Abstract
Privacy and security is very critical for mobile users and in-depth research into the area highlights a need for more scientific literature on the perception and challenges of end users to better align the design of privacy and security controls with user expectations. In this paper, we have explored the perceptions of the usability of privacy and security settings in mobile applications from mobile users in Saudi Arabia. The findings highlight that gender, age, and education level of users do not have any positive correlation with the privacy and security usability perceptions of mobile users. On the other hand, user concerns about privacy and security and the trustworthiness levels of end users regarding mobile phone privacy and security have a positive impact on end users’ perception of privacy and security usability. Furthermore, privacy usability perception has a positive impact on users’ feelings about their control over the privacy and security of their mobile phones. Based on the results of this empirical study, we propose that user-centric design of privacy and security controls, transparent data handling policies, periodic data management status preview and validation by end users, user education guidelines, strict governmental policies, and automated security settings recommendations can enhance the usability of the privacy and security of mobile phone applications. Our study did not take the geographical location of respondents into account, nor were the respondents balanced based on age and gender. In future work, these weaknesses need to be taken into account, and more qualitative studies can help to extract design guidelines for usable and secure mobile applications.
1. Introduction
Mobile applications provide convenience and efficiency for various daily tasks ranging from work to leisure and entertainment. These applications handle the personal, financial, and health data of users and protection of such sensitive data from unauthorized access is important. However, concerns over privacy and security issues of user data managed by these mobile applications are also increasing. Once the end users are confident that a certain mobile application is secure this will enhance end users trust and adoption rate. Furthermore, privacy laws and regulations such as the general data protection regulation (GDPR) require mobile applications to adopt transparent data privacy practices. Furthermore, the design of privacy and security controls in these mobile applications should be easy to use so that end users’ tasks are facilitated with minimal effort. Such well-designed privacy and security controls allow users to manage their data in an effective manner and ensure that such well-designed applications provide a competitive advantage to mobile applications providers. Therefore, it is important to understand the end user’s perception about the usability of privacy and security controls of mobile applications.
In this paper, we explore the perception of the usability of privacy and security settings of mobile phones of users from Saudi Arabia to better understand their concerns. The selection of Saudi Arabia as a case setting is due to the higher density of mobile internet usage. According to a survey, the number of internet users is estimated reach 39.18 million by 2029, the internet penetration rate is going to reach 98%, and the number of mobile phone internet users is estimated to reach 38.01 million by 2029 in Saudi Arabia [1]. In order to maintain this high number of mobile phone internet users, the need for usable privacy and security of mobile phones becomes very critical. Therefore, in this paper, we have focused on mobile phone users in Saudi Arabia regarding the perception of the usability of the privacy and security settings of mobile phones.
In order to minimize the security vulnerabilities, extensive technologies focusing on improving privacy and security have emerged. One of the key technologies to ensure security in mobile applications is the development of authentication mechanisms where biometric and behavioral characteristics of users are taken into account [2]. Similarly, multi-factor authentication mechanisms provide stronger security without sacrificing user convenience [3]. Techniques such as differential privacy [4] and homomorphic encryption [5] enable data analysis while preserving the confidentiality of sensitive information.
Moreover, decentralized and blockchain-based systems offer new avenues for enhancing privacy and data control in mobile applications [6]. Despite these extensive technological advancements, security concerns of end users have increased and human factors have become major contributors to cybersecurity threats. As a result, usable privacy and security controls in mobile applications has gained significant attention, which advocates for integrating user privacy and security and a positive user experience.
It is imperative to integrate privacy and security considerations into the design of mobile applications and services during the development stage rather than as an afterthought. Issues such as limiting the collection of unnecessary user data, anonymizing data wherever possible, and providing clear privacy policies outlining how user data is handled need to be dealt with optimally in the software design process.
In addition, during the application development stage the system designers should integrate privacy-enhancing features in mobile applications such as private browsing modes, ad tracker blockers, and encrypted messaging. These features empower users to take control of their digital privacy while using their mobile devices by setting secure and strong passwords, patterns, or other biometric authentication mechanisms. However, such features should be easy to set up and use, while still providing adequate protection against unauthorized access. Achieving such a balance typically means weighing privacy against usefulness; therefore, the requirement engineering stage of the application development lifecycle should focus on security features to be developed in mobile applications.
Moreover, mobile operating systems should provide easily accessible and understandable privacy settings so that end users can control permissions for each application conveniently to control access to their location, camera, microphone, contacts, etc. Clear explanations should accompany each permission request to help users make informed decisions to control the privacy and security of their personal data [7,8]. Therefore, user perceptions of privacy and security issues have a significant impact on their adoption and usage behavior [9,10]. In order to design usable privacy and security controls it is important to understand user perceptions to continuously improve the usability of privacy and security controls. This paper contributes to the literature by providing detailed insights of the perceptions of mobile users in Saudi Arabia of the usability of privacy and security controls.
2. Related Work
Due to the recent importance of cybersecurity, there has been a significant amount of research on the security of mobile applications. In the literature, trust, control, and perceived risks are termed as key determinants of users’ privacy-related decisions [11,12]. There are many studies to understand the security implications of mobile applications in different domains. For instance, Chatterjee et al. [13] explored user behavior in conducting financial transactions using smartphones and highlighted that privacy concerns have a significant impact on the usage by end users. Similarly, Choi et al. [14] explored the usage of traveler applications by end users to understand the relationship between application security and usage intention. They found user security, trust, and end user satisfaction, alongside fulfillment of expectations, play a significant role in the continued use of travel applications.
Almaiah et al. [15] found that the perceived trust, security, and service quality of applications results in an increased adoption of mobile banking applications by end users. Kanaan et al. [16] carried out an empirical study in Jordon and concluded that privacy, security, and service quality have a positive impact on the trust of end users. In a similar research project carried out in Spain and Portugal, Martínez-Navalón et al. [17] found that privacy and perceived ease of use of applications positively impacts the usage of banking applications by end users, and there was no significant evidence that the nationality of end users has an impact on the trust, privacy, and ease of use perception of end users. The use of social networking applications is on the rise by end users, which further enhances the threat to users’ privacy and data security. In the literature, there is a detailed discussion on security threats posed by social network applications, and Bhattacharya et al. [18] have developed a taxonomy of machine learning solutions to secure online social networks.
Kulyk et al. [19] noted that a higher density of smartphone use has resulted in extensive personal data being stored in smartphones, which may be misused by different mobile applications installed on those smartphones. They further discussed that although app stores provide some indication of the potential security implications of mobile applications, the effectiveness of such information is limited as it is confusing to end users, especially those with limited technical expertise. In order to educate the end users, the authors prepared a brochure which can help end users’ awareness.
Lin et al. [20] found that the evolution of mobile applications in the health sector has resulted in privacy, security, and usability challenges, and they proposed a set of principles for mobile application designers to enhance the privacy and security of healthcare applications, making them more secure and resilient. Pattnaik et al. [21] carried out an analysis of twitter datasets to understand the discussion of twitter users about cybersecurity and the privacy of computing devices. The study found interesting insights, e.g., the number of tweets about cybersecurity from non-technical users increased after the COVID-19 pandemic showing more awareness of end users. The study highlighted that end users have overall negative sentiments, showing a concern about cybersecurity by end users. The study advocates a more rigorous research effort by keeping in view the users’ perceptions. In another study, Alsyouf et al. [22] analyzed the use of health record systems by patients using a technology acceptance model and concluded that security, privacy, and usability are the key enablers for successful use of electronic health records by end users.
In another study, Du et al. [23] looked into mismatches in mobile applications in security settings and data collection by third party data collection libraries in mobile applications. They identified 157 such inconsistencies and reported them to relevant application developers to rectify them. Valero et al. [24] highlighted that end users experience serious privacy and security concerns while using smart personal assistants, and the handling of user data by these agents is not transparent. Groen et al. [25] have advocated that adoption of a human centered design approach in the development of security technologies can facilitate end users by taking into account diverse needs, contexts, and user behaviors in the design process. Aljedaani et al. [26] carried out an empirical study in Saudi Arabia and highlighted that end users have limited knowledge about security features of such mobile applications. The study reported that users were not aware of data protection mechanisms adopted by these mobile applications to protect user data and this can result in their failure to use these applications. Therefore, the study advocates for better communication support from application providers regarding user data management to foster successful usage.
Cerf et al. [27] have highlighted that there is a need for more effective security controls for end users to manage their privacy and security settings. The authors highlighted that despite the provision of security controls, the management of such controls may be difficult by end users; therefore, there is a need to integrate usability aspects in the design of privacy and security controls to enable end users to better manage their personal data. Chennamaneni and Gupta [28] have highlighted that personality traits significantly contribute in predicting users’ privacy behavior while using mobile applications. The findings highlighted that in line with protection motivation theory, end users who have higher levels of neuroticism in their personality tend to adopt higher levels of security protection behavior in their usage of mobile applications.
In another study, Akter et al. [29] highlighted the advantages of involving community members to increase awareness and promoting secure behavior among end users. They further highlighted that such an involvement can help in identifying security risks, which may not be identified by deploying only technical measures. Brunotte et al. [30] have highlighted that provision of privacy explanation helps in increasing the end users’ trust of software. Therefore, it is critical that data management processes of technological systems should be transparent and users are consistently informed about their data privacy. Similarly, Assal et al. [31] highlighted that the actual usability of mobile applications is below the end users’ expectations; therefore, end users find it difficult to manage their security controls optimally. As a result, the usage rate of privacy features in mobile applications is limited; therefore, designers of these applications need to take into account the user experience while designing security features of mobile applications.
Feth et al. [32] have proposed a user centric model to improve privacy and security. The model takes into account users’ needs, behaviors, and contexts during the design of privacy and security controls, which can result in more usable security solutions having more resilience. Liu et al. [33] have highlighted that customizable user security profiles can help in improving the privacy and security of mobile phones. Creating such profiles can help in customizing the privacy and security preferences of end users, and security settings can be automated based on user preferences, thus reducing the user’s cognitive load and making the user security settings adjustment process more usable. Wu et al. [34] in their study also highlighted the importance of usability in designing privacy and security controls. They highlighted that well designed, clear notifications help in improving users’ security perceptions and trust of the mobile applications, whereas poorly designed notifications negatively impact users’ perceptions and lead to lower user retention. Acar et al. [35] argued that usable privacy and security should not only include the perception of end users, but rather it should also take into account developers and all other stakeholders as well. Such a 360-degree approach will help in designing more comprehensive security solutions and ultimately help in enhancing overall privacy and security.
Di Nocera et al. [36] concluded that there is a strong need to embed usability aspects in designing privacy and security controls to facilitate end users. The authors further highlighted the need for more rigorous research in this domain to support end users in managing the security controls effectively. In another study, Pattan and Madamanchi [37] investigated context aware mobile applications and concluded that usability aspects in such applications’ security controls is compromised due to the enormous dynamicity of the applications’ functions. As a result, end users have difficulties in managing their security preferences, which can lead to insecure behavior of end users. The authors highlighted that intuitive and flexible privacy and security control mechanisms should be designed to optimize the security settings of mobile applications based on users’ expectations. Christin et al. [38] have highlighted the need for striking a balance in automated controls and user controls to foster usable privacy in mobile sensing applications. Due to diverse data collection sensors, users struggle to continually control the data privacy settings. Therefore, the integration of automated controls and user controls can help users in fostering effective controls to protect their data privacy.
Gutfleisch et al. [39] looked into the key reasons for integrating usable security into software end products. They highlighted the lack of communication among security researchers and product developers, limited resources for usability testing, and competing priorities undermining usability concerns. The authors also highlighted that user experience is not taken into account in the design of security controls, resulting in difficulties for end users in using the software. They, therefore, emphasized the need to integrate usability issues into the security design process. Mathis et al. [40] pushed for the involvement of experts in the design of security systems to have their input early in the development lifecycle to make security systems more robust and usable as well.
Chin et al. [41] noted the mismatch between end users’ privacy and security perceptions and actual security mechanisms implemented in smartphones. As a result of this gap, potential security breaches may happen; therefore, users must be educated about potential security risks of smartphones to make informed decisions. Zhang [42] looked into the usability of in-app browsing interfaces and highlighted that such interfaces may mislead end users about the origin of the content. Furthermore, the study highlighted that usability issues can hinder the effectiveness of security features.
Similarly, Balapour et al. [6] have highlighted that user perception is very critical in fostering the successful use of mobile applications by end users. The authors highlighted that if end users perceive an application as secure their adoption rate increases and a negative security perception will lower the trust of users. Therefore, it is important to address end users’ privacy and security concerns to enhance end users’ trust. Reuters et al. [43] looked into the progress made in the usable privacy and security research field and highlighted that despite the progress in the field, transparency of privacy and security practices and the ability to tailor security settings are still critical challenges to foster usable security solutions and there is a need for sustained research on these themes.
Musa et al. [44] have proposed a blockchain based storage approach for Android mobile applications to secure the data. Khan et al. [45] have highlighted that there is limited empirical evidence on the usability effectiveness of implicit authentication as compared to explicit authentication. The authors carried out an empirical study that highlighted that 91% of participants rated implicit authentication as more convenient and 81% perceived that it provides them with the required level of security. Liu et al. [46] have developed a recommender system which adopts crowdsourcing to enhance the privacy and usability of mobile applications. This system reflects on crowdsourced data to recommend privacy permissions to end users, thus minimizing the cognitive load on end users and facilitating them to foster personalized security settings.
Moreover, Frik et al. [47] discussed the usability of smartphone privacy and security settings, and the implications have not been investigated in depth, especially with the less technically skilled end users. They conducted a study to gain insight into the perceptions of users and found that the majority of end users are not aware of their ability to control their privacy and security settings on smartphones. They noted that some socio demographic groups of end users are more prone to privacy and security issues.
Alt and von Zezschwitz [48] highlighted that the design of privacy and security mechanisms should take into account diverse user needs and contexts. Furthermore, they highlighted the need for better user education and adoption of communication strategies to better inform end users about the privacy and security mechanisms.
In another empirical study, Ferreira et al. [49] investigated security issues in Android applications and found that the majority of applications collect personal data unnecessarily and transfer them to the network without the end user’s consent. Therefore, it is critical to bring transparency in data communication and improve overall application security. Chen et al. [50] highlighted that privacy settings in mobile applications are often difficult to find; therefore, most end users are unable to control their information in the default mode of an application. They conducted an experiment and explored 100,000 mobile applications and found that 36.29% applications had difficult to control security settings, and among them, 82.16% were sharing user data in their default mode.
Lin et al. [51] noted that automated tools for observing mobile app behavior do not accurately reflect user behavior, making it unclear whether data usage is based on user consent. The authors used crowdsourcing techniques to understand smartphone users’ security expectations and identified potential security breach points in mobile applications.
Nema et al. [52] discussed how end users of mobile applications have diverse perspectives which are based on the nature and type of data collected by mobile applications as well as their contexts. Therefore, it is critical to involve a large base of end users to understand their privacy and security priorities to foster usable mobile application security mechanisms.
Jacobs and McDaniel [53] carried out a review to outline critical factors to foster usable security and highlight that there is a need for better integration of usability factors in the design process of privacy and security controls. Ismail et al. [54] have highlighted that mobile application developers can use crowdsourcing as a means to understand end user behavior regarding privacy management, and as a result, the usability issue can be resolved to better design the security management features of mobile applications. Martin and Shilton [55] carried out an empirical study to understand users’ privacy expectations of mobile devices and found that context influences the users’ expectations; therefore, it is important to understand user expectations to better design privacy controls and establish effective communication with end users regarding the use of data.
From the related work, we can deduce that there is a need for better usability for privacy and security controlling mechanisms, users’ perceptions are key for better design, and the diversity of users’ background and context impact end users’ adoption of security and control mechanisms. Therefore, there is a need to strengthen the body of knowledge to provide more insights of user perceptions and awareness regarding privacy and security implications to further improve the privacy and security of mobile applications. Based on the review of literature, following six hypotheses have been developed for our study.
Hypothesis 1:
Gender of users has a positive impact on perception of usable privacy of mobile phone users.
Hypothesis 2:
Age of users has a positive impact on perception of usable privacy of mobile phone users.
Hypothesis 3:
Study level of users has a positive impact on perception of usable privacy of mobile phone users.
Hypothesis 4:
Users concerns of privacy and security have a positive impact on perception of usable privacy of mobile phone users.
Hypothesis 5:
Trustworthiness level of users of mobile phone privacy and security has a positive impact on perception of usable privacy of mobile phone users.
Hypothesis 6:
Usable privacy perception has a positive impact on users’ feelings about controlling privacy and security of mobile phones.
3. Materials and Methods
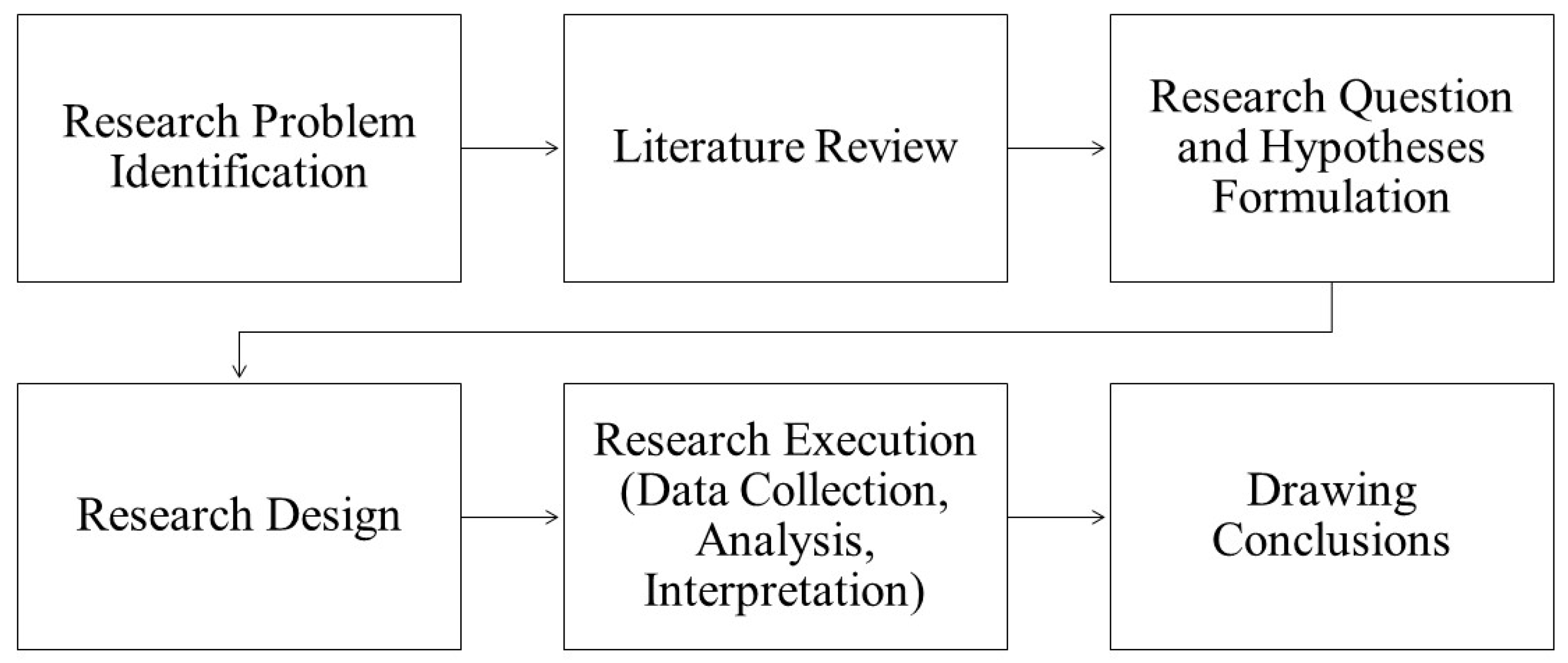
As shown in Figure 1, we followed a standard scientific approach for our study. We started with research problem identification regarding the usability of privacy and security and then carried out a rigorous literature review to identify knowledge gaps. After this, we developed research questions and formulated the hypotheses. The hypotheses were tested through a designed research approach, followed by data collection, analysis, and interpretation. Based on the findings, recommendations were formulated.
Figure 1.
Research design.
In order to evaluate our hypotheses, we conducted a quantitative study. Quantitative studies are widely used across different disciplines to analyze data and generalize the findings [56]. This study used a questionnaire for data collection. Designing a questionnaire requires considerable efforts to decide the required length, type of options for questions, sample size, sampling methods, etc. [57]. The questionnaire for this study was designed by reviewing earlier studies [11,58]. While designing the questionnaire, theoretical constructs came mainly from the usable privacy and information systems domain. The individual questions were mainly based on a five-point Likert scale (strongly disagree, disagree, neutral, agree, and strongly agree). Once the first draft of the questionnaire prepared, it was reviewed by a colleague for content validity.
After, the feedback questionnaire was revised and Google forms were used to collect the empirical data. The questionnaire was rolled out in May 2024, and 889 responses were collected, among which 3 responses were rejected, resulting in 886 valid responses. For data collection, we relied on a non-probability sampling technique and used a snowball sampling approach. Initially, we approached some connections by rolling out the questionnaire link using WhatsApp messages and emails. We requested the help of these initial contacts to further roll out the questionnaire link to their peers. Joining the survey was voluntary and data was collected anonymously and kept confidential. Participants were invited through email to join our survey, and there was a qualification criterion that the respondent was a mobile phone user.
Keeping in view the 886 valid responses and a confidence level of 95%, we achieved a margin of error of 3.23%. Once the data had been collected, it was processed in Microsoft Excel to get the percentages of the responses, and after this, the complete data sheet was coded into numeric data to process it using SmartPLS 4[59] to identify the relevance of the constructs in the model outcome. During our analysis, we applied the bootstrapping procedure using the partial least squares method with 5000 iterations. After the formulation of the model, the p-value was used to approve or reject our hypotheses. The discriminant validity was measured using the Fornell–Larcker criterion and heterotrait–monotrait ratio of correlations. Discriminant validity helps in providing the confidence that the constructs used for data collection are aligned with the research questions.
4. Results
As shown in Table 1, our survey included 308 male and 578 female respondents and a large number of respondents belonged to the age group of 19–25 years, and their study level was undergraduate.

Table 1.
Demographic attributes of respondents.
In our questionnaire, there were four questions relevant to user concerns. As shown in Table 2, in the first question, 59.37% respondents strongly agreed that they used a password or a biometric control to secure their mobile phone. In the second question, we intended to understand the users’ concerns about the privacy of their personal information on their mobile phones, and the majority of respondents chose the middle ground. In the third question, we enquired from users about how often they review the privacy policy of mobile applications before using them, and the majority of respondents indicated that they review such policies sometimes. In the last question, we enquired about how concerned the user is about personal information privacy while using mobile applications, and only 7% strongly agreed, 16.14% agreed that they were not concerned, and 39.39% of respondents remained in the middle, whereas 24.83% disagreed, and 12.64% strongly disagreed with it.

Table 2.
Responses to questions focusing on end user concerns.
There were eight questions related to trustworthiness of mobile applications in our questionnaire, which are shown in Table 3. The first question was about the presence of concerns that intruders will know the user’s location, and 18.74% strongly agreed, and 32.28% respondents agreed that they have this concern. The second question asked about the possibility of an intruder accessing a user’s photos and personal data, and 21.22% strongly agreed, and another 34.65% respondents agreed that they were concerned about it. In the next question, respondents were asked whether they have the concern that someone would take over control of their mobile phone, and in response to this question, 19.07% strongly agreed, and another 25.85% respondents remained neutral; however, 45% respondents agreed or strongly agreed. Furthermore, 17.04% respondents strongly agreed and 34.54% agreed that there is uncertainty associated with the intended use of their personal information regarding mobile applications providers, whereas 34.31% remained neutral, 10.50% disagreed, and 3.61% strongly disagreed. In response to the next question, 22.91% respondents strongly agreed and another 37.70% agreed that they are concerned that installed mobile applications will use their personal information without their authorization. In response to the next question in our survey, 13.21% respondents strongly agreed and 22.22% agreed that installed mobile applications would tell the truth regarding data management practices to end users. In addition, 11.74% respondents strongly agreed and 28.33% agreed that they believe that all mobile application providers are in general predictable and consistent regarding the use of personal data of end users. Overall, only 12.08% of respondents strongly agreed and 27.43% agreed that they consider mobile phone communication safe.

Table 3.
Responses to questions focusing on trustworthiness of mobile applications.
In the context of the usability privacy perception of mobile applications, there were nine questions in our questionnaire which area shown in Table 4. In the first question, we asked the respondents whether the mobile operating systems provide easily accessible and understandable privacy settings, and 25.28% respondents strongly agreed, 36.12% agreed, 27.54% remained neutral, 7.11% disagreed, and 3.95% strongly disagreed with it. In response to the next question that locating and reviewing privacy and security policies and guidelines of mobile applications are usable and easily accessible in the mobile applications, only 18.62% respondents strongly agreed, another 35.33% agreed, 31.94% remined neutral, whereas 10.95% respondents disagreed, and 3.16% strongly disagreed. In response to the question that users can easily find out who has what level of access in mobile applications, 12.98% respondents strongly agreed, 25.73% agreed, 34.09% remained neutral, 20.32% disagreed, and 6.88% strongly disagreed. Regarding the question, I know how my data will be processed and by whom, 12.98% strongly agreed, 25.73% agreed, 32.17% remained neutral, 20.77% disagreed, and 8.35% strongly disagreed. In addition, 13.43% respondents strongly agreed, 35.21% agreed, and 32.39% remained neutral to the fact that it is normally clearly mentioned on mobile applications that data will not be accessed without my explicit consent. Another 14.45% respondents disagreed, and 4.51% strongly disagreed with it.

Table 4.
Responses of question focusing on usability privacy perception of mobile applications.
In response to the next question about whether it is clearly mentioned on mobile applications which security measures are used in the applications, 13.09% respondents strongly agreed, 35.10% agreed, 34.76% remained neutral, 13.21% disagreed, and 3.84% strongly disagreed. Furthermore, 17.61% respondents strongly agreed and another 34.09% agreed that they will be made aware of any changes in the privacy policy of mobile applications. In response to the next question about whether mobile applications educate users about setting up privacy and security controls, 16.70% strongly agreed, 30.70% agreed, 31.60% remained neutral, 16.25% disagreed, and 4.74% strongly disagreed that mobile applications provide such features. Regarding the integration of privacy-enhancing tools and features in mobile applications, 15.46% respondents strongly agreed, 35.89% agreed, 34.09% remained neutral, 10.95% disagreed, and 3.61% respondents strongly disagreed.
In the section on user feelings regarding the privacy and security of mobile applications, we had 8 questions in the questionnaire which are shown in Table 5. In the first question, we enquired about whether users are aware of how to control the privacy and security of mobile applications, and 15.80% of respondents strongly agreed, 35.33% agreed, 30.81% remained neutral, 13.32% disagreed, and 4.74% strongly disagreed. In the second question, we asked respondents whether they feel that they can protect their mobile phone from hackers/phishers if they take good care of computer security. In response to this question, 23.59% respondents strongly agreed, 31.72% agreed, 28.10% remained neutral, 12.87% disagreed, and 3.72% strongly disagreed with it. In response to the next question, 13.77% strongly agreed, 24.04% agreed, 30.47% remained neutral, 21.78% disagreed, and 9.93% strongly disagreed with the fact they regularly review policies and the security/privacy certificate of mobile applications before installing them on their mobile phones.

Table 5.
Responses to questions focusing on users’ feelings on privacy and security of mobile applications.
In response to the next question, 41.65% strongly agreed, 26.41% agreed, 22.12% remained neutral, 5.53% disagreed, and 4.29% strongly disagreed with the fact that it is important to pay attention to cybersecurity. In response to the next question, around 52% respondents strongly agreed or agreed with the fact that cybersecurity issues worry them. In response to the next question, 29.80% respondents strongly agreed, 35.55% agreed, 25.17% remained neutral, 6.32% disagreed, and 3.16% strongly disagreed that they think that if they pay special attention to cybersecurity, it will make a difference. In response to the next question regarding the belief that their personal information is not interesting for others and no one will hack their phone, 18.28% respondents strongly agreed, 26.41% agreed, 28.67% remained neutral, 18.28% disagreed, and 8.35% strongly disagreed. In the last question, we asked the respondents whether they felt that, regardless of the security mechanisms they might adopt, individuals with bad intentions could still break into their mobile phones, and 18.85% strongly agreed, 28.33% agreed, 30.59% remained neutral, 13.77% disagreed, and 8.47% strongly disagreed.
In order to validate our hypotheses, we used p-values as a measure, and as shown in Table 6, the p-values of hypotheses 1, 2, and 3 are above 0.05 [60], which is considered a threshold value for approving hypotheses; therefore, the first 3 hypotheses are rejected. This implies that our study finds that the gender, age, and study level of users are not deemed to positive influence the mobile end user’s perception of the usability of privacy. As shown in Table 6, hypotheses 4 and 5 achieved a p-value of 0, which approves hypotheses, which highlights that regarding user concerns of privacy and security, the trustworthiness of mobile phone privacy and security of end users has a positive impact on the usability of privacy perception. Furthermore, hypothesis 6 highlights that the usability privacy perception of end users having a positive impact on users feeling in control of their mobile phone security is also approved in our study.

Table 6.
Results of hypotheses.
In order to measure the discriminant validity, we used the Fornell–Larcker criterion, and as shown in Table 7, the topmost values are the maximum in each of the columns, except trustworthiness and user feeling, where the difference is 0.034 and 0.08, respectively, which is very minor and can be ignored [61]; therefore, the validity is confirmed.

Table 7.
Fornell–Lacker criterion for discriminant validity.
Furthermore, the heterotrait–monotrait ratio of correlations was counted, and as per Henseler et al. [62] and Hair et al. [63], the value should be below 0.9. As is shown in the HTMT matrix in Table 8, all values are below 0.9, which also proves the construct validity.

Table 8.
HTMT matrix discriminant validity.
5. Discussion
The empirical findings highlight that the number of mobile users with strongly agree and agree responses is limited and there is a need to improve the privacy and security perception of end users. Gender, age, and education level did not positively contribute to perception, but the trustworthiness level of mobile users and users’ concerns of privacy and security positively contributed to enhanced awareness of end users, which in turn positively impacts end users’ feelings about controlling the privacy and security of mobile phones.
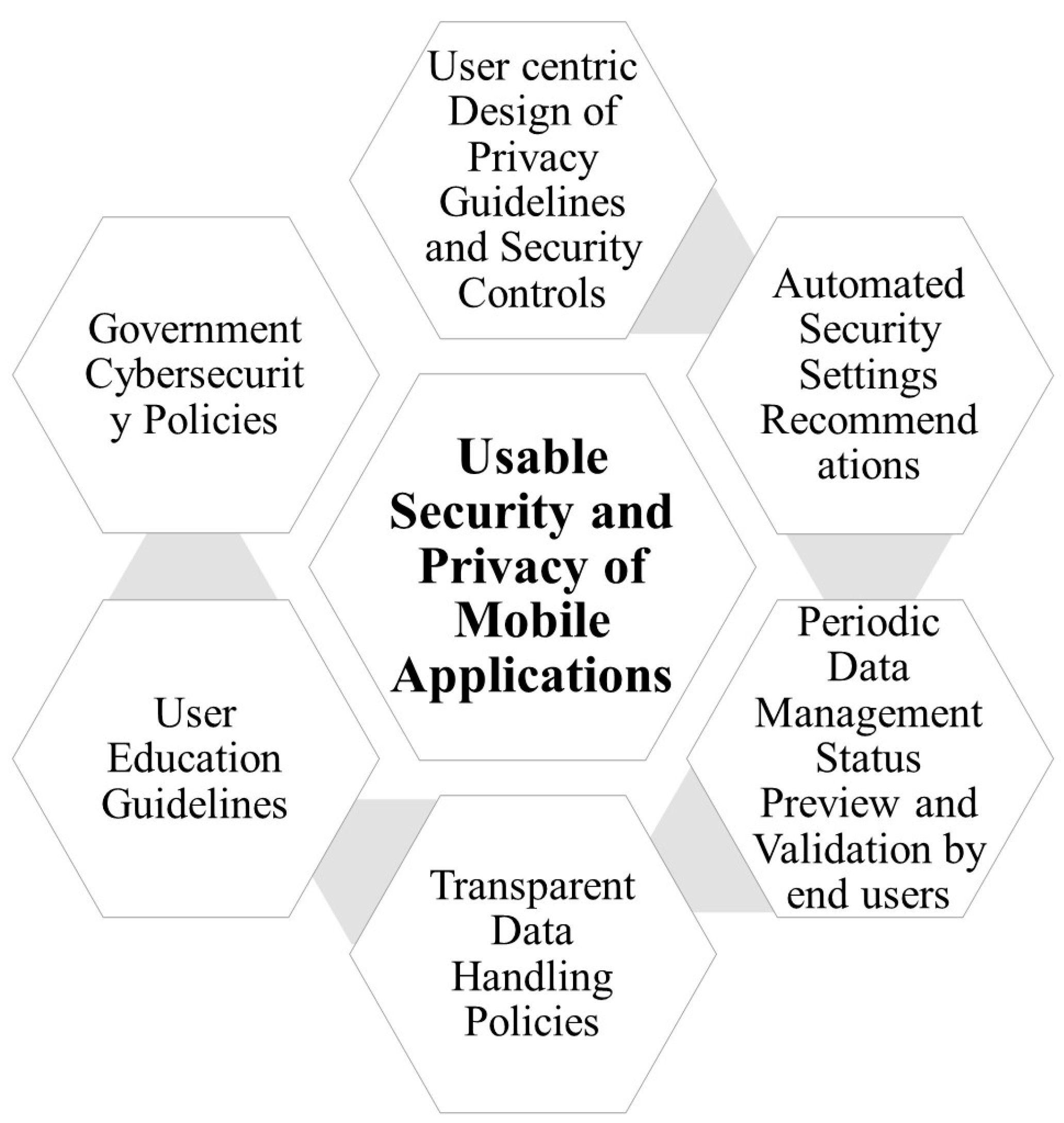
This work has significant practical implications for policy makers and mobile application designers. In order to improve the usability of privacy and security awareness of end users, we propose a model which is based on six key elements, as shown in Figure 2. We highlight that the design of privacy and security controls should focus on usability aspects to ensure that end users can easily locate and use these controls. This is in line with the findings in many earlier studies [37,39,42,46,54]. The adoption of a user-centric approach is necessary in the development process by fostering participatory design practices [64,65]. This approach will help in simplified user interfaces, use of end user language rather than technical terms, reduced information overload, interactive controls, and accessible privacy features.
Figure 2.
Model to improve usability of privacy and security awareness among mobile users.
Another design recommendation is to provide automated security recommendations to end users where artificial intelligence capabilities can be integrated, as most users may not be aware what the optimal privacy and security settings are [33,38,51]. Advanced approaches such as federating learning and differential privacy can be adopted for optimally training security models and setting up customized security settings. Another design feature to improve the usability of privacy and security in our model is to provide regular data management status previews for end users so that they are aware of what kind of security permissions are available in applications and they can validate these settings [23,27].
The fourth element of our model highlights that mobile applications should have transparent data handling policies which should be visible to end users, which will improve the confidence level of end users [66]. Mobile applications may adopt a minimal data collection approach and allow easy data deletion features. Furthermore, mobile applications need to educate users about security implications, and a game-based approach may be adopted. The minimal cognitive load principle from usability engineering can be applied on privacy and security controls to provide users with easy-to-use tips and guidelines to enhance their information security awareness.
The last element of the model highlights the governmental role in designing regulations to reassure end users that data management by mobile application providers is safe and regulated by governmental policies [10]. Designing appropriate regulations for organizations and individuals increases end users’ confidence in adopting mobile applications as well as helping in the digital literacy of the general public.
One of the limitations of our study is that the number of male respondents was less as compared to the female respondents, and a majority of respondents were in the age group of 19–25 years, which may have had an impact on the findings. Furthermore, the geographical location of respondents in Saudi Arabia was not considered in our survey. Future studies can work on these limitations, and qualitative studies need to be conducted to further understand the design implications of the identified issues. Additionally, participatory design approaches can be used in application design stages to design usable mobile applications.
6. Conclusions
The usability of the privacy and security of mobile phone applications is an emerging area. As the literature highlights, there is a need for more detailed studies to understand users’ perceptions; therefore, in this paper, we have focused on the mobile users in Saudi Arabia to understand their perceptions. The study highlights that the gender, age, and education levels of end users do not have any impact on the privacy and security usability perception of mobile users. It also found that end users’ concerns regarding privacy and security positively impact the perception of mobile users. Similarly, the trustworthiness level of users regarding mobile phone privacy and security positively impacts the usability privacy perception of end users. Furthermore, the usability privacy perception has a positive impact on users’ feelings about controlling the privacy and security of mobile phones. Based on our study, we presented a model to improve the usability privacy and security perception of mobile applications. This model advocates for six enablers, which are the adoption of user-centric approaches to design privacy and security controls, transparent data handling policies, periodic data management status preview and validation by end users, user education guidelines, strict governmental policies, and automated security settings recommendations.
Funding
The study was conducted without any external funding.
Institutional Review Board Statement
The study was conducted in accordance with the Declaration of Helsinki, and the protocol was approved by the Ethics Committee of Imam Abdulrahman Bin Faisal University on 23 April 2024. (IRB-2024-09-310).
Informed Consent Statement
Informed consent for participation in the questionnaire was obtained from all subjects.
Data Availability Statement
The data of this study is not made public due to privacy issues; however, it can be acquired on request from the corresponding author.
Acknowledgments
The author would like to thank all the respondents for filling the questionnaire for this study.
Conflicts of Interest
The authors declare no conflicts of interest.
References
- Available online: https://www.statista.com/statistics/558821/number-of-mobile-internet-user-in-saudi-arabia/ (accessed on 5 September 2024).
- Dahia, G.; Jesus, L.; Pamplona Segundo, M. Continuous authentication using biometrics: An advanced review. Wiley Interdiscip. Rev. Data Min. Knowl. Discov. 2020, 10, e1365. [Google Scholar] [CrossRef]
- Sinigaglia, F.; Carbone, R.; Costa, G.; Zannone, N. A survey on multi-factor authentication for online banking in the wild. Comput. Secur. 2020, 95, 101745. [Google Scholar] [CrossRef]
- Wei, K.; Li, J.; Ding, M.; Ma, C.; Yang, H.H.; Farokhi, F.; Jin, S.; Quek, T.Q.S.; Poor, H.V. Federated learning with differential privacy: Algorithms and performance analysis. IEEE Trans. Inf. Forensics Secur. 2020, 15, 3454–3469. [Google Scholar] [CrossRef]
- Wood, A.; Najarian, K.; Kahrobaei, D. Homomorphic encryption for machine learning in medicine and bioinformatics. ACM Comput. Surv. (CSUR) 2020, 53, 1–35. [Google Scholar] [CrossRef]
- Balapour, A.; Nikkhah, H.R.; Sabherwal, R. Mobile application security: Role of perceived privacy as the predictor of security perceptions. Int. J. Inf. Manag. 2020, 52, 102063. [Google Scholar] [CrossRef]
- Flechais, I.; Mascolo, C.; Sasse, M.A. Integrating security and usability into the requirements and design process. Int. J. Electron. Secur. Digit. Forensics 2007, 1, 12–26. [Google Scholar] [CrossRef]
- Riyadh HT, M.A.; Bhardwaj, D.; Dabrowski, A.; Krombholz, K. Usable Authentication in Virtual Reality: Exploring the Usability of PINs and Gestures. In Applied Cryptography and Network Security, Proceedings of the 22nd International Conference, Abu Dhabi, United Arab Emirates, 5–8 March 2024; Springer Nature: Cham, Switzerland, 2024; pp. 412–431. [Google Scholar]
- Saker, R.; Abu Issa, O. Case Study: Assessing the Security of a ZigBee Smart HomeNetwork. 2024. Available online: https://lnu.diva-portal.org/smash/get/diva2:1837833/FULLTEXT01.pdf (accessed on 5 September 2024).
- Saeed, S. A customer-centric view of E-commerce security and privacy. Appl. Sci. 2023, 13, 1020. [Google Scholar] [CrossRef]
- Saeed, S. Digital Workplaces and Information Security Behavior of Business Employees: An Empirical Study of Saudi Arabia. Sustainability 2023, 15, 6019. [Google Scholar] [CrossRef]
- Saeed, S. Education, Online Presence and Cybersecurity Implications: A Study of Information Security Practices for Computing Students in Saudi Arabia. Sustainability 2023, 15, 9426. [Google Scholar] [CrossRef]
- Chatterjee, S.; Chaudhuri, R.; Vrontis, D.; Hussain, Z. Usage of smartphones for financial transactions: From the consumer privacy perspective. J. Consum. Mark. 2023, 40, 193–208. [Google Scholar] [CrossRef]
- Choi, K.; Wang, Y.; Sparks, B.A.; Choi, S.M. Privacy or security: Does it matter for continued use intention of travel applications? Cornell Hosp. Q. 2023, 64, 267–282. [Google Scholar] [CrossRef]
- Almaiah, M.A.; Al-Otaibi, S.; Shishakly, R.; Hassan, L.; Lutfi, A.; Alrawad, M.; Qatawneh, M.; Alghanam, O.A. Investigating the role of perceived risk, perceived security and perceived trust on smart m-banking application using SEM. Sustainability 2023, 15, 9908. [Google Scholar] [CrossRef]
- Kanaan, A.; AL-Hawamleh, A.; Abulfaraj, A.; Al-Kaseasbeh, H.; Alorfi, A. The effect of quality, security and privacy factors on trust and intention to use e-government services. Int. J. Data Netw. Sci. 2023, 7, 185–198. [Google Scholar] [CrossRef]
- Martínez-Navalón, J.G.; Fernández-Fernández, M.; Alberto, F.P. Does privacy and ease of use influence user trust in digital banking applications in Spain and Portugal? Int. Entrep. Manag. J. 2023, 19, 781–803. [Google Scholar] [CrossRef]
- Bhattacharya, M.; Roy, S.; Chattopadhyay, S.; Das, A.K.; Shetty, S. A comprehensive survey on online social networks security and privacy issues: Threats, machine learning—based solutions, and open challenges. Secur. Priv. 2023, 6, e275. [Google Scholar] [CrossRef]
- Kulyk, O.; Gerber, P.; Marky, K.; Beckmann, C.; Volkamer, M. Does this app respect my privacy? Design and evaluation of information materials supporting privacy-related decisions of smartphone users. In Proceedings of the Workshop on Usable Security (USEC’19), San Diego, CA, USA, 24 February 2019; pp. 1–10. [Google Scholar]
- Lin, W.; Xu, M.; He, J.; Zhang, W. Privacy, security and resilience in mobile healthcare applications. Enterp. Inf. Syst. 2023, 17, 1939896. [Google Scholar] [CrossRef]
- Pattnaik, N.; Li, S.; Nurse, J.R. Perspectives of non-expert users on cyber security and privacy: An analysis of online discussions on twitter. Comput. Secur. 2023, 125, 103008. [Google Scholar] [CrossRef]
- Alsyouf, A.; Lutfi, A.; Alsubahi, N.; Alhazmi, F.N.; Al-Mugheed, K.; Anshasi, R.J.; Alharbi, N.I.; Albugami, M. The use of a technology acceptance model (TAM) to predict patients’ usage of a personal health record system: The role of security, privacy, and usability. Int. J. Environ. Res. Public Health 2023, 20, 1347. [Google Scholar] [CrossRef]
- Du, X.; Yang, Z.; Lin, J.; Cao, Y.; Yang, M. Withdrawing is believing? detecting inconsistencies between withdrawal choices and third-party data collections in mobile apps. In Proceedings of the 2024 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 20–23 May 2024; IEEE Computer Society: Washington, DC, USA, 2024; p. 14. [Google Scholar]
- Valero, C.; Pérez, J.; Solera-Cotanilla, S.; Vega-Barbas, M.; Suarez-Tangil, G.; Alvarez-Campana, M.; López, G. Analysis of security and data control in smart personal assistants from the user’s perspective. Future Gener. Comput. Syst. 2023, 144, 12–23. [Google Scholar] [CrossRef]
- Groen, E.C.; Feth, D.; Polst, S.; Tolsdorf, J.; Wiefling, S.; Iacono, L.L.; Schmitt, H. Achieving usable security and privacy through Human-Centered Design. In Human Factors in Privacy Research. In Human Factors in Privacy Research; Springer International Publishing: Cham, Switzerland, 2023; pp. 83–113. [Google Scholar]
- Aljedaani, B.; Ahmad, A.; Zahedi, M.; Babar, M.A. End-users’ knowledge and perception about security of clinical mobile health apps: A case study with two Saudi Arabian mHealth providers. J. Syst. Softw. 2023, 195, 111519. [Google Scholar] [CrossRef]
- Cerf, S.; Robu, B.; Marchand, N.; Bouchenak, S. Privacy protection control for mobile apps users. Control Eng. Pract. 2023, 134, 105456. [Google Scholar] [CrossRef]
- Chennamaneni, A.; Gupta, B. The privacy protection behaviours of the mobile app users: Exploring the role of neuroticism and protection motivation theory. Behav. Inf. Technol. 2023, 42, 2011–2029. [Google Scholar] [CrossRef]
- Akter, M.; Tabassum, M.; Miazi, N.S.; Alghamdi, L.; Kropczynski, J.; Wisniewski, P.J.; Lipford, H. Evaluating the impact of community oversight for managing mobile privacy and security. In Proceedings of the Nineteenth Symposium on Usable Privacy and Security (SOUPS 2023), Anaheim, CA, USA, 6–8 August 2023; pp. 437–456. [Google Scholar]
- Brunotte, W.; Specht, A.; Chazette, L.; Schneider, K. Privacy explanations–a means to end-user trust. J. Syst. Softw. 2023, 195, 111545. [Google Scholar] [CrossRef]
- Assal, H.; Hurtado, S.; Imran, A.; Chiasson, S. What’s the deal with privacy apps? A comprehensive exploration of user perception and usability. In Proceedings of the 14th International Conference on Mobile and Ubiquitous Multimedia, Linz, Austria, 30 November 2015–2 December 2015; pp. 25–36. [Google Scholar]
- Feth, D.; Maier, A.; Polst, S. A user-centered model for usable security and privacy. In Human Aspects of Information Security, Privacy and Trust, Proceedings of the 5th International Conference, HAS 2017, Held as Part of HCI International 2017, Vancouver, BC, Canada, 9–14 July 2017; Proceedings 5; Springer International Publishing: Cham, Switzerland, 2017; pp. 74–89. [Google Scholar]
- Liu, B.; Lin, J.; Sadeh, N. Reconciling mobile app privacy and usability on smartphones: Could user privacy profiles help? In Proceedings of the 23rd International Conference on World Wide Web, Seoul, Republic of Korea, 7–11 April 2014; pp. 201–212. [Google Scholar]
- Wu, D.; Moody, G.D.; Zhang, J.; Lowry, P.B. Effects of the design of mobile security notifications and mobile app usability on users’ security perceptions and continued use intention. Inf. Manag. 2020, 57, 103235. [Google Scholar] [CrossRef]
- Acar, Y.; Fahl, S.; Mazurek, M.L. You are not your developer, either: A research agenda for usable security and privacy research beyond end users. In Proceedings of the 2016 IEEE Cybersecurity Development (SecDev), Boston, MA, USA, 3–4 November 2016; pp. 3–8. [Google Scholar]
- Di Nocera, F.; Tempestini, G.; Orsini, M. Usable Security: A Systematic Literature Review. Information 2023, 14, 641. [Google Scholar] [CrossRef]
- Pattan, N.; Madamanchi, D. Study of usability of security and privacy in context aware mobile applications. In Mobile Computing, Applications, and Services, Proceedings of the First International ICST Conference, MobiCASE 2009, San Diego, CA, USA, 26–29 October 2009; Revised Selected Papers 1; Springer: Berlin/Heidelberg, Germany, 2009; pp. 326–330. [Google Scholar]
- Christin, D.; Engelmann, F.; Hollick, M. Usable privacy for mobile sensing applications. In Information Security Theory and Practice. Securing the Internet of Things, Proceedings of the 8th IFIP WG 11.2 International Workshop, WISTP 2014, Heraklion, Greece, 2–30 July 2014; Proceedings 8; Springer: Berlin/Heidelberg, Germany, 2014; pp. 92–107. [Google Scholar]
- Gutfleisch, M.; Klemmer, J.H.; Busch, N.; Acar, Y.; Sasse, M.A.; Fahl, S. How does usable security (not) end up in software products? Results from a qualitative interview study. In Proceedings of the 2022 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 22–26 May 2022; IEEE: New York, NY, USA, 2022; pp. 893–910. [Google Scholar]
- Mathis, F.; Vaniea, K.; Khamis, M. Prototyping usable privacy and security systems: Insights from experts. Int. J. Hum. Comput. Interact. 2022, 38, 468–490. [Google Scholar] [CrossRef]
- Chin, E.; Felt, A.P.; Sekar, V.; Wagner, D. Measuring user confidence in smartphone security and privacy. In Proceedings of the Eighth Symposium on Usable Privacy and Security, Washington, DC, USA, 11–13 July 2012; pp. 1–16. [Google Scholar]
- Zhang, Z. On the usability (in) security of in-app browsing interfaces in mobile apps. In Proceedings of the 24th International Symposium on Research in Attacks, Intrusions and Defenses, San Sebastian, Spain, 6–8 October 2021; pp. 386–398. [Google Scholar]
- Reuter, C.; Iacono, L.L.; Benlian, A. A quarter century of usable security and privacy research: Transparency, tailorability, and the road ahead. Behav. Inf. Technol. 2022, 41, 2035–2048. [Google Scholar] [CrossRef]
- Musa, H.S.; Krichen, M.; Altun, A.A.; Ammi, M. Survey on blockchain-based data storage security for Android mobile applications. Sensors 2023, 23, 8749. [Google Scholar] [CrossRef]
- Khan, H.; Hengartner, U.; Vogel, D. Usability and security perceptions of implicit authentication: Convenient, secure, sometimes annoying. In Proceedings of the Eleventh Symposium on Usable Privacy and Security (SOUPS 2015), Ottawa, Canada, 22–24 July 2015; pp. 225–239. [Google Scholar]
- Liu, R.; Cao, J.; Zhang, K.; Gao, W.; Liang, J.; Yang, L. When privacy meets usability: Unobtrusive privacy permission recommendation system for mobile apps based on crowdsourcing. IEEE Trans. Serv. Comput. 2016, 11, 864–878. [Google Scholar] [CrossRef]
- Frik, A.; Kim, J.; Sanchez, J.R.; Ma, J. Users’ expectations about and use of smartphone privacy and security settings. In Proceedings of the 2022 CHI Conference on Human Factors in Computing Systems, New Orleans, LA, USA, 29 April 2022–5 May 2022; pp. 1–24. [Google Scholar]
- Alt, F.; von Zezschwitz, E. Emerging trends in usable security and privacy. I-COM 2019, 18, 189–195. [Google Scholar] [CrossRef]
- Ferreira, D.; Kostakos, V.; Beresford, A.R.; Lindqvist, J.; Dey, A.K. Securacy: An empirical investigation of Android applications’ network usage, privacy and security. In Proceedings of the 8th ACM Conference on Security & Privacy in Wireless and Mobile Networks, New York, NY, USA, 22–26 June 2015; pp. 1–11. [Google Scholar]
- Chen, Y.; Zha, M.; Zhang, N.; Xu, D.; Zhao, Q.; Feng, X.; Yuan, K.; Suya, F.; Tian, Y.; Chen, K.; et al. Demystifying hidden privacy settings in mobile apps. In Proceedings of the 2019 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 19–23 May 2019; IEEE: New York, NY, USA, 2019; pp. 570–586. [Google Scholar]
- Lin, J.; Amini, S.; Hong, J.I.; Sadeh, N.; Lindqvist, J.; Zhang, J. Expectation and purpose: Understanding users’ mental models of mobile app privacy through crowdsourcing. In Proceedings of the 2012 ACM Conference on Ubiquitous Computing, Pittsburgh, PA, USA, 5–8 September 2012; pp. 501–510. [Google Scholar]
- Nema, P.; Anthonysamy, P.; Taft, N.; Peddinti, S.T. Analyzing user perspectives on mobile app privacy at scale. In Proceedings of the 44th International Conference on Software Engineering, Pittsburgh, PA, USA, 21–29 May 2022; pp. 112–124. [Google Scholar]
- Jacobs, D.; McDaniel, T. A survey of user experience in usable security and privacy research. In HCI for Cybersecurity, Privacy and Trust, Proceedings of the 4th International Conference, HCI-CPT 2022, Held as Part of the 24th HCI International Conference, HCII 2022, Virtual Event, 1–26 July 2022; Springer International Publishing: Cham, Switzerland; pp. 154–172.
- Ismail, Q.; Ahmed, T.; Caine, K.; Kapadia, A.; Reiter, M. To permit or not to permit, that is the usability question: Crowdsourcing mobile apps’ privacy permission settings. Proc. Priv. Enhancing Technol. 2017, 4, 119–137. [Google Scholar] [CrossRef]
- Martin, K.; Shilton, K. Putting mobile application privacy in context: An empirical study of user privacy expectations for mobile devices. Inf. Soc. 2016, 32, 200–216. [Google Scholar] [CrossRef]
- Holton, E.F.; Burnett, M.F. Research in Organizations. Foundations and Methods of Inquiry. The Basics of Quantitative Research. 2005, pp. 29–44. Available online: http://www.kharazmi-statistics.ir/Uploads/Public/book/research%20in%20organization.pdf (accessed on 9 November 2024).
- Lietz, P. Research into questionnaire design: A summary of the literature. Int. J. Mark. Res. 2010, 52, 249–272. [Google Scholar] [CrossRef]
- Nikkhah, H.R.; Grover, V.; Sabherwal, R. Post hoc security and privacy concerns in mobile apps: The moderating roles of mobile apps’ features and providers. Inf. Comput. Secur. 2024, 32, 1–37. [Google Scholar] [CrossRef]
- Available online: https://www.smartpls.com/ (accessed on 9 November 2024).
- Hair, J.F., Jr.; Sarstedt, M.; Hopkins, L.; Kuppelwieser, V.G. Partial least squares structural equation modeling (PLS-SEM): An emerging tool in business research. Eur. Bus. Rev. 2014, 26, 106–121. [Google Scholar] [CrossRef]
- Rahim, M.A.; Magner, N.R. Confirmatory factor analysis of the styles of handling interpersonal conflict: First-order factor model and its invariance across groups. J. Appl. Psychol. 1995, 80, 122. [Google Scholar] [CrossRef]
- Henseler, J.; Ringle, C.M.; Sarstedt, M. A new criterion for assessing discriminant validity in variance-based structural equation modeling. J. Acad. Mark. Sci. 2015, 43, 115–135. [Google Scholar] [CrossRef]
- Hair, J.F.; Hult GT, M.; Ringle, C.M.; Sarstedt, M. A Primer on Partial Least Squares Structural Equation Modeling (PLS-SEM), 3rd ed.; Sage: Thousand Oakes, CA, USA, 2022. [Google Scholar]
- Saeed, S.; Bajwa, I.S.; Mahmood, Z. Human Factors in Software Development and Design; IGI Global: Hershey, PA, USA, 2015. [Google Scholar]
- Saeed, S.; Bamarouf, Y.A.; Ramayah, T.; Iqbal, S.Z. Design Solutions for User-Centric Information Systems; IGI Global: Hershey, PA, USA, 2016. [Google Scholar]
- Gull, H.; Saeed, S.; Iqbal, S.Z.; Bamarouf, Y.A.; Alqahtani, M.A.; Alabbad, D.A.; Saqib, M.; Al Qahtani, S.H.; Alamer, A. An empirical study of mobile commerce and customers security perception in Saudi Arabia. Electronics 2022, 11, 293. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).