1. Introduction
Nowadays, in an online environment where tons of personal data are shared and instantaneously stored in servers or clouds that are distributed all over the globe, it is very difficult for people to maintain control over sensitive information when necessary. Here, we refer to different types of information, such as emails, photos, videos, and audio that are an essential part of our lives. If we cannot control or take care of our data, they can be accessed, stolen, altered, or copied by alien entities in seconds, without our consent.
Thus, data protection has become important to every member of society. Large companies have been caught up in the conflict due to server data leakages that exposes all of a user’s stored information. Even though information is processed and protected in many ways in order to prevent attacks and protect digital assets from being compromised, these processes are often inadequate in keeping them secure. This reality poses an enormous challenge both for privacy and cybersecurity. This is where data encryption comes in.
Encryption helps to protect information by turning readable data into unreadable results. Nowadays, the most popular globally used applications are based on sharing and storing images online. Image encryption has become one of the most critical tools in today’s cyberworld. A digital image is characterized by intrinsic features such as bulk data, high pixel correlation, and redundancy. Therefore, image encryption is an extremely important technology to ensure the security of sensitive information. Different image encryption schemes are outlined in this paper, such as optical transformation [
1,
2,
3,
4], cellular automata [
5,
6,
7], DNA coding [
8,
9,
10,
11,
12], data encryption standard (DES) [
13,
14,
15], advanced encryption standard (AES) [
16,
17,
18,
19,
20], and Blowfish [
21]. However, the last three were mainly designed for textual information rather than digital image information.
In 1989, the British mathematician Matthews introduced the first chaos-based encryption algorithm, where a logistic map was used as a key generator [
22]. In fact, chaotic behaviors can be determined by nonlinear dynamic systems, where any tiny initial deviation will be exponentially amplified. Intrinsic properties of chaotic systems, such as ergodicity, sensitive dependence on initial conditions, random like behavior, and the mixing effect, lead to a natural relationship and structural similarity between chaos and cryptography. This is an important milestone for chaos-based encryption technology.
Later, in 1998, Fridrich introduced the first general architecture for a chaos-based image cipher [
23] consisting of permutation and diffusion. In the first stage, pixels were permutated by a two-dimensional area-preserving chaotic map. Then, pixel values were modified using a discretized chaotic map in the diffusion procedure. This architecture became the most popular structure and has been adopted in many chaos-based image encryption algorithms. For instance, Chen et al. [
24] used a 3D Arnold’s cat map for substitution and employed Chen’s chaotic system for the diffusion process. In [
25], an image encryption algorithm with a permutation–diffusion structure was introduced and a tent map used to shuffle the positions of image pixels, and delayed coupled map lattices (DCML) were then employed to confuse the relationship between the plain and cipher image.
Some researchers improved the two-stage structure, presenting a one-stage structure. Wang et al. [
26] proposed an image encryption algorithm that combined the permutation and diffusion stages into one stage, where the plain image was divided into blocks that could be permutated as a unit, and another algorithm that could simultaneously perform confusion and diffusion was proposed in [
27], but the pixel of the image was the unit in confusion. In addition, a three-stage image encryption structure was developed and introduced; Seyedzadeh et al. [
28] used a quantum logistic map to diffuse the relationship of pixels, employed a two-dimensional logistic map to modify the values of diffused pixels, and exploited random circular shift operation to rearrange the bits of each encrypted pixel. Zhu et al. [
29] introduced an improved permutation–diffusion architecture, which included three stages: plain pixel-related swapping confusion, diffusion, and plain pixel-related swapping confusion.
However, a ciphertext or cipher image can easily be deciphered by chosen plaintext and ciphertext attacks [
30,
31,
32] if the permutation operation just changes the position of the pixel in the permutation stage, and the pseudorandom sequence generated by the chaotic system is independent of the plaintext and diffusion process. To avoid attackers cracking cryptosystems by using an order from top to bottom and from left to right, a variety of image encryption algorithms using bit-level permutation have been proposed. Xu et al. [
33] proposed a novel bit-level image encryption algorithm via chaotic maps, such as a technique that uses piecewise linear chaotic maps (PWLCM) and bit-level permutations to achieve this goal. In [
34], Zhu et al. proposed a bit-level permutation scheme for image encryption that is based on both Arnold’s cat and logistic maps. In [
35], a new bit-level encryption algorithm was developed based on spatiotemporal nonadjacent coupled map lattices that made it possible for any bit in pixels to break the limit of its bit plane without extra space in the permutation process. The permutation process at the bit level is actually able to simultaneously change the positions and gray values of pixels for high-resolution images; however, this requires more computational resources which naturally increases the iterative times of chaotic systems.
On the other hand, low-dimensional chaotic maps, such as the logistic map, are easy to use and require fewer computational resources. For high security considerations, low-dimensional chaotic systems are rarely applied for ciphering confidential images with high security requirements. In addition, some general methods can decipher these images, such as phase-space reconstruction or nonlinear prediction, but it is difficult to decipher images with high-dimensional chaotic systems. High-dimensional chaotic systems, especially hyperchaotic systems, have a larger key space, better sensitivity, more complex dynamic characteristics, and randomness. Consequently, a hyperchaotic system is especially appropriate for data protection with high security considerations [
36,
37,
38,
39,
40]. In 2008, Gao and Chen [
36] proposed a hyperchaos-based image encryption algorithm using pixel-level permutation; although this algorithm has the advantage of a large key space, Ruouma and Belghith [
37] demonstrated that it could not resist chosen plaintext and ciphertext attacks due to the permutation process being at the pixel level. Further, hyperchaos-based image encryption algorithms with DNA encoding and genetic recombination were separately presented by Zhang et al. [
38] in 2013, and Wang and Zhang [
39] in 2016. Similarly, complex permutation and ciphering processes demand much greater consumption of computational resource in order to satisfy high security requirements.
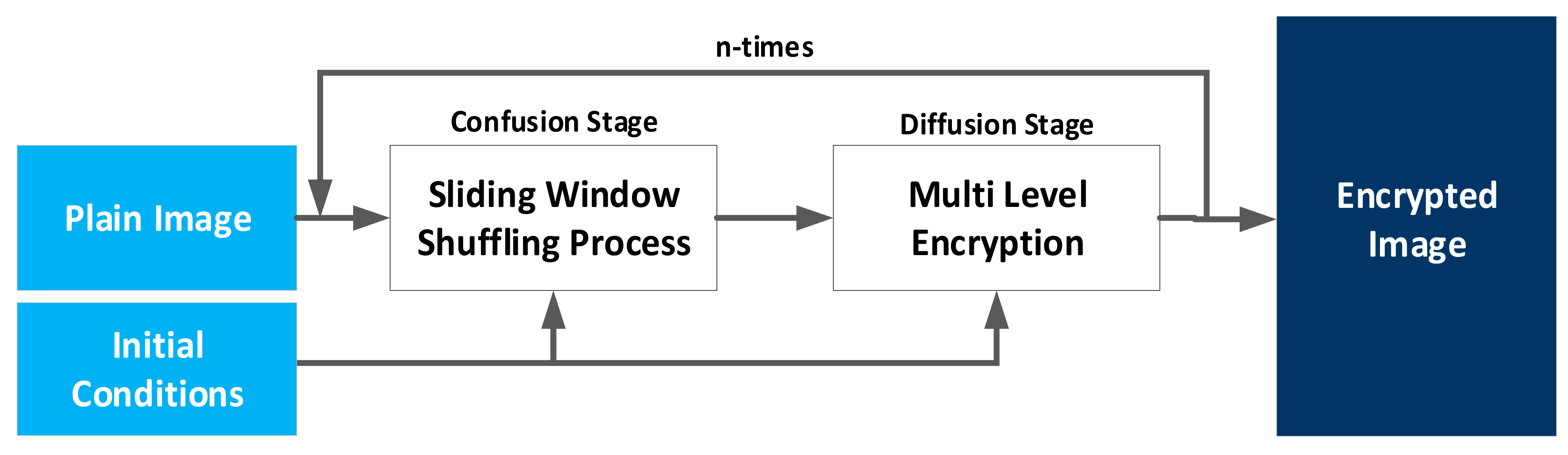
According to research achievements and valuable experiences from the works listed in this paper, a cloud image data protection algorithm with a multilevel encryption scheme and automated-selection mechanism was developed. The proposed algorithm was designed to work with all image types regardless of their features. The automated-selection mechanism commonly used nowadays, which is a simple sliding window, improves the efficiency when the cryptosystem is used to cipher big images and other types of images not considered by other mechanisms, such as 4K and HD images.
Furthermore, a bit-level permutation process in the confusion stage and a hyperchaos-based ciphering and hierarchical encryption process in the diffusion stage make the current system even more secure. The initial conditions for the confusion and diffusion stages are defined at the beginning of the process. This is to produce large chaos trajectories that eventually become pseudorandom values after the correct iteration of hyperchaotic systems and several chaotic maps. A subsection of the image is chosen by an appropriate automated-selection mechanism to start the encryption process. Then, the process shuffles the image at the bit level via a logistic map in the confusion stage, which not only relocates the bits within the selected subimage, but also changes the pixel values, increasing the permutation efficiency.
Finally, through a combination of two hyperchaotic systems and a second logistic map, the diffusion stage becomes a multilevel encryption scheme that makes patterns much harder to identify, and vastly increases the amount of data needed to analyze in order to break the cipher image. Therefore, the system is highly secure and beneficial to many companies looking for a fast, safe, and efficient way to cipher their images, especially those which are high-resolution.
The rest of this paper is organized as follows. In
Section 2, the interactive encryption algorithm is described step by step. Simulation results and security analysis are discussed in
Section 3, and in
Section 4, the conclusions are summarized.