1. Introduction
A software audit (SA) is a systematic examination of the software’s design, implementation, and results in relation to predetermined criteria (such as quality, progress, or conformity with goals, standards, and laws) [
1,
2]. Audits of software may be performed either in-house by organizations such as development teams or by external entities. For larger audits, it may be necessary for many people to work together under the direction of a single lead auditor. In most cases, certain tools are used to collect the necessary data for a SA. Audits of functionality or security might be performed with the use of various analytic tools [
3,
4,
5,
6,
7]. Proprietary tools may be reviewed as part of a compliance audit if and when software is sold or its status has to be confirmed. Audits are necessary for ensuring consistent software quality, removing unused licenses, optimizing corporate processes, and meeting regulatory and compliance needs [
6,
8,
9].
There are usually two types of audits that are commonly used in software organizations: those conducted inside an organization by its staff, and those conducted by an outside party [
10]. SA performed by an outside party might be helpful when in-house knowledge is lacking or when you need a second, unbiased opinion. It may also be necessary to bring in an outside auditor if your internal team is overburdened, inexperienced, or otherwise unable to complete the audit on time. Internal audits are crucial and should be conducted on a regular basis, but they frequently lack the rigor and expertise that may be provided by external specialists. Because both sorts are necessary, it is important to note that external auditors, thanks to their objectivity and thoroughness, often find more genuine concerns. As developers often do not know what to look for in terms of legal and compliance concerns, it is useful to have an outside party perform an audit of the software [
11,
12,
13].
Auditing is the procedure of examining the documents and records of a software development organization for errors and discrepancies. Data stored here must accurately reflect the workings of the program and the transactions that have taken place inside it. As these files are maintained internally, there is a great potential for fraud or manipulation on the part of employees with access to them [
6,
14,
15]. Due to the many incentives for falsifying these documents, audits are essential for ensuring accuracy. In accordance with current auditing standards, auditors must have reasonable confidence that the organization’s records, when considered as a whole, are free from serious misrepresentation, whether due to simple mistakes or fraud. In order to offer a clean or qualified opinion, auditors must satisfy themselves that the financial statements of the business are free of substantial errors.
Since the audit is becoming more crucial to the stability of the software marketplaces, major efforts have been undertaken in recent years to increase its efficacy. The adoption of new auditing standards, maintaining audit records, and adopting computer-assisted audit tools and procedures are notable among the primary endeavors [
16,
17,
18]. Despite all these efforts and strict regulation by the government, audit fraud persist globally. In order to make SA free from fraudulent behavior, there is a need for an end-to-end transparent system that could detect any fraudulent activity by internal or external auditors. To address this gap, this study provides a blockchain-based solution for securing the audit process from internal or external fraud. Blockchain technology (BCT) has the ability to affect all recordkeeping activities, including the initiation, processing, authorization, recording, and reporting of transactions [
19,
20,
21]. When new blockchain-based methodologies and processes arise, the function and skill sets of auditors may shift. For instance, techniques for getting adequate audit evidence must consider both conventional stand-alone general ledgers and blockchain-based ledgers. In addition, reporting and accounting might benefit from improved consistency and openness, allowing for more effective data extraction and analysis. BCT may have a substantial influence on how auditors carry out their engagements. It helps in automation and data analytics. Keeping in view the importance of blockchain and some other cutting-edge technologies such as 5G and cloud, we propose a framework named smart and secure framework for transparent auditing (SSFTA). The explicit contribution of the paper is as follows:
Proving the detailed overview/taxonomy of the audit process, including audit types, features, principles, and steps of conducting the audit process;
Reviewing and evaluating the research on the influence of BCT on auditing;
Proposed SSFTA as a framework that would aid auditors in using 5G, Cloud, and BCT to enhance company information systems, save time, and avoid fraudulent activities during software auditing;
Using smart contracts and digital ledger (DTL) for transparency and accountability.
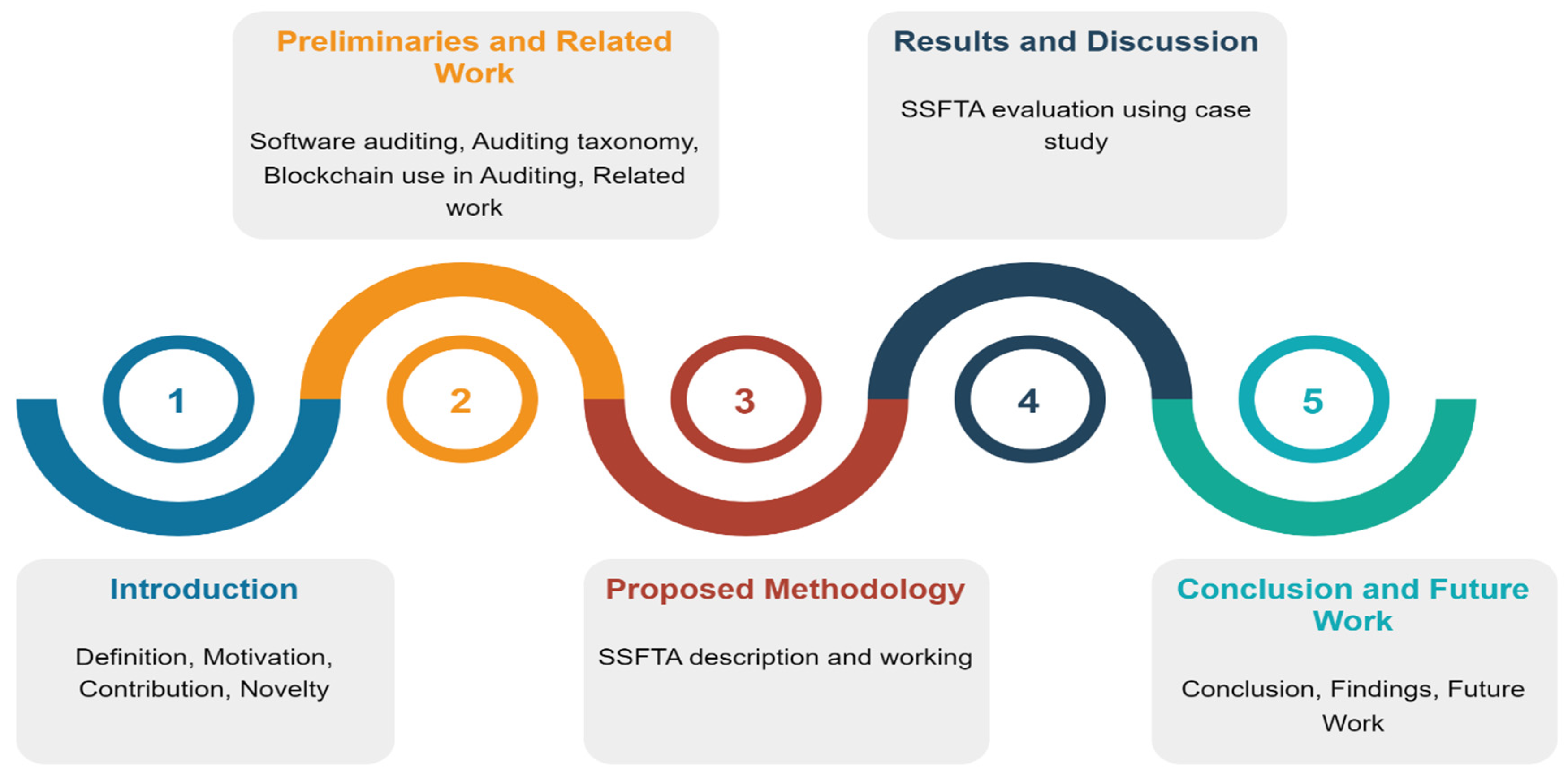
The organization of the paper is briefly elaborated in
Figure 1.
Table 1 provides the details of important abbreviations used in the paper.
3. Proposed Methodology
Organizations rely heavily on SA because they check to see whether a software product or process is compliant with rules, norms, and policies. In contrast, BCT may cause a major shift in the auditing and controlling industry. In this part, we propose the SSFTA framework to offer a smart and secure audit procedure, bearing in mind the significance of both audit and BCT.
Figure 3 provides a pictorial overview of SSFTA. According to SSFTA, software organizations create audit policies that include remediation procedures, remediators, and policy rules where particular breaches are defined by policy regulations. When an audit scan finds a breach of a policy rule, the remediation procedure is initiated, and remediators are appointed users with the authority to address the violation. Remediators can be a single user or a group of people appointed to address security violations. These policy rules are stored in the private cloud from which authorized persons can access them. Once the policy rules are defined, they are documented using a smart contract so that they may be immutable. Once the organization decides to conduct IA or external audit (XA), these policy rules are shared with the audit team.
The organization defines the audit subject and criteria to the audit team, which is also written in the form of a smart contract and also stored in the private cloud to make it immutable and secure. The audit team collects information about the audit environment, collects audit logs, and uses automated audit tools to perform the audit process along with the manual auditing process. An audit log, sometimes referred to as an audit trail, is a record of the actions taken by the IT devices on a network in response to certain events. Event logs are recorded in audit logs and often relate to a single operation or a set of activities. They keep track of who performed an action, the action itself, and the reaction of the system. The procedures and technologies used by auditors to carry out audit processes are characterized by automation. The operational environment comprises a company’s or organization’s policies and processes, as well as the creation of protocols for the more efficient implementation of environmental laws and regulations. The audit team must make sure that they examine environmental compliance and implementation in great detail. After analyzing environmental parameters, getting audit logs, and selecting audit automation tools, the audit team starts the audit process by following the seven steps mentioned in SSFTA. During the audit process, the audit response team monitors the audit process and generates the monitoring reports that are stored in blockchain DTL and cloud. Once the audit process is complete, the results are stored in the cloud. The organization accesses the monitoring reports and audit results from the cloud using 5G to obtain insights into the audit result. The process of using BCT, DTL, and smart contracts is mentioned in Algorithm 1.
| Algorithm 1 Audit Process using blockchain DTL and smart contract |
| Let |
| ; |
| ; ; ; |
| ; ; |
| 1. |
| 2. |
| 3. |
| 4. |
| 5. |
| 6. |
| 7. |
| 8. |
| 9. |
| 10. |
| 11. |
| 12. |
| 13. |
| 14. |
| 15. |
| 16. |
| 17. |
| 18. |
| 19. |
| 20. |
| 21. |
| 22. |
| 23. |
| 24. |
| 25. |
| 26. |
| 27. |
| 28. |
| 29. |
| 30. |
| 31. |
| 32. |
| 33. |
| 34. |
| 35. |
Practical Implications of the Proposed Framework
Software auditing is the process of evaluating the conformance and quality of software to verify its correctness and fairness. The audit reports must accurately reflect a software’s real status and functioning. When software is created domestically, there is a considerable danger of manipulation or fraud by insiders. There are several personal motivations for these manipulations; thus, auditing is essential to guarantee that nothing is misrepresented. Traditional auditing procedures make it difficult to provide transparency. Blockchain is a DTL that enables safe, transparent, and tamper-proof transactions. It may be used in the software audit process to build confidence amongst process participants and monitor changes. The whole software audit process, from audit planning to audit report creation, may be recorded using blockchain technology. The blockchain gives visibility over who made what modifications, when, how those changes were made, and where those finished changes went. This ensures that everyone participating in the process is informed of any changes or updates, preventing disagreements or misunderstandings. The advantages of using blockchain in software auditing include enhanced security, shorter project completion times owing to less paperwork, and more precision due to immutable data. The proposed framework not only uses BCT, but rather it also leverages the potentials of 5G and clouds for efficient data storage and transmission. To make the audit process transparent, everything is documented using DTL and smart contract; further, the role of the audit response and monitoring team is also highlighted to ensure the security and transparency of the whole process.
Further, the conventional type of audit evidence, which was proof produced by the firm or based on papers from outside sources, will be evolved into information that is communicated, processed, kept, or retrieved electronically using SSFTA. Technologies such as cloud computing, 5G, and blockchain used in SSFTA allow auditors to extract and evaluate the whole accounting data without the requirement for sampling in the big data environment of today. The dependability of this method is substantially greater than manual data collection because of automated data extraction. Blockchain also has the potential to improve the reliability of the evidence. Aggregating information will no longer be necessary since blockchain can store audit proof from many sources. Sampling is another stage of the audit process that has been modified by blockchain. Data analytics and storage are used to examine whole data sets rather than simply samples picked by auditors. With the continual sharing of data across 5G and the cloud, an effective internal control environment is produced. The audit process using SSFTA will be evolved from being utilized for testing and exams toward being a preventative one. Using the proposed SSFTA, the position of the auditor will be changed from one assurance to one of strategic partners and counselors.
4. Results and Discussion
Confidence and well-informed software marketplaces depend on audit reports that are both thorough and accurate. While audit findings contribute to successful root cause analysis, future planning, generating recommendations, and many more, it is crucial that audit quality and consistency of execution be improved to preserve trust in the independent assurance they provide. Both quantitative and qualitative approaches to audit process executions have flaws that are somewhat offset by the other’s benefits. Quantitative evaluation of the audit process lends itself well to establishing cause-and-effect relationships, testing hypotheses, and determining the opinions, attitudes, and practices of a large population, whereas qualitative evaluation of the audit process lends itself well to developing hypotheses and theories and describing processes such as decision making and communication. Quantitative research creates factual, trustworthy result data that are typically generalizable to wider groups, while qualitative research generates rich, comprehensive, and valid process data based on the participant’s viewpoints and interpretations rather than the investigator’s. In this study, the qualitative approach was chosen for the evaluation of SSFTA due to several reasons: the majority of existing studies focus on financial audits, whereas there are few studies on software audits; since the software is developed for and by humans, the qualitative approach provides more insight into the proposed software audit process. Furthermore, qualitative approaches investigate the limits and flaws of a process more thoroughly. They provide a deeper comprehension of the richness and diversity of human experience in all-natural contexts. We used a case study as a qualitative assessment method for the SSFTA evaluation. A case study is a research method used to develop a comprehensive, multifaceted knowledge of a complicated subject in its real-world setting.
In order to evaluate the proposed methodology, we conducted a case study with a well-known software industry. The subject organization is a market leader in the software industry. It commenced operations in 1977. The organization has competence in a wide range of software solutions and IT services. Digital commerce, application development and integration, business applications, cloud services, data analysis and management, application development and integration, IT infrastructure, and business process outsourcing are among their areas of specialization. An online appointment was scheduled with the company through some reference. In this online session, we elaborated on the working and potentials of SSFTA to the participants. In the end, they were requested to fill out a questionnaire to evaluate the SSFTA based on three key parameters, namely, ease of use, security, and structure of SSFTA. The questionnaire consists of three sections. Section one includes a detailed description of SSFTA. Section two was related to the demographics of respondents, and section three consisted of questions related to the three measurement parameters mentioned above. The respondents were asked to provide their feedback about SSFTA on a Likert scale as follows: Strongly Agree = 5, Agree = 4, Neutral = 3, Disagree = 2, and Strongly Disagree = 1. The 12 representatives from the organization participated in the questionnaire, and the total and average of the strongly agree and agree was calculated. Below we discuss the details of responses against each parameter.
Table 3 shows the questions that were asked by the respondents to evaluate the usability and ease of use of the SSFT. The respondents were asked to answer these questions using the Likert scale. Once all the responses were performed, the total of strongly agree and agree was calculated. A total of 70% was set as a threshold value, which means if 8 out of 12 respondents agree on a certain question, quality exists in the SSFT.
Figure 4 shows the statistics of respondents for each question related to ease of use. Most of the questions were ranked more than 8, which shows that SSFTA is easy to use for a software audit.
Table 4 includes the four questions that were asked of the respondents to evaluate the security of SSFTA. The respondents’ evaluation of the questions related to SSFTA security is depicted in the graph of
Figure 5.
According to
Figure 5, the total percentage of agreement was more than the threshold value for each question related to the security of the software audit process while using SSFTA. This shows that SSFTA is helpful in preventing software from audit fraud.
Table 5 lists three questions that were used to evaluate the structure of SSFTA. These questions aimed to evaluate whether the structure of SSFTA is self-explanatory and applicable.
Figure 6 depicts the respondents’ evaluation regarding the structure of SSFTA. The results of
Figure 6 show that SSFTA is self-explanatory, applicable in real software settings, and uses the latest tools and technologies for software auditing.
Now, BCT has expanded well beyond bitcoin and is being tried out in a variety of corporate and financial contexts. However, a major obstacle to blockchain’s disruptive potential is that the technology is still in its infancy and has not been demonstrated at the business size. Several accounting firms have launched blockchain projects to learn more about the potential of this technology, yet only a select number have used it in their audits. Much of the current research, as shown in
Table 2, just investigate the possibilities and identifies the difficulties of using BCT in auditing. Moreover, not a single one of these investigations is dedicated to software audit rather than financial transaction audit. In addition, the proposed remedies in these studies are only suggestions and have not been subjected to any kind of empirical testing. The current studies on how BCT is used in auditing only use BCT to make the auditing process easier. They do not look at how other cutting-edge technologies could be used. Our proposed work is different from what has already been performed in many ways: First, it looks at the role of BCT in the process of auditing software. Second, SSFTA offers a complete auditing process with efficient ways to store, send, and protect audit data. SSFTA uses the power of 5G, cloud computing, and BCT to make the auditing process speedy and transparent.
- b.
Weaknesses and limitations of the proposed methodology
-
Following are the limitations and weaknesses of the proposed methodology
We did not find enough studies on software audit using blockchain, so it was difficult to find the parameters based on which proposed framework SSFTA may be compared with existing research
Blockchain technology is still new and has not been tested on a large scale yet, which is a big problem for its potential to change the world. Therefore, to implement SSFTA in real settings, much training and organizational support are required.
The proposed framework was evaluated using a case study with 12 respondents only (although the sample was representative), which is a small sample, and results cannot be fully generalized for the whole population.
Organizations need enough resources to implement the proposed framework.
- c.
Reliability of obtained observations
Targeting a sizable population was challenging because of the lack of adoption and understanding of blockchain technology in the healthcare industry. Nonetheless, we choose a representative sample to guarantee the accuracy of the results. To learn more about a certain population and make in-depth observations about it, a representative sample is one method that may be employed. A representative sample is a tiny subgroup group that aims to proportionately reflect defined traits demonstrated in a target population [
47,
48]. In order to ensure that our sample is representative of the whole, we asked the company in question to include members of the quality assurance/quality control team and the software audit team in our online session and survey evaluations. Twelve professionals with at least five years of expertise in quality assurance or software testing were surveyed and participated in an online session.
5. Conclusions and Future Work
BCT is already being discussed as one of the next megatrends. Researchers and organizations are beginning to comprehend the potential advantages of this technology and are investigating how its numerous uses might disrupt our current reality. The capacity to transfer BCT from idea to acceptance and manufacturing, however, has been limited so far. When it comes to auditing, BCT might provide significant advantages by lowering auditors’ labor, minimizing fraud, and optimizing current procedures; nevertheless, little research has been conducted in this area. Current research on the use of blockchain technology in auditing focuses mostly on the auditing of financial transactions and the use of BCT to optimize the auditing process. We were unable to locate any research evaluating the usage of BCT in software audits. To address this deficiency, we suggested the SSFTA blockchain-enabled framework to investigate the function of BCT in software audits. A case study was conducted to assess the usability, security, and structure of SSFTA. The questionnaire was created to collect experts’ opinions on SSFTA, and the findings indicate that the proposed framework provides an end-to-end simple, secure, and transparent software auditing procedure.
In the future, we are planning to perform a survey with diverse and vast software experts to better evaluate the applicability of the proposed framework.