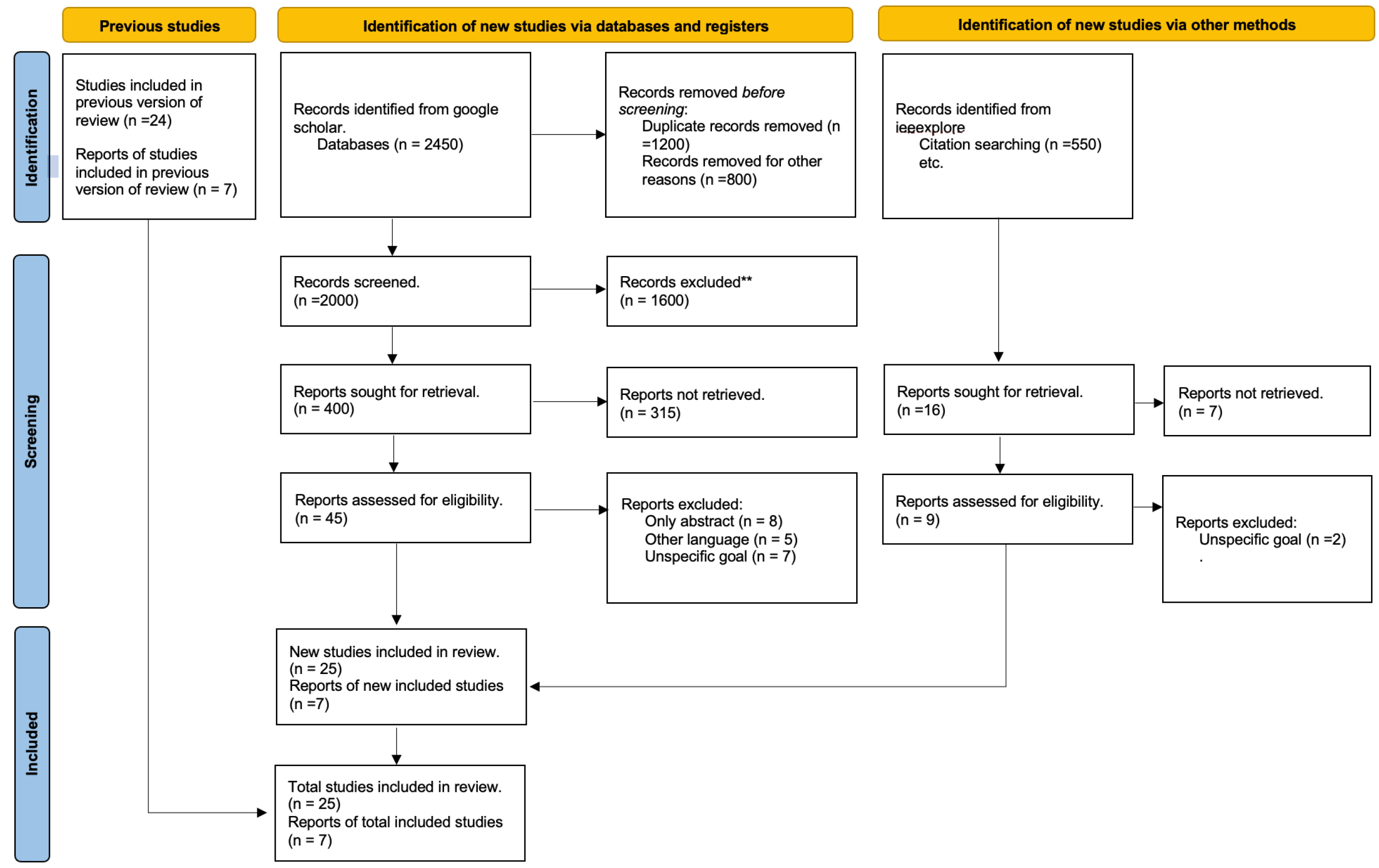
Integrating the lightweight blockchain and fog computing in drone operations is a burgeoning area of research characterized by a diverse range of studies that explore various aspects of this technological convergence. In this Literature Survey section, we delve into the findings and insights gleaned from the selected 32 papers, which were meticulously chosen through the PRISMA framework. This survey aims to dissect the existing body of knowledge, highlighting key advancements, identifying prevailing challenges, and uncovering potential opportunities within this domain. It provides a critical examination of the current state of research, offering a comprehensive synthesis of how lightweight blockchains and fog computing can collaboratively enhance the security and efficiency of drone operations. The following subsections will present an in-depth analysis of the selected studies, categorizing them based on their primary focus areas: technological implementation, security enhancements, efficiency improvements, and practical applications in drone operations.
3.1. Key Research on Blockchain Applications and Innovations
Blockchain technology has emerged as a critical component in the evolution of drone operations, offering solutions to some of the most pressing challenges in this field. The advantages of the blockchain are manifold, encompassing enhanced security, data integrity, and operational efficiency. In the following discussion, we explore these benefits in greater detail, beginning with an overview of the transformative potential of blockchains for drones. In the context of drone operations, blockchain technology offers unparalleled advantages in securing communication channels, data storage, and operational protocols. For instance, the development of lightweight blockchain protocols, as discussed by Finlow-Bates, can significantly reduce the computational overhead by up to 40%, a critical factor for the limited computational resources available on drones [
5]. Moreover, the blockchain’s decentralized nature ensures that data related to drone flight paths, mission-critical decisions, and video feeds are immutable and protected against unauthorized alterations. The versatility of the blockchain, highlighted by Khor et al., extends beyond traditional applications to secure the vast networks of drones, facilitating secure, tamper-proof logging of drone operations and maintenance records, and ensuring the integrity of data collected during surveillance or inspection missions. This secure, decentralized ledger system is paramount for military and emergency response drones, where data integrity and security are non-negotiable.
Finlow-Bates’s, ref. [
5], approach represented an entirely new protocol, which aimed to improve security and efficiency in blockchain systems while highlighting the tactical incorporation of smart contracts. This protocol starts with an initialization phase for setting up system parameters followed by the generation of cryptographically signed transactions. These transactions go through a strict consensus mechanism to guarantee that only legitimate and validated transactions are allowed into the blockchain. Moreover, the protocol innovatively aggregates transactions, thus optimizing data storage and improving processing speed. Therefore, the study showed an improvement in performance by up to 40% for computational overhead more than traditional methods. This improvement is highly important for applications in resource-limited conditions, including IoT devices. It also investigates real-life implementations of lightweight blockchains, which can benefit people in various fields such as supply chain control and healthcare. Worth noting is that the team used advanced cryptographic techniques to protect data integrity, ensuring that keeping processes streamlined did not compromise security core principles inherent in blockchain technology.
Khor et al. [
6] underscored the vast applicability of the blockchain beyond its conventional use in cryptocurrencies, emphasizing its transformative potential in sectors such as healthcare, supply chain management, and public record keeping. However, the study also shed light on notable security challenges, including threats like the 51% attack, which could compromise the decentralized system’s integrity. To counteract these threats, the authors advocated for integrating advanced cryptographic techniques and continuously updating blockchain protocols. Additionally, the research highlighted the pressing need for regulatory frameworks to guide blockchain technology’s ethical and secure implementation in various domains. The authors concluded with an optimistic outlook on the future of blockchains, foreseeing the rise of hybrid systems that combine the strengths of both public and private blockchains.
Michailidis et al. [
7] highlighted the potential of AI-based predictive analysis to enhance blockchain operations with a specific focus on transaction validations. Apart from performing tasks, the AI’s ability to enhance security is also highlighted by its capability of threat detection and mitigation in real time. While the fusion holds out promises of simplified consensus protocols and resource efficiency, the authors warn about potential issues such as difficulties related to the integration of AI algorithms within blockchain frameworks or even that training models effectively would necessarily require substantial datasets.
Andola et al. [
8] presented a blockchain framework for the Internet of Drones (IoD), aiming at better authentication and anonymity. They suggest four ways to conceal drone identities during blockchain communication using non-interactive zero-knowledge proof (NIZKP) with bilinear maps. The study in particular highlights the untraceability of identities and protection against certain weaknesses such as malleability attacks.
Rupa, C et al. [
9] presented BCT-based VC devices such as UAVs, drones, and the IoT that serve as an approach to enhance security at the data protection level. Implementing this in an Ethereum-based public blockchain, with Pentatope-based elliptic curve cryptography and SHA for privacy, the proposed design stores data within a virtual vehicle monitoring system. It adopts the Ganache platform for BCT, which guarantees data security. Although it proves effective and secure, there are still several issues associated with the approach including integration difficulties, risks concerning signal data safety, a high-cost level connected to computations, as well as testing problems when working with several devices. Future implementations are wide testing and in other areas of the IoT.
Gupta, R et al. [
10] suggested distributed frameworks for drone monitoring of areas such as healthcare, segment defense, and smart cities with features like improved security and data processing. The challenges identified at this point include data privacy issues such as the public Ethereum blockchain, computational complexity, energy inefficiency, processing delays on UAVs, and a lack of standardization; furthermore, quantum computing poses potential threats. This paper focuses on the issues that should be addressed in future research, especially those related to data privacy toward meeting its challenges of computational reduction energy efficiency, UAV processing improvement, blockchain standardization via proper technologies, and finally quantum-secure network design.
Aggarwal, S et al. [
11] suggested a blockchain-based model for secure data diffusion on the Internet of Drones (IoD) in 2019. The model is made up of three layers: user, infrastructure, and IoD; it uses a distributed network based on the Ethereum technology for checking verifications. An algorithm to select a forger node was also proposed as an approach to the creation and validation of blocks. Even though the authors have identified some potential system weaknesses including spoofing and denying-services attacks, they claimed their model is credible, as well as scalable for data propagation in an IoD environment. Future work may include fine-tuning the model, security improvements, and investigating other blockchain technologies.
Alkadi, R et al. [
12] investigated the application of blockchain technology in Unmanned Aerial Vehicle (UAV) networks. They point out the flaws including low power supply, a lack of mediating third parties, and compatibility problems between different blockchain systems. The authors suggest further steps for the development of homogeneous solutions, simulation tool creation, blockchain enhancements in interconnectivity, and addressing UAV application’s multiplicity challenges.
Javed et al. [
13] discussed the current security issues arising from developments in the IoD domain. As drones present obvious vulnerabilities, in particular, the fact that these systems use unencrypted wireless communication and enjoy only rather limited computational means, potential threats like GPS spoofing, drone hijacking, or just man-in-the-middle attacks are highlighted in this paper. Javed et al. proposed a new authentication scheme that combines blockchain technology using Hyperelliptic Curve Cryptography (HECC). This innovative approach proposes an implementation of blockchains as a Certificate Authority (CA), obviating the necessity for well-known CAs or Trusted Third Parties (TTPs).
Mershada et al. [
14] delved into the challenges and solutions of integrating blockchain technology within resource-constrained devices commonly found in applications like smart homes and the Internet of Vehicles. Recognizing the inherent security benefits of blockchains, such as immutability and distributed consensus, the paper underscores the difficulties of its implementation due to the resource-intensive nature of traditional blockchain systems. The study presents a comprehensive taxonomy of “lightweight” blockchain solutions tailored for these constrained networks to address this. The authors categorize solutions into five pivotal areas: blockchain architecture, device authentication, cryptography models, consensus algorithms, and storage methods. Through this taxonomy, Mershada et al. highlight existing gaps and provide direction for future research, aiming to foster the development of a holistic lightweight blockchain system suitable for networks with limited resources.
The integration of blockchain technology with drone systems presents a myriad of opportunities and challenges. On the one hand, the blockchain’s inherent security attributes such as immutability, distributed consensus, and resilience against cyber-attacks make it a compelling solution for bolstering the security of drone communication and operations. On the other hand, the resource-intensive nature of traditional blockchain systems can pose challenges, especially when implemented on constrained devices. Innovative approaches, such as lightweight blockchain solutions, have been put out to deal with these issues, attempting to balance security and effectiveness.
Table 1 Summary of Key Research on Blockchain Applications and Innovations, provides a comprehensive overview of the advancements and innovations in this space, highlighting efforts to overcome these challenges. As the field evolves, continued research and collaboration between blockchain and drone experts will be crucial to unlock the full potential of these combined technologies.
3.3. Key Research on Fog Computing Applications and Innovations
Fog computing, being at the forefront of edge computing technologies, has garnered significant attention from the research community. Various studies have explored its potential, applications, challenges, and innovations. Here is a summary of fundamental research studies in this domain.
Ometov et al. [
16] took a deep dive into the safety issues that come with cloud, edge, and fog computing. They saw that these tech areas create a special mix of ways to handle data and each has its build and power. Even though being different can be good, it can also make things risky, especially when keeping data safe and private. The work they performed pointed out the key dangers and showed how each area is unlike the others. Because more people worry about keeping their data safe and to themselves, the authors shared some smart ways to deal with these risks as computing keeps changing.
Aazam et al.’s [
17] paper focuses on integrating fog computing and cloud computing to improve the efficiency of IoT systems. It aims to address the limitations of cloud-only and edge-only solutions in the IoT by proposing a fog-assisted IoT framework.
Hou et al. [
15] explained the complexities of ensuring latency and reliability in drone swarms. Much of the paper focuses on the reliability model for drone operations. The authors consider various disturbances that drone swarms might encounter during their operations. They draw upon established reliability models, suggesting that drones and communication link failures follow the Poisson process. The paper explores the intricate mathematical models and equations to quantify and ensure the reliability of drone operations.
In the context of the developing IoT landscape, Haouari et al. [
18] underline the importance of fog computing. There is an urgent need for low-latency solutions because real-time applications are necessary and smart gadgets are quickly becoming commonplace due to the quick spread of smart devices and the requirement for real-time applications. Due to its centralized nature, traditional cloud computing often needs help in meeting these demands. The authors introduce fog computing as a decentralized approach, bringing computational resources closer to end-users and devices. This paper comprehensively explores fog computing, its potential advantages, applications in real-world scenarios, and the challenges it aims to address.
Ahanger et al.’s [
19] research explores the evolving landscape of the Internet of Things (IoT) and its intersection with fog computing. As the IoT paradigm transforms the technological world, leading to increased interconnectivity of objects and data exchange, a challenge emerges due to the resource constraints of IoT devices. To address this, the authors introduce the concept of edge or fog computing. This decentralized approach is designed to aid IoT devices’ inefficient data handling and delivery. The authors emphasize that fog computing is not replacing centralized cloud systems but rather an enhancement, supplementing its capabilities.
Brogi et al. [
20] explored the realm of fog computing, emphasizing the placement of applications within the fog framework. The goal is to expand cloud capabilities to the IoT to improve service quality and support applications that require low latency. The study offers a thorough analysis of current techniques, offering an overview of current algorithms, open-source prototypes, and test use cases. Additionally, it classifies the literature based on the characteristics of applications and the fog infrastructure, highlighting constraints and optimization metrics. The work concludes by pinpointing open challenges in the domain of application placement in fog computing.
Xu jie Li et al. [
21] discussed the complexities of task offloading within UAV-enabled fog computing networks. As smart devices proliferate and 5G communication evolves, the urgency for efficient task-offloading mechanisms in such networks becomes paramount. The research underscores the challenge as a combinatorial optimization problem, introducing a novel offloading scheme anchored on the fireworks algorithm. As the findings suggest, this approach notably outperforms traditional methods like genetic algorithms in minimizing task delays and optimizing data transmission rates. Such advancements are pivotal in enhancing the operational efficiency of fog computing networks, especially in multi-task scenarios.
Kalatzis et al. [
3] addressed the challenges and solutions related to UAV-enabled IoT systems. It presents a distributed agent-based layered architecture designed to enable UAV-based fire detection, leveraging the capabilities of the IoT ecosystem. The focus is on efficiently consuming UAV processing, energy, and communication resources to ensure timely and accurate fire incident detection within surveilled areas. A vital feature of the proposed solution is the establishment of low-latency access to servers at the network’s edge, allowing resource-constrained UAVs and their sensors to offload energy-consuming tasks selectively.
Aazam et al. [
22] emphasized the importance of offloading tasks from devices that might be computationally constrained. Offloading refers to outsourcing tasks to another entity, especially when devices cannot execute specific intelligent tasks, such as those required for smart healthcare or virtual reality. The authors present a taxonomy of offloading, highlighting various criteria, including excessive computation, latency requirements, load balancing, and data management. Furthermore, they discuss several middleware technologies pivotal for the IoT, such as Cloudlet, Mobile Edge Computing (MEC), and Nano Datacenters. These technologies facilitate offloading by providing computational resources closer to the end devices. The paper underscores the rapid advancements in communication technologies that have paved the way for efficient offloading in fog computing.
Abdali et al. [
23] discussed how fast the IoT is growing and why it leans on cloud computing. But, they see problems with using only cloud computing for the IoT, like delays and too much data. They say fog computing (FC) could help. FC works between the cloud and IoT, performing tasks at the edge of the network. This helps sort out the issues with just using cloud computing. They look closely at fog computing, showing its setup, which includes the cloud service layer, fog layer, and edge layer. They highlight that FC is like a smart setup put at the edge of the network to help with quick data handling, cut down delays, and make the IoT work better.
Table 2: Summary of Key Research on Fog Computing Applications and Innovations, presents a detailed overview of the recent advancements and innovative uses of fog computing technology. Among the innovative applications of fog computing, its integration into drone operations stands out as a transformative approach to enhancing operational efficiency and data processing capabilities. Fog computing’s edge processing facilitates real-time data analysis directly from drones, offering significant advantages in various scenarios.
3.3.1. Case Study on Environmental Monitoring
One notable application involves environmental monitoring, where drones equipped with sensors collect vast amounts of data on air quality, temperature, or vegetation. By leveraging fog computing, these data can be processed and analyzed almost instantaneously at the edge. This immediate analysis allows for quick action in response to environmental changes or emergencies, significantly reducing the time from data collection to decision-making.
3.3.2. Support for Autonomous Drone Navigation
In areas with limited or no connectivity, fog computing plays a crucial role in supporting autonomous drone navigation. By processing data locally, drones can make real-time navigational decisions, navigate complex environments, and avoid obstacles without relying on distant cloud servers. This capability is vital for search and rescue missions in remote areas, where quick, autonomous decision-making can save lives.
3.3.3. Fog-Assisted IoT Framework
A study by Aazam et al. proposes a fog-assisted IoT framework that exemplifies how fog computing can optimize drone operations. By reducing the reliance on centralized cloud servers, this framework ensures that drones can operate more efficiently, with lower latency and improved data processing speed. Such frameworks highlight the potential of fog computing to revolutionize drone operations, making them more responsive, reliable, and capable of handling complex tasks in real time [
22].
These case studies illuminate the practical benefits and challenges of integrating fog computing into drone operations. The environmental monitoring example underscores fog computing’s capacity to facilitate immediate data processing and action, essential for timely environmental management and disaster response. Similarly, the autonomous navigation case study reveals how fog computing supports drones’ operational independence and decision-making in connectivity-limited scenarios. These real-world applications not only validate the theoretical potential of fog computing in enhancing drone efficiency and security but also open avenues for further research and development. Future studies should explore innovative fog computing architectures, algorithms, and security protocols to address the evolving demands of drone technology. The integration of fog computing and drones represents a promising frontier for research, offering significant opportunities to revolutionize drone operations across various sectors.
3.4. Lightweight Blockchain Framework with Fog Computing
In the dynamic landscape of the IoT, secure, scalable, and efficient frameworks are paramount. The integration of lightweight blockchain frameworks and fog computing has garnered significant attention in recent years as a potential solution to the challenges faced by the IoT. Exploring the related work in this domain offers insights into the current state of research and sheds light on the advancements, gaps, and future directions. This section delves into a critical analysis and summary of seminal works that investigate the intersection of lightweight blockchain and fog computing technologies. The focus is on understanding how these combined technologies can be leveraged effectively in the context of the Internet of Things (IoT). Through this analysis, we aim to shed light on the advancements, challenges, and potential solutions that emerge when these technologies are synergistically applied to IoT scenarios.
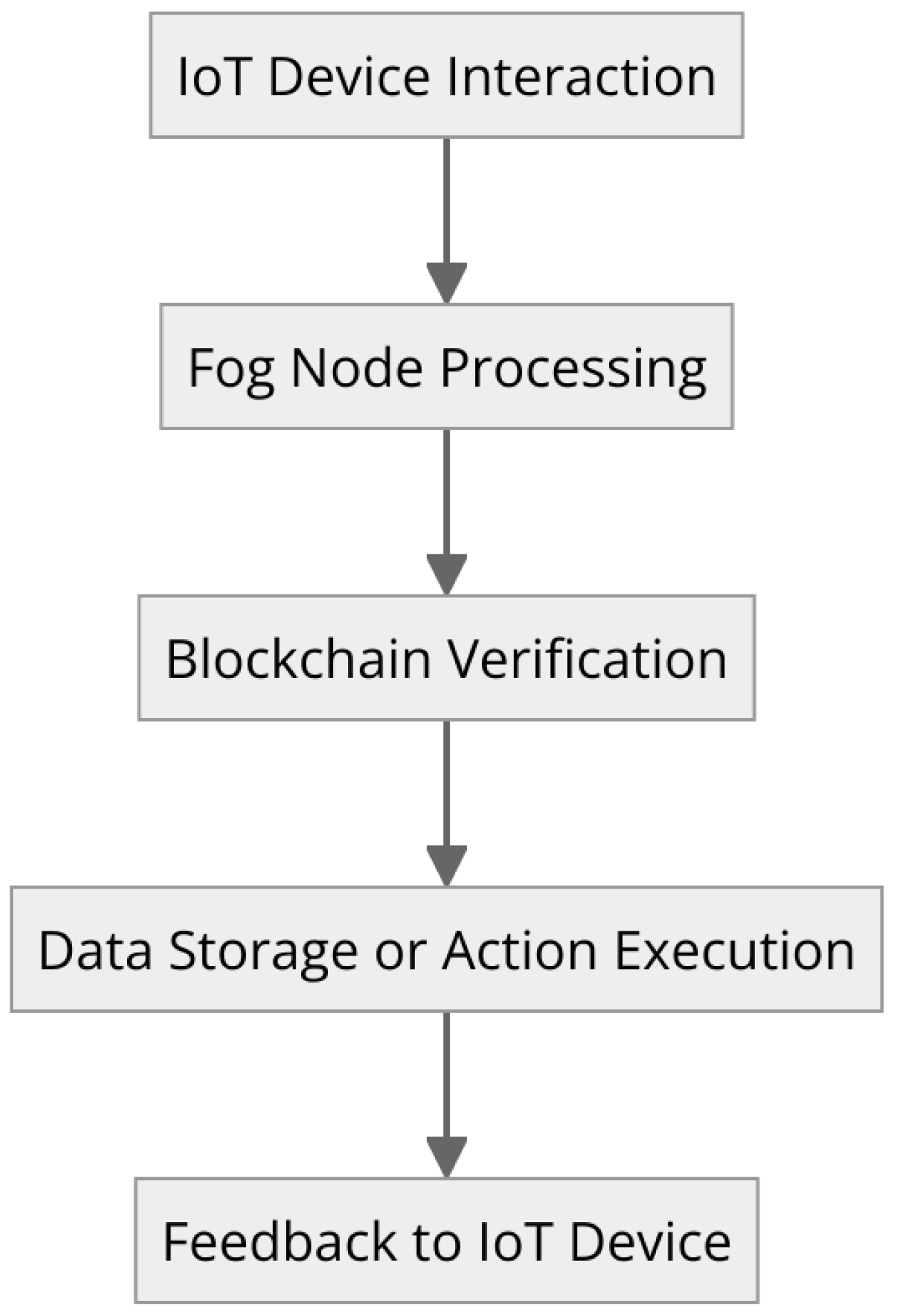
In today’s digital age, the rapidly expanding IoT ecosystem has ushered in many interconnected devices that continuously generate, transmit, and receive data. Amidst this intricate web of communication, maintaining robust cybersecurity becomes paramount to prevent malicious breaches and unauthorized data access. In this context, the amalgamation of the blockchain and fog computing emerges as a beacon of cyber resilience. The blockchain, renowned for its decentralized, tamper-proof, and transparent architecture, fortifies data integrity and combats potential threats, making every transaction traceable and immutable. However, the sheer volume of data and the latency-sensitive nature of many IoT applications can strain traditional blockchain implementations. Enter fog computing—a game-changer that operates as an intermediary layer between IoT devices and central cloud infrastructures. By processing and filtering data closer to its generation point, fog nodes optimize bandwidth usage, slash latency, and provide real-time insights while bolstering security at the edge. This synergy between blockchain’s unparalleled cybersecurity capabilities and fog computing’s localized efficiency crafts a formidable defense mechanism, significantly elevating the security posture of the vast IoT landscape [
24].
Figure 2: Integration workflow of blockchain and fog computing in the IoT, visually illustrates this innovative synergy, offering a clear depiction of how these technologies interlink to enhance IoT security and operational efficiency.
3.5. Key Research on Lightweight Blockchain Framework with Fog Computing
Khan et al. [
25] introduced a pioneering approach to monitoring land surface alterations by integrating drones, fog computing, and blockchain technology. Their blockchain-aware framework emphasizes distributed data management and monitoring, where image-based data captured by drones are transmitted to fog nodes. The primary innovation lies in utilizing a secure hash-encrypted (SH-256) consortium peer-to-peer (P2P) network, ensuring the integrity and security of the data. Furthermore, the authors employ smart contracts to automate the distributed monitoring system, encompassing UAV registration, daily image capture, and transaction updates in immutable storage. This framework is particularly pertinent for observing deforestation and energy generation changes in urban landscapes. Integrating these advanced technologies ensures efficient and automated monitoring and fortifies data management with enhanced security measures.
Alzoubi and Aljaafreh [
26] looked at how blockchains and fog computing are coming together, especially for the Internet of Things, or IoT. They say fog computing is super important. Cisco came up with it in 2012 to help IoT gadgets work with the cloud better, giving quick services when asked. At the same time, they talk about how Blockchain is not in one place; it is spread out. It is known for being safe, strong, and open. They tell us there are different kinds of blockchains: public, private, and group ones, and each works in its own way. They even discuss different blockchain setups, like the first Bitcoin and the flexible Ethereum with all its extra parts. Their review is a big help in understanding how the blockchain and fog can work together and why it is so important for our digital world today.
Eddine et al. [
27] defined the IoV domain, representing a transformative opportunity in both automotive and academic fields. However, the authors emphasize that IoV is fraught with severe security challenges characteristic of open-field IoT deployments. To tackle these weaknesses, the paper presents ”EASBF”—a novel authentication technique that makes use of blockchain technology in fog computing-powered IoV platforms. One of the key aspects of EASBF design is its use of elliptic curve cryptography (ECC) and one-way hash functions to ensure strong information integrity, as well as protection from numerous cyber threats. Moreover, the decentralized nature of blockchain’s architecture is coupled with fog computing efficiency, thereby making EASBF a strong solution to address IoV’s latency and security issues. This research highlights the importance of strong authentication systems in IoV environments and provides a practical design for their implementation via the EASBF scheme.
Shukla et al. [
28] pointed out the emerging security weaknesses, in particular, with the integration of these devices into wider network systems. The study, therefore, proposes a groundbreaking solution that integrates FC and blockchains to offset these challenges. This combined approach seeks to enhance healthcare IoT devices when it comes to security, authentication, and real-time processing. The core of their proposition is focused on the Advanced Signature-Based Encryption (ASE) algorithm aimed at the authentication and verification of everything related to Patient Health Data (PHD), as well as IoT devices. This integrated FC–blockchain model has the potential to improve data security device identification and ensure that there is a smooth transmission of information in an environment for healthcare IoT devices without being centralized.
Kamruzzaman et al. [
29] investigated the transformative role of the blockchain, IoT, and fog computing in advancing healthcare services within the paradigm of smart cities. As urban environments increasingly integrate advanced information and communication technologies, the study underscores the pivotal role of these three technologies as catalysts for smart healthcare initiatives. While the IoT’s expansive incorporation offers vast data collection and exchange capabilities, it grapples with challenges like cost efficiency and data privacy. The blockchain emerges as a solution, providing a decentralized framework that safeguards data integrity and ensures enhanced interoperability. Concurrently, fog computing, bridging the gap between data at network edges and cloud computing, promises reduced latency and heightened efficiency, vital for real-time healthcare applications. As the study suggests, the trio of technologies collectively paves the way for a more secure, efficient, and responsive healthcare infrastructure within the smart city landscape.
Bouachir et al. [
30] examined the transformative potential of blockchains and fog computing in cyberphysical systems, particularly spotlighting their application in smart industries. Integrating these technologies becomes paramount as the IoT landscape burgeons. The study underscores the role of the blockchain as a decentralized, tamper-resistant ledger, emphasizing its capability to bolster data protection and establish decentralized trust within Industrial IoT (IIoT) frameworks. Concurrently, fog and edge computing emerge as pivotal architectures, decentralizing data processes and ensuring real-time data management at the network’s edge. The authors propose an innovative Industrial Cyberphysical System (ICPS) model, amalgamating blockchains and fog/edge computing, aiming to surmount challenges in security, data storage, and quality of service. This exploration accentuates the synergistic potential of these technologies in revolutionizing smart industry operations, offering insights into enhanced data security, efficient real-time processing, and adept data management in the digital era.
Liu et al. [
31] deal with the important issue of securing private information generated by IoT devices especially those transmitted through possibly insecure networks. The paper emphasizes the weaknesses associated with present encryption and access control solutions, especially their vulnerability to single points of breakdown. To eliminate these problems, the authors propose a brand new distributed access control system based on blockchain technology. With the use of fog computing, however, this system can offer enhanced security by processing data closer to their source and, consequently, reducing latency and potential exposure. Additionally, the study includes MLNCML and LSB techniques to encrypt IoT data at edge nodes to secure them during transit as well as storage. The authors also promote attribute-based access control as a dynamic, fine-grained solution for controlling IoT data access. The experiment published in the research validates the efficiency of the proposed mechanism for safeguarding IoT data privacy. This research highlights the importance of combining blockchains with fog computing and sophisticated encryption techniques as a reliable solution for strengthening the IoT when it comes to issues concerning data security.
Muthanna et al. [
32] proposed an integrated framework to fortify the security and reliability of IoT networks. Recognizing the challenges posed by the proliferation of IoT devices, such as security concerns, massive traffic, and energy constraints, the research emphasizes the integration of fog computing, Software-Defined Networking (SDN), and the blockchain. The fog computing paradigm is highlighted for its capability to process and store data closer to their source, thereby reducing latency and bolstering security. With its distinct separation of the forwarding and control planes, SDN offers a dynamic network structure further enhanced by a distributed controller scheme. The blockchain is introduced to ensure a decentralized, trustful environment, which is particularly vital for IoT’s vast, interconnected landscape. The authors also present a data offloading algorithm and a traffic model, aiming for optimal resource utilization and efficient data flow. Through simulations and testbed evaluations, the study validates the potential of this integrated approach in achieving reduced end-to-end latency, heightened security, and efficient resource utilization in IoT networks.
Ngabo et al. [
33] address the security vulnerabilities inherent in the fog computing architecture and the Cloud of Things (CoT) technology, particularly concerning medical data mining. With the rapid advancements in fog computing and CoT, there is a surge in data mining management and artificial intelligence operations. However, this multi-layered model, comprising the edge, fog, and cloud layers, is susceptible to various security threats. Given the vast amount of data generated within this architecture, traditional data storage and security mechanisms need to be revised. The authors propose a public-permissioned blockchain security mechanism to counter these challenges, fortified with the elliptic curve cryptography (ECC) digital signature. This approach ensures an immutable security solution transaction transparency and effectively prevents the unauthorized tampering of patient records within the IoT’s fog layer. By leveraging blockchain technology and ECC digital signatures, the study offers a robust solution to the fog computing model’s challenges of latency, centralization, and scalability. The research underscores the potential of blockchain technology in ensuring data security, especially for sensitive medical data, in the IoT landscape.
Gumaei et al. [
34] presented a framework integrating blockchain technology with drones for enhanced security in a 5G setting. Recognizing the vulnerabilities of drones, especially in data security, the research introduces a combination of a deep recurrent neural network (DRNN) and edge computing for drone identification and flight mode detection using Radio Frequency (RF) signals. The integration of blockchains ensures data integrity and secure transmission. Using the DroneRF dataset for evaluation, the proposed DRNN model demonstrated high accuracy in drone detection and mode identification, highlighting the potential of blockchain and 5G synergy in drone operations.
Kaur et al. [
35] addressed the challenges of data transmission in vehicular networks. Recognizing the limitations of cloud-based models, the authors introduce vehicular fog computing (VFC) to bring computing resources closer to vehicles. To ensure secure communication in VFC, they propose an authentication scheme using blockchain and elliptic curve cryptography (ECC). This approach promises secure, efficient, and reliable data transmission in vehicular networks, making it a significant contribution to the field.
In the evolving landscape of drone technology, the integration of lightweight blockchains and fog computing emerges as a pivotal advancement, promising to significantly enhance the operational efficiency and security of drone operations. This synergy is not just theoretical but has begun to manifest in pilot studies and frameworks that showcase tangible benefits in real-world applications.
As we delve deeper into the potential of merging lightweight blockchain technologies with fog computing for IoT applications, it becomes crucial to survey the landscape of existing research.
Table 3: provides a comprehensive summary of key research contributions in this field. This table encapsulates pivotal studies, highlighting innovative approaches and outcomes that underline the synergy between lightweight blockchain and fog computing. Such a summary not only showcases the breadth of exploration but also serves as a testament to the dynamic advancements being made toward securing and optimizing IoT infrastructures. Reviewing this table will offer readers insight into the foundational and cutting-edge work that lays the groundwork for future developments in integrating blockchain and fog computing technologies.
3.5.1. Theoretical Models and Synergistic Potential
The theoretical model underlying the integration of lightweight blockchains and fog computing hinges on combining the blockchain’s inherent strengths in securing data through its decentralized ledger system with fog computing’s ability to process data at the edge, close to where they are generated. This combination ensures that drone operations benefit from both enhanced data integrity and reduced latency, which are crucial for applications requiring immediate decision-making and action, such as border surveillance and emergency response scenarios.
One of the cornerstone benefits of this integration is the enhanced security provided by blockchain technology. Through its decentralized control, blockchain ensures that data recorded from drone operations, including flight paths, mission-critical decisions, and collected environmental data, remain immutable and secure from tampering. This aspect is vital for maintaining the integrity of sensitive operations and safeguarding against cyber threats.
Concurrently, fog computing addresses the efficiency aspect by significantly reducing the latency involved in data processing. By situating data processing closer to the drone, fog computing facilitates real-time analytics and decision-making, a necessity for drones operating in dynamic or hostile environments where every second counts.
3.5.2. Monitoring Land Surface Changes with Khan et al.’s Framework
A practical illustration of this integration’s potential is seen in the work of Khan et al., who developed a blockchain-aware framework for monitoring land surface changes [
25]. In their study, drones equipped with sensors collect image-based data, which are then securely transmitted to fog nodes for immediate processing. The application of a secure hash-encrypted consortium peer-to-peer (P2P) network, alongside the use of smart contracts, ensure both the integrity and security of the transmitted data. This framework is particularly relevant for environmental monitoring, offering a blueprint for utilizing the combined strengths of lightweight blockchains and fog computing to achieve secure, efficient, and automated monitoring of vast areas.
3.5.3. Implications for Future Drone Operations
The integration of lightweight blockchains and fog computing holds immense promise for the future of drone operations across various domains. Beyond environmental monitoring, this synergy can be adapted for urban planning, agricultural management, and disaster response, among other applications. The key to unlocking this potential lies in further research and development, focusing on refining integration techniques, enhancing the scalability of blockchains within the fog computing architecture, and addressing the challenges of real-time data processing.
In conclusion, the symbiotic relationship between lightweight blockchains and fog computing presents a forward-thinking approach to addressing the twin challenges of security and operational efficiency in drone technology. By harnessing this integration, the future of drone operations can be reimagined, paving the way for drones that are not only smarter and faster but also inherently secure.
3.6. Elevating Drone Operations with Blockchain and Fog Computing
The systematic review of 32 seminal papers has illuminated the burgeoning intersection of blockchain and fog computing technologies within the realm of drone operations. This fusion is poised to redefine the operational paradigms of drones, offering enhanced security, efficiency, and scalability. The reviewed literature not only underscores the theoretical feasibility of this integration but also showcases practical implementations and the tangible benefits therein.
Advancements through Integration
The collective insights from the reviewed papers reveal a consensus on the pivotal role of blockchains in fortifying the security framework for drone operations. By leveraging blockchains, data integrity and privacy are significantly bolstered, thereby mitigating risks associated with data tampering and unauthorized access. Concurrently, fog computing emerges as a critical enabler of real-time data processing capabilities. Its proximity to data sources—drones in motion—dramatically reduces latency, a crucial factor in time-sensitive applications such as emergency response and live surveillance.
A notable advancement highlighted in our review is the development of lightweight blockchain protocols, which are particularly suited for the limited computational resources available on drones. These protocols ensure that the security benefits of blockchain are realized without imposing prohibitive computational demands.
Despite the progress, our review has identified several gaps that warrant further investigation. One such gap is the need for more robust and scalable integration frameworks that can seamlessly accommodate the dynamic nature of drone networks. Current models, while promising, often fall short in addressing the complex interplay between blockchains and fog computing in highly mobile and variable drone environments.
Another critical area for future research is the optimization of consensus mechanisms within blockchains to suit the unique requirements of fog computing architectures. The goal here is to devise mechanisms that balance the need for security and decentralization with the imperative for high-speed data processing and minimal energy consumption.
Environmental sustainability emerges as another significant concern. The energy-intensive nature of conventional blockchain operations, particularly those based on Proof of Work (PoW) consensus algorithms, poses sustainability challenges. Exploring energy-efficient consensus algorithms, such as Proof of Stake (PoS) or Directed Acyclic Graph (DAG) technologies could provide a pathway to more sustainable drone operations.
3.7. Strategies for Latency Minimization in Drone Operations
In the rapidly evolving domain of drone technology, minimizing latency in operational data processing is not merely a performance enhancer but a critical necessity. Latency, the delay before a transfer of data begins following an instruction for its transfer, directly impacts the effectiveness, safety, and responsiveness of drone operations. This is especially true in applications requiring real-time decision-making and action, such as surveillance, emergency response, and military operations, where even minimal delays can have significant consequences.
The integration of fog computing and blockchain technologies presents a promising approach to addressing these latency challenges. Fog computing, with its architecture that brings computational resources closer to the data source (i.e., the drones), significantly reduces the time required for data transmission and processing. This proximity enables real-time data analysis and decision-making directly at the edge of the network, where drones operate, thereby minimizing latency.
Moreover, blockchain technology contributes to this objective by providing a secure and decentralized framework for data transactions. While traditionally not associated with speed due to its computational intensity, lightweight blockchain protocols have been developed specifically for use in environments like fog computing, where efficiency is paramount. These protocols ensure that data integrity and security are maintained without the latency typically associated with blockchain operations.
Together, fog computing and blockchains offer a dual approach to tackling latency: fog computing addresses the physical proximity and immediacy of data processing, while blockchains ensure the rapid, secure transmission of these data across the network. This integration heralds a new era of drone operations, where the challenges of latency are significantly mitigated, enabling drones to perform more complex, sensitive tasks with greater reliability and efficiency.
3.7.1. Real-Time Data Processing Capabilities
The adoption of fog computing significantly amplifies the real-time data processing capabilities essential for drone operations. By situating computational resources in closer proximity to the operational environment, fog computing drastically reduces the latency traditionally encountered in data transmission to centralized cloud services. This architectural advantage facilitates instant data analysis and decision-making, a requisite for drones engaged in time-sensitive missions such as surveillance, search and rescue, and immediate environmental assessment [
36].
The essence of fog computing in enhancing real-time data processing lies in its ability to perform complex computational tasks at or near the data source. This includes data filtering, aggregation, and analysis directly on the edge of the network, where drones operate. Such localized processing eliminates the time delays inherent in sending vast volumes of data back and forth to distant servers, thereby ensuring that drones can react to dynamic environmental changes and make informed decisions promptly.
Moreover, fog computing supports the deployment of advanced machine learning models and algorithms directly onto the drone or nearby edge devices. This capability allows drones to learn from new data in real time, adapt their operational parameters, and execute autonomous decisions based on immediate data insights [
37]. For instance, a drone monitoring forested areas for wildfire detection can instantly analyze images for signs of fire, calculate the potential spread using real-time weather data processed through fog nodes, and communicate alerts without the latency that would hinder a timely response.
In practice, real-time data processing through fog computing has been exemplified in agricultural drones that monitor crop health. These drones utilize near-edge processing to analyze spectral imagery on the fly, identifying areas of stress, disease, or need for irrigation. The immediate processing of such data enables precise, real-time adjustments to agricultural practices, showcasing the pivotal role of fog computing in enhancing the efficiency and responsiveness of drone operations.
By leveraging the decentralized nature of fog computing, drone operations are poised to achieve unprecedented levels of autonomy and operational efficiency, driven by the capacity for real-time data processing. This technological evolution not only broadens the scope of applications for drones but also sets new benchmarks for their performance in critical and everyday tasks alike.
3.7.2. Optimization of Communication Protocols
The optimization of communication protocols plays a critical role in minimizing latency and enhancing the efficiency of drone operations integrated with fog computing and blockchain technologies. By refining how data are transmitted and processed between drones, fog nodes, and blockchain networks, these optimizations ensure faster, more reliable communication essential for real-time drone applications.
One key strategy involves the use of lightweight communication protocols that are specifically designed for the limited bandwidth and power resources characteristic of drone and fog computing environments. These protocols reduce the data payload size and streamline the data transmission process, significantly cutting down the time it takes for messages to travel across the network. For example, the MQTT (Message Queuing Telemetry Transport) protocol, known for its lightweight and efficient messaging system, is widely adopted in IoT and drone communications for its low power consumption and minimal data packet size, making it ideal for real-time applications.
In the context of blockchain integration, the optimization also extends to consensus algorithms, which are fundamental to ensuring data integrity and trust within the network. Traditional blockchain consensus mechanisms like Proof of Work (PoW) are computationally intensive and can introduce delays. As a remedy, more efficient consensus algorithms such as Proof of Stake (PoS) or Practical Byzantine Fault Tolerance (PBFT) are being explored and adapted for fog computing environments. These algorithms offer a balance between security and speed, enabling quicker transaction validations without the extensive computational overhead, thereby reducing latency in blockchain transactions.
Moreover, advancements in communication protocol optimization include the development of adaptive routing algorithms that dynamically select the most efficient data paths between drones and fog nodes. These algorithms take into account factors such as network congestion, node availability, and data priority to optimize the route data takes, further reducing latency and enhancing the overall responsiveness of the system [
38].
An illustrative example of these optimizations in action can be seen in disaster response scenarios, where drones equipped with sensors collect critical data from the affected area. Through optimized communication protocols, these data are swiftly transmitted to nearby fog nodes for immediate analysis, and relevant insights are quickly shared with emergency responders via a blockchain network. The use of efficient consensus algorithms ensures that this crucial information is processed and validated rapidly, allowing for timely decision-making and coordinating response efforts.
In summary, the optimization of communication protocols is pivotal to leveraging the full potential of fog computing and blockchains in drone operations. By facilitating faster, more efficient data exchange and processing, these optimizations are instrumental in advancing drone capabilities, particularly in scenarios requiring real-time or near-real-time responses [
39].