Abstract
The paper focuses on the application of new orthogonal transforms in digital watermarking. Novel types of transforms and their characteristics are presented. Potential methods for watermark embedding and recovery are also proposed. They assume embedding hidden information in the transform domains using the luminance channel of the original image. Image spectra are obtained by dividing the original image into smaller blocks that then are further processed by performing the forward transform operation. A watermark is embedded by modifying the spectral coefficients with relatively low values. Since there are various types of transforms, the latter process is realized in an adaptive manner. The proposed solutions were evaluated by measuring the level of visual distortion with respect to the total size of the inserted data. Additionally, the bit error rate (BER) in the recovery phase is also analyzed. The elaborated methods seem to be useful for applications in digital signal and image processing where high imperceptibility and low BER are of great importance. New orthogonal transforms were proved to be useful in watermarking tasks, and in some cases, they can even outperform the classic DCT approach.
1. Introduction
Digital watermarking is a method that consists of inserting hidden information into multimedia content, such as images, videos, or audio recordings. Nowadays, in all areas where these digital materials are transmitted, stored, or processed, it is a crucial task to provide adequate protection and prevent the sensitive or valuable data from unauthorized access, modification, or theft. Watermarking algorithms can address all these problems. In addition, they can be used to detect copyright infringement, undesired manipulations, and distribution. Solutions based on watermarking may be also applied in steganographic communication and for the pseudonymization or anonymization of sensitive and private information.
A watermarking algorithm should be properly designed by taking into account the target application and key features it should provide. The most common characteristic is low visual distortion upon the embedding process as well as high recovery accuracy when the watermark is extracted. It should also guarantee that it will be capable of storing sufficient amount of data to perform all the functions it was designed to realize.
A watermark can be embedded in the spatial or transform domain. Operating in the spatial domain means direct modification of multimedia data, such as, for example, color bands or brightness in case of images. The typical example of this approach is the Least Significant Bit (LSB) [1], where the least significant bits of multimedia objects are replaced with information bits. For instance, image pixel values might be altered by substituting the LSB for the message bitstream values. Transform domain techniques result in the modification of spectral coefficients in the given transform domain. They usually provide better results than the ones that operate in the spatial domain [2,3].
The most common transforms used for watermark insertion are discrete cosine transform (DCT) [4,5,6,7], discrete Fourier transform (DFT) [8,9], discrete wavelet transforms (DWT) [10,11], and Walsh–Hadamard transform [12]. In addition, transform-based methods can be used jointly with other techniques, such as, e.g., discrete fractional random transform (DFRNT) [3] or singular value decomposition (SVD) [13].
Usually, the aforementioned transform types are modified and enhanced in order to improve some aspects of the already known watermarking approaches. On the other hand, sometimes, even completely new transforms are proposed and tested as far as their applicability in various tasks is concerned. As an example, Periodic Haar Piecewise-Linear (PHL) transform was evaluated and confirmed to be useful for watermarking purposes by achieving promising results and even outperforming classic DCT transform in some aspects [14]. Another attempt was preseneted in [15], where multiparameter discrete transforms based on discrete orthogonal polynomials are used for watermark embedding.
In this paper, another set of recently introduced orthogonal transforms has been investigated with regard to their applicability in digital watermarking [16].
The paper is organized as follows. The following section presents the transform types that are analyzed. Section 3 describes the watermark embedding methods used for the assessment of the usability of the transforms being examined. Section 4 contains the experimental results and comparisons of the proposed solutions with the DCT approach. Finally, Section 6 presents the conclusions and future work.
2. New Orthogonal Transforms
The transforms analyzed in this paper were first proposed in [16]. The main characteristic of these transforms is that their matrices are orthogonal and symmetric. This makes it possible to use only one matrix for both forward and inverse transform operation. Another key feature is the parameterization in matrix generation process. This allows for the creation of an infinite number of transform matrices and at the same time can result in achieving various spectra depending on the set of selected parameter values. In addition, some parameters may be used as a security feature. For instance, in order to create a sample transform matrix, the user only needs to define its size and first three elements. These three values can be treated as a security mechanism that can prevent unauthorized persons from retrieving or getting access to secret information—for instance, in the form of a watermark embedded in a spectrum of an image. In addition, there are a few methods for matrix generation. The five major ones will be briefly introduced in the below subsections.
2.1. Full Non-Exponential Matrix
The matrix has a square shape and size (). This form of matrix has a recurrent structure and can be generated by using the below formula:
and
A sample matrix for is presented below:
For matrices , where , it is sufficient to select only the first three elements of the first row, and the remaining elements need to satisfy the following relation:
In this way, the basis sequence consisting of N elements () is obtained. Then, the following relations hold true:
where:
—transpose matrix I—unit matrix
—inverse matrix
C—coefficients
2.2. Full Non-Exponential Matrix with Arbitrary Parameter
For the non-exponential type of matrix, presented in the previous subsection, for each subsequent group of four elements of basis sequence:
there is a relation:
The coefficient can be any positive number. Then, each subsequent group of four elements of the basis sequence may be calculated by multiplying the previous group by satisfying Condition (4).
This way, the basis sequence will have the following form:
where —positive real number
2.3. Full Exponential Matrix
This type of matrix is created when its basis sequence consists of consecutive powers of the real number a having the following form:
where:
a—any real number,
k—integer,
Therefore, the formula for the generation of the exponential type of matrix of size , takes the form of the below recursive relation:
where
and , k—integer
For , we have:
2.4. Sparse Non-Exponential/Exponential Matrix
This type of matrix is created by generating matrices of smaller dimensions and positioning them on the diagonal of the matrix currently being created. The sparse matrix has the following form:
where
—matrix with dimension
For example, for the parameters , the matrix is
where
3. Watermark embedding
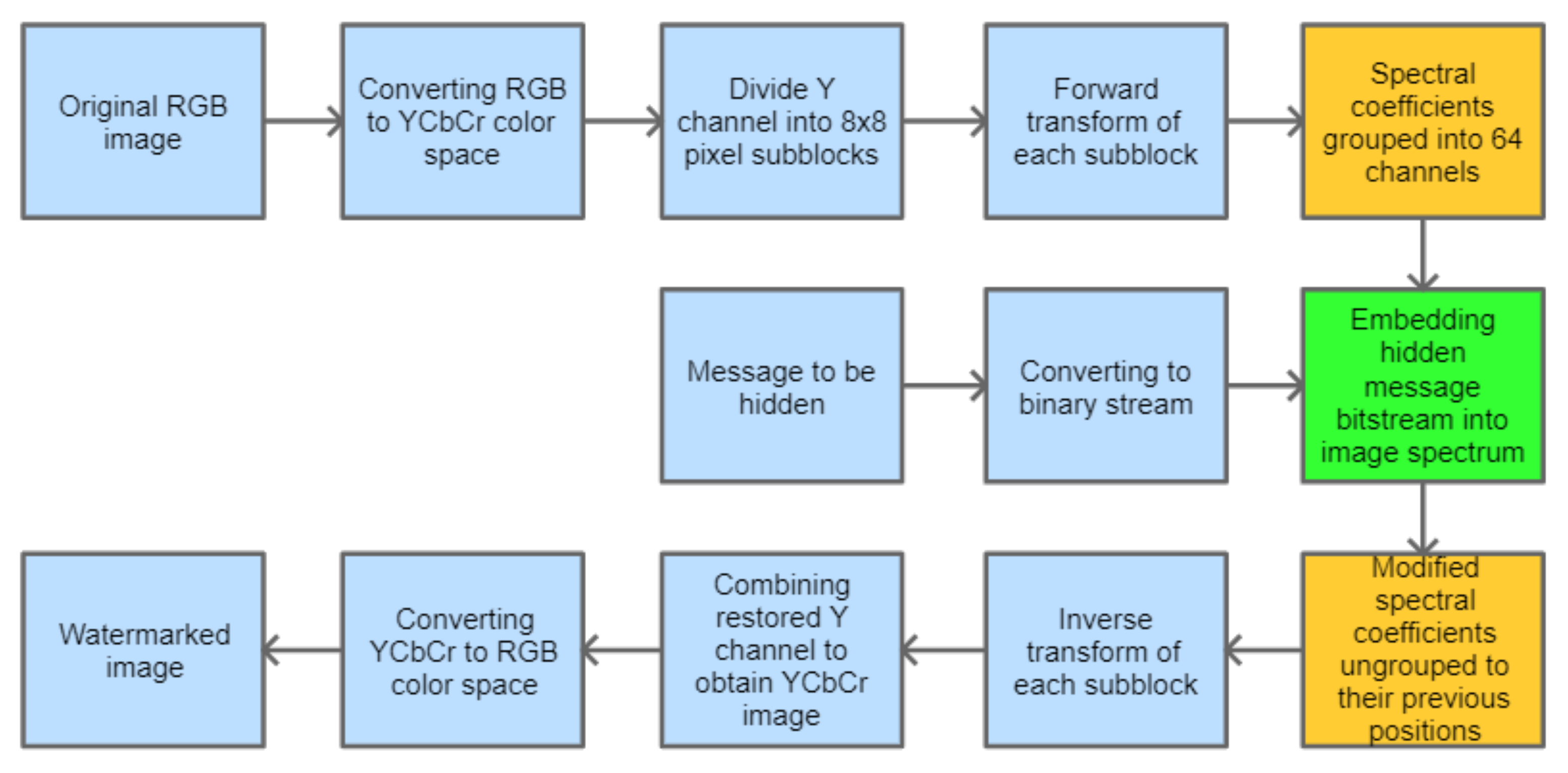
The watermarking algorithm, analyzed in this paper, is based on embedding a random bitstream in the domain of one of the transforms described in Section 2. It is assumed that only the grayscale image, represented by the luminance channel, is processed. As it is usually done, forward and inverse transform operations are performed on smaller subimages, having the size of 8 × 8 pixels. As a result, we obtain a lot of processed blocks, each containing 64 spectral coefficients. This is the standard procedure, which is followed before the subsequent steps are realized. This base procedure for watermark embedding is depicted in Figure 1. The blocks highlighted in orange are optional. The block highlighted in green is the one for which different embedding solutions can be used. Since the aim of this paper is to gain some knowledge about the applicability of the novel orthogonal transforms in digital watermarking, several approaches, both simple and those more sophisticated, are investigated in order to learn which transform types and which embedding methods are the most suitable for specific cases and goals that we want to achieve. Thus, five approaches have been examined and verified. Methods 1 and 4 are classic techniques used as a reference, while methods 2, 3, and 5 are proposed as their adaptive extensions that aim at the efficient use of the presented matrix types. These approaches are presented in the following subsections.
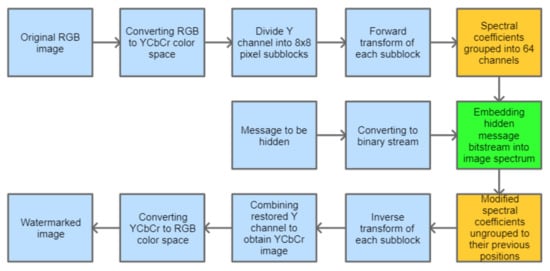
Figure 1.
Block diagram for the base process of watermark embedding.
3.1. Method 1: Direct LSB Modification of Image Spectrum (M1)
In this approach, the hidden message is evenly distributed in the image spectrum. Channel grouping is not performed; thus, the orange blocks from Figure 1 are skipped. The information bits are inserted into least significant bits of the selected spectral coefficients, similarly as in the JSteg algorithm [17]. This method is very simple, but its main drawback is that it does not analyze the spectrum of an image, and the embedding process for the given message length is always performed in the same way.
3.2. Method 2: Adaptive Substitution of Grouped Spectral Coefficients (M2)
This method consists of grouping of the spectrum and then selecting these channels that carry the lowest amount of signal information. Spectrum grouping means that each channel contains all the spectral coefficients that were taken from the same position of each block processed in the forward transform step. This results in 64 transform channels. The further processing is dependent on the nature of the given transform. For instance, the Discrete Cosine Transform has a property of locating the coefficients that represent the low frequencies, to which human eye is much more sensitive, in the top-left channel of the image spectrum with applied grouping [18]. Then, moving across the spectrum in the zigzag order leads to channels representing higher frequencies which are not so noticeable for people. That is why a watermark is inserted in the middle-band frequencies as a trade-off between high robustness and good visual quality. During JPEG compression, the coefficients from the bottom-right channels, representing high frequencies, are removed. However, this paper will not focus on robustness to different attacks such as compression, and for the testing phase, the PNG image format was selected since it supports lossless data compression. Nevertheless, in case of the transforms described in Section 2, their nature may be diverse, and in order to assure that the conditions related to the visual quality and recovery accuracy are met, it is not possible to always follow the same scheme. Therefore, the blocks in which the information bits are inserted are determined in an adaptive manner. This is realized by the calculation of mean values for all the spectrum channels and sorting them in the ascending order. Then, based on this order, the spectral coefficients from the following channels are modified in order to store the information bits. This method consists of replacing the spectral coefficient values with information bit values multiplied by the given constant. Up to some extent, the bigger this constant is, the higher the accuracy in the recovery phase. However, it is accompanied by the higher degradation of the quality of the image with an embedded watermark.
3.3. Method 3 (M3): Adaptive LSB Modification of Grouped Spectral Coefficients
In order to improve the quality of the watermarked image and at the same time be able to recover the hidden information with high accuracy, the previous method was slightly modified. In contrast, the information bits are inserted into least significant bits of the spectral coefficients for the given channels. Although it requires casting real spectrum coefficients to integer type and then setting the last bit to zero or one, this approach provides satisfactory results as far as visual perception and recovery accuracy are concerned. Except for the rounding operation, statistically, only half of the least significant bit replacement operations will result in a change of the coefficient value.
3.4. Method 4 (M4): Standard QIM Approach
This method also involves the grouping of spectral coefficients. However, the embedding process is different, and its details are presented in [4]. It is based on the quantized projection embedding where randomly permutated columns of a Hadamard matrix are used as base vectors. The projection is quantized with a quantization step based on the default JPEG quantization table. Then, it is used to modify the vector of coefficients from the given block by applying the quantization operator, corresponding to a bit value of the embedded data, for the consecutive frequency bands.
In order to reconstruct the image when all bits are embedded, the transform coefficients need to be reordered back to their previous position, and the inverse transform needs to be applied.
In the extraction phase, all previous steps need to be performed in order to calculate the projection which is then rounded with respect to the given quantization step. When the result is an even number, then the recovered bit is ’0’; otherwise, it is ’1’.
3.5. Method 5 (M5): Adaptive QIM Approach
In contrast to the previous method, this approach uses adaptive channel selection for watermark embedding, depending on the transform type, instead of following the zigzag order. This limits the undesired effects observed when applying a zigzag order in the watermark embedding process for the set of transform types described in Section 2. On the other hand, it may not suit so well for DCT transform, since in this case, a zigzag order is preferred.
4. Experimental Results
4.1. Image Dataset
For test purposes, 32 images from the ’Images 4k’ dataset [19] have been selected. The dataset consists of 2057 files. The selected images represent various visual characteristics in order to generalize the results and make them more reliable. These characteristics include low contrast, high contrast, low brightness, high brightness, and different color distributions (dominant colors and color variety). The width and height of test images were reduced by half, resulting in a 1920 × 1080 size to speed up the calculations and watermark embedding process.
4.2. Transforms Selected for the Experiments
The following transforms and their parameters were selected for watermark embedding:
- Full non-exponential matrix (NONEXP):
- Sparse non-exponential matrix (NONEXP_SPARSE):
- Full non-exponential matrix with arbitrary parameter (NONEXP_BETA):
- Full exponential matrix (EXP):
- Sparse exponential matrix (EXP_SPARSE):
4.3. Transform Preprocessing
In order to provide satisfactory results as far as both high imperceptibility and low error rate in the recovery phase are concerned, each matrix applied for forward and inverse transform operations had to be initially preprocessed. Upon creation of the matrix according to the standard procedure described in Section 4.2, all its elements are divided by the sum of all elements from the first row of the matrix. This results in all matrix elements belonging to the range: . In this way, when calculating the spectrum of an image, all the spectral coefficients will not reach high values, which will prevent the embedded bits from being lost while saving the image upon inverse transform operation. This transform preprocessing is mainly focused on the assurance that the whole message hidden in an image will be fully recoverable.
4.4. Algorithm Testing
The main targets for the analyzed watermark algorithms are the high imperceptibility of the watermark embedded in an image, high recovery accuracy, and large capacity of the watermark. Therefore, the Peak Signal-to-Noise Ratio (PSNR) is taken as a measure of perceptual quality, and the bit error rate (BER) indicates the level of incorrectly recovered bits. The measurements of these ratios were performed for watermarks inserted in the domains of transforms listed in Section 4.2.
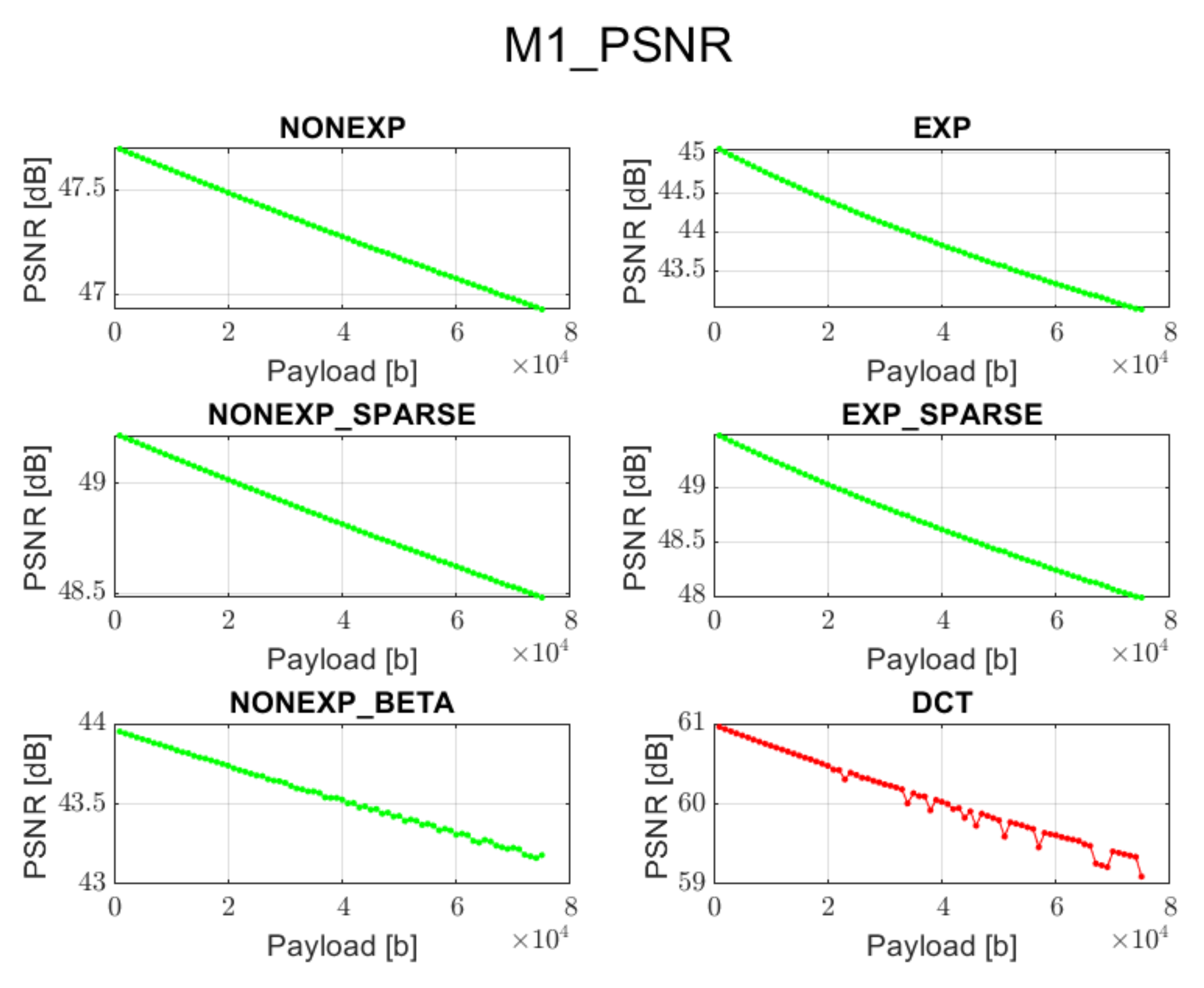
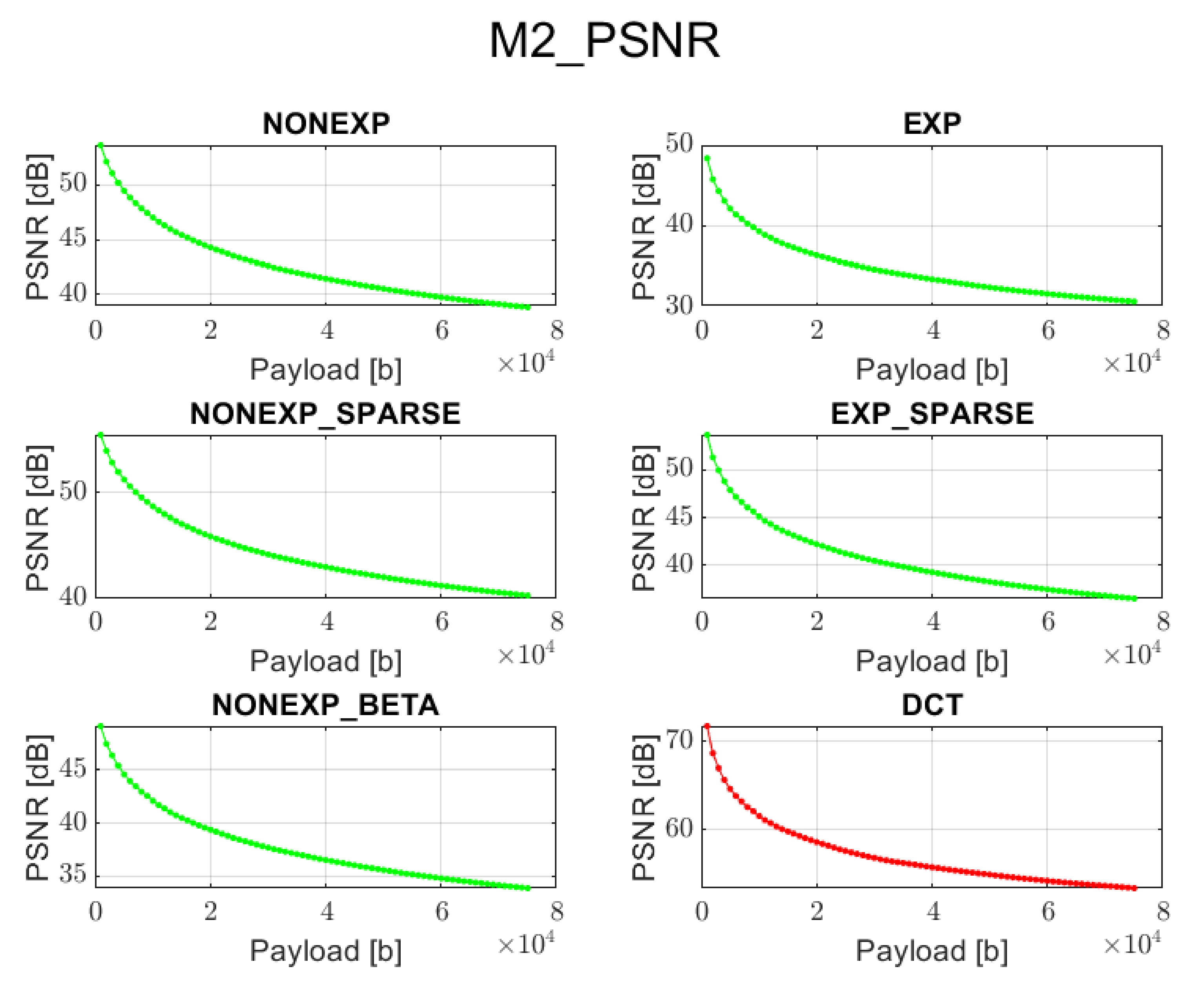
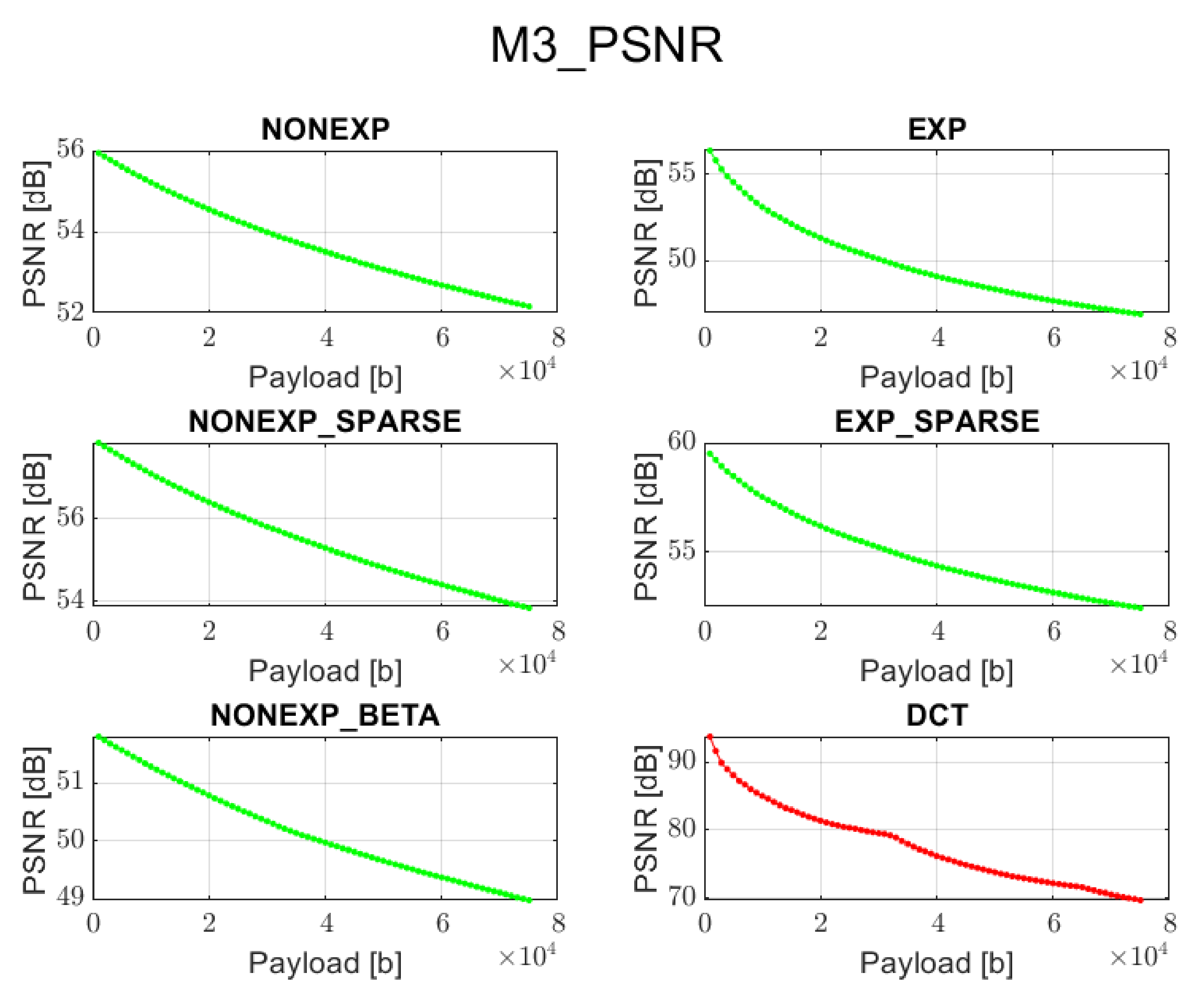
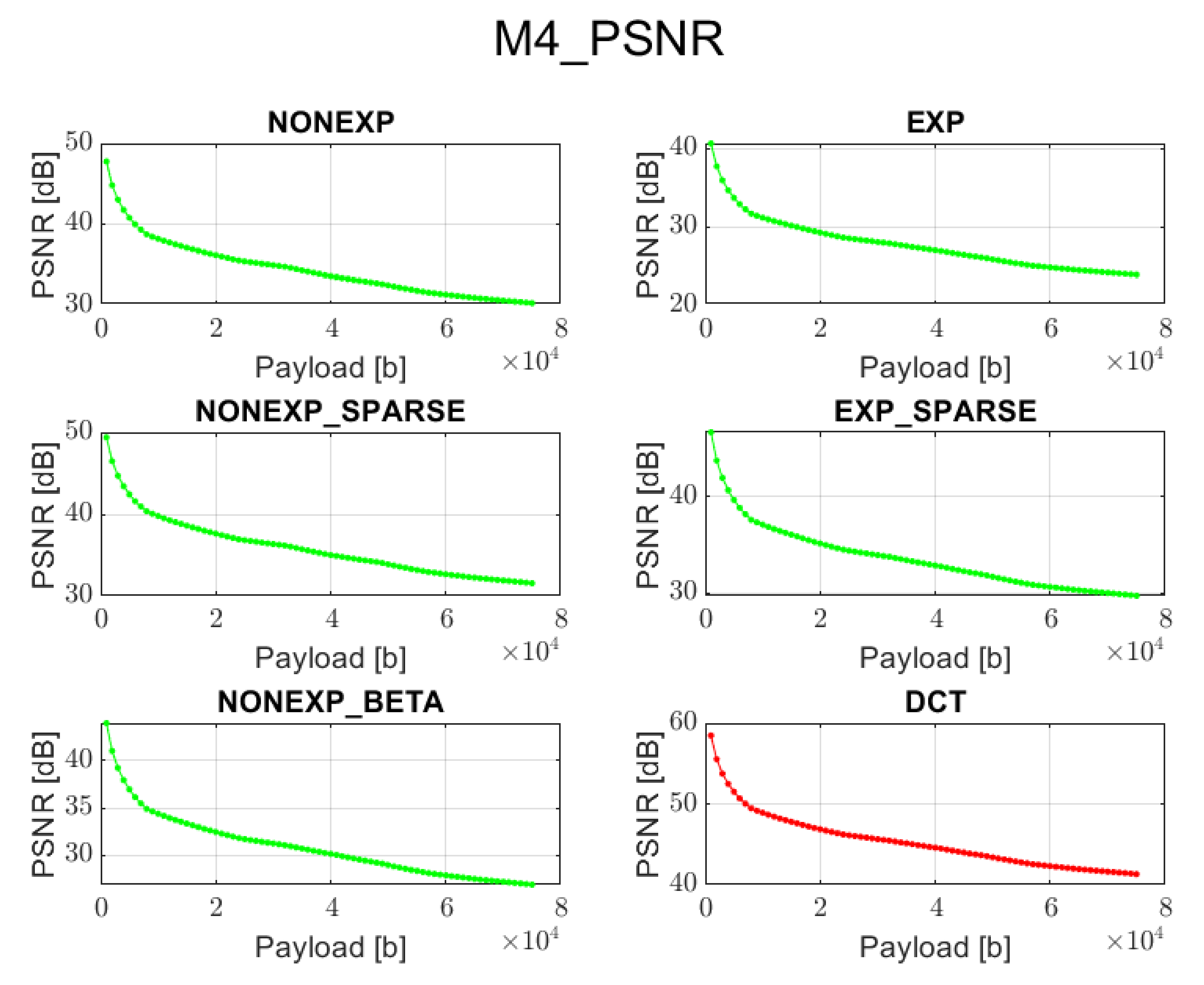
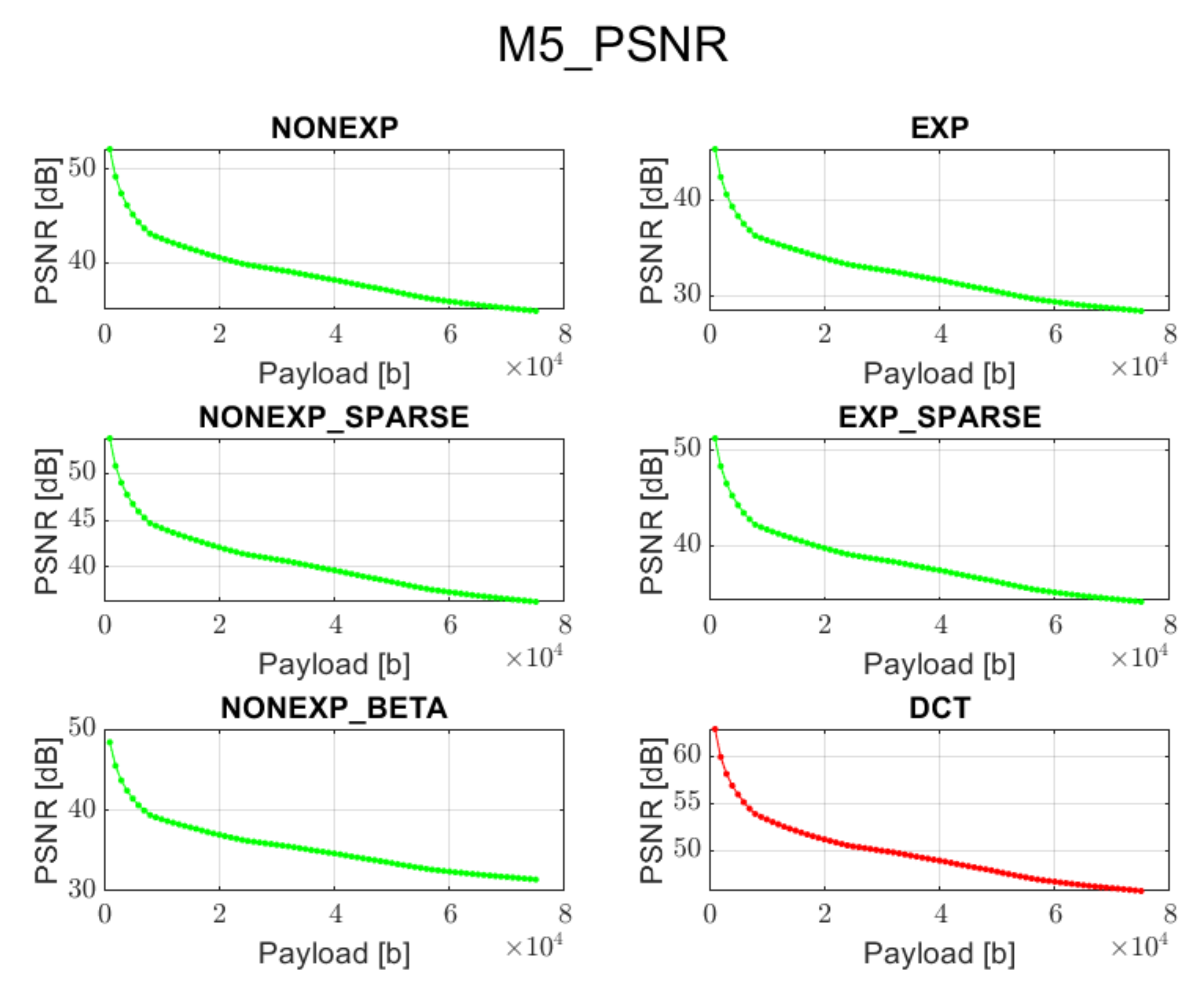
The relation between PSNR ratio and the length of the inserted bitstream, for all the above-mentioned embedding methods and transforms, is presented in Figure 2, Figure 3, Figure 4, Figure 5 and Figure 6 (in order to better distinguish both types of transforms, the graphs for the proposed orthogonal transforms are marked in green while for DCT in red). It can be observed that a perceptual quality of an image with a watermark embedded in the DCT spectrum is consistently better than in the case of the remaining orthogonal transforms. However, it is worth highlighting that for methods M1, M2, and M3, the BER is very poor, which means that the watermark cannot be recovered. Thus, the PSNR results in these cases need to be ignored. Only in the case of method M4 is the BER for DCT very low, so only the corresponding PSNR value may be used as a reference. Nonetheless, both transforms can provide satisfying results. It is assumed that the PSNR above 35 dB for 8-bit images indicates that the two images being compared are visually identical, with no perceptual loss of quality [20]. In most cases, such results are achieved, and a PSNR below 35 dB is observed only in case of longer bitstreams or embedding approaches, which apparently do not fit the given transform.
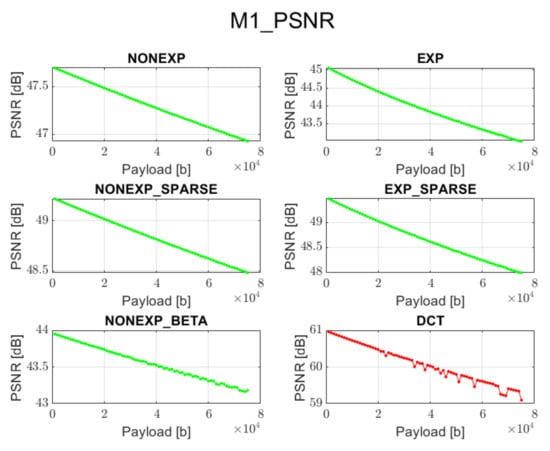
Figure 2.
Relation between PSNR and embedded data size for method 1 and all transform types.
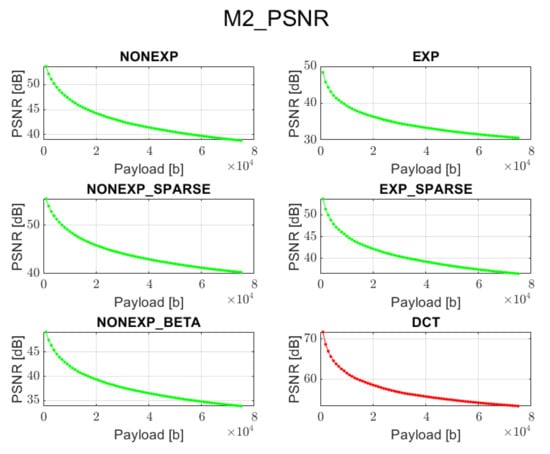
Figure 3.
Relation between PSNR and embedded data size for method 2 and all transform types.
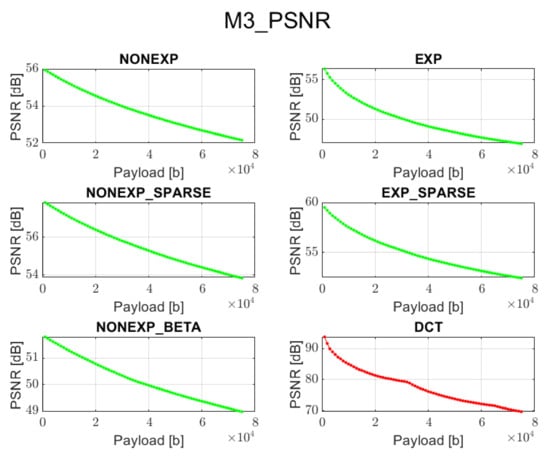
Figure 4.
Relation between PSNR and embedded data size for method 3 and all transform types.
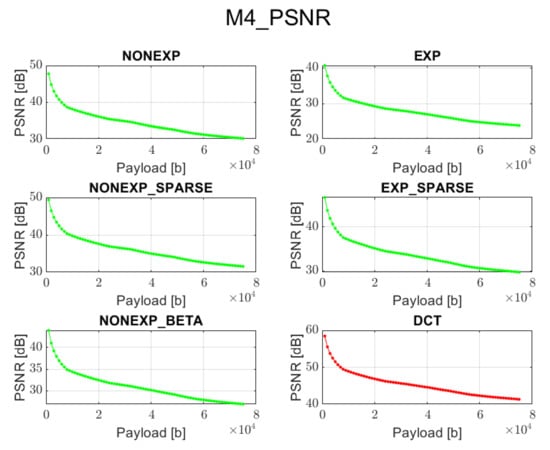
Figure 5.
Relation between PSNR and embedded data size for method 4 and all transform types.
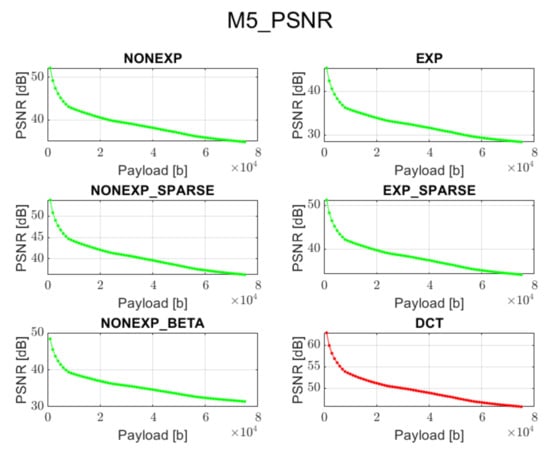
Figure 6.
Relation between PSNR and embedded data size for method 5 and all transform types.
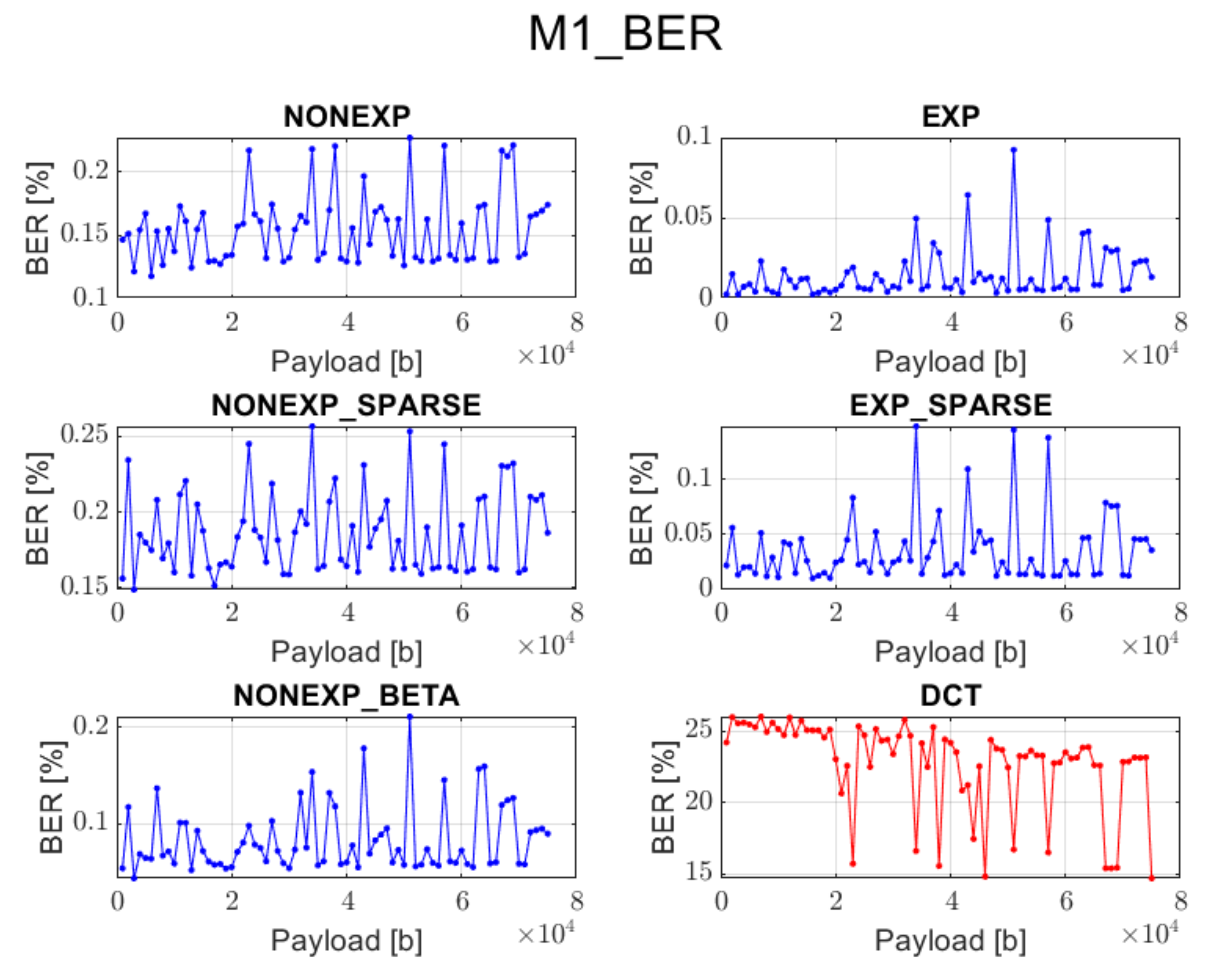
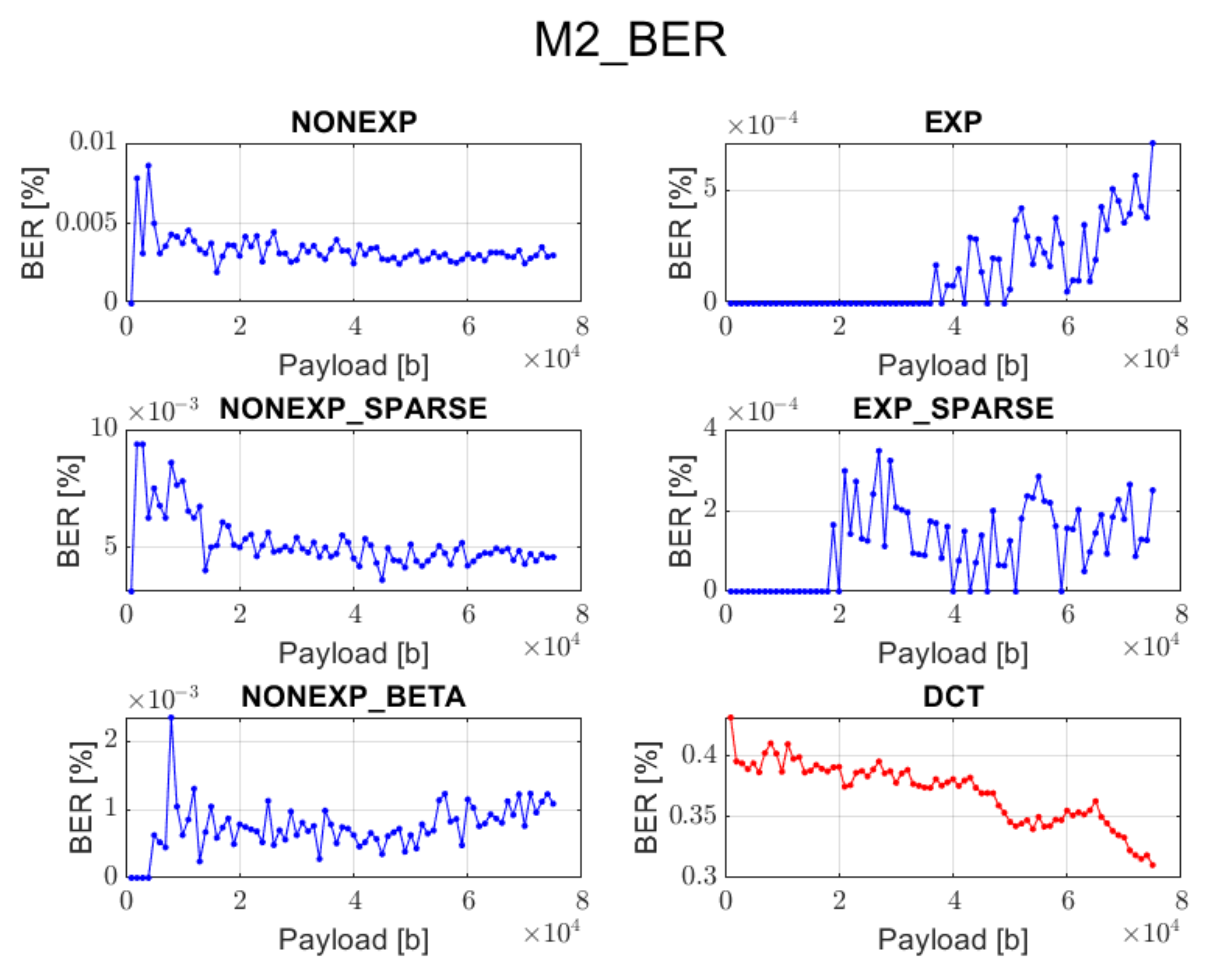
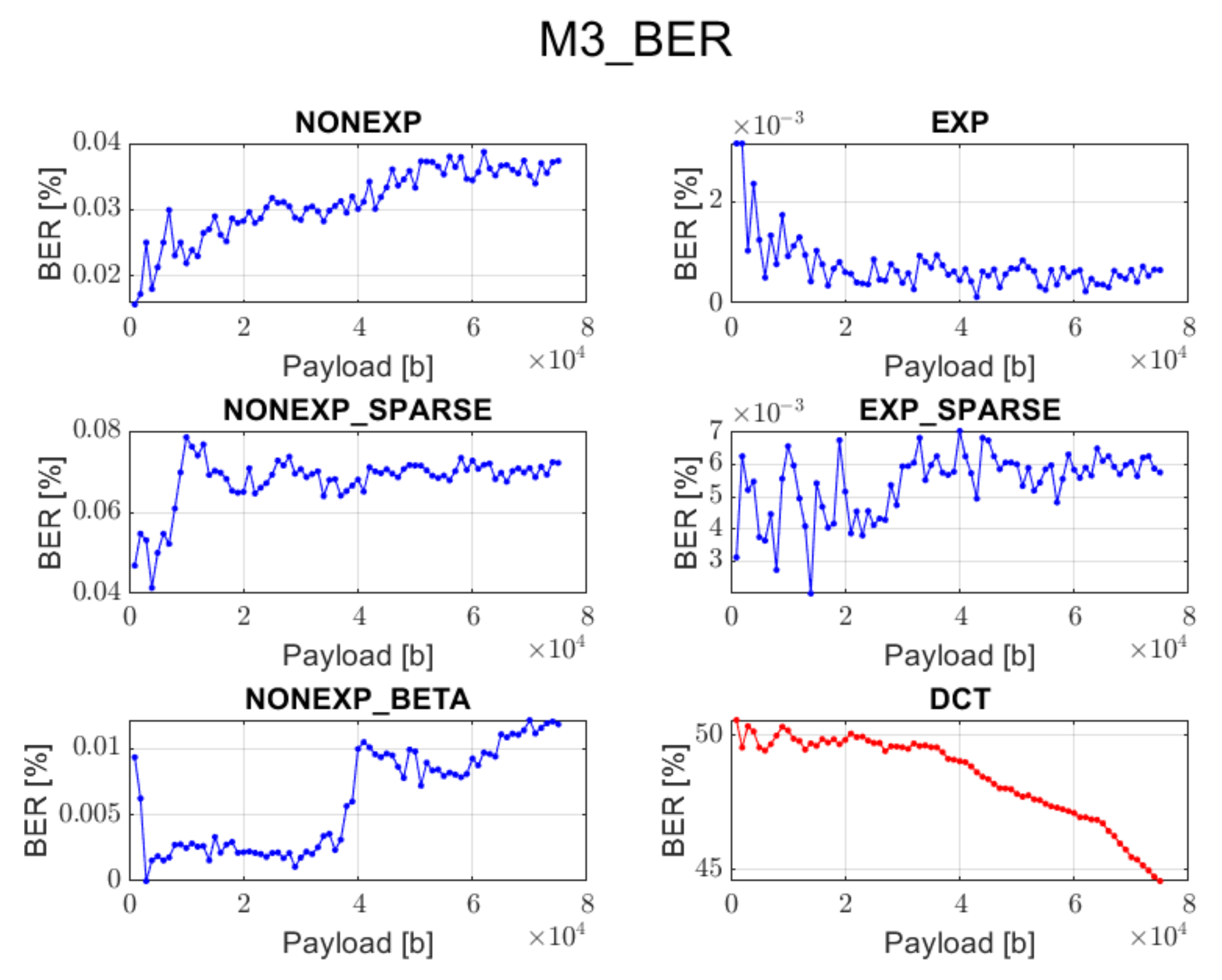
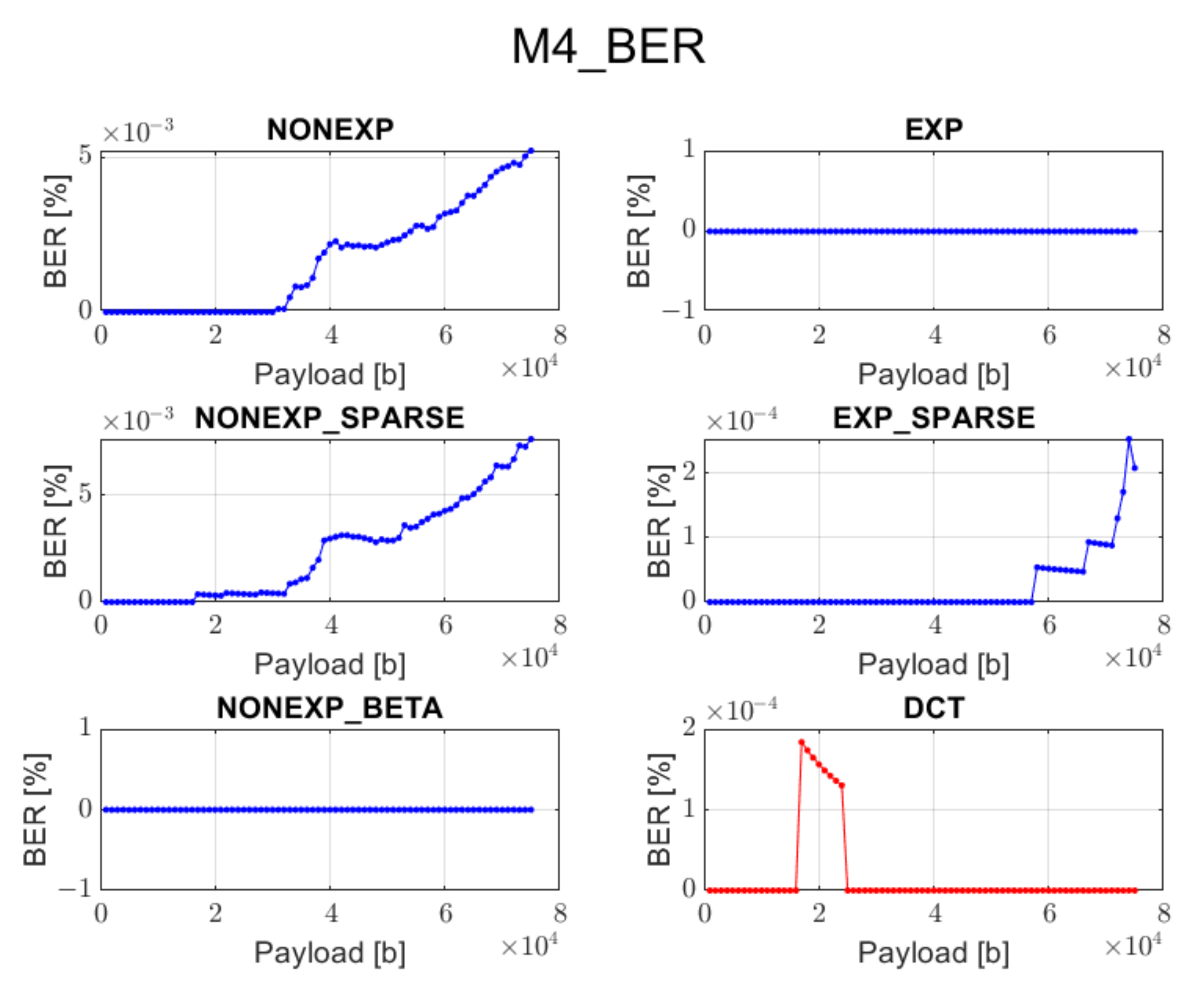
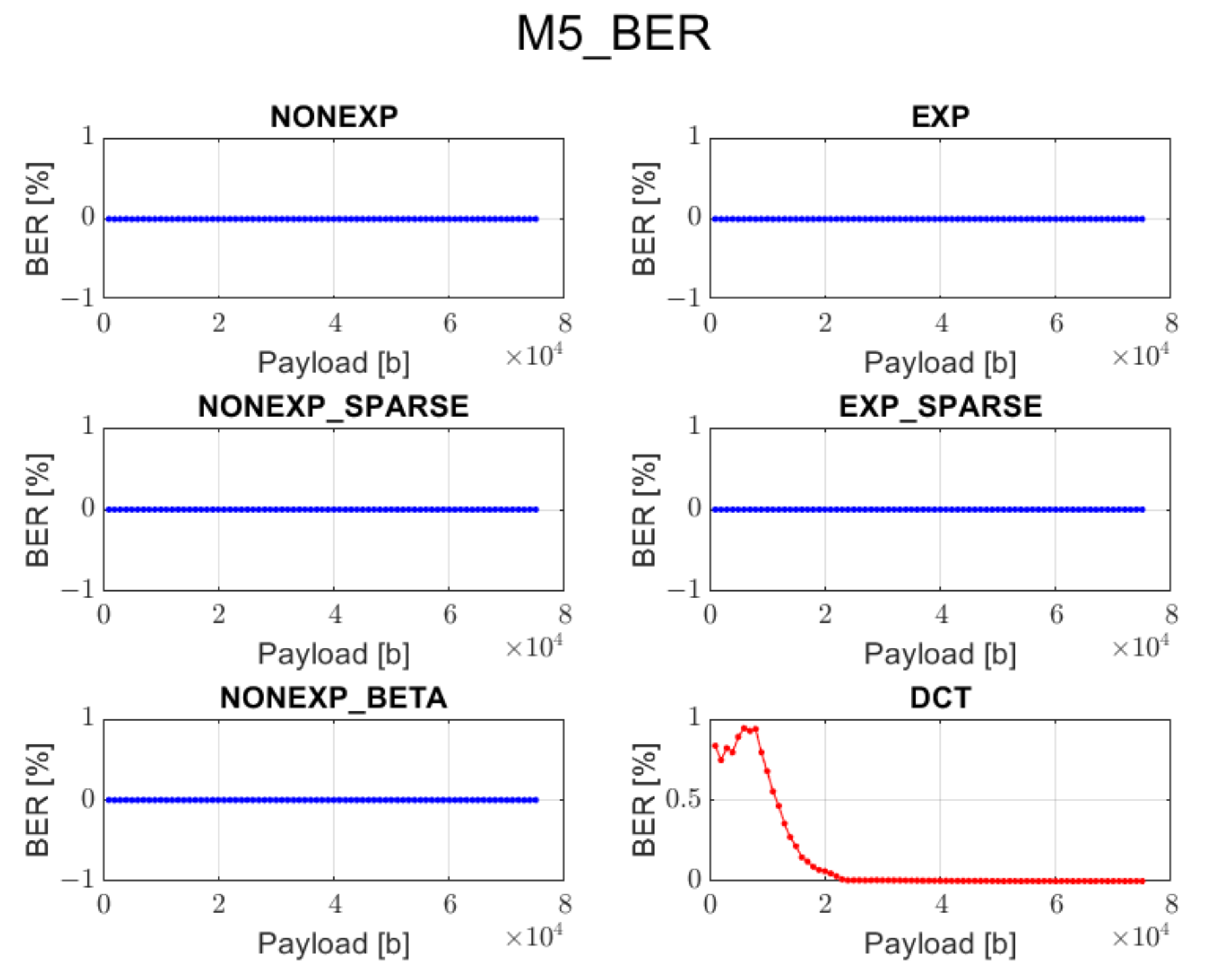
The relation between BER ratio and the length of a hidden message, for particular embedding approaches and transforms, is shown in Figure 7, Figure 8, Figure 9, Figure 10 and Figure 11 (in order to better distinguish both types of transforms, the graphs for the proposed orthogonal transforms are marked in blue while for DCT in red). As can be seen, some methods do not guarantee a sufficient level of accuracy during the extraction process. It is understandable in the case of Method 1 since it uses even distribution during the embedding stage. For proposed orthogonal transforms, methods 2, 3, and 5 provide adaptive embedding, which selects these blocks of spectral coefficients that should not degrade the original image and at the same time allow for almost full data recovery. The BER does not exceed 0.1% in most situations, with the total length of the watermark bitstream ranging from 1000 to 75,000 bits. When using method 4 or 5, the BER is predominantly equal to zero. The DCT approach provides the most reliable and acceptable results for method 4. This could be predicted due to the fact that this method uses a zigzag order for channel selection during the watermark insertion phase, which is specifically designed for this type of transform and is also used in JPEG compression [21]. Although a watermark inserted in the presented orthogonal transform domains seems to fit better in different embedding approaches, both transform types are useful when a large amount of information needs to be inserted into an image.
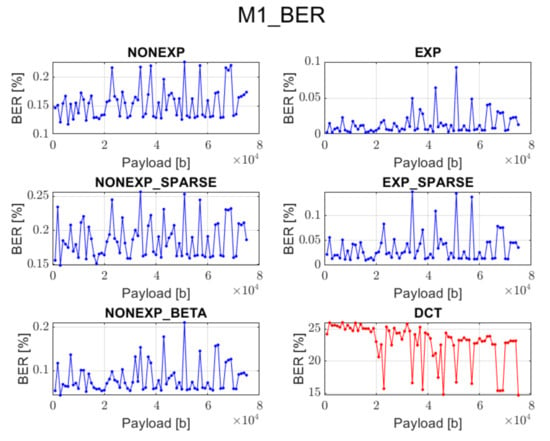
Figure 7.
Relation between BER and embedded data size for method 1 and all transform types.
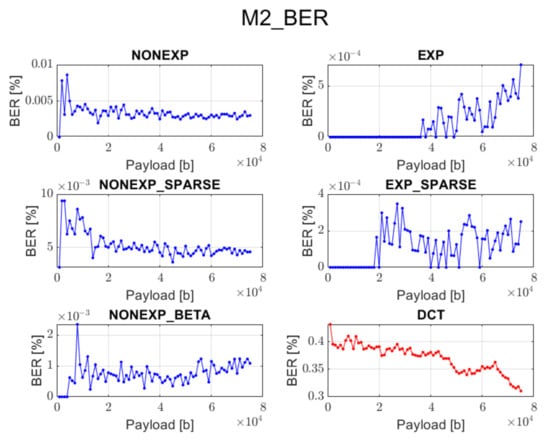
Figure 8.
Relation between BER and embedded data size for method 2 and all transform types.
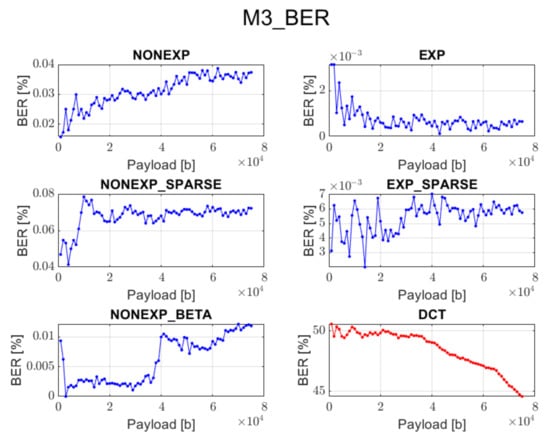
Figure 9.
Relation between BER and embedded data size for method 3 and all transform types.
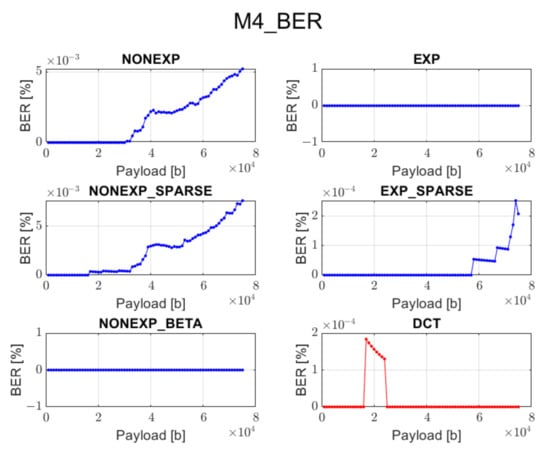
Figure 10.
Relation between BER and embedded data size for method 4 and all transform types.
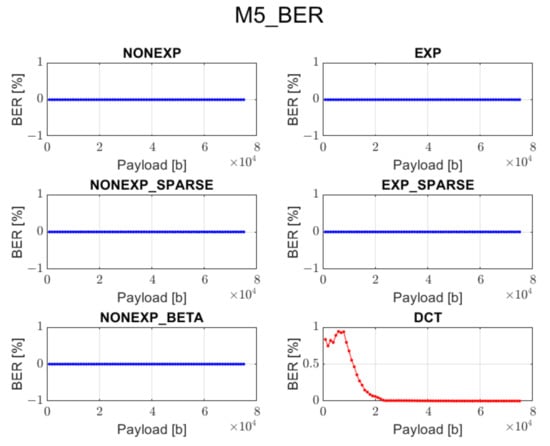
Figure 11.
Relation between BER and embedded data size for method 5 and all transform types.
As an example, the watermarked image for one of the test images is shown in Figure 12.

Figure 12.
Sample watermarked image obtained by using method 3 and sparse exponential matrix for the message length equal to 50,000 bits.
5. Summary of Results
Based on the performed experiments, we can conclude the following:
- Both approaches provide satisfying results as far as both high imperceptibility and data recovery accuracy are concerned.
- All presented types of transforms may be used to embed a watermark of high capacity.
- The DCT method works well only when using method 4 for data embedding, and then, it provides better visual quality and comparable accuracy of information recovery in comparison with the proposed transforms.
- The proposed orthogonal transforms provide satisfactory results for both PSNR and BER when using methods 2, 4, or 5 and for some cases also method 3.
- The DCT method cannot guarantee data recovery during the extraction process in case of methods 1, 2, 3, and 5.
- Spectrum analysis and adaptive watermark embedding guarantees that the proposed orthogonal transforms can provide promising results and may be found useful in many potential applications.
- Matrix parameterization is an interesting feature that might be used as a security mechanism for both data embedding and recovery.
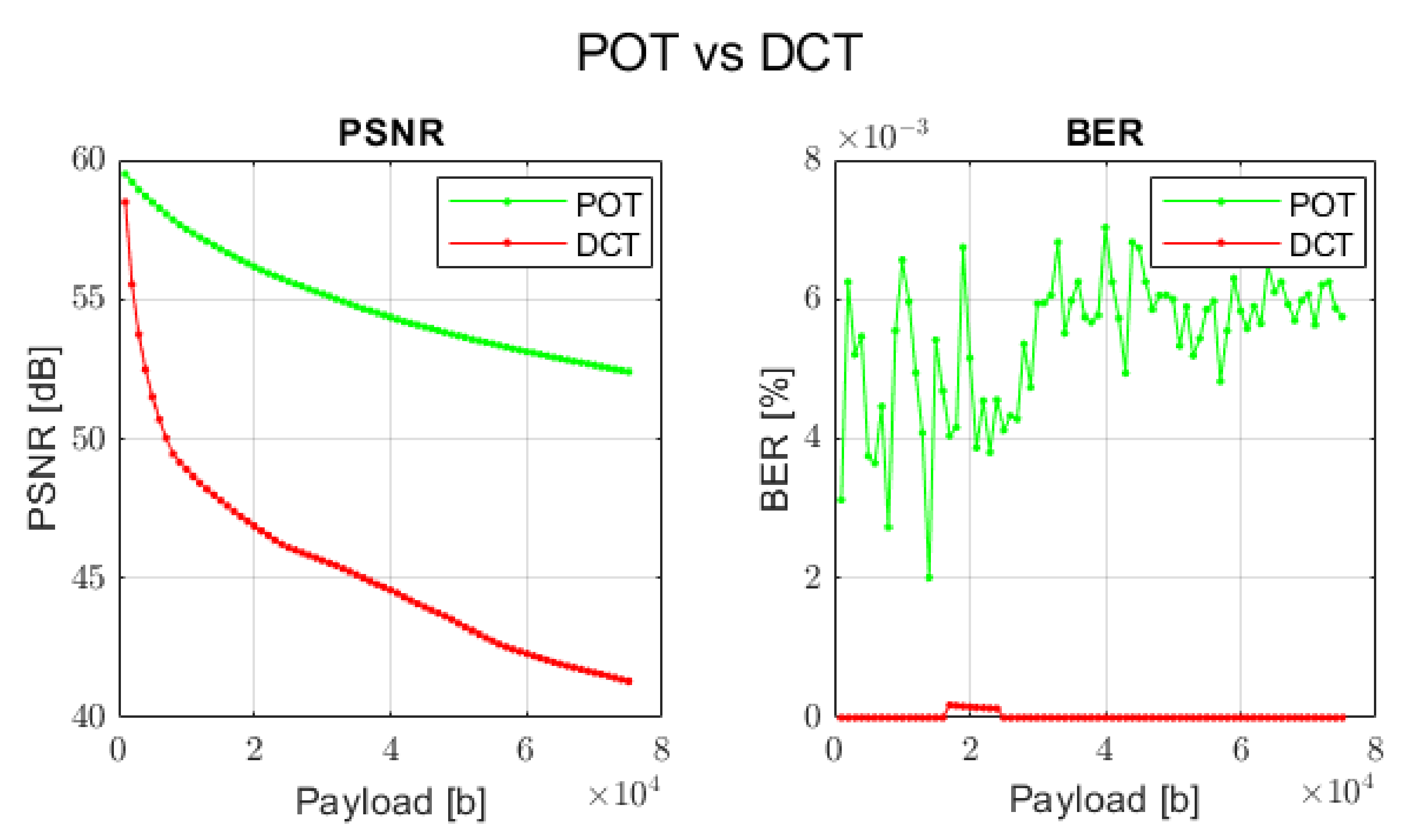
Since the proposed and DCT transforms have their unique nature, in order to compare these two approaches, the concrete combinations of watermark embedding methods and types of transforms have been selected.
- For proposed orthogonal transforms: method 3 and sparse exponential matrix of size 8 × 8 pixels.
- For DCT transform: method 4 and DCT matrix of size 8 × 8 pixels.
The comparison results are depicted in Figure 13.
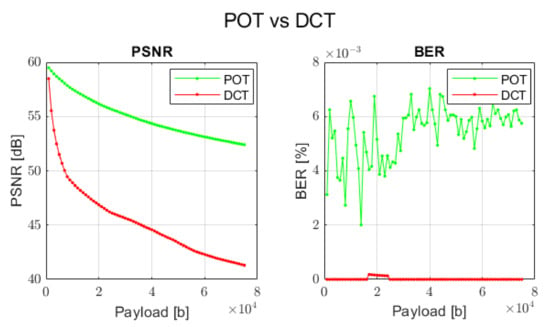
Figure 13.
Comparison between proposed orthogonal transform (POT) and DCT transform with respect to PSNR and BER.
As can be seen, the proposed orthogonal transforms can even outperform the DCT approach when the visual perception is our main goal. Conversely, if the main target of the application is to guarantee full data recovery and some level of image distortion is acceptable (but still satisfying), one can apply a different type of the proposed transforms with another embedding scheme. This is especially noticeable in case of method 5 and all types of transforms. This means that depending on the task one wants to realize, an adequate procedure can be selected in order to provide expected results.
6. Conclusions and Future Work
We have presented novel watermarking algorithms that utilize new types of orthogonal transforms. The elaborated methods satisfy the initially defined requirements as far as high perceptual quality and low BER are concerned. Simultaneously, they provide a high capacity of the inserted information. Moreover, the new orthogonal transforms in most cases provide better results than those of the DCT approach. All these features result in a wide range of potential applications in multimedia systems and services.
Further steps will include analysis of the algorithm behavior in the presence of various attacks and finding potential improvements in order to assure a sufficient robustness level. Moreover, it is planned to carry out research on the spectrum shaping by the selection and optimization of the transform parameters.
Author Contributions
Conceptualization, P.B. and A.D.; methodology, P.B. and A.D.; software, P.B.; validation, P.B. and A.D.; formal analysis, P.B. and A.D.; investigation, P.B.; writing—original draft preparation, P.B.; writing—review and editing, A.D. All authors have read and agreed to the published version of the manuscript.
Funding
This research was funded by the European Union’s Horizon 2020 Research and Innovation Programme, under Grant Agreement no. 830943, the ECHO project.
Institutional Review Board Statement
Not applicable.
Informed Consent Statement
Not applicable.
Data Availability Statement
Not applicable.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Yan, D.; Wang, R. Data Hiding for Audio Based on Piecewise Linear Haar Transform. In Proceedings of the 2008 Congress on Image and Signal Processing, Sanya, China, 27–30 May 2008; pp. 688–691. [Google Scholar]
- Sharma, P.K.; Sau, P.C.; Sharma, D. Digital image watermarking: An approach by different transforms using level indicator. In Proceedings of the 2015 Communication, Control and Intelligent Systems (CCIS), Mathura, India, 7–8 November 2015; pp. 259–263. [Google Scholar]
- Zhou, N.R.; Hou, W.M.X.; Wen, R.H.; Zou, W.P. Imperceptible digital watermarking scheme in multiple transform domains. Multimed. Tools Appl. 2018, 77, 30251–30267. [Google Scholar] [CrossRef]
- Lan, T.; Tewfik, A.H. A novel high-capacity data-embedding system. IEEE Trans. Image Process. 2006, 15, 2431–2440. [Google Scholar] [PubMed]
- Suhail, M.A.; Obaidat, M.S. Digital watermarking-based DCT and JPEG model. IEEE Trans. Instrum. Meas. 2003, 52, 1640–1647. [Google Scholar] [CrossRef]
- Li, H.; Guo, X. Embedding and Extracting Digital Watermark Based on DCT Algorithm. J. Comput. Commun. 2018, 6, 287–298. [Google Scholar] [CrossRef] [Green Version]
- Xu, Z.J.; Wang, Z.Z.; Lu, Q. Research on Image Watermarking Algorithm Based on DCT. Procedia Environ. Sci. 2011, 10, 1129–1135. [Google Scholar] [CrossRef] [Green Version]
- Pun, C. A Novel DFT-based Digital Watermarking System for Images. In Proceedings of the 2006 8th international Conference on Signal Processing, Beijing, China, 16–20 November 2006. [Google Scholar]
- Liao, X.; Li, K.; Yin, J. Separable data hiding in encrypted image based on compressive sensing and discrete fourier transform. Multimed. Tools Appl. 2017, 76, 20739–20753. [Google Scholar] [CrossRef]
- Candik, M.; Matus, E.; Levicky, D. Digital Watermarking in Wavelet Transform Domain. Radioengineering 2001, 10, 1–4. [Google Scholar]
- Narang, M.; Vashisth, S. Digital Watermarking using Discrete Wavelet Transform. Int. J. Comput. Appl. 2013, 74, 34–38. [Google Scholar] [CrossRef]
- Kalarikkal Pullayikodi, S.; Tarhuni, N.; Ahmed, A.; Shiginah, F.B. Computationally Efficient Robust Color Image Watermarking Using Fast Walsh Hadamard Transform. J. Imaging 2017, 3, 46. [Google Scholar] [CrossRef] [Green Version]
- He, Y.; Hu, Y. A Proposed Digital Image Watermarking Based on DWT-DCT-SVD. In Proceedings of the 2018 2nd IEEE Advanced Information Management Communicates, Electronic and Automation Control Conference (IMCEC), Xi’an, China, 25–27 May 2018; pp. 1214–1218. [Google Scholar]
- Dziech, A.; Bogacki, P.; Derkacz, J. A Novel Watermark Method for Image Protection Based on Periodic Haar Piecewise-Linear Transform. In Proceedings of the International Conference on Multimedia Communications, Services and Security. Communications in Computer and Information Science, Kraków, Poland, 8–9 October 2020; p. 1284. [Google Scholar]
- Annaby, M.H.; Ayad, H.A.; Prestin, J.; Rushdi, M.A. Multiparameter discrete transforms based on discrete orthogonal polynomials and their application to image watermarking. Signal Process. Image Commun. 2021, 99, 116434. [Google Scholar] [CrossRef]
- Dziech, A. New Orthogonal Transforms for Signal and Image Processing. Appl. Sci. 2021, 11, 7433. [Google Scholar] [CrossRef]
- Fan, L.; Gao, T.; Yang, Q.; Cao, Y. An extended matrix encoding algorithm for steganography of high embedding efficiency. Comput. Electr. Eng. 2011, 37, 973–981. [Google Scholar] [CrossRef]
- Cabeen, K.; Gent, P. Image Compression and Discrete Cosine Transform. College of Redwoods. Available online: https://www.math.cuhk.edu.hk/~lmlui/dct.pdf (accessed on 30 January 2022).
- ‘Images 4k’ Dataset from Kaggle. Available online: https://www.kaggle.com/evgeniumakov/images4k (accessed on 30 January 2022).
- Aherrahrou, N.; Tairi, H. PDE based scheme for multi-modal medical image watermarking. BioMed Eng. OnLine 2015, 14, 108. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Ahmed, N.; Natarajan, T.; Rao, K.R. Discrete Cosine Transform. IEEE Trans. Comput. 1974, 23, 90–93. [Google Scholar] [CrossRef]
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).