Abstract
With the rapid development of communication technology, unmanned aerial vehicles (UAVs) have been widely used in the military, rescue, agricultural and other fields. The security and privacy issues are one of the biggest challenges for UAV communications. In this paper, we propose a certificate signing based on an Elliptic Curve multiple authentication scheme (CSECMAS). The scheme employs multiple authentication tools to ensure the legitimacy of the identity and the integrity of the information. We treat multiple UAVs as a cluster, and after establishing a secure session between the ground control station (GCS) and the UAV, we use the fitness function to select one node from them as the key node. Mutual authentication between the UAVs through the key node establishes secure conversations while increasing the security and resistance to destruction of the entire communication network. The proposed protocol is formally analyzed and verified by using the model-checking tool SPIN. The informal analysis shows that the protocol can resist various attacks, such as man-in-the-middle attacks, replay attacks, and DoS attacks. The performance analysis shows that the proposed protocol is superior compared to other related protocols.
Keywords:
UAV; CSECMAS; multiple authentication; the fitness function; the key node; security; formal analysis 1. Introduction
With the rapid development of UAV technology, it has become widely used in various fields. In the military, UAVs can infiltrate the enemy to carry out precise target strikes, reconnaissance patrols and other high-risk tasks; for civilian use, they are widely used in the service industry, agricultural and industrial scenarios, such as UAV express delivery, disaster rescue in complex environments, aerial irrigation of crops, and network relay in communication scenarios [1,2,3,4]. They bring great convenience to people’s production and life.
Typically, UAVs operate remotely by receiving commands from the GCS, and the information transmitted is essentially highly sensitive and critical [5]. Therefore, security is the top priority in UAVs communication. SamyKamkar has designed and developed a set of UAV hijacking scheme, which can make the UAV fly to uncontrollable areas by tampering with GPS data, resulting in unpredictable consequences [6,7].
Meanwhile, a vulnerability has been discovered in DJI drones, which allowed attackers to intercept users’ identity tokens, steal account information, violate users’ privacy, and even hijack the drones by logging into DJI forums as a legitimate identity [8]. Therefore, we should design a robust protocol to protect the communication security of UAVs. The current security threats in drones [9,10,11,12,13] are:
- Eavesdropping attack: This type of attack is a passive attack. During the execution of the protocol, attackers can listen and obtain communication messages between nodes through an insecure communication channel without interfering with the normal operation of the protocol, and then attackers can analyze the messages to obtain some communication information or key information to carry out further attacks.
- Replay attack: After attackers intercept the communication message between nodes, they retransmit the intercepted message, causing all nodes in the system to process the message again. If nodes in the system do not judge the expired message, the replayed message may have unpredictable consequences for the network system.
- Message tampering attack: Attackers intercept the message sent by the node and modify it according to the attack purpose, then send the modified message to the recipient of the original message. In this type of attack, attackers can change the intercepted message in part or in whole in any way desired.
- Man-in-the-middle attack: This type of attack is usually found in protocols that lack mutual authentication between the two parties. Attackers can submit the question asked by one subject in the protocol to another participant for an answer, and then submit the answer to the subject who asked the question.
- Denial of Service Attack (DoS Attack): Attackers make the system network unavailable to other legitimate users by continuously taking up resources on the system network. The rapid relative movement between UAVs easily causes frequent connection and disconnection of communication links, whereas nodes can join or leave the network at any time, which makes the network topology change rapidly and causing frequent changes in the trust relationship between nodes. If the authentication of the leaving nodes or newly joined nodes into the network is too simple, attackers will get the disconnected node’s information and then simulate the disconnected nodes to request re-entry authentication, causing security risks to the system.
Therefore, the proposed security solution for UAV communications needs to be able to meet the following security objectives [14,15].
- Session Key Agreement: The generated session key should be negotiated by both parties, rather than generated and distributed by the other party. Both parties shall contribute equally to the generation of the session key.
- User Anonymity and Untraceability: The protocol needs to achieve user anonymity and untraceability, which means that attackers cannot get the user’s identity. As a result, attackers cannot judge whether the session content is from the same user, cannot distinguish the specific identity of the user, and therefore cannot trace the user’s behavior.
- Message Integrity: Integrity means that the data has not been destroyed or altered during transmission or storage. The recipient of the message must be able to verify the integrity of the received message. If the message was found to have been tampered with or lost, the session should be stopped immediately and a resend requested. At the same time, the sender of the message cannot deny that it has ever sent the message. The most common methods of achieving integrity are encapsulation and signing.
- Mutual authentication: Each communication node in the network can authenticate with each other to confirm the legitimacy of the identity of the communicating nodes.
- Confidentiality: Data transmitted in the public network must be transmitted in encrypted cipher text, and the transmission of sensitive information in clear text is prohibited. It is mainly divided into forward and backward confidentiality. If the long-term private key of the protocol participant is intercepted by attackers, and attackers cannot thereby roll out the session key that the participant negotiated to obtain before the private key was compromised. Forward confidentiality means that a node leaving the network cannot gain access to confidential data transmitted afterwards. Backward confidentiality means that a newly joined node cannot read confidential data that has been transmitted before.
- Freshness: The recipient of the message should first check the timestamp of the received message to determine whether it meets the freshness requirement.
As a result, the main purpose of this paper is to design a safe and reliable UAV communication protocol to achieve mutual authentication between UAV and GCS and establish a secure session. The main contributions of this paper are as follows:
- We propose a certificate signing based on an Elliptic Curve multiple authentication scheme (CSECMAS) to achieve secure sessions between UAVs and the GCS.
- The key node is selected using the fitness function, through which a secure session can be established between any two UAVs in the network. Increasing the resistance of the entire network to destruction.
- The proposed scheme is analyzed using formal and informal analysis techniques to ensure the security of the protocol.
- Compared with other related protocols in terms of security properties and node computational overhead, the results shows that the protocol is resistant to a wide range of attacks and performs better.
The rest of the paper is organized as follows. Section 2 describes the current research on UAV communication protocols. Section 3 describes the proposed protocol in detail and Section 4 presents a formal and non-formal security analysis of the protocol. The final section gives the performance analysis, simulation results and conclusions respectively.
2. Related Works
In recent years, UAV communication security has become a hot topic of research in the field of information security. A large amount of research has focused on the study and application of security mechanisms to ensure the basic security attributes of UAVs, such as confidentiality, integrity, and authentication, to protect them from various cyber security attacks.
Won et al. [9] proposed a secure communication protocol for drones and smart objects based on an efficient certificate-free tag key encapsulation mechanism (eCLSC-TKEM); however, it was not resistant to drone capture attacks, and if it is captured, the key and communication information of the drone will be compromised, damaging the communication security of the drone. Seo et al. [15] proposed a security solution for UAV delivery services using White-Box Cryptography (WBC) and Public Key Infrastructure (PKI) to guarantee the security of keys and the secure storage of information, while also considering security properties such as confidentiality, integrity, and non-repudiation. Wang et al. [16] proposed the Long-Term Evolution (LTE) based key management scheme for UAV control systems to achieve efficient and secure control of UAVs and discussed in depth security attributes such as authentication, confidentiality, and integrity. Blazy et al. [17] proposed a UAV-GCS secure communication protocol that ensured the confidentiality of communication messages by using effective cryptography and highlights various security attribute requirements, such as not being able to compromise the security of the UAV or the freshness of the key when forensically examining a captured UAV.
Li et al. [18] designed an identity-based access control (IBAC) model employing a bilinear pairing operation where the sender could send the message in a certificate-free encryption (CLC) environment to the recipient who is in an identity-based encryption (IBC) environment. In terms of implementation, this mechanism requires a gateway node between two IoT smart devices and is also costly. Benzarti et al. [19] proposed an initial architecture based on authentication. In this scheme, the UAV is equipped with an RFID tag that provides a unique identification. During the authorization process, a temporary UAV identification was provided to protect privacy and generate cryptographic keys, however, the scheme lacks mutual authentication, which made the system vulnerable to man-in-the-middle attacks and simulation attacks.
Chen et al. [20] proposed a direct anonymous mutual authentication (MA-DAA) scheme for UAV networks, which was well suited to the low bandwidth and low computing power of UAVs compared to existing direct anonymous authentication (DAA) schemes. Its solution was based on the Trusted Platform Module (TPM), a specialized and expensive security co-processor that needs to be integrated into the system, leading to higher costs. Tian et al. [21] proposed a privacy protection and authentication technique for edge assisted IoD networks. The scheme took into account the high mobility characteristics of UAVs and significantly reduces authentication costs by incorporating mobile edge computing (MEC) devices. However, the scheme had not been effectively formalized and proven.
A new authentication and key agreement (AKA) scheme between users and nodes was proposed in Ref. [22]. Using the hash function and bitwise dissimilarity operation, it did not require a gateway node and was suitable for resource-constrained nodes. The scheme considered confidentiality, message integrity and authenticity requirements in UAV communication and how to establish secure communication between UAVs. However, the scheme was vulnerable to man-in-the-middle attacks and node simulation attacks. Turkanović et al. [23] proposed a lightweight AKA scheme for UAV communication between new users and nodes without the aid of gateway nodes, adopting hash functions and XOR operations, which did not resist man-in-the-middle attacks and node simulation attacks, and does not provide anonymity protection for nodes. Farash et al. [24] proposed an improved AKA scheme to address the shortcomings in the scheme of literature [23], which overcooked the shortcomings in the scheme of literature [23] but was not resistant to known specific temporary information attacks and user simulation attacks, etc. Amin et al. [25] found security problems in the scheme of literature [24] and proposed a smartcard-based AKA scheme, but it still may be subject to smart card loss attacks and offline password guessing attacks.
Challa et al. [26] proposed a new signature-based elliptic curve AKA scheme. This approach features increased communication and computational overhead compared to previous approaches. Wazid et al. [27] proposed a new lightweight user AKA scheme for deploying Internet of Drones (IoD) setups. The scheme relied on a fuzzy extractor, a one-way cryptographic hash function and a bitwise anomaly operation. However, the proposed authentication protocol was vulnerable to session-specific temporary message attacks when the powerful Canetti-Krawczyk (CK) adversary stole temporary keys. In addition, the scheme failed to provide session key agreement. To overcome this shortcoming, Zhang et al. [28] proposed an improved alternative scheme. The summary of the related works is given in Table 1.

Table 1.
The summary of the related works.
3. The Proposed Protocol
3.1. System Model
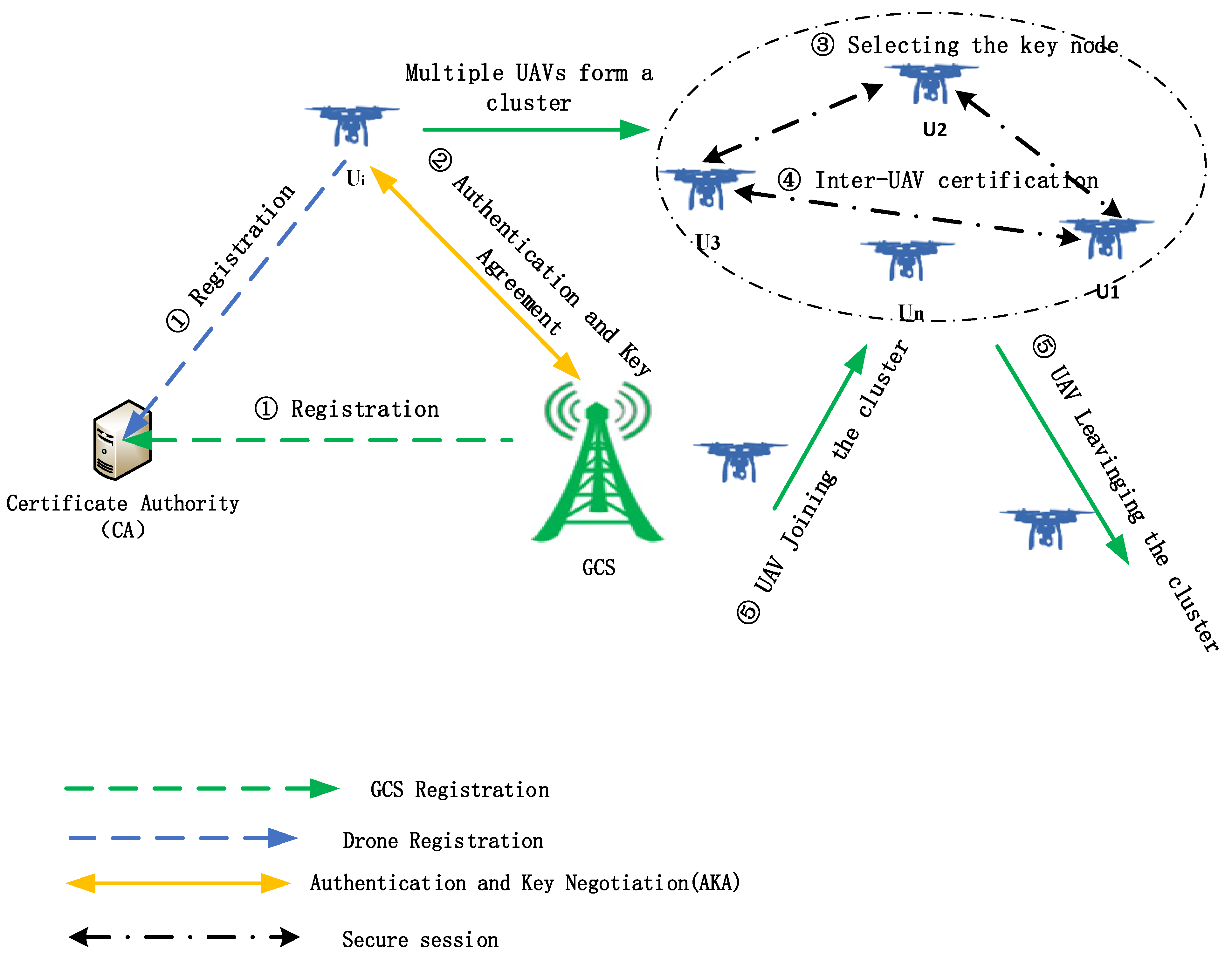
The system model considered in this paper consists of multiple UAVs, the GCS, and the certificate authority (CA), as shown in Figure 1. First, both the GCS and the UAV should register with the CA to obtain the certificate. Secondly, the UAVs perform authentication and key agreement to establish a secure communication session. Finally, one of the multi-UAVs is selected as the key node, through which the UAVs can achieve mutual secure communication.
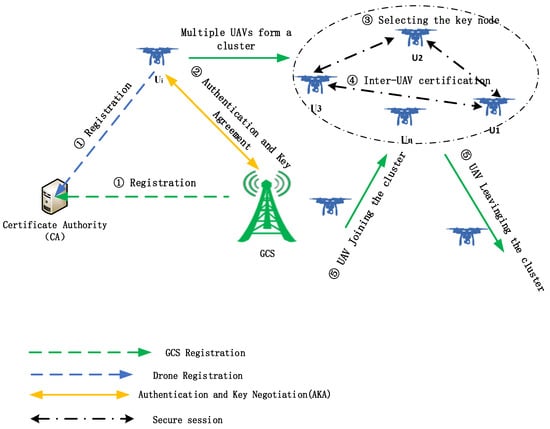
Figure 1.
System model.
3.2. Attacker Model
With the increasing trend of adversarial communication, attackers can interfere with UAV communication by means of channel listening and message replay in response to the highly open nature of UAV communication links. This scenario is characterized by the Dolev-Yao attacker model [29], which is commonly used in formal analysis of security protocols, as “the network is under the control of the attacker”. Therefore, attackers in this scenario are considered to have similar network attack capabilities to attackers in the Dolev-Yao attacker model, as defined below.
- The ability to listen to, intercept and store all messages passing through the UAV network, including authentication and communication information.
- The ability to decrypt intercepted authentication messages and to use the key parameters obtained to forge authentication and communication messages.
- The ability to establish a link to the UAV via a proxy node and send constructed or intercepted authentication and communication messages to participate in the authentication and communication between the UAV and the GCS.
3.3. The Proposed Scheme
In this subsection, we will specify the process of authentication and key agreement between the UAV and the ground control station, including the following phases, namely: (i) initialization phase, (ii) registration phase, (iii) UAV-GCS authentication, (iv) Inter-UAV authentication, and (v) the key refresh. Table 2 gives a description of the symbols used in the authentication process. This protocol uses four types of keys: the master key, the refresh key, the session key, and the authentication key.

Table 2.
Explanation of symbols.
- The master key: The master key is generated via the Elliptic Curve Diffie-Hellman Key Exchange (ECDH) protocol, but is not used to encrypt messages, but rather to assist in the generation of session keys and authentication keys.
- The refreshing key: Shared between the UAV and the ground control station and used with the primary key to generate the session key and authentication key. After each generation of the session key and authentication key, a new refresh key is generated by applying a hash function to the current refresh key and deleting the current key and replacing it with the new key. This provides forward secrecy to the protocol; it is assumed that when a node is attacked, information about that node’s previous communications will not be compromised. Because attackers cannot generate the old key, the previous refresh key is no longer available at the time of the attack, nor is the master key.
- The authentication key and the session key: The session key is used as the key for the data-to-data encryption algorithm that provides data confidentiality for communication between the ground control station and the UAV and between UAVs. The authentication key uses a separate key for encryption and authentication to guarantee the legitimacy of the identity.
3.3.1. The Initialization Phase
The initialization consists mainly of the generation and distribution of system parameters and authentication information. First, a compliant elliptic curve is selected and the points on this curve form a generating element of group . The order of is required to be a large prime number . As well as being equipped with various cryptographic functions such as digital signature algorithms, encryption and decryption functions, cryptographic hashing functions (e.g., HMAC; hash-based message authentication codes), pseudo-random number generators (PRNGs), etc. The certificate authority (CA) then generates the private and public keys and prepares the public parameter set. The steps are as follows.
- The CA uses a random number generator to generate a random number as the CA’s private key and calculates the public key: .
- Select the public parameter set, set to and publish.
3.3.2. The Registration Phase
During the registration phase, both the UAV and the GCS need to be registered with the CA; the exact process of registration of the UAV is given below:
- The drone chooses its own identifier , then generates a random number as the private key , calculates the message digest , and computes the public key .
- The drone generates message and calculates encrypted message . The certificate private key is used to over-encrypt the message sent, and sends a message to the CA requesting registration.
- The CA decrypts the information after receiving it and calculates the certificate information .
- The CA loads out the drone certificate for the drone
where is a hash function; is the time expiry date of the certificate; is the public key of node A; and is a signature pair using the CA’s private key . The ground control station is similar to the UAV registration. Therefore, we will not go into details.
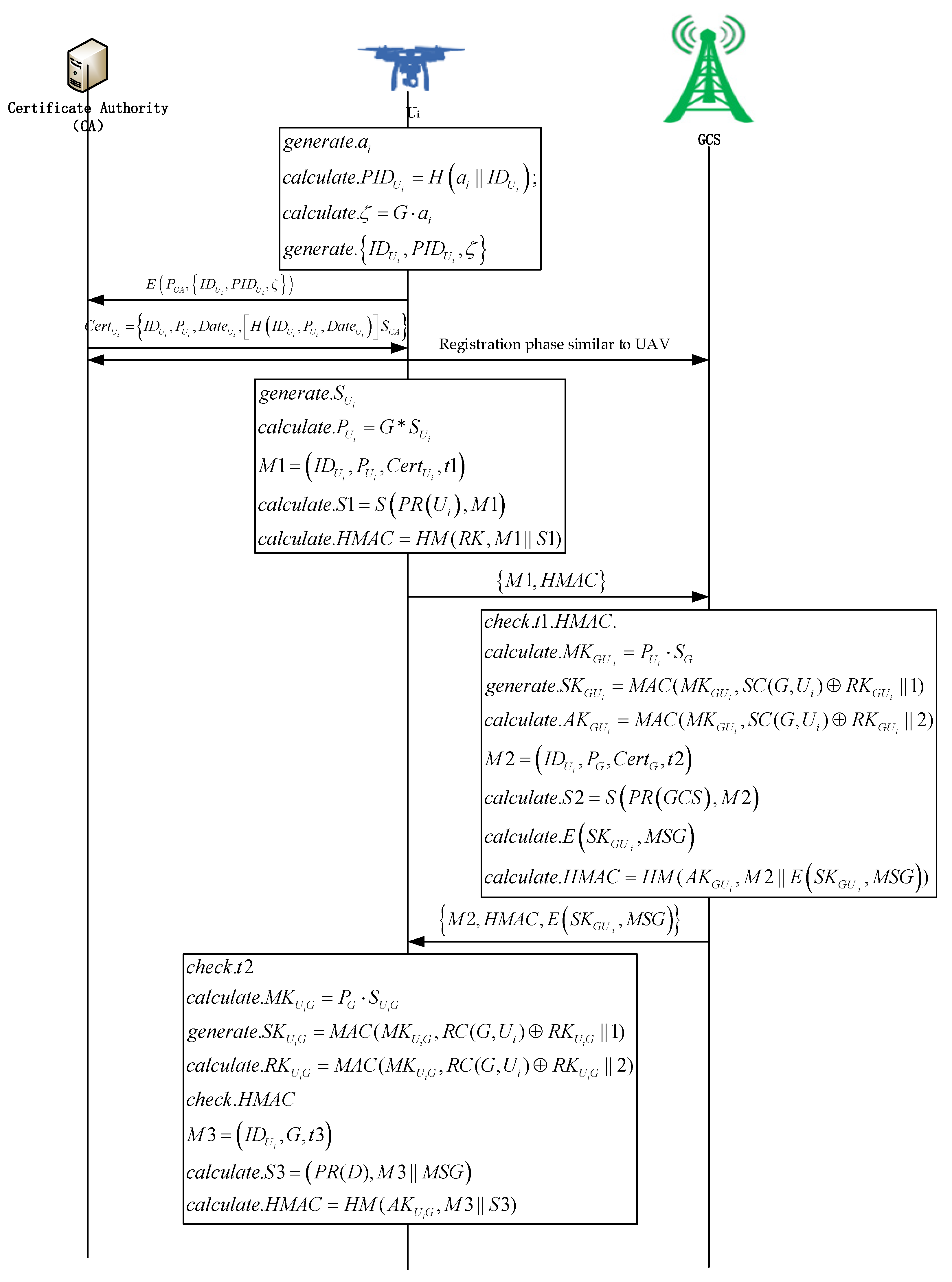
3.3.3. UAV-GCS Authentication Phase
The following is the specific process of identity authentication:
Step 1:
- The UAV generates a random number as its private key , and calculates the public key .
- The UAV generates information , and then signs , namely , calculates value, namely .
- The UAV generates the transmission information: .
Step 2:
- When the GCS receives the information from the UAV , first verify the freshness of the timestamp . If the requirements are met, continuing to the next step, otherwise, the authentication fails.
- It will calculate , and compare it with the received value. If it is the same, continue to the next step, if not, authentication fails.
- The GCS will check the validity of the certificate and use the public key of the UAV’s certificate to verify the signature . If correct, the GCS successfully certifies the UAV and will continue; otherwise, the authentication fails.
- The GCS generates a random number as its private key , and calculates the master key ; the session key , the identity authentication key .
- Then information is generated, and the message is signed, namely ;
- Encrypting the information and calculate and .
- Generating the transmission information .
Step 3:
- The UAV receives the information from the GCS , the freshness of the timestamp should be verified firstly. Judging whether it meets the freshness requirement.
- It will verify the validity of the certificate and use the certificate public key of the GCS to verify the signature . If correct, the UAV successfully certifies the GCS. Will continue; otherwise, the authentication fails.
- The UAV will compute the master key , the session key , and the identity authentication key .
- The value will be calculated and compared to the received value. Similarly, the UAV successfully authenticates the GCS.
- After decrypting the encrypted information , the UAV will receive the information sent by the GCS.
- The UAV will generate information , sign the message , namely , and calculate . It generates the send information .
Step 4:
- When the GCS receives the message , the freshness of the timestamp should be verified firstly.
- It will verify whether the value is consistent with the received one.
- If so, will verify the validity of the certificate and use the certificate public key of the UAV to verify the signature.
- If the verification is successfully, it can be judged that the UAV has successfully received the message sent by the GCS. Similarly, the UAV can verify that the GCS has successfully received the information sent by the UAV by signing .
Therefore, multi-key agreement and multi-authentication are used to achieve authentication between the UAV and the GCS, and to generate the master key, through which the secure session key and the authentication key are generated. The authentication process is shown in Figure 2.
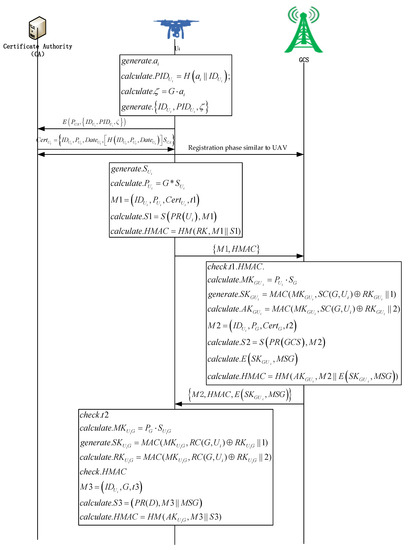
Figure 2.
Authentication process of the proposed protocol.
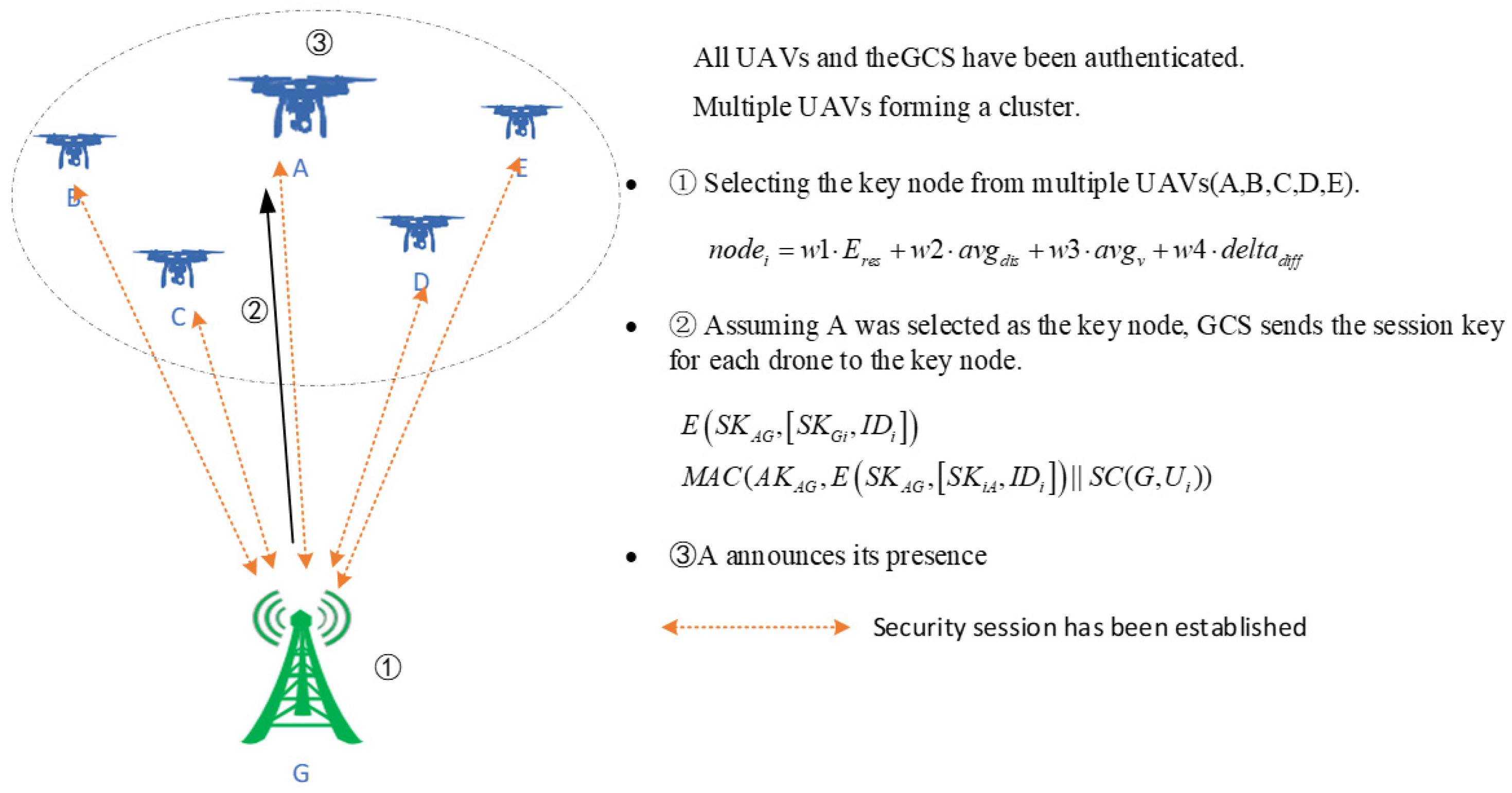
3.3.4. UAV-UAV Authentication Phase
Once the UAV and GCS have completed mutual authentication, we propose to use the key node to achieve mutual authentication and communication between UAVs. Firstly, multiple UAVs can be viewed as a cluster, then a suitable node from the cluster can be selected as the key node using the fitness function, and finally mutual authentication and communication between the UAVs can be achieved through the key node. Through the key node, we can enhance the destructiveness of the whole UAV communication network, making the communication efficiency between UAVs enhanced, also improving the security of the whole network.
- A.
- Selection of the Key Node
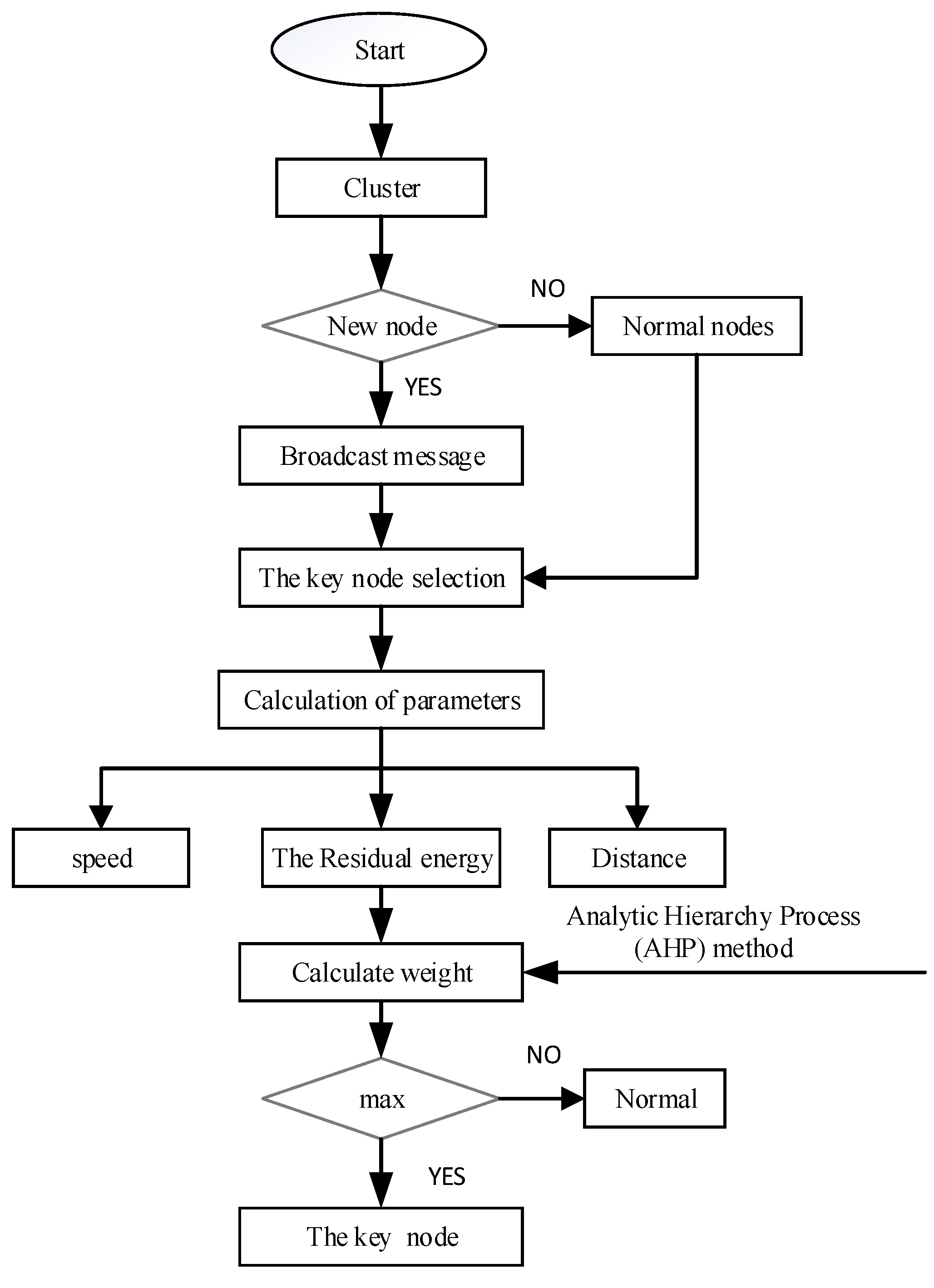
When the UAV is used as the key node, its function is limited to key management and storage. Therefore, when selecting critical nodes, we must consider three essential factors: the distance between nodes, the speed of the nodes and the residual energy.
- The remaining energy
When the UAV is used as the key node, its function is limited to key management and storage. Therefore, the key node will consume more energy than other normal nodes. The current energy of a drone node is defined as
where is the initial energy of the UAV, is the average energy consumption of each neighboring node, is the number of nodes in communication and is the communication period.
- 2.
- Speed
Due to the high speed of movement of the UAV, if the key node moves at high speed, it will lead to the whole communication being in an unstable state, resulting in frequent disconnections and connections of the communication link as well as frequent changes of the key nodes; the selection of fast-moving nodes should be avoided. The mobility of node can be calculated as
where is the position of the UAV at time , is the position of the UAV at time .
- 3.
- Distance
As the distance between drone nodes is always changing, when two UAVs are far away from each other, the communication link between them is unreliable or unstable, so the distance between the UAV nodes is one of the factors that should be taken into account.
where is the number of neighbors of the given UAV, is the position of this UAV, and is the position of its neighbors.
When all parameters have been determined, we use the fitness function based on the weighted characteristic formula to select the key node and use the Analytic Hierarchy Process (AHP) method to determine the weighting parameters, as shown in Figure 3.
where:
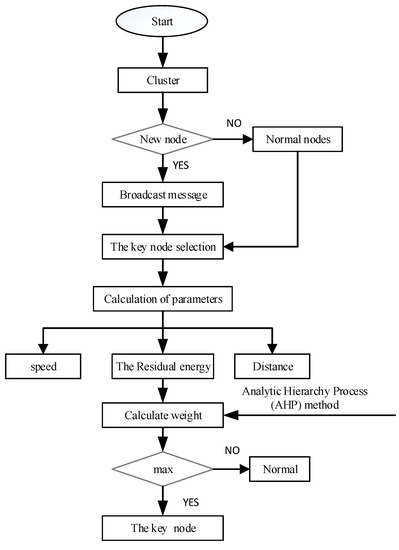
Figure 3.
Flow chart for selecting the key node.
- is the value of the fitness function of the node i.
- are the weight representing distance, speed, and the remaining energy, respectively, derived from the Analytic Hierarchy Process and satisfying the requirement that .
- is the average distance between the UAV and its neighbors.
α, β and γ are weighting parameters between 0 and 1 determined through hierarchical analysis (AHP).
First, the energy weight parameters should be greater than β and γ. This is because when the node is identified as a critical node and its function is restricted to key management, the key node should have the maximum energy level. Then, for the monitoring of neighboring nodes, the speed of the UAV should be flat or uniform. Therefore, the weight parameter for speed should β should be greater than γ. Based on this information and by applying the AHP method, we can elaborate the pairwise comparison matrix shown in Table 3, where A is the residual energy, B is the speed and C is the distance.

Table 3.
Paired comparison matrix.
Note that the priority vectors are obtained from the normalized eigenvectors of the matrix and denote the α, β and γ weight values respectively. The diagonal of the matrix is always 1 and the lower triangular matrix is filled using the formula , where denotes the ratio of the standard weight to the standard weight. The basic 1 to 9 scale can be used to rank the judgements as shown in Table 4.

Table 4.
A fundamental 1 to 9 scale.
is the Eigen value and is obtained from the summation of products between each element of Eigen vector and the sum of columns of the reciprocal matrix.
where RI is the Random Index, whose values are cited in Table 5.

Table 5.
Random Consistency Index (RI).
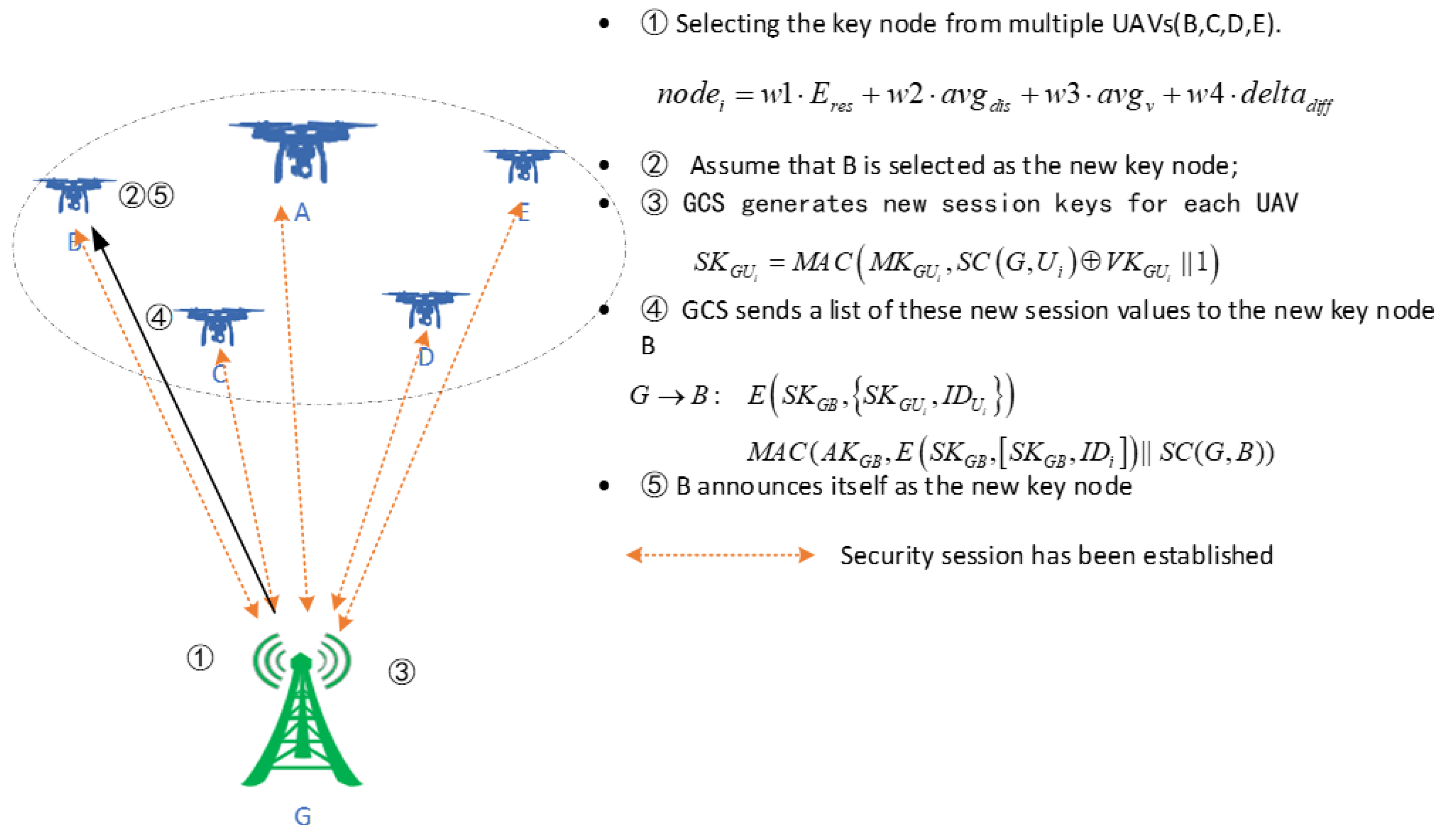
When selecting the key node, it can be any of the UAVs, which reduces the possibility of a specific UAV being subject to the targeted DoS attack. Once the key node in the cluster is identified, GCS forms a list of session keys for each node in the cluster, and sends it to that key node, and encrypts it using its session key. This is shown in Figure 4.
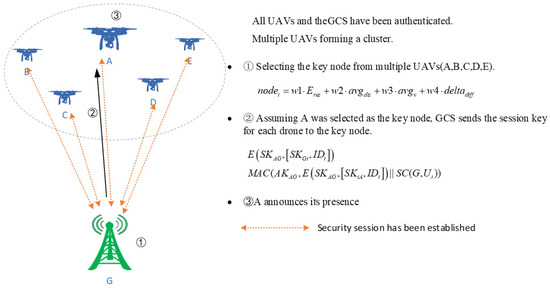
Figure 4.
Selection of the key node.
Because the key node changes periodically, or when the key node is compromised or attacked, the key node needs to be reelected to ensure the security of the UAV cluster communication network, as shown in Figure 5.
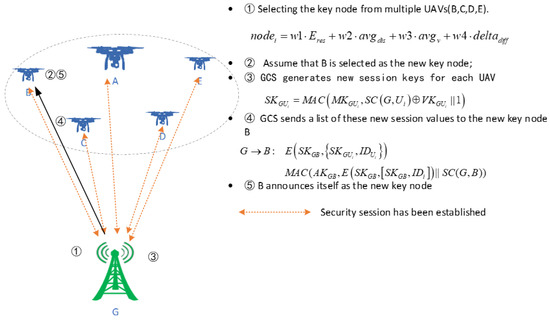
Figure 5.
Refresh of the key node.
- B.
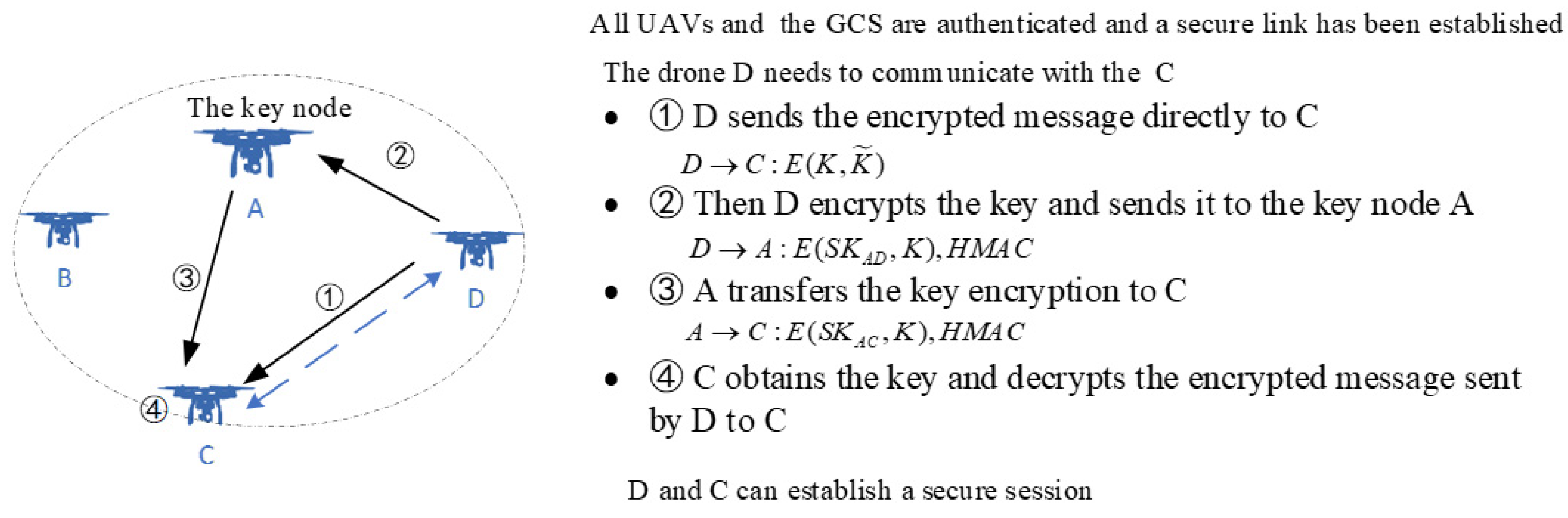
- Mutual authentication between UAVs
When the UAVs in the cluster (e.g., D and C) need to communicate, it is only necessary for them to implement a secure link between the UAVs through the key node (e.g., A). First, D generates two random numbers and , and sends an encrypted message to C; then D encrypts the key and sends the message to the key node A; A decrypts the key and transmits the message to C; C decrypts the key and obtains and decrypts the message to obtain , which is then used as the session key between the two nodes. As shown in Figure 6.
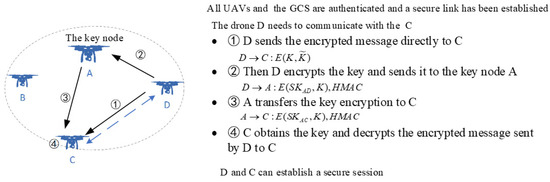
Figure 6.
Mutual authentication between UAVs.
3.3.5. Key Refreshing and Dynamic Joining of Drones
Due to the dynamic nature of UAVs, keys need to be refreshed within a fixed time frame or due to malicious events (e.g., a damaged drone dropping a packet) and UAV malfunction. In these cases, the key must be updated to secure the UAV communication. The key will be updated in the following steps:
- The GCS generates a new session key and authentication key by refreshing the key.
- The GCS send encrypted messages to the UAV.
- The UAV receives the encrypted message and generates its own new session key and authentication key, and then decrypts the encrypted message. If the decryption is successful, the key refresh is successful, otherwise, it fails, this means that the drone may be controlled or badly damaged.
- Immediately afterwards, the UAV generates a new refresh key and then the UAV sends an encrypted message to the GCS to keep the counters in synchronization.
- The GCS also generates a new refresh key, while both the UAV and the ground control station delete the old key.
4. Security Analysis
4.1. Formal Analysis
This section focuses on the formal analysis and verification of the proposed protocol using the model detection tool Simple Promela Interpreter (SPIN). The SPIN is a powerful model detection tool proposed by Holman in 1989, which is semantically clear, easy to understand and efficient. It was awarded the Software Systems Development Award by the ACM in 2002.
4.1.1. The Honest Subject Modeling
The first step in the construction of the model is the definition of the finite set of names.
where U, G and I represents the UAV, GCS, and intruder respectively. Values Tc, Ts and Tc1 are time variables respectively; Rt represents an unrecognized identity; gD the symbolic representation of a generic data item used by attackers.
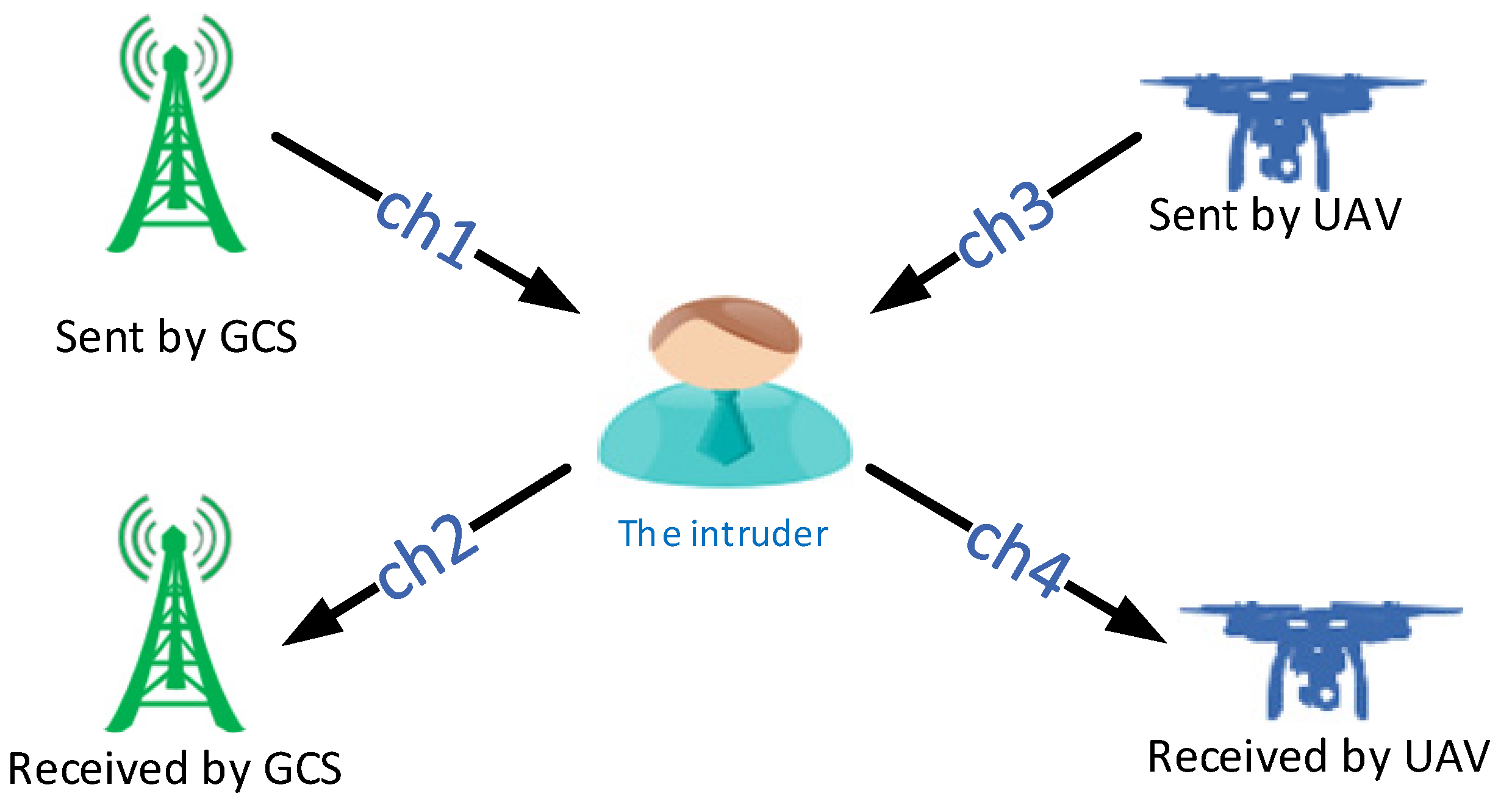
The second step in the construction of the model is the definition of the channels used by the principals to communicate with each other. We use a four-channel modeling approach to describe the attacker’s capabilities, including two channels between the GCS and attackers and two channels between the UAV and attackers. In this way, a large number of repeated sub message items and ignoring the parallelism of multi-rounds protocols can be avoided, which leads to the increase of state migration caused by cross-running between processes and the explosion of state space. Figure 7 is a schematic diagram of four channel parallel modeling:
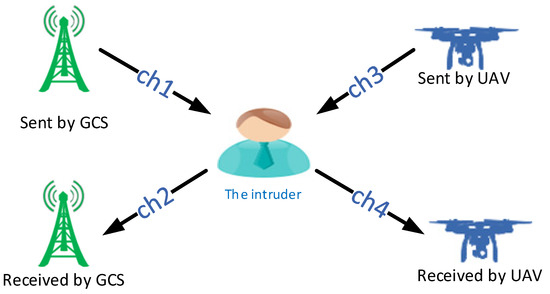
Figure 7.
Four-channel modeling.
Channel ch1 and ch2 represent the channel between the GCS and attackers. Channel ch3 and ch4 represent the channel between attackers and UAV; [0] indicates that the transmission data and reception data in the channel are synchronized. In the modeling process, we use send and receive to represent the sending and receiving of messages respectively.
Sending statement: send is the sender of the message, msg1 and msg2 are the knowledge items of the message, time is the timestamp, and K is the key that encrypts msg1, msg2 and time.
Receiving statement: . The function eval () is used to judge whether the received message value is the same as the target value in the message channel ch2. If so, the message will be received, otherwise, the message will be discarded. At the same time, the key word atomic {} in Promela language is also introduced to complete the receiving and sending operations under the same atom, which can effectively reduce the state space
4.1.2. The Attackers Modeling
The most critical point of the Dolev-Yao intruder model is to build the attacker’s knowledge base function, so that attackers can clearly know the knowledge obtained by attackers, and then attackers can forge and forward information according to the knowledge in the knowledge base function.
The critical aspect of building the attacker’s knowledge base is to specify the knowledge acquired by attackers and the knowledge learned by attackers. The attacker’s knowledge base is obtained by taking the intersection of the knowledge acquired by attackers and the knowledge learned by attackers, as shown in Table 6. The knowledge acquired by attackers is generally obtained from the knowledge intercepted by attackers, as shown in Table 7. The knowledge that attackers need to learn is obtained by analyzing the information received by the subject and combining the knowledge that attackers need to learn based on different numerical variables, as shown in Table 6. Finally, by taking the intersection of the knowledge obtained by the intruder and the knowledge that attackers can learn, the knowledge base function of attackers can be obtained, as shown in Table 8.

Table 6.
Knowledge elements that attackers can eventually acquire.

Table 7.
Knowledge elements that attackers can learn.

Table 8.
Knowledge elements that attackers need.
4.1.3. Property Characterization
In order to verify whether the protocol is secure, it is necessary to describe the security attributes of the protocol. In SPIN, the model-checking tool, LTL is used to describe the attributes that the protocol needs to meet, and the security of the protocol is verified through the established LTL formula.
The security properties of the protocol, each of the basic propositions involved can be represented in Promela by a global Boolean variable that is true at a specific stage of the protocol’s operation. We initialize the variables needed in the protocol.
IniRunning and IniCommit are two macros used to update the values of the variables recording the atomic predicates that are used to express the authentication properties. IniRunningUG indicates that the UAV initiates the session with the GCS. If the initial value is 0, the UAV does not initiate the session with the GCS; IniCommitGU indicates that the UAV submits the session with the GCS; if the initial value is 0, the UAV does not submit the session with the GCS.
The global variable is then macroed so that the value of that variable can be updated by the macro definition, IniRunning () is shown below.
Finally, according to the security attributes of the system, the LTL formula of identity authentication between the UAV and GCS is described when UAV is connected to GCS:
This formula implies that the UAV must initiate a conversation with the GCS before it can submit a conversation with the GCS, or that the GCS has never initiated a conversation with the UAV, and others similar to this. The full safety attributes are described below.
4.1.4. Analysis of Experimental Results
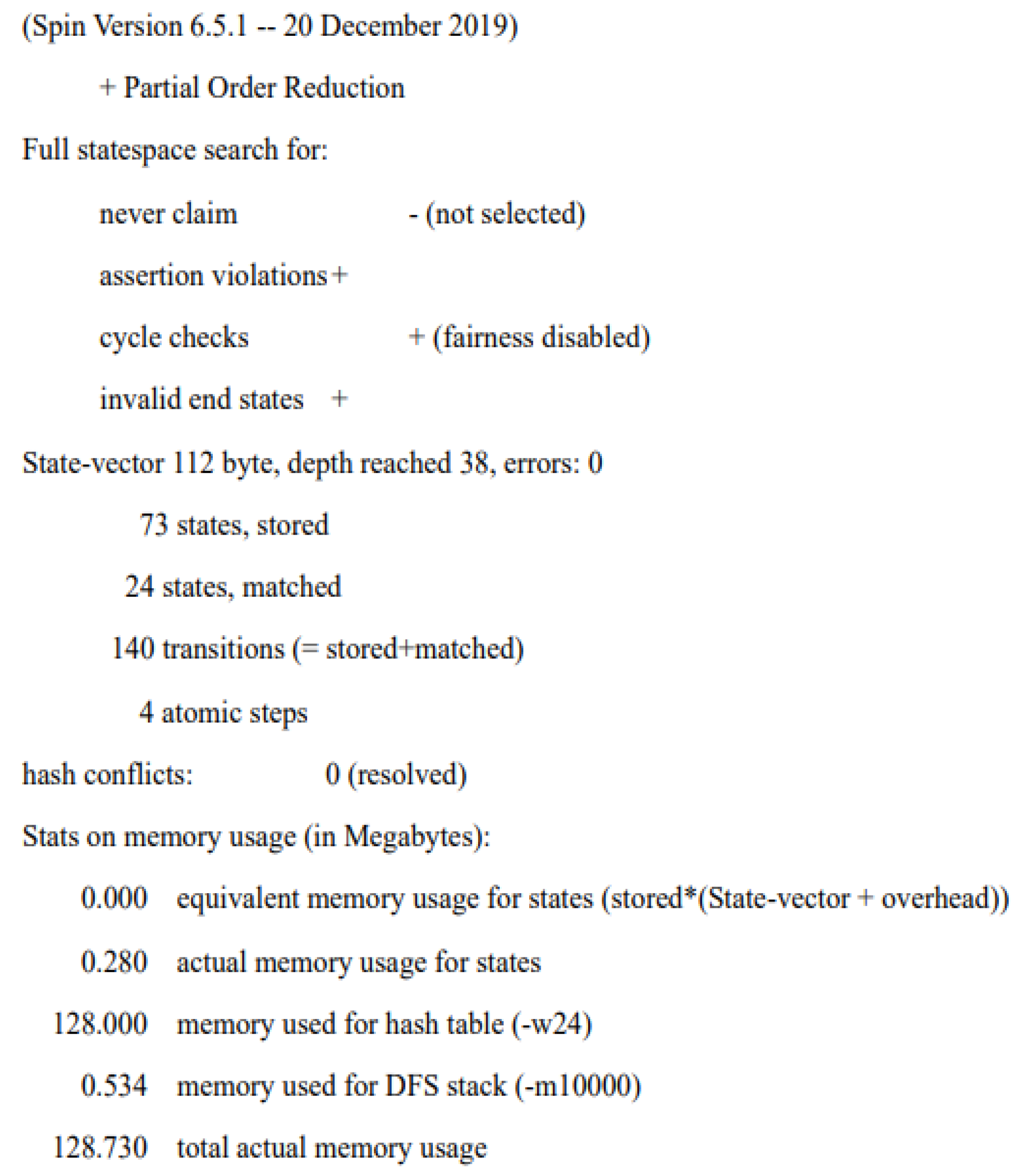
The model was validated using the tool SPIN and the results showed no attribute violations of the protocol and the validation results are shown in Figure 8.
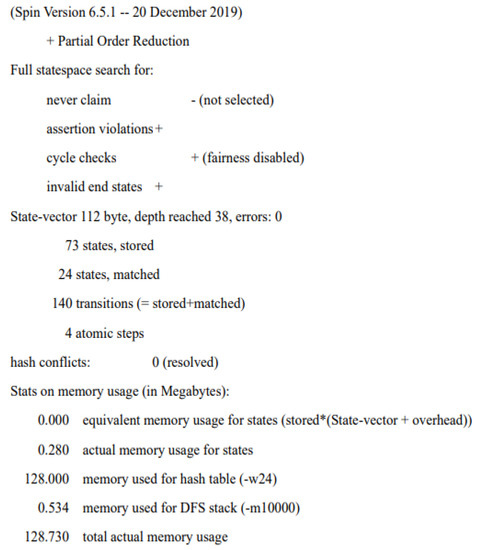
Figure 8.
Results of the experiment.
In the Verification Output window, perform the LTL attribute validation of the linear temporal logic in SPIN and observe the results as shown in Figure 8. The first part shows the version of model detection tool SPIN. The second part shows the operation of the whole model according to the experimental design. By default, the whole model is searched in all state space, and no error counterexample is generated, which meets the security requirements of the protocol. The third part describes that the global status system uses 112 bytes of memory space, the longest depth-first search path in the detection process contains 73 state transitions, no errors are detected in the search process, and the detection will automatically stop and report errors if there are any. There are 140 different global system states stored in the state space, each state needs 112 bytes to be described effectively, 24 traversal states are encountered, and the total amount of work is 140 state search traversals. The fourth part shows the amount of bytes in the memory space used by the data, and the total character size is 128.730 MB.
4.2. Informal analysis
4.2.1. Mutual Authentication
The proposed protocol can satisfy mutual authentication between both
- : The GCS first verifies and HMAC values, then uses the public key of the UAV certificate to verify , if successful, the UAV is successfully authenticated
- , is verified firstly, and then is verified with the public key of the GCS certificate, followed by multiple key, and HMAC value authentication. This method ensures the security of the two-way authentication phase of the protocol. Participants can authenticate each other by verifying that the received message is valid.
4.2.2. Perfect Forward Secrecy
Values and are randomly generated during communication, ensuring that the session key is randomly and evenly distributed in the key space. Attackers have no information advantage to calculate the session key from the intercepted messages and . Even if the attackers have obtained the session key of one of the communicating parties, it is impossible to obtain any information about the previous session key through this session key. The session key is generated from the refresh key , the master key and the counter value . After each session key is generated, the refresh key applies a hash function to the current refresh key to generate a new refresh key that removes and replaces the old one. As a result, no attackers can obtain any information about the old refresh key and thus cannot generate a session key; thus, the protocol has perfect forward security.
4.2.3. Session Key Agreement
According to the proposed protocol, the CCS and UAV negotiate the master key and then combine the refresh key and counter to calculate the session key and authentication key, rather than having one party generate and distribute them alone. Thus, the AKA protocol enables session key agreement.
4.2.4. Privileged Internal Attacks
This attack is carried out by entities in the UAV communication network, eavesdropping and obtaining valuable information from the communication. In the proposed protocol, only two communicating entities exchange information, regardless of whether they are in the authentication or communication phase, and no other entity is involved in the process. At the same time, the CA is already equipped with an insider threat program [30] that captures and neutralizes any insider threat, preventing it from sabotage, espionage, theft, and fraud. The model thus prevents unauthorized users from gaining authentication and access to system resources and prevents attacks by privileged insiders.
4.2.5. Replay Attack
In the replay attack, it is possible for attackers to eavesdrop and obtain communication messages between the UAV and the GCS and replay the authentication information or communication messages in the session. Therefore, using the timestamp mechanism to protect the freshness of the sent message and signing the timestamped message before sending it not only ensures the freshness of the received message, but also the integrity of the message. Attackers are unable to sign the timestamp and cannot achieve a replay attack. When the recipient receives the message, it first checks the freshness of the timestamp so that it can detect the replayed message, so the protocol is resistant to replay attacks.
4.2.6. Man-in-the-Middle Attacks
In a man-in-the-middle attack, attackers can eavesdrop and impersonate a communications entity to communicate with the UAV or GCS for the purposes of message tampering and information theft. If attackers modify messages , and , but lack information about internal credentials such as and , as well as the randomness of , and timestamps, attackers cannot complete the man-in-the-middle attack.
4.2.7. Denial of Service Attacks (DoS)
In the DoS attack, attackers hijack network resources to make them unusable by network entities. In the protocol, each message sent contains a timestamp, and both GCS and UAV verify the validity of the timestamp. In addition, during the authentication process, the timestamp and HMAC verification are doubly authenticated before the authentication signature, which can help defend against DoS attacks.
4.2.8. Drone Capture Attacks
When a UAV is captured, attackers can obtain the communication and key information stored in the UAV and then simulate it to establish a session with the UAV or the GCS. In the proposed protocol, even if attackers obtain the master key, the session key, and the authentication key, they cannot establish a session with the UAV or the GCS. Because the entire UAV network conducts keys refresh when the drone is captured, the unidirectional nature of the hash function and the random nature of the keys make it impossible for attackers to calculate the session key and the authentication key for the next phase of communication. Therefore, the scheme is resistant to drone capture attacks.
4.2.9. Desynchronization Attack
Desynchronization attack means that attackers block or intercept the interaction of the subject during the key update phase so that one party completes the key update and the other fails to do so. In this protocol, each legitimate entity is authenticated to perform the key update, and the key update is performed by passing the authentication, as well as determining whether the message is truncated and retransmitted by the freshness of the timestamp. Therefore, this protocol is resistant to desynchronization attacks.
5. Performance Analysis
This section compares the proposed protocol with the last three years of UAV communication protocols in terms of security and computational overhead.
- Comparison of safety characteristics
Table 9 shows a comparative analysis between the security properties of the protocols that shows the proposed protocol performs well and satisfy the requirements in all the given security properties. The literature [31,32,33] all satisfy anonymity, session key agreement, resistance to replay attacks, man-in-the-middle attacks and DoS attacks. In perfect forward secrecy, it is found that literature [32] does not satisfy the requirements. In addition, there is no mention of perfect backward secrecy in the literature [31,32,33]. As a result, if any long-term key used to derive past session keys has been made public, the adversary can use the session key to recover the encrypted message to obtain sensitive data, making subsequent sessions vulnerable to various attacks if any current long-term key is damaged. Previous protocols [31,32] are not able to resist privileged insider attacks. For resisting drone capture attacks, those described by [31] do not satisfy the requirements; and in [32] the problem is not mentioned.

Table 9.
Comparison of safety characteristics.
- Comparison of node overhead calculations
Let represent the execution time of Hash function operation; represents the execution time of Fuzzy extractor operation; represents the execution time of exponentiation operation; represents the execution time of Elliptic curve scalar point multiplication operation; represents the execution time of Bilinear pairing operation; represents the execution time of XOR operation; represents the execution time of pseudo-random number generation; represents the execution time of Key encryption and decryption operation; represents the execution time of elliptic curve point addition operation; represents the execution time of Concatenation operation; represents the execution time of Digital signature operation. The results are derived from a system with Intel Dual core 2.40 GHz processor, 18.04.5 Ubuntu operating system, and 5.7 GB RAM. The time of each operation is used as given in [34,35]: takes 0.0023 ms, takes 5.427 ms, takes 1.25 ms, takes 2.26 ms, takes 5.811 ms, takes 0.000126 ms; takes 0.00253 ms takes 3.85 ms takes 0.0288 ms, takes 0.00587 ms, takes 1.25 ms.
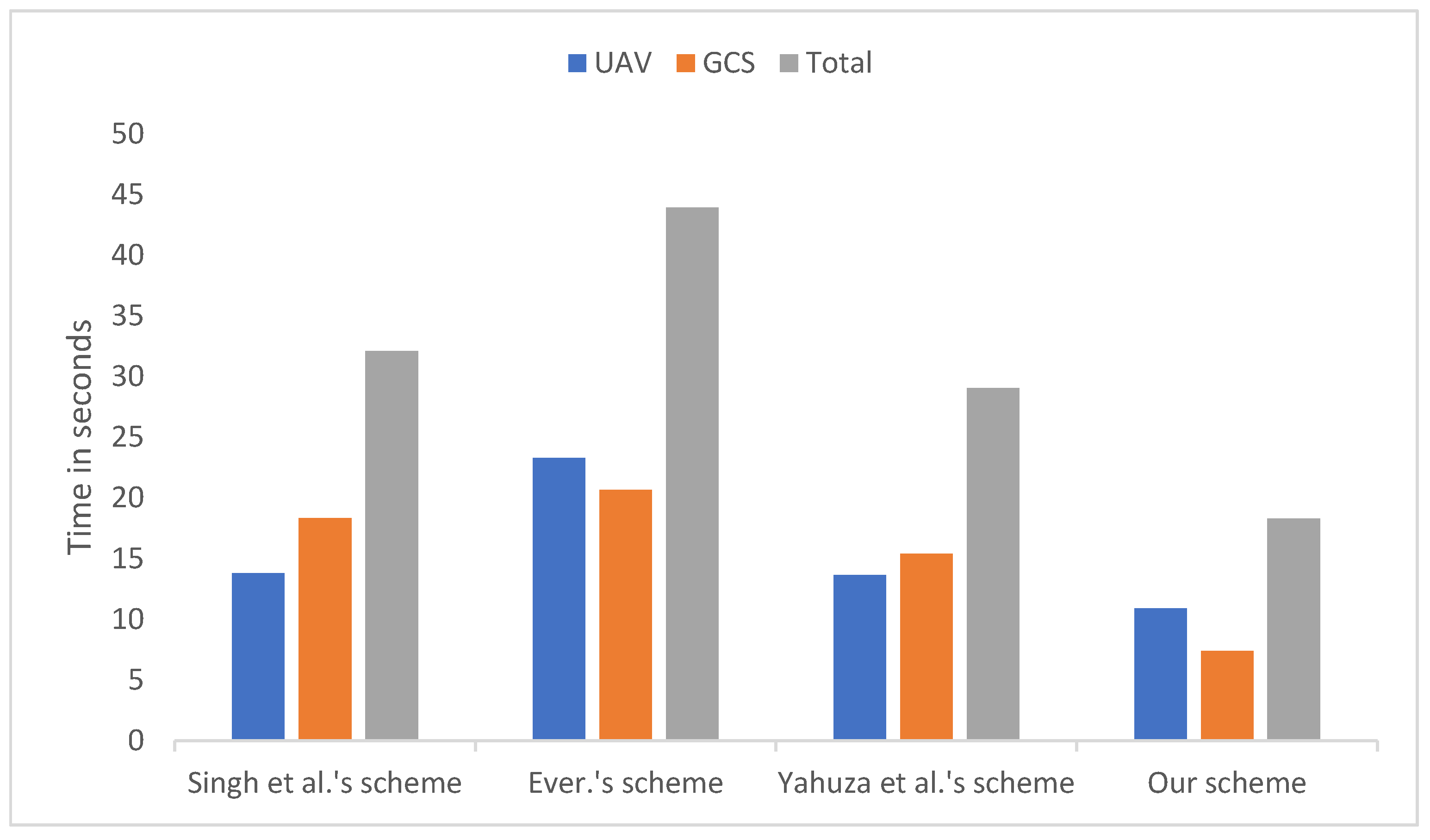
In the proposed protocol, the computation cost for UAV and GCS are and . Therefore, the total computed consumption is , about 18.298 ms. On the other hand, the schemes of Refs. [31,32,33] need approximately 32.12 ms, 19.152 ms and 29.0818 ms, respectively, as shown in Table 10 and Figure 9. This cost is better than the schemes of Refs. [31,32,33]. The proposed protocol is more balanced in terms of computational cost across nodes and the total computational cost is moderate.

Table 10.
Comparison of node computation overheads.
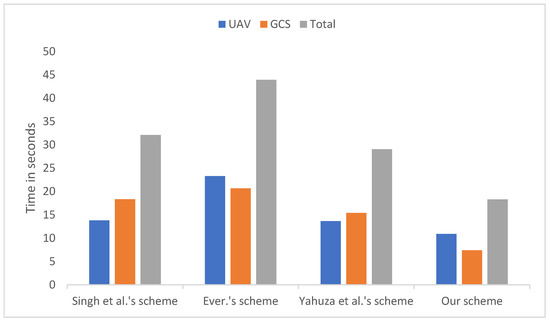
Figure 9.
Comparison of costing by node.
- Comparison of communication overheads
In this section, we compare the communication costs of the different participants involved in the transmission of messages during the authentication and key negotiation phases. Therefore, to estimate the communication costs, the sizes of the various credentials we take into account, such as timestamps, identities, random numbers, the digest of a hash function and elliptic curve point are 32 bits, 160 bits, 160 bits, 160 bits and 160 bits, respectively. Moreover, the outputs of AES symmetric encryption/decryption and signature operation are assumed 256 bits and 1024 bits respectively.
In the proposed protocol, the participating entities exchange three messages during the authentication and key negotiation phases:,, , whose costs are 576 bits, 832 bits, 1536 bits. Therefore, the total communication cost is 576 + 832 + 1536 = 2944 bits. On the other hand, the existing schemes of Ref. [31], Ref. [32] and Ref. [33] demand the communication costs of 3254 bits, 3312 bits, and 2496 bits, respectively. It is evident from Table 11 that the proposed protocol needs slightly lower communication cost than other existing schemes.

Table 11.
Comparison of communication overheads.
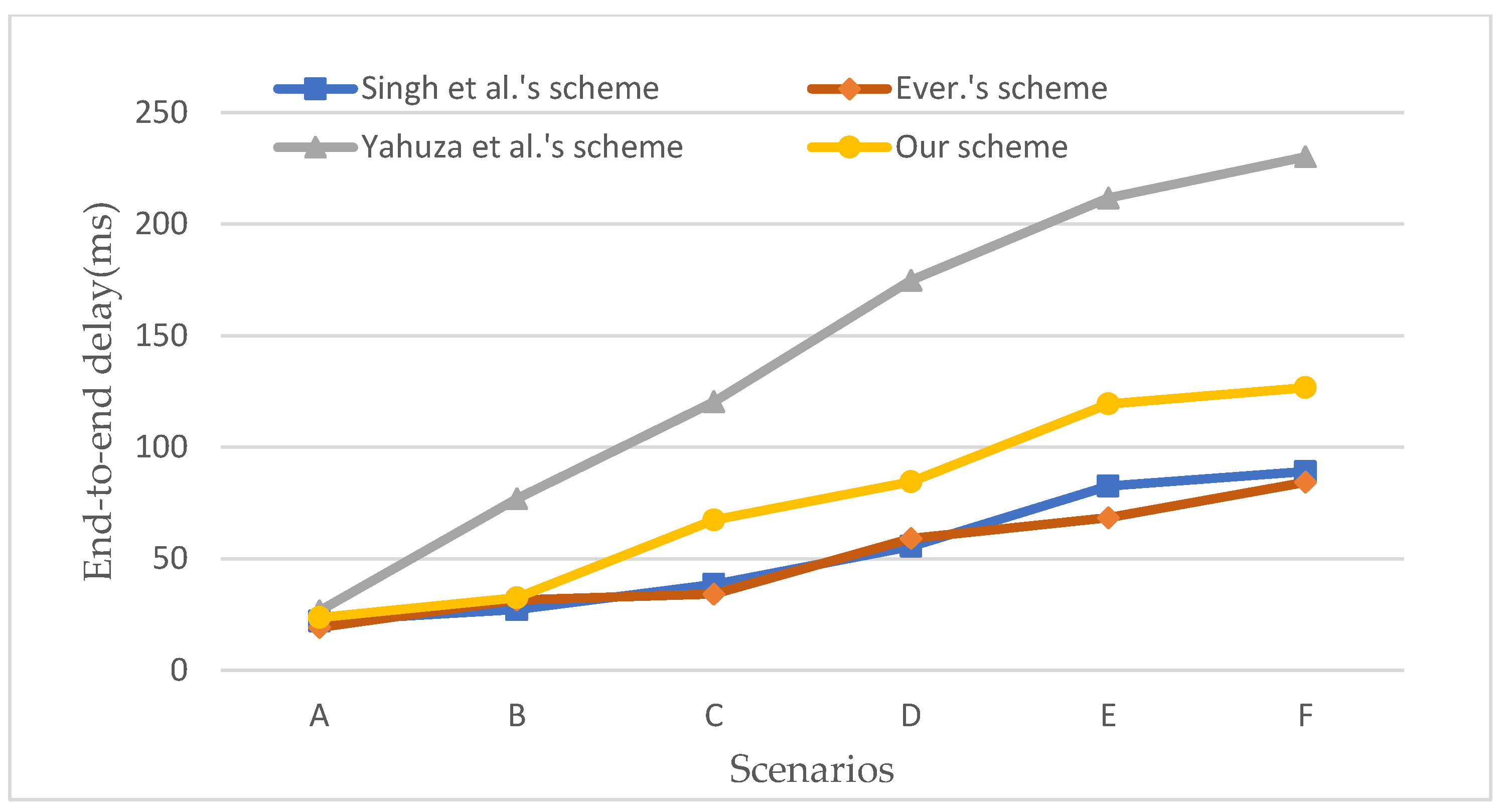
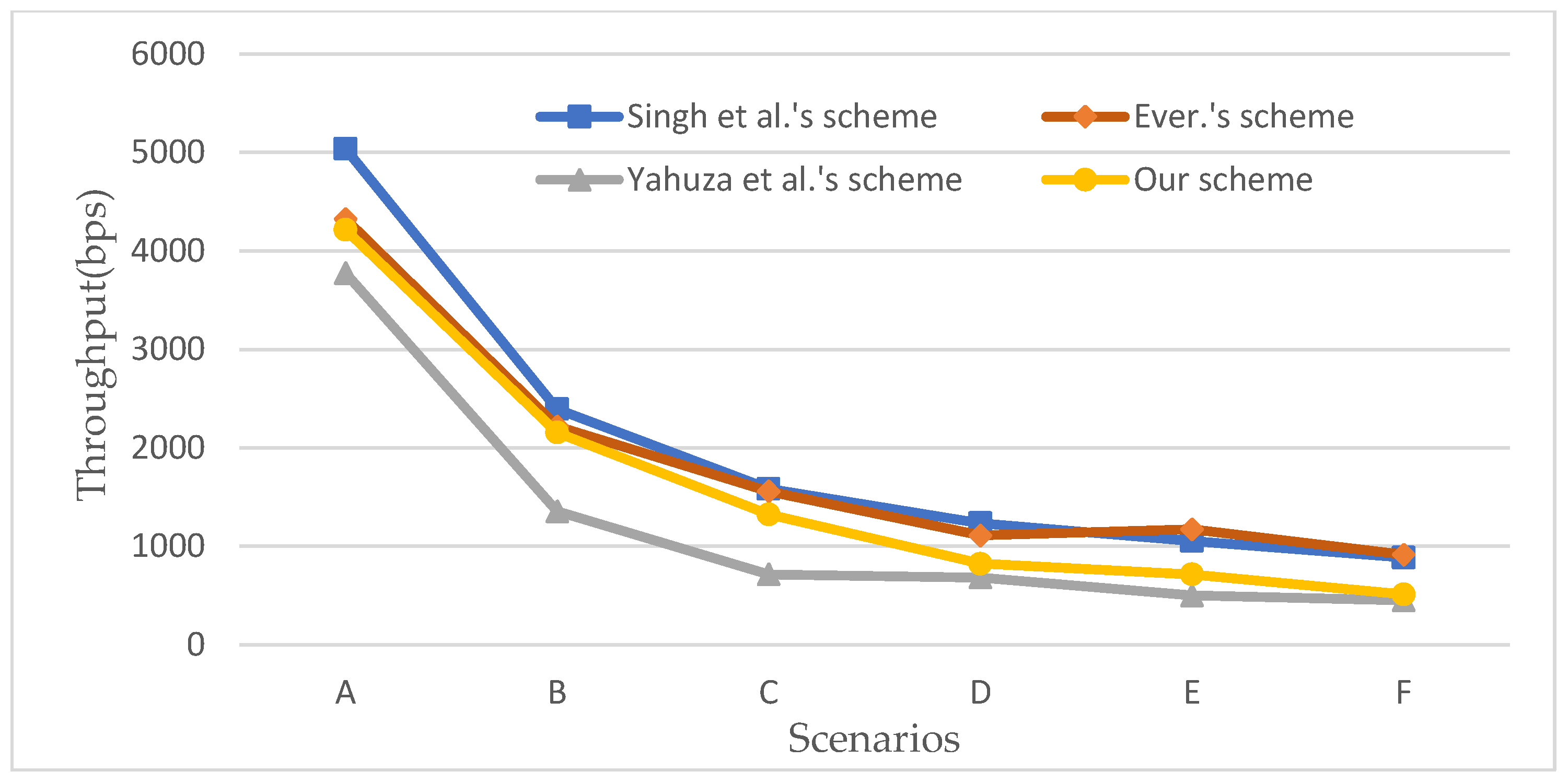
6. NS3 Simulation
In this section, the proposed protocol is simulated and analyzed using the NS3 tool. The performance of the CSCMS protocol in terms of end-to-end delay and throughput is evaluated. The experimental environment is shown in Table 12. The experiments will be carried out in six simulation scenarios and the end-to-end latency simulation comparison results are shown in Figure 10 and the throughput simulation comparison results are shown in Figure 11. The experimental results show that with the increasing number of UAVs, the end-to-end delay of information transmission gradually increases, and the throughput of information transmission continuously declines.

Table 12.
Simulation environment.
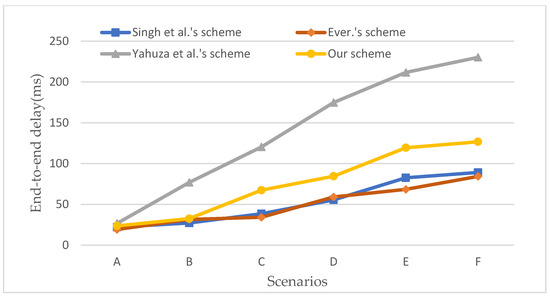
Figure 10.
Comparison of end-to-end delays among different schemes [31,32,33].
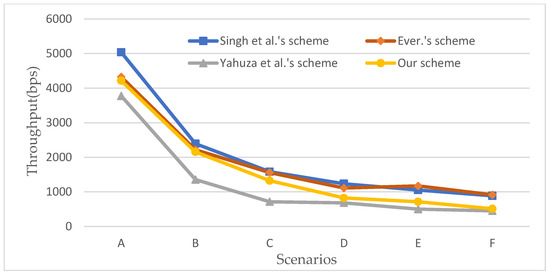
Figure 11.
Comparison of throughputs among different schemes [31,32,33].
The NS3 simulation results show that the protocol in this paper has lower end-to-end delay and higher throughput. The protocol in [31] is slightly better than this paper in terms of end-to-end latency and throughput, but it has higher computational overhead, high transmission latency in the authentication phase, and lacks mutual authentication and cannot resist privileged insider attacks and drone capture attacks, as well as lacking backward secrecy. The protocol in [32] is slightly better than this paper in terms of end-to-end latency and throughput, but its computational overhead is higher than this paper’s protocol and, similar to [31], it is not resistant to privileged insider attacks, and there is no mention of backward secrecy or resistance to drone capture attacks. The protocol in [33] has better transmission latency and computational overhead in the authentication phase than the protocol in this paper, but its end-to-end delay is too large, and its throughput is lower, and as like [31,32], neither of them mentions backward secrecy. In summary, the CSECMAS protocol satisfies security and applicability at a little performance cost.
7. Conclusions
This paper focuses on the analysis and research of security issues arising in UAV communication. We propose a security protocol suitable for UAV communication and use the key node to achieve secure communication between UAVs using multiple key encryption combined with hash functions and digital signature technology to achieve multiple identity authentication between both, effectively improving the security of the protocol. Through formal analysis of the proposed protocol, the verification results did not find any vulnerability, proving that the protocol has high security; finally, the security analysis and performance evaluation of the protocol were conducted, and the results showed that the protocol has the advantages of anonymity, integrity, and perfect forward secrecy.
However, the following issues with this protocol still need further investigation: privacy protection is particularly important for drone communication, and identity privacy is not considered in the textual scheme. Although pseudonyms are used to hide the real identity, there is still the possibility of associativity. How to achieve privacy protection of user identities in a simpler way is still an issue that needs to be addressed. Drone privacy protection is particularly important, and identity privacy is not considered in the textual scheme. Although it is possible to use pseudonyms in a way that to hide the real identity, there is still the possibility of associativity. How to implement a simpler way to protect the privacy of the user’s identity is still an issue that needs to be addressed.
Author Contributions
Methodology, L.L. and X.L.; Software, L.L.; Formal analysis, L.L.; Writing—original draft, L.L. and X.L.; Writing—review & editing, Y.W. and L.T.; Supervision, Y.W. and L.T. All authors have read and agreed to the published version of the manuscript.
Funding
This research received no external funding.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Liu, J.; Wang, W.; Wang, T.; Shu, Z.; Li, X. A Motif-Based Rescue Mission Planning Method for UAV Swarms Using an Improved PICEA. IEEE Access 2018, 6, 40778–40791. [Google Scholar] [CrossRef]
- Sutheerakul, C.; Kronprasert, N.; Kaewmoracharoen, M.; Pichayapan, P. Application of Unmanned Aerial Vehicles to Pedestrian Traffic Monitoring and Management for Shopping Streets. Transp. Res. Procedia 2017, 25, 1717–1734. [Google Scholar] [CrossRef]
- Fan, R.; Cui, J.; Jin, S.; Yang, K.; An, J. Optimal Node Placement and Resource Allocation for UAV Relaying Network. IEEE Commun. Lett. 2018, 22, 808–811. [Google Scholar] [CrossRef]
- Khan, M.A.; Ectors, W.; Bellemans, T.; Ruichek, Y.; Yasar, A.-U.; Janssens, D.; Wets, G. Unmanned Aerial Vehicle-based Traffic Analysis: A Case Study to Analyze Traffic Streams at Urban Roundabouts. Procedia Comput. Sci. 2018, 130, 636–643. [Google Scholar] [CrossRef]
- Bunse, C.; Plotz, S. Security analysis of drone communication protocols. In Proceedings of the International Symposium on Engineering Secure Software and Systems, Paris, France, 26–27 June 2018; Springer: Cham, Switzerland, 2018; Volume 9, pp. 96–107. [Google Scholar] [CrossRef]
- Humphreys, T. Statement on the Vulnerability of Civil Unmanned Aerial Vehicles and Other Systems to Civil GPS Spoofing; University of Texas at Austin: Austin, TX, USA, 2012; pp. 1–16. [Google Scholar]
- Krishna, C.G.L.; Murphy, R.R. A review on cybersecurity vulnerabilities for unmanned aerial vehicles. In Proceedings of the 2017 IEEE International Symposium on Safety, Security and Rescue Robotics (SSRR), Shanghai, China, 11–13 October 2017; Volume 4, pp. 194–199. [Google Scholar] [CrossRef]
- Choudhary, G.; Sharma, V.; You, I. Sustainable and secure trajectories for the military Internet of Drones (IoD) through an efficient Medium Access Control (MAC) protocol. Comput. Electr. Eng. 2019, 74, 59–73. [Google Scholar] [CrossRef]
- Won, J.; Seo, S.-H.; Bertino, E. A secure communication protocol for drones and smart objects. In Proceedings of the 10th ACM Symposium on Information, Computer and Communications Security, Singapore, 14–17 April 2015; ACM: New York, NY, USA, 2015; pp. 249–260. [Google Scholar] [CrossRef]
- Rodday, N.M.; Schmidt, R.D.O.; Pras, A. Exploring security vulnerabilities of unmanned aerial vehicles. In Proceedings of the NOMS 2016—2016 IEEE/IFIP Network Operations and Management Symposium, Istanbul, Turkey, 25–29 April 2016; Volume 16, pp. 993–994. [Google Scholar] [CrossRef]
- Chriki, A.; Touati, H.; Snoussi, H.; Kamoun, F. FANET: Communication, mobility models and security issues. Comput. Netw. 2019, 163, 106877. [Google Scholar] [CrossRef]
- Khan, N.A.; Jhanjhi, N.Z.; Brohi, S.N.; Nayyar, A. Emerging Use of UAV’s: Secure Communication Protocol Issues and Challenges. In Drones in Smart-Cities; Elsevier: Amsterdam, The Netherlands, 2020; pp. 37–55. [Google Scholar]
- Abdi, F.; Chen, C.-Y.; Hasan, M.; Liu, S.; Mohan, S.; Caccamo, M. Preserving Physical Safety Under Cyber Attacks. IEEE Internet Things J. 2018, 6, 6285–6300. [Google Scholar] [CrossRef]
- Petit, J.; Mammeri, Z. Authentication and consensus overhead in vehicular ad hoc networks. Telecommun. Syst. 2011, 52, 2699–2712. [Google Scholar] [CrossRef]
- Seo, S.-H.; Won, J.; Bertino, E.; Kang, Y.; Choi, D. A Security Framework for a Drone Delivery Service. In Proceedings of the 2nd Workshop on Micro Aerial Vehicle Networks, Systems, and Applications for Civilian Use, Singapore, 26 June 2016; Volume 26, pp. 29–34. [Google Scholar] [CrossRef]
- Wang, G.; Lim, K.; Lee, B.-S.; Ahn, J.Y. Handover Key Management in an LTE-based Unmanned Aerial Vehicle Control Network. In Proceedings of the 2017 5th International Conference on Future Internet of Things and Cloud Workshops (FiCloudW), Prague, Czech Republic, 21–23 August 2017; Volume 5, pp. 200–205. [Google Scholar] [CrossRef]
- Blazy, O.; Bonnefoi, P.-F.; Conchon, E.; Sauveron, D.; Akram, R.N.; Markantonakis, K.; Mayes, K.; Chaumette, S. An Efficient Protocol for UAS Security. In Proceedings of the 2017 Integrated Communications, Navigation and Surveillance Conference (ICNS), Herdon, VA, USA, 18–20 April 2017; Volume 4, pp. 1–21. [Google Scholar] [CrossRef]
- Li, F.; Han, Y.; Jin, C. Practical access control for sensor networks in the context of the Internet of Things. Comput. Commun. 2016, 89, 154–164. [Google Scholar] [CrossRef]
- Benzarti, S.; Triki, B.; Korbaa, O. Privacy Preservation and Drone Authentication Using ID-Based Signcryption. SOMET 2018, 303, 226–239. [Google Scholar] [CrossRef]
- Chen, L.; Qian, S.; Lim, M.K.; Wang, S. An enhanced direct anonymous attestation scheme with mutual authentication for network-connected UAV communication systems. China Commun. 2018, 15, 61–76. [Google Scholar] [CrossRef]
- Tian, Y.; Yuan, J.; Song, H. Efficient privacy-preserving authentication framework for edge-assisted Internet of Drones. J. Inf. Secur. Appl. 2019, 48, 102354. [Google Scholar] [CrossRef]
- Semal, B.; Markantonakis, K.; Akram, R.N. A Certificateless Group Authenticated Key Agreement Protocol for Secure Communication in Untrusted UAV Networks. In Proceedings of the 2018 IEEE/AIAA 37th Digital Avionics Systems Conference (DASC), London, UK, 23–27 September 2018; IEEE: Piscataway, NJ, USA, 2018; pp. 1–8. [Google Scholar] [CrossRef]
- Turkanović, M.; Brumen, B.; Hölbl, M. A novel user authentication and key agreement scheme for heterogeneous ad hoc wireless sensor networks, based on the Internet of Things notion. Ad Hoc Netw. 2014, 20, 96–112. [Google Scholar] [CrossRef]
- Farash, M.S.; Turkanović, M.; Kumari, S.; Hölbl, M. An efficient user authentication and key agreement scheme for heterogeneous wireless sensor network tailored for the Internet of Things environment. Ad Hoc Netw. 2016, 36, 152–176. [Google Scholar] [CrossRef]
- Amin, R.; Islam, S.H.; Biswas, G.; Khan, M.K.; Leng, L.; Kumar, N. Design of an anonymity-preserving three-factor authenticated key exchange protocol for wireless sensor networks. Comput. Netw. 2016, 101, 42–62. [Google Scholar] [CrossRef]
- Challa, S.; Wazid, M.; Das, A.K.; Kumar, N.; Reddy, A.G.; Yoon, E.-J.; Yoo, K.-Y. Secure Signature-Based Authenticated Key Establishment Scheme for Future IoT Applications. IEEE Access 2017, 5, 3028–3043. [Google Scholar] [CrossRef]
- Wazid, M.; Das, A.K.; Kumar, N.; Vasilakos, A.V.; Rodrigues, J.J.P.C. Design and Analysis of Secure Lightweight Remote User Authentication and Key Agreement Scheme in Internet of Drones Deployment. IEEE Internet Things J. 2018, 6, 3572–3584. [Google Scholar] [CrossRef]
- Zhang, Y.; He, D.; Li, L.; Chen, B. A lightweight authentication and key agreement scheme for Internet of Drones. Comput. Commun. 2020, 154, 455–464. [Google Scholar] [CrossRef]
- Dolev, D.; Yao, A. On the security of public key protocols. IEEE Trans. Inf. Theory 1983, 29, 198–208. [Google Scholar] [CrossRef]
- Guido, M.D.; Brooks, M.W. Insider threat program best practices. In Proceedings of the 46th Hawaii International Conference on System Sciences, Wailea, HI, USA, 7–10 January 2013; IEEE: Piscataway, NJ, USA, 2013; Volume 46, pp. 1831–1839. [Google Scholar] [CrossRef]
- Singh, J.; Gimekar, A.; Venkatesan, S. An efficient lightweight authentication scheme for human-centered industrial Internet of Things. Int. J. Commun. Syst. 2019, 6, e4189. [Google Scholar] [CrossRef]
- Ever, Y.K. A secure authentication scheme framework for mobile-sinks used in the Internet of Drones applications. Comput. Commun. 2020, 155, 143–149. [Google Scholar] [CrossRef]
- Yahuza, M.; Idris, M.Y.I.; Wahab, A.W.A.; Nandy, T.; Bin Ahmedy, I.; Ramli, R. An Edge Assisted Secure Lightweight Authentication Technique for Safe Communication on the Internet of Drones Network. IEEE Access 2021, 9, 31420–31440. [Google Scholar] [CrossRef]
- Tanveer, M.; Zahid, A.H.; Ahmad, M.; Baz, A.; Alhakami, H. LAKE-IoD: Lightweight Authenticated Key Exchange Protocol for the Internet of Drone Environment. IEEE Access 2020, 8, 155645–155659. [Google Scholar] [CrossRef]
- Abbasinezhad-Mood, D.; Nikooghadam, M. Design and hardware implementation of a security-enhanced elliptic curve cryptography based lightweight authentication scheme for smart grid communications. Futur. Gener. Comput. Syst. 2018, 84, 47–57. [Google Scholar] [CrossRef]
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).