DpGuard: A Lightweight Attack Detection Method for an Industrial Bus Network
Abstract
1. Introduction
- (1)
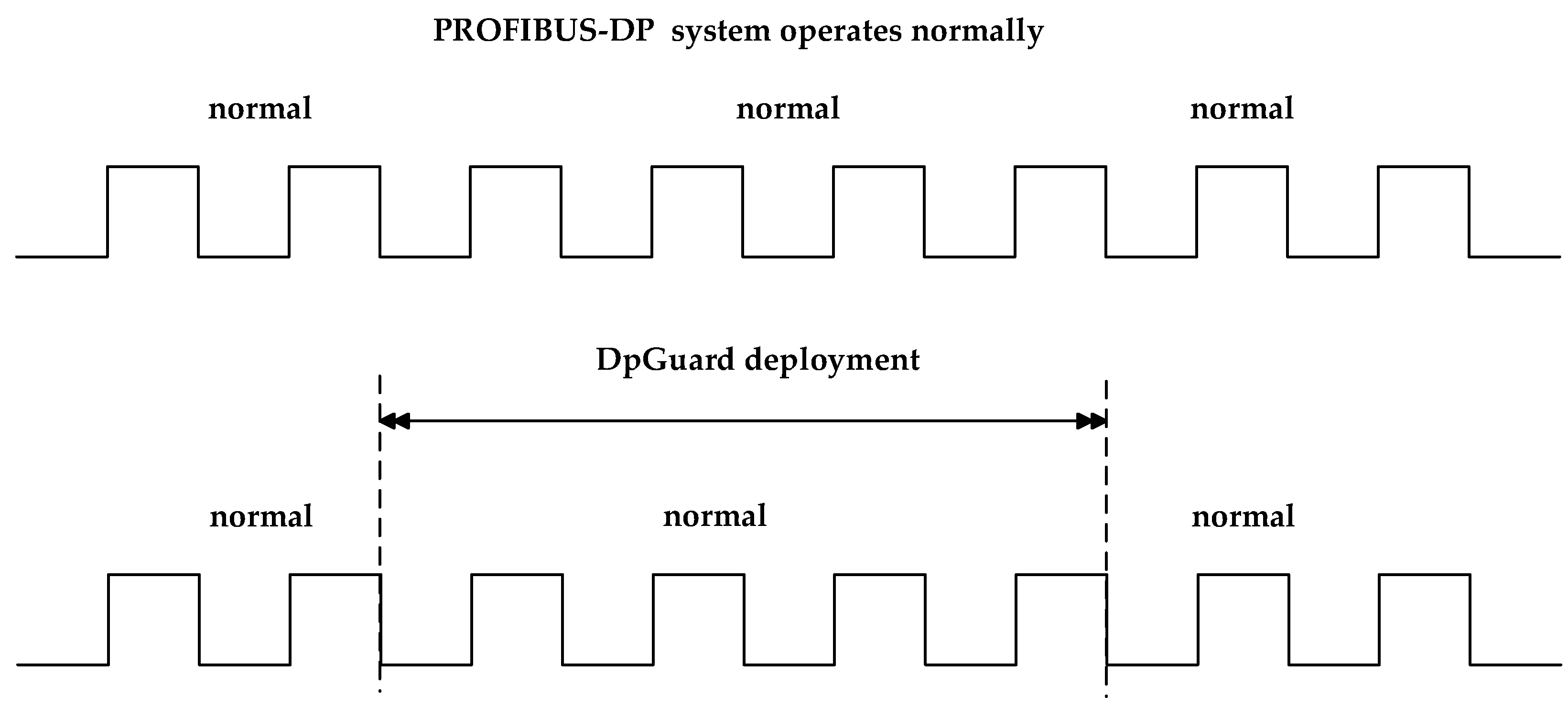
- We proposed a new scheme, DpGuard, that uses the characteristics of ICS traffic to correlate the initialization phase and the data exchange phase to automatically build a finite-state machine model to detect fault injection and semantic attacks in real-time using industrial serial protocol messages;
- (2)
- We developed a prototype system for attack detection based on a PROFIBUS-DP protocol communication system. Although the system was developed for a specific serial protocol, based on the idea it could be modified to extend and adapt it to other serial protocols such as CAN and MODBUS RTU;
- (3)
- We evaluated the scheme using two Siemens PLCs deployed on a PROFIBUS-DP system. The experiments showed that the scheme could detect fault injection and semantic attacks accurately in real-time without affecting the normal operation of the industrial serial network system. Our scheme outperformed the four other representative detection methods in terms of detection accuracy.
2. Background
2.1. PROFIBUS-DP System
2.2. PROFIBUS-DP Protocol
3. Related Work
4. Threat Model
5. Methods
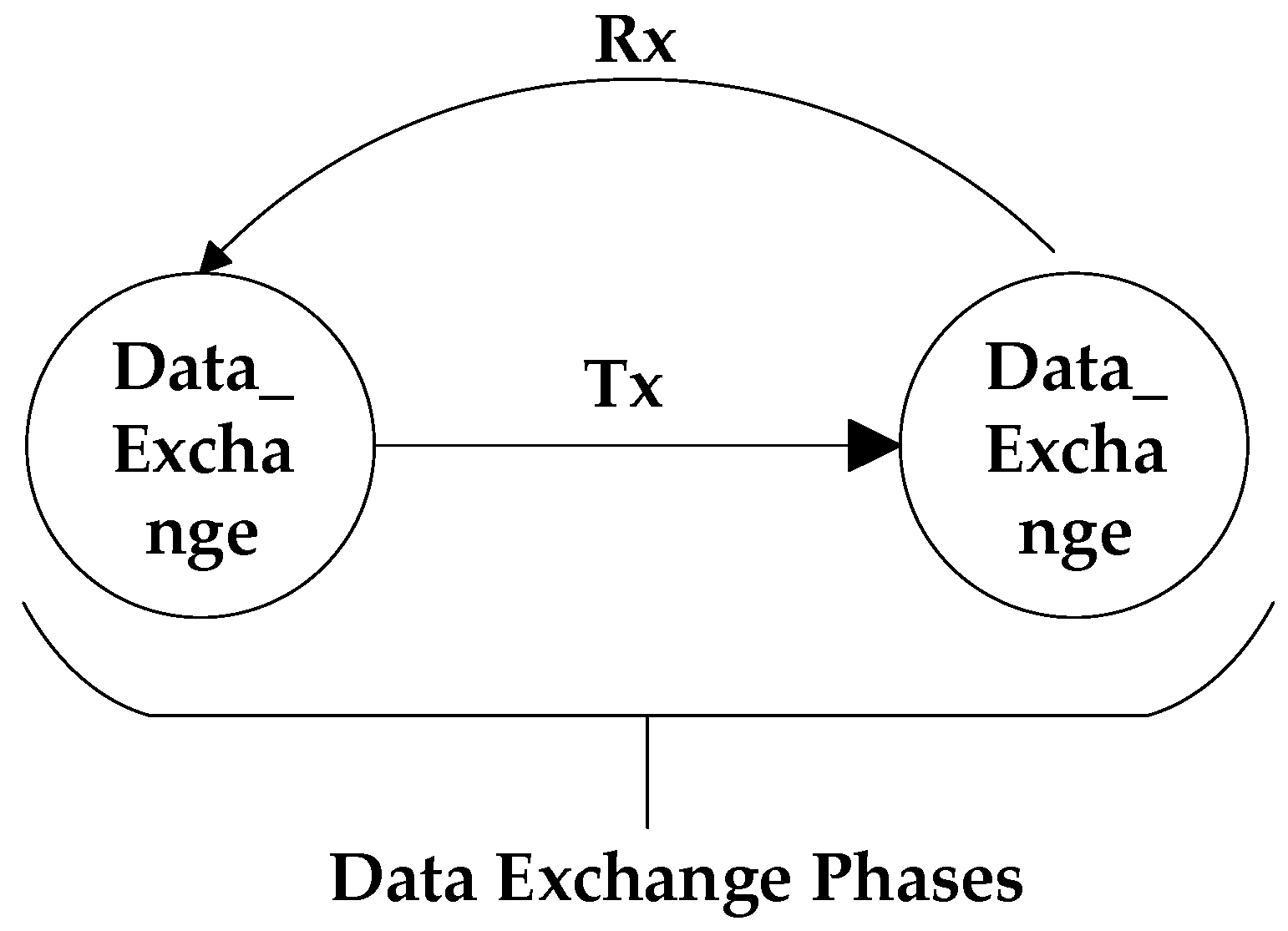
5.1. FSM
5.2. Model Training
5.2.1. Definition
5.2.2. Building the FSM Model
- (1)
- sd = “DC”, da = “02”, sa = “02”
- (2)
- sd = “10”, da = “08”, sa = “02”, fc = “49”, fcs = “53”, ed = “16”
- (3)
- sd = “10”, da = “02”, sa = “08”, fc = “00”, fcs = “0A”, ed = “16”
- (4)
- sd = “68”, ler = “05”, lers = “05”, sd = “68”, da = “88”, sa = “82”, fc = “6D”, du = “3C 3E”, fcs = “F1”, ed = “16”
- (5)
- sd = “A2”, da = “82”, sa = “88”, fc = “08”, du = “3E 3C 00 04 00 FF 00 00”, fcs = “8F”, ed = “16”
- (6)
- sd = “68”, ler = “10”, lers = “10”, sd = “68”, da = “88”, sa = “82”, fc = “5D”, du = “3D 3E B8 1E 01 00 42 24 01 40 01 00 42”, fcs = “A3”, ed = “16”
- (7)
- sd = “E5”
- (8)
- sd = “68”, ler = “09”, lers = “09”, sd = “68”, da = “88”, sa = “82”, fc = “7D”, du = “3E 3E 00 20 20 10”, fcs = “53”, ed = “16”
- (9)
- sd = “E5”
- (10)
- sd = “68”, ler = “05”, lers = “05”, sd = “68”, da = “02”, sa = “08”, fc = “08”, du = “01 00”, fcs = “AA”, ed = “16”
- (11)
- sd = “68”, ler = “05”, lers = “05”, sd = “68”, da = “08”, sa = “02”, fc = “5D”, du = “00 01”, fcs = “79”, ed = “16”
5.3. Detection Algorithm and Its Description
| Algorithm 1 Finite-state Machine (M) Detection Attack Algorithm |
| Input: real-time industrial bus network message serial (p0, p1, …, pn) |
| Input: set of state events Q, state transfer function の, state transfer probability θ |
| Output: fault injection and semantic attack alarm serial (p0, p1, …, pn) |
| While: |
| if then: |
| Alert (“Fault Injection Attack”) |
| else: |
| RecoderState |
| θ () = の (, ) |
| if then: |
| Alert (“Semantic Attack”) |
| else: |
| Next (serial) |
| endif |
| endif |
| END |
6. Evaluation
6.1. Experimental Environment
6.2. Experimental Data Generation
6.3. Experimental Results and Analysis
6.3.1. Detection Capabilities
6.3.2. Selection of θ
6.3.3. Impact Performance
7. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- SP 800–82; Guide to Industrial Control Systems (ICS) Security: Supervisory Control and Data Acquisition (SCADA) Systems, Distributed Control Systems (DCS), and Other Control System Configurations Such as Programmable Logic Controllers (PLC). NIST: Gaithersburg, MD, USA, 2011.
- De Moura, R.L.; Franqueira, V.N.L.; Pessin, G. Towards Safer Industrial Serial Networks: An Expert System Framework for Anomaly Detection. In Proceedings of the 2021 IEEE 33rd International Conference on Tools with Artificial Intelligence (ICTAI), Washington, DC, USA, 1–3 November 2021; pp. 1197–1205. [Google Scholar]
- Tovar, E.; Vasques, F. Real-time fieldbus communications using Profibus networks. IEEE Trans. Ind. Electron. 1999, 46, 1241–1251. [Google Scholar] [CrossRef]
- Francis, C.R. Design of the cryosat system. In Proceedings of the IEEE International Geoscience and Remote Sensing Symposium, Toronto, ON, Canada, 24–28 June 2002; Volume 3, pp. 1759–1761. [Google Scholar]
- Chandan, R.R.; Mishra, P.K. FSM based Intrusion Detection of Packet Dropping Attack using Trustworthy Watchdog Nodes. Recent Adv. Comput. Sci. Commun. 2021, 14, 2817–2827. [Google Scholar] [CrossRef]
- Song, H.M.; Kim, H.R.; Kim, H.K. Intrusion detection system based on the analysis of time intervals of CAN messages for in-vehicle network. In Proceedings of the 2016 International Conference on Information Networking (ICOIN), Kota Kinabalu, Malaysia, 13–15 January 2016; pp. 63–68. [Google Scholar]
- Morris, T.; Vaughn, R.; Dandass, Y. A retrofit network intrusion detection system for MODBUS RTU and ASCII industrial control systems. In Proceedings of the 2012 45th Hawaii International Conference on System Sciences, Maui, HI, USA, 4–7 January 2012. [Google Scholar]
- Kneib, M.; Huth, C. Scission: Signal Characteristic-Based Sender Identification and Intrusion Detection in Automotive Networks. In Proceedings of the 2018 ACM SIGSAC Conference, Toronto, ON, Canada, 15–19 October 2018. [Google Scholar]
- Tylman, W. Native Support for Modbus RTU Protocol in Snort Intrusion Detection System; Springer International Publishing: Brunów, Poland, 2013. [Google Scholar]
- Ike, M.; Phan, K.; Sadoski, K.; Valme, R.; Lee, W. SCAPHY: Detecting Modern ICS Attacks by Correlating Behaviors in SCADA and PHYsical. arXiv 2022, arXiv:2211.14642. [Google Scholar]
- De Santo, D.; Malavenda, C.S.; Romano, S.P.; Vecchio, C. Exploiting the MIL-STD-1553 avionic data bus with an active cyber device. Comput. Secur. 2021, 100, 102097. [Google Scholar] [CrossRef]
- Cole, B.D. Commissioning and Implementing a PROFIBUS Network in the Universal Water System. Master’s Thesis, Murdoch University, Perth, Australia, 2015. [Google Scholar]
- Gabor, G.; Pintilie, C.; Dumitrescu, C.; Costica, N.; Plesca, A.T. Application of Industrial PROFIBUS-DP Protocol. In Proceedings of the 2018 International Conference and Exposition on Electrical and Power Engineering (EPE), Iasi, Romania, 18–19 October 2018; pp. 614–617. [Google Scholar]
- Felser, M. PROFIBUS Manual, Ed.1.2.2; ePubli GmbH: Berlin, Germany, 2012. [Google Scholar]
- Nutzerorganisation eV, P. PROFIBUS System Description-Technology and Application. Order 2010, 4, 1102–1117. [Google Scholar]
- Roesch, M. Snort-Lightweight Intrusion Detection for Networks. In Proceedings of the LISA’99: 13th Systems Administration Conference, Seattle, WA, USA, 7–12 November 1999; pp. 229–238. [Google Scholar]
- The Zeek Network Security Monitor. 2019. Available online: https://www.zeek.org/ (accessed on 1 January 2023).
- Morris, T.H.; Jones, B.A.; Vaughn, R.B.; Dandass, Y.S. Deterministic Intrusion Detection Rules for MODBUS Protocols. In Proceedings of the Hawaii International Conference on System Sciences, Maui, HI, USA, 7–10 January 2013. [Google Scholar]
- Tomlin, L.; Farnam, M.R. A Clustering Approach to Industrial Network Intrusion Detection. In Proceedings of the 2016 Information Security Research and Education (INSuRE) Conference (INSuRECon-16), Online, 30 September 2016. [Google Scholar]
- Cho, K.-T.; Shin, K.G. Viden: Attacker Identification on In-Vehicle Networks. In Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security (CCS’17), Dallas, TX, USA, 30 October–3 November 2017; ACM: New York, NY, USA, 2017; pp. 1109–1123. [Google Scholar] [CrossRef]
- Bhatia, R.; Kumar, V.; Serag, K.; Celik, Z.B.; Payer, M.; Xu, D. Evading Voltage-Based Intrusion Detection on Automotive CAN. In Proceedings of the Network and Distributed System Security Symposium, Online, 21–25 February 2021. [Google Scholar]
- Dias, A.L.; Sestito, G.S.; Brandao, D. Performance analysis of profibus dp and profinet in a motion control application. J. Control Autom. Electr. Syst. 2017, 28, 86–93. [Google Scholar] [CrossRef]
- Lee, K.C.; Lee, S.; Lee, M.H. Remote fuzzy logic control of networked control system via Profibus-DP. IEEE Trans. Ind. Electron. 2003, 50, 784–792. [Google Scholar]
- Vitturi, S. DP-Ethernet: The Profibus DP protocol implemented on Ethernet. Comput. Commun. 2003, 26, 1095–1104. [Google Scholar] [CrossRef]
- Han, Y.; Etigowni, S.; Li, H.; Zonouz, S.; Petropulu, A. Watch me, but don’t touch me! Contactless control flow monitoring via electromagnetic emanations. In Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security, Dallas, TX, USA, 30 October–3 November 2017; pp. 1095–1108. [Google Scholar]
- Liu, Y.; Wei, L.; Zhou, Z.; Zhang, K.; Xu, W.; Xu, Q. On code execution tracking via power side-channel. In Proceedings of the 2016 ACM SIGSAC Conference on Computer and Communications Security, Vienna, Austria, 24–28 October 2016; pp. 1019–1031. [Google Scholar]
- Le, A.; Roedig, U.; Rashid, A. LASARUS: Lightweight Attack Surface Reduction for Legacy Industrial Control Systems. In Proceedings of the Engineering Secure Software and Systems: 9th International Symposium, Bonn, Germany, 3–5 July 2017; pp. 36–52, ISBN 978-3-319-62104-3. [Google Scholar] [CrossRef]
- Salehi, M.; Bayat-Sarmadi, S. PLCDefender: Improving Remote Attestation Techniques for PLCs Using Physical Model. IEEE Internet Things J. 2020, 8, 7372–7379. [Google Scholar] [CrossRef]
- Revent Intrusion and Maintain Network Integrity with Data Diodes. Available online: https://advenica.com/en/cds/data-diodes (accessed on 1 January 2023).
- Fu, Q.C. Design of communication protocol based on FSM. Power Syst. Technol. 2006, 30, 214–217. [Google Scholar]
- Chu, P.M. Synthesizing protocol specifications from service specifications in the FSM model. In 1988 Computer Networking Symposium; IEEE Computer Society: Washington, DC, USA, 1988. [Google Scholar]
- Lang, R. Schnell in ex-ex-sensoren direkt an profibus dp v1. Etz Elektrotech. Zeistchrift 1999, 120, 28–30. [Google Scholar]
- Uzair, M. Communication Methods (Protocols, Format & Language) for the Substation Automation & Control. Available online: https://www.eng.uwo.ca/people/tsidhu/Documents/project%20report%20Uzair.pdf (accessed on 1 January 2023).
- Chen, W.H.; Hsu, S.H.; Shen, H.P. Application of SVM and ANN for intrusion detection. Comput. Oper. Res. 2005, 32, 2617–2634. [Google Scholar] [CrossRef]
- Wang, Y. A multinomial logistic regression modeling approach for anomaly intrusion detection. Comput. Secur. 2005, 24, 662–674. [Google Scholar] [CrossRef]
- Ingre, B.; Yadav, A.; Soni, A.K. Decision tree based intrusion detection system for NSL-KDD dataset. In Proceedings of the Information and Communication Technology for Intelligent Systems (ICTIS 2017), Ahmedabad, India, 25–26 March 2017; Volume 2, pp. 207–218. [Google Scholar]





| Type of Attack | Attack Description | Attack Test Cases |
|---|---|---|
| Fault attack | Replay of non-normal-format messages | 0x68100202327D16 |
| Replay of function code message | 0x100802005316 | |
| Replay of SC frames | 0xE5 | |
| Replay of SD1 frame | 0x100802495316 | |
| New function code | 0x100802xx5316 * | |
| New destination address | 0x10xx02495316 * | |
| New length of main site SD2 news | 0x68xxxx6888826D3C3EF116 * | |
| New length of slave SD2 message | 0xA28288083E3C000400FF00008F16 | |
| Semantic attack | Register tampering | 0x6805056808027DxxxxED16 * |
| Diagnosis message tampering | 0x68xx68xxxxxx3E3Cx…xx16 * | |
| Input data tampering | 0x68xx68xxxxxx3E38x…xx16 * | |
| Slave address tampering | 0x68090968xxxxxx373Exxxxxx16 * | |
| Output data tampering | 0x68xx68xxxxxx3E39xxx16 * | |
| Token frame tampering | 0xDCxx02 * |
| Parameter Name | Parameter Value |
|---|---|
| Communication Rate | 19,200 |
| GSD | si03806a.gsd |
| Address | 8 |
| Power Modules | 6ES7 138-4CA01-0AA0 PM-E DC24V |
| DO Module | 6ES7 132-4BB30-0AA0 2DO DC24V |
| DI Module | 6ES7 131-4BD01-0AA0 4DI DC24V |
| Type of Attack | Attack Description | Quantity |
|---|---|---|
| Normal | Normal packets | 3588 |
| Fault attack | Replay of non-normal-format messages | 300 |
| Replay of function code message | 450 | |
| Replay of SC frames | 200 | |
| Replay of SD1 frame | 200 | |
| New function code | 200 | |
| New destination address | 200 | |
| New length of main site SD2 news | 300 | |
| New length of slave SD2 message | 300 | |
| Semantic attack | Register tampering | 250 |
| Diagnosis message tampering | 250 | |
| Input data tampering | 250 | |
| Slave address tampering | 250 | |
| Output data tampering | 250 | |
| Token frame tampering | 250 |
| Predicted Positive | Prediction Negative | |
|---|---|---|
| Reference Positive | TP (true positive) | FN (false negative) |
| Reference Negative | FP (false positive) | TN (true negative) |
| Method | Fault Attack | Semantic Attack | ||||||
|---|---|---|---|---|---|---|---|---|
| Accuracy | Precision | Recall | F1 | Accuracy | Precision | Recall | F1 | |
| Ref. [35] | 0.6745 | 0.7201 | 0.6700 | 0.6884 | 0.6011 | 0.5945 | 0.6043 | 0.6100 |
| Ref. [34] | 0.8780 | 0.8921 | 0.8442 | 0.8792 | 0.7109 | 0.7034 | 0.7034 | 0.7264 |
| Ref. [36] | 0.8827 | 0.8930 | 0.8672 | 0.8703 | 0.7133 | 0.7254 | 0.7197 | 0.7206 |
| Ref. [2] | 0.9990 | 0.9964 | 0.9892 | 0.9928 | 0.7300 | 0.7292 | 0.7255 | 0.7273 |
| DpGuard | 1.0000 | 1.0000 | 1.0000 | 1.0000 | 0.9980 | 0.9922 | 0.9980 | 0.9912 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Li, Z.; Wei, Q.; Ma, R.; Geng, Y.; Yang, Y.; Lv, Z. DpGuard: A Lightweight Attack Detection Method for an Industrial Bus Network. Electronics 2023, 12, 1121. https://doi.org/10.3390/electronics12051121
Li Z, Wei Q, Ma R, Geng Y, Yang Y, Lv Z. DpGuard: A Lightweight Attack Detection Method for an Industrial Bus Network. Electronics. 2023; 12(5):1121. https://doi.org/10.3390/electronics12051121
Chicago/Turabian StyleLi, Zecun, Qiang Wei, Rongkuan Ma, Yangyang Geng, Yahui Yang, and Zhuo Lv. 2023. "DpGuard: A Lightweight Attack Detection Method for an Industrial Bus Network" Electronics 12, no. 5: 1121. https://doi.org/10.3390/electronics12051121
APA StyleLi, Z., Wei, Q., Ma, R., Geng, Y., Yang, Y., & Lv, Z. (2023). DpGuard: A Lightweight Attack Detection Method for an Industrial Bus Network. Electronics, 12(5), 1121. https://doi.org/10.3390/electronics12051121






