According to Shannon [
22], entropy is a measure of the uncertainty associated with a random variable. There are several papers that are using entropy to detect covert channels, such as those using information entropy [
23] or relative entropy [
24] for detection of network storage channels, corrected conditional entropy [
25] for detection of network timing channels, etc. In this section, we will present a detection methodology of known covert channels based on the concept of cross-entropy, which is close to the concept of relative entropy given in [
24]. Since we do not have access to real traffic, the testing of different parameters for this methodology is left for future work.
Thus, in the real scenarios, the hospital can monitor their regular traffic, and can calculate its entropy separately for different properties, which are of interest. One example of the DICOM case is to calculate the entropy of a probability distribution of values for the command element Message ID, or its halves.
When we have dataset with samples of covert communication
Q that tries to mimic a probability distribution of regular communication
P, the ideal case for the steganographic parties is that these two distributions are equal, which in the language of cross-entropy means that their cross-entropy
is equal to the entropy
of
P. By measuring how much the cross-entropy
differs from the entropy
of regular traffic
P, we can draw some conclusions about the covert communication. The actual difference between these two values can be seen as a measure of how a probability distribution
Q is different from a reference probability distribution
P, and is known as Kullback–Leibler divergence or relative entropy:
The hypothesis is that if the adversary is using non-encrypted text as secret message, the produced covert probability distribution Q will differ a lot from the P of regular traffic. Here we will define the detecting methodology for a general case. Let the adversary use non-encrypted text with characters of the length N bits (for example, for ASCII characters, N is 7 or 8). The passive warden can use the following steps:
In the future work, above-mentioned approach must be tested in real scenarios, and a significant difference, together with other parameters of the methodology (e.g., number of needed samples, or time interval for suspected flow) needs to be defined. However, we will perform an experimental evaluation under testbed conditions in the remainder.
Experimental Evaluation
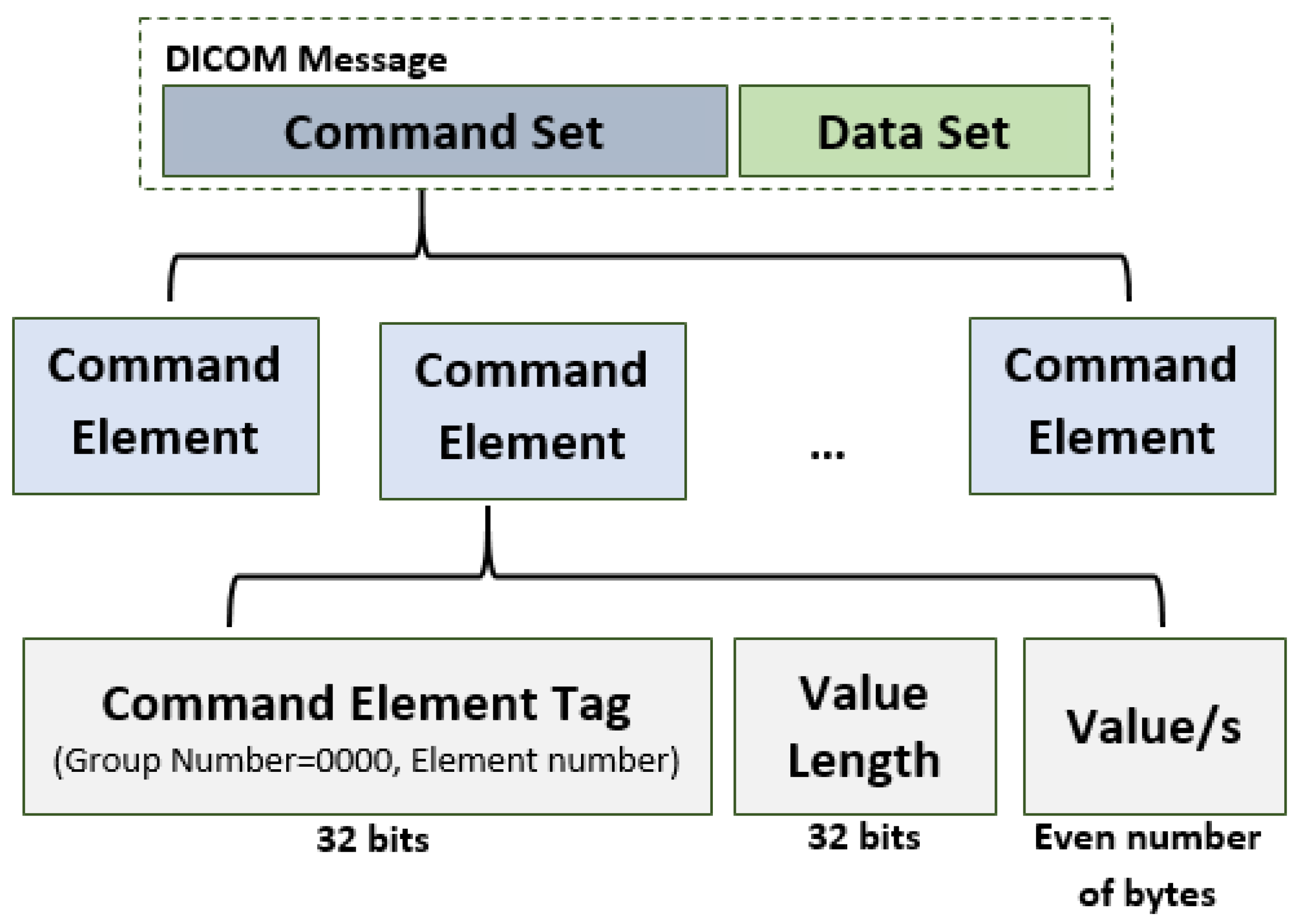
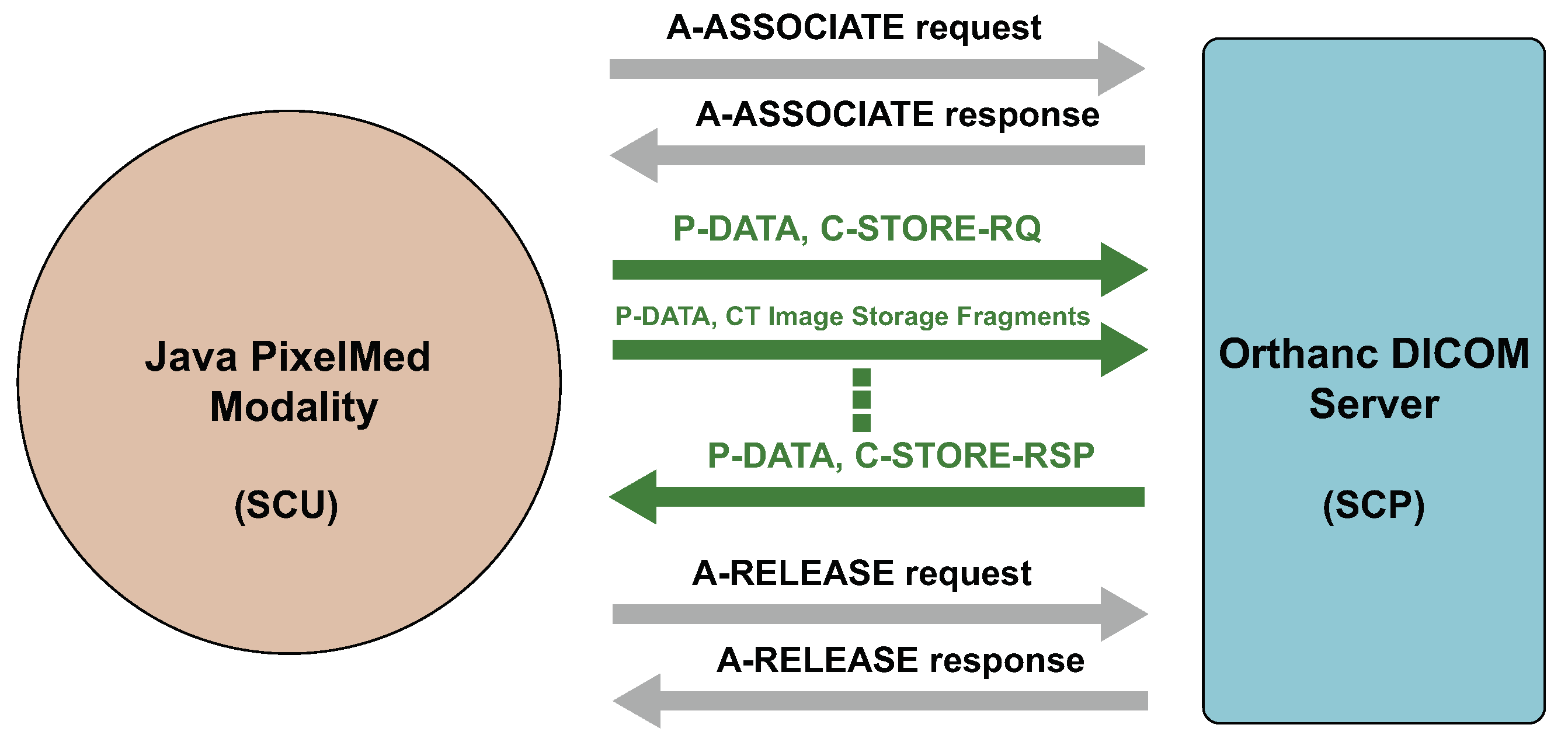
Due to the lack of datasets that we can use for our research for the evaluation of the covert channels, we created an experimental scenario. It consists of a modality (as a SCU) that sends images to a DICOM server (as a SCP), see
Figure 11. Detailed communication between the SCU and SCP can be seen in
Figure 12. For this purpose, we used the Elastic Compute Cloud (
https://aws.amazon.com/ec2/, accessed on 5 December 2021) (EC2) service from the Amazon Web Services (AWS).
We created two EC2 instances. In our scenario one of the instances plays the role of a modality, while the other is a DICOM server. The modality instance is from the type t2.medium, with the following configuration: AMD64 architecture, 2 vCPU, 4 GB RAM and 30 GB General Purpose SSD (gp2) storage. The server instance is from the type t2.large, with AMD64 architecture, 2 vCPU, 8 GB RAM and 30 GB SSD gp2 storage. Both instances run the Microsoft Windows Server 2019 Base 64-bit operating system with the code name “ami-0b17e49efb8d755c3”.
We implemented the modality in the Java programming language using the PixelMed library (
http://www.pixelmed.com/dicomtoolkit.html, accessed on 20 December 2021). It is a library which provides implementations of functions that can be used for creating associations between SCUs and SCPs, sending DICOM files, receiving, moving and other DICOM operations.
For our experiments we used the Orthanc DICOM server (
https://www.orthanc-server.com/, accessed on 20 December 2021) version 1.9.7. It is an open source and lightweight server with an ubiquitous web interface. Orthanc has support for all DICOM functions, REST API to automate the flow of images and SDK for integration with native applications.
For our experimental evaluation, we also recorded the traffic on the DICOM server. For this purpose, we used the tool Wireshark version 3.6.0 (
https://www.wireshark.org/, accessed on 20 December 2021).
We created three variants of the experimental scenario:
Scenario with legitimate traffic
Scenario with implemented covert channel—sending an ASCII covert message
Scenario with implemented covert channel—sending an AES encrypted covert message
In the first variant, the modality sends DICOM images to the Orthanc server. For our experimental scenario, in all variants we used images from the Public Lung Database (
https://www.via.cornell.edu/databases/simbadb.html, accessed on 20 December 2021) [
26]. It contains Computed Tomography (CT) images showing large lesions in the lungs. This dataset also consists of images from different categories such as: Emphysema, Single Large Nodules, Single Small Nodules, Repeat Single Session, CT Angiography, and others. For our experiments we used the Emphysema subset. It contains more than 5000 DICOM images. We used the images located in the following folder hierarchy EM0085/1.2.826.0.1.3680043.2.656.4.1.7.83/S02A01. Due to the protection of the patients’ privacy, this dataset has been anonymized. In this variant of our experiments, the modality takes a picture from the folder and sends it to the Orthanc server. The images are sent in one association and a random Message ID is generated for each DICOM message.
In the second variant of our experimental scenario, we implemented the covert channel with Message ID (CC1.1). The modality as a covert sender sends ASCII covert message to the DICOM server as a covert receiver. With one DICOM message, 2 hidden ASCII characters are sent.
In the third variant, we used the same implementation of the covert channel CC1.1 from the variant 2, but here an AES encrypted covert message is sent.
In all variants, the sending of DICOM messages is conducted in a random time interval of about 15 min, which means that for a time interval of 1 h about 4 images are sent. We recorded the traffic on the server side for a time period of 12 and a half hours at most. In this way, we are using 50 DIMSE STORE-RQ services for storing 50 images in the archive per each variant. For the covert traffic this corresponds to the sending of 100 characters.
To show some insights of how it is likely to capture irregularities in Message ID half values, we are using the same number of DIMSE STORE services for three types of traffic: regular traffic, covert traffic with ASCII characters and covert traffic encrypted with AES block cipher.
Figure 13 plots the frequency distribution of the 8-bit Message ID half values for regular traffic for two datasets,
P and
R. One can notice that there are quite similar.
Figure 14 and
Figure 15 plot the frequency distribution of the 8-bit Message ID half values for covert traffic with ASCII characters and encrypted with AES block cipher, respectfully. The difference in the first case from the regular traffic is more obvious, than in the second case when AES is used.
Because we do not have real hospital traffic for a long period of time, we can use the probability distributions for the obtained datasets, P and R for regular traffic datasets, for covert traffic dataset with ASCII characters and for covert traffic dataset encrypted with AES.
From the
Table 4, one can notice that cross-entropy between
P and
R of two regular traffic datasets is pretty close to the cross-entropy between
P and
(between the first regular traffic dataset and the covert traffic dataset encrypted with AES). Also, both of them are quite different from the cross-entropy between
P and
(between the first regular traffic dataset and the covert traffic dataset with ASCII characters). So, even for small datasets and beside the existence of big differences between the entropy
and calculated cross-entropy values between the
P and other datasets, one can conclude that another regular traffic dataset
R and covert traffic dataset encrypted with AES
have almost the same distance to
, while the covert traffic dataset with ASCII characters
shows a much larger distance to
. This means that covert traffic with ASCII characters can easily be distinguished from regular traffic, even for smaller samples. For the AES encrypted covert traffic this is not a case.
Table 5 confirms this behaviour: it compares the obtained cross-entropy values between the second regular dataset
R and other used datasets.
We will leave the testing of different parameters of the methodology (e.g., threshold value for detecting a significant difference between the cross-entropy and the entropy of regular traffic) for future work and will conduct these experiments when real hospital traffic will become available to us.