Design of Low Probability Detection Signal with Application to Physical Layer Security
Abstract
1. Introduction
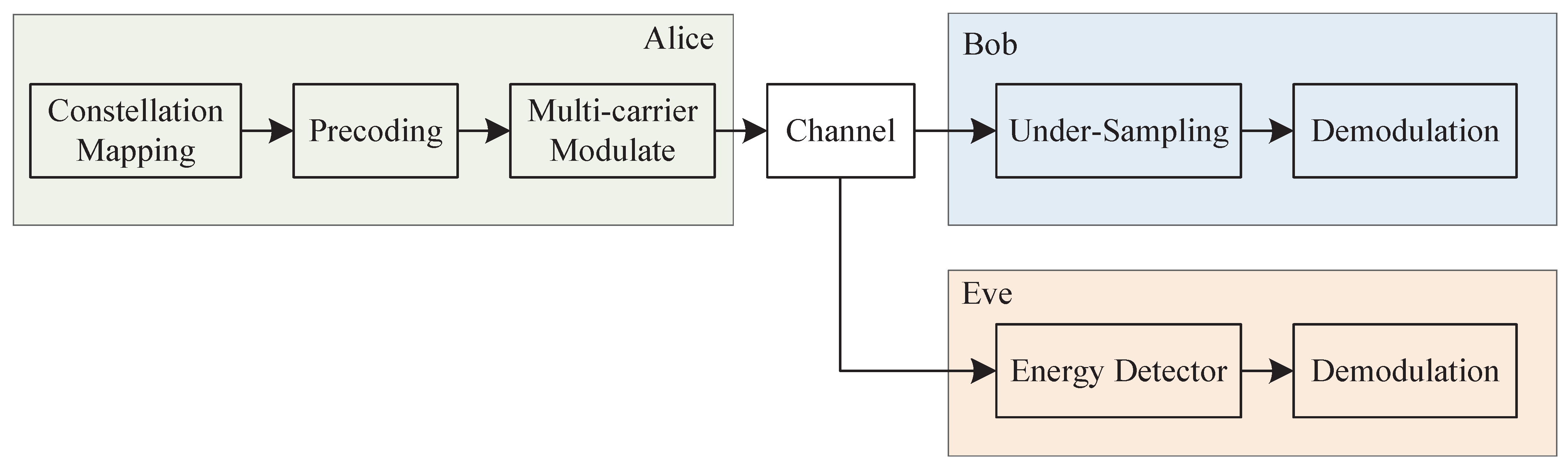
2. LPD Signal Design and Detection Method
2.1. LPD Signal Waveform Design
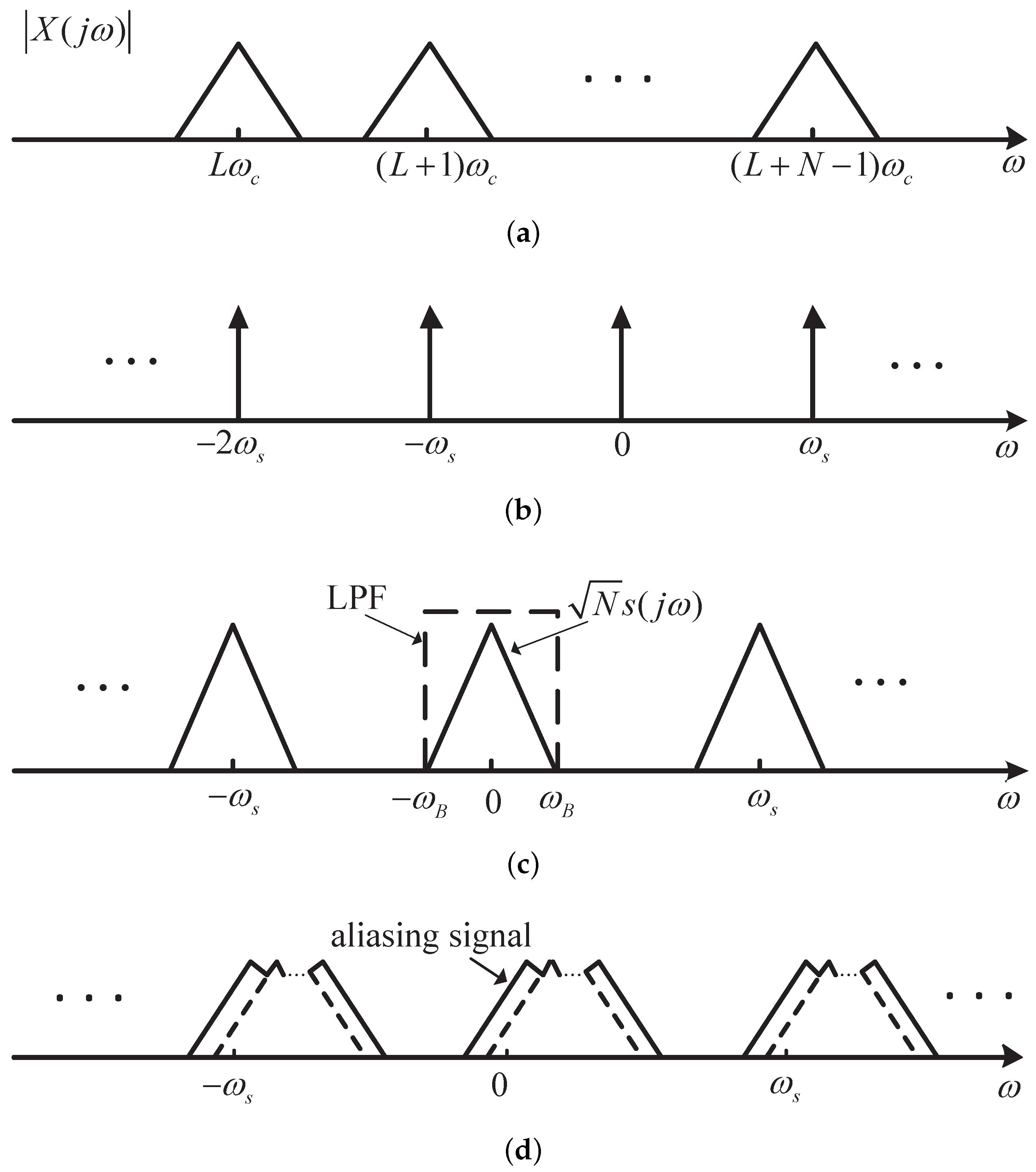
2.2. Principle of Under-Sampling Method for Intended Receiver
2.3. Practical Receiver Design
2.4. Complexity Analysis of Receiver
3. Design of Physical Layer Security Communication System Using Proposed LPD Signal
3.1. Wireless-Tap Channel Model
- Bob sends a transmission request signal to Alice, followed by pilot signals in the same frequency that Alice is going to use for secure data transmission.
- Alice estimates the sampling clock offset and CSI via the pilot signals.
- According to the sampling clock offset between Alice and Bob, Alice shifts the central frequencies of sub-band signals to ensure that they are aligned at Bob’s side after sampling.
- As the CSI of the channel from Bob to Alice has become known, the CSI from Alice to Bob can also be informed according to the channel reciprocal principle. Then, a precoding scheme is employed to enhance both capacity and security.
- Alice securely transmits the modified LPD signal to Bob.
3.2. Sampling Clock Offset Compensation
3.3. Precoding Scheme for Fading Channel
4. Performance Evaluation
4.1. Energy Detection Method
4.2. Detection Performance at Bob’s and Eve’s Ends
5. Simulation Results
5.1. LPD Performance
5.2. Comparison of BER Performance between Bob and Eve
6. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Xu, H.; Yu, W.; Griffith, D.; Golmie, N. A Survey on Industrial Internet of Things: A Cyber-Physical Systems Perspective. IEEE Access 2018, 6, 78238–78259. [Google Scholar] [CrossRef]
- Humayed, A.; Lin, J.; Li, F.; Luo, B. Cyber-Physical Systems Security–A Survey. IEEE Internet Things J. 2017, 64, 1802–1831. [Google Scholar] [CrossRef]
- Inayat, U.; Zia, M.F.; Mahmood, S.; Berghout, T.; Benbouzid, M. Cybersecurity Enhancement of Smart Grid: Attacks, Methods, and Prospects. Electronics 2022, 11, 3854. [Google Scholar] [CrossRef]
- Cheminod, M.; Durante, L.; Valenzano, A. Review of Security Issues in Industrial Networks. IEEE Trans. Ind. Inform. 2013, 9, 277–293. [Google Scholar] [CrossRef]
- Angueira, P.; Val, I.; Montalbán, J.; Seijo, Ó.; Iradier, E.; Fontaneda, P.S.; Fanari, L.; Arriola, A. A Survey of Physical Layer Techniques for Secure Wireless Communications in Industry. IEEE Commun. Surv. Tutor. 2022, 24, 810–838. [Google Scholar] [CrossRef]
- Zou, Y.; Wang, G. Intercept Behavior Analysis of Industrial Wireless Sensor Networks in the Presence of Eavesdropping Attack. IEEE Trans. Ind. Inform. 2016, 12, 780–787. [Google Scholar] [CrossRef]
- Yan, S.; Zhou, X.; Hu, J.; Hanly, S.V. Low Probability of Detection Communication: Opportunities and Challenges. IEEE Wirel. Commun. 2019, 26, 19–25. [Google Scholar] [CrossRef]
- Shi, C.; Wang, F.; Salous, S.; Zhou, J. Low Probability of Intercept-Based Optimal OFDM Waveform Design Strategy for an Integrated Radar and Communications System. IEEE Access 2018, 6, 57689–57699. [Google Scholar] [CrossRef]
- Shannon, C.E. Communication Theory of Secrecy Systems. Bell Syst. Tech. J. 1949, 28, 656–715. [Google Scholar] [CrossRef]
- Loepp, S.; Wootters, W.K. Protecting Information From Classical Error Correction to Quantum Cryptography; Cambridge University Press: Cambridge, UK, 2006. [Google Scholar]
- Simon, C. The Foundations of Quantum Information and Feasible Experiments. Ph.D. Dissertation, University Wien, Vienna, Austria, 2000. [Google Scholar]
- Zhang, H.G.; Gan, L.; Liao, H.S.; Wei, P.; Li, L.P. Estimating Spreading Waveform of Long-code Direct Sequence Spread Spectrum Signals at a Low Signal-to-noise ratio. IET Signal Process. 2012, 6, 358–363. [Google Scholar] [CrossRef]
- Zhou, X.; Song, L.; Zhang, Y. Physical Layer Security in Wireless Communications; CRC Press: Boca Raton, FL, USA, 2013. [Google Scholar]
- Wyner, A.D. The Wire-tap Chennel. Bell Syst. Tech. J. 1975, 54, 1355–1387. [Google Scholar] [CrossRef]
- Csiszár, I.; Körner, J. Broadcast Channels With Confidential Messages. IEEE Trans. Inf. Theory 1978, 24, 339–348. [Google Scholar] [CrossRef]
- Hero, A.O. Secure Space-time Communication. IEEE Trans. Inf. Theory 2003, 49, 3235–3249. [Google Scholar] [CrossRef]
- Hong, Y.W.P.; Lan, P.C.; Kuo, C.C.J. Enhancing Physical-Layer Secrecy in Multiantenna Wireless Systems: An Overview of Signal Processing Approaches. IEEE Signal Process. Mag. 2013, 30, 29–40. [Google Scholar] [CrossRef]
- Zhang, W.; Chen, J.; Kuo, Y.; Zhou, Y. Artificial-Noise-Aided Optimal Beamforming in Layered Physical Layer Security. IEEE Commun. Lett. 2019, 23, 72–75. [Google Scholar] [CrossRef]
- Sun, C.; Fei, Z.; Li, B.; Wang, X.; Li, N.; Hu, L. Secure Transmission in Downlink Non-orthogonal Multiple Access based on Polar Codes. China Commun. 2021, 18, 221–235. [Google Scholar] [CrossRef]
- Pfeiffer, J.; Fischer, R.F.H. Multilevel Coding for Physical-Layer Security. IEEE Trans. Commun. 2022, 70, 1999–2009. [Google Scholar] [CrossRef]
- Zheng, M.; Tao, M.; Chen, W.; Ling, C. Secure Polar Coding for the Two-Way Wiretap Channel. IEEE Access 2018, 6, 21731–21744. [Google Scholar] [CrossRef]
- Li, J.; Ye, N.; Ma, S.; Bu, X.; An, J. Multi-User Hybrid Beamforming Design for Physical Layer Secured mmWave LOS Communications. Electronics 2021, 10, 2635. [Google Scholar] [CrossRef]
- Li, L.; An, J.; Wang, Z.; Li, X. Under-sampling Spectrum-sparse Signals based on Active Aliasing for Low Probability Detection. Secur. Commun. Netw. 2015, 8, 4087–4097. [Google Scholar] [CrossRef]
- Proakis, J.G.; Salehi, M. Digital Communications, 5th ed.; McGraw-Hill: New York, NY, USA, 2007. [Google Scholar]
- Dhawan, S.K. Time Measurement With a Multiphase Clock. IEEE Trans. Nucl. Sci. 1983, 30, 293–296. [Google Scholar] [CrossRef]
- Yao, C.; Willson, A.N. A 2.8-3.2GHz Fractional-N Digital PLL With ADC-Assisted TDC and Inductively Coupled Fine-Tuning DCO. IEEE J. -Solid-State Circuits 2013, 48, 698–710. [Google Scholar] [CrossRef]
- Gilbert, S. Linear Algebra and Its Application, 4th ed.; Cengage Learning: Stamford, CT, USA, 2005. [Google Scholar]








Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Li, L.; Lv, J.; Ma, X.; Han, Y.; Feng, J. Design of Low Probability Detection Signal with Application to Physical Layer Security. Electronics 2023, 12, 1075. https://doi.org/10.3390/electronics12051075
Li L, Lv J, Ma X, Han Y, Feng J. Design of Low Probability Detection Signal with Application to Physical Layer Security. Electronics. 2023; 12(5):1075. https://doi.org/10.3390/electronics12051075
Chicago/Turabian StyleLi, Lintao, Jiayi Lv, Xin Ma, Yue Han, and Jiaqi Feng. 2023. "Design of Low Probability Detection Signal with Application to Physical Layer Security" Electronics 12, no. 5: 1075. https://doi.org/10.3390/electronics12051075
APA StyleLi, L., Lv, J., Ma, X., Han, Y., & Feng, J. (2023). Design of Low Probability Detection Signal with Application to Physical Layer Security. Electronics, 12(5), 1075. https://doi.org/10.3390/electronics12051075





