Application Layer-Based Denial-of-Service Attacks Detection against IoT-CoAP
Abstract
:1. Introduction
- RQ1: Is it effective to secure CoAP in the application layer from DDoS attacks?
- RQ2: What are the CoAP-level features that can be dedicated to secure CoAP in its perimeter?
- RQ3: What is the best machine learning technique that can be performed well in detecting DDoS attacks against CoAP?
- 1-
- Extending and balancing the CIDAD dataset using GANs.
- 2-
- Focusing on the CoAP level features to ensure the security of CoAP in its vicinity.
- 3-
- Build a machine learning model that can classify the benign against malware with an accuracy of 98% using the decision tree algorithm.
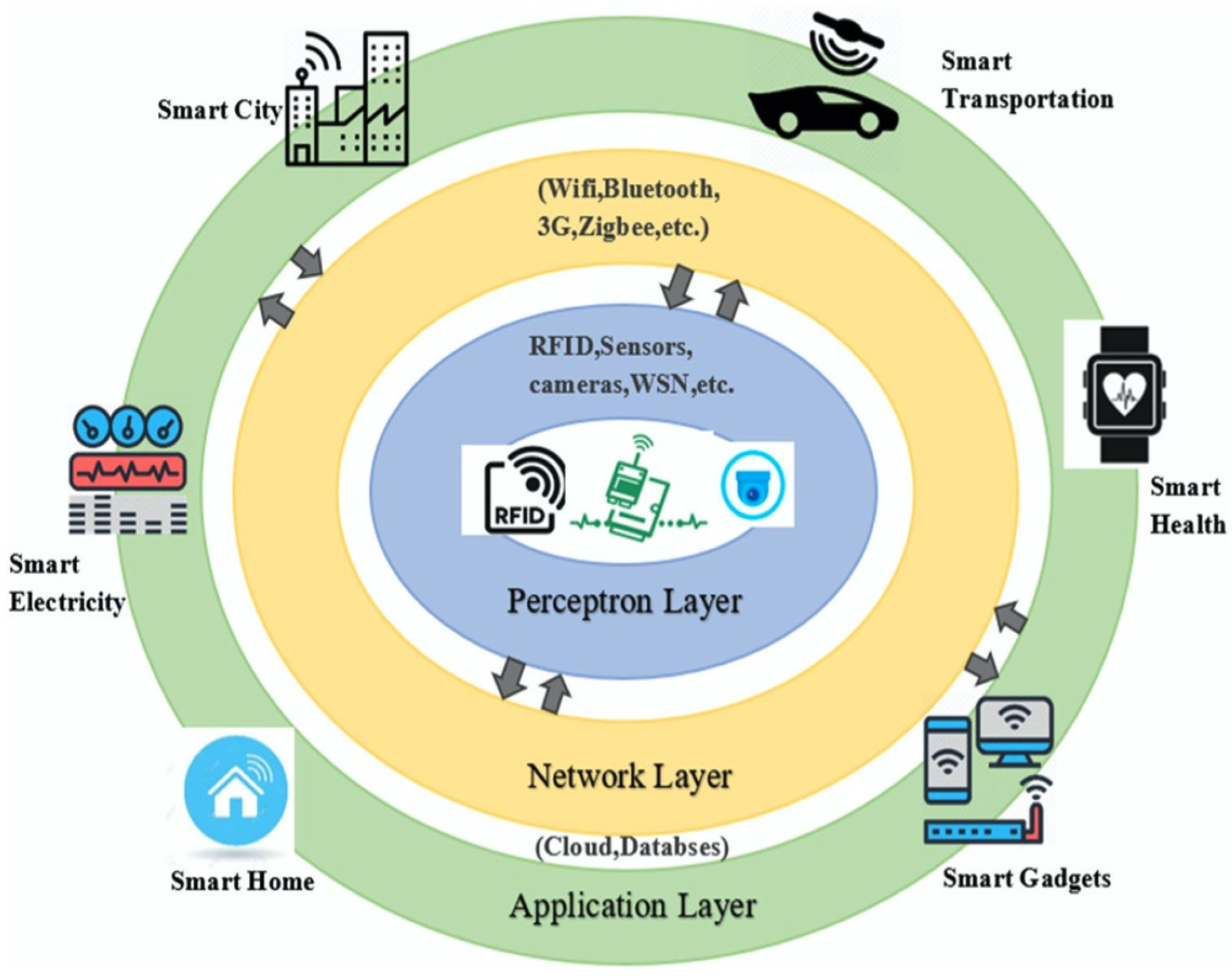
1.1. IoT Overview
1.1.1. IoT Protocols
- 1-
- IEEE 802.15.4 Protocol
- 2-
- The 6LoWPAN protocol
- 3-
- Routing—RPL protocol
- 4-
- CoAP Protocol
1.1.2. CoAP Architecture
Messaging Model
- 1-
- Confirmable Message (CON): In this mode, all messages are marked as confirmable messages (reliable mode). The message is resent using a default timeout until an ACK (acknowledgement) is received from the recipient with the same message ID as the sender. If the recipient fails to process the confirmable message, it will send an RST (reset) message rather than ACK to reset the communication. Figure 4 shows the confirmable mode between the client and the server.
- 2-
- Non-Confirmable Message (NON): If reliable delivery is not desired, the message can be sent as a non-confirmable message (unreliable mode). For duplication checking purposes, each message is assigned an ID even though its receival is not to be acknowledged. Figure 5 depicts the NON-message between the client and the server.
Request/Response Model
Message Format
- (1)
- Version (V): Unsigned integer (2-bit) that represents the CoAP version number. This field takes (01 binary), and other values are reserved for future versions. If the message comes with unknown version numbers, it must be ignored.
- (2)
- Type (T): Unsigned integer (2-bit) that represents 0 for Confirmable, 1 for Non-Confirmable, 2 for Acknowledgement, or 3 for reset as illustrated in the previous section.
- (3)
- Token Length (TKL): Unsigned integer (4-bit) with a length of 0 to 8 bytes. Length of 9–15 bytes is specialized for message format errors.
- (4)
- Code: Unsigned integer (8-bit) that is further divided into the most significant bits (3-bit) and the less significant bits (5-bit). It is represented as “c.dd” (“c” can be 0–7 as a digit for the 3-bit, and “dd” can be two digits in the range from 00 to 31 for the 5-bit). The most significant bits view 0 for a request, 2 for a successful response, 4 for a client error response, or 5 for a server error response. The other most significant bits are reserved. The code 0.00 represents an empty message as a special case.
- (5)
- Message ID: Unsigned integer (16-bit) used for duplicate vetting purposes. It is also used to match Acknowledgement/Reset messages to messages of type Confirmable or Non-Confirmable, respectively.
- (6)
- Token: It is used to correlate requests and responses and can range from 0 to 8 bytes, based on the length stated in the TKL field.
- (7)
- Options: The value can be 0 by another option or by the payload.
- (8)
- Payload: If it exists, it is prefixed by a (0xFF) marker as a benchmark for payload start. To calculate the length of the payload, it is counted from the end of the marker until the UDP datagram end.
Method Definitions
CoAP URIs
2. Related Technologies
2.1. DDoS Attacks in IoT
- A-
- Mirai
- B-
- Wirex
- C-
- Reaper
- D-
- Torri
2.2. CoAP Security Overview
- A-
- NoSec Mode: No security protocol is engaged (DTLS disabled). Alternatively, assuming that the lower-layer protocol will implement the security mechanism; therefore, the messages are transferred with no security.
- B-
- Pre-sharedKey Mode: DTLS is enabled. This mode has a list of pre-shared keys and there is a list of nodes that is assumed to engage in the communication for every key. For instance, in a significant scenario, every node has its key if it engages in CoAP communication. In contrast, if a specific pre-shared key is shared with two entities or more, the entities are authenticated as a group by that key and would no longer be considered as specific peers.
- C-
- RawPublicKey Mode: DTLS is enabled. This mode is used for device authentication. It provides each device with an asymmetric key that helps them in identifying and communicating with other devices without a certificate.
- D-
- Certificate Mode: DTLS is enabled. In this mode, the asymmetric key paired with an X.509 certificate is reserved for a given device. The certificate is validated by a CA (Certification Authority).
2.2.1. Proposed Defense Mechanisms for Securing CoAP against DDoS Attacks
DTLS for CoAP Security
SDN for CoAP Security
Machine Learning for CoAP Security
Other Methods for CoAP Security
3. Materials and Methods
3.1. Dataset Collection
3.2. Feature Extraction
3.3. Model Training
- 1-
- Environment Setup: In this step, we imported the data after cleaning and normalizing it, as previously discussed in Section 3.1 and Section 3.2.
- 2-
- Analyzing the data: We selected only the features that are relevant to the label by calculating the Lasso regression and ANOVA analysis, which resulted in the selection of only 6 features from a total of 86 CoAP message features.
- 3-
- Data Preprocessing: In this phase, we handled the missing values by calculating the average of the column, and then filled the missing values with the average. Some of the features contained large numbers in order to solve this issue and keep the model calculations simple. Additionally, we normalized these values using the max-min technique to retain the values between 0 and 1.
- 4-
- Model design: For each classifier, we ran the experiment and validated the performance for each model using the cross-validation technique to avoid overfitting and underfitting. We set up the fold to 5 and calculated the accuracy for each round, and then compared it to the model performance. Neither overfitting nor underfitting was observed in our experiment.
- 5-
- Evaluating the performance: The performance for each model was calculated in terms of accuracy, precision, recall, and F1-score. The following section elaborates on the results of the model performance in detail.
4. Results
4.1. LinearSVC
4.2. Random Forest
4.3. Decision Tree
4.4. Naïve Byes
5. Discussion
6. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Vishwakarma, R.; Jain, A.K. A survey of DDoS attacking techniques and defense mechanisms in the IoT network. Telecommun. Syst. 2020, 73, 3–25. [Google Scholar] [CrossRef]
- Syed, N.F. IoT-MQTT Based Denial of Service Attack Modeling and Detection. Ph.D. Thesis, Edith Cowan University, Joondalup, Australia, 2020. [Google Scholar]
- Hussain, F.; Abbas, S.G.; Husnain, M.; Fayyaz, U.U.; Shahzad, F.; Shah, G.A. IoT DoS and DDoS Attack Detection using ResNet. arXiv 2020, arXiv:2012.01971. [Google Scholar]
- Ragab, M.; Sabir, M.F.S. Outlier detection with optimal hybrid deep learning enabled intrusion detection system for ubiquitous and smart environment. Sustain. Energy Technol. Assess. 2022, 52, 102311. [Google Scholar] [CrossRef]
- Iglesias-Urkia, M.; Orive, A.; Urbieta, A.; Casado-Mansilla, D. Analysis of CoAP implementations for industrial Internet of Things: A survey. J. Ambient. Intell. Humaniz. Comput. 2018, 10, 2505–2518. [Google Scholar] [CrossRef]
- Alhaidari, F.A.; Alqahtani, E.J. Securing Communication between Fog Computing and IoT Using Constrained Application Protocol (CoAP): A Survey. J. Commun. 2020, 15, 14–30. [Google Scholar] [CrossRef]
- Bhardwaj, K.; Miranda, J.C.; Gavrilovska, A. Towards IoT-DDoS prevention using edge computing. In {USENIX} Workshop on Hot Topics in Edge Computing (HotEdge 18); USENIX: Berkeley, CA, USA, 2018. [Google Scholar]
- Shafiq, M.; Tian, Z.; Sun, Y.; Du, X.; Guizani, M. Selection of effective machine learning algorithm and bot-IoT attacks traffic identification for the internet of things in the smart city. Future Gener. Comput. Syst. 2020, 107, 433–442. [Google Scholar] [CrossRef]
- Vishwakarma, R.; Jain, A.K. A Honeypot with Machine Learning based Detection Framework for defending IoT based Botnet DDoS Attacks. In Proceedings of the 2019 3rd International Conference on Trends in Electronics and Informatics (ICOEI), Tirunelveli, India, 23–25 April 2019; pp. 1019–1024. [Google Scholar]
- Rahman, R.A.; Shah, B. Security analysis of IoT protocols: A focus in coap. In Proceedings of the 2016 3rd MEC International Conference on big Data and Smart City (ICBDSC), Muscat, Oman, 15–16 March 2016; pp. 1–7. [Google Scholar]
- Mohamadi, M.; Djamaa, B.; Senouci, M.R. Industrial internet of things over IEEE 802.15. 4 TSCH networks: Design and challenges. Int. J. Internet Technol. Secur. Trans. 2020, 10, 61–80. [Google Scholar] [CrossRef]
- Musaddiq, A.; Bin Zikria, Y.; Zulqarnain; Kim, S.W. Routing protocol for low-power and lossy networks for heterogeneous traffic network. EURASIP J. Wirel. Commun. Netw. 2020, 2020, 21. [Google Scholar] [CrossRef] [Green Version]
- Shelby, Z.; Hartke, K.; Bormann, C. The Constrained Application Protocol (CoAP) (No. rfc7252). 2014. Available online: https://www.rfc-editor.org/rfc/rfc7252 (accessed on 18 April 2023).
- Maleh, Y.; Ezzati, A.; Belaissaoui, M. An enhanced DTLS protocol for internet of things applications. In Proceedings of the 2016 International Conference on Wireless Networks and Mobile Communications (WINCOM), Fez, Morocco, 26–29 October 2016; pp. 168–173. [Google Scholar]
- Munshi, A.; Alqarni, N.A.; Almalki, N.A. DDoS attack on IoT devices. In Proceedings of the 2020 3rd International Conference on Computer Applications & Information Security (ICCAIS), Riyadh, Saudi Arabia, 19–21 March 2020; pp. 1–5. [Google Scholar]
- Saveetha, D.; Maragatham, G. Design of Blockchain enabled intrusion detection model for detecting security attacks using deep learning. Pattern Recognit. Lett. 2021, 153, 24–28. [Google Scholar] [CrossRef]
- Katib, I.; Ragab, M. Blockchain-Assisted Hybrid Harris Hawks Optimization Based Deep DDoS Attack Detection in the IoT Environment. Mathematics 2023, 11, 1887. [Google Scholar] [CrossRef]
- Haroon, A.; Akram, S.; Shah, M.A.; Wahid, A. E-lithe: A lightweight secure DTLS for IoT. In Proceedings of the 2017 IEEE 86th Vehicular Technology Conference (VTC-Fall), Toronto, ON, Canada, 24–27 September 2017; pp. 1–5. [Google Scholar]
- Kajwadkar, S.; Jain, V.K. A Novel Algorithm for DoS and DDoS attack detection in Internet of Things. In Proceedings of the 2018 Conference on Information and Communication Technology (CICT), Jabalpur, India, 26–28 October 2018; pp. 1–4. [Google Scholar]
- Alzahrani, B.; Fotiou, N. Enhancing Internet of Things Security using Software-Defined Networking. J. Syst. Arch. 2020, 110, 101779. [Google Scholar] [CrossRef]
- Granjal, J.; Pedroso, A. An Intrusion Detection and Prevention Framework for Internet-Integrated CoAP WSN. Secur. Commun. Netw. 2018, 2018, 1753897. [Google Scholar] [CrossRef] [Green Version]
- Granjal, J.; Silva, J.M.; Lourenço, N. Intrusion detection and prevention in coap wireless sensor networks using anomaly detection. Sensors 2018, 18, 2445. [Google Scholar] [CrossRef] [PubMed] [Green Version]
- Doshi, R.; Apthorpe, N.; Feamster, N. Machine Learning DDoS Detection for Consumer Internet of Things Devices. In Proceedings of the 2018 IEEE Security and Privacy Workshops (SPW), San Francisco, CA, USA, 24 May 2018; pp. 29–35. [Google Scholar]
- Anirudh, M.; Thileeban, S.A.; Nallathambi, D.J. Use of honeypots for mitigating DoS attacks targeted on IoT networks. In Proceedings of the 2017 International Conference on Computer, Communication and Signal Processing (ICCCSP), Chennai, India, 10–11 January 2017; pp. 1–4. [Google Scholar]
- Vigoya, L.; Fernandez, D.; Carneiro, V.; Cacheda, F. (8135, January 01). Cidad.pcap · Dad-Repository/CIDAD@A109B87. Available online: https://github.com/dad-repository/cidad/commit/a109b8706174af5d6b1cb06f6afac5fe0ce2b28e (accessed on 14 April 2023).
- Kahng, M.; Thorat, N.; Chau, D.H.P.; Viegas, F.B.; Wattenberg, M. GAN Lab: Understanding Complex Deep Generative Models using Interactive Visual Experimentation. IEEE Trans. Vis. Comput. Graph. 2018, 25, 310–320. [Google Scholar] [CrossRef] [PubMed] [Green Version]



























| Version (V) | Type (T) | Token Length (TKL) | Code | Message ID |
|---|---|---|---|---|
| Token (if any) | ||||
| Options (if any) | ||||
| Payload (if any) | ||||
| Research Objective | Methodology Used | Results | Limitation |
|---|---|---|---|
| Detect and mitigate DDoS attack against CoAP (2016) | DTLS handshake is extended with a cookie exchange technique to check the authentication of a message. | Low computation time by delegating all handshake to a third party. | The assumption of third party (Proxy AC server) is trustworthy all the time. |
| Secure DTLS for IoT (2017) | Trusted Third Party (TTP) is used to avoid DDoS attack and reduce overhead on the server side. | Energy consumption, reduced packet size, and reduced running time outperforms similar works. | DTLS is computationally heavy for IoT devices. |
| Deploy a honeypot to detect DDoS attack (2017) | Deploy a honeypot with two phases, first to log the anomalies and second to verify or block the client. | Sixty percent efficiency when a honeypot is implemented. | Anomaly-based detection may result in high false-positive rate. |
| Detect DDoS against IoT (2018) | Compare the payload of benign and malicious packet, define a threshold and if exceeded, the source IP is blocked. | Evaluate malicious packet delivery ratio and legitimate packet drop ratio. | Focuses on packet payload feature only. |
| Prevention framework from intrusion and DDoS attack (2018) | Relies on threshold by limiting the incoming request to a fixed number and if exceeded, the source request is blocked. | Fair energy and memory consumption when running the proposed system. | Susceptible to spoofing attack. |
| Protect 6LoWPAN and CoAP from DDoS attack (2018) | Employ anomaly-based detection system to protect CoAP from DDoS attack. | SVM classifies the anomalies with accuracy of 93%. | High false-positive rate of 20%. |
| Detect IoT DDoS attack (2018) | Machine learning DDoS detection framework. | RF, KNN, Neural Networks gain approximately 99% accuracy. | Some IoT devices have different regular patterns but not distinct patterns. |
| Defend IoT against DDoS while maintaining benign traffic (2018) | Leverage the fast retransmit and flow control mechanism of TCP to retransmit benign packets at fastest rate and malicious packet at harmless rate. | Compared to D-WARD, FR-WARD performs better in retransmission, duration, and energy consumption. | Susceptible to other kinds of attacks. |
| Test CoAP MITM attack which results in spoofing, sniffing, and DDoS attack (2019) | Set up a client/server architecture to check whether the communication between the two devices using CoAP is secure. | Burp suite tool is used to intercept the communication between the client and the server. | Susceptible to sniffing attack. |
| Securing CoAP messages (2020) | SDN-based approach is developed to authorize the messages of CoAP. | Decrease overhead to the controller and CoAP responses become faster. | N/A |
| Design blockchain enabled IDS with deep learning (2022) | (IDS)-based deep learning integrated with blockchain to detect abnormal behavior in big networks. | The proposed model outperforms the conventional system in terms of accuracy. | N/A |
| Blockchain-Assisted Hybrid Harris Hawks Optimization-Based Deep DDoS Attack Detection in the IoT Environment (2023) | Hybrid Harris Hawks with sine cosine and a deep learning-based intrusion detection system to detect DDoS attacks against IoT network. | Obtain accuracy of 99.05% with BoT-IoT dataset. | N/A |
| Field Name | Description | Type | Versions |
|---|---|---|---|
| coap.block | Block | Frame number | 3.4.0 to 4.0.5 |
| coap.block.count | Block count | Unsigned integer (32 bits) | 3.4.0 to 4.0.5 |
| coap.block.error | Block defragmentation error | Frame number | 3.4.0 to 4.0.5 |
| coap.block.multiple_tails | Block has multiple tails | Boolean | 3.4.0 to 4.0.5 |
| coap.block.overlap | Block overlap | Boolean | 3.4.0 to 4.0.5 |
| coap.block.overlap.conflicts | Block overlapping with conflicting data | Boolean | 3.4.0 to 4.0.5 |
| coap.block.reassembled.in | Reassembled in | Frame number | 3.4.0 to 4.0.5 |
| coap.block.reassembled.length | Reassembled block length | Unsigned integer (32 bits) | 3.4.0 to 4.0.5 |
| coap.block.too_long | Block too long | Boolean | 3.4.0 to 4.0.5 |
| coap.block_length | Block Length | Unsigned integer (32 bits) | 3.4.0 to 4.0.5 |
| coap.block_payload | Block Payload | Byte sequence | 3.4.0 to 4.0.5 |
| coap.blocks | Blocks | Label | 3.4.0 to 4.0.5 |
| coap.code | Code | Unsigned integer (8 bits) | 1.6.0 to 4.0.5 |
| coap.invalid_option_number | Invalid Option Number | Label | 1.12.0 to 4.0.5 |
| coap.invalid_option_range | Invalid Option Range | Label | 1.12.0 to 4.0.5 |
| coap.length | Length | Unsigned integer (32 bits) | 3.2.0 to 4.0.5 |
| coap.mid | Message ID | Unsigned integer (16 bits) | 1.12.0 to 4.0.5 |
| coap.ocount | Opt Count | Unsigned integer (8 bits) | 1.10.0 to 1.10.14 |
| coap.opt.accept | Accept | Character string | 1.8.0 to 4.0.5 |
| coap.opt.block_mflag | More Flag | Unsigned integer (8 bits) | 1.6.0 to 4.0.5 |
| coap.opt.block_number | Block Number | Unsigned integer (32 bits) | 1.6.0 to 4.0.5 |
| coap.opt.block_size | Encoded Block Size | Unsigned integer (8 bits) | 1.6.0 to 4.0.5 |
| coap.opt.ctype | Content-type | Character string | 1.6.0 to 4.0.5 |
| coap.opt.delta | Opt Delta | Unsigned integer (8 bits) | 1.6.0 to 4.0.5 |
| coap.opt.delta_ext | Opt Delta extended | Unsigned integer (16 bits) | 1.12.0 to 4.0.5 |
| coap.opt.desc | Opt Desc | Character string | 1.10.0 to 4.0.5 |
| coap.opt.end_marker | End of options marker | Unsigned integer (8 bits) | 1.12.0 to 4.0.5 |
| coap.opt.etag | Etag | Byte sequence | 1.6.0 to 4.0.5 |
| coap.opt.hop_limit | Hop Limit | Unsigned integer (8 bits) | 3.4.0 to 4.0.5 |
| coap.opt.if_match | If-Match | Byte sequence | 1.8.0 to 4.0.5 |
| coap.opt.if_none_match | If-None-Match | Byte sequence | 1.8.0 to 1.8.15 |
| coap.opt.jump | Opt Jump | Unsigned integer (8 bits) | 1.10.0 to 1.10.14 |
| coap.opt.length | Opt Length | Unsigned integer (8 bits) | 1.6.0 to 4.0.5 |
| coap.opt.length_ext | Opt Length extended | Unsigned integer (16 bits) | 1.12.0 to 4.0.5 |
| coap.opt.location | Location | Character string | 1.6.0 to 1.6.16 |
| coap.opt.location_path | Location-Path | Character string | 1.8.0 to 4.0.5 |
| coap.opt.location_query | Location-Query | Character string | 1.8.0 to 4.0.5 |
| coap.opt.max_age | Max-age | Unsigned integer (32 bits) | 1.6.0 to 4.0.5 |
| coap.opt.name | Opt Name | Character string | 1.10.0 to 4.0.5 |
| coap.opt.object_security_expand | Expanded Flag Byte | Boolean | 2.6.0 to 3.2.18 |
| coap.opt.object_security_kid | Key ID | Byte sequence | 2.6.0 to 4.0.5 |
| coap.opt.object_security_kid_context | Key ID Context | Byte sequence | 2.6.0 to 4.0.5 |
| coap.opt.object_security_kid_context_len | Key ID Context Length | Unsigned integer (8 bits) | 2.6.0 to 4.0.5 |
| coap.opt.object_security_kid_context_present | Key ID Context Present | Boolean | 2.6.0 to 4.0.5 |
| coap.opt.object_security_kid_present | Key ID Present | Boolean | 3.0.0 to 4.0.5 |
| coap.opt.object_security_non_compressed | Non-compressed COSE message | Boolean | 2.6.0 to 3.2.18 |
| coap.opt.object_security_piv | Partial IV | Byte sequence | 2.6.0 to 4.0.5 |
| coap.opt.object_security_piv_len | Partial IV Length | Unsigned integer (8 bits) | 2.6.0 to 4.0.5 |
| coap.opt.object_security_reserved | Reserved | Boolean | 3.4.0 to 4.0.5 |
| coap.opt.object_security_signature | Signature Present | Boolean | 2.6.0 to 3.2.18 |
| coap.opt.observe | Observe | Unsigned integer (32 bits) | 2.0.0 to 4.0.5 |
| coap.opt.payload_desc | Payload Desc | Character string | 1.10.0 to 2.2.17 |
| coap.opt.proxy_scheme | Proxy-Scheme | Character string | 2.0.0 to 4.0.5 |
| coap.opt.proxy_uri | Proxy-Uri | Character string | 1.8.0 to 4.0.5 |
| coap.opt.size1 | Size1 | Unsigned integer (32 bits) | 2.0.0 to 4.0.5 |
| coap.opt.subscr_lifetime | Lifetime | Unsigned integer (32 bits) | 1.6.0 to 1.12.13 |
| coap.opt.token | Token | Character string | 1.6.0 to 1.10.14 |
| coap.opt.unknown | Unknown | Byte sequence | 1.10.0 to 4.0.5 |
| coap.opt.uri_auth | Uri-Authority | Character string | 1.6.0 to 1.6.16 |
| coap.opt.uri_host | Uri-Host | Character string | 1.8.0 to 4.0.5 |
| coap.opt.uri_path | Uri-Path | Character string | 1.6.0 to 4.0.5 |
| coap.opt.uri_path_recon | Uri-Path | Character string | 2.4.0 to 4.0.5 |
| coap.opt.uri_port | Uri-Port | Unsigned integer (16 bits) | 1.8.0 to 4.0.5 |
| coap.opt.uri_query | Uri-Query | Character string | 1.6.0 to 4.0.5 |
| coap.optcount | Option Count | Unsigned integer (8 bits) | 1.6.0 to 1.8.15 |
| coap.option_length_bad | Option length bad | Label | 1.12.0 to 4.0.5 |
| coap.option_object_security_bad | Invalid Object-Security Option Format | Label | 2.6.0 to 3.2.2 |
| coap.option_oscore_bad | Invalid OSCORE Option Format | Label | 3.2.3 to 4.0.5 |
| coap.oscore_kid | OSCORE Key ID | Byte sequence | 2.6.0 to 4.0.5 |
| coap.oscore_kid_context | OSCORE Key ID Context | Byte sequence | 2.6.0 to 4.0.5 |
| coap.oscore_piv | OSCORE Partial IV | Byte sequence | 2.6.0 to 4.0.5 |
| coap.payload | Payload | Character string | 1.12.0 to 4.0.5 |
| coap.payload_desc | Payload Desc | Character string | 2.4.0 to 4.0.5 |
| coap.payload_length | Payload Length | Unsigned integer (32 bits) | 2.4.0 to 4.0.5 |
| coap.request_first_in | Retransmission of request in | Frame number | 3.2.0 to 4.0.5 |
| coap.response_first_in | Retransmission of response in | Frame number | 3.2.0 to 4.0.5 |
| coap.response_in | Response In | Frame number | 2.2.0 to 4.0.5 |
| coap.response_time | Response Time | Time offset | 2.2.0 to 4.0.5 |
| coap.response_to | Request In | Frame number | 2.2.0 to 4.0.5 |
| coap.retransmitted | Retransmitted | Label | 3.2.0 to 4.0.5 |
| coap.tid | Transaction ID | Unsigned integer (16 bits) | 1.6.0 to 1.10.14 |
| coap.token | Token | Byte sequence | 1.12.0 to 4.0.5 |
| coap.token_len | Token Length | Unsigned integer (8 bits) | 1.12.0 to 4.0.5 |
| coap.type | Type | Unsigned integer (8 bits) | 1.6.0 to 4.0.5 |
| coap.unknown_option_number | Unknown Option Number | Label | 3.2.5 to 4.0.5 |
| coap.version | Version | Unsigned integer (8 bits) | 1.6.0 to 4.0.5 |
| Feature | Description | Type |
|---|---|---|
| coap.mid | Message ID | Unsigned integer (2 bytes) |
| coap.opt.desc | Opt Desc | Character string |
| coap.opt.location_query | Location-Query | Character string |
| coap.opt.uri_host | Uri-Host | Character string |
| coap.retransmitted | Retransmitted | Label |
| coap.code | Code | Unsigned integer (1 byte) |
| Fold No. | Fold 1 | Fold 2 | Fold 3 | Fold 4 | Fold 5 | Model Accuracy |
|---|---|---|---|---|---|---|
| Performance | 0.654 | 0.651 | 0.653 | 0.653 | 0.645 | 0.655 |
| Fold No. | Fold 1 | Fold 2 | Fold 3 | Fold 4 | Fold 5 | Model Accuracy |
|---|---|---|---|---|---|---|
| Performance | 0.924 | 0.924 | 0.925 | 0.923 | 0.923 | 0.92 |
| Fold No. | Fold 1 | Fold 2 | Fold 3 | Fold 4 | Fold 5 | Model Accuracy |
|---|---|---|---|---|---|---|
| Performance | 0.985 | 0.985 | 0.985 | 0.984 | 0.987 | 0.987 |
| Fold No. | Fold 1 | Fold 2 | Fold 3 | Fold 4 | Fold 5 | Model Accuracy |
|---|---|---|---|---|---|---|
| Performance | 0.702 | 0.706 | 0.707 | 0.707 | 0.710 | 0.70 |
| Model | Accuracy | Precision | Recall | F1-Score |
|---|---|---|---|---|
| LinearSVC | 59% | 62% | 48% | 54% |
| Decision Tree | 98% | 98% | 98% | 98% |
| Random Forest | 92% | 90% | 96% | 93% |
| Naïve Byes | 63% | 62% | 69% | 65% |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Almeghlef, S.M.; AL-Ghamdi, A.A.-M.; Ramzan, M.S.; Ragab, M. Application Layer-Based Denial-of-Service Attacks Detection against IoT-CoAP. Electronics 2023, 12, 2563. https://doi.org/10.3390/electronics12122563
Almeghlef SM, AL-Ghamdi AA-M, Ramzan MS, Ragab M. Application Layer-Based Denial-of-Service Attacks Detection against IoT-CoAP. Electronics. 2023; 12(12):2563. https://doi.org/10.3390/electronics12122563
Chicago/Turabian StyleAlmeghlef, Sultan M., Abdullah AL-Malaise AL-Ghamdi, Muhammad Sher Ramzan, and Mahmoud Ragab. 2023. "Application Layer-Based Denial-of-Service Attacks Detection against IoT-CoAP" Electronics 12, no. 12: 2563. https://doi.org/10.3390/electronics12122563









