large and only light-weight countermeasures work. This situation is not very common, but considering the cunning techniques of attackers in reality CPS defenders need to take actions in case of emergency. As shown in
Figure 10,
Figure 11 and
Figure 12, the performance of dynamic strategies on the final scope of infection with various initial infection ratios are considered on three types of networks. Here, the detection time threshold
is set to be 5. As the increase of initial infection ratio, the average steady scope of infection grows to 100% with different rate and the average steady
falls to 0%. More specifically, it is clear that FSE and MPC outperform FSA on the steady state of both security and safety situation among three kinds of networks. When the initial infection ratio is 1%, the average final ratio of infected vertexes of FSA is around 38%, 64%, and 78% on square-lattice networks, ER networks and scale-free networks, respectively, while that of MPC and FSE is below 10% and 20%. The performance on
assurance of FSA is much worse than MPC and FSE, reporting around 51%, 20%, and 3%, respectively, when the initial infection ratio is 1%, whereas that of MPC and FSE is more than 90% and 70%.
The performance of FSE is slightly better than that of MPC in reducing the scope of infection, but FSE is intrinsically inferior to MPC in safety assurance of CPS. The superiority of FSE in final ratio of infection over MPC is not more than 15% on square-lattice networks and ER networks and 25% on scare-free networks, but MPC can sometimes exceed FES around 45% in the steady
. More significantly, even though more vertexes are immune to malwares when using FSE rather than MPC, the CPS is not likely to function well at all because of the extremely fragmented condition. For instance, in
Figure 12 when initial infected ratio is 10%, FSE outperforms MPC in final ratio of infection reporting nearly 25% versus 46%; however, the corresponding
of FSE and MPC is about 5% and 38%. That is, the CPS adopting FSE becomes a combination of isolated vertexes and network fragments which cannot supports most of the function requirements, although around 75% of these components are not infected. On the other hand, the CPS adopting MPC still has 54% of vertexes which are not infected; meanwhile, 38% vertexes are in the same giant component and belong to the set of 54% uninfected vertexes, i.e., this giant component is protected to be secure and safety at the same time.
Similar results on Italian coupled communication and power grid network can be obtained when the extreme case is taking account, shown in
Figure 13. MPC is still the best choice when considering the balance between fail-secure ability and fail-safe ability among those three dynamic defense strategies. The performance of FSE is slightly better than that of MPC in reducing the scope of infection where the gap between is not more than 10%. MPC is intrinsically superior to FSE in safety assurance of CPS, reporting 52% versus 14% in final
. Besides, the inferiority of FSA to the other strategies on Italian coupled network is not very large compared to that on generated networks. However, based on the results in
Figure 7,
Figure 8 and
Figure 9, we can conclude that the performance difference between different strategies will become more distinctive as the increase of detection difficulty.
To summarize, considering the extreme case that the unprotected exposure is relatively large and only light-weight countermeasures work, MPC is the best choice when both fail-secure and fail-safe ability is essential among those dynamic strategies on both generated and real-case CPS networks. The reason lies on the fact that a defender who adopts MPC can reduce the scope of final infection and maintain the communication and other normal functions of the giant component to a large extent. Therefore, when the defender faces a stealth APT attack with fewer heavy-weight countermeasures to defense the CPS in an emergency, the proposed MPC strategy can provide a option of using light-weight countermeasures so as to achieve a balance between fail-secure ability and fail-safe ability while retarding the stealth malware propagation in CPS.