Abstract
This paper examines the flocking control issue of the Cucker–Smale model in the presence of denial-of-service (DoS) attacks and communication delays. In the setting of DoS attacks, the attacker only obstructs the information communication between agents during the activation phases, while it concentrates on supplying its own energy during the dormancy phases. Furthermore, the communication delays are assumed to be time-varying and heterogeneous. Firstly, a general control input scheme that defends against DoS network attacks and communication delays is constructed. Secondly, on the basis of the presented control input and the properties of graph theory, the flocking control issue is equivalently transformed into a products convergence issue of infinite sub-stochastic matrices. Finally, an algebraic condition is obtained to formulate all the agents that asymptotically achieve the flocking behavior. Moreover, the obtained theoretical results are verified by a numerical example.
1. Introduction
In the past few decades, an increasing number of scholars have begun to apply the laws of the biological world to science and technology, and attention has been directed to the collective control behavior of multi-agent systems (MASs), which is motivated by the collective behaviors of nature, such as bird migration, predation by wolves, ant colonies etc. These collective behaviors have attracted great attention on account of their outstanding practicability, potential value, and versatility in industrial applications and engineering. Hence, these collective behaviors are fundamental in being established by workable mathematical models for the purposes of further discussions and applications.
Flocking is an emblematic, collective behavior that has received extensive attention and has been applied in several scientific disciplines, such as multi-robot systems [1], the formation of unmanned aerial vehicles [2,3], and the opinion dynamics of social networks [4,5]. The flocking model has several principal evolution and optimization stages. Vicsek [6] created a mathematical model of flocking behavior, which has been a great help for follow-up research. Subsequently, Cucker and Smale [7] put forward the Cucker–Smale (C–S) model to estimate the flocking behavior of natural networks, specifically for the flocking of birds and the swarming of locusts. In this C–S model, the intimate relationship between individuals is quantified by a weight function that is related to distance. Based on the theory of biological evolution, Darwin [8] claimed that the intimacy between individuals is related to density. The distance between members of a population is a crucial indication of population density. Specifically, increasing the population density is often as a result of the interaction distance between individuals decreasing. Meanwhile, a prominent characteristic of the flocking behavior model is to quantify population intimacy by using a weight function that takes distance into account. It is worth noting that this makes the C–S model more in line with the natural laws in the biological world. In order to study these collective behaviors more deeply and to apply them to the engineering field, the C–S model has been extensively investigated by scholars [9,10,11,12]. The literature [13] has proposed a stochastic flocking strategy that is utilized under randomly switching network topologies. Further, the work of [14] explored the collective behavior determined via the C–S model in a random environment. One study, by [15], addressed the flocking under hierarchical leadership topologies. In addition, the flocking control issue for a multi-agent network with lossy links was discussed in [16].
Since wireless communication in multi-agent networks is of a broadcasting type in nature, it is vulnerable to a variety of destructive attacks. Denial-of-service (DoS) attacks present one of the most universal and destructive forms in which the information transmissions of a system are obstructed, and where communication channels are interfered with and data packets are lossed. It is especially impossible to completely defend against DoS attacks for all channels of MASs; this is because the information transmission between individuals in a multi-agent system is relatively independent. DoS attacks pose a serious threat to the security control of a system as they lead to system instability or even complete collapse. Consequently, the control issue of MASs under DoS attacks has witnessed a growing interest in the past few years [17,18]. The work of [19] studied the impulsive controllers in cyber-physical multi-agent systems when subjected to a general type of DoS signals. Considering the security control problem of a class of network systems in the presence of DoS network attacks, a novel resilient triggering protocol was demonstrated in [20]. The consensus issue regarding MASs in presence of DoS attacks was investigated in [21]. This paper [22] mainly studied the network attack problem of power systems, including various detectable (e.g., false data injection, denial-of-service) and stealth (replay, bias injection) attacks. The parametric uncertainty of a multi-area load frequency control system was discussed in [23]. As we know, flocking control that does not take DoS attacks into consideration has many published results [13,14,15,16]. Up to now, in the literature, there have been relatively few valuable results that consider the flocking control about multi-agent collective behavior when under DoS attacks. It is unknown whether these control strategies are effective when the system is attacked. In light of this, proposing a unique-state update mechanism for the C–S model’s flocking behavior under DoS attacks is intriguing, and it is this fact that is the primary driving force behind this work.
We have studied the flocking control in [24], which is based on DoS network attacks, before. As for this present work, we analyze a similar problem but in the presence of communication delays. In fact, there is a delay in multi-agent communication, information interactions between agents cannot be propagated infinitely, and they are receipted after a short time delay because of the constrained transmission speed. Therefore, it is also natural to admit that individuals receive and process information after delays. A small delay could have an impact on the system enforcement and stability. Meanwhile, delays in information transmission and processing are acknowledged to exist in engineer systems as in robotics and spacecrafts [25,26]. Due to these practical issues, scholars have obtained a large number of research results for the collective behaviors between agents with various delays. Considering the second-order discrete-time MASs, the consensus behavior of this was discussed in [27]. Further, the work of [28] studied the leader-following consensus for MASs under input time delays. The work of [29] discussed the consensus tracking problem with state time delays, as well as developed an effective strategy. In addition, the consensus issue of discrete-time MASs with interactions delays was designed in [30]. Reference [31] investigated a distributed dynamic tracking control strategy for the communication delays of MASs. Through considering packet loss and communication delay problems, tracking consistency regulation was developed in [32]. The containment control of first-order MASs are subject to communication delays, and this problem was solved in [33]. Further, for high-order MASs, the work of [34] discussed the containment control under fixed time delays. The work of [35] proposed fully distributed stated update protocols to ensure the solvability of the containment control issues of MASs. It can be seen that the research on the collective behaviors of MASs in the case of delays has achieved many valuable results, but these results mainly focused on consensus control, tracking control, and contain control. It is remarkable that there are few results regarding flocking control in the presence of delays. Generally, agents cannot immediately respond to the received information in practical engineering, and they are limited by the finite speeds of information transmission and spreading. That is to say, there are time delays in the process of receiving and processing information by agents. Therefore, there is important theoretical value and practical significance in experimenting with the flocking control issue under time delays.
The above existing pieces of literature inspire us to explore the flocking control issues of MASs under DoS attacks and communication delays. Such an endeavor can reveal, in detail, not only the inner rules of collective behavior, but it can also provide a theoretical basis for communication delay and network attack issues in practical engineering applications. The following is a summary of the major contributions.
- (1)
- The weight function model proposed in this paper is more general; it only needs to be positive in its decreasing functions with positive lower bounds, and it does not need specific function forms. Different from the most existing results [36,37,38,39,40,41] that are only suitable for a weight function with strict specific forms, our model is more versatile in engineering application scenarios.
- (2)
- Most of the available published works [9,10,12,14,15,16] on the flocking control of the C–S model only use an ideal simplified model that ignores the effects of DoS attacks and communication delays, which are inevitable in communication devices that operate between agents. This paper takes both into account, which can help us to study flocking behaviors in nature and can help us to apply it to engineering applications.
- (3)
- The topology structure of the network is complicated and time-varying, which complicates the feasibility and stability investigation of the C–S model. To address this problem, we transformed the realization of the flocking behavior of the C–S model into a convergence issue of the error system. An effective approach regarding the products of sub-stochastic matrices is original, as well as producing an analysis of the errors and achieving a model of flocking behavior. All the individuals finally realized the flocking behavior, and the expression of the convergence rate for each agent is given.
The remainder of this paper is broken down into the following sections to allow for a complete analysis of this significant issue. The theoretical foundations and some brief concepts about digraph theory are introduced in Section 2. Section 3 is concerned with the Cucker–Smale model and the control protocol. In addition, the DoS model time-varying and heterogeneous delays models are also developed in this section. Section 4 presents the main findings of the research, focusing on the three key themes regarding the convergence of agent velocities and positions. Further, the sufficient conditions for developing flocking behavior and the proofs for this are shown in this section. Subsequently, a numerical simulation is shown in Section 5 to illustrate the proposed approach. Finally, Section 6 includes the final observations.
2. Mathematical Preliminaries
2.1. Notations
Let , denote the p-dimensional real column vectors and the real matrices. means a column vector with p ones, and presents an p-dimensional identity matrix. A diagonal matrix with the diagonal elements is denoted by . Let be the Euclidean norm, and represents the absolute value of a number. The matrix is nonnegative while . According to the relative properties of graph theory, the infinite norm of matrix A is defined by . Let represent a block matrix that includes the first r rows and the first s columns of this matrix. The sum of the ith row for matrix A is expressed as . If its row sum satisfies , it is called a row-stochastic matrix. Furthermore, it is sub-stochastic if .
2.2. Signed Digraph
Signed digraphs effectively describe the communication and information interactions between individuals. When considering a signed digraph , it consists of the vertices and edges . In particular, denotes the vertices set, and presents the edge set. For the arbitrary vertexes and , the edge is presented if and only if receives information from vertex . We excluded self-loops in this paper, i.e., . In addition, the neighbor set of the node is described as . In accordance with this, the adjacency matrix is denoted as , where , if and only if , otherwise In addition, the Laplacian matrix is manifested as , where and . In addition, based on the theoretical analysis of the degree matrix, the degree matrix of graph is relevant to the Laplacian matrix and adjacency matrix. The expression is . Let denote a directed path from to , which is represented by a sequence of finite non-null edges
where are distinct nodes. It is worth noting that the distance from to (denoted by ) is equal to the number of edges in the shortest path from to .
Remark 1.
In this study, we use the assumption that the system consists of n followers and one leader. For each node , , if it has no neighbors set, it is generally referred to as the leader, otherwise it is the follower. The leader transmits information to the followers through the communication channels, but does not receive any information in return. In this paper, it is acknowledged that networks have a forest topology with roots at the leader. It is admitted that each arbitrary follower has at least one direct channel from the leader.
2.3. Periodic DoS Attacks Model
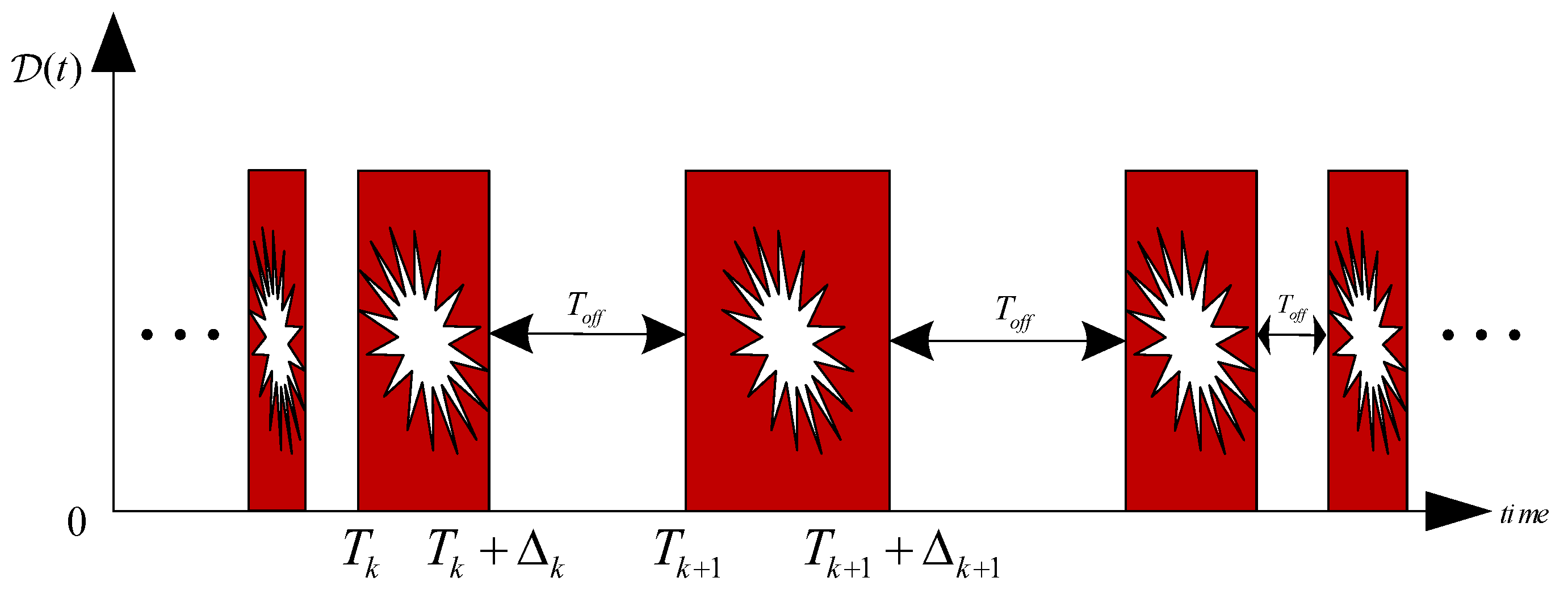
The security control of MASs are often substantially threatened by network attacks, among which DoS is a representative type. DoS attacks always lead to communication interruption, packet loss, etc. In most previous studies (e.g., [42,43]), the probability of occurrence for these problems occurs according to a specific probability distribution. This is relatively easy to detect for defenders, who reduce the difficulty of defense. In general, it is hence undeniable that it is impossible for an attacker to interrupt the system regularly. In contrast, attackers are random and difficult to detect in practical engineering. Successive attacks not only consume a lot of energy, but are also easily detected by defenders. In light of this, reference [44] developed an universal assault model that makes no assumptions about the underlying attack technique and in which the attacker’s actions are only limited by the frequency and duration of DoS attacks. Consequently, there is no doubt that the adversaries are random and have restricted energy when a DoS jamming attack is launched against the system. Therefore, it is reasonable to consider that the adversaries have limited energy and are random when launching DoS jamming attacks. In general, adversaries always want to attack more network channels with less attack energy by using advanced jamming techniques. The time sequences of DoS attacks is shown in Figure 1.
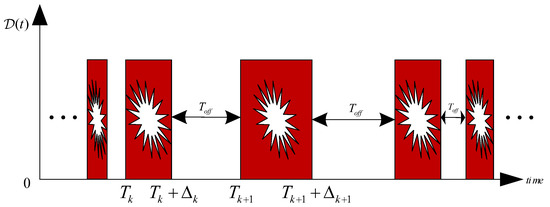
Figure 1.
Time sequences of DoS attacks.
Based on the above analysis combined with the work in [44], we believe that the DoS attack model is arbitrary and is only restricted by the frequency of occurrence and duration of DoS attacks (which contain active stages and a dormant stages). The jammers attack a limited number of links in the network with restricted energy during the activation stage, and energy is stored in preparation for the next attack period in the dormant period. Therefore, it is reasonable to admit that the DoS model satisfied the following assumption.
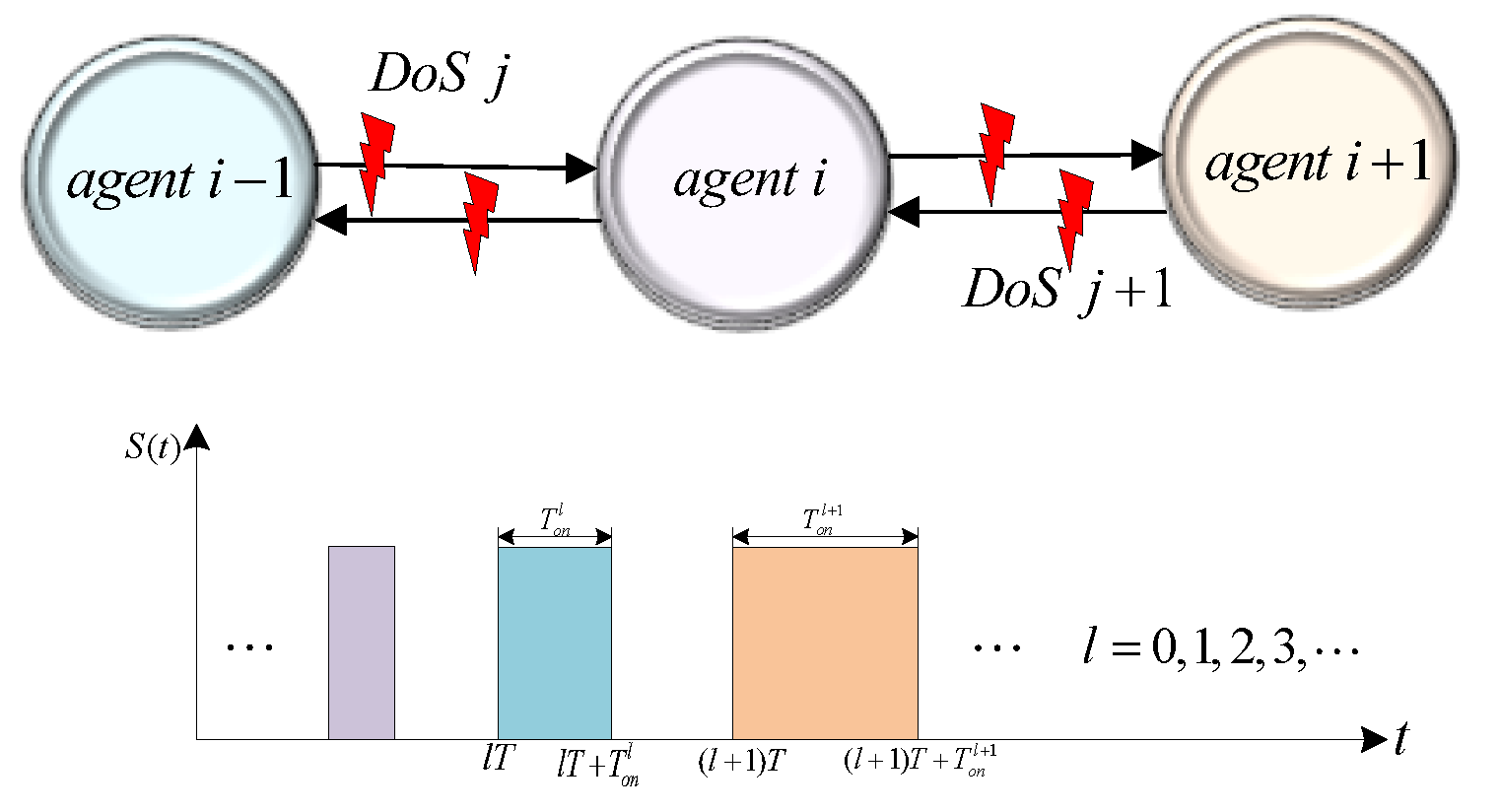
DoS attacks mainly affect the timeliness of information transmission, thereby causing the signal to be interrupted. Generally, the attackers intermittently prevent the communication channels to save energy. Let and , separately present the time attackers launching the networks and the total time the attackers lasted. Furthermore, , presents DoS attacks in active stages, and , denotes the DoS attacks in dormant phases, . A time series block diagram of the periodic DoS attack model is shown in Figure 2. The DoS attack model can be shown as
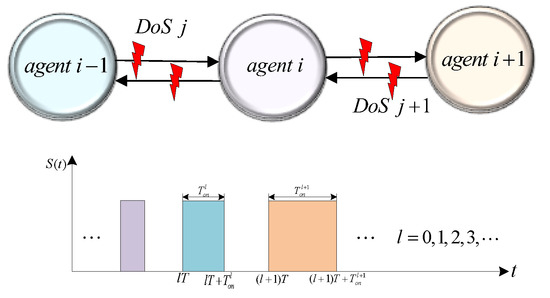
Figure 2.
Schematic and Time sequences of DoS attacks.
2.4. Description of Time-Varying and Heterogeneous Delays
There is a delay in the information interactions between individuals in the biological world, such as bird migration, bee colony foraging, schooling of fishes, etc. It is widely shared that there are delays in information communication between agents. In this work, a kind of time-varying and heterogeneous delay model is constructed, which presents , where t denotes the delay interval , and means the delay between agents . This model describes the fact that the information transmission delay for arbitrary two agents is not fixed and that the delay interval between agents is different.
Assumption 1.
The agents (UAV, robotics, etc.) interact with each through information transfer, and delays exist in the information transmission and processing stages. By taking into account the validity for the transmission of information, it is assumed that , where presents the higher stages of delays. In addition, the delays between agents are strictly positive and symmetric, i.e.,
Remark 2.
We address the flocking control of a C–S model with time-varying and heterogeneous delays in both velocities and positions, which is distinct from the results that have previously been found [45,46,47,48]. Most existing results usually assume that the delay is a constant. Conversely, the communication delays between various agents frequently vary in the majority of engineering circumstances. Consequently, the presented delay model in this work is an expansion and generalization of previous findings, which is more reasonable and valuable. Therefore, fixed delays and homogeneous delays can both be effectively controlled using the strategy outlined in this work.
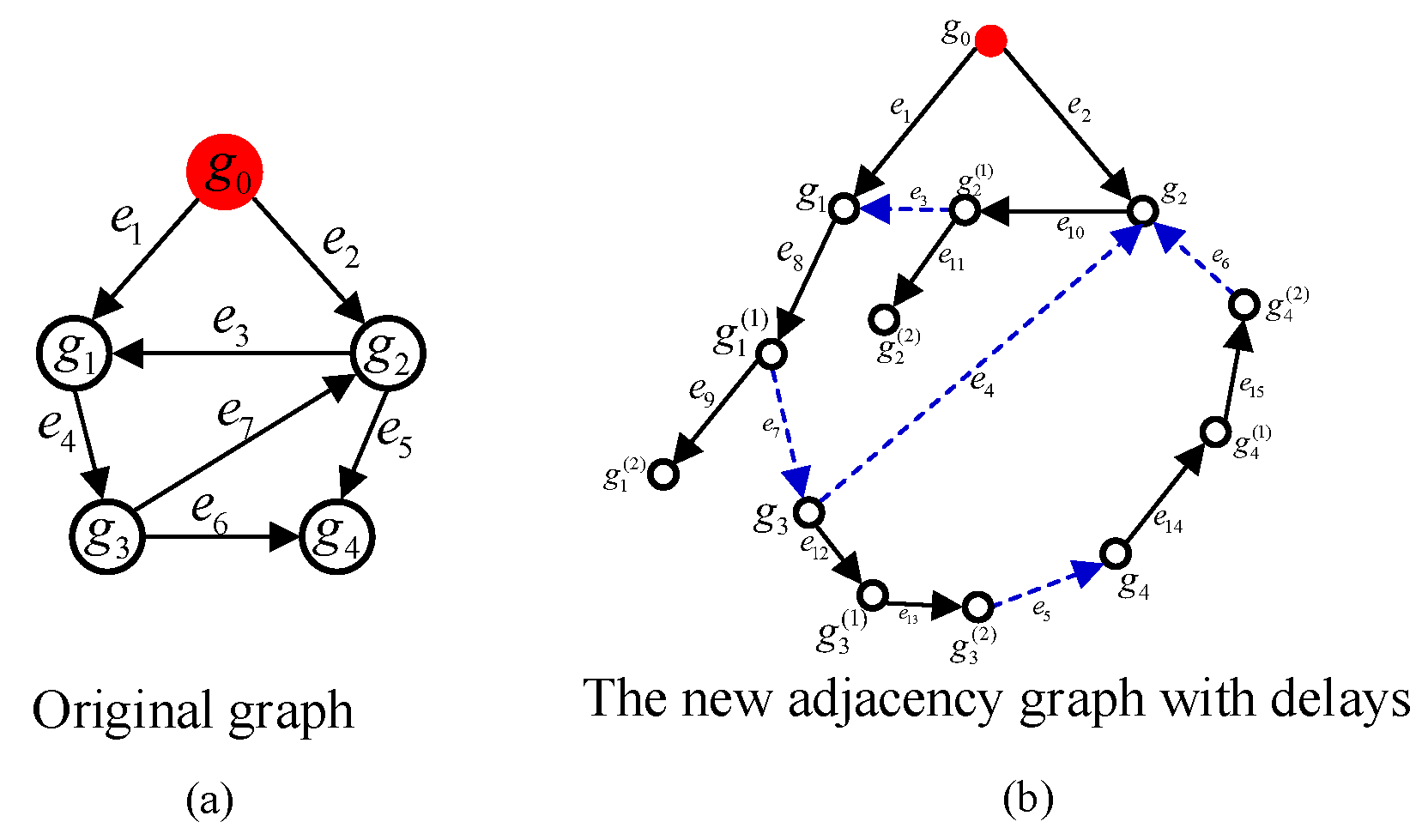
We utilized a multi-agent network system to illustrate the delay model in detail. Consider an original digraph with one leader (), and four followers with seven edges, as shown in Figure 3a. Let the time delay be confined to two, that is, . When considering the consistency of information transmission between agents, two series of virtual nodes need to be added for each follower, which is presented as and . Thus, the vertex order is shown as follows:
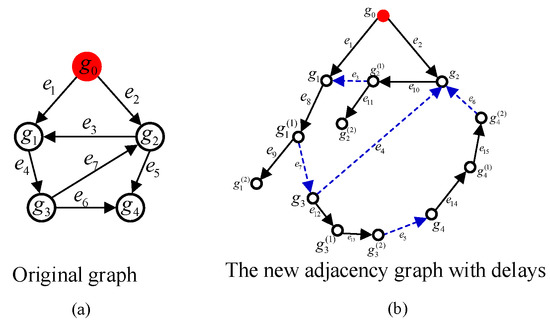
Figure 3.
Topology Network with one leader and four followers with time-varying and heterogeneous delays.
This paper holds the view that the information received indirectly by the agents has time-varying and heterogeneous delays. Without a loss of generality, it is remarkable that the time delay of the five edges among followers to at time are respectively random , as shown in Figure 3b. It can be seen that the links in the original network topology diagram still exist in the new diagram, which is represented by the blue dotted line. There are three kinds of delays, that is, 0, 1, and 2. Among them, 0 means that there is no delay, such as the link between agent and . 1 or 2 respectively indicate that the delay between the followers is one or two time intervals, such as the channels from to and to .
3. Problem Formulation
As in [16], we consider the implementation of the flocking behavior model based on the discrete-time MASs. The flocking behavior is manifested as the state of all agents synchronizing to the leader, the specific performance is that all agents move with the same velocity, and the final position converges to a convex hull with an upper bound.
When considering a system with agents, set , in which denotes the leader, and are the followers. Without a loss of generality, let and denote the agent’s position and velocity, respectively, where is the updated time-step size. Therefore, the discrete time dynamic system for any agent is explored as
where represents the acceleration of the agents, and which is also the control law that needs to be designed. depicts the set containing all discrete instants, where . We admit that the time instants have bounds, that is, . In the next description, are conveniently simplified to .
On the basis of the above preparations, the distributed control protocol is presented as
The weight quantifies the information interactions between agents and presents the communication rate. Specifically, the degree of intimacy between individuals decreases as the distance increases. The intimacy of individuals in multi-agents networks is represented by a weight function. Therefore, it is reasonable that the weight function decreases continuously with the distance , where the rate of decay is l.
As previously noted, the attackers interrupt some or all of the C–S model links during the active time, and they halt all operations during the dormant period. The network topology is also time-varying as a result of this. Use of a time-varying structurally balanced signed digraph is hence appropriate. Therefore, it is appropriate to utilize to represent the new topology. The node set includes one leader (i.e., ) and n followers. includes these directed edges that successfully transmit information between individuals. Considering that some links may be subject to DoS attacks, the new set for agent is defined as: .
According to the C–S model with leadership, the leader simply transmits information and does not receive it, that is, the leader is not affected by other agents. Therefore, the adjacency matrix of the C–S model is presented as follows:
Remark 3.
Through depending on Darwin’s theory of biological evolution, interpersonal cooperation increases with population density. Clearly, the closer proximity of people contributes significantly to the rise in population density. These occurrences give the construction and study of the weight function in this paper a theoretical foundation. The distance between agents is an important factor affecting inter-individual communication. In this paper, the weight function we considered was related to distance, which can more specifically quantify the communication between individuals.
As mentioned in Remark 3, the weight function quantifies the communication between agents through a distance-related function. The distance between agents should not only be infinite, but should also avoid collisions. Therefore, there is no doubt that it is reasonable to assume that the weight function is bounded.
Assumption 2.
In this work, we admitted that the agent’s weight function , is a continuous bounded function. Meanwhile, it is non-negative and monotonically non-increasing, that is, the weight function satisfies the following inequality: , where , , where and represent the maximum and minimum bounds, respectively, i.e., .
In the control strategy Equation (3), all the information received from neighboring nodes was used for the state update of each node in each iteration. Regarding the DoS attacks, part or all of the communication channels were denied. Therefore, the design of the controller was designed separately according to whether it was attacked or not. In addition, the communication between individuals is limited by the transmission distance and requires a certain interval. In addition, time intervals are required for individuals to receive and process information. Therefore, there are delays during the information interactions in a multi-agent network system, which is represented by in the controller.
Based on the aforementioned analysis, the reconstructed controller of a C–S model (2) under DoS attacks (1) and time-varying communication delays is presented as follows:
where denotes the communication delays of channel at time instant t for agents and . While , all communication channels are effective. If in a system under DoS attacks, i.e., , the information interactions of the network are based on unattacked channels.
Remark 4.
Together with Equation (4), for arbitrary agent , it is worth pointing out that there is no delay on itself. Further, the time-varying and heterogeneous delay information comes from other neighbor agents, i.e., . This model is more realistic, that is, the agent knows its own information, but that the information coming from other agents is delayed. However, the analysis is quite complex and changes, thus it will be set out in detail below.
With the use of these analyses and descriptions, we defined the flocking behavior in the C–S model.
Definition 1.
The first condition depicts the alignment rule that all agents eventually synchronize with the same velocity. The second condition is the cohesion rule, that is, the distance between all followers with the leader, and this should be stored within a certain range rather than as an infinite distance. All agents converge to a convex hull with an upper bound. That is, these two conditions guarantee that the flocking behavior for the C–S model (2) will be achieved.
4. Main Results
This section mainly verifies the two conditions of flocking behavior (5) theoretically. We transformed the realization of the flocking behavior into a convergence issue of the agents’ position and velocity error system. Then, the convergence issue of the agents’ velocity and position errors is analyzed and discussed through the properties of the signed graph and sub-stochastic matrix mechanisms. At the same time, we established a control strategy that quantified the communication distances between individuals. Further, we arrived at an algebraic condition that implemented the flocking behavior, one which relays the initial states, topological structure, and weight functions of the agents.
Let denote the adjacency matrix of digraph for a C–S model when subjected to DoS attacks at time t with time delay . This yields the following:
Considering the information interactions time delay between agents, we defined some nonnegative matrices to present the time-delayed communication. We considered that there is a communication channel between agents and , i.e., , and the delay is expressed as . The adjacency matrix that contains the delay information is manifested as and . Further, if , then for any . Thus, we have .
In this work, we designed a set of agents, which consisted of one single leader (i.e., ) and n followers (i.e., …). Let denote the agents’ position error with the velocity error . Accordingly, the error vectors are designed as
where , , , , are the leader’s position and velocity.
For the agent combined with the system of equations, i.e., Equation (2), Equation (4), and Equation (6), the following is yielded:
For the arbitrary followers , we can further calculate the velocity errors through Equation (8). Thus, we have
In this paper, it is admitted that there are delays when the agent receives information from other neighbor agents, but there is no delay in the transmission of itself. For a multi-agent system containing a leader and multiple followers, in general, the leader does not receive information from any followers. The leader only sends information to followers, and the information does not contain delays. For the leader , Equation (2) can be reconstituted as
When combining Equation (9) and Equation (10) with the matrix , the error vectors regarding the agents’ velocity and position, i.e., Equation (7), are formulated as
where , , .
Based on Definition 1, the implementation of the flocking behavior of the C–S model (2) is comparable to the resolution of the error system’s (11) convergence. In order to analyze the communication delays between individuals, we further constructed error vectors with delays as per the below:
In accordance with the discussion of the C–S model (2) and the Equation (11), we provided an original lemma on matrix , which contains several paramount characters in the infinite norm of the matrices. This lemma helps us to analyze the convergence of the error system (12) theoretically.
Lemma 1.
Proof.
Based on Equation (12), we first verified that matrix is non-negative via the sub-stochastic matrix theory. The diagonal elements are . When combined with Condition (13), we have . It is obvious that when it is through the upper bound of . This means that is a nonnegative matrix in which .
In addition, the row sums of matrix satisfy the following:
Furthermore, we obtained the maximum row sum of matrix , which satisfied that .
Therefore, through combining Equation (14) with the properties of infinite norms, it is evidenced that . Consequently, we can conclude that the is a sub-stochastic matrix through the definition of the sub-stochastic matrix that is detailed in [16]. □
By employing , a new matrix is performed, i.e.,
where with . A new digraph is formulated. We verified some important properties of topological graph through a theorem based on matrix theory. Next, a lemma based on matrix theory was used to verify some important properties of topological graph .
Lemma 2.
If the signed digraph has a spanning tree rooted at the leader and inequality (13) is satisfied, then the following inequalities can be demonstrated:
Proof.
An important theorem in matrix theory about the norm of infinity allows us to prove the following inequalities. It is hence undeniable that , where signify the real matrices.
Through combining Equation (2), it is deduced that
By Lemma 1, it is known that . Thus
□
Lemma 1 gives several crucial properties about the agent’s velocity and position errors. Next, on account of the convergence of infinite sub-stochastic matrix products, we provide a theoretical convergence result regarding the agent’s velocity error in Theorem 1.
Conveniently, we divided all time instants into a series of continuous, nonempty, uniformly bounded time intervals The network topology is time-varying because of the communication delays among agents. Considering the heterogeneous and time-varying delay model proposed in this technical notes, we define the longest distance P from the single leader to arbitrary followers in graph as
Theorem 1.
When considering the C–S model (2) under DoS (1), as well as the time-varying and heterogeneous delays (where the update-step size τ satisfies (13)), it is supposed that the interaction topology contains a spanning tree at the leader. For each interval , there exists
where , defines the time number of DoS attacks in .
Proof.
Since comprises a spanning tree rooted at the leader, for each node , there exists a directed path from to , i.e., in , where , are the finite distinct nodes and the path length is
Let present the left products of the matrices. According to matrix theory, the following equation can be obtained:
Thus, we separate matrix into two submatrices; namely, and . Further, we figured out the sum of the th row of this matrix on account of the infinite matrix products.
For arbitrary agent of system (2), if there is an edge from the leader to this agent, i.e., . then the information transfer between agents is represented by a weight value and is included in the adjacency matrix A.
Moreover, the th row sum of matrix is calculated as
Assume that there is an edge between agents and , i.e., , we thus have
Further, the th row sum of is computed as
By appraising , ⋯ in a similar way as , we further resolve the th row sum of matrix , which yields
Moreover, we discuss matrix . When relying on the strength of conclusion in Lemma 1, it is worth remarking that is a sub-stochastic matrix. It is hence undeniable that .
When using the property about sub-stochastic matrices again, which is analyzed in work [49], we have
where . Consequently, is a sub-stochastic matrix as well.
Similarly, it is obvious that is a sub-stochastic matrix; thus, we have
Therefore, we obtain
For arbitrary , , by developing the properties of the infinite norm with Equation (21), we can obtain
Theorem 1 provides a favorable property of the agents’ velocity error. Thus, the algebraic conditions for realizing the flocking behavior can be given.
Theorem 2.
When considering the C–S model (2) subjects to DoS (1), as well as the time-varying and heterogeneous delays , the update step size τ satisfies Equation (13) and the weight function satisfies Assumption 2. If the interaction topology has a spanning tree rooted at the leader, then the flocking behavior of the C–S model (2) under DoS attacks, as well as of the time-varying and heterogeneous delays, is achieved. This means that
where
Based on Theorem 1 and Equation (23), the convergence rate for each agent by the C–S model (2) is established as
Equation (24a) and Equation (24b) are the conditions for the individuals to realize flocking behavior. Equation (24a) says that the velocity error tends to zero over time. This means that the velocities of all individuals eventually converge to a uniform state. Equation (24b) indicates that the distance error between individuals has an upper bound value. That is to say, all individuals converge to the convex hull formed by the leader. The upper bound value is shown as in Equation (25). Equation (26) is the convergence rate for each agent.
Proof.
In accordance with the constraints of time step by the discrete C–S model, the longest distance from the leader to the followers P, and the lower boundary value of the weight function , it is concluded that the rate satisfies . Further, it is obvious that .
This then yields
Equation (27) implies that will converge exponentially to zero as time passes on.
Furthermore, we obtain
Based on Equation (28), we know that will converge exponentially to zero with .
Then, in accordance with Equation (23), Lemma 1, and Theorem 1, the position errors of Equation (15a) are estimated as
Combined with the result , we thus obtain
It is concluded that sequence is bounded with the ratio .
Further, we obtain
Consequently,
This completes the proof. □
Remark 5.
The C–S model defines the weight function as based on absolute distance and Euclidean distance, which is based on the research of biological theory. It can be seen from Equation (3) that the weight function is related to the distance. In addition, this weight function is a positive and decreasing function with nonzero upper and lower bounds. It can be seen from Equation (25) and Equation (26) that the lower bound of the weight function will affect the convergence rate of the agent and the upper bound value of the relative distance error. Specifically, the smaller the lower bound value of the weight function, the faster the convergence rate of the C–S model for the flocking behavior.
5. Numerical Simulations
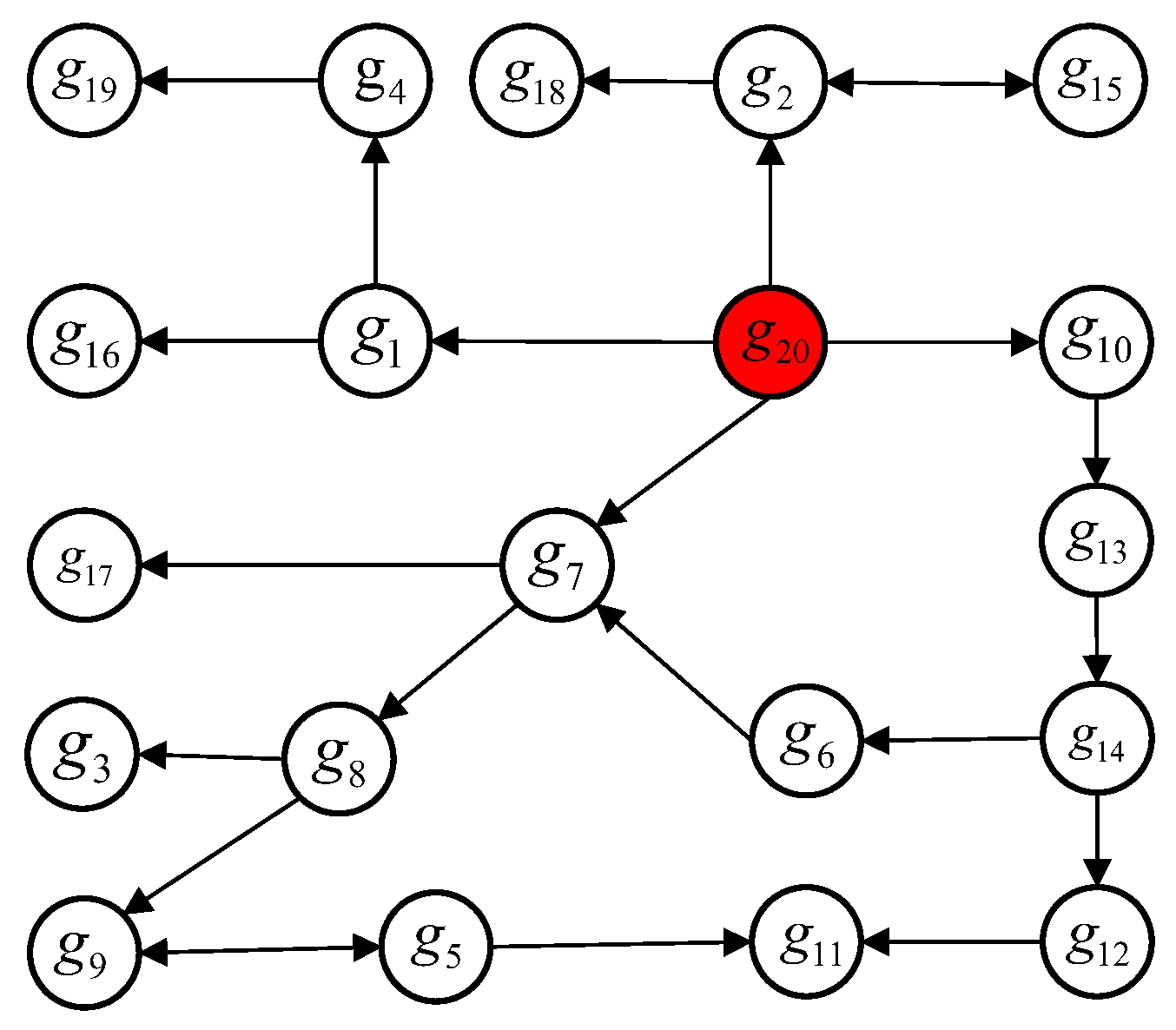
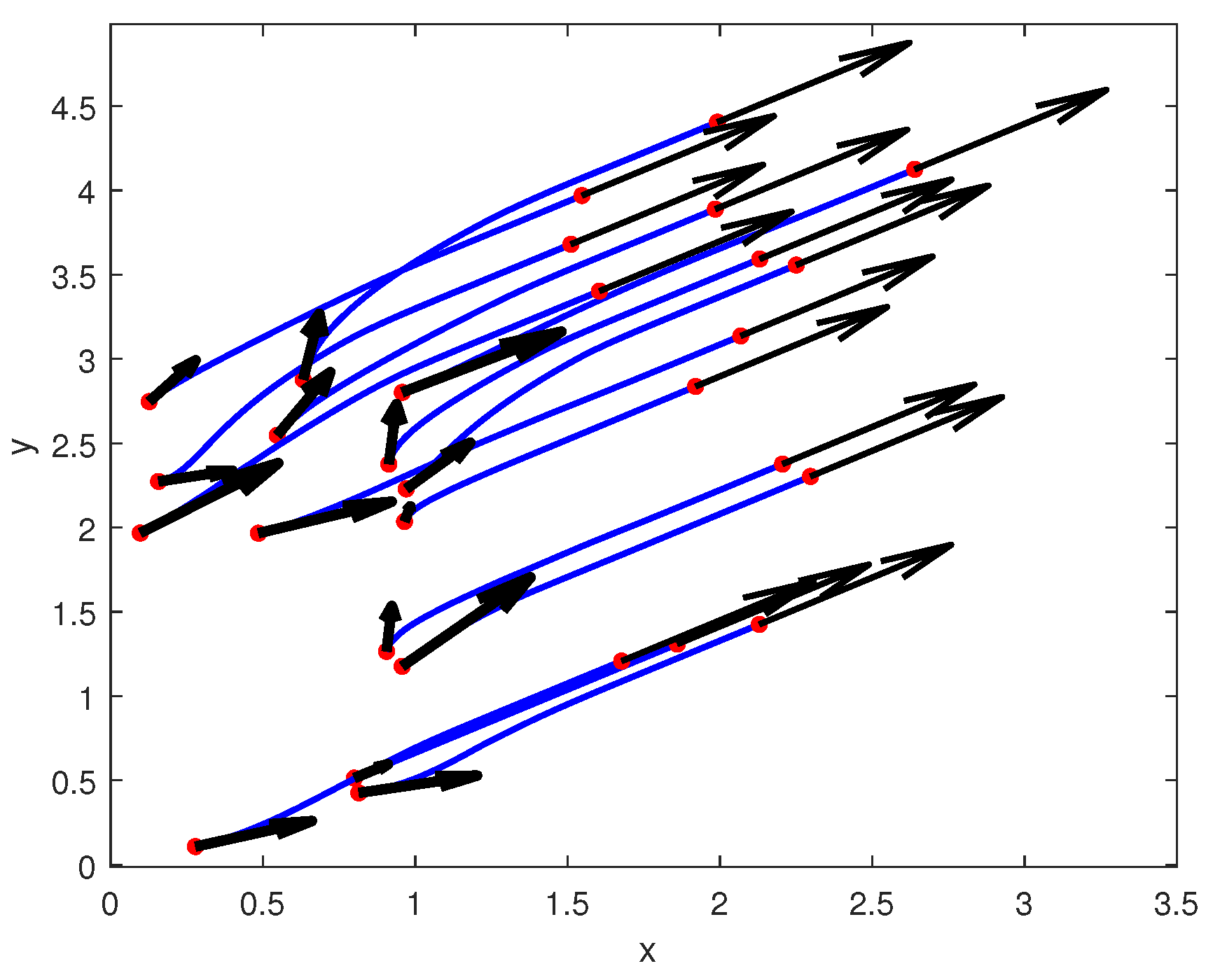
To demonstrate the effectiveness of our theoretical findings, we will offer a supporting example in this section. Consider a leader–follower C–S model with twenty agents where is the leader and present the followers, as shown in Figure 4. The DoS attacks could interrupt the agents’ communication channels while they transfer information. We acknowledge that the link rather than the agent itself is the target of the attack. Therefore, the number of links in the topological network may decrease after a DoS attack, but the number of agents remains constant. During the active phase of the DoS model, we assume that three randomly chosen links in the topology network will be attacked. The time-varying and heterogeneous communication delays among agents are randomly selected in . The initial positions are randomly selected from and the velocity is chosen from . The weight functions are
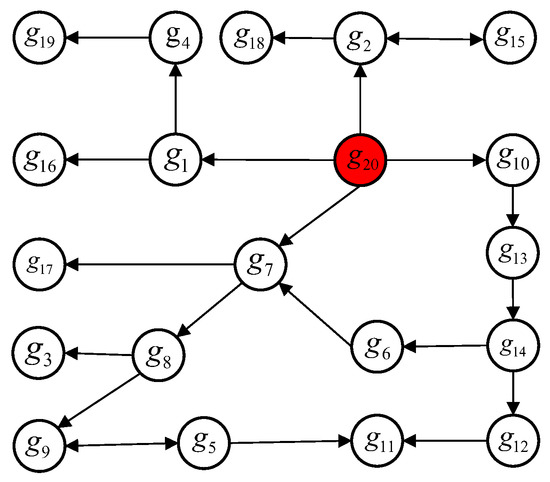
Figure 4.
Topology Network with one leader and nineteen followers.
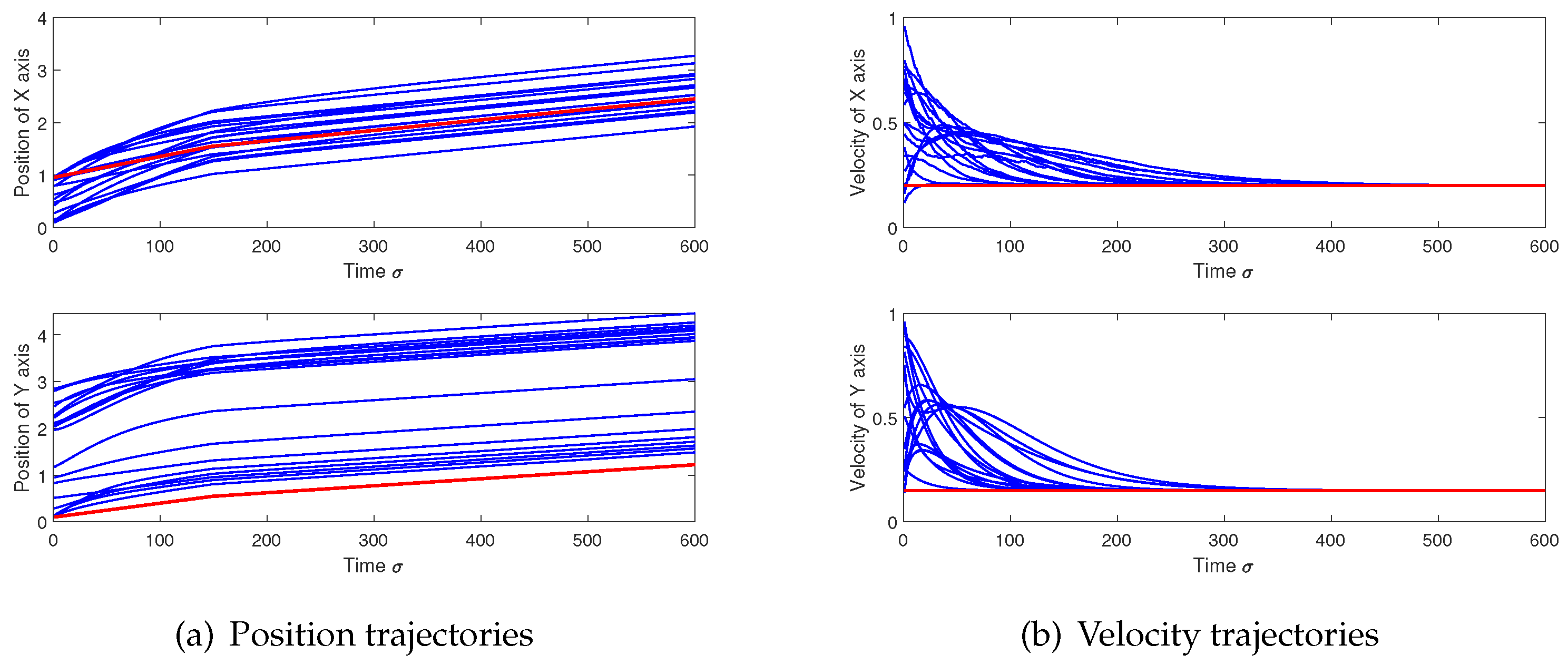
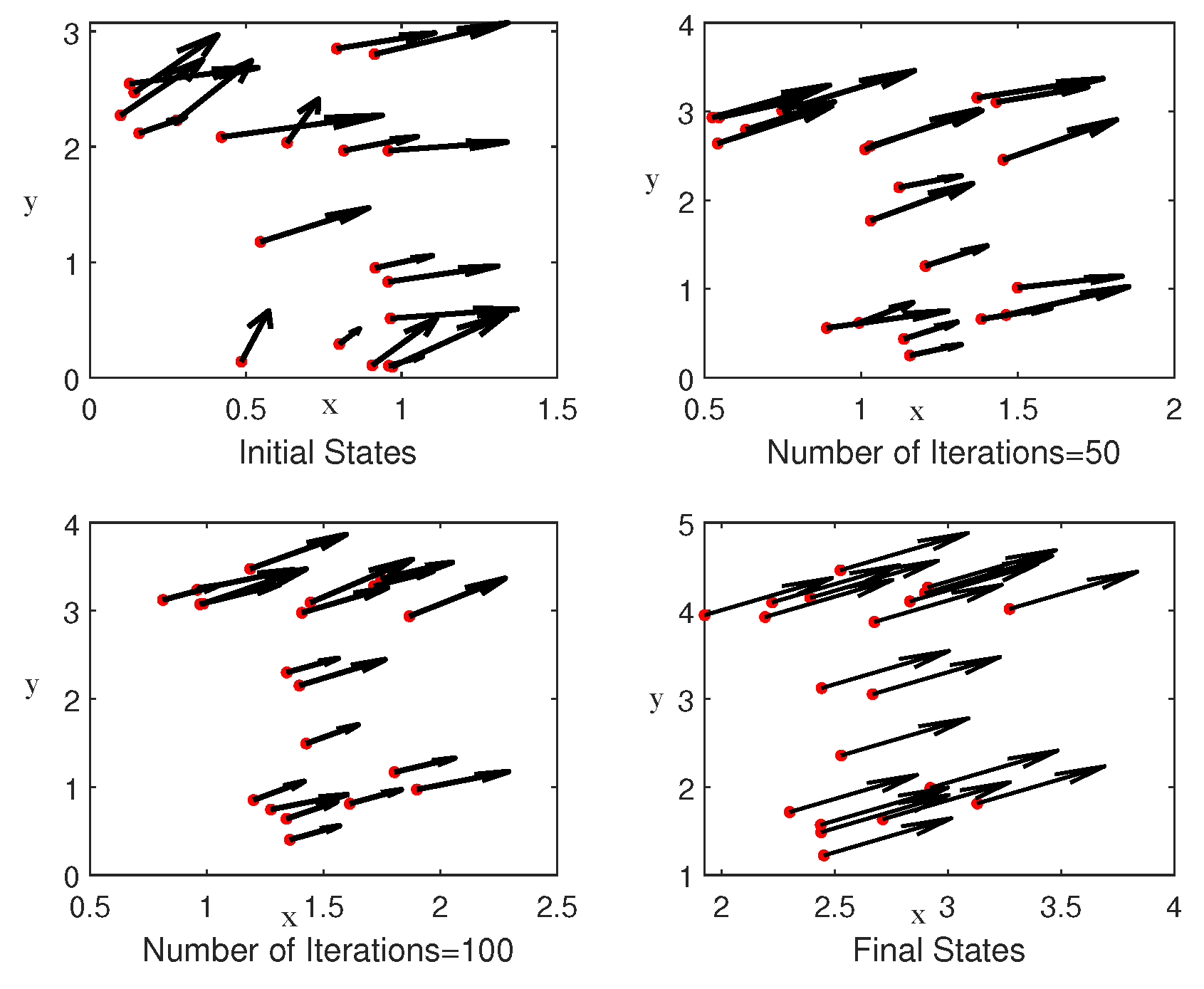
According to the boundary value of the weight function and the cardinality of the set , we have , . Based on the condition (13), the time update step is chosen as . As shown in Figure 5, all agents converge asymptotically from their initial states to their stable states. Particularly, Figure 5a shows that whole agents move in the same directions in the boundary area. The red line represents the position and movement information of the leader, and the blue line represents the followers. It can be seen that the positions of all followers converge to a convex hull centered on the leader. Figure 5b signifies that all followers converge asymptotically to the uniform velocity. The red line represents the speed of the leader, and the blue line represents the speed of the follower. It can be seen from the figure that all the followers are at the same speed as the leader from the initial random initialization state. The process of all agents implementing the flocking behavior is shown in Figure 6. These four subgraphs show that the agents gradually tend to consistent states from the initial random states when the result of the number of iterations increases. In Figure 6, the red dot represents the position of the individual, the horizontal axis represents the position in the x direction, and the vertical axis represents the position in the y direction. The direction and length of the arrow indicate the direction and magnitude of the individual’s velocity. As the number of iterations increases, the individual changes from the initial random state to the swarming behavior, the direction of the speed tends to be the same, and the magnitude of the speed also tends to be the same. These numerical simulation results verified the correctness of the theoretical discussion presented in this paper. It can be concluded that the C–S model (2) under DoS attacks (1) and delays can formulate the flocking behaviors through the controller (4).
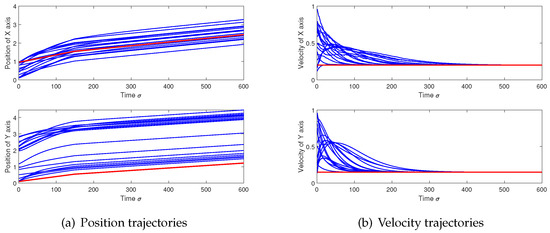
Figure 5.
Decomposed motion trajectories of 20 agents. The upper and lower sub-figures denote the position and velocity evolution of all agents in the x-axis and y-axis, respectively. The red curve means the leader and the blue curve means the followers.
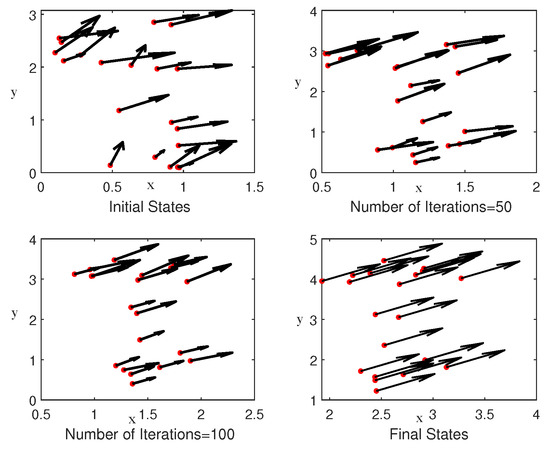
Figure 6.
The 2D flocking behavior with 20 agents.
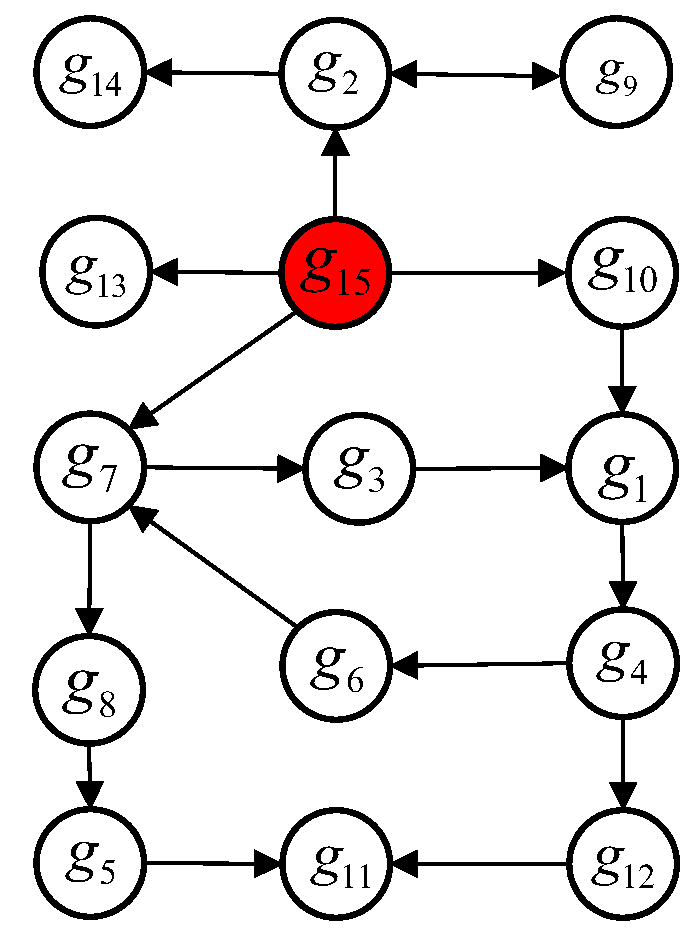
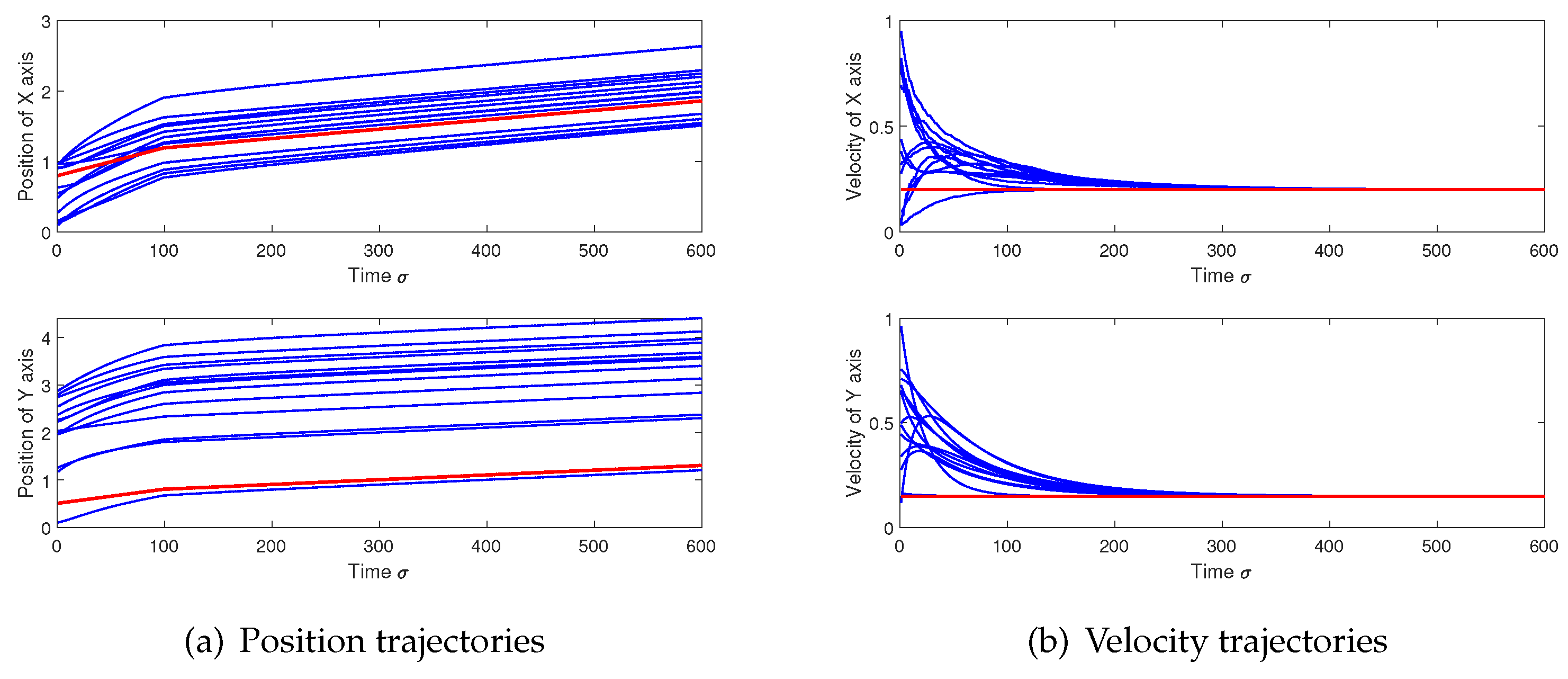
In this paper, it is accepted that there exists delays between the agents and the leader. We consider a system with 15 agents, which includes a leader and 14 followers, as shown in Figure 7. In addition, we verified that the existence of time delays between the leader and the follower was also feasible in the simulation, as shown in Figure 8. It is presented that all agents have the same velocity as the leader, as shown in Figure 8a. Furthermore, the distance between the agents were controlled within a bounded value, which achieve a cohesion with other agents during the movement, as shown in Figure 8b. The movement process of all agents is shown in Figure 9—from the initial random state to the flocking behavior at the end.
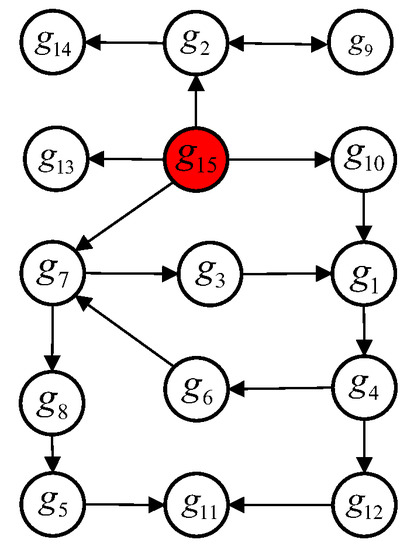
Figure 7.
Topology Network with one leader and fourteen followers.
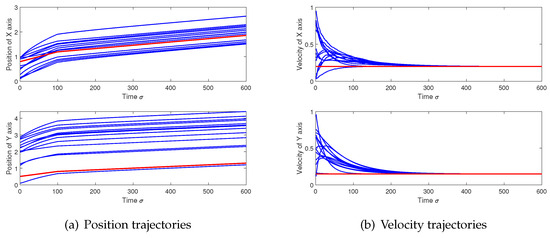
Figure 8.
Decomposed motion trajectories of 15 agents. The upper and lower sub-figures denote the position and velocity evolution of all agents in the x-axis and y-axis, respectively. The red curve means the leader and the blue curve means the followers.
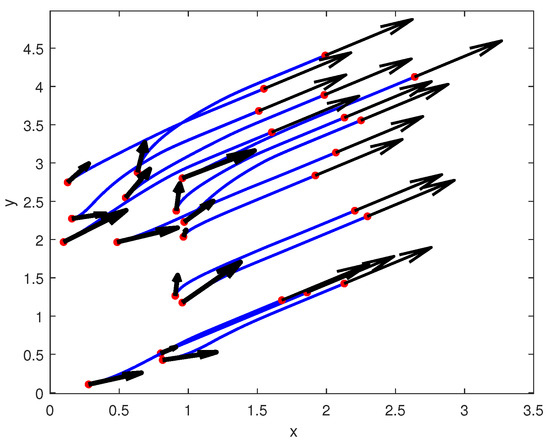
Figure 9.
The 2D flocking behavior with 15 agents.
6. Conclusions
In this work, the flocking of the Cucker–Smale model was examined in the presence of time-varying and heterogeneous delays, and DoS attacks. Compared with the existing results on the C–S model, the weight function in this paper does not need a specific form; it only needs to satisfy any positive weights that decrease in function with a non-zero lower bound. The feasibility and stability analysis of the original system is changed into a matrix convergence issue by creating error vectors for the agents’ position and velocity. Furthermore, this convergence problem was examined by using the infinite product properties of sub-stochastic matrices. Additionally, a sufficient condition that was associated with the initial states, the topological structure, and the upper bound of time delays was devised in order to achieve flocking behavior. It is worth mentioning that the least convergence rate and the upper bound of the final state difference between the leader and the followers are given. Moreover, it was examined how DoS assaults and time-delayed communications affect the convergence rate and the final distance between agents. A simulation example was finally used to illustrate a theoretical result. In the future, we will further analyze the cooperation and competition relationship between individuals, as well as study the flocking control, which includes positive and negative weights.
Author Contributions
X.S.: conceptualization, methodology, and writing—original draft; Z.M.: writing—original draft and numerical simulation; W.X.: validation and writing—review & editing; Y.Y. and K.C.: validation, writing—review & editing, and supervision; G.Q.: writing—review & editing. All authors have read and agreed to the published version of the manuscript.
Funding
This research was supported in part by the National Natural Science Foundation of China (62103080,62003278), the Natural Science Foundation of Sichuan Province (2023NSFSC1431), and the China Postdoctoral Science Foundation (2021M700696).
Data Availability Statement
The data presented in this study are available in the simulation section of this paper.
Conflicts of Interest
No conflicts of interest exists in the submission of this manuscript, and all authors approve the manuscript for publication. I would like to declare on behalf of my co-authors that the work described was original research that has not yet been published and is not under consideration for publication elsewhere, in whole or in part. All the authors listed have approved the manuscript that is enclosed.
References
- Casado, R.; Bermúdez, A. A simulation framework for developing autonomous drone navigation systems. Electronics 2020, 10, 7. [Google Scholar] [CrossRef]
- Reyhanoglu, M.; Jafari, M.; Rehan, M. Simple Learning-Based Robust Trajectory Tracking Control of a 2-DOF Helicopter System. Electronics 2022, 11, 2075. [Google Scholar] [CrossRef]
- Shao, J.; Shi, L.; Cheng, Y.; Li, T. Asynchronous Tracking Control of Leader–Follower Multiagent Systems With Input Uncertainties Over Switching Signed Digraphs. IEEE Trans. Cybern. 2021, 52, 6379–6390. [Google Scholar] [CrossRef] [PubMed]
- Shi, L.; Li, W.; Shi, M.; Shi, K.; Cheng, Y. Opinion Polarization Over Signed Social Networks With Quasi Structural Balance. IEEE Trans. Autom. Control. 2023, 66, 3789–3793. [Google Scholar] [CrossRef]
- Shi, L.; Liu, Q.; Shao, J.; Cheng, Y.; Zheng, W.X. A Cooperation-Competition Evolutionary Dynamic Model Over Signed Networks. IEEE Trans. Autom. Control. 2023. [Google Scholar] [CrossRef]
- Vicsek, T.; Czirók, A.; Ben-Jacob, E.; Cohen, I.; Shochet, O. Novel type of phase transition in a system of self-driven particles. Phys. Rev. Lett. 1995, 75, 1226. [Google Scholar] [CrossRef]
- Cucker, F.; Smale, S. Emergent behavior in flocks. IEEE Trans. Autom. Control. 2007, 52, 852–862. [Google Scholar] [CrossRef]
- Darwin, C. On the Origin of Species by Means of Natural Selection; Or, The Preservation of Favored Races in the Struggle for Life; A.L. Burt: New York, NY, USA, 1875. [Google Scholar]
- Shi, L.; Cheng, Y.; Shao, J.; Sheng, H.; Liu, Q. Cucker-Smale flocking over cooperation-competition networks. Automatica 2022, 135, 109988. [Google Scholar] [CrossRef]
- Park, J.; Kim, H.J.; Ha, S.Y. Cucker-Smale flocking with inter-particle bonding forces. IEEE Trans. Autom. Control. 2010, 55, 2617–2623. [Google Scholar] [CrossRef]
- Sun, Z.; Mou, S.; Deghat, M.; Anderson, B.D. Finite time distributed distance-constrained shape stabilization and flocking control for d-dimensional undirected rigid formations. Int. J. Robust Nonlinear Control. 2016, 26, 2824–2844. [Google Scholar] [CrossRef]
- Dong, J.G.; Qiu, L. Flocking of the Cucker-Smale model on general digraphs. IEEE Trans. Autom. Control. 2016, 62, 5234–5239. [Google Scholar] [CrossRef]
- Dong, J.G.; Ha, S.Y.; Jung, J.; Kim, D. On the stochastic flocking of the Cucker–Smale flock with randomly switching topologies. Siam J. Control. Optim. 2020, 58, 2332–2353. [Google Scholar] [CrossRef]
- Ha, S.Y.; Jeong, J.; Noh, S.E.; Xiao, Q.; Zhang, X. Emergent dynamics of Cucker–Smale flocking particles in a random environment. J. Differ. Equ. 2017, 262, 2554–2591. [Google Scholar] [CrossRef]
- Juang, J.; Liang, Y.H. Avoiding collisions in Cucker–Smale flocking models under group-hierarchical multileadership. SIAM J. Appl. Math. 2018, 78, 531–550. [Google Scholar] [CrossRef]
- Shao, J.; Zheng, W.X.; Shi, L.; Cheng, Y. Leader–follower flocking for discrete-time Cucker–Smale models with lossy links and general weight functions. IEEE Trans. Autom. Control. 2020, 66, 4945–4951. [Google Scholar] [CrossRef]
- Sun, L.; Zhang, Y.; Sun, C. Stochastic denial-of-service attack allocation in leader-following multiagent systems. IEEE Trans. Syst. Man Cybern. Syst. 2021, 52, 2848–2857. [Google Scholar] [CrossRef]
- Zhao, L.; Yang, G.H. Adaptive fault-tolerant control for nonlinear multi-agent systems with DoS attacks. Inf. Sci. 2020, 526, 39–53. [Google Scholar] [CrossRef]
- Feng, S.; Tesi, P. Resilient control under denial-of-service: Robust design. Automatica 2017, 79, 42–51. [Google Scholar] [CrossRef]
- Sun, H.; Peng, C.; Zhang, W.; Yang, T.; Wang, Z. Security-based resilient event-triggered control of networked control systems under denial of service attacks. J. Frankl. Inst. 2019, 356, 10277–10295. [Google Scholar] [CrossRef]
- Liu, H.; Wang, Z. Sampled-data-based consensus of multi-agent systems under asynchronous denial-of-service attacks. Nonlinear Anal. Hybrid Syst. 2021, 39, 100969. [Google Scholar] [CrossRef]
- Patel, A.; Roy, S.; Baldi, S. Wide-Area Damping Control Resilience Towards Cyber-Attacks: A Dynamic Loop Approach. IEEE Trans. Smart Grid 2021, 12, 3438–3447. [Google Scholar] [CrossRef]
- Tao, T.; Roy, S.; Baldi, S. Stable Adaptation in Multi-Area Load Frequency Control under Dynamically-Changing Topologies. IEEE Trans. Power Syst. 2020, 36, 2946–2956. [Google Scholar] [CrossRef]
- Shi, X.; Shi, L.; Cheng, Y.; Chen, K. Flocking control for Cucker–Smale model under denial-of-service attacks. Int. J. Robust Nonlinear Control. 2022, 32, 9997–10010. [Google Scholar] [CrossRef]
- Dong, J.G.; Ha, S.Y.; Kim, D.; Kim, J. Time-delay effect on the flocking in an ensemble of thermomechanical Cucker–Smale particles. J. Differ. Equations 2019, 266, 2373–2407. [Google Scholar] [CrossRef]
- Zhang, L.; Orosz, G. Consensus and disturbance attenuation in multi-agent chains with nonlinear control and time delays. Int. J. Robust Nonlinear Control. 2017, 27, 781–803. [Google Scholar] [CrossRef]
- Lin, P.; Jia, Y. Consensus of second-order discrete-time multi-agent systems with nonuniform time-delays and dynamically changing topologies. Automatica 2009, 45, 2154–2158. [Google Scholar] [CrossRef]
- Zhu, W.; Jiang, Z.P. Event-based leader-following consensus of multi-agent systems with input time delay. IEEE Trans. Autom. Control. 2014, 60, 1362–1367. [Google Scholar] [CrossRef]
- Zhou, X.; Wang, H.; Tian, Y.; Dai, X. Consensus tracking via quantized iterative learning control for singular nonlinear multi-agent systems with state time-delay and initial state error. Nonlinear Dyn. 2021, 103, 2701–2719. [Google Scholar] [CrossRef]
- Yin, X.; Yue, D. Event-triggered tracking control for heterogeneous multi-agent systems with Markov communication delays. J. Frankl. Inst. 2013, 350, 1312–1334. [Google Scholar] [CrossRef]
- Hu, J.; Chen, G.; Li, H.X. Distributed event-triggered tracking control of leader-follower multi-agent systems with communication delays. Kybernetika 2011, 47, 630–643. [Google Scholar]
- Jiang, X.; Xia, G.; Feng, Z.; Jiang, Z. Consensus tracking of data-sampled nonlinear multi-agent systems with packet loss and communication delay. IEEE Trans. Netw. Sci. Eng. 2020, 8, 126–137. [Google Scholar] [CrossRef]
- Wang, D.; Wang, W. Necessary and sufficient conditions for containment control of multi-agent systems with time delay. Automatica 2019, 103, 418–423. [Google Scholar] [CrossRef]
- Li, B.; Yang, H.Y.; Chen, Z.Q.; Liu, Z.X. Distributed containment control of multi-agent systems with general linear dynamics and time-delays. Int. J. Control. Autom. Syst. 2018, 16, 2718–2726. [Google Scholar] [CrossRef]
- Wang, F.Y.; Ni, Y.H.; Liu, Z.X.; Chen, Z.Q. Fully distributed containment control for second-order multi-agent systems with communication delay. Isa Trans. 2020, 99, 123–129. [Google Scholar] [CrossRef]
- Cucker, F.; Dong, J.G. Avoiding collisions in flocks. IEEE Trans. Autom. Control. 2010, 55, 1238–1243. [Google Scholar] [CrossRef]
- Li, Z.; Xue, X. Cucker–Smale flocking under rooted leadership with fixed and switching topologies. Siam J. Appl. Math. 2010, 70, 3156–3174. [Google Scholar] [CrossRef]
- Dalmao, F.; Mordecki, E. Cucker–Smale flocking under hierarchical leadership and random interactions. Siam J. Appl. Math. 2011, 71, 1307–1316. [Google Scholar] [CrossRef]
- Dalmao, F.; Mordecki, E. Hierarchical Cucker-Smale model subject to random failure. IEEE Trans. Autom. Control. 2012, 57, 1789–1793. [Google Scholar] [CrossRef]
- He, Y.; Mu, X. Cucker–Smale flocking subject to random failure on general digraphs. Automatica 2019, 106, 54–60. [Google Scholar] [CrossRef]
- Wang, X.; Sun, J.; Wu, Z.; Li, Z. Robust integral of sign of error-based distributed flocking control of double-integrator multi-agent systems with a varying virtual leader. Int. J. Robust Nonlinear Control. 2022, 32, 286–303. [Google Scholar] [CrossRef]
- Cong, M.; Mu, X.; Hu, Z. Sampled-data-based event-triggered secure bipartite tracking consensus of linear multi-agent systems under DoS attacks. J. Frankl. Inst. 2021, 358, 6798–6817. [Google Scholar] [CrossRef]
- Xiong, J.; Lam, J. Stabilization of linear systems over networks with bounded packet loss. Automatica 2007, 43, 80–87. [Google Scholar] [CrossRef]
- De Persis, C.; Tesi, P. Input-to-state stabilizing control under denial-of-service. IEEE Trans. Autom. Control. 2015, 60, 2930–2944. [Google Scholar] [CrossRef]
- Erban, R.; Haskovec, J.; Sun, Y. A Cucker–Smale model with noise and delay. Siam J. Appl. Math. 2016, 76, 1535–1557. [Google Scholar] [CrossRef]
- Choi, Y.P.; Haskovec, J. Cucker-Smale model with normalized communication weights and time delay. arXiv 2016, arXiv:1608.06747. [Google Scholar]
- Pignotti, C.; Trélat, E. Convergence to consensus of the general finite-dimensional Cucker-Smale model with time-varying delays. arXiv 2017, arXiv:1707.05020. [Google Scholar] [CrossRef]
- Pignotti, C.; Vallejo, I.R. Flocking estimates for the Cucker–Smale model with time lag and hierarchical leadership. J. Math. Anal. Appl. 2018, 464, 1313–1332. [Google Scholar] [CrossRef]
- Shi, L.; Zheng, W.X.; Shao, J.; Cheng, Y. Sub-super-stochastic matrix with applications to bipartite tracking control over signed networks. SIAM J. Control. Optim. 2021, 59, 4563–4589. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).