Abstract
Smart Agriculture or Agricultural Internet of things, consists of integrating advanced technologies (e.g., NFV, SDN, 5G/6G, Blockchain, IoT, Fog, Edge, and AI) into existing farm operations to improve the quality and productivity of agricultural products. The convergence of Industry 4.0 and Intelligent Agriculture provides new opportunities for migration from factory agriculture to the future generation, known as Agriculture 4.0. However, since the deployment of thousands of IoT based devices is in an open field, there are many new threats in Agriculture 4.0. Security researchers are involved in this topic to ensure the safety of the system since an adversary can initiate many cyber attacks, such as DDoS attacks to making a service unavailable and then injecting false data to tell us that the agricultural equipment is safe but in reality, it has been theft. In this paper, we propose a deep learning-based intrusion detection system for DDoS attacks based on three models, namely, convolutional neural networks, deep neural networks, and recurrent neural networks. Each model’s performance is studied within two classification types (binary and multiclass) using two new real traffic datasets, namely, CIC-DDoS2019 dataset and TON_IoT dataset, which contain different types of DDoS attacks.
1. Introduction
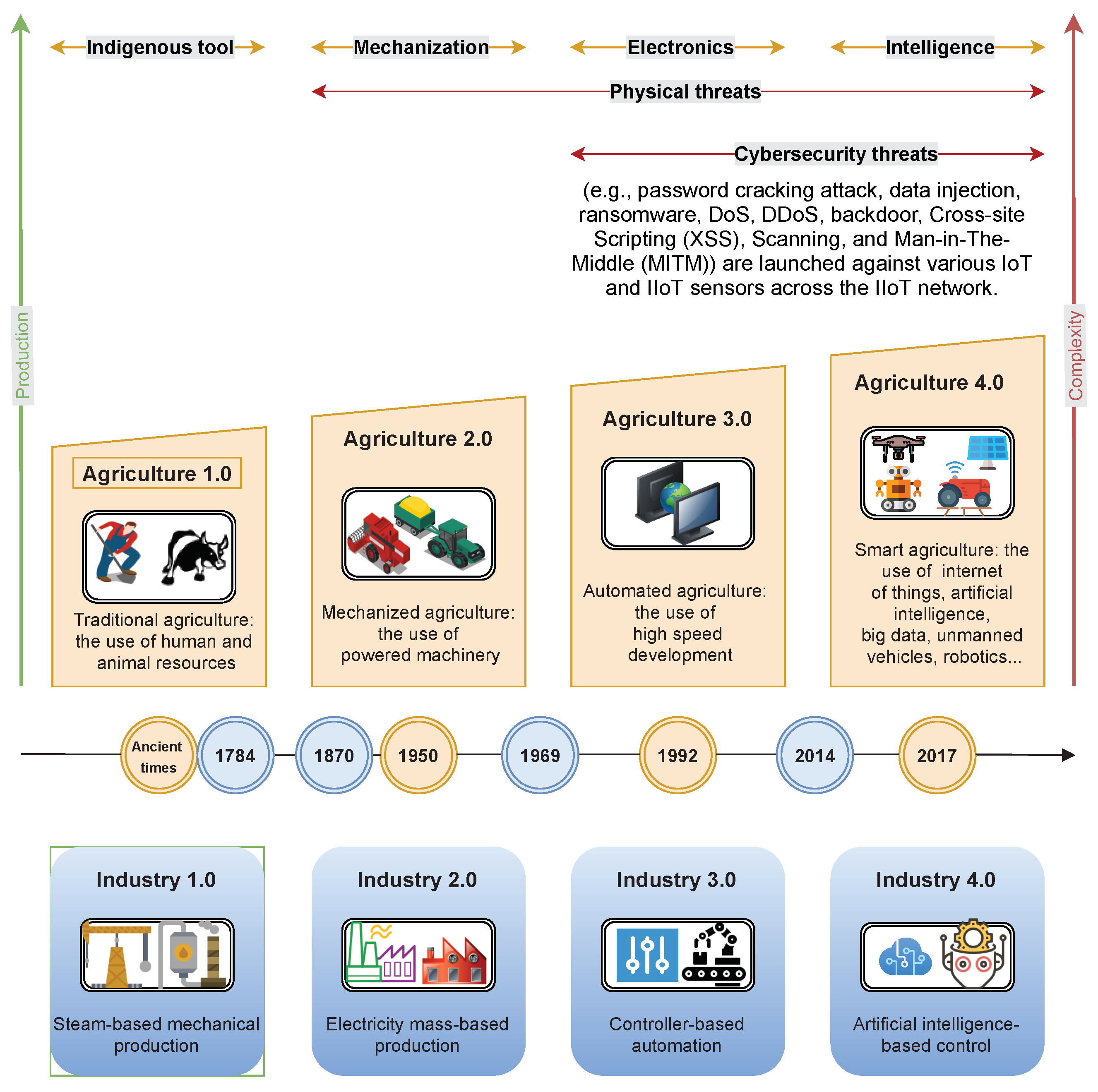
The 4th revolution of the industrial era (or Industry 4.0) is the new industry trend that defines the Smart Factory concept [1]. This concept is based on emerging technologies such as Fog computing, Cloud computing, Artificial Intelligence, Deep learning… etc. To provide an optimization of operations and reduction of costs, these technologies are employed to establish a connection between machines and the Internet, through the Internet-of-Things, to collect information in the Cloud and Edge and then process them using artificial intelligence algorithms. Industry 4.0 is expected to transform the agricultural industry and advance the 4th agricultural revolution, known as Agriculture 4.0. The first three industrial revolutions deeply reshaped the agricultural industries from indigenous agriculture (Agriculture 1.0) towards mechanized agriculture (Agriculture 2.0) and recent precision farming (Agriculture 3.0), as presented in Figure 1 [2,3].
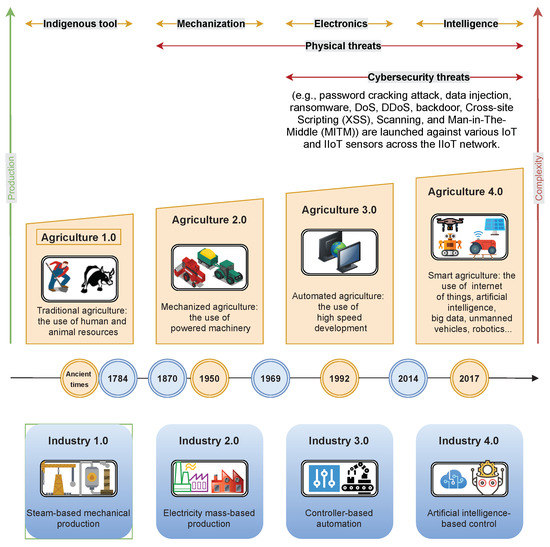
Figure 1.
Agricultural revolutions with industrial revolutions and related cyber security threats.
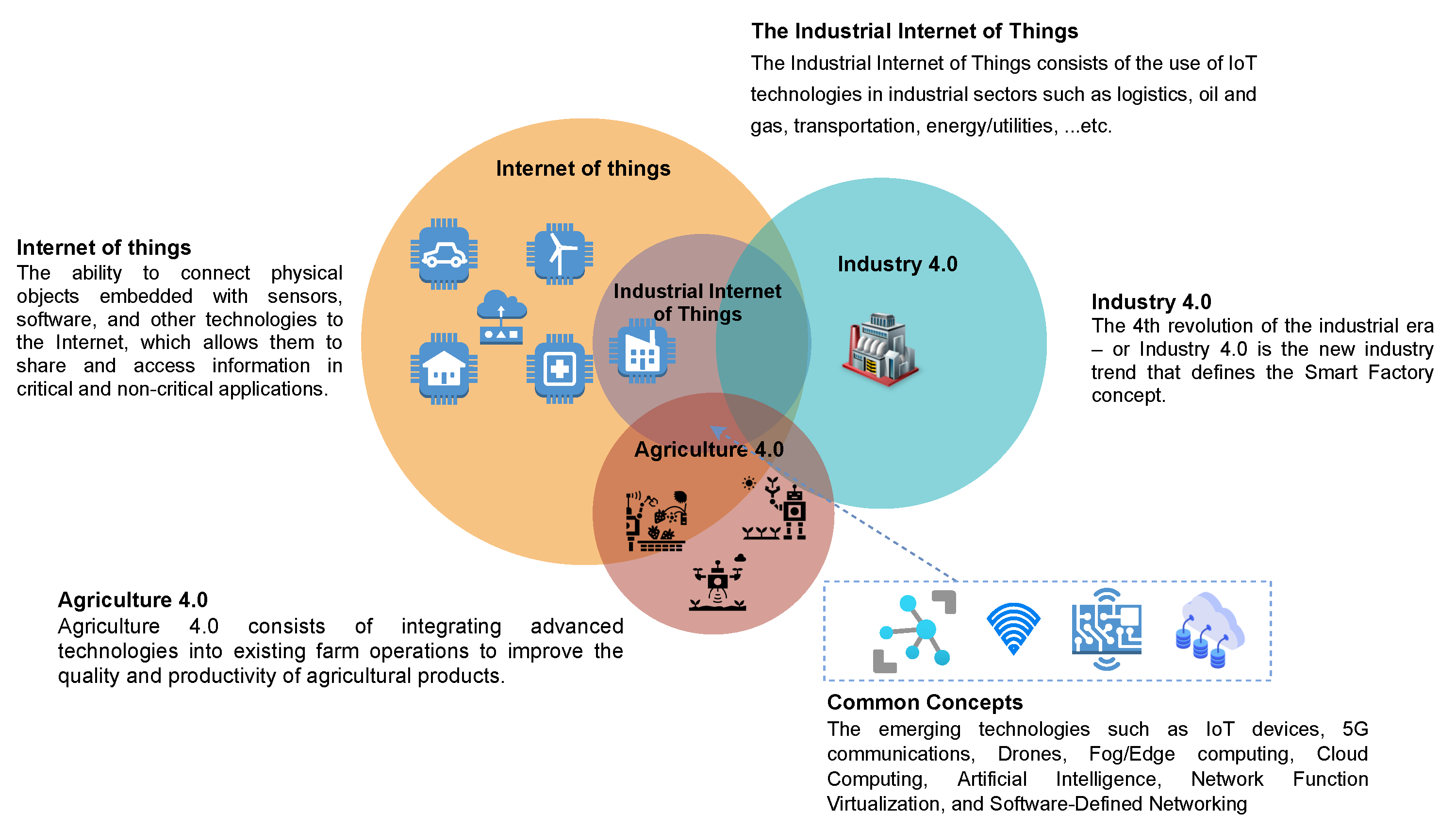
In the most recent years, the IoT application has been deployed for Agriculture 4.0 using wireless sensor networks such as, Supply chain management, Smart monitoring, Smart water, Agrochemicals applications, Disease management, and Smart harvesting. Figure 2 presents the IoT, IIoT, Industry 4.0, Agriculture 4.0 and the common concepts. Industry 4.0 focuses primarily on the manufacturing sector, Agriculture 4.0 focuses on the Agriculture sector, whereas IIoT covers all sectors where industrial/professional equipment is used. However, with thousands of IoT-based devices deployed in the open field, there are many new cyber security threats in Agriculture 4.0. When an adversary attempting to penetrate Agriculture 4.0 network, it use several different approaches such as DDoS attacks, scanning attacks, false data injection attacks, to disrupt the functioning of the IoT-based devices. For example, in the soil pH parameters, if the pH rises excessively, it means that the farmer will increase ammonium input, and if the pH falls, it indicates that the farmer will reduce ammonium input. With this information, an adversary can launch DDoS attacks to disrupt the pH parameters. Hence, this private information (i.e., the pH parameters) must be protected from cyber attacks [4]. To protect Agriculture 4.0 from destruction, change, unauthorized access, or attack, Security researchers propose the use of an intrusion detection system (IDS) beside the authentication, access control, and integrity techniques [5,6,7].
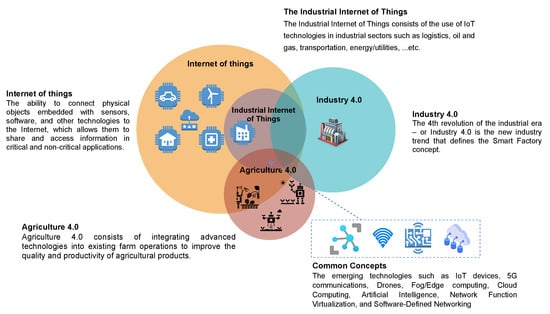
Figure 2.
IoT, IIoT, Industry 4.0, Agriculture 4.0 and the common concepts.
The IDS system is a mechanism monitoring the network traffic, which is used to detect suspicious or abnormal activities and then enables preventive measure on the intrusion risks. Therefore, intrusion detection systems can be divided into two major types, namely, (1) Network Intrusion Detection Systems (NIDS) and (2) Host Intrusion Detection Systems (HIDS). The NIDS is typically deployed or located at critical network points to ensure that it covers the locations where the traffic is more susceptible to attacked, while the HIDS systems works on any device on the network that has Internet access. To detecting intrusion, there are two main techniques, namely, IDS (1) based on anomalies and (2) IDS based on signatures [8]. The signature-based IDS (i.e., Misuse Detection or Knowledge-based Detection) concentrates on identifying a “signature”, patterns of intrusion event, and it is as efficient as updating the database at a specific moment of time. Based on monitoring regular activities, the anomaly-based IDS (i.e., Behavior-based Detection) uses machine learning techniques to compare trustworthy behavioral patterns with new behaviors. When an administrator receives an alert via the IDS system, it uses Intrusion Prevention Systems (IPS) to block the threat such as Trojan horse, DDoS attacks, etc. [9].
This paper focuses on developing and employing deep-learning approaches for detecting cyber threats (i.e., anomaly-based IDS). There are some recently proposed IDS systems that employ deep learning strategies for IoT applications, such as wireless networks [10], big data environments [11], industrial cyber–physical systems [12], SCADA systems [13], smart grids [14], internet of vehicles [15], and cloud computing [16]. Deep learning approaches are also used in Agriculture 4.0, for crop hail damage, soil and vegetation/crop mapping, crop monitoring, irrigation, greenhouse monitoring, etc. [17]. However, there are eight big challenges in the field of intrusion detection systems for Agriculture 4.0: (1) Data collection that contains IIoT traffics with cyber attacks, (2) Less amount of training data, (3) Non-representative training data, (4) Poor quality of data, (5) Irrelevant/unwanted features, (6) Overfitting the training data, (7) Underfitting the training data, (8) Offline learning & deployment of the model [18]. Our proposed model overcomes these challenges. The datasets used in our paper are very popular, recent, and used by the scientific community for developing intrusion detection systems for IIoT networks.
Our contributions in this work are:
- We propose three deep learning-based IDS models, including a convolutional neural network-based IDS model, a deep neural network-based IDS model, and a recurrent neural network-based IDS model.
- We provide a performance evaluation and comparative analysis of machine learning and deep learning approaches for cyber security in agriculture 4.0.
- We review three models of deep learning; namely, convolutional neural networks, deep neural networks, and recurrent neural networks. Each model’s performance is studied within two classification types (binary and multiclass) using two new real traffic datasets, namely, CIC-DDoS2019 dataset and TON_IoT dataset.
- We focus on the following important performance indicators: false alarm rate (FAR), precision, F-score, detection rate (DR), recall, True Negative Rate (TNR), False Accept Rate (FAR), ROC Curve, and accuracy.
2. Related Work
The popularity of deep learning in different fields of Big Data has created a lot of attention in the area of cyber security. According to its architectural conception, deep learning can be categorized in various types, such as generative and discriminative [19]. The intrusion detection systems have been investigated with the use of shallow and deep networks to identify anomalous patterns in both network and host-based systems. The summary of deep learning approaches for network intrusion detection for the IoT networks is presented in Table 1.

Table 1.
Summary of deep learning approaches for network intrusion detection for the IoT networks.
Diro and Chilamkurti [20] designed a distributed attack detection system based on deep learning for the IoT networks. The authors proposed to deploy this system at the fog computing layer for hosting attack detection systems and training models. Three cyber security datasets are used in the performance evaluation, including, NSL-KDD, ISCX, and KDDCUP99, in which the results show a precision of 71%, 98.56%, and 97%, for R2L.U2R attacks, Probe attacks, and DoS attacks, respectively. Muna et al. [21] an anomaly detection system, named ADS, for detecting cyber attacks in the industrial internet of things. The ADS system uses deep learning techniques, in which the unsupervised deep auto-encoder algorithm is used to train network normal patterns of behavior and generate the correct settings. Both NSL-KDD and UNSW-NB15 are used in the evaluation of performance which the results of the experiments demonstrate a detection ratio of 99% and a false positive ratio of 1.8%.
Based on scanning the DNS services in smart city applications of IoT, Vinayakumar et al. [23] presented an instruction detection mechanism against botnet attacks. Specifically, the proposed mechanism uses a two-tier environment for monitoring DNS logs and searching the domain name generated by the domain generation algorithm through deep learning algorithms to minimize false alarm rates. Latif et al. [25] designed an intrusion detection mechanism that uses a lightweight random neural network for detecting cyber threats in the industrial internet of things. Compared to traditional machine learning techniques such as SVM, ANN, and decision tree, the proposed system shows good performance on an open-source dataset called DS2OS. The DS2OS dataset contains seven types of attacks, including, DoS attacks, Scan, Data type probing, Malicious control, Wrong setup, Spying, and Malicious operation. These attacks are not sufficient to prove the performance of an intrusion detection mechanism for identifying cyber threats in the industrial IoTs.
To identify an adversary who tries to insert useless data and detecting phishing and Botnet attack, Parra et al. [24] proposed distributed architecture using two deep learning approaches, namely, a Distributed CNN scheme and LSTM network. The DCNN is used in an IoT micro-security add-on, while the LSTM is used by the back-end server. The N-BaIoT dataset is employed in the evaluation of performance, where outcomes show an accuracy of 98% and 94.30% during the training phase and the testing phase, respectively. To detecting IoT malware, Haddad Pajouh et al. [22] designed an intrusion detection mechanism using a recurrent neural network. The proposed mechanism employs three stages; namely, collection data, feature extrication, and deep threat classifier. The results of the experiments demonstrate the highest accuracy of 98.18% under the 10-fold cross-validation analysis and efficient compared to conventional machine learning classifiers such as Naive Bayes, K-Nearest Neighbor, Random Forest, and Decision Tree. Koroniotis et al. [27] proposed a network forensics scheme, called PDF, for detecting and monitoring the attack patterns in IoT based networks. The PDF scheme is based on three stages, namely, (1) extracting data, (2) adapt parameters of deep learning, and (3) identify anomalous incidents. The particle swarm optimization algorithm is used in the second stage, whereas the deep neural model is used in the third stage. The experimental results reveal an accuracy of 99.9% compared to 93.2% with decision tree and 72.7% with naïve bayes.
NG and Selvakumar [29] proposed an anomaly detection framework based on vector convolutional deep learning technique. The authors proposed also that the computations are processed at the fog nodes. The experiments conducted on the UNSW Bot-IoT dataset show an accuracy of 99.71%, 99.80%, 99.92%, 77.22%, for DDoS attacks, DoS attacks, Reconnaissance attacks, and Theft attacks, respectively. Therefore, to detect cyber attacks in the Internet-of-Medical-Things (IMoT), Manimurugan et al. [26] introduced an intrusion detection mechanism using the deep belief network technique. The proposed mechanism is evaluated using the CICIDS 2017 dataset which shows an accuracy of 97.71% and 96.37% for PortScan attack and infiltration attack, respectively. Popoola et al. [31] developed a hybrid intrusion detection mechanism, called LAE-BLSTM, for the detection of botnets in IoT networks. The LAE-BLSTM mechanism uses deep Bidirectional Long Short-Term Memory (BLSTM) and Long Short-Term Memory Autoencoder (LAE). The LAE is used for the dimensionality reduction of the feature, while the BLSTM is used to identify the traffic of botnet attacks from benign traffic in IoT networks. The Bot-IoT dataset used in the evaluation of performance, which demonstrates that the LAE-BLSTM mechanism reached a data size reduction ratio of 91.89%.
3. IDS Implementation
In this section, we propose three deep learning-based IDS models for detection of cyber attacks in Agriculture 4.0, including recurrent neural network-based IDS model, convolutional neural network-based IDS model, and deep neural network-based IDS model.
3.1. Network Model
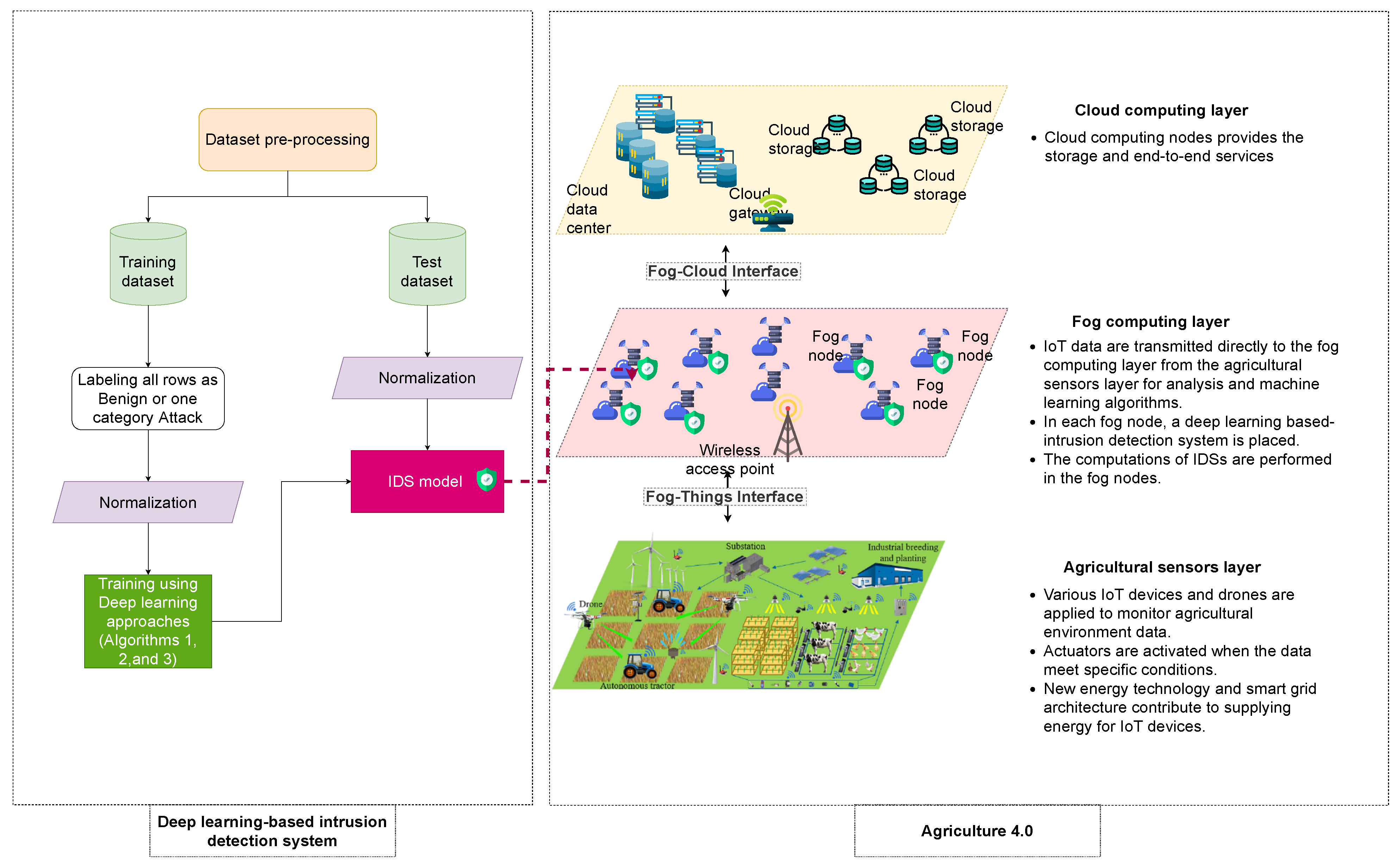
The considered network model of Agriculture 4.0 is presented in Figure 3, which is based on three layers, namely, (1) Agricultural sensors layer, (2) Fog computing layer, and (3) Cloud computing layer. The agricultural sensors layer consists of various IoT devices and drones applied to monitor agricultural environment data. Actuators are activated in the agricultural sensors layer when the data meet specific conditions. New energy technology and smart grid architecture are placed in the agricultural sensors layer for supplying energy for IoT devices. In each fog node, a deep learning based-intrusion detection system is placed. The IoT data are transmitted directly to the fog computing layer from the agricultural sensors layer for analysis and machine learning algorithms, while Cloud computing nodes provide the storage and end-to-end services. The computations of deep learning based-intrusion detection systems are performed in the fog nodes. We consider that there is a group of attackers that launch DDoS attacks in order to affect the functioning of the network, which can affect food safety, agri-food supply chain efficiency, and agricultural productivity.
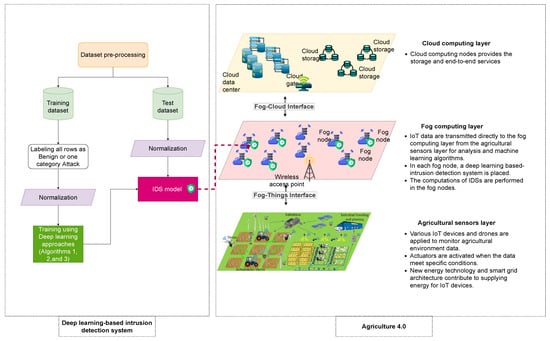
Figure 3.
The proposed deep learning-based IDS for DDoS attack in Agriculture 4.0.
3.2. Rnn-Based Ids
Recurrent neural networks, or RNN, are a category of neural networks for processing sequential data (i.e., a sequence of values , …, ). It allows the previous predictions to be used as inputs, using hidden states. The RNN is based on the multilayer perceptron which is an acyclic neural network structured in layers, namely, an input layer, one or more intermediate layers called hidden layers, and an output layer. The multilayer perceptron is described by the n layers that compose it and which are successive. The layer of multilayer perceptron is defined by: where is the number of neurons in the layer L. is the affine transformation defined by the vector and the matrix . Note that the is a bias vector, which is an additive set of weights in a neural network that requires no input.
For an input vector sequence containing the features of an input dataset of attacks with , we have an output vector sequence with by the initialization of the internal state vectors as follows:
and
Then, for each time step, all the layers of the network are recursively applied to the previous layer’s output vector:
To alleviate the vanishing gradient problem, there are two solution, namely, Gated recurrent units (GRUs) and Long short-term memory (LSTM). We use in our algorithm the LSTM which is one of the most popular RNN architectures to date. The LSTM is described as follows [36]:
Where is the forget gate, is the memory cell, is the input gate, is the output gate, and is the new hidden state.
The proposed RNN-based IDS architecture for detection of cyber attacks in Agriculture 4.0 is presented in Algorithm 1 which is written in Python language. The description of each functions used in Algorithms 1–3 are presented in Table 2.

Table 2.
Functions used in Algorithms 1–3.
| Algorithm 1 Build the model using RNN |
Input: , Initialization: Define Sequential model:
|
| Algorithm 2 Build the model using CNN |
Input: , Initialization: Define Sequential model:
|
| Algorithm 3: Build the model using DNN |
Input: , Initialization: Define Sequential model:
|
3.3. Cnn-Based Ids
Convolutional networks, also known as convolutional neural networks, or CNNs, represent a dedicated class of neural network for data processing with a familiar network structure. The name “convolutional neural network” means that the network uses a mathematical operation called convolution [37]. Therefore, a convolutional neural network structure is composed of a set of processing layers, as follows:
- The convolution layer (CONV) that manages the data from a receiver cell. There are three hyperparameters to dimension the volume of the convolution layer: the depth, stride, and zero-padding. The formula for calculating the number of neurons in the output volume is described as follows:where is the size of the input volume, S is the kernel field size of the convolutional layer neurons, M is the amount of zero padding, and P is the stride.
- The pooling layer (POOL), which enables to reduce the size of the intermediate image by compressing the information and operates on each feature map independently.
- The correction layer (Rectified Linear Unit, ReLU), which is often referred to as the “ReLU” in reference to the activation function. The ReLU applies the non-saturating activation function, which is described as follows:Note that there are other functions that can be used to increase nonlinearity, such as the sigmoid function, which is described as follows:
- The “fully connected” (FC) layer is a perceptron-type layer.
- The loss layer as the final layer of a neural network. Different loss functions can be used such as Euclidean loss, Softmax loss, and Sigmoid cross-entropy loss.
The proposed CNN-based IDS architecture for detection of cyber attacks in Agriculture 4.0 is presented in Algorithm 2 which is written in Python language.
3.4. Dnn-Based Ids
A deep neural network (DNN) is an artificial neural network (ANN) with more layers intermediate between input and output layers. The DNN consist of five-part: neurons, weights, synapses, biases, and functions. The inputs are linked with weights . The full-fledged deep learning system is based on multilayer perception (defined in RNN-based IDS) with the application of various activation functions that produce real values, rather than Boolean values as in the classical perceptron. To help to adjust the input weights and minimize the “loss”, the backpropagation algorithm is applied to performs iterative backward passes. The proposed DNN-based IDS architecture for detection of cyber attacks in Agriculture 4.0 is presented in Algorithm 3 which is written in Python language based on the following packages Pandas (https://pandas.pydata.org/pandas-docs/stable/ (accessed on 1 April 2021 )), NumPy (https://numpy.org (accessed on 1 April 2021)), SciPy (https://scipy.org (accessed on 1 April 2021)), TensorFlow (https://tensorflow.org/ (accessed on 1 April 2021)), and Keras (https://keras.io/ (accessed on 1 April 2021)).
4. Performance Evaluation
Agriculture 4.0 consists of integrating advanced technologies into existing farm operations to improve the quality and productivity of agricultural products. These advanced technologies include IoT devices, 5G communications, Drones, Fog/Edge computing, Cloud Computing, Artificial Intelligence, Network Function Virtualization, and Software-Defined Networking. Based on these technologies, we used and selected the most recent data sets that contain DDoS attack scenarios against these technologies used by Agriculture 4.0. Specifically, we used the following two new real traffic datasets, namely, CIC-DDoS2019 dataset [34] and TON_IoT dataset [35]. They are chosen for three reasons: (1) because they were built for a TCP/IP communication stack, (2) contain DDoS attacks, and (3) represent the nature of Agriculture 4.0 (in particular its IoT and IIoT sensors and cloud-edge traffic). The TON_IoT dataset was designed based on interacting network elements and IoT/IIoT systems with the three layers of Edge, Fog, and Cloud to simulate a real-world execution of current production IoT/IIoT networks. The NSX-VMware platform was utilized as Software-Defined Network (SDN) and Network Function Virtualisation (NFV) technologies to facilitate the management of the interaction between these three layers. The experiment is conducted on Google Colaboratory (https://colab.research.google.com (accessed on 1 April 2021 )) using python 3 with the Graphics Processing Unit (GPU) and TensorFlow.
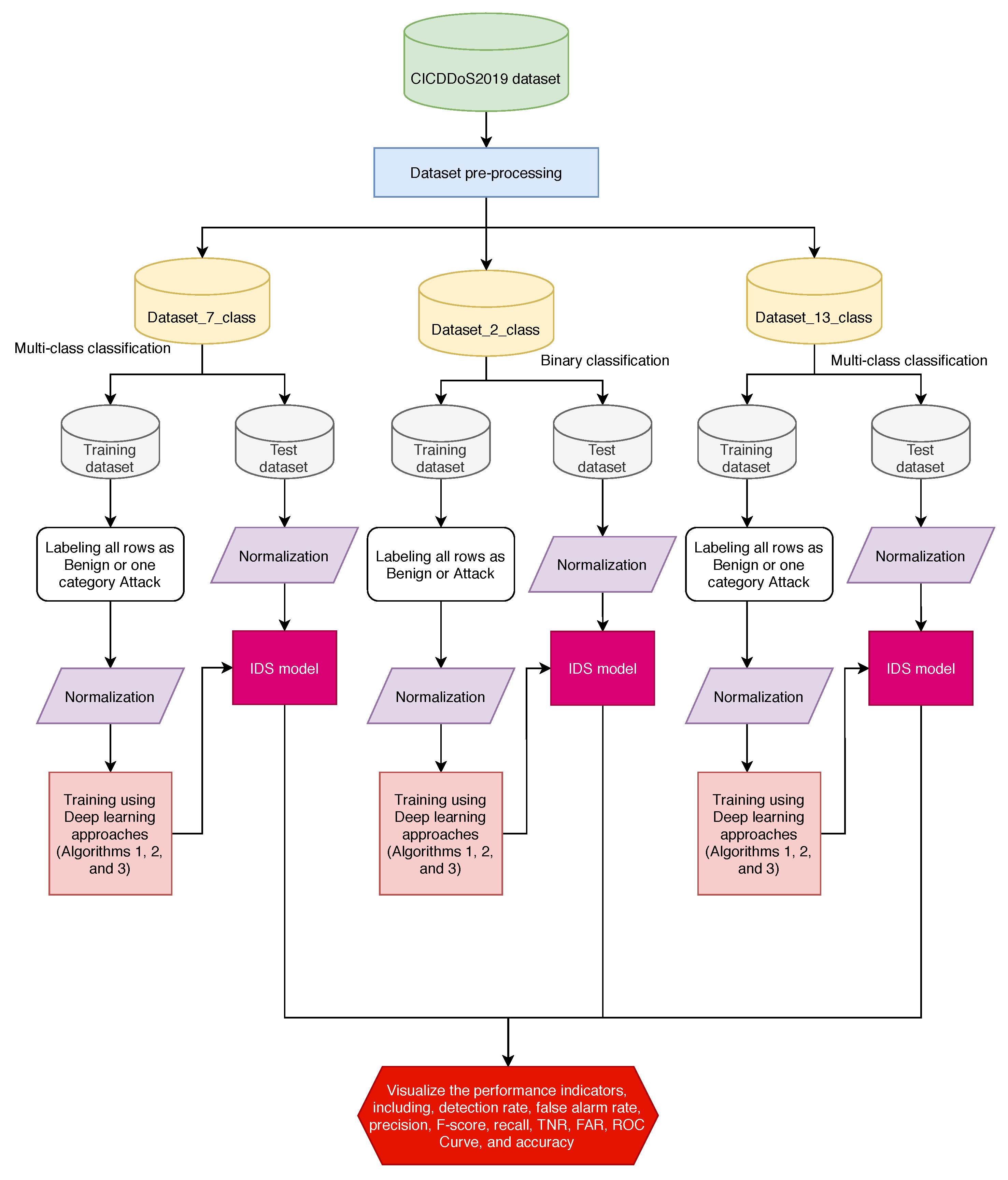
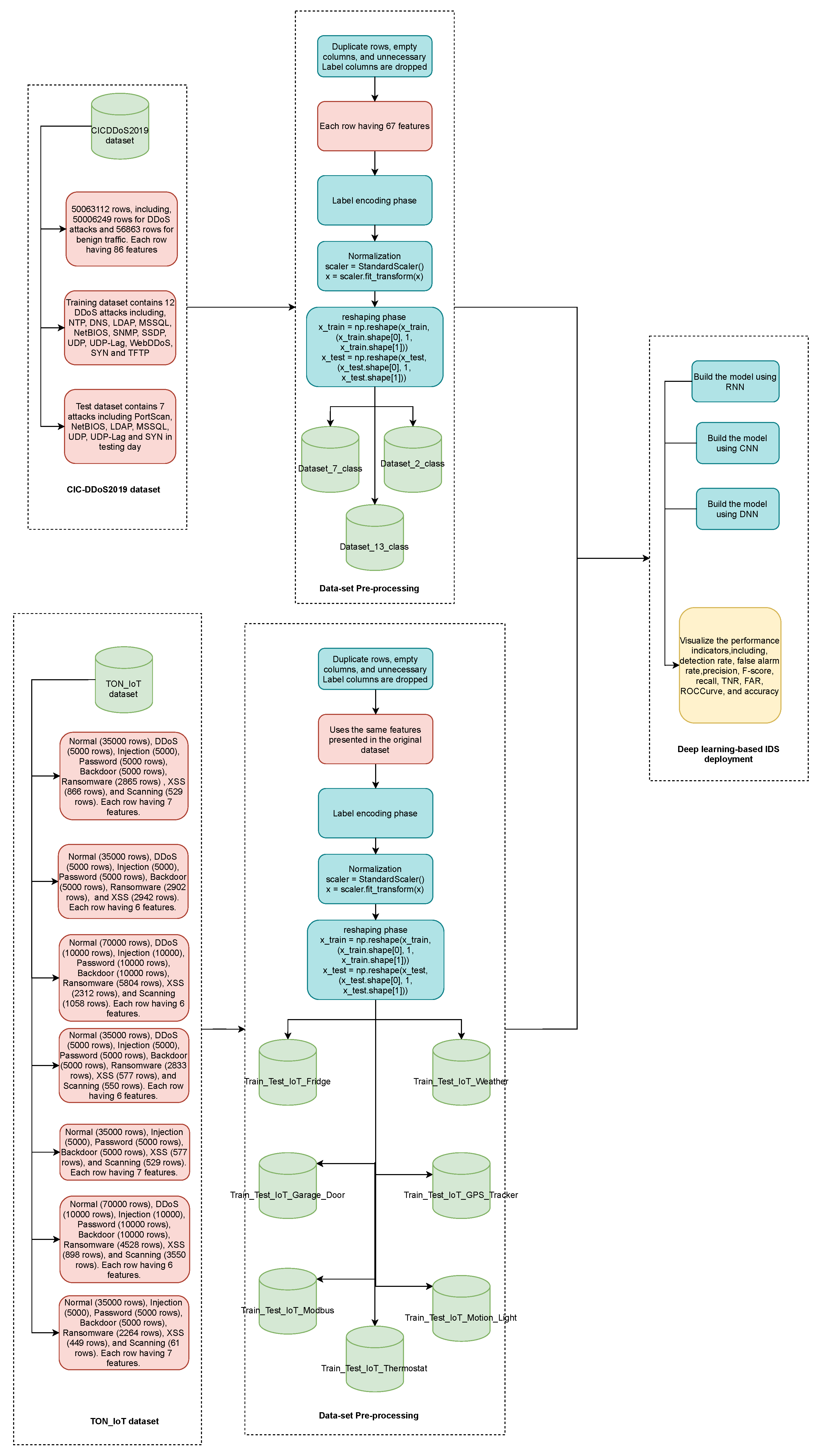
The details of the IDS experiment methodology are shown in Figure 4 and an overview of pre-processing of CIC-DDoS2019 dataset [34] and TON_IoT dataset [35] with the Deep learning-based IDS deployment is presented in Figure 5. More precisely, the approach is composed of four steps: (1) datasets step, (2) pre-processing step, (3) training step, and (4) testing step. The hyperparameters employed in deep learning strategies are shown in Table 3.
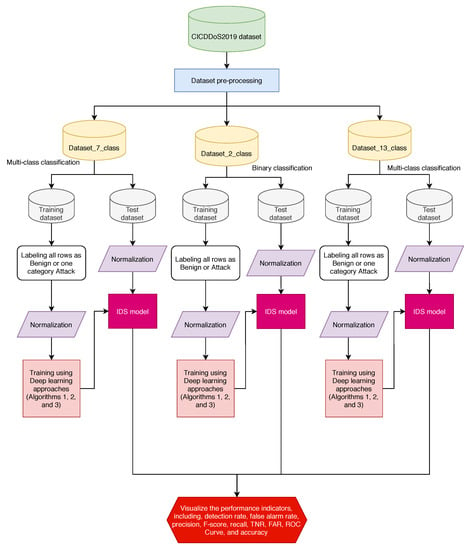
Figure 4.
Flowchart of the cyber security intrusion detection methodology.
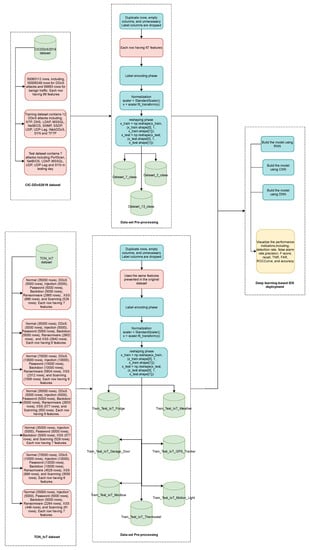
Figure 5.
Overview of pre-processing of CIC-DDoS2019 dataset [34] and TON_IoT dataset [35] with Deep learning-based IDS deployment.

Table 3.
The hyperparameters employed in deep learning approaches.
4.1. Pre-Processing of the Cic-Ddos2019 Dataset
The CIC-DDoS2019 dataset [34] includes 50,063,112 records, including, 50,006,249 rows for DDoS attacks and 56,863 rows for benign traffic. Each row having 86 features. The statistics for attacks in training and testing for the dataset are summarized in Table 4. The training dataset contains 12 DDoS attacks including, Network Time Protocol (NTP), Domain Name System (DNS), Lightweight Directory Access Protocol (LDAP), Microsoft SQL Server (MSSQL), NETwork Basic Input Output System (NetBIOS), Simple Network Management Protocol (SNMP), Simple Service Discovery Protocol (SSDP), User Datagram Protocol (UDP), UDP-Lag, WebDDoS, SYN and TFTP, while the test dataset contains seven attacks, namely, MSSQL, NetBIOS, PortScan, LDAP, UDP, UDP-Lag and SYN in testing day.

Table 4.
Attack types in CICDDoS2019 dataset.
- NTP-based attack: is a DDoS attack based on a reflection where an attacker uses Network Time Protocol (NTP) server functionality to flood a specific client-server or other networks with an increased quantity of UDP data traffic. This attack can make the destination and its network infrastructure unavailable to normal traffic.
- DNS-based attack: is a DDoS attack based on a reflection where an attacker uses a Botnet to create a large number of resolution requests to a targeted IP address.
- LDAP-based attack: is a DDoS attack based on a reflection where an attacker sends requests to a publicly available vulnerable LDAP server to generate large responses (amplified), reflected to a target server.
- MSSQL-based attack: is a DDoS attack based on a reflection where an attacker exploits the Microsoft SQL Server Resolution Protocol (MC-SQLR) by executing scripted requests using a forged IP address in order to appear as coming from the target server.
- NetBIOS-based attack: is a DDoS attack based on a reflection where an attacker sends spoofed “Name Release” or “Name Conflict” messages to a victim machine in order to refuse all NetBIOS network traffic.
- SNMP-based attack: This attack is a volumetric DDoS threat that uses the Simple Network Management Protocol (SNMP) to generate attack volumes of hundreds of gigabits per second in order to clog the target’s network pipes.
- SSDP-based attack: is a DDoS attack based on a reflection where an attacker sends an amplified amount of traffic to a targeted victim using Universal Plug and Play (UPnP) networking protocols.
- UDP-Lag-based attack: This attack aims to slow down/interrupt the targeted host with IP packets containing UDP datagrams.
- WebDDoS-based attack: This threat takes advantage of legitimate HTTP GET or POST queries to compromise a Web server or application.
- SYN-based attack: This attack exploits the normal TCP three-way handshake (i.e., sending SYN (synchronize), sending SYN-ACK (synchronize-acknowledge), and responds with an ACK (acknowledge)) to use resources on the targeted network server and make it unresponsive.
- TFTP-based attack: This attack exploits the Trivial File Transfer Protocol (TFTP) by employing TFTP servers connected to the internet. Specifically, an attacker performs a request by default for a file, and the victim TFTP server sends the data back to the requesting target host.
- PortScan-based attack: This attack performs a network security audit by conducting port scanning on a specific machine or on an entire network. The scanning is done using queries to determine which services are running on a remote host.
To analyze the efficiency of machine learning and deep learning strategies in terms of binary classification (i.e., Classification tasks with two classes) and multi-class classification (i.e., Classification tasks with more than two classes), We create three different datasets, named Dataset_2_class, Dataset_7_class, and Dataset_13_class. The statistics for attacks in training and testing for each dataset are summarized in Table 5, Table 6 and Table 7, respectively.

Table 5.
Attack types in Dataset_2_class.

Table 6.
Attack types in Dataset_7_class.

Table 7.
Attack types in Dataset_13_class.
4.2. Pre-Processing of the Ton_iot Dataset
The TON_IoT dataset [35] is a new testbed for an IIoT network that contains three types of data, namely, network data, operating systems data, and telemetry data [38]. The telemetry datasets of IoT and IIoT sensors are presented in 7 files as presented in Table 8. The contents of these files are described as following:

Table 8.
Attack types in TON_IoT dataset.
- File 1 “Train_Test_IoT_Weather”: It contains Normal (35,000 rows), DDoS (5000 rows), Injection (5000), Password (5000 rows), Backdoor (5000 rows), Ransomware (2865 rows), XSS (866 rows), and Scanning (529 rows). The file presents the IoT data of temperature measurements, pressure readings, and humidity readings of a weather sensor linked to the network.
- File 2 “Train_Test_IoT_Fridge”: It contains Normal (35,000 rows), DDoS (5000 rows), Injection (5000), Password (5000 rows), Backdoor (5000 rows), Ransomware (2902 rows), and XSS (2942 rows). The file presents the IoT data of temperature measurements and temperature conditions of a fridge sensor linked to the network.
- File 3 “Train_Test_IoT_Garage_Door”: It contains Normal (70,000 rows), DDoS (10,000 rows), Injection (10,000), Password (10,000 rows), Backdoor (10,000 rows), Ransomware (5804 rows), XSS (2312 rows), and Scanning (1058 rows). The file presents the IoT data of a door sensor linked to the network where the door is closed or open.
- File 4 “Train_Test_IoT_GPS_Tracker”: It contains Normal (35,000 rows), DDoS (5000 rows), Injection (5000), Password (5000 rows), Backdoor (5000 rows), Ransomware (2833 rows), XSS (577 rows), and Scanning (550 rows). The file presents the IoT data of latitude value and longitude value of GPS tracker sensor linked to the network.
- File 5 “Train_Test_IoT_Modbus”: It contains Normal (35,000 rows), Injection (5000), Password (5000 rows), Backdoor (5000 rows), XSS (577 rows), and Scanning (529 rows). The file presents the IoT data of Modbus function code that is responsible for reading an input register.
- File 6 “Train_Test_IoT_Motion_Light”: It contains Normal (70,000 rows), DDoS (10,000 rows), Injection (10,000), Password (10,000 rows), Backdoor (10,000 rows), Ransomware (4528 rows), XSS (898 rows), and Scanning (3550 rows). The file presents the IoT data of a light sensor that is either on or off.
- File 7 “Train_Test_IoT_Thermostat”: It contains Normal (35,000 rows), Injection (5000), Password (5000 rows), Backdoor (5000 rows), Ransomware (2264 rows), XSS (449 rows), and Scanning (61 rows). The file presents the IoT data of the current temperature reading of a thermostat sensor connected with the network.
4.3. Performance Metrics
The performance metrics chosen to evaluate machine learning and deep learning strategies is very important. In our study, we focus on the following important performance metrics: detection rate (DR), false alarm rate (FAR), precision, F-score, recall, TNR, FAR, ROC Curve, and accuracy. Table 9 illustrates four possibilities for both correct and erroneous classification.
where , , , and denote true positive, true negative, false positive, and false negative, respectively. The False Positive (FP) indicates the benign data that is incorrectly classified as an attack, while the True Negative (TN) indicates the benign data that is correctly classified as benign. The True Positive (TP) indicates the attack data that is correctly classified as an attack. The False Negative (FN) indicates the attack data that is incorrectly classified as benign.

Table 9.
Confusion matrix.
4.4. Results
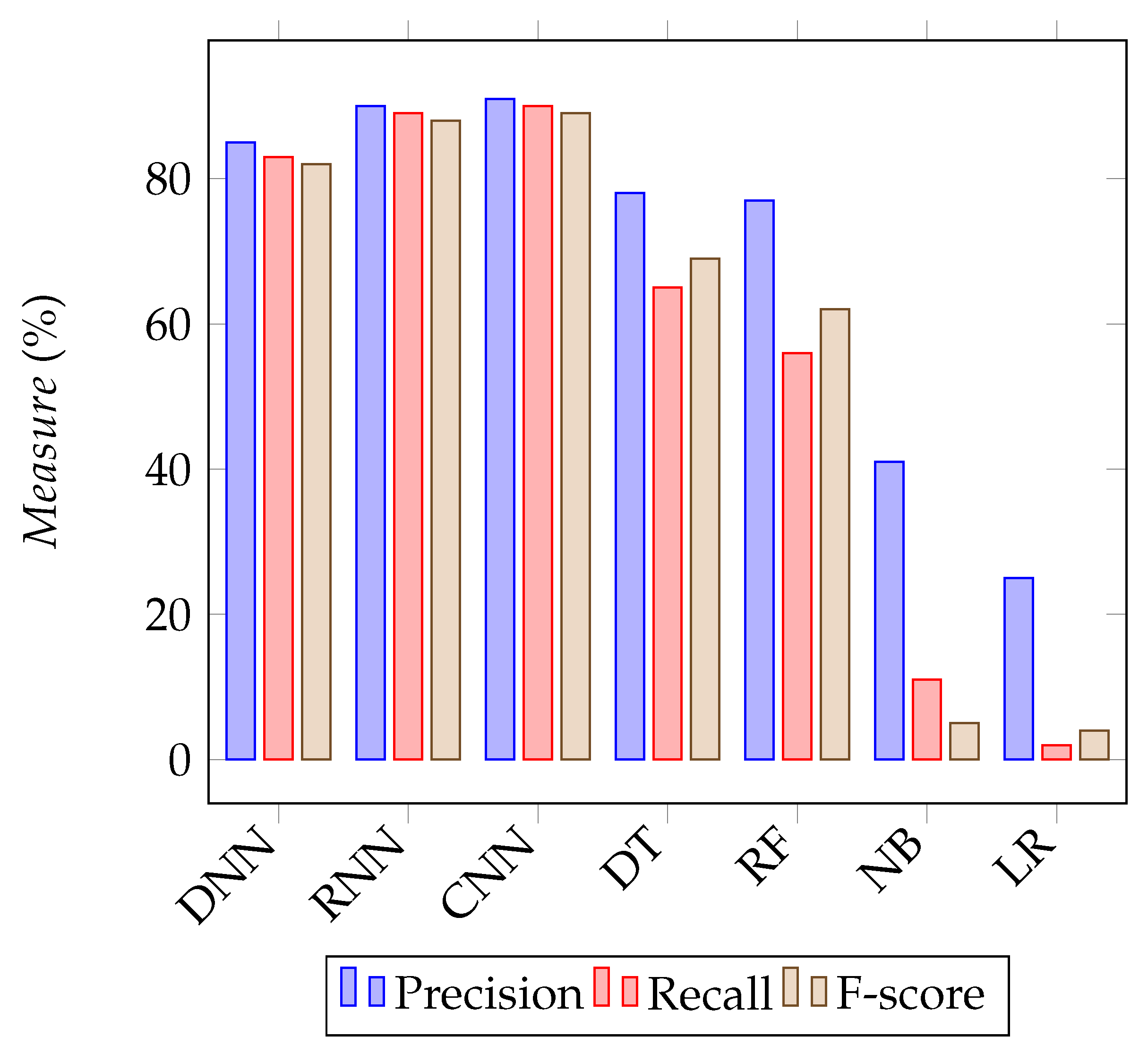
The performance of deep learning strategies relative to other machine learning strategies (i.e., DT: Decision Tree, RF: Random forests, NB: Naive Bayes, LR: Logistic Regression) in terms of Precision, Recall, and F-score are shown in Figure 6. In term of Precision, the deep learning techniques give good results in comparison to other machine learning strategies, namely, decision tree, random forests, naive bayes, and logistic regression, and the convolutional neural network model provides the higher ratio with 91%. Both in terms of Recall and F-score, deep learning techniques give good results in comparison to other machine learning strategies, in which the convolutional neural network model provides the higher ratio with 90% and 89%, respectively. The results show that deep learning techniques can provide better performance in cyber security intrusion detection for Agriculture 4.0.
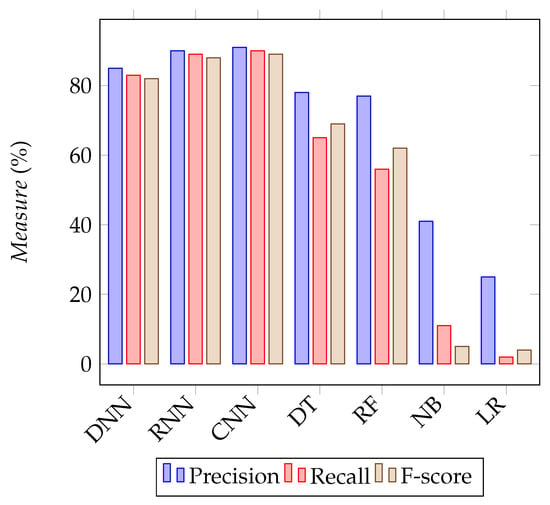
Figure 6.
The performance experimental results of deep learning approaches relative to other machine learning strategies in terms of Precision, Recall, and F-score.
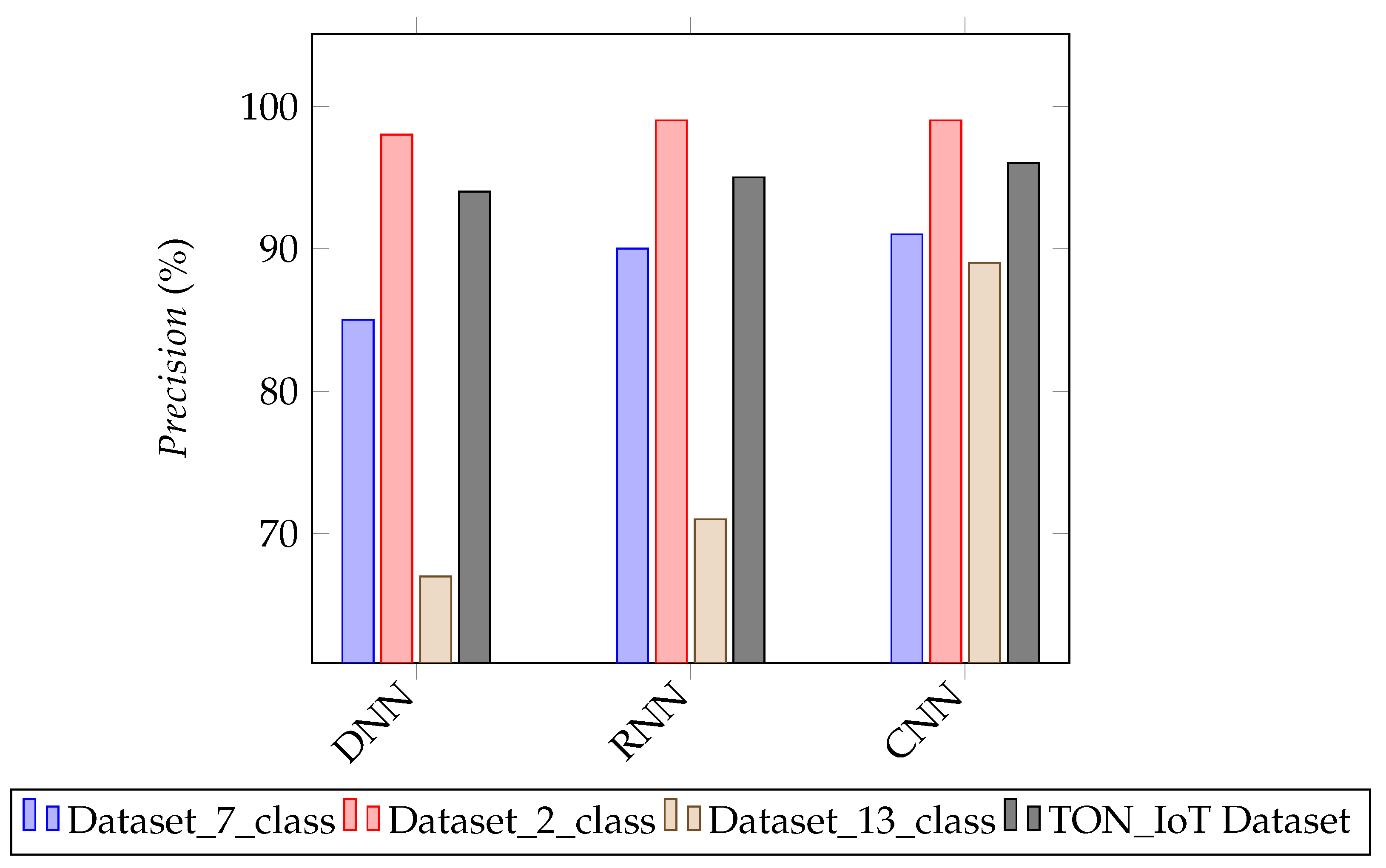
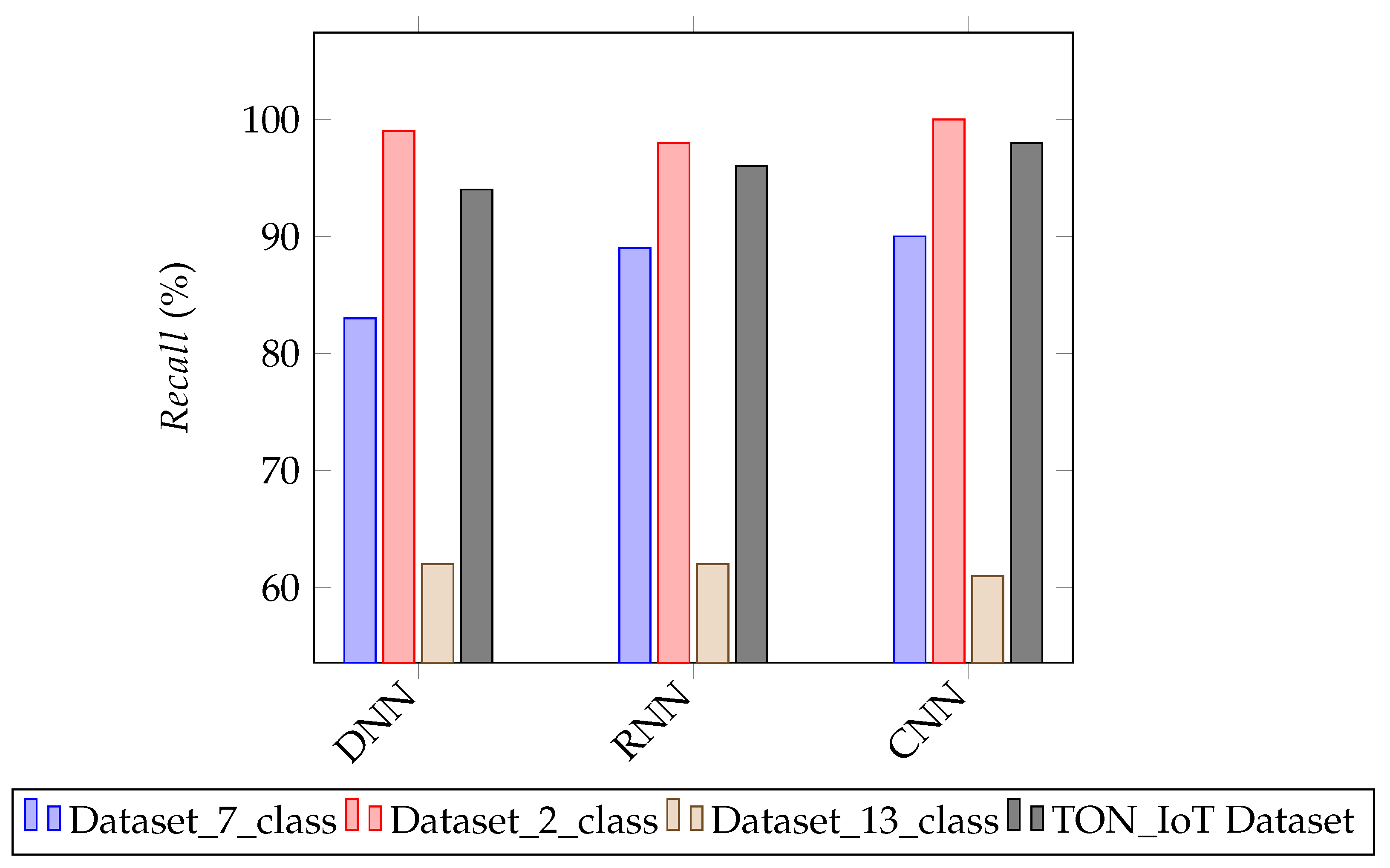
The performance experimental results of deep learning techniques in term of Precision under binary classification and multiclass classification are shown in Figure 7. The results show that deep learning techniques give a higher positive prediction in terms of binary classification compared to multiclass classification. Specifically, the convolutional neural network model achieves a precision of 99% in binary classification compared to 90% in multiclass classification. Therefore, the performance experimental results of deep learning techniques in term of Recall with binary classification compared to multiclass classification are shown in Figure 8. The results show that deep learning techniques give a higher positive prediction in terms of binary classification compared to multiclass classification. Specifically, the deep neural network model achieves a recall of 99% in binary classification compared to 83% and 62% in multiclass classification. In addition, the recurrent neural network model achieves an F-score of 99% in binary classification compared to 88% and 56% in multiclass classification.
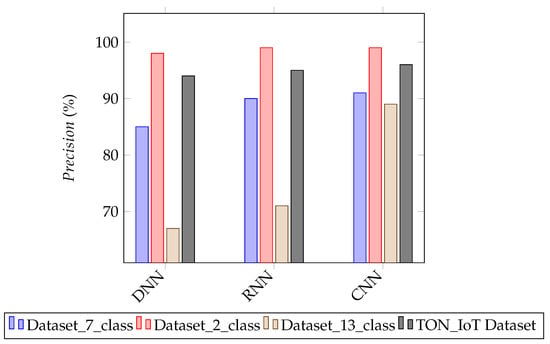
Figure 7.
The performance experimental results of deep learning approaches in term of Precision with binary classification and multiclass classification.
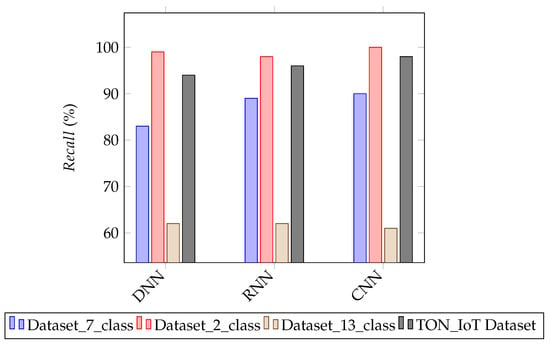
Figure 8.
The performance experimental results of deep learning approaches in term of Recall with binary classification and multiclass classification.
Table 10 presents the performance of deep learning approaches relative to benign and various types of attacks in Dataset_7_class (i.e., multi-class classification). We can observe that the convolutional neural network model provides the higher true negative rate with 99% and the highest detection rate for two attacks type, namely, DrDoS_LDAP and Syn. The deep neural network model gives the higher detection ratio for two attack types, namely, DrDoS_MSSQL and Syn. The recurrent neural network model gives the higher detection ratio for four attack types, namely, DrDoS_LDAP, DrDoS_NetBIOS, DrDoS_UDP, and Syn. In addition, we observe a low detection of UDP-lag attack and this is due to the low learning rate of this attack.

Table 10.
The performance experimental results of deep learning approaches relative to benign and various types of attacks in Dataset_7_class (Multi-class classification ).
Table 11 presents the performance of deep learning approaches relative to normal and various types of attacks in TON_IoT dataset (i.e., multi-class classification). We can observe that all three deep learning techniques provide a higher true negative rate. The recurrent neural network model gives a higher detection ratio for three attack types, namely, Injection, Password, and Scanning. The convolutional neural network gives the higher detection ratio for five attacks, namely, DDoS, Backdoor, Ransomware, XSS, and Scanning.

Table 11.
The performance experimental results of deep learning approaches relative to normal and various types of attacks in TON_IoT dataset (Multi-class classification).
Table 12 presents the performance of deep learning approaches relative to benign and various types of attacks in Dataset_13_class (i.e., multi-class classification). We can observe that all three deep learning techniques provide the higher true negative rate. The deep neural network model gives the higher detection ratio for five attack types, namely, DrDoS_DNS, DrDoS_NTP, DrDoS_SSDP, TFTP, and UDP-lag. The recurrent neural network model gives the higher detection ratio for four attack types, namely, DrDoS_MSSQL, DrDoS_NTP, DrDoS_NetBIOS, and DrDoS_UDP. The convolutional neural network gives the higher detection ratio for Syn attack with 65%. Therefore, we observe a low detection of WebDDoS attack and this is due to the low learning rate of this attack. For binary classification, we can be seen that that all three deep learning techniques provide the higher true negative rate with 99% and the highest detection rate with 100%, as presented in Table 13.

Table 12.
The performance experimental results of deep learning approaches relative to benign and various types of attacks in Dataset_13_class (Multi-class classification).

Table 13.
The performance experimental results of deep learning approaches relative in Dataset_2_class (Binary classification).
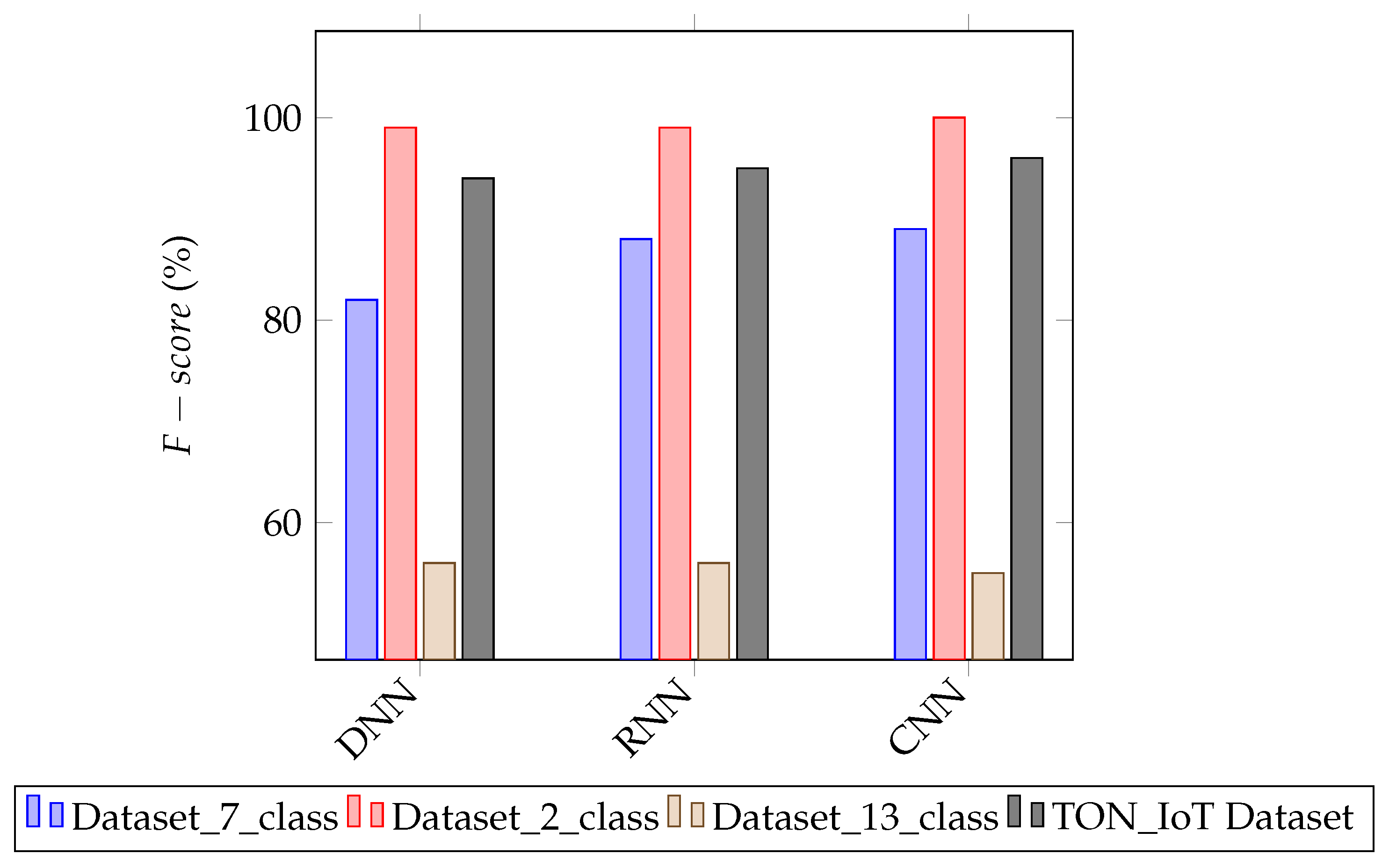
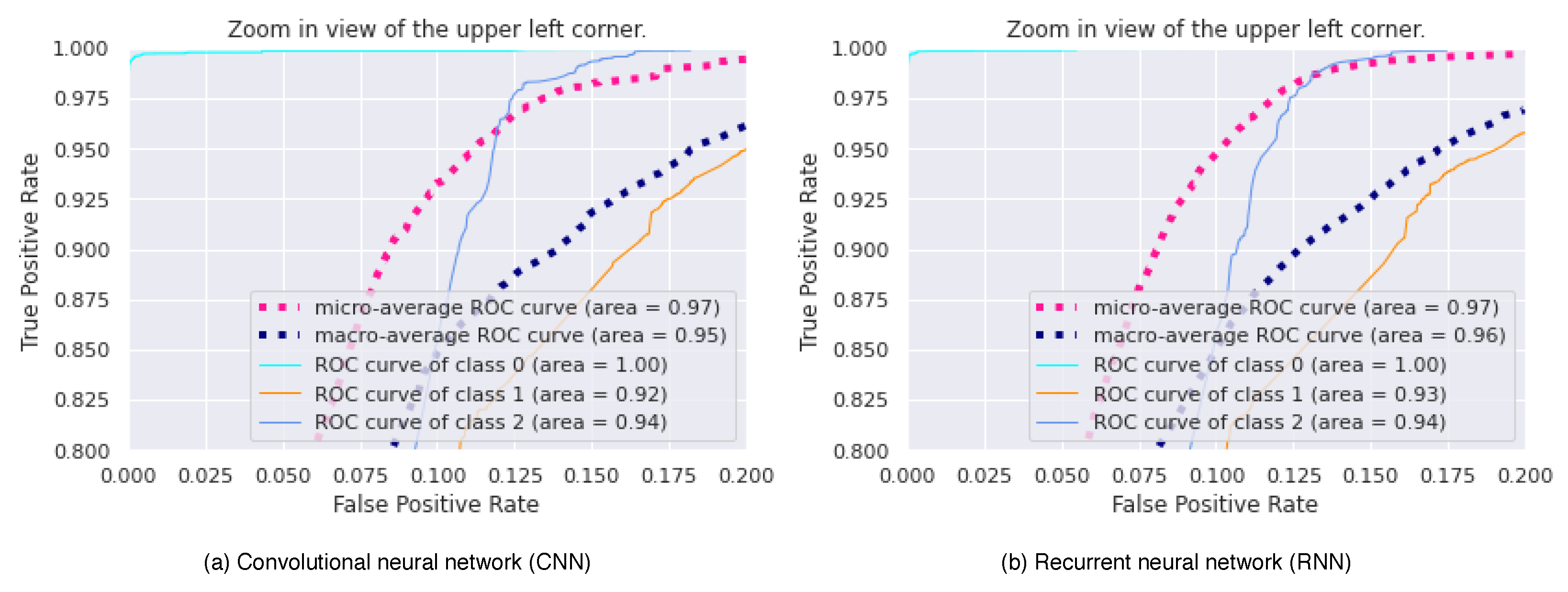
The performance experimental results of deep learning approaches in term of F-score with binary classification and multiclass classification are presented in Figure 9. The results show that deep learning techniques can provide better performance in cyber security intrusion detection for Agriculture 4.0. The Receiver Operating Characteristic (ROC) curve for Dataset_13_class is depicted in Figure 10, which is a plot of intrusion detection accuracy against the false positive probability. We can identify the obvious better performance of both deep learning techniques, namely, convolutional neural network and recurrent neural network, since all the values of AUC (Area Under Curve) for three classes, including, class 0: BENIGN, class 1: DrDoS_DNS, and class 2: DrDoS_LDAP, are between 0.94 and 1.00.
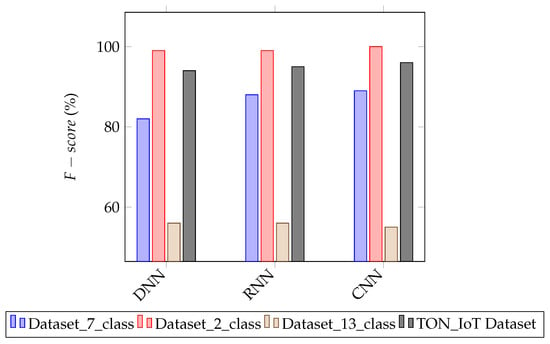
Figure 9.
The performance experimental results of deep learning approaches in term of F-score with binary classification and multiclass classification.
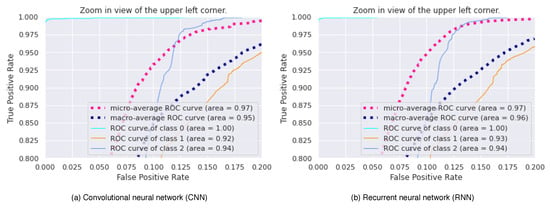
Figure 10.
The Receiver Operating Characteristic (ROC) for Dataset_13_class. class 0: BENIGN, class 1: DrDoS_DNS, class 2: DrDoS_LDAP.
Table 14 presents the accuracy, FAR, and training time of deep learning approaches with different hidden nodes and learning rates in four datasets; namely, Dataset_2_class, Dataset_7_class, Dataset_13_class, and TON_IoT dataset. In binary class classification (i.e., Dataset_2_class) and TON_IoT dataset, the convolutional neural network achieves high accuracy of 99.95% compared to both recurrent neural network and deep neural network, when the number of hidden nodes is 100 and the learning rate is 0.5. In multi-class classification (i.e., Dataset_7_class), the recurrent neural network achieves high accuracy of 93.88% compared to both deep neural network and convolutional neural network, when the learning rate is 0.5 and the number of hidden nodes is 30. In multi-class classification (i.e., Dataset_13_class), the convolutional neural network achieves high accuracy of 95.12% compared to both recurrent neural network and deep neural network, when the number of hidden nodes is 100 and the learning rate is 0.5. These results show that the recurrent neural network is efficient compared to the convolutional neural network with a lower number of hidden nodes.

Table 14.
The accuracy, FAR, and training time of deep learning approaches with different hidden nodes and learning rate in four datasets, namely, Dataset_2_class, Dataset_7_class, Dataset_13_class, and TON_IoT dataset.
Table 15 compares the performance of our work with other state-of-the-art methods that are tested under the CIC-DDoS2019 dataset and the TON_IoT dataset. The comparison is conducted with respect to network model, dataset, task, machine learning model, and accuracy. We can observe that our IDS model based on CNN incur the best results in terms of accuracy. This is due to the strategy of our pre-processing for both datasets that reduce the computation complexity and due to the use of simple deep learning models with larger batch sizes and fewer layers.

Table 15.
Comparison with related work tested on CIC-DDoS2019 dataset and TON_IoT dataset.
5. Conclusions
In this paper, we proposed three deep learning-based IDS models, including a convolutional neural network-based IDS model, a deep neural network-based IDS model, and a recurrent neural network-based IDS model. Specifically, we provided a performance evaluation and comparative analysis of machine learning and deep learning approaches for cyber security in agriculture 4.0. Each model’s performance is studied within two classification types (binary and multiclass) using two new real traffic datasets; namely, CIC-DDoS2019 dataset and TON_IoT dataset. The results show that deep learning techniques give good results in comparison to other machine learning strategies (e.g., decision tree, random forests, naive bayes, and logistic regression) in terms of important performance indicators, including detection rate, false alarm rate, precision, F-score, recall, true negative rate, false accept rate, ROC Curve, and accuracy. In addition, the IDS model based on CNN outperforms the state-of-the-art deep learning IDS methods, which were tested under the CIC-DDoS2019 dataset and TON_IoT dataset, by recording an accuracy of 99.95% for binary traffic detection and 99.92% for multiclass traffic detection.
Author Contributions
Conceptualization, M.A.F., L.S., H.D. and K.-K.R.C.; Methodology, M.A.F., L.S., H.D. and K.-K.R.C.; Software, M.A.F., L.S., and H.D.; Validation, M.A.F., L.S., and H.D.; formal analysis, M.A.F., L.S., and H.D.; investigation, M.A.F., L.S., and H.D.; resources, M.A.F., L.S., and H.D.; data curation, M.A.F., L.S., and H.D.; writing—original draft preparation, M.A.F., L.S., and H.D.; writing—review and editing, M.A.F., L.S.,and K.-K.R.C.; visualization, M.A.F., L.S.; supervision, M.A.F., L.S. and K.-K.R.C. All authors have read and agreed to the published version of the manuscript.
Funding
This work was supported in part by the Research Start-Up Fund for Talent Researcher of Nanjing Agricultural University under Grant 77H0603 and in part by the National Natural Science Foundation of China under Grant 62072248. The work of K.-K. R. Choo was supported only by the Cloud Technology Endowed Professorship.
Data Availability Statement
We used the CIC-DDoS2019 dataset and TON_IoT dataset, which are publicly accessed datasets (https://www.unb.ca/cic/datasets/ddos-2019.html, https://ieee-dataport.org/documents/toniot-datasets) (accessed on 1 April 2021), for the evaluation of the proposed IDS.
Conflicts of Interest
All authors declare no conflict of interest.
References
- Chen, B.; Wan, J.; Shu, L.; Li, P.; Mukherjee, M.; Yin, B. Smart factory of industry 4.0: Key technologies, application case, and challenges. IEEE Access 2017, 6, 6505–6519. [Google Scholar] [CrossRef]
- Friha, O.; Ferrag, M.A.; Shu, L.; Maglaras, L.; Wang, X. Internet of Things for the Future of Smart Agriculture: A Comprehensive Survey of Emerging Technologies. IEEE/CAA J. Autom. Sin. 2021, 8, 718–752. [Google Scholar] [CrossRef]
- Liu, Y.; Ma, X.; Shu, L.; Hancke, G.P.; Abu-Mahfouz, A.M. From Industry 4.0 to Agriculture 4.0: Current Status, Enabling Technologies, and Research Challenges. IEEE Trans. Ind. Inform. 2020, 17, 4322–4334. [Google Scholar] [CrossRef]
- Ferrag, M.A.; Shu, L.; Yang, X.; Derhab, A.; Maglaras, L. Security and Privacy for Green IoT-Based Agriculture: Review, Blockchain Solutions, and Challenges. IEEE Access 2020, 8, 32031–32053. [Google Scholar] [CrossRef]
- Yang, X.; Shu, L.; Chen, J.; Ferrag, M.A.; Wu, J.; Nurellari, E.; Huang, K. A Survey on Smart Agriculture: Development Modes, Technologies, and Security and Privacy Challenges. IEEE/CAA J. Autom. Sin. 2021, 8, 273–302. [Google Scholar] [CrossRef]
- Buczak, A.L.; Guven, E. A survey of data mining and machine learning methods for cyber security intrusion detection. IEEE Commun. Surv. Tutor. 2015, 18, 1153–1176. [Google Scholar] [CrossRef]
- Chen, J.W.; Lin, W.J.; Cheng, H.J.; Hung, C.L.; Lin, C.Y.; Chen, S.P. A smartphone-based application for scale pest detection using multiple-object detection methods. Electronics 2021, 10, 372. [Google Scholar] [CrossRef]
- Liao, H.J.; Lin, C.H.R.; Lin, Y.C.; Tung, K.Y. Intrusion detection system: A comprehensive review. J. Netw. Comput. Appl. 2013, 36, 16–24. [Google Scholar] [CrossRef]
- Muna, A.H.; Sitnikova, E. Developing a Security Testbed for Industrial Internet of Things. IEEE Internet Things J. 2020, 8, 5558–5573. [Google Scholar]
- Kasongo, S.M.; Sun, Y. A deep learning method with wrapper based feature extraction for wireless intrusion detection system. Comput. Secur. 2020, 92, 101752. [Google Scholar] [CrossRef]
- Hassan, M.M.; Gumaei, A.; Alsanad, A.; Alrubaian, M.; Fortino, G. A hybrid deep learning model for efficient intrusion detection in big data environment. Inf. Sci. 2020, 513, 386–396. [Google Scholar] [CrossRef]
- Li, B.; Wu, Y.; Song, J.; Lu, R.; Li, T.; Zhao, L. DeepFed: Federated Deep Learning for Intrusion Detection in Industrial Cyber-Physical Systems. IEEE Trans. Ind. Inform. 2020, 17, 5615–5624. [Google Scholar] [CrossRef]
- Gao, J.; Gan, L.; Buschendorf, F.; Zhang, L.; Liu, H.; Li, P.; Dong, X.; Lu, T. Omni SCADA intrusion detection using deep learning algorithms. IEEE Internet Things J. 2020, 8, 951–961. [Google Scholar] [CrossRef]
- Ferrag, M.A.; Maglaras, L. DeepCoin: A novel deep learning and blockchain-based energy exchange framework for smart grids. IEEE Trans. Eng. Manag. 2019, 67, 1285–1297. [Google Scholar] [CrossRef]
- Nie, L.; Ning, Z.; Wang, X.; Hu, X.; Li, Y.; Cheng, J. Data-Driven Intrusion Detection for Intelligent Internet of Vehicles: A Deep Convolutional Neural Network-based Method. IEEE Trans. Netw. Sci. Eng. 2020, 7, 2219–2230. [Google Scholar] [CrossRef]
- Abusitta, A.; Bellaiche, M.; Dagenais, M.; Halabi, T. A deep learning approach for proactive multi-cloud cooperative intrusion detection system. Future Gener. Comput. Syst. 2019, 98, 308–318. [Google Scholar] [CrossRef]
- Kamilaris, A.; Prenafeta-Boldú, F.X. Deep learning in agriculture: A survey. Comput. Electron. Agric. 2018, 147, 70–90. [Google Scholar] [CrossRef]
- Top 8 Challenges for Machine Learning Practitioners. Available online: https://towardsdatascience.com/top-8-challenges-for-machine-learning-practitioners-c4c0130701a1 (accessed on 1 May 2021).
- Ferrag, M.A.; Maglaras, L.; Janicke, H.; Smith, R. Deep learning techniques for cyber security intrusion detection: A detailed analysis. In Proceedings of the 6th International Symposium for ICS & SCADA Cyber Security Research 2019, Athens, Greece, 10–12 September 2019; pp. 126–136. [Google Scholar]
- Diro, A.A.; Chilamkurti, N. Distributed attack detection scheme using deep learning approach for Internet of Things. Future Gener. Comput. Syst. 2018, 82, 761–768. [Google Scholar] [CrossRef]
- Muna, A.H.; Moustafa, N.; Sitnikova, E. Identification of malicious activities in industrial internet of things based on deep learning models. J. Inf. Secur. Appl. 2018, 41, 1–11. [Google Scholar]
- HaddadPajouh, H.; Dehghantanha, A.; Khayami, R.; Choo, K.K.R. A deep recurrent neural network based approach for internet of things malware threat hunting. Future Gener. Comput. Syst. 2018, 85, 88–96. [Google Scholar] [CrossRef]
- Vinayakumar, R.; Alazab, M.; Srinivasan, S.; Pham, Q.V.; Padannayil, S.K.; Simran, K. A visualized botnet detection system based deep learning for the Internet of Things networks of smart cities. IEEE Trans. Ind. Appl. 2020, 56, 4436–4456. [Google Scholar] [CrossRef]
- Parra, G.D.L.T.; Rad, P.; Choo, K.K.R.; Beebe, N. Detecting Internet of Things attacks using distributed deep learning. J. Netw. Comput. Appl. 2020, 163, 102662. [Google Scholar] [CrossRef]
- Latif, S.; Zou, Z.; Idrees, Z.; Ahmad, J. A Novel Attack Detection Scheme for the Industrial Internet of Things Using a Lightweight Random Neural Network. IEEE Access 2020, 8, 89337–89350. [Google Scholar] [CrossRef]
- Manimurugan, S.; Al-Mutairi, S.; Aborokbah, M.M.; Chilamkurti, N.; Ganesan, S.; Patan, R. Effective Attack Detection in Internet of Medical Things Smart Environment Using a Deep Belief Neural Network. IEEE Access 2020, 8, 77396–77404. [Google Scholar] [CrossRef]
- Koroniotis, N.; Moustafa, N.; Sitnikova, E. A new network forensic framework based on deep learning for Internet of Things networks: A particle deep framework. Future Gener. Comput. Syst. 2020, 110, 91–106. [Google Scholar] [CrossRef]
- Zhou, X.; Hu, Y.; Liang, W.; Ma, J.; Jin, Q. Variational LSTM enhanced anomaly detection for industrial big data. IEEE Trans. Ind. Inform. 2020, 17, 3469–3477. [Google Scholar] [CrossRef]
- Bhuvaneswari Amma, N.G.; Selvakumar, S. Anomaly detection framework for Internet of things traffic using vector convolutional deep learning approach in fog environment. Future Gener. Comput. Syst. 2020, 113, 255–265. [Google Scholar]
- Khoa, T.V.; Saputra, Y.M.; Hoang, D.T.; Trung, N.L.; Nguyen, D.; Ha, N.V.; Dutkiewicz, E. Collaborative learning model for cyberattack detection systems in iot industry 4.0. In Proceedings of the 2020 IEEE Wireless Communications and Networking Conference (WCNC), Seoul, Korea, 25–28 May 2020; pp. 1–6. [Google Scholar]
- Popoola, S.I.; Adebisi, B.; Hammoudeh, M.; Gui, G.; Gacanin, H. Hybrid Deep Learning for Botnet Attack Detection in the Internet of Things Networks. IEEE Internet Things J. 2021, 8, 4944–4956. [Google Scholar] [CrossRef]
- Al-Hawawreh, M.; Moustafa, N.; Garg, S.; Hossain, M.S. Deep Learning-enabled Threat Intelligence Scheme in the Internet of Things Networks. IEEE Trans. Netw. Sci. Eng. 2020. [Google Scholar] [CrossRef]
- Ge, M.; Syed, N.F.; Fu, X.; Baig, Z.; Robles-Kelly, A. Towards a deep learning-driven intrusion detection approach for Internet of Things. Comput. Netw. 2021, 186, 107784. [Google Scholar] [CrossRef]
- Sharafaldin, I.; Lashkari, A.H.; Hakak, S.; Ghorbani, A.A. Developing realistic distributed denial of service (DDoS) attack dataset and taxonomy. In Proceedings of the 2019 International Carnahan Conference on Security Technology (ICCST), Chennai, India, 1–3 October 2019; pp. 1–8. [Google Scholar]
- TON_IOT DATASETS. Available online: https://ieee-dataport.org/documents/toniot-datasets (accessed on 4 April 2021).
- DiPietro, R.; Hager, G.D. Deep learning: RNNs and LSTM. In Handbook of Medical Image Computing and Computer Assisted Intervention; Elsevier: Amsterdam, The Netherlands, 2020; pp. 503–519. [Google Scholar]
- LeCun, Y.; Bengio, Y.; Hinton, G. Deep learning. Nature 2015, 521, 436–444. [Google Scholar] [CrossRef] [PubMed]
- Alsaedi, A.; Moustafa, N.; Tari, Z.; Mahmood, A.; Anwar, A. TON_IoT telemetry dataset: A new generation dataset of IoT and IIoT for data-driven Intrusion Detection Systems. IEEE Access 2020, 8, 165130–165150. [Google Scholar] [CrossRef]
- Jia, Y.; Zhong, F.; Alrawais, A.; Gong, B.; Cheng, X. Flowguard: An intelligent edge defense mechanism against IoT DDoS attacks. IEEE Internet Things J. 2020, 7, 9552–9562. [Google Scholar] [CrossRef]
- Li, J.; Liu, M.; Xue, Z.; Fan, X.; He, X. Rtvd: A real-time volumetric detection scheme for ddos in the internet of things. IEEE Access 2020, 8, 36191–36201. [Google Scholar] [CrossRef]
- de Assis, M.V.; Carvalho, L.F.; Rodrigues, J.J.; Lloret, J.; Proença, M.L., Jr. Near real-time security system applied to SDN environments in IoT networks using convolutional neural network. Comput. Electr. Eng. 2020, 86, 106738. [Google Scholar] [CrossRef]
- Alamri, H.A.; Thayananthan, V. Bandwidth Control Mechanism and Extreme Gradient Boosting Algorithm for Protecting Software-Defined Networks Against DDoS Attacks. IEEE Access 2020, 8, 194269–194288. [Google Scholar] [CrossRef]
- Zhang, Y.; Xu, J.; Wang, Z.; Geng, R.; Choo, K.K.R.; Pérez-Díaz, J.A.; Zhu, D. Efficient and Intelligent Attack Detection in Software Defined IoT Networks. In Proceedings of the 2020 IEEE International Conference on Embedded Software and Systems (ICESS), Shanghai, China, 10–11 December 2020; pp. 1–9. [Google Scholar]
- Kumar, P.; Gupta, G.P.; Tripathi, R. TP2SF: A Trustworthy Privacy-Preserving Secured Framework for sustainable smart cities by leveraging blockchain and machine learning. J. Syst. Archit. 2021, 115, 101954. [Google Scholar] [CrossRef]
- Pontes, C.; Souza, M.; Gondim, J.; Bishop, M.; Marotta, M. A new method for flow-based network intrusion detection using the inverse Potts model. IEEE Trans. Netw. Serv. Manag. 2021. [Google Scholar] [CrossRef]
- Assis, M.V.; Carvalho, L.F.; Lloret, J.; Proença, M.L., Jr. A GRU deep learning system against attacks in software defined networks. J. Netw. Comput. Appl. 2021, 177, 102942. [Google Scholar] [CrossRef]
- Kumar, P.; Gupta, G.P.; Tripathi, R. An ensemble learning and fog-cloud architecture-driven cyber-attack detection framework for IoMT networks. Comput. Commun. 2021, 166, 110–124. [Google Scholar] [CrossRef]
- Javeed, D.; Gao, T.; Khan, M.T. SDN-Enabled Hybrid DL-Driven Framework for the Detection of Emerging Cyber Threats in IoT. Electronics 2021, 10, 918. [Google Scholar] [CrossRef]
- Nie, L.; Wu, Y.; Wang, X.; Guo, L.; Wang, G.; Gao, X.; Li, S. Intrusion Detection for Secure Social Internet of Things Based on Collaborative Edge Computing: A Generative Adversarial Network-Based Approach. IEEE Trans. Comput. Soc. Syst. 2021. [Google Scholar] [CrossRef]
- Kumar, R.; Kumar, P.; Tripathi, R.; Gupta, G.P.; Gadekallu, T.R.; Srivastava, G. Sp2f: A secured privacy-preserving framework for smart agricultural unmanned aerial vehicles. Comput. Netw. 2021, 187, 107819. [Google Scholar] [CrossRef]
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).