Abstract
In this research article, we propose a new structure namely inverse left almost semigroup (LA-semigroup) by adding confusion in our proposed image encryption scheme along with discrete and continuous chaotic systems in order to complement the diffusion characteristics. The performance analysis was conducted in terms of the correlation analysis, the pixels uniformity analysis, the sensitivity analysis, the information entropy analysis, and pixels difference based measurements. The results show that the proposed algorithm has better information security properties, which can provide strong security and a high performance.
1. Introduction
The existing world demands fast and secure communication. The bandwidth is increasing every day due to third generation, fourth generation and fifth generation technologies. Digital contents can be easily accessed through any geographical remote area because of the ideology of a global village. By advancing the technologies, smart and simple to access information from any remote station creates a massive insecurity of digital information. The security of digital multimedia is one of the vital problems of the information sciences. The widespread broadcasting and distribution of digital information over the internet, especially social media like Facebook and Twitter, have made it important to protect our most important information from theft, illegal copying, handling and sharing. The advancement of digital media technology and other multimedia related technology has made it possible to perform some standard procedures in order to improve the security of our digital images/audio/videos from being utilized criminally over the web.
There are a number of information security techniques that have been designed whose algorithms are based on cryptography, which is one of the most important branch of cryptology that is used to make an encryption scheme to secure information. Classical encryption techniques usually utilize either substitution or permutation to develop a cryptosystem; for instance, mono-alphabetical and polyalphabetic ciphers. The use of only substitution or permutation while developing any encryption scheme is susceptible to different cryptographic attacks. Consequently, the cryptosystems are getting weaker every day due to the advancement of technologies and computational powers of machines. In 1949, Claude Shannon gave the idea of confusion and diffusion, which completely changed the security mechanisms of the digital world. The information theory added a new pillar in information security. After the theory of Claude Shannon, the idea of confusion and diffusion was extensively used, which means substitution and permutation were utilized at a time in modern block ciphers [1,2]. According to Shannon, confusion specifies the connections between the cipher text and the key as much as complex whereas diffusion corresponds to the redundancy in the statistical data of the plaintext used in the statistical data of the cipher text. This master idea fundamentally changed the ideology of modern block and steam ciphers. The ideas of confusion and diffusion were utilized in a number of modern block ciphers namely international data encryption standard (IDEA), data encryption standard (DES), and advanced encryption standard (AES).
Thereafter, different new techniques were designed which use chaos theory, wavelets transform, discrete transforms, optics, DNA sequences and quantum spinning and rotations [3,4,5,6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,33,34]. In recent times, chaos theory has been used in an extensive way for the development of image encryption mechanisms [35,36]. The three fundamental characteristics of chaos that have made it possible to use it in the development of encryption algorithms are sensitive to the initial condition, topological mixing, and dense periodic orbits. These three properties were closely related to cryptography. Due to the cryptographically robust characteristics of chaos, we have utilized the Lorenz chaotic system while designing our novel image encryption technique.
So far, different types of mathematical structures were utilized namely Group, Ring, Galois field and Galois ring for the construction of a substitution box (S-box), which is one of the most important nonlinear components of any modern block ciphers. The thrust of new mathematical structures for the development of encryption techniques is one of the most important areas of research in information security [8,11,12,15]. An algebraic structure equipped with a closed and left invertive binary operation is called a left almost semigroup (abbreviated as LA-semigroup). This notion was made known by Kazim and Naseeruddin in the early 1970s [37]. Mushtaq and Yusuf discussed some important properties in [38]. Such groupoids are also called right modular groupoids or left invertive groupoids or incorrectly as Abel Grassmann’s groupoid [39,40,41]. By successive applications of the left invertive law in an arbitrary LA-semigroup, it can be seen that the medial identity naturally holds in an LA-semigroup. It is important to mention here that every LA-semigroup is always medial but its converse is not true. It is a non-associative and non-commutative structure midway between a groupoid and commutative semigroup.
In order to define the associative powers of elements in an LA-semigroup the identity (ss)s = s(ss) was introduced in Reference [42]. An LA-semigroup with this additional property is called a locally associative LA-semigroup. Some important decompositions of locally associative LA-semigroups were also investigated in References [42,43]. Consider a locally associative LA-semigroup defined by the Table 1.

Table 1.
Locally associative left almost semigroup (LA-semigroup).
Where , substantiates that a locally associative LA-semigroup not need to have associative powers necessarily.
The LA-semigroups, after the evolved from the study of a diverse generalization of groups and semigroups. It has become a separate branch within itself with a considerable number of research results. The reason for its procession is its natural existence in almost all mathematical contexts in which groups and semigroups have been developed.
The study of LA-semigroups has wide applications in the locally associative LA-semigroups, abelian groups, the theory of fuzzy LA-semigroups, ternary semihypergroups, -semihypergroups, neutrosophic LA-semigroups, soft sets and the theory of non-commutative groupoids [42,43,44,45,46,47,48,49]. Here, we propose a new scheme for the encryption of images based on an inverse LA-semigroup and a modified nonlinear chaotic map, which has better confusion and diffusion characteristics that are necessary for a modern substitution-permutation network.
This article comprises of five sections. In Section 2, we introduce fundamentals of a novel structure inverse LA-semigroups. In Section 3, we propose an algorithm for the encryption of images. The efficiency and safety measures for the suggested algorithm are examined in Section 4. The numerical measures are also discussed in Section 4 to examine the response of suggested scheme against differential attacks. Finally, give conclusions in the Section 5.
2. Preliminaries
This section is primarily related to some standard definitions, which will be quite useful in subsequent sections.
Definition 1.
An LA-semigroup is a pairwhereis a non-empty set;satisfiesfor all. One can easily observe that the medial identitynaturally holds in the LA-semigroups. It is important to mention here that every LA-semigroup is always medial but its converse is not true.
Definition 2.
An LA-semigroupsatisfying the left permutable lawis called LA**-semigroup. An LA-semigroup with left identity is always LA**-semigroup and LA**-semigroup naturally satisfies the paramedial identity.
We provide counter examples of three groupoids of order in Table 2, where (i) is a medial groupoid but not an LA-semigroup, (ii) is a left permutable groupoid, which is also paramedial but not an LA-semigroup, (iii) is a left permutable groupoid with left identity but not an LA-semigroup (see Table 2).

Table 2.
Counter Examples.
Definition 3.
An LA-semigroup ( equiped with left identity , that is, for all is LA-monoid. One can notice that left permutable law and paramedial law always hold in an LA-monoid . We also investigate a paramedial groupoid with a left identity is LA**-semigroup. An element for which there exist an element such that , then is called left inverse of . Right inverse for an element in an LA-monoid can also be defined analogously. It is easy to observe that if is the left inverse for an element , that is, . Then . Then . Showing that left and right inverses are unique in an LA-monoid. An LA-monoid, in which each element has its left inverse element is known as LA-group.
Definition 4.
An LA-semigroupsatisfying the weak associative lawis called LA*-semigroup. The identitiesare equivalent in an LA-semigroup.
Definition 5.
LA-group is an LA-monoid in which each element has a unique left multiplicative inverse. LA-monoids are special cases of LA-semigroups whereas LA-groups are special cases of LA-monoid.
Definition 6.
An LA-semigroupis unipotent iffor all. We define a transformationbyfor all.
Proposition 1.
An LA-semigroupis unipotent if and only if, where.
Lemma 1.
Every unipotent left cancellative LA-semigroup is paramedial.
Let ( and be any two LA-semigroups of the same order. A mapping is a homomorphism if it preserves the multiplication, that is, and an anti-homomorphism if it reverts the multiplication that is, . If such mapping is bijective, then it is known as isomorphism and anti-isomorphism respectively. If such a bijection exists, then the groupoids are isomorphic and anti-isomorphic respectively.
For instance, if two LA-semigroups have isomorphic tables, they have the same structural properties. So we say that an isomorphism is an action between two multiplication tables. If we are provided with a permutation of the elements of , we transform the table by permuting the rows according to , then each column, and permuting the values at the end. An anti-isomorphism is an action followed by transposing the resulting table of an isomorphism. The outcome of applying the permutation is given in Table 3 (ii). Table 3 (i) and Table 3 (ii) are isomorphic. If has elements then atmost multiplication tables isomorphic to given LA-semigroup.

Table 3.
A Multiplication table is mapped to another multiplication under permutation (b, d).
Theorem 1.
Letbe an LA-semigroup satisfying paramedical law. Then, one has
- (i)
- is an anti-endomorphism.
- (ii)
- is sub LA-semigroup of.
- (iii)
- is a congruence relation.
Definition 7.
An LA-semigroup, in which for everythere exists a uniquefor whichandis called an inverse LA-semigroup. This notion was made known by Mushtaq and Iqbal in Reference [9]. They proved some interesting facts and a famous Wagner Preston theorem on the representation of inverse LA-semigroups [9]. An inverse LA*-semigroup and inverse LA**-semigroup are defined analogously. Some interesting results are that every LA-group is an inverse LA-semigroup more precisely an inverse LA**-semigroup but the converse is not true [10]. Presentation of a semigroup is a set of generators and relations which completely depicts a particular semigroup of a finite or an infinite semigroup. Ruskuc worked on semigroup presentations in his PhD thesis [11]. Here, we find thatrepresents an inverse LA**-semigroup of order 256 generated by. Here, by an S-box of order, we mean a latin square of sizewhose entries are selected from a set ofdifferent symbols in such a way that there is no repetition in any row and column of the table.
3. Proposed Digital Image Encryption Algorithm
The present section deals with the encryption procedure.
3.1. Image Encryption
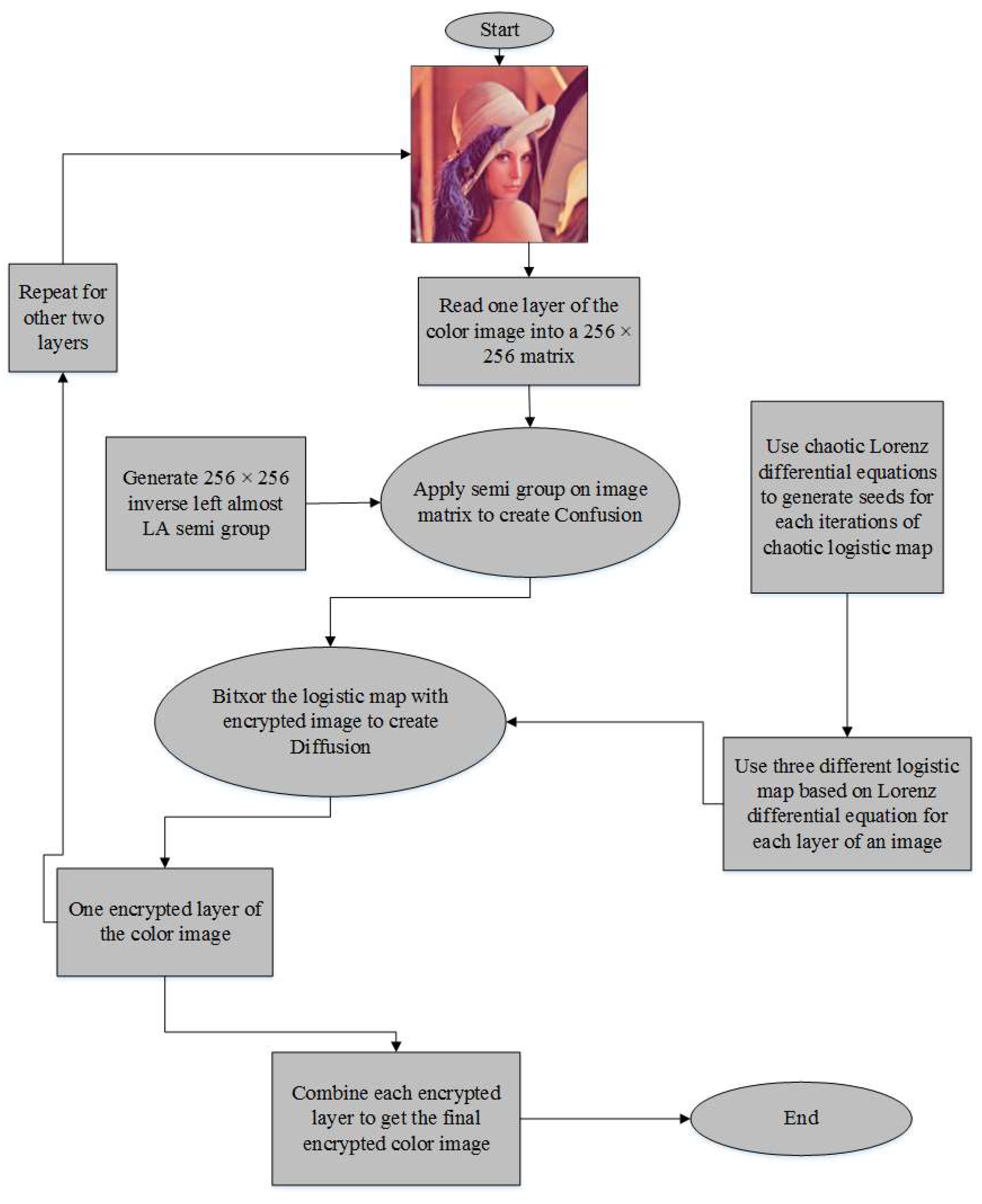
Designed image encryption techniques comprise of confusion and diffusion. As illustrated in Figure 1, the encryption method is based on the steps given below:
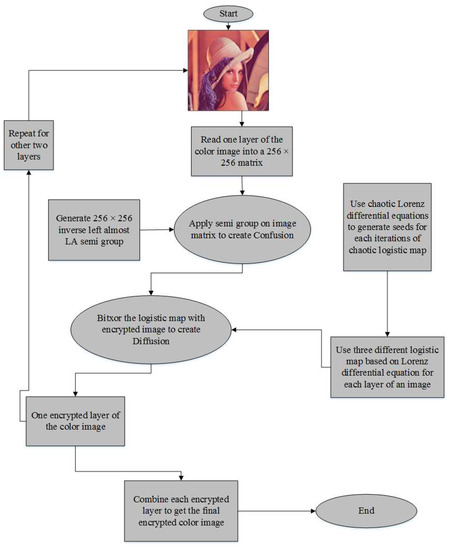
Figure 1.
Proposed encryption algorithm.
Step 1: Take a standard digital color image of size
Step 2: Read the inverse left almost LA-semigroup of order m
Step 3: Apply a substitution transformation by using the LA-semigroup as listed in Step 2, which adds confusion to the proposed algorithm.
Step 4: Generate chaotic sequences using Lorenz chaotic differential equations with a logistic map (seed values for each iteration comes from the Lorenz chaotic differential equation utilized three chaotic logistic maps used seeds from x, y and z directions solutions of Lorenz chaotic differential equations).
Step 5: Apply a bitwise addition under modulo 2, of confused image produced in Step 3 with the chaotic sequences generated in Step 4 for each layer of the digital image that uses x component values for the red layer, y component values from the green layer and z component values of the logistic map for the blue layer of a given image.
Step 6: Apply all of the above steps on each layer of the digital image.
Step 7: Display the encrypted image.
3.2. Image Decryption
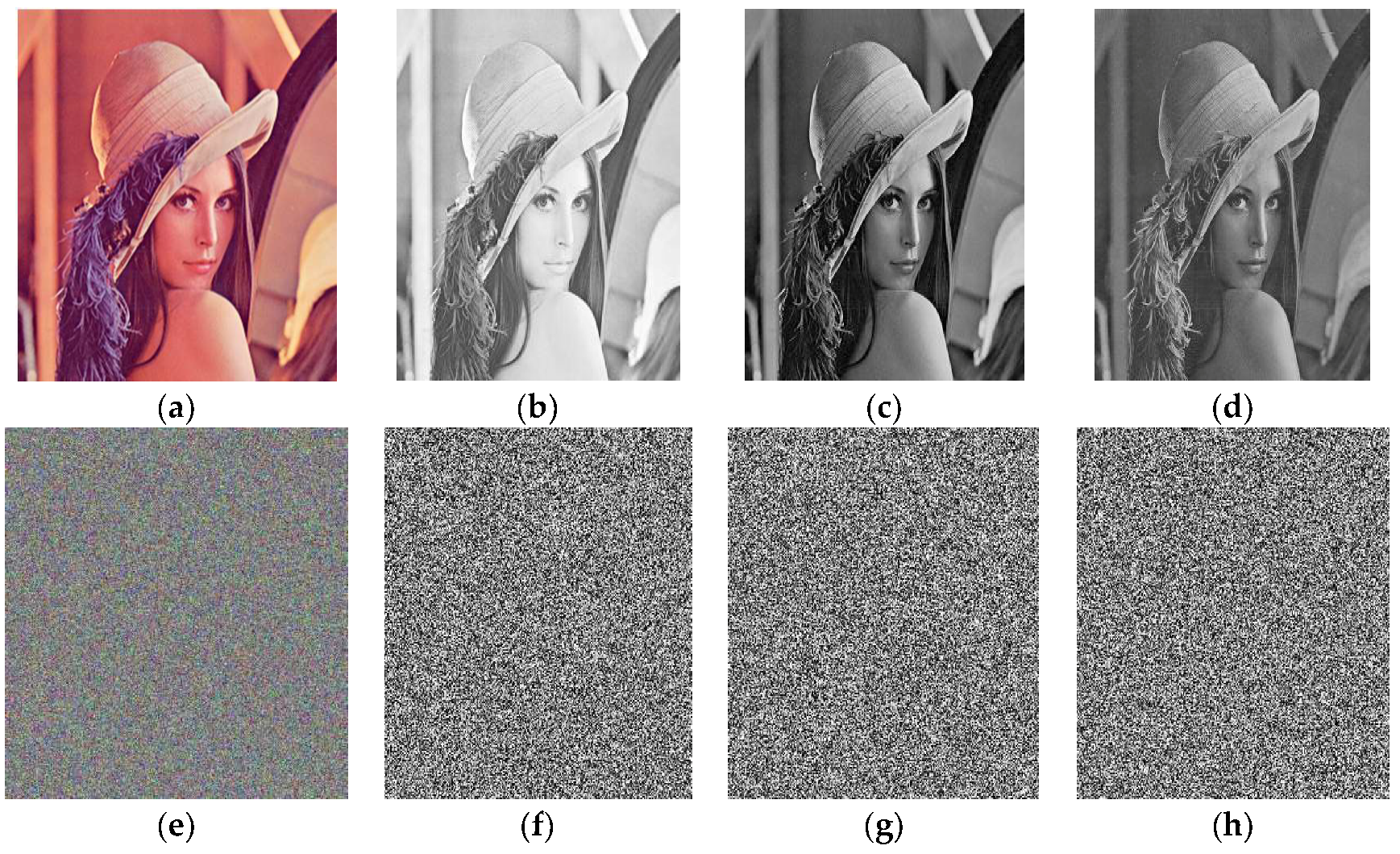
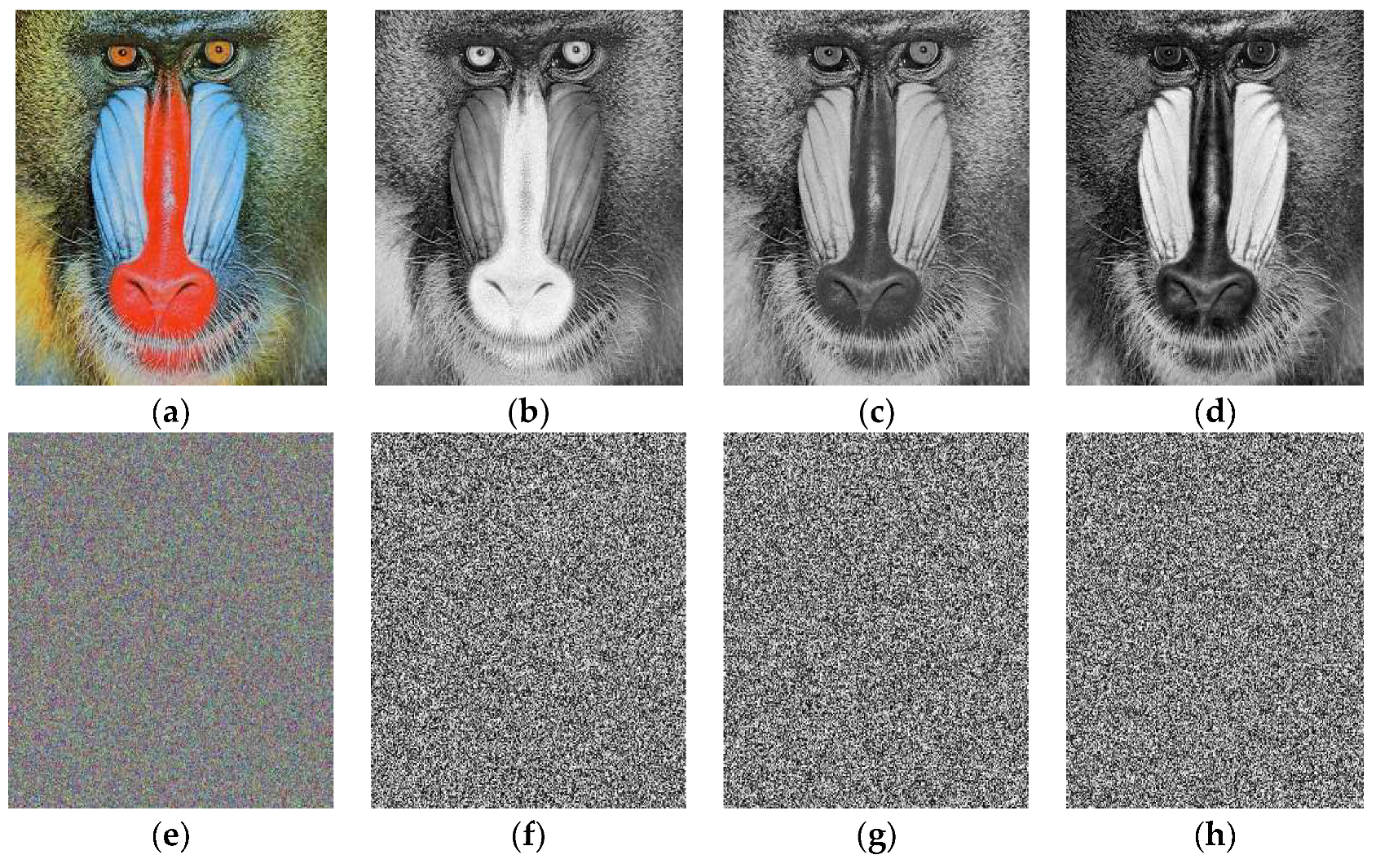
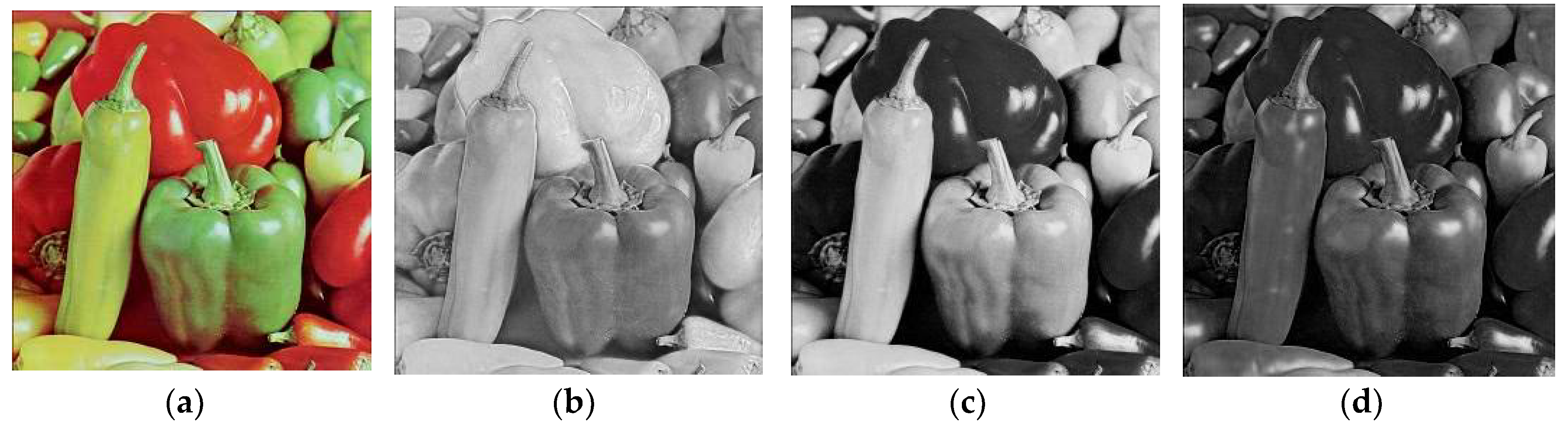
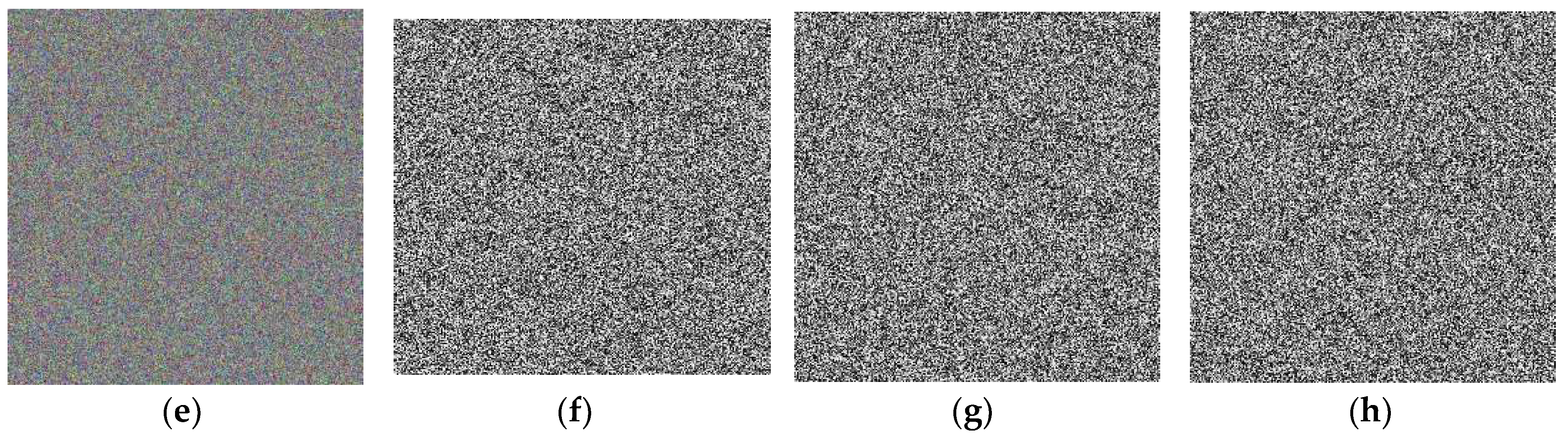
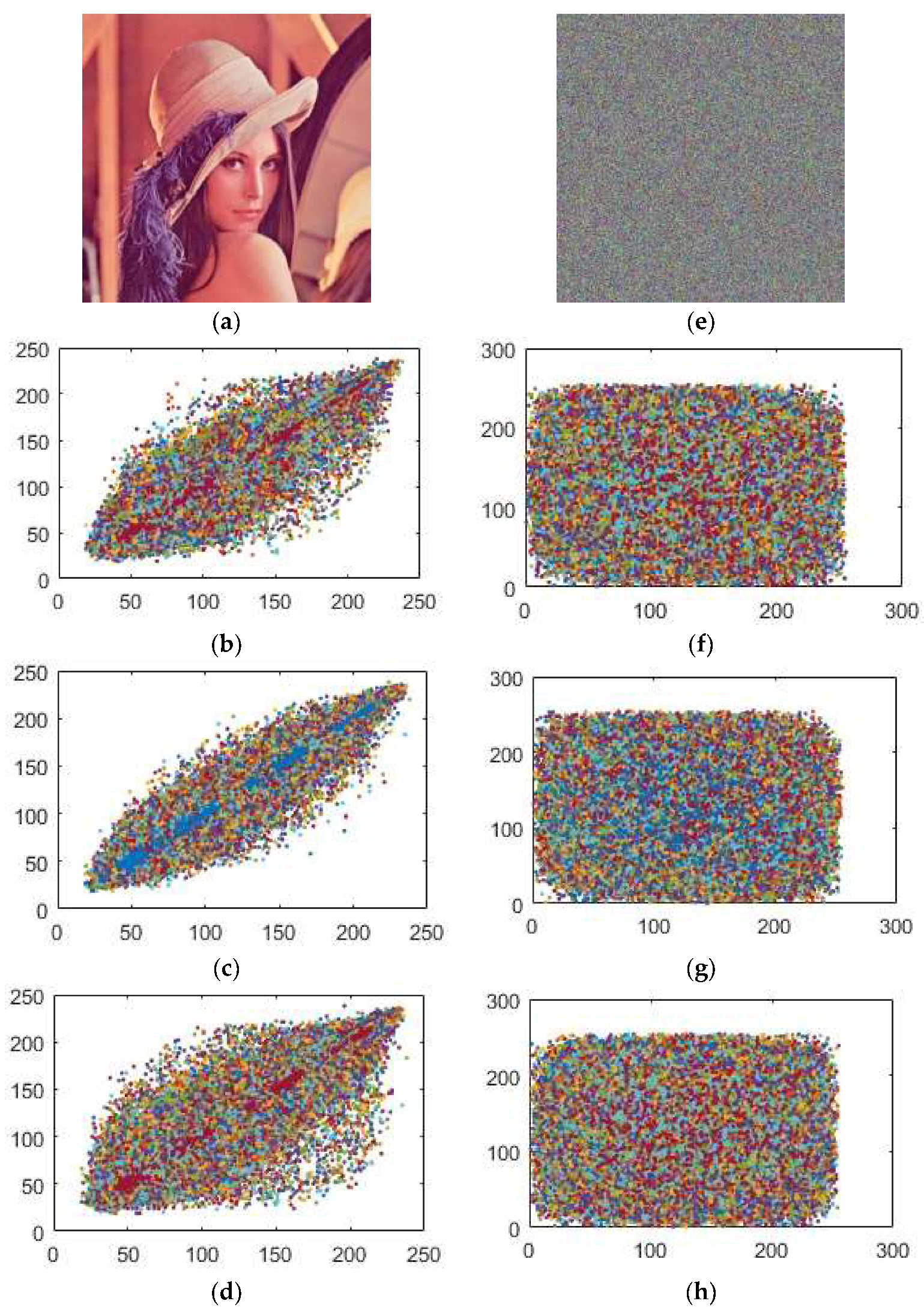
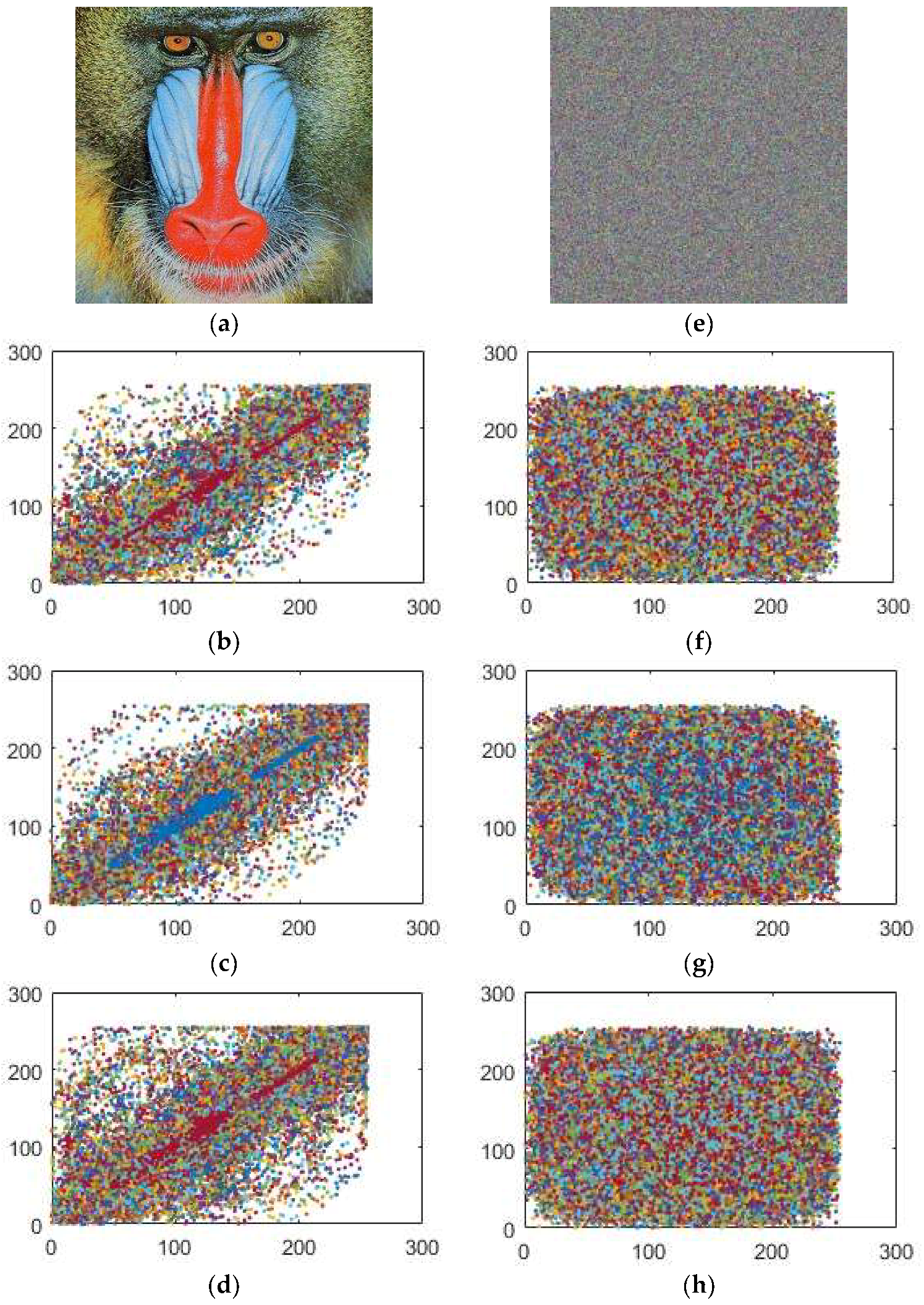
This method is used as a reverse process of our encryption procedure. The encrypted images through our proposed algorithm can be seen in Figure 2, Figure 3 and Figure 4 respectively.
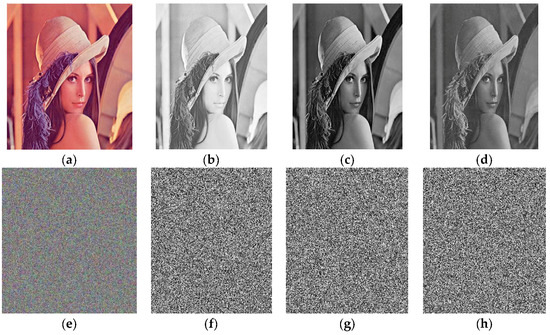
Figure 2.
The images (e), (f), (g) and (h) are layer-wise encrypted results for images of Lena (a) plain image; (b) red; (c) green and (d) blue components respectively.
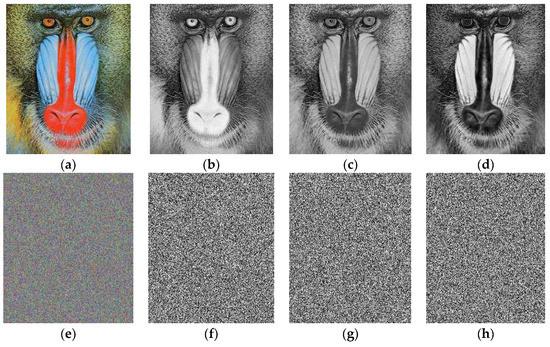
Figure 3.
The images (e), (f), (g) and (h) are layer-wise encrypted results for images of Baboon (a) plain image; (b) red; (c) green and (d) blue components respectively.
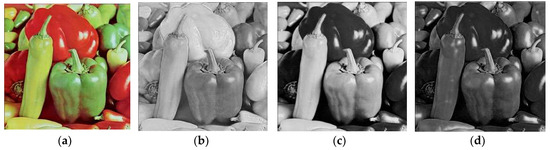
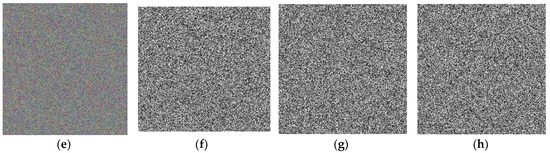
Figure 4.
The images (e), (f), (g) and (h) are layer-wise encrypted results for images of Peppers (a) plain image; (b) red; (c) green and (d) blue components respectively.
4. Security Analysis of the Proposed Algorithm
Here, we apply some statistical measures on the typical digital contents to examine the safety during execution of the proposed encryption scheme. These measurements are strictly based on a precise evaluation, a realistic inspection and an inconsistency criterion for the encryption of images.
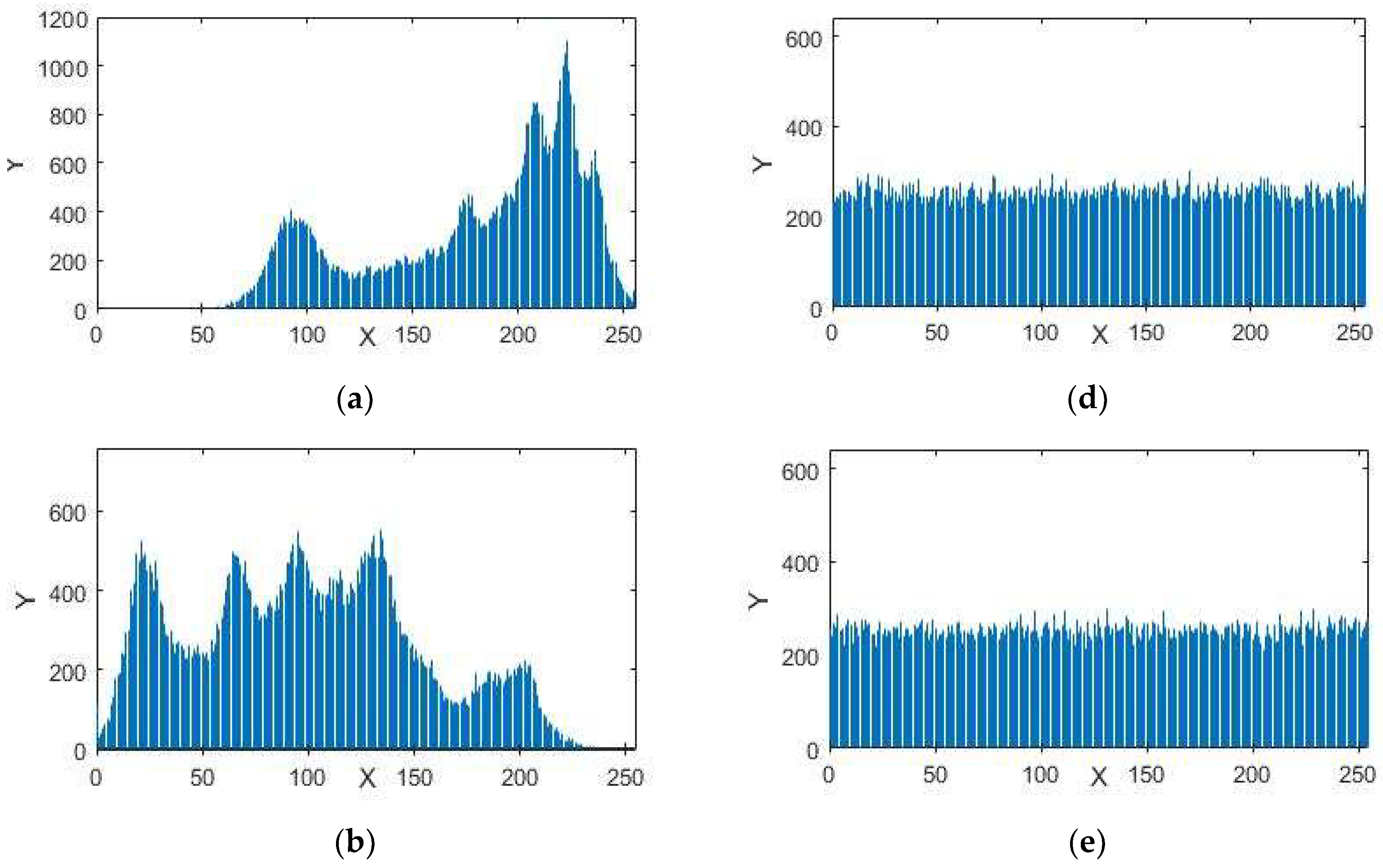
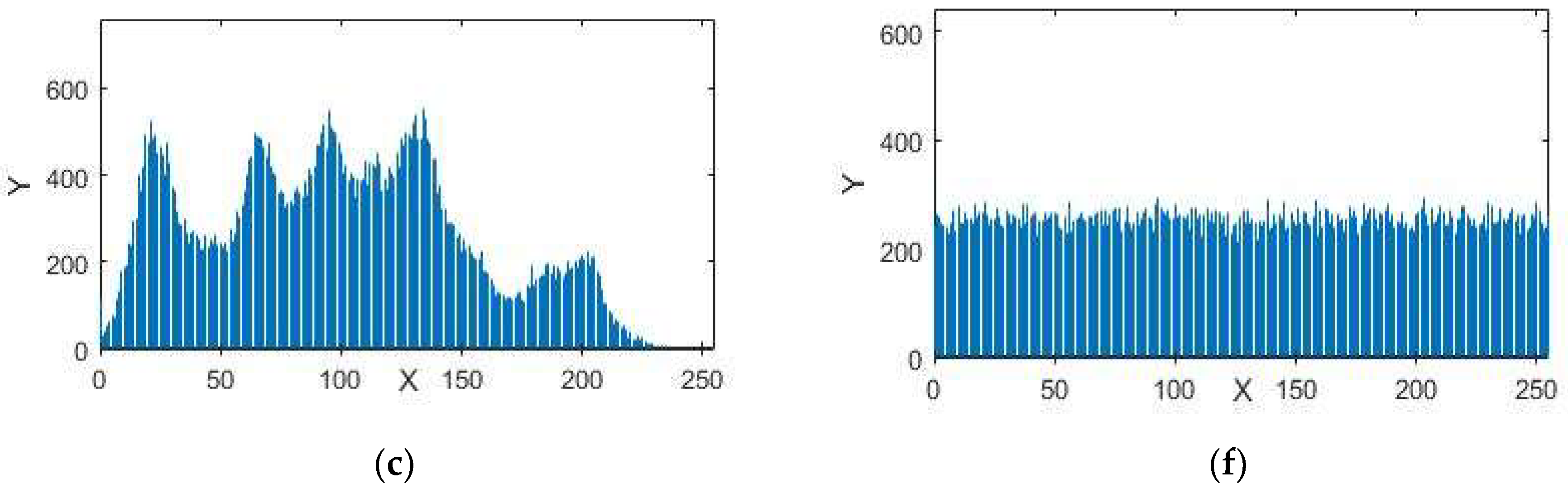
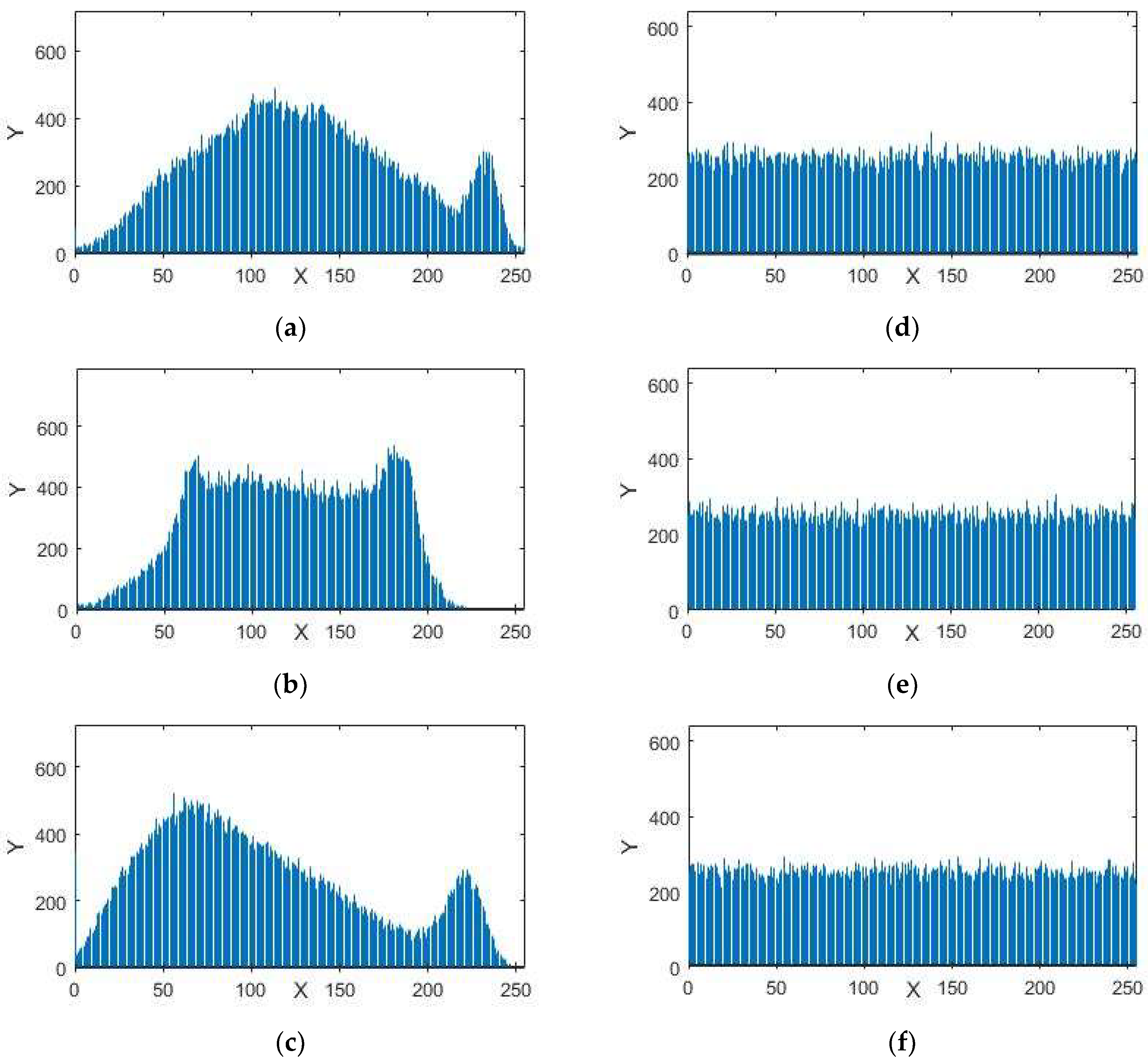
4.1. Uniformity Analysis of Image Pixels
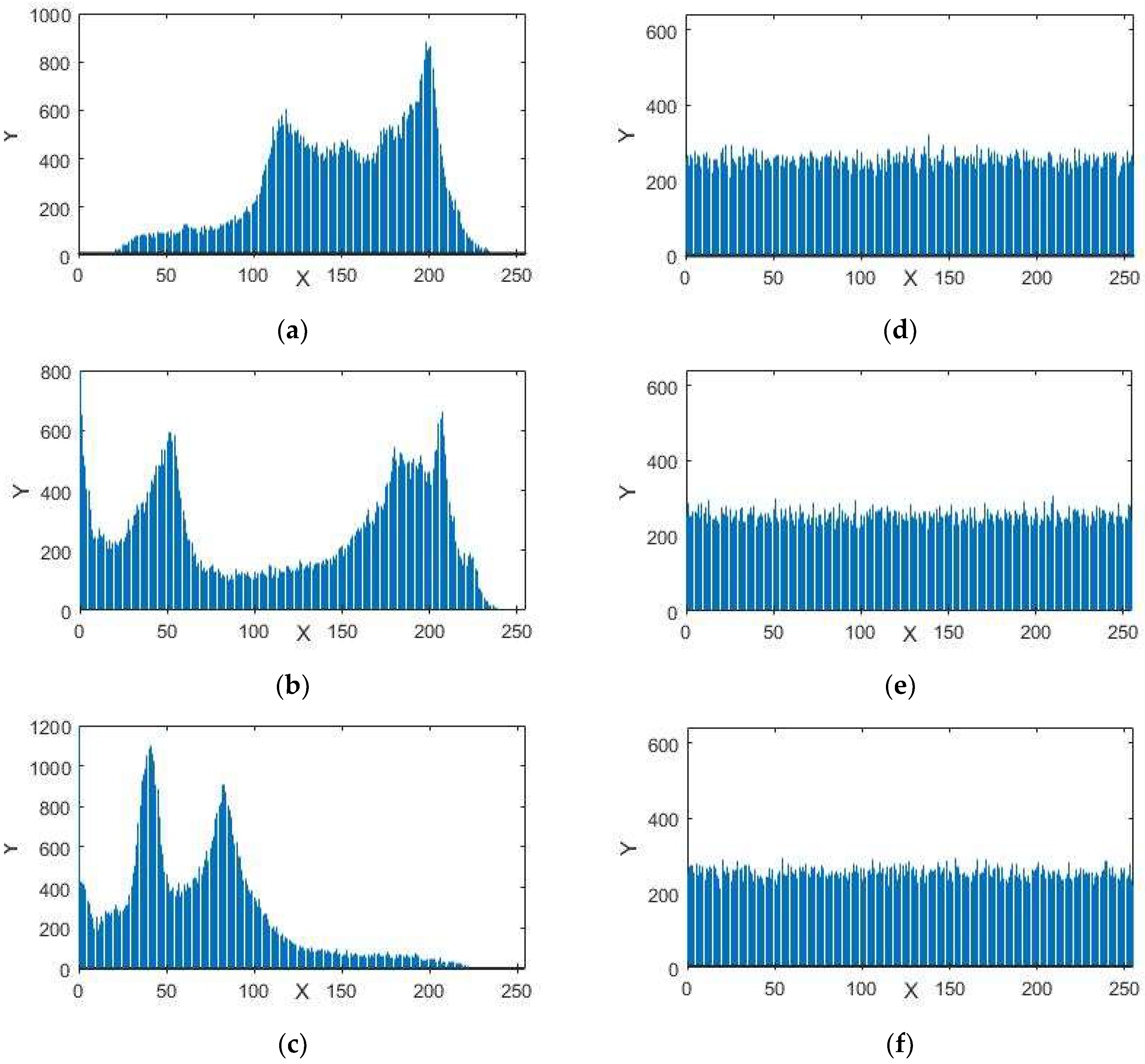
A histogram of an image provides information about the circulation of the pixel intensity esteems for an image. A protected framework in encryption can have an identical histogram to resist statistical assaults. The histograms in Figure 5, Figure 6 and Figure 7 represent the standard and encrypted images of Lena, Baboon, and Peppers. From Figure 5, Figure 6 and Figure 7, we analyzed that the histograms of the standard images are not uniform, whereas the histograms of the encrypted digital images are uniform. The uniformity of pixel heights in the histograms of the encrypted images creates difficulty for attackers to find the clue for the maximum information region.
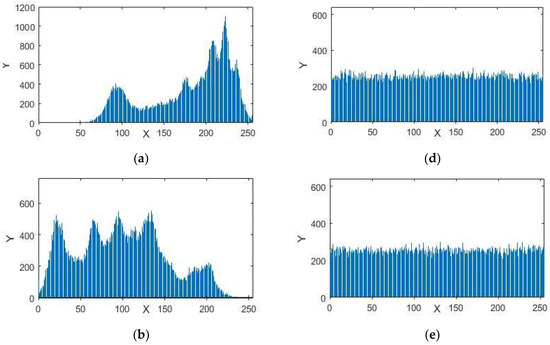
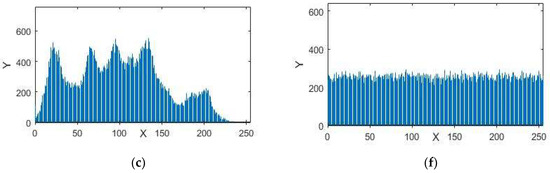
Figure 5.
Histograms (a) red component; (b) green component and (c) blue component for the original images of Lena with size 256 × 256. Histograms (d) red component; (e) green component; (f) blue component for the encrypted images of Lena.
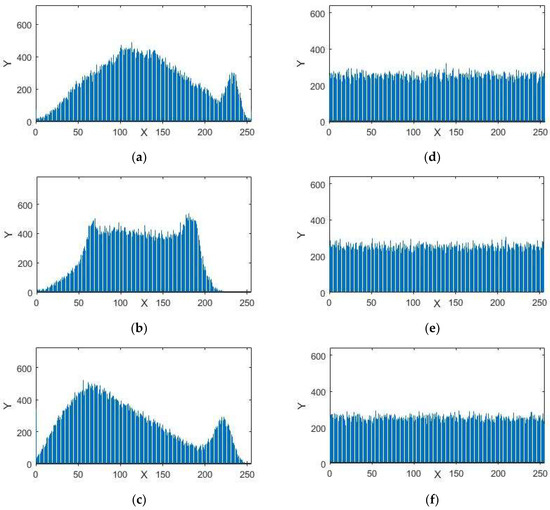
Figure 6.
Histograms (a) red component; (b) green component and (c) blue component for the original images of Baboon with size 256 × 256. Histograms (d) red component; (e) green component; (f) blue component for the encrypted images of Baboon.
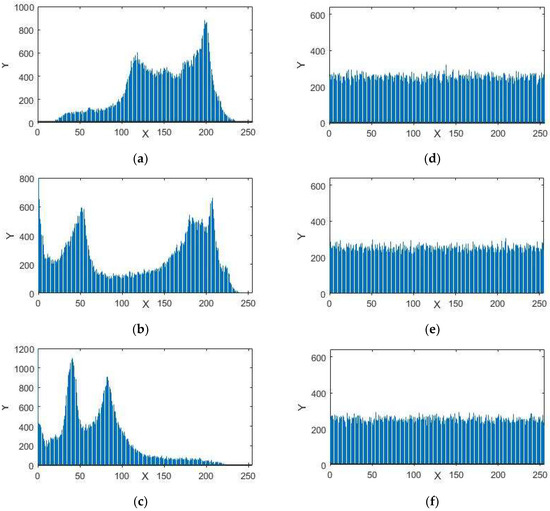
Figure 7.
Histograms (a) red component; (b) green component and (c) blue component for the original images of Peppers with size 256 × 256. Histograms (d) red component; (e) green component; (f) blue component for the encrypted images of Peppers.
4.2 Correlation Analysis for Adjacent Pixels
The purpose of the correlation analysis was to examine the connections of neighboring pixels in the original and encrypted images. Mathematically, the correlation coefficients of two neighboring pixels is defined as:
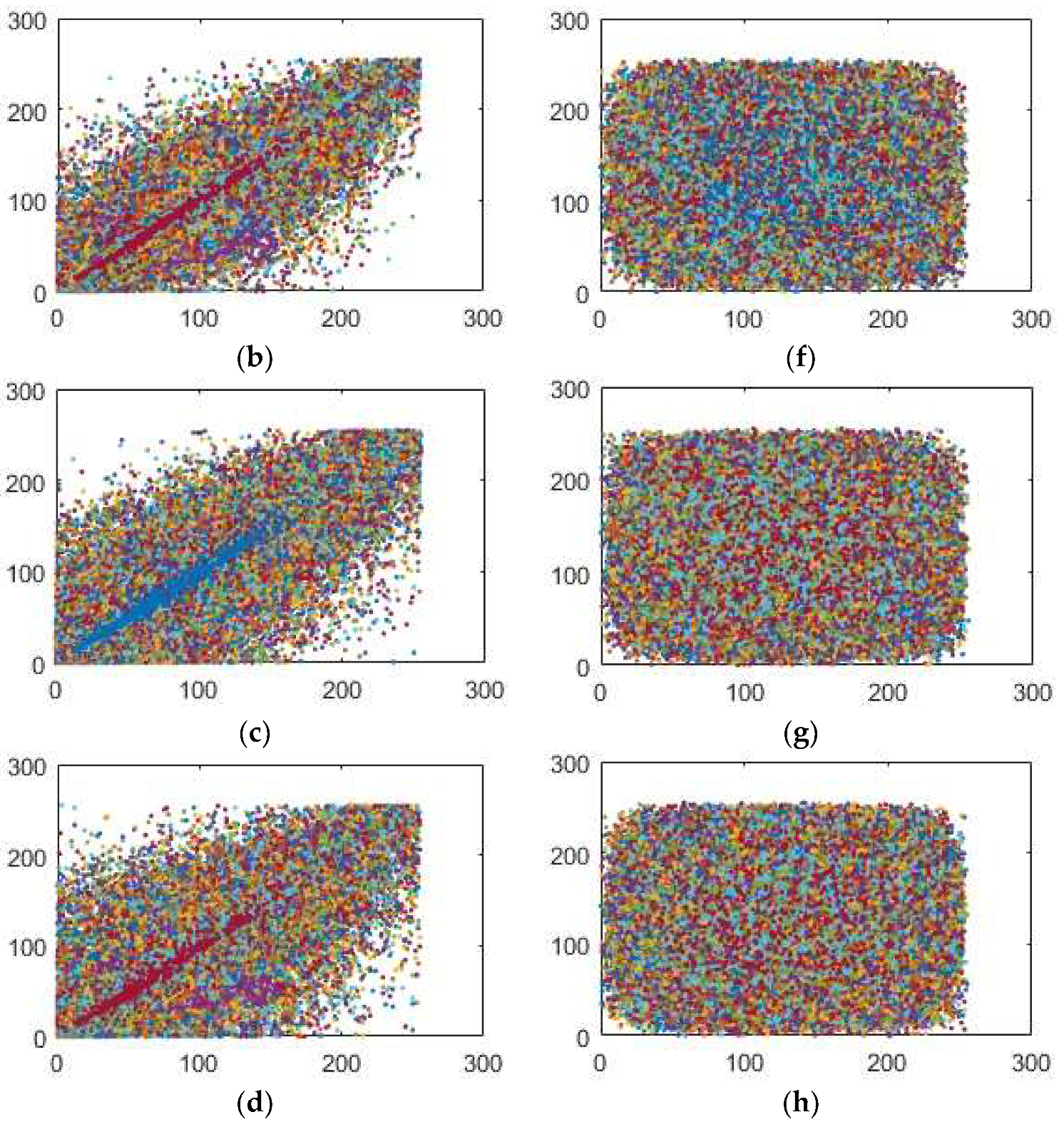
where X and Y are the estimations of two neighboring pixels of gray scale image, Var(X) and Var(Y) are deviations of X and Y individually and Cov(X,Y) represents the covariance. The correlation coefficients of the plain and encrypted digital images have a distinctive substance displayed in Table 4, Table 5, Table 6 and Table 7 identified by the plain and enciphered digital images are provided in Figure 8, Figure 9 and Figure 10. In addition, Table 4 contains the quantified evaluation of the correlation coefficient demonstrating the diffusion of the unique and encoded images horizontally, vertically and diagonally. Presently, we consider 2000 pairs of randomly selected neighboring pixels to look over the original and the enciphered images horizontally, vertically and diagonally. In Table 4, the correlation coefficients for the green, blue and red parts of the encrypted images are quite small, which implies an irrelevant correlation between adjoining pixels.

Table 4.
Color components-wise correlation coefficient of cipher images.

Table 5.
Correlation coefficients of original and encrypted images.

Table 6.
Correlation coefficients of the plain and cipher image for the Lena color image of size 256 × 256.

Table 7.
Comparison between the correlation coefficients of the proposed scheme and recent techniques using Lena image.
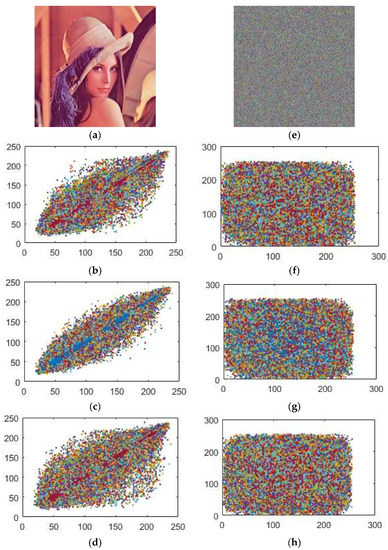
Figure 8.
Correlation coefficients between the pairs of the pixels for (a) Original Lena image; (b) horizontally; (c) vertically and (d) diagonally (e) enciphered Lena image; (f) horizontally; (g) vertically; (h) diagonally.
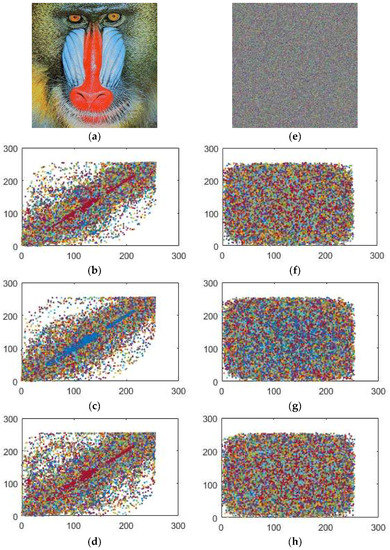
Figure 9.
Correlation coefficients between the pairs of the pixels for (a) original Baboon image; (b) horizontally; (c) vertically and (d) diagonally (e) enciphered Baboon image; (f) horizontally; (g) vertically; (h) diagonally.

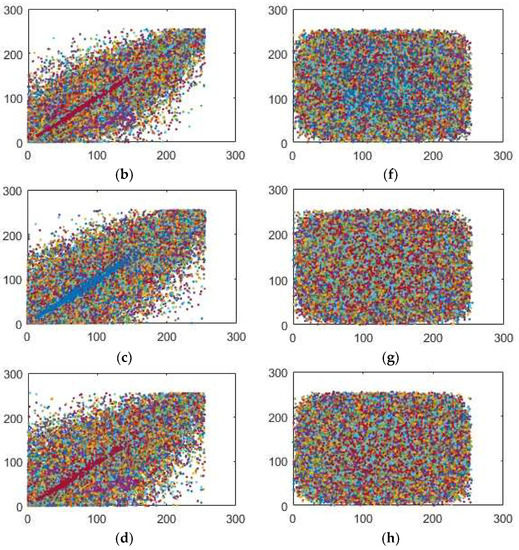
Figure 10.
Correlation coefficients between the pairs of the pixels for (a) original Peppers image; (b) horizontally; (c) vertically and (d) diagonally (e) enciphered Peppers image; (f) horizontally; (g) vertically; (h) diagonally.
In addition, high correlation coefficients for the red, green and blue parts of the original images make data spillage conceivable. Table 6 provides us with similar position correlations for the red, green and blue parts, while Table 7 gives the adjoining position correlations for the red, green and blue parts. From Table 6 and Table 7, we analyze that the correlation coefficients of the encrypted digital images for the red, green and blue parts are all lower than −0.002, while the greatest correlation coefficient for the original images is 0.9652 in the event of the Lena image, 0.8310 for the Baboon and 0.9444 for the Peppers image, which indicates that the correlations for the red, green and blue parts of the encrypted images are adequately diminished. Therefore, our encryption scheme is highly defensive against statistical attacks.
In addition, we plotted the correlation coefficients for the red, green and blue parts of the original images in Figure 8a–d, Figure 9a–d and Figure 10a–d and the encrypted images Figure 8e–h, Figure 9e–h and Figure 10e–h toward every directions, as delineated in Figure 8, Figure 9 and Figure 10. The solid correlation between adjoining pixels of the plain images is apparent as the specks are congregated along the slanting in Figure 8a–d, Figure 9a–d and Figure 10a–d. Nonetheless, the specks are scattered over the whole plane in Figure 8a–d, Figure 9a–d and Figure 10a–d, which shows that the correlation is incredibly diminished in the encrypted digital images.
4.3. Pixel Modification Based Measurements
The quality of an image depends upon the pixel difference which is calculated by means the mean square error (MSE), average difference (AD), maximum difference (MD), normalized absolute error (NAE), normalized cross correlation (NCC), structure content (SC) and peak signal to noise ratio) values (PSNR). These metrics are used for the comparison of unlike images.
4.3.1. Mean Square Error (MSE)
An encrypted image should not be equivalent to the original digital image due to the application of the encryption scheme over the plain image, which surely adds some noise to the actual digital content. We find MSE of the plain and encrypted images to analyze the level of enciphering. Mathematically, MSE is defined as:
where and are the pixels positioned in the j-th row and k-th column of the plain and enciphered images respectively. A larger value of the MSE enhances the security of the encryption scheme.
4.3.2. Peak Signal to Noise Ratio (PSNR)
Mathematically, PSNR is defined as:
where is the maximum value of pixel which can occur. The low value of PSNR shows the more difference of the original and enciphered images. In Table 8, we discuss values MSE and PSNR to ensure the versatility of the suggested scheme.

Table 8.
MSE and PSNR of the suggested scheme.
4.3.3. Normalized Absolute Error (NAE)
Mathematically, normalized absolute error (abbreviated as NAE) is defined as:
It is the proportion of the encrypted digital content to the original image. A bigger estimation of NAE demonstrates the great nature of coming about the scrambled image after the encryption process.
4.3.4. Maximum Difference (MD)
Mathematically, the maximum difference is defined as:
where
It measures the maximum of the error signal. A higher value of the maximum difference indicates that the quality of the encryption scheme is better.
4.3.5. Average Difference (AD)
The average difference measures the pixel contrast between the original image and its corresponding enciphered image. This quantitative measure is only utilized in object revealing and pattern recognition applications and it can likewise be pertinent to any image preparing applications where we locate the normal distinction between two digital contents. A larger estimation of the AD indicates the great quality of the digital image encryption (see Table 9). Mathematically, the average difference is defined as:

Table 9.
Pixel difference-based and correlation-based measures of the proposed encryption scheme.
The value of AD is ideally zero for two same digital images.
4.4. Similarities Measures
The likenesses between two signals can be estimated through a cross-correlation, structure similarity, and structure content. These are the standard devices for assessing how much two signs are comparable or divergent. It is a basic way to match two image patches, for highlight recognition and in addition a part of more refined systems. The method has a few favorable circumstances. We have used a standardized correlation and structure content with the end goal to demonstrate the dissimilarities among the original and scrambled images.
4.4.1. Normalized Cross Correlation (NCC)
A normalized cross-correlation (NCC) has been normally utilized as a metric to assess the level of likeness (or difference) between two digital images. The normalized cross-correlation is limited in the range between −1 and 1. The setting of the location edge esteem is significantly less difficult than the cross-correlation. The NCC measures the cozy connection between two images, it might be plain and enciphered digital images. All of the correlation-based measures are considered as 1, as the distinction between the two images is considered as zero. In each image, the similitude estimation is done dependent on the direct splendor and complexity varieties of utilizing cross-correlation. Mathematically, normalized cross-correlation is defined as:
where m × n is the size of both plain image P and cipher image C. The estimation of NCC for encryption varies from or not near unity, which unmistakably means that the proposed scheme includes solid dissimilarities among the pixels of plain and scrambled images (see Table 9).
4.4.2. Structural Content (SC)
This measure viably thinks about the aggregate weight of an original signal to that of a coded or given. It is, hence, a worldwide metric. This measure is likewise called as structural content (SC), and in the event that it is spread at 1, at that point the changed over image is of better quality and a huge estimation of SC implies that the image is of low quality. Mathematically, structural content is defined as:
On account of the plain and encoded images, the estimation of SC is not close to unity because the encryption scheme includes confusion and diffusion-like noise and commotion in the original image. The estimation of SC isn’t near one if there should be an occurrence of all advanced standard shading images (red, green and blue layers) (see Table 9).
4.5. Entropy Investigation
Entropy is evaluated to analyze the spreading of the gray scale estimations of the images. The coarser the image is, the bigger the entropy is. For an irregular image with 256 gray levels, the entropy ought to, in a perfect world, be 8 [9]. On the off chance that the entropy of the encrypted image is under 8, there is a probability of consistency, and this is a risk to the anticipated security. Mathematically, we can represent the entropy H for a data source y is characterized as:
where are all possible states of information and yi is the source images. For a completely sporadic source exuding signs, entropy should be N. In Table 10, the entropies of different plain and enciphered image entropies are given as demonstrated by the plain images in Figure 2, Figure 3 and Figure 4. These values are very close to the theoretical value which is 8. Consequently, information spillage in our encryption is negligible and well secured for physical attacks. We have looked at data entropy for our proposed encryption method with the already developed encryption plans. Table 11 shows that the entropy of the offered scheme for the scrambled images are better than the already available algorithms.

Table 10.
Entropies of various plain and enciphered images.

Table 11.
Comparison between the entropies for 256 × 256 Lena image.
In Table 11 and Table 12, we compare the entropy of the proposed algorithm to the already defined algorithms. Our entropies are approximately equal to 8, which is the most suitable value. This minimizes the chance of data spillage during the encryption. Consequently, the proposed image cryptosystem is secure against an entropy assault. In addition, the entropy estimations of the introduced scheme are better than the encryption schemes [3,4,5,6].

Table 12.
Comparison of the entropy of the proposed algorithm to the already defined algorithms.
4.6. Robustness against Differential Attack
Diffusion is a basic parameter to examine the randomness in the encryption scheme. It is an important measurement in the proposed digital image encryption algorithm because it reflects even a minor change in the plain image [4,5]. By and large, the enemy may roll out by a slight improvement. For instance, by altering a single pixel of the original image and after that observe the difference in the outcome. Along these lines, we may discover a significant connection of the original and encrypted image. Since a little change in the original image can create a critical change in the encrypted image. Thus, differential attacks would be exceptionally wasteful and for all intents and purposes futile. On the off chance that an encryption scheme has a decent trademark, the connection between the original image and the encrypted image is extremely complex and it cannot be expected easily. We can measure the diffusion of an encryption scheme by changing a pixel in the original image [6]. To measure the effect of a one-pixel change in the original image and encrypted image, we used three estimations MAE, NPCR and UACI to examine security in the encrypted image against differential attacks. Suppose and are encrypted images before and after one pixel change in the plain image respectively. Then the MAE, NPCR and UACI are defined as:
where
represent the value of pixel at grid and D(i, j) is a bipolar array at grid
In Table 13 and Table 14, we have MAE (> 75), (NPCR (> 99%) and UACI (≈ 33%) for the red, green and blue part of the encrypted standard images. These values of MAE, NPCR and UACI are very close to the best-approximated values already available in the literature. Hence, the suggested encryption algorithm can create more difficulty for differential attackers.

Table 13.
The evaluation of the security measurements of the suggested encrypted algorithm.

Table 14.
The evaluation of the security measurements of the suggested encrypted algorithm.
A comparison of the differential analysis with some of the already existing results is listed in Table 15 and Table 16 respectively.

Table 15.
A comparison of calculated UACI and NPCR for 512 × 512 plain Lena image.

Table 16.
NPCR, UACI values for the color components of the digital Lena image of size 256 × 256.
We have also calculated the pixels difference base and similarities measurements between the original encrypted image and the one bit change encrypted image . The mathematical expressions for the pixels difference and similarity measures for and are given below:
where
The analyses of the pixel difference and similarity measures are shown in Table 17. This shows that a slight difference in the neighboring pixels creates an avalanche effect, which is one of the basic requirements while designing any image encryption technique. The numerical values of MSE, PSNR, NCC, NAE AD, SC and MD for original encrypted image and the one bit change encrypted image clearly reflect that our proposed algorithm is resistive against differential attacks.

Table 17.
Pixel difference analysis for the one bit change encrypted image with the plain image.
5. Conclusions
The present research article provides a new idea for the construction of an image encryption technique. A completely new inverse LA-semi group was investigating and applied for substitution, which is one of the most important components in symmetric encryption. This new mechanism added confusion, which is fundamentally responsible for breaking the pattern between the original and encrypted information. Moreover, we have utilized chaotic continuous systems in order to add diffusion into our proposed image encryption scheme. The proposed idea adds a new milestone for oncoming researchers.
Author Contributions
The major part of this article has been taken from the Ph.D. thesis of I.Y. who designed the method and mathematical structure of inverse LA-semigroup. M.K. performed the experiments and made helpful suggestions to improve the paper. Both authors read and approved the final version of the article.
Funding
We have not received any external funding for the research and publication of this article.
Acknowledgments
The authors are very grateful to vice chancellor Sayed Wilayat Hussain, Institute for Space Technology, Islamabad 44000 Pakistan for providing a decent research environment.
Conflicts of Interest
We have no conflict of interest for the publication of this article.
References
- Xie, E.Y.; Li, C.; Yu, S.; Lü, J. On the cryptanalysis of Fridrich’s chaotic image encryption scheme. Signal Process. 2017, 132, 150–154. [Google Scholar] [CrossRef]
- Li, C.; Lin, D.; Lü, J. Cryptanalyzing an Image-Scrambling Encryption Algorithm of Pixel Bits. IEEE MultiMedia 2017, 24, 64–71. [Google Scholar] [CrossRef]
- Rhouma, R.; Meherzi, S.; Belghith, S. OCML-based colour image encryption. Chaos Soliton. Fractals 2009, 40, 309–318. [Google Scholar] [CrossRef]
- Liu, H.; Wang, X. Color image encryption using spatial bit level permutation and high-dimension chaotic system. Opt. Commun. 2011, 284, 3895–3903. [Google Scholar] [CrossRef]
- Liu, H.; Wang, X.; Kadir, A. Color image encryption using Choquet fuzzy integral and hyper chaotic system. Optik 2013, 124, 3527–3533. [Google Scholar] [CrossRef]
- Kadir, A.; Hamdulla, A.; Guo, W. Color image encryption using skew tent map and hyper chaotic system of 6th-order CNN. Optik 2014, 125, 1671–1675. [Google Scholar] [CrossRef]
- Waseem, H.M.; Khan, M. Information Confidentiality Using Quantum Spinning, Rotation and Finite State Machine. Int. J. Theor. Phys. 2018, 57, 3584–3594. [Google Scholar] [CrossRef]
- Khan, M.; Shah, T.; Batool, S.I. A new approach for image encryption and watermarking based on substitution box over the classes of chain rings. Multimed. Tools Appl. November 2017, 76, 24027–24062. [Google Scholar] [CrossRef]
- Belazi, A.; Khan, M.; El-Latif, A.A.A.; Belghith, S. Efficient cryptosystem approaches: S-boxes and permutation substitution-based encryption. Nonlinear Dyn. 2017, 87, 337–361. [Google Scholar] [CrossRef]
- Khan, M.; Asghar, Z. A novel construction of substitution box for image encryption applications with Gingerbreadman chaotic map and S8 permutation. Neural Comput. Appl. 2018, 29, 993–999. [Google Scholar] [CrossRef]
- Khan, M.; Shah, T. Construction and applications of chaotic S-boxes in image encryption. Neural Comput. Appl. 2016, 27, 677–685. [Google Scholar] [CrossRef]
- Khan, M.; Shah, T. An efficient construction of substitution box with fractional chaotic system. Signal Image Video Process. 2015, 9, 1335–1338. [Google Scholar] [CrossRef]
- Khan, M.; Shah, T. An efficient chaotic image encryption scheme. Neural Comput. Appl. 2015, 26, 1137–1148. [Google Scholar] [CrossRef]
- Khan, M.; Shah, T. A novel construction of substitution box with Zaslavskii chaotic map and symmetric group. J. Intell. Fuzzy Syst. 2015, 28, 1509–1517. [Google Scholar]
- Huang, C.K.; Nien, H.H. Multi chaotic systems based pixel shuffle for image encryption. Opt. Commun. 2009, 282, 2123–2127. [Google Scholar] [CrossRef]
- Mondal, B.; Kumar, P.; Singh, S. A chaotic permutation and diffusion based image encryption algorithm for secure communications. Multimed. Tools Appl. 2018, 77, 31177–31198. [Google Scholar] [CrossRef]
- Enayatifar, R.; Abdullah, A.H.; Isnin, I.F. Chaos-based image encryption using a hybrid genetic algorithm and a DNA sequence. Opt. Lasers Eng. 2014, 56, 83–93. [Google Scholar] [CrossRef]
- Zhen, P.; Zhao, G.; Min, L.; Jin, X. Chaos-based image encryption scheme combining DNA coding and entropy. Multimed. Tools Appl. 2016, 75, 6303–6319. [Google Scholar] [CrossRef]
- Khan, M. A novel image encryption scheme based on multiple chaotic S-boxes. Nonlinear Dyn. 2015, 82, 527–533. [Google Scholar] [CrossRef]
- Yang, B.; Liao, X. A new color image encryption scheme based on logistic map over the finite field ZN. Multimed. Tools Appl. 2018, 77, 21803–21821. [Google Scholar] [CrossRef]
- Enayatifar, R.; Abdullah, A.H.; Isnin, I.F.; Altameem, A.; Lee, M. Image encryption using a synchronous permutation-diffusion technique. Opt. Lasers Eng. 2017, 90, 146–154. [Google Scholar] [CrossRef]
- Hamza, R.; Titouna, F. A novel sensitive image encryption algorithm based on the Zaslavsky chaotic map. Inf. Secur. J. Glob. Perspect. 2016, 25, 162–179. [Google Scholar] [CrossRef]
- Tong, X.J.; Zhang, M.; Wang, Z.; Ma, J. A joint color image encryption and compression scheme based on hyperchaotic system. Nonlinear Dyn. 2016, 84, 2333–2356. [Google Scholar] [CrossRef]
- Zhang, Y.S.; Xiao, D. Self-adaptive permutation and combined global diffusion for chaotic color image encryption. AEU Int. J. Electron. Commun. 2014, 68, 361–368. [Google Scholar] [CrossRef]
- Wang, X.; Teng, L.; Qin, X. A novel colour image encryption algorithm based on chaos. Signal Process. 2012, 92, 1101–1108. [Google Scholar] [CrossRef]
- Linhua, Z.; Liao, X.; Wang, X. An image encryption approach based on chaotic maps. Chaos Solitons Fractals 2005, 24, 759–765. [Google Scholar]
- Zhou, Q.; Wong, K.; Liao, X.; Xiang, T.; Hu, Y. Parallel image encryption algorithm based on discretized chaotic map. Chaos Solitons Fractals 2008, 38, 1081–1092. [Google Scholar] [CrossRef]
- Gao, H.; Zhang, Y.; Liang, S.; Li, D. A new chaotic algorithm for image encryption. Chaos Solitons Fractals 2006, 29, 393–399. [Google Scholar] [CrossRef]
- Mao, Y.; Chen, G.; Lian, S. A novel fast image encryption scheme based on 3D chaotic bakermaps. Int. J. Bifurc. Chaos 2004, 14, 3613–3624. [Google Scholar] [CrossRef]
- Etemadi Borujeni, S.; Eshghi, M. Chaotic image encryption design using tompkins-paige algorithm. Math. Prob. Eng. 2009, 2009. [Google Scholar] [CrossRef]
- Zhang, G.; Liu, Q. A novel image encryption method based on total shuffling scheme. Opt. Commun. 2011, 284, 2775–2780. [Google Scholar] [CrossRef]
- Wu, X.; Wang, K.; Wang, X.; Kan, H. Lossless chaotic color image cryptosystem based on DNA encryption and entropy. Nonlinear Dyn. 2017, 90, 855–875. [Google Scholar] [CrossRef]
- Dong, C. Color image encryption using one-time keys and coupled chaotic systems. Signal Process. Image Commun. 2014, 29, 628–640. [Google Scholar] [CrossRef]
- Praveenkumar, P.; Amirtharajan, R.; Thenmozhi, K.; Bosco, J.; Rayappan, B. Triple chaotic image scrambling on RGB—A random image encryption approach, Security Comm. Networks 2015, 8, 3335–3345. [Google Scholar]
- Li, C.; Lin, D.; Lü, J.; Hao, F. Cryptanalyzing an image encryption algorithm based on autoblocking and electrocardiography. IEEE MultiMedia 2018, 25. [Google Scholar] [CrossRef]
- Hua, Z.; Jin, F.; Xu, B.; Huang, H. 2D Logistic-Sine-coupling map for image encryption. Signal Process. 2018, 149, 148–161. [Google Scholar] [CrossRef]
- Kazim, M.A.; Naseeruddin, M. On almost semigroups. Alig. Bull. Math. 1972, 2, 1–7. [Google Scholar]
- Mushtaq, Q.; Yusuf, S.M. On LA-semigroups. Alig. Bull. Math. 1978, 8, 65–70. [Google Scholar]
- Ježek, J.; Kepka, T. Modular groupoids. Czech. Math. J. 1984, 34, 477–487. [Google Scholar]
- Holgate, P. Groupoids satisfying a simple invertive law. Math. Stud. 1992, 61, 101–106. [Google Scholar]
- Protić, P.V.; Stevanović, N. On Abel-Grassmann’s groupoids (exposition). In Proceedings of the Mathematical Conference Pristina, Pristina, Kosovo, 28 September–1 October 1994; pp. 27–29. [Google Scholar]
- Mushtaq, Q.; Yusuf, S.M. On locally associative LA-semigroups. J. Nat. Sci. Math. 1979, 1, 57–62. [Google Scholar]
- Mushtaq, Q.; Iqbal, Q. Decomposition of a Locally Associative LA-semigroup. Semigr. Forum 1990, 41, 155–164. [Google Scholar] [CrossRef]
- Mushtaq, Q.; Iqbal, M. On representation theorem for inverse LA-semigroups. Pak. Acad. Sci. 1993, 4, 247–254. [Google Scholar]
- Mushtaq, Q.; Khan, M. Semilattice decomposition of a locally associative AG**-Groupoid. Algebra Colloq. 2009, 16, 17–22. [Google Scholar] [CrossRef]
- Dudek, W.A.; Gigoń, R.S. Completely inverse AG**-groupoids. Semigr. Forum 2013, 87, 201–229. [Google Scholar] [CrossRef]
- Ruskuc, N. Semigroup Presentations. Ph.D. Thesis, University of St Andrews, St Andrews, Scotland, 1995. [Google Scholar]
- Yaqoob, N.; Chinram, R.; Ghareeb, A.; Aslam, M. Left almost semigroups characterized by their interval valued fuzzy ideals. Afr. Matematika 2013, 24, 231–245. [Google Scholar] [CrossRef]
- Yaqoob, N. Applications of rough sets to -hyperideals in left almost -semihypergroups. Neural Comput. Appl. 2012, 21, 267–273. [Google Scholar] [CrossRef]
© 2018 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).