Abstract
The Internet of Things (IoT) is rapidly growing and is projected to develop in future years. The IoT connects everything from Closed Circuit Television (CCTV) cameras to medical equipment to smart home appliances to smart automobiles and many more gadgets. Connecting these gadgets is revolutionizing our lives today by offering higher efficiency, better customer service, and more effective goods and services in a variety of industries and sectors. With this anticipated expansion, many challenges arise. Recent research ranked IP cameras as the 2nd highest target for IoT attacks. IoT security exhibits an inherent asymmetry where resource-constrained devices face attackers with greater resources and time, creating an imbalanced power dynamic. In cybersecurity, there is a symmetrical aspect where defenders implement security measures while attackers seek symmetrical weaknesses. The SILEX malware case highlights this asymmetry, demonstrating how IoT devices’ limited security made them susceptible to a relatively simple yet destructive attack. These insights underscore the need for robust, proactive IoT security measures to address the asymmetrical risks posed by adversaries and safeguard IoT ecosystems effectively. In this paper, we present the IoT vulnerabilities, their causes, and how to detect them. We focus on SILEX, one of the famous malware that targets IoT, as a case study and present the lessons learned from this malware.
Keywords:
cybersecurity; cyber-attacks; IoT; security; SILEX malware; smart homes; vulnerabilities; asymmetry; symmetry 1. Introduction
The Internet of Things (IoT) strives to connect everyday physical objects into an interconnected ecosystem of digital data that are accessible at any time and from any location. In the IoT, “things” are embedded with sensing, processing, and actuation capabilities and work independently to give smart and novel services [1]. In [2], the basic IoT architecture was described as follows: Sensors are attached to each IoT component in the first layer to record the environment, which is then sent across the network to the base station in the second layer. The data acquired at the base station are transferred to the next level for data analysis and prediction. The number of IoT devices is growing rapidly; by 2025, it is expected to reach 64 billion [3]. This continuing adoption of IoT devices around the world and the evolution of smart devices with more features than typical home devices, along with the absence of adequate security knowledge, has led to the appearance of new types of cyber-threats that have devastating and dangerous effects [4].
As a subset of IoT, the Industrial Internet of Things (IIoT) signifies a profound and transformative shift within the industrial landscape. It revolves around the seamless integration of sensors, devices, machinery, and data analytics into industrial operations. IIoT applications transcend diverse sectors, such as manufacturing, energy, healthcare, and agriculture. For instance, within manufacturing, IIoT plays a pivotal role in enabling predictive maintenance, thereby curtailing downtime and optimizing production processes. In the energy sector, it empowers intelligent grid management and resource optimization.
As more people and organizations invest in buying smart devices such as routers, CCTV cameras, sensors, and many other smart devices, cybercriminals are seeing financial chances of attacking these appliances [5]. They use exploited networks of smart devices to conduct Distributed Denial of Service (DDoS) attacks or other types of malicious attacks [6]. To know how these new types of attacks work, honeypots, which are fake networks used to attract cybercriminals and examine their behaviors [7]. Kaspersky detected more than 100 million IoT attacks from 276,000 unique Internet Protocol (IP) addresses in the first six months of 2019 [8]. This number is seven times higher than the number detected in the first half of 2018 when around 12 million were captured coming from 69,000 IP addresses [8]. The convergence of two different worlds, symmetry phenomena and the complex landscape of IoT vulnerabilities and attacks, may not be immediately apparent. However, there exist many ideas and insights that can illuminate the challenges and dynamics of safeguarding the IoT in an increasingly connected world.
In this paper, we focus on the main vulnerabilities existing in IoT devices, their causes, and how to detect them through organized detection stages. We also explore the relationship between symmetry concepts and IoT security, emphasized through a case study: the SILEX malware. By examining this complex connection, we shed light on the complexities of safeguarding IoT ecosystems in the face of asymmetrical threats. The lessons learnt from the SILEX malware are addressed, as well as recommendations for IoT security.
The contributions of this paper are as follows:
- Present the research carried out in the area of IoT attacks.
- Discuss the IoT security vulnerabilities, their causes, detection stages and actions.
- Overview the IoT attacks’ classification, their advantages and disadvantages from an attackers’ perspective.
- Overview the SILEX malware and the lessons learned in securing against this malware.
- Highlight the inherent imbalance in security capabilities between IoT devices and attackers.
- Explain the symmetrical aspect of the ongoing competition between cybersecurity defenders and attackers and emphasize the importance of addressing the inherent asymmetry in IoT security.
- Examine the SILEX malware as an example of an asymmetric cyberattack targeting IoT devices.
2. Related Work
In this section, we explain the asymmetry in IoT Security and present the research in the area of IoT attacks, vulnerabilities, and mitigations in Section 2.1 and Section 2.2, respectively.
2.1. Asymmetry in IoT Security
In IoT networks, there is often an asymmetry in terms of security capabilities between the devices (sensors, smart appliances, etc.) and the attackers. IoT devices are typically resource-constrained and may lack robust security mechanisms, making them vulnerable to attacks. Attackers, on the other hand, have more resources and time to exploit these vulnerabilities, creating an asymmetrical power dynamic. Table 1 summarizes the key aspects of asymmetry in IoT security, highlighting the disparities between IoT devices and attackers across various dimensions.

Table 1.
IoT Security asymmetry comparison: challenges faced by IoT devices versus advantages of attackers.
2.2. Literature Review
In this section, we present the research in the area of IoT attacks, vulnerabilities, and mitigations. A survey on detecting cybersecurity attacks on the Internet of Things using artificial intelligence methods was presented in [9]. The authors in [10] examined intrusion detection systems in the Internet of Things, including approaches, deployment strategies, validation strategies, threats, public datasets, and obstacles. A survey on attacks and countermeasures of cyber-threats to industrial IoT was presented in [11]. The authors of [12] investigated the impact of several forms of DoS attacks on IoT gateways and determined that the wired-to-wireless category is the most harmful. A deep study of how a honeypot system can be used to avert a DoS attack was proposed, and verified, in [13], while a study of different attacks targeting IoT systems comparing their damage and efficiency levels was presented in [14]. In [15], the authors studied the IP camera security posture and concluded that the camera has three vulnerabilities: data are not transferred encrypted; the rTSP URL used to stream data may be brute-forced; and the credentials are saved in a mobile application in clear text. DDoS attacks on both IPV4 and IPv6 networks were tested and compared in [16]. The authors concluded that IPV6 networks have a higher risk of being attacked through DDoS attacks. The security of video surveillance systems was reviewed in [17], and the authors provided best practices to protect them. The attacks, vulnerabilities, and methods to protect smart homes and cities were summarized and presented in [18]. The attacks that threaten the confidentiality, integrity, and availability of IoT devices were analyzed in [19]. In [20], the authors analyzed two types of internet-connected cameras and found new unknown security vulnerabilities. The authors in [21] presented a taxonomy of IoT attacks. They mentioned a range of threats that can compromise the security and functionality of connected devices and systems. Common IoT attacks include DDoS attacks, which flood IoT devices with traffic to overwhelm and disrupt their operations. In addition, MQTT exploit is the de facto standard communication protocol in the IoT systems and is a widely used lightweight messaging protocol designed for efficient communication between IoT devices and systems.
The challenges and obstacles faced when implementing IoT solutions were discussed in [22]. This could include cybersecurity concerns issues, data privacy, and scalability challenges. IoT systems, often comprising diverse devices and sensors, face vulnerabilities that can be exploited by malicious actors. Common cyber-threats in IoT include malware infiltration, data breaches, DoS attacks, and unauthorized access to operational technology networks. These attacks can disrupt essential industrial processes, compromise data integrity, and pose significant risks to safety and production. Interested readers can refer to [23], and [24] for further details about IoT standards, challenges, and cybersecurity strategies.
3. IoT Security
In this section, we discuss the IoT security vulnerabilities and the IoT symmetry in attacks and defense in Section 3.1 and Section 3.2, respectively.
3.1. IoT Security Vulnerabilities and Attacks
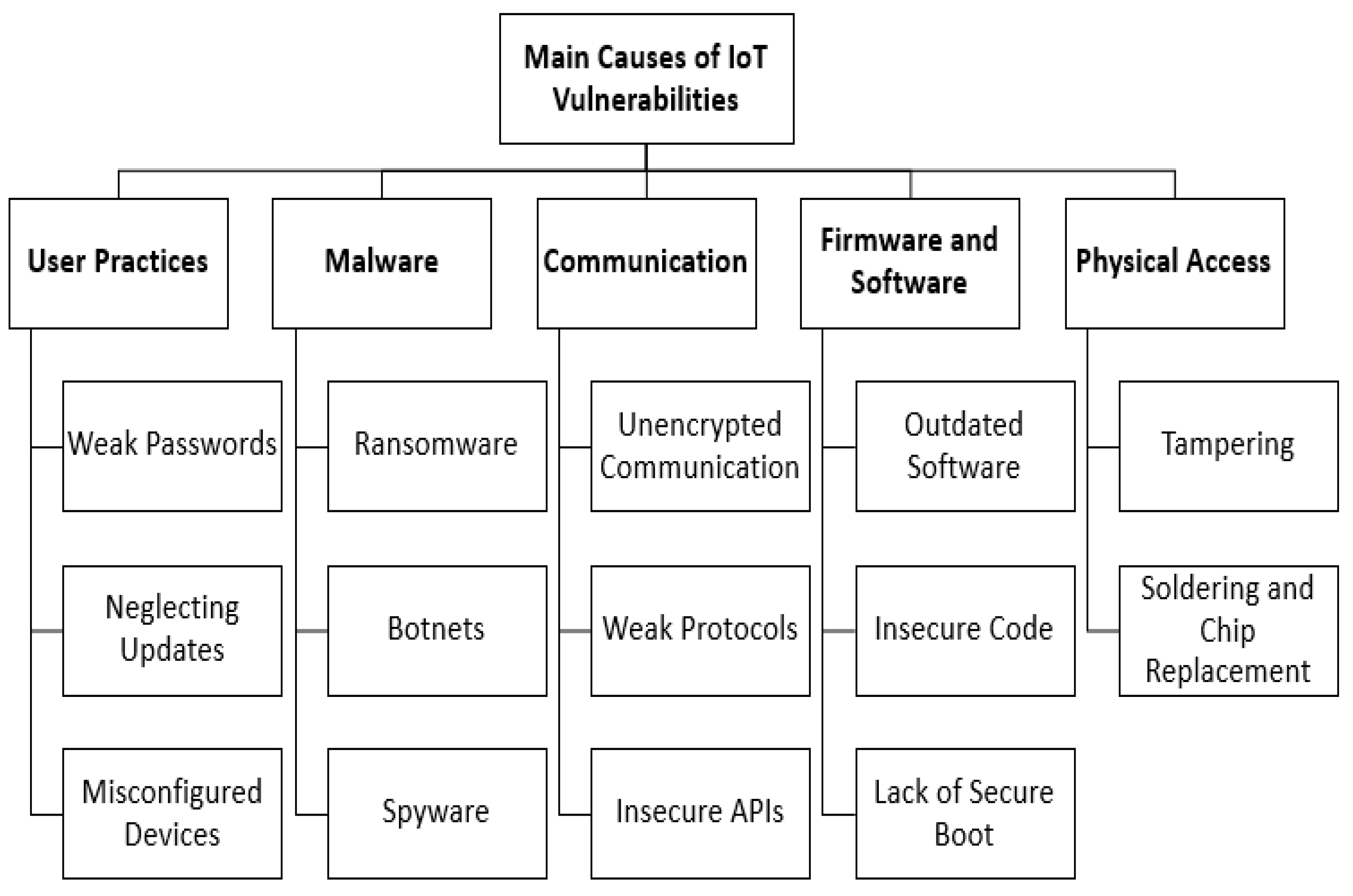
The IoT suffers from a lot of vulnerabilities. A taxonomy of IoT vulnerabilities was presented in [25]. The IoT Devices Vulnerability statistics to Palo Alto Networks 2018 mentioned in [26] reveal the weight of different categories of vulnerabilities. The users are the weakest link in the security ecosystem. The IoT security vulnerabilities are due to many reasons. Figure 1 depicts the main causes of IoT security vulnerabilities. Table 2 presents a comprehensive taxonomy of IoT vulnerabilities, categorizing them into distinct levels that are further classified into specific subcategories. Each subcategory is accompanied by illustrative examples, shedding light on the diverse range of threats that IoT systems face. Understanding and addressing these vulnerabilities is crucial in fortifying the security of IoT ecosystems and ensuring their reliable and safe operation.
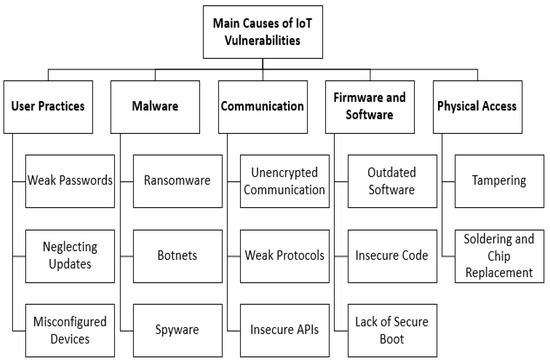
Figure 1.
The main causes of IoT vulnerabilities.

Table 2.
IoT vulnerabilities’ taxonomy.
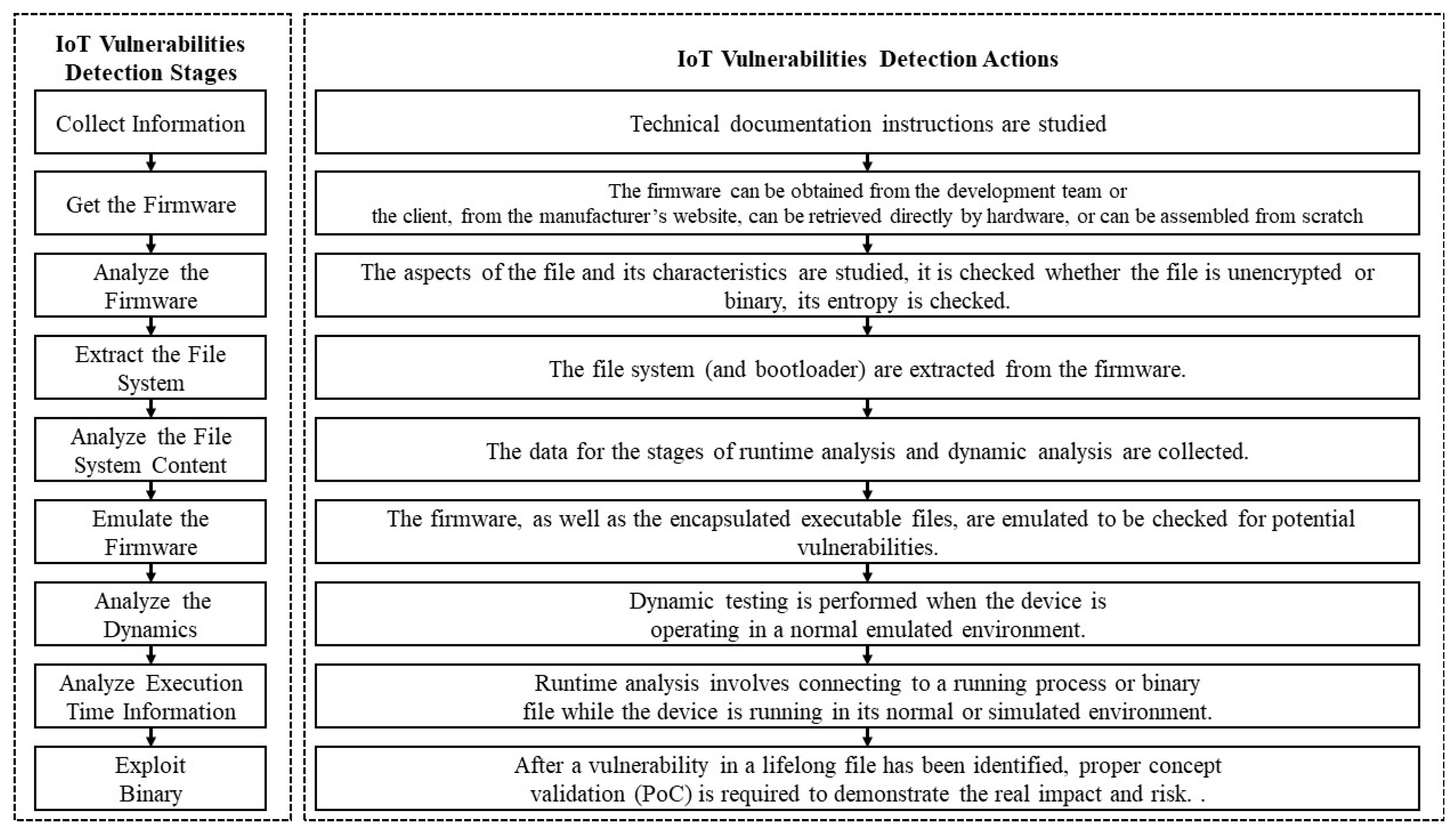
The security of Internet of Things (IoT) devices is of paramount importance in today’s interconnected world. As the number of IoT devices continues to proliferate, so does the potential attack surface for malicious actors. To safeguard against vulnerabilities and threats, a systematic and rigorous approach to IoT vulnerabilities’ detection and analysis is essential. The OWASP identified analysis stages in order to detect the IoT firmware vulnerabilities [26]. We summarized the different stages in Figure 2.
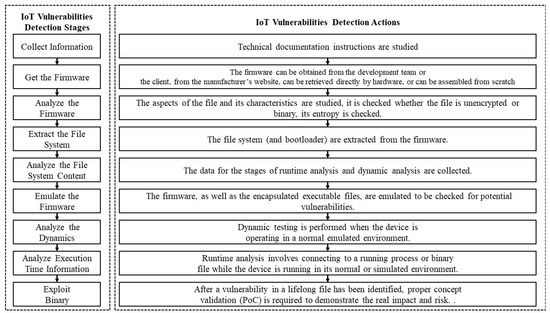
Figure 2.
IoT vulnerabilities’ detection stages and associated actions.
This process involves a series of carefully orchestrated stages, each with its specific objectives and methods. These stages aim to dissect and scrutinize every aspect of an IoT device, from its firmware to its runtime behavior, to uncover potential weaknesses that could be exploited by adversaries. In this comprehensive guide, we will delve into each stage of the IoT vulnerabilities’ detection process, providing in-depth insights, examples, and the tools required for effective analysis.
From the initial step of collecting information and acquiring firmware to the critical phases of dynamic analysis and exploitation, we will explore the intricacies of IoT security assessment. Each stage contributes to building a comprehensive understanding of an IoT device’s security posture, enabling organizations to fortify their defenses and protect against emerging threats.
Whether for a security professional, a developer, or an organization seeking to ensure the security of IoT deployments, the following steps explain the knowledge and methodologies needed to conduct thorough IoT vulnerabilities’ detection, ultimately contributing to a safer and more secure IoT ecosystem. Table 3 summarizes each step of the IoT vulnerability detection process along with the objectives, description, tools, examples, challenges, advantages, and disadvantages.

Table 3.
IOT vulnerability detection detailed process.
Successfully navigating these challenges while harnessing the advantages of each step is essential for conducting a thorough and effective IoT vulnerabilities’ detection process. The selection of methods and tools should align with the specific context of the device, its security measures, and the overarching goals of the assessment.
Calculating the cost of each IoT vulnerabilities’ detection stage involves considering various factors, including the complexity of the task, the expertise required, the time involved, and any associated tools or resources. These costs can vary widely depending on the specific context and organization. Table 4 summarizes the cost range and reasoning for the IoT vulnerabilities’ detection stages.

Table 4.
Cost associated with IOT vulnerabilities’ detection stages.
The actual costs can vary significantly depending on factors like the complexity of the firmware, the skills of the personnel involved, and the tools and resources available. In the following, we present other factors that can affect the cost of each stage in IoT vulnerabilities’ detection in more detail.
- Complexity of the Firmware:
- Complexity plays a crucial role in determining costs. More complex firmware, with numerous components and intricate code structures, will generally require more time and effort to analyze. Complex firmware may also use advanced security measures, increasing the expertise and tools needed for analysis.
- Skills and Expertise of Personnel:
- The skill level and expertise of the individuals involved significantly impact costs: Highly skilled and experienced security analysts may be more efficient and effective in identifying vulnerabilities, potentially reducing the cost. Junior or less experienced analysts may require more time for analysis and may not catch all vulnerabilities, increasing the cost. Specialized expertise in areas like reverse engineering, cryptography, and hardware security can also affect costs.
- Availability of Specialized Tools:
- The availability of specialized tools can affect both the cost and efficiency of the analysis as access to advanced debugging, reverse engineering, and emulation tools can streamline the analysis process, potentially reducing costs. The cost of acquiring and maintaining these tools should be considered.
- Time Required for Analysis:
- Time is a significant cost factor in IoT vulnerabilities’ detection: Extensive analysis and testing require more time, which can translate into higher labor costs. Rapid detection and resolution of vulnerabilities can reduce the overall cost by preventing potential security breaches.
- Firmware Source and Quality:
- The source of the firmware and its quality can affect costs: Obtaining firmware directly from the manufacturer or development team can be more reliable and reduce costs compared to reverse engineering. Poorly documented or obfuscated firmware may require more effort and time for analysis, increasing costs.
- Hardware Complexity and Protection Mechanisms:
- If the IoT device’s hardware has strong security protections, such as hardware encryption or secure boot processes, it can make firmware extraction and analysis more challenging and costly.
- Volume and Complexity of File System Content:
- The size and complexity of the file system content influence costs: analyzing a large and intricate file system with numerous configuration files and executables may require more time and expertise, increasing costs.
- Emulation and Runtime Analysis Environment:
- Creating a realistic emulation environment can be costly: Specialized hardware, software, and configurations may be needed for accurate emulation. The cost of setting up and maintaining this environment should be considered.
- Development of Exploits and PoCs:
- Developing proof of concept (PoC) exploits for identified vulnerabilities is a high-cost activity: Skilled programmers and security experts are required. Extensive testing and validation are necessary to ensure the PoC accurately demonstrates the vulnerability’s real impact.
In summary, the cost of IoT vulnerabilities’ detection is influenced by a combination of technical, personnel-, and resource-related factors. These factors can interact in complex ways, making it essential to consider them carefully when planning and budgeting for security analysis in IoT systems. The actual costs will depend on the unique characteristics of the IoT device, the security analysis process, and the organization’s capabilities and resources. In case the vulnerabilities are not detected, they can be exploited, which leads to attacks on the IoT. In [27], the authors classified the different types of IoT attacks. Table 5 presents a summary of IoT attacks, including their description, subcategories, examples, advantages from the attackers’ perspective, and cost factors.

Table 5.
IoT attacks’ classification, description, examples, advantages from attackers’ perspective, and cost factors.
3.2. IoT Symmetry in Attacks and Defense
In the context of cybersecurity, there is often a symmetrical aspect to the defense and attacks. For every security measure or defense mechanism put in place to protect IoT devices, attackers may seek out symmetrical weaknesses or vulnerabilities to exploit. This ongoing symmetry battle between defenders and attackers is reminiscent of the concept of symmetry in adversarial relationships. Table 6 provides an overview of the dynamic interplay between cyberattacks and defense strategies in the realm of cybersecurity, highlighting key aspects of symmetry and asymmetry.

Table 6.
Symmetry in cybersecurity: attacks versus defense.
4. The SILEX Malware
In the IoT networks, existing malware threats pose significant risks to the security and functionality of connected devices. For example, the Mirai botnet capitalizes on weak credentials to transform IoT devices into an army of bots for devastating DDoS attacks. Another example, the Stuxnet, although initially designed for industrial systems, underscores the potential dangers to IoT devices in critical infrastructure. In this article, our focus is to offer the interested reader a concise discussion of the SILEX Malware.
The use of weak passwords, default passwords, or passwords disclosed to the network has proven to be the most serious vulnerability thus far. Despite the obvious requirement for a secure password, some users continue to utilize default passwords. SILEX, an IoT malware, took advantage of this in June 2019, converting over 2000 IoT devices into “bricks” in one hour. It was built by a 14-year-old hacker, who instilled fear and began targeting and destroying IoT devices with weak passwords. SILEX is an internet-based virus designed to render IoT devices useless. It concentrated on Unix-based devices with pre-configured usernames and passwords. When SILEX discovers a susceptible device, it will overwrite all system storage with random data, erase the firewall rules and network settings, and then restart the system, rendering the device useless to users. This malware could only live for a day or two but was extremely detrimental to IoT companies in such a short time. The SILEX malware has attacked thousands of IoT devices.
The SILEX malware targets and compromises IoT devices in a systematic manner by using default credentials to log into IoT devices. But to retrieve the credentials, the malware first corrupts the IoT device storage, removing network configurations, then drops the firewall rules, and finally deletes the network configuration. As a result, the affected IoT devices become completely inoperable. SILEX achieves this by exploiting a combination of known vulnerabilities and easily guessable passwords, allowing it to infiltrate devices swiftly and spread its infection across vulnerable networks. Silex malware is so powerful that when an IoT device is affected, it is impossible to recover. However, by manually reinstalling the device firmware, one can recover the infected IoT device.
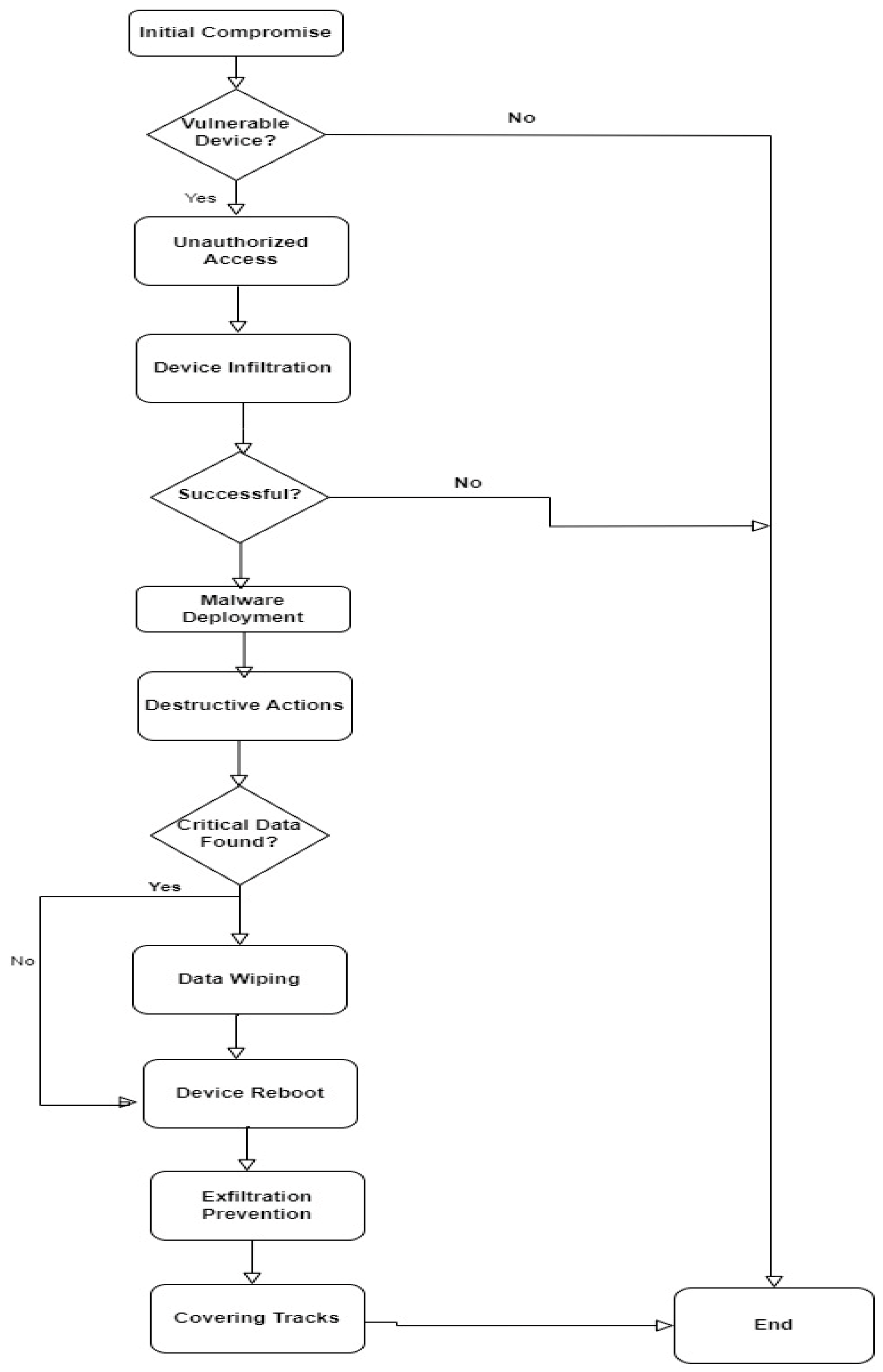
The attack steps for the SILEX malware on IoT devices generally involve the following:
- Initial Compromise:
Scanning for Vulnerable Devices: the malware scans the internet for IoT devices with known vulnerabilities, such as default passwords or unpatched software.
Unauthorized Access: once a vulnerable device is identified, the malware attempts to gain unauthorized access using default credentials or known exploits.
- 2.
- Device Infiltration:
Password Brute-Force: SILEX may attempt to guess the device’s password through a brute-force attack.
Exploiting Vulnerabilities: it may exploit known security vulnerabilities in the device’s software or firmware to gain access.
- 3.
- Malware Deployment:
Downloading and Executing Payload: once inside the device, SILEX downloads and executes its malicious payload, which includes components to target the device’s critical functions.
- 4.
- Destructive Actions:
Data Wiping: SILEX wipes the data on the device, including configurations and stored information.
Disabling Network Interfaces: it disables network interfaces to isolate the device from the internet, preventing remote access or updates.
Corrupting Firmware: the malware can corrupt the device’s firmware, rendering it inoperable.
Terminating Processes: it terminates critical processes, disrupting the device’s normal operation.
- 5.
- Overwriting Storage:
Overwriting Storage Devices: SILEX may write random data to the device’s storage, making data recovery impossible.
- 6.
- Device Reboot:
Forcing a Reboot: to ensure the changes take effect, the malware often forces the device to reboot.
- 7.
- Device Unusable:
Brick the Device: after these actions, the IoT device becomes effectively “bricked” or unusable. It can no longer perform its intended functions.
- 8.
- Exfiltration Prevention:
Terminating Data Exfiltration: SILEX may also prevent the device from exfiltrating sensitive data to external servers, limiting the attacker’s access to the device’s information.
- 9.
- Covering Tracks:
Deleting Logs: to minimize detection, SILEX may delete logs and traces of its activities.
The attack steps taken by the SILEX malware are illustrated in Figure 3.
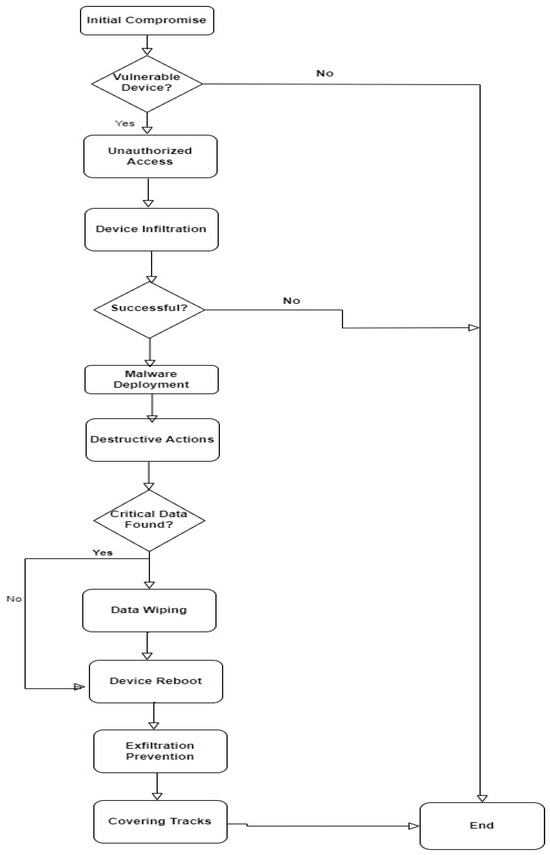
Figure 3.
SILEX malware IoT attack steps.
The SILEX MALWARE case study can be seen as an example of an asymmetric cyberattack targeting IoT devices. SILEX MALWARE, which emerged in 2019, was designed to target and compromise IoT devices, rendering them inoperable by deleting their firmware. This case study highlights the vulnerability of IoT devices to relatively simple yet destructive attacks. The lack of security measures or the asymmetry in the level of security in these devices made them easy targets for an attacker who exploited this asymmetry to cause significant damage. Table 7 illustrates the asymmetry between IoT devices and the SILEX Malware across multiple critical dimensions of IoT security.

Table 7.
Asymmetry between IoT devices and the SILEX malware across multiple critical dimensions of IoT security.
The SILEX malware attack on IoT devices highlights several important lessons and takeaways for both individuals and organizations:
- Security Awareness:
It emphasizes the critical need for security awareness in the IoT landscape. Many IoT devices are deployed with default passwords or unpatched vulnerabilities, making them easy targets. Users and manufacturers should be proactive in addressing these issues.
- 2.
- Regular Updates and Patching:
One of the key lessons is the importance of regular software and firmware updates. Devices should be promptly updated to mitigate known vulnerabilities and protect against evolving threats.
- 3.
- Strong Authentication:
The attack underscores the necessity for strong authentication mechanisms, such as complex passwords and two-factor authentication (2FA), to prevent unauthorized access.
- 4.
- Supply Chain Security:
Securing the supply chain is crucial. Manufacturers should implement measures to verify the integrity of components and software to avoid compromise before the devices reach consumers.
- 5.
- Network Monitoring and Intrusion Detection:
Implementing intrusion detection systems (IDPS) and network monitoring tools can help identify unusual activities early on and respond to potential threats promptly.
- 6.
- Physical Security:
Adequate physical security measures are essential to prevent unauthorized physical access to IoT devices. This includes securing devices in locked cabinets or rooms.
- 7.
- Education and Training:
Users and employees should receive training on IoT security best practices and be aware of social engineering threats to avoid falling victim to attacks.
- 8.
- Data Backup and Recovery:
Regular data backups and recovery plans can help minimize data loss in the event of a destructive attack like SILEX. Having offline backups can be particularly helpful.
- 9.
- Incident Response Plans:
Organizations should have well-defined incident response plans in place to efficiently respond to and recover from IoT security incidents.
- 10.
- Third-Party Security Audits:
Regular security audits and vulnerability assessments, performed by third-party experts, can help identify weaknesses that might be overlooked internally.
- 11.
- Regulatory Compliance:
Compliance with data protection laws and regulations (e.g., GDPR) is vital. Non-compliance can result in legal repercussions and penalties.
- 12.
- Sustainable IoT Ecosystem:
Manufacturers should prioritize device longevity and support, ensuring that security updates and patches are available for a reasonable time after purchase.
- 13.
- Network Segmentation:
The segmentation of IoT devices from critical network infrastructure can help contain the impact of an attack, isolating affected devices from more critical systems.
These lessons emphasize the importance of proactive measures, ongoing vigilance, and a multi-faceted approach to IoT security. As the IoT landscape continues to expand, it is crucial to apply these lessons to protect the increasing number of connected devices from evolving threats.
To counter these threats, security solutions encompass network segmentation to isolate IoT devices, robust authentication mechanisms, intrusion detection and prevention systems for early threat detection, regular firmware updates to patch vulnerabilities, and a security-by-design approach to embed robust safeguards into IoT devices from their inception. These multifaceted security measures are vital in safeguarding IoT ecosystems against a constantly evolving landscape of malware threats. In recent years, artificial intelligence-based approaches have yielded significant results in security detection, including IoT security [28]. Improvements required to make IoT applications more secure and resilient without compromising their dependability were mentioned in [29]. In Table 8, we summarize the main enhancements to secure IoT applications.

Table 8.
Security recommendations to improve the IoT security.
5. Conclusions and Future Work
Security in IoT is significantly important due to the increasing number of connected devices and the potential risks associated with these devices. IoT security has an inherent asymmetry, with resource-constrained devices often lacking the robust defenses required to prevent sophisticated attackers. This asymmetry creates a power dynamic in which cyber-adversaries, armed with greater resources and time, can exploit vulnerabilities in IoT ecosystems.
In this paper, we presented the state-of-the-art research efforts to secure IoT devices, and we listed and illustrated the top 10 IoT vulnerabilities as seen in the OWASP project. IoT security is an ongoing process, and it requires a combination of technical measures, policy enforcement, and user awareness to effectively mitigate the evolving threats in the IoT landscape. Moreover, we compared the symmetrical aspects of cybersecurity defense and offense, emphasizing the competition between defenders and attackers. This ongoing battle mirrors the concept of symmetry in adversarial relationships, highlighting the need for constant vigilance and adaptation in IoT security.
The case study of SILEX malware has illustrated the real-world consequences of this asymmetry, showcasing how a relatively simple but devastating attack can exploit the vulnerabilities in IoT devices lacking adequate security measures. SILEX malware serves as a reminder of the urgency to secure IoT devices, update firmware, and implement robust security practices to mitigate the risks associated with such asymmetrical attacks.
In essence, our exploration of symmetry and asymmetry within the context of IoT vulnerabilities and attacks underscores the imperative for a proactive and balanced approach to IoT security. Addressing the inherent asymmetry in IoT ecosystems is paramount to safeguarding these devices from increasingly sophisticated and destructive cyber-threats. As we move forward in the digital age, understanding and acting upon these insights will be pivotal in strengthening the grounds of IoT security and protecting the integrity of the interconnected world.
In the future, we plan to propose a new lightweight mitigation technique for the SILEX malware.
Author Contributions
Conceptualization, B.I.M.; methodology, B.I.M.; formal analysis, B.I.M., M.S.E. and A.D.J.; investigation, M.S.E.; writing—original draft preparation, B.I.M.; visualization, M.S.E. and M.A.A.; supervision, M.S.E., A.D.J. and M.A.A.; project administration, M.A.A.; funding acquisition, A.D.J. All authors have read and agreed to the published version of the manuscript.
Funding
This research received no external funding.
Data Availability Statement
Not applicable.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Harbi, Y.; Aliouat, Z.; Refoufi, A.; Harous, S. Recent security trends in internet of things: A comprehensive survey. IEEE Access 2021, 9, 113292–113314. [Google Scholar] [CrossRef]
- Sikder, A.K.; Petracca, G.; Aksu, H.; Jaeger, T.; Uluagac, A.S. A survey on sensor-based threats to internet-of-things (iot) devices and applications. arXiv 2018, arXiv:1802.02041. [Google Scholar]
- Mian, A.N.; Shah, S.W.H.; Manzoor, S.; Said, A.; Heimerl, K.; Crowcroft, J. A value-added IoT service for cellular networks using federated learning. Comput. Netw. 2022, 213, 109094. [Google Scholar] [CrossRef]
- Sarker, I.H.; Khan, A.I.; Abushark, Y.B.; Alsolami, F. Internet of things (IoT) security intelligence: A comprehensive overview, machine learning solutions, and research directions. Mob. Netw. Appl. 2022, 14, 1–7. [Google Scholar] [CrossRef]
- Verma, A.; Shri, C. Cyber Security: A Review of Cyber Crimes, Security Challenges and Measures to Control. Vision 2022, 17, 09722629221074760. [Google Scholar] [CrossRef]
- Almaraz-Rivera, J.G.; Perez-Diaz, J.A.; Cantoral-Ceballos, J.A. Transport and application layer DDoS attacks detection to IoT devices by using machine learning and deep learning models. Sensors 2022, 22, 3367. [Google Scholar] [CrossRef] [PubMed]
- En, S.X.; Ling, L.S.; Hao, F.C. Honeypots for Internet of Things Research: An Effective Mitigation Tool. Preprints 2021, 2021090461. [Google Scholar] [CrossRef]
- IoT Under Fire: Kaspersky Detects More than 100 Million Attacks on Smart Devices in H1 2019. Available online: https://www.kaspersky.com/about/press-releases/2019_iot-under-fire-kaspersky-detects-more-than-100-million-attacks-on-smart-devices-in-h1-2019 (accessed on 24 September 2023).
- Abdullahi, M.; Baashar, Y.; Alhussian, H.; Alwadain, A.; Aziz, N.; Capretz, L.F.; Abdulkadir, S.J. Detecting Cybersecurity Attacks in the Internet of Things Using Artificial Intelligence Methods: A Systematic Literature Review. Electronics 2022, 11, 198. [Google Scholar] [CrossRef]
- Khraisat, A.; Alazab, A. A critical review of intrusion detection systems in the internet of things: Techniques, deployment strategy, validation strategy, attacks, public datasets, and challenges. Cybersecurity 2021, 4, 1–27. [Google Scholar] [CrossRef]
- Tsiknas, K.; Taketzis, D.; Demertzis, K.; Skianis, C. Cyber threats to industrial IoT: A survey on attacks and countermeasures. IoT 2021, 2, 163–186. [Google Scholar] [CrossRef]
- Lee, Y.; Lee, W.; Shin, G.; Kim, K. Assessing the impact of dos attacks on iot gateway. In Advanced Multimedia and Ubiquitous Engineering: MUE/FutureTech; Springer: Singapore, 2017; pp. 252–257. [Google Scholar]
- Anirudh, M.; Thileeban, S.A.; Nallathambi, D.J. Use of honeypots for mitigating DoS attacks targeted on IoT networks. In Proceedings of the 2017 International Conference on Computer, Communication and Signal Processing (ICCCSP), Chennai, India, 10–11 January 2017; pp. 1–4. [Google Scholar]
- Deogirikar, J.; Vidhate, A. Security attacks in IoT: A survey. In Proceedings of the 2017 International Conference on I-SMAC (IoT in Social, Mobile, Analytics and Cloud) (I-SMAC), Palladam, India, 10–11 February 2017; pp. 32–37. [Google Scholar]
- Seralathan, Y.; Oh, T.T.; Jadhav, S.; Myers, J.; Jeong, J.P.; Kim, Y.H.; Kim, J.N. IoT security vulnerability: A case study of a Web camera. In Proceedings of the 2018 20th International Conference on Advanced Communication Technology (ICACT), Chuncheon, Republic of Korea, 11–14 February 2018; pp. 172–177. [Google Scholar]
- Favaretto, M.; Tran Anh, T.; Kavaja, J.; De Donno, M.; Dragoni, N. When the price is your privacy: A security analysis of two cheap IoT devices. In Proceedings of 6th International Conference in Software Engineering for Defence Applications: SEDA 2018; Springer International Publishing: Berlin/Heidelberg, Germany, 2020; pp. 55–75. [Google Scholar]
- Šimon, M.; Huraj, L. A Study of DDoS Reflection Attack on Internet of Things in IPv4/IPv6 Networks. In Software Engineering Methods in Intelligent Algorithms. CSOC 2019. Advances in Intelligent Systems and Computing; Silhavy, R., Ed.; Springer: Berlin/Heidelberg, Germany, 2019; Volume 984. [Google Scholar]
- Alladi, T.; Chamola, V.; Sikdar, B.; Choo, K.K.R. Consumer IoT: Security vulnerability case studies and solutions. IEEE Consum. Electron. Mag. 2020, 9, 17–25. [Google Scholar] [CrossRef]
- Rajendran, G.; Nivash, R.S.R.; Parthy, P.P.; Balamurugan, S. Modern security threats in the Internet of Things (IoT): Attacks and Countermeasures. In Proceedings of the 2019 International Carnahan Conference on Security Technology (ICCST), Chennai, India, 1–3 October 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Valente, J.; Koneru, K.; Cardenas, A. Privacy and Security in Internet-Connected Cameras. In Proceedings of the 2019 IEEE International Congress on Internet of Things (ICIOT), Milan, Italy, 8–13 July 2019; pp. 173–180. [Google Scholar] [CrossRef]
- Krishna, R.R.; Priyadarshini, A.; Jha, A.V.; Appasani, B.; Srinivasulu, A.; Bizon, N. State-of-the-art review on IoT threats and attacks: Taxonomy, challenges, and solutions. Sustainability 2021, 13, 9463. [Google Scholar] [CrossRef]
- Folgado, F.J.; González, I.; Calderón, A.J. Data acquisition and monitoring system framed in Industrial Internet of Things for PEM hydrogen generators. Internet Things 2023, 22, 100795. [Google Scholar] [CrossRef]
- Ahmed, Y.A.; Huda, S.; Al-rimy, B.A.S.; Alharbi, N.; Saeed, F.; Ghaleb, F.A.; Ali, I.M. A Weighted Minimum Redundancy Maximum Relevance Technique for Ransomware Early Detection in Industrial IoT. Sustainability 2022, 14, 1231. [Google Scholar] [CrossRef]
- Dhirani, L.L.; Armstrong, E.; Newe, T. Industrial IoT, Cyber Threats, and Standards Landscape: Evaluation and Roadmap. Sensors 2021, 21, 3901. [Google Scholar] [CrossRef] [PubMed]
- Anand, P.; Singh, Y.; Selwal, A.; Alazab, M.; Tanwar, S.; Kumar, N. IoT Vulnerability Assessment for Sustainable Computing: Threats, Current Solutions, and Open Challenges. IEEE Access 2020, 8, 168825–168853. [Google Scholar] [CrossRef]
- Liashenko, O.; Kazmina, D.; Rosinskiy, D.; Dukh, Y. Analysis of Vulnerabilities of IoT-Devices and Methods of Their Elimination. Comput. Linguist. Intell. Syst. 2021, 2021, 27–37. [Google Scholar]
- El-Gendy, S.; Azer, M.A. Security Framework for Internet of Things (IoT). In Proceedings of the 2020 15th International Conference on Computer Engineering and Systems (ICCES), Cairo, Egypt, 15–16 December 2020; pp. 1–6. [Google Scholar] [CrossRef]
- Fragkos, G.; Minwalla, C.; Plusquellic, J. Tsiropoulou EE. Artificially intelligent electronic money. IEEE Consum. Electron. Mag. 2020, 10, 81–89. [Google Scholar] [CrossRef]
- ElKashlan, M.; Azer, M. Mitigating IoT Security Challenges Using Blockchain. In Proceedings of the 2020 15th International Conference on Computer Engineering and Systems (ICCES), Cairo, Egypt, 15–16 December 2020; pp. 1–6. [Google Scholar]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).