1. Introduction
Since the birth of medical imaging technology, medical images that, in the auxiliary diagnosis of the industry, play an increasingly important role in making accurate diagnoses for doctors, include computed tomography (CT) images, X-ray images, ultrasound images, magnetic resonance imaging (MRI) images, electrocardiograms, electroencephalograms, angiography images, radionuclide images etc. generated by medical imaging systems [
1]. Especially in recent years, due to the rapid development of life sciences, materials science, robotics engineering and information science, doctors can use imaging systems that already have microscopic resolution to directly generate medical images, and can even operate nanorobots deep inside patients’ bodies to perform molecular-level real-time diagnoses and cancer targeted therapy, according to the micro-camera on the robot and the images returned by various sensors. At present, many hospitals have developed their own smart medical platforms [
1,
2]. These platforms facilitate patients’ access to electronic medical records and medical images. Some rare and precious medical images stored on such systems also provide valuable technical exchanges and case sharing between doctors and peers. For the convenience of diagnoses, doctors usually embed the personal information of the patient directly in the medical images, which brings many safety hazards for the storage and transmission of medical images. Patients’ private information may be leaked or subject to malicious attacks. The use of medical image watermarking (MIW) technology can effectively solve this problem [
3,
4].
Digital watermarking was first proposed to protect the copyright of digital multimedia on the Internet. Now we can hide the personal information of patients in the corresponding medical images according to their characteristics so as to protect the privacy of patients, avoid tampering with patients’ data, and make sure that such material is transmitted safely on the Internet. But for medical images, unique characteristics must also be taken into account. Such images are an important means for doctors to obtain pathology information about patients. In the medical field, the quality requirements for patients’ pathology medical data are extremely strict, and no changes are allowed [
5]. Anything that may affect medical pathology data is not advisable. Hence, study of medical image digital watermarking is particularly important [
6].
Kutter et al. proposed the second-generation watermark algorithm in 1999, which applied image features to watermark embedding and extraction, and gave rise to zero-watermark technology. In recent years, numerous medical watermarking algorithms have been developed. Scholars and experts in various countries have done lots of research on the digital watermarking of medical images. These research algorithms are divided into three categories, each of which will now be summarized. (1) Those based on Region of Non-Interest (RONI); Rahman et al. [
7] designed a hybrid watermark using bose, ray, hocquenghem (BCH) coding, chaos theory and RRNS in spatial domain, and the RONI was used to embed watermark information; Abokhdair et al. [
8] first divided the host medical image, then hid the patient data and the hash values in a Region of Interest (ROI), hid the tamper recovery data and the hash values of tamper detection in RONI. Each embeddable ROI pixel can hide one or two bits to reduce ROI distortion; Parah et al. [
9] proposed two different algorithms. By modifying the threshold value, the transform domain coefficient of 8x8 is compared with the size of watermark and Electronic Patients Record (EPR). One algorithm embeds both watermark and EPR into ROI and RONI, and the other keeps the ROI unchanged and hides the watermark and EPR in RONI; Thanki et al. [
10], using a human visual system (HVS) model to identify the RONI of the cover medical image, explicitly inserted the watermark into the RONI of the cover medical image to obtain a watermarked medical image; Zhang et al. [
11], using Laplacian and a horizontal set segmented the medical images into ROI and RONI, whereby the watermark information was embedded into a RONI based on Contourlet transformation and singular value decomposition (SVD); Taher et al. [
12] proposed a blind hybrid watermark algorithm for MRI images, which used a histogram to divide the image into ROI and RONI, and embedded the watermark into the RONI’s spatial and wavelet domains; Maedeh Jamali et al. [
13] looked for RONI using saliency to find the smallest overlap with the ROI. When embedding, discrete wavelet transform and discrete cosine transformation (DWT-DCT) is used with redundant watermarks. When extracting, a vote is used. (2) The second category is based on reversible watermarking. Arsalan et al. [
14] proposed a new technique named ‘IRW-Med’, using the concept of a compression function to reduce the embedding distortion, and the integer wavelet transform (IWT) as an embedded domain to realize the reversibility of the watermark; Kelkar et al. [
15] introduced two innovative reversible algorithms, which were both based on a histogram shift to improve the hidden capacity, and to divide the image into non-overlapping blocks to embed the watermark; Turuk et al. [
16] proposed a reversible watermarking scheme using quantization functions embedded in multiple watermarks and a novel tracking key to restore original medical images; Lei et al. [
17] inserted data and signature information into the original medical image via a recursive modulation algorithm after wavelet transform and singular value decomposition. In this method, the watermark strength is controlled by differential evolution. (3) The final category is based on classical conventional digital watermarking. In the literature [
18,
19,
20,
21,
22], an algorithm of multiple watermarks for medical images is implemented. As Aditi Zear et al. [
18] used SVD, DCT, DWT respectively for different type of watermarks, and back propagation neural networks (BPNN) to eliminate the impact of noise when extracting watermarks; they also enhanced its security by using Arnold transform; Rohit Thanki et al. [
19] used fast discrete curvelet transform (FDCuT) for medical images to obtain the different frequency coefficients of the curve decomposition, and adopted DCT for high frequency coefficients. Then, the watermark is modified according to the medium frequency coefficient of a white gaussian noise (WGN) sequence image. During extraction, the same sequence of correlation is used to achieve blind recovery; Jinwei Wang et al. [
20] proposed a new kind of multi-watermark which is controlled by secret key. The proposed hybrid decoder is optimal and locally optimal. It follows multiple multiplication rules and is based on the minimum risk of bayes. Their DWT coefficients are modeled as generalized gaussian distributions; Xiaochen Yuan et al. [
21] proposed a local multi-watermark algorithm, which used the the robust and adaptive feature detector based on daisy descriptor (RAF3D) design adaptive detector to embed multiple watermarks into the orthogonal space of a feature extraction region at the same time. When extracting, the image can be extracted independently; Amit Kumar Singh et al. [
22] proposed a spread spectrum watermarking algorithm, which used a haar wavelet to perform the binary sub-band decomposition, and then embedded different forms of watermark information in the intermediate frequency and second order selected frequency bands of the first order DWT respectively, according to the different contexts in which it was used. The three categories are shown in
Figure 1.
For algorithms based on the first and third categories, the embedding of watermarks affects the images themselves, and these watermarking algorithms have poor anti-geometric attack capabilities; they cannot even resist the tiny geometric transformations [
9,
10,
22,
23,
24]. For medical images, the particularity is that the embedded watermark cannot affect the diagnosis of doctors, and cannot obviously change the main content of medical images, especially for the region of interest of the image. The second category uses reversible digital watermarks. Although the watermark image can be restored to the original image without loss, the watermark is not robust. Therefore, finding a feature vector that can resist geometric attacks in medical images so that the algorithm can show good robustness without changing the original image is a problem that has long puzzled researchers [
7,
8,
12,
13,
20,
21].
Consequently, this paper proposes a multi-watermark robust algorithm based on a dual-tree complex wavelet transform and discrete cosine transform (DTCWT-DCT) using perceptual hash and henon mapping. By selecting the low frequency coefficients of the medical images in the DTCWT-DCT transform domain and performing symbol transformation, the features of the medical image may be extracted. Then, using henon chaos and hash function properties, different initial values of the chaotic sequences and XOR operation are given to encrypt each watermark. Finally, based on common watermark technology, a set of secret keys are generated by combining the concepts of the “third party”, chaotic encryption and cryptography technology to complete the embedding and extraction of the multi-watermark.
The main contribution of the present research is:
(1) A new method is proposed to extract stable features of medical images according to human vision, which does not require any changes to the original images, and is highly resistant to geometric attacks.
(2) The encryption of watermarks uses a chaotic system and hash function properties, which are extremely sensitive to the initial value, to enhance the security of watermarks.
(3) The embedding of watermarks generates a set of secret keys that can be stored by a third party. The region of interest need not be selected, which can effectively protect the privacy of patients.
(4) The extraction of watermarks does not require the original image, i.e., zero watermark and blind extraction.
(5) It solves the problem that existing algorithms cannot simultaneously offer protection against geometric attacks and robustness. The proposed algorithm has good robustness and invisibility.
3. The Proposed Algorithm
The proposed algorithm is based on DTCWT-DCT and a henon map. It is a multi-watermark scheme for medical images, which meets the requirements of zero watermark and blind extraction. It has strong resistance to geometric attacks and displays good robustness. The algorithm consists of five parts: feature extraction of the medical image, preprocessing of multi-watermark, embedding of the multi-watermark, extraction of the multi-watermark and recovery of the multi-watermark. In the feature extraction stage, based on human visual features, a new feature sequence based on perceptual hashing was found in the DTCWT-DCT domain to participate in the watermark operation. In the design of the algorithm, common watermark technology is organically combined with henon chaotic encryption, cryptography and the third-party concept, which not only allows the digital watermark to resist conventional and geometric attacks, but also makes the algorithm strong and robust. Meanwhile, the use of multiple watermarks also enhances the security of medical image transmissions, which can better protect the privacy of patients.
Figure 6 shows the working principle of the proposed algorithm. First, DTCWT-DCT transform was performed on an original medical image for a vector
conforming to human visual features found in the transformation domain. And binarization was performed on multiple watermarks to obtain multiple corresponding watermarks
. Then, different initial values were taken for henon chaos to generate multiple different chaotic sequences
. For these chaotic sequences, the symbol operation was applied to obtain the binary encryption matrixes
, and the encrypted watermarks
are obtained using
and
,
. Next, logical operations are performed on
and
. According to the encrypted watermarks
and the visual feature vector
of the image, binary logic sequences
are generated through the Hash function. These binary logic sequences
can be stored in a third-party platform. When testing, the same method was performed to the test medical image to extract the visual feature vector
, and the watermarks
contained in the image were extracted by
and the
generated earlier. The chaotic sequences
and the encryption matrixes
were generated using the same henon initial value as the above method. Then, the restored watermarks
were obtained by hashing
and
.
A detailed algorithm description is shown in
Figure 6.
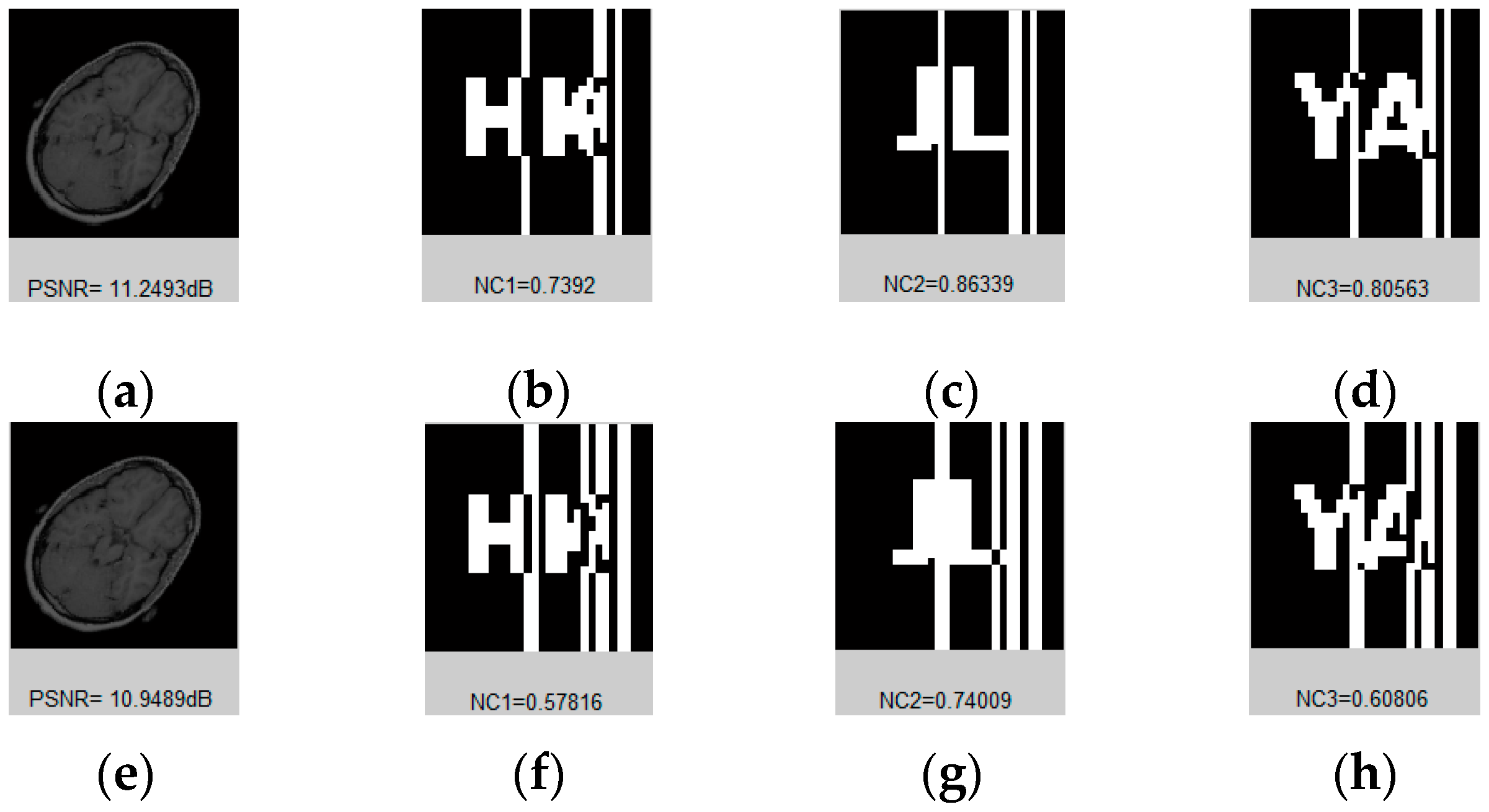
3.1. Feature extraction
In order to find a visual feature applicable to medical images, a normal human brain image (128 pixels × 128 pixels) was randomly selected to carry out the DTCWT-DCT transformation, and this image was subjected to a variety of different types of attacks, as shown in
Figure 7. By observing the coefficient data of the low-frequency part of the image after transformation, we found that although its numerical value changed significantly, its symbol remained basically the same.
Table 1 lists the low frequency coefficients of the brain image under different attacks. In this paper, we selected 32 bits of low-frequency data for symbol transformation, and directly replaced data greater than or equal to 0 with 1, and all other data with 0. For the sake of explanation, we only list the first 10 data in the table; all data were in 1.0e+003 units. In this way, we obtained a set of DTCWT-DCT low-frequency coefficient symbol sequences of the original image, i.e., ‘1100010010’. As seen from
Table 1, after transformation, the symbol sequences of all attacked images were consistent with the original image, and the NC values were all equal to 1.00.
Then, taking this conclusion as a reference, we conducted the same test on a large number of randomly selected medical images, and verified the value of the normalized correlation coefficient between the images using their respective 32-bit symbol vectors.
Figure 8 and
Table 2 show some of the medical images and the NC values between them. From the data, it can be concluded that the NC values of the different images obtained using the feature vector selected with the above method are all less than 0.5, and their own NC values are 1.00. These results are consistent with human visual features. Therefore, we can take the sequence of coefficient symbols in the low-frequency part of the medical image transformed by DTCWT-DCT as its effective visual feature vector, and correlate the watermarks with it to design the multi-watermarking algorithm.
3.2. Watermarks Pretreatment
Before embedding the watermark, henon chaos must be applied, and a preprocessing operation is carried out to obtain the watermark of chaotic encryption.
Figure 9 shows the steps of watermarks pretreatment.
Step 1: Choose the initial values to create chaotic sequences , and get binary encryption matrixes via symbolic operations. Instead the values of with ‘1’ if they are bigger than the average, and instead with ‘0’ if smaller.
Step 2: Obtain the encrypted watermarks by operating the binary watermarks and the binary encryption matrixes through the hash function.
3.3. Watermarks Embedding
3.4. Watermarks Extraction
3.5. Watermarks Restoration
Then, the ownership of the image to be tested and the patient’s personal information were determined according to the correlation degree of and .