Abstract
To protect the privacy of cloud data, encryption before uploading provides a solution. However, searching for target data in ciphertext takes effort. Therefore, searchable encryption has become an important research topic. On the other hand, since the advancement of quantum computers will lead to the crisis of cracking traditional encryption algorithms, it is necessary to design encryption schemes that can resist quantum attacks. Therefore, we propose a multi-keyword searchable identity-based proxy re-encryption scheme from lattices. In addition to resisting quantum attacks, the proposed scheme uses several cryptographic techniques to improve encryption efficiency. First, identity-based encryption is used to reduce the computation and transmission costs caused by certificates. Second, the proposed scheme uses proxy re-encryption to achieve the purpose of outsourced computing, allowing the proxy server to reduce the computation and transmission costs of the users. Third, the proposed multi-keyword searchable encryption can provide AND and OR operators to increase the flexibility of searchability. Moreover, the access structure of the proposed scheme is not based on a linear secret sharing scheme (LSSS), avoiding the errors caused by an LSSS-based structure in decryption or search results. Finally, we also give formal security proof of the proposed scheme under the decisional learning with errors assumption.
Keywords:
post-quantum cryptography; lattice-based cryptography; multi-keyword search; identity-based encryption; proxy re-encryption MSC:
68P25
1. Introduction
Encrypting data before uploading to the cloud has become a standard method to protect data privacy. With the advancement of technology, cloud services have become a part of people’s daily lives. Sharing data through the cloud server can reduce the storage cost of the user end, but at the same time, there will be concerns about data leakage. Therefore, to protect the data’s confidentiality, users may encrypt it before uploading it to the cloud server. Based on the convenience of key management, most people use the public key cryptography system to encrypt data. To confirm the correctness of a user’s public key, a certificate of the user’s public key is often required as proof. However, since the management and verification of certificates will lead to more computation and transmission costs, many certificate-less public key cryptosystems have been proposed.
Functional encryption is a type of certificate-less public key encryption. For example, identity-based encryption (IBE), attribute-based encryption (ABE), and subset-predicate encryption (SPE) are functional encryption methods. In 1984, Shamir proposed the first IBE scheme [1]. In his scheme, the data owner can use the receivers’ identities as the encryption keys, thereby saving the management and verification of certificates. In 2005, Sahai and Waters proposed a fuzzy IBE scheme [2]. Since a fuzzy identity can be regarded as an attribute, the scheme of Sahai and Waters is considered the first ABE scheme. In ABE schemes, the data owner can use attributes to encrypt data, so there is no need to use certificates. The concept of SPE was first introduced by Katz et al. [3] in 2017. In SPE schemes, the data owner can select an attribute set to encrypt data, and the receivers can decrypt it if and only if their attributes are subsets of the attribute set of the encrypted data.
Proxy re-encryption (PRE) is used to reduce file-sharing costs. To change the recipient of the ciphertext from Alice to Bob, one may decrypt the ciphertext with Alice’s private key and then encrypt it with Bob’s public key. However, this method is inefficient, and how to directly convert the ciphertext becomes an issue. Therefore, the purpose of PRE is to directly convert the ciphertext without decrypting it. The first PRE scheme was proposed by Blaze et al. in 1998 [4]. In their scheme, a semi-trusted proxy is allowed to transform the ciphertext for Alice into the ciphertext for Bob without changing the content of the message, thereby reducing the computation and transmission costs of sharing files. On the other hand, PRE can be used in combination with functional encryption. For example, the first identity-based PRE scheme was proposed by Green and Ateniese [5] in 2007; the first attribute-based PRE scheme was proposed by Liang et al. in 2009 [6].
Searchable encryption (SE) solves the problem that files cannot be searched after encryption. Although encryption can protect data privacy, searching for encrypted data takes effort. To solve this problem, Song et al. [7] proposed the first SE scheme in 2000, whereas encrypted files are searchable. In 2004, Boneh et al. proposed the first SE scheme with keyword search [8]. In Boneh et al.’s scheme, users can choose a keyword to search for files. In 2007, Hwang and Lee [9] proposed SE that supports multi-keyword search, increasing the flexibility of searchability.
On the other hand, due to the rapid development of quantum computers, some traditional encryption schemes are facing a crisis of being cracked. Due to the special properties of quantum bits, quantum computers can perform parallel operations on large amounts of data. Therefore, quantum computers can use their parallel computing capabilities to solve some traditional hard problems on classical computers. In 1994, Shor proposed a quantum algorithm [10] that can find the prime factors of a large integer. In addition, the discrete logarithm problem, which is generally considered as difficult as the prime factorization problem, is also considered to be at risk of being solved by quantum algorithms. Therefore, encryption schemes based on such mathematical problems suffer from the risk of being cracked.
Lattice-based cryptography has been extensively researched and validated for security on both classical and quantum algorithms. To resist quantum attacks, the National Institute of Standards and Technology (NIST) launched a post-quantum cryptography standards competition. In July 2022, the competition winner was Kyber [11], a lattice-based public-key encryption algorithm. The competition result shows that lattice-based schemes are generally considered to be effective against quantum attacks. Lattice-based cryptography is considered quantum-resistant because it is based on mathematical problems that are difficult for quantum computers to solve. Quantum computers cannot solve the shortest vector problem exponentially faster than classical computers, which means that quantum attacks would not be able to break the encryption schemes based on that problem. The Learning with Errors (LWE) problem is also considered intractable for quantum computers. In addition, no known quantum algorithm can break the Decisional Learning with Errors (D-LWE) problem, which has applications in many fields.
Many lattice-based public-key cryptosystems have been proposed. In 1996, Ajtai [12] proposed a one-way hash function based on the shortest vector problem. In 1997, Goldreich et al., proposed the first public-key cryptosystem based on the closest vector problem. Hoffstein et al. [13] proposed a public key encryption scheme called the Number Theory Research Unit (NTRU) in 1998. Although the security of NTRU is not formally proven, its computation cost is lower than previous schemes. In 2005, Regev [14] proposed the LWE problem, which is at least as hard as the worst case of the shortest independent vectors problem. Since then, most of the lattice-based public-key cryptosystems published after 2005 were based on the LWE problem due to the low computational cost required. Even the Kyber algorithm [11], the winner of the NIST post-quantum competition, is based on the LWE problem.
One of the advantages of the lattice encryption algorithm is that it can provide functional encryption. In 2008, Gentry et al., published an IBE scheme based on LWE. In 2013, Boneh proposed the first lattice-based ABE scheme [15]. In 2014, Singh et al. proposed the first identity-based PRE [16]. In 2019, Liu et al. [17] proposed an ABE protocol for searchable keywords. In 2022, Wang et al. [18] proposed a searchable SPE scheme.
Outsourcing computation reduces the computation and transmission costs of the data sender. In 2019 Zhang et al. [19] proposed a lattice-based SE support outsourcing computation. In their scheme, DO will generate oriented keys and send them to PS. With those keys, PS can prove that DO has authorized it to assist in encryption. With the assistance of PS, DO can save some computation and transmission costs.
Some lattice-based SE schemes [17,20,21,22] use linear secret sharing scheme (LSSS) as the access structure, but using LSSS under the LWE problem may cause problems. Because the Gaussian elimination method used to solve the LSSS problem will generate coefficients that cannot be guaranteed to be small enough, the decryption or search results after running LSSS may be wrong. Therefore, LSSS-based schemes under the LWE problem cannot be realized in practice. To avoid this problem, the proposed scheme uses a tree-based access structure.
1.1. Problem Statements
In summary, to improve the efficiency of cloud services, an encrypted file-sharing scheme should meet the following features:
- The encryption should resist quantum attacks.
- The encrypted file should be searchable. Moreover, the scheme should support multi-keyword to increase the flexibility of searchability.
- To reduce the file-sharing costs of the data owner, the scheme should support PRE.
- The encryption should avoid the cost of using certificates.
Unfortunately, no known scheme can achieve these features simultaneously. Therefore, we propose a scheme to satisfy these features simultaneously.
1.2. Contributions
We proposed a multi-keyword searchable identity-based proxy re-encryption scheme from lattices. To highlight the contributions, the features comparison between the proposed scheme and other schemes is shown in Table 2. The proposed scheme is the first to offer the following properties simultaneously:
- To resist quantum attacks, the security of the proposed scheme is based on the LWE problem from lattices.
- The flexibility of searchability is increased through the proposed multi-keyword search that supports AND and OR operations. The access structure is tree-based rather than LSSS-based, avoiding possible errors in the decryption and search phases.
- KGC only needs to assist users in generating private keys during the registration phase. The burden on the KGC is reduced since it does not involve other phases. Moreover, the risk of KGC being attacked by adversaries through the network can be reduced.
- The proposed scheme supports PRE to reduce file-sharing costs of the data owner. The concept of outsourcing computation is added to the scheme design. As the number of data users increases, the costs required for the data owner remain the same, and the proxy server will handle the increased workload.
- Users’ access rights are verified in both the search phase and the decryption phase to prevent adversaries from illegally accessing files.
- The proposed scheme is identity-based, which avoids the cost of using certificates.
2. Preliminaries
The definitions of lattice, trapdoors, and hardness assumptions are shown here. Furthermore, the access structure, system model, and security model of the proposed scheme are presented here.
2.1. Lattices
Definition 1.
An n-dimensional lattice is defined as a set of linear combinations of m linearly independent vectors .
where is a basis of , and the rank of is m.
Definition 2.
Given a prime number q, a basis , and a vector .
Three types of lattices are defined as follows:
2.2. Discrete Gaussians
Definition 3.
Given a Gaussian parameter , a vector , and .
- The discrete Gaussian distribution over is
- The sum of all is
- The Gaussian function on is
2.3. Inhomogeneous Short Integer Solution (ISIS)
Definition 4 (ISIS problem).
Given a prime q, a random matrix , a target vector , and a parameter , the goal is to find a non-zero vector such that and .
The ISIS problem is a variant of the Shortest Vector Problem (SVP) in lattices, which is known to be computationally hard. It falls within the class of NP-hard problems and is believed to be resistant to efficient classical and quantum algorithms. Lattice-based schemes often design public and private keys based on the ISIS problem. and are often used as public parameters or public keys, while is often used as a private key.
2.4. Decisional Learning with Errors (D-LWE)
Given a prime q, a Gaussian distribution over , and a positive integer n. Assume that there is a non-specified oracle , which could be a truly uniform random sampler or a noisy pseudo-random sampler . and are defined as follows:
- The noisy pseudo-random sampler outputs pseudo-random samples , where is sampled from , is a consistent secret vector, and is a uniformly random vector.
- The truly random sampler outputs uniformly random samples in .
Definition 5 (D-LWE problem).
Given a polynomial number of samples from . Decide whether is or .
Definition 6.
The advantage of an adversary to break the D-LWE problem is defined as
Definition 7 (D-LWE Assumption).
If no polynomial-time algorithm has a non-negligible advantage in solving the D-LWE problem, then the D-LWE assumption holds.
The D-LWE problem is widely regarded as a hard problem in lattice-based cryptography. Many lattice-based cryptographic schemes, such as encryption, signatures, and key exchange protocols, rely on the hardness of D-LWE for their security. As long as solving the D-LWE problem is difficult, the security of those schemes will be guaranteed.
2.5. Trapdoor Functions
There are two types of trapdoor functions.Type 2 trapdoor functions are smaller, faster, and better than Type 1 trapdoor functions. The type 2 trapdoor functions are based on the one-way function proposed by Regev [23], and their security is constructed on the hardness of the learning with errors problem (LWE). In 2012, Micciancio and Peikert [24] proposed an efficient trapdoor generation function. Then, Genise and Micciancio [25] gave improved algorithms in 2018. Therefore, the proposed scheme applies the trapdoor generation functions [24,25] and introduces them here.
Given a prime q and two positive integers . To obtain a trapdoor of a lattice, a gadget vector is defined as , where . Moreover, a gadget matrix is defined as
Definition 8.
- Given a matrix and an invertible matrix . Output a matrix and a trapdoor of , where . Moreover, the trapdoor’s quality guaranteed that , where the function extracts the Euclidean length of the input, and the little-omega notation is an asymptotic notation.
Definition 9.
- Given a matrix , a trapdoor of , an invertible matrix , a target , and a Gaussian parameter σ. Output a vector such that .
The details of how to generate with a gadget matrix is described as follows:
- Randomly choose a perturbation vector with , and divide into two parts :
- Compute
- Choose a vector from , and compute
- Output .
Definition 10.
- Given a matrix ( is an arbitrary matrix), a trapdoor of , an invertible matrix , and a Gaussian parameter σ. Output a trapdoor of .
will call repeatedly until getting a trapdoor containing d linearly independent vectors such that .
2.6. Tree-Based Access Structure
In the proposed scheme, the data owner will choose a set of keywords while encrypting data, and a data user may determine a keyword-search policy while generating a search token. Moreover, the cloud server will send the encrypted data to the data user if satisfies . The access structure in the proposed scheme is a tree-based access structure supporting OR and AND gates.
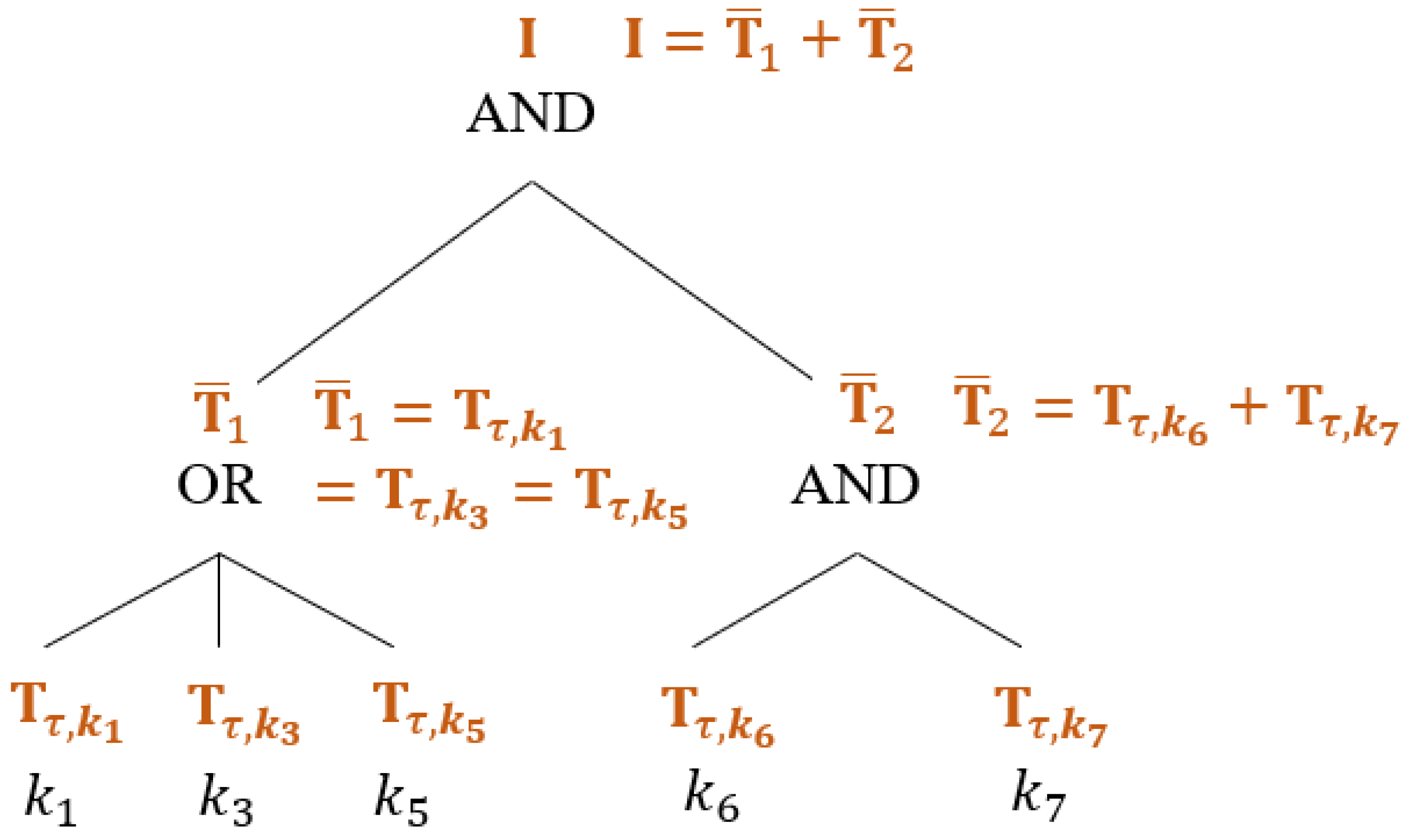
Figure 1 shows an example of the tree-based access structure applied in the proposed scheme. In the example, the keyword-search policy , where denotes the i-th keyword in the system. Here is how to generate , which will be used in the proposed scheme. First, the data user will set the value of the root node as an identity matrix . Second, since the root node has two child nodes and requires an AND gate, the data user will compute two invertible matrices such that . Third, since has three child nodes and requires an OR gate, the data user will set . Fourth, since has two child nodes and requires an AND gate, the data user will compute two invertible matrices such that . Finally, each belonging to will be used to generate a search token in the proposed scheme. If a keyword set can exactly satisfy , then . For example, in Figure 1, both and can exactly satisfy , then .
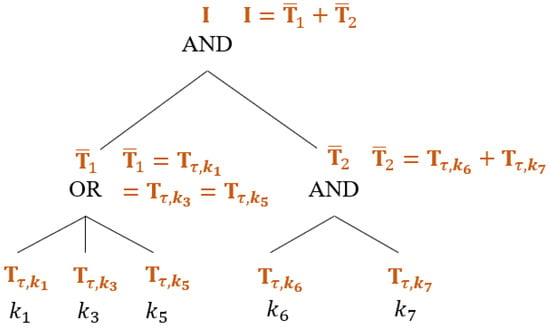
Figure 1.
Example of a Tree-Based Keyword-Search Policy .
2.7. System Model
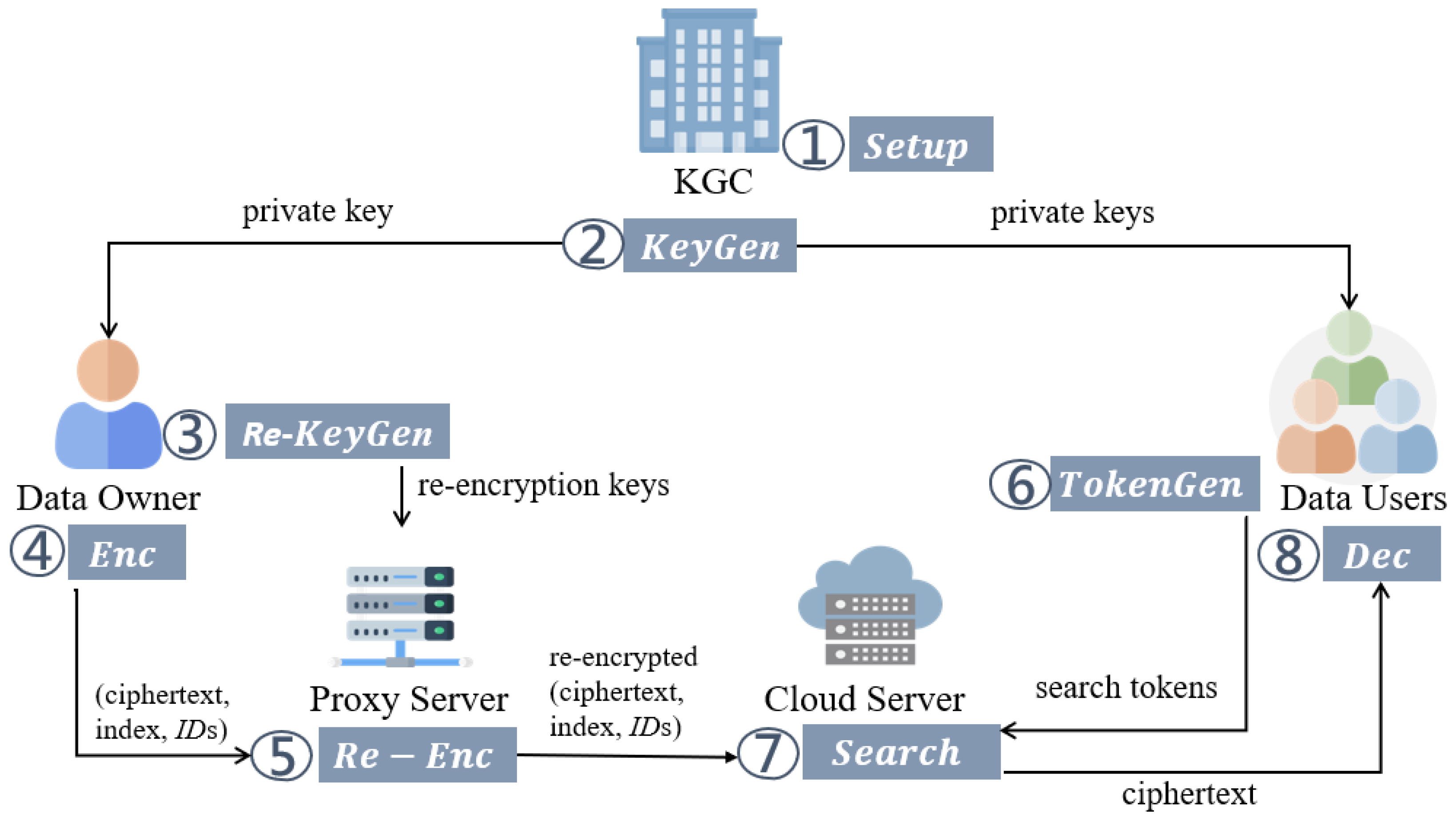
Figure 2 shows the system model of the proposed scheme. It includes five system roles, and their behaviors are defined as follows.
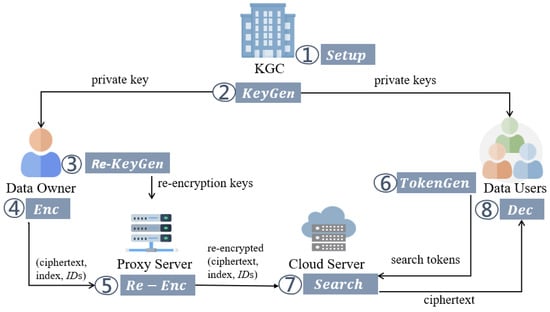
Figure 2.
The System Model.
- Key Generation Center (KGC): KGC is fully trusted and is responsible for system setup and key distribution.
- Data Owner (DO): DO can pre-generate re-encryption keys and send them to PS before the encryption phase. Then, in the encryption phase, DO computes the ciphertext, index, and s (a set of DUs’ identities). Then, DO sends (ciphertext, index, s) to PS.
- Proxy Server (PS): PS is fully trusted and responsible for re-encryption. After receiving the re-encryption keys, ciphertext, index, and s from DO, PS re-encrypts the ciphertext and index. Finally, PS sends the re-encrypted results to CS.
- Cloud Server (CS): CS is honest-but-curious and responsible for data storage and search.
- Data User (DU): DU can send a search request with a search token to CS to download matching ciphertexts.
The proposed scheme consists of the following polynomial-time algorithms.
- : Taking a security parameter as input, KGC outputs the public parameters and the master secret key .
- : With a user’s identity and as inputs, KGC computes the private key of the user.
- Re-KeyGen(): Taking DU’s identity , and as inputs, the user computes the re-encryption key .
- Enc(: Taking an identity , a one-bit message , and a keyword set as inputs, DO outputs the ciphertext and the index .
- Re-Enc(): Given the ciphertext , the index , DO’s identity , DU’s identity , and a re-encryption key as inputs, PS computes the re-encrypted ciphertext and re-encrypted index .
- TokenGen(): Taking a keyword-search policy , , and as inputs, DU can compute the search token .
- or : Given , , and as inputs, CS checks whether matches . If the result matches, CS sends to DU. Otherwise, CS sends ⊥ to DU.
- Dec(): With and , DU decrypts and gets the plaintext .
2.8. Security Model
Based on the security requirements of cloud services, the proposed scheme achieves indistinguishability under chosen plaintext attacks (IND-CPA) and indistinguishability under chosen keyword attacks (IND-CKA). The security model is defined as the following IND-CPA and IND-CKA games. Assume that is a polynomial-time adversary, and the simulator simulates the games.
2.8.1. Ciphertext Security
The IND-CPA game is defined as follows:
- : gives a target identity to . receives a polynomial number of samples from the D-LWE oracle.
- initializes the system and sends public parameters to .
- can adaptively issue the following queries multiple times:
- –
- query: gives an identity to . sends to .
- –
- query: gives an identity to . sends to .
- –
- KeyGen query gives an identity . If , aborts it. Otherwise, sends to .
- –
- Re-KeyGen query gives DO’s identity and DU’s identity . If , aborts it. Otherwise, sends to .
- : submits two messages () to . randomly chooses . Then, computes the ciphertext related to . Finally, sends to .
- : may do more queries as in .
- : Finally, answers a bit . If , wins the IND-CPA game.
Definition 11.
The advantage of to win the IND-CPA game is defined as
Definition 12.
If no polynomial-time adversary wins the IND-CPA game with a non-negligible advantage, then the proposed scheme is IND-CPA secure.
2.8.2. Keyword-Search Security
The IND-CKA game is defined as follows:
- : gives a target identity and two target keywords to . randomly chooses and will use for the challenge. Furthermore, receives a polynomial number of samples from the D-LWE oracle.
- initializes the system and sends public parameters to .
- can adaptively issue the following queries multiple times:
- –
- query: gives an identity to . sends to .
- –
- query: gives an identity to . sends to .
- –
- KeyGen query gives an identity . If , aborts it. Otherwise, sends to .
- –
- Re-KeyGen query gives DO’s identity and DU’s indetiy . If , aborts it. Otherwise, sends to .
- –
- TokenGen query gives an identity and a keyword-search policy . If ( and ( contains or )), aborts it. Otherwise, sends to .
- : submits a signal to start the . computes the index related to . Finally, sends to .
- : may do more queries as in .
- : Finally, answers a bit . If , wins the IND-CKA game.
Definition 13.
The advantage of to win the IND-CKA game is defined as
Definition 14.
If no polynomial-time adversary wins the IND-CKA game with a non-negligible advantage, then the proposed scheme is IND-CKA secure.
3. Related Works
This section introduces a traditional SE scheme and some lattice-based schemes in recent years. The features comparison between the proposed scheme and those schemes will be shown in Section 6.
3.1. Huang et al.’s [26] Traditional Multi-Keyword Attribute-Based SE Scheme
Huang et al. [26] proposed a traditional multi-keyword attribute-based SE scheme in 2022. Their scheme supports AND and NOT operators in keyword search queries. Moreover, user access rights are verified during the decryption and keyword-search phases. However, since the scheme is based on discrete logarithm hard problems, it cannot resist quantum attacks. Since Huang et al.’s scheme uses traditional encryption, their scheme will not be compared in computation and transmission costs.
3.2. Wang et al.’s [27] Public Key SE Scheme from Lattices
In 2020, Wang et al. [27] introduced a public key SE scheme, which supports conjunctive keyword search (multi-keyword but only AND operators). Their multi-user scheme uses a user’s identity’s hash value as its public key. Therefore, their scheme is IBE. However, their scheme does not detail the decryption phase.
3.3. Attribute-Based SE Schemes from Lattices
Four attribute-based SE schemes are introduced here. Their access structures are all LSSS, which may cause errors in decryption.
3.3.1. Liu et al.’s [17] Scheme
In 2019, Liu et al. [17] proposed an attribute-based SE scheme. Since their method verifies user access rights only in the decryption phase, anyone can search the ciphertext without authentication in the keyword-search phase. Although there are multi-keywords in Liu et al.’s Encryption, the search token contains only one keyword. Liu et al.’s method requires KGC to be online to help users generate search tokens. Moreover, the access structure is LSSS, which may cause errors in decryption.
3.3.2. Varri et al.’s [20] Scheme
In 2021, Varri et al. [20] proposed an attribute-based SE scheme supporting multi-keyword searches. Although their method verifies user access rights in the keyword-search phase, all users use the same decryption key in the decryption phase. Although there are multi-keywords in their Encryption, the search token contains only one keyword. Therefore, the scheme does not support multi-keyword. Moreover, Varri et al.’s method also requires KGC to be online to generate search tokens. Furthermore, the access structure is LSSS, which may cause errors in decryption.
3.3.3. Chen’s [21] Scheme
In 2021, Chen [21] proposed an attribute-based SE scheme supporting dynamic membership management. His scheme is based on Wang’s scheme [28]. His method verifies user access rights in both the decryption and the keyword-search phases. Moreover, his search algorithm verifies times to ensure that the user is valid. However, the access structure is LSSS, which may cause errors in decryption. Moreover, the data user needs to know the access structure of the data before generating a search token. The algorithms of his scheme are shown as follows:
3.3.4. Wang’s [22] Scheme
In 2022, Wang [22] proposed an attribute-based multi-keyword SE scheme supporting dynamic membership management. Her scheme is based on Chen’s scheme [21]. Therefore, her scheme shares many similar features with Chen’s scheme, and the access structure is LSSS, which may cause errors in decryption. Moreover, the keywords are only protected by the hash function, which may be attacked by offline dictionary attacks.
3.4. Zhang et al.’s [19] Identity-Based SE Scheme from Lattices
In 2019, Zhang et al. [19] introduced an identity-based SE scheme, which reduces data owners’ computation and transmission costs with a proxy mechanism. Users can generate search tokens by themselves so that KGC can be offline. However, their scheme does not detail the decryption phase. Moreover, DU needs to know which proxy PS sent the data when generating a search token. Furthermore, CS needs a special public key of PS when testing the search.
3.5. Wang et al.’s [18] Lattice-Based SE Schemes Supporting SPE
In 2022, Wang et al. [18] proposed a SE scheme supporting SPE. Their scheme verifies user access rights during the decryption and keyword-search phases. Moreover, users can generate search tokens in Wang et al.’s method. Although their method supports multi-keywords, only OR operations are supported.
3.6. Lattice-Based SE Schemes Supporting PRE
Two lattice-based SE schemes supporting PRE are introduced here. Both schemes do not support functional encryption.
3.6.1. Zhang et al.’s [29] Scheme
In 2021, Zhang et al. [29] introduced an SE scheme providing proxy re-encryption. In their scheme, although users can generate search tokens by themselves, KGC must be online to help users generate re-encryption keys. Moreover, their scheme does not detail the decryption phase.
3.6.2. Hou et al.’s [30] Scheme
In 2022, Hou et al. [30] proposed a multi-keyword SE scheme with proxy re-encryption. Their scheme supports semantic aware search in keyword search queries. However, like Zhang et al.’s method, Hou et al.’s scheme does not detail the decryption phase and requires KGC to be online to generate re-encryption keys.
4. Construction
This section presents the proposed multi-keyword searchable identity-based proxy re-encryption scheme from lattices. The system model is defined in Section 2.7.
4.1. Algorithms
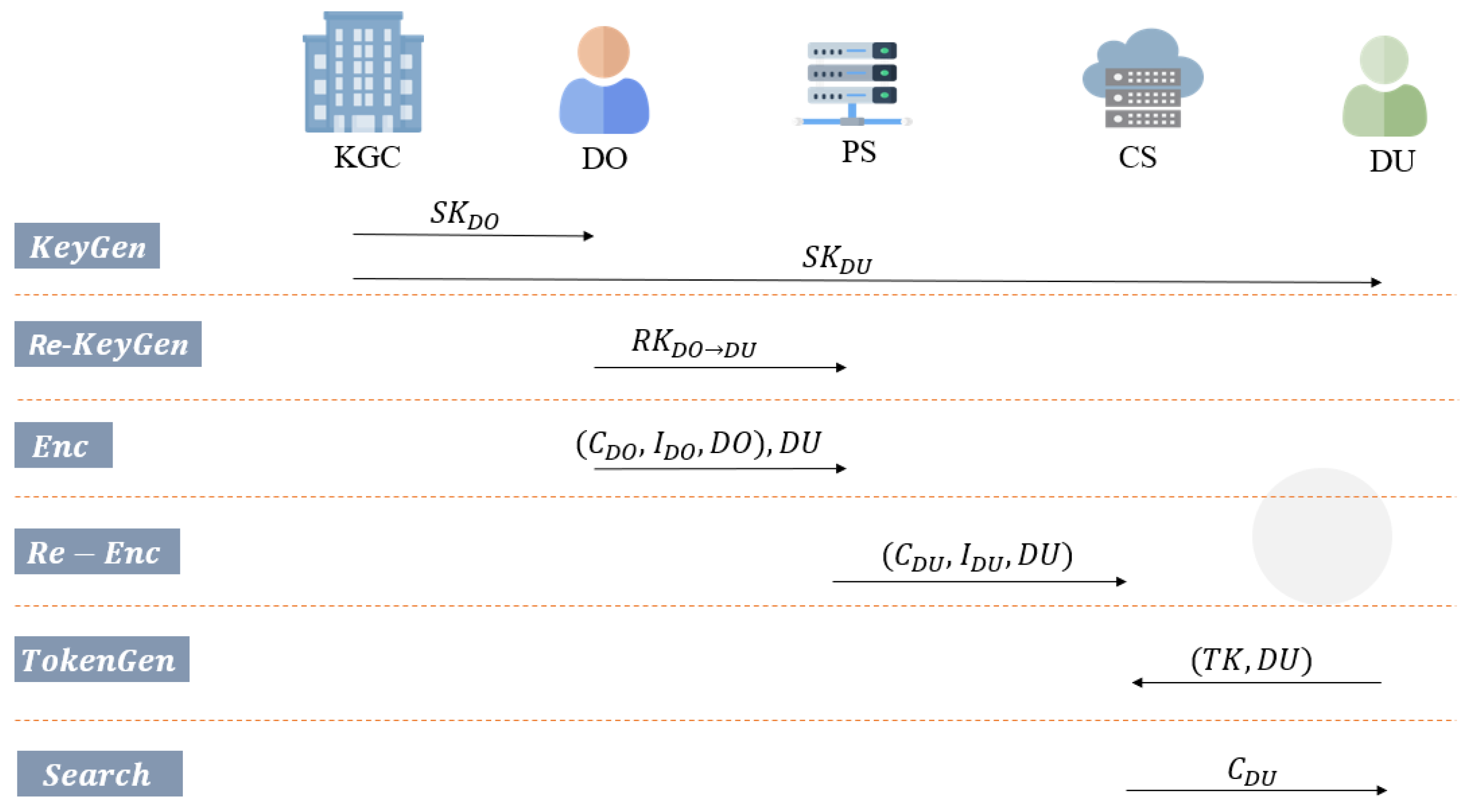
Table 1 shows the notations of the proposed scheme. Figure 3 presents the data flow of the proposed scheme. To make the figure simple and easy to understand, Figure 3 only shows the case of one DU. In actual situations, there may be multiple DUs, and DO should provide a re-encryption key to PS for each DU. Then, PS will compute a re-encrypted ciphertext and a re-encrypted index for each DU.

Table 1.
Notations.
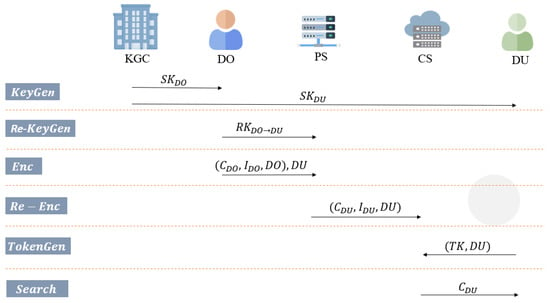
Figure 3.
Data Flow of The Proposed Scheme.
The proposed scheme includes eight algorithms as follows (Appendix A).
- Taking a security parameter , KGC sets up the system by the following steps:
- Select a Gaussian distribution , a Gaussian parameter , a prime q, four integers n, , l, and w, a keyword set , a random matrix , an invertible matrix , a random vector . Let .
- Select three hash functions , , and , where the output of or is an invertible matrix.
- Generate a matrix and a corresponding trapdoor of by invoking defined in Section 2.5, where is a gadget matrix defined in Section 2.5.
- Publish the public parameters and keep the master secret key .
In algorithm, is a special matrix that is public. can be an identity matrix and be public. Due to the difficulty of solving the ISIS problem defined in Section 2.3, even given , , , and , it is hard to find . Therefore, only the trapdoor needs to be kept secret. - With a user’s and as inputs, KGC runs to compute the user’s private key by the following steps:
- Compute .
- Set .
- Compute .
- Run DelTrap() defined in Section 2.5 to generate such that , where is a trapdoor of .
- Run SampleD () to generate so that .
- Set . and send it to the user.
will be treated as the public key associated with the user . However, because the number of bits of the matrix is relatively high, directly storing will consume a large storage space. Therefore, users only need to store the ID, and when users need to use A, they use the hash function to compute it. Anyone who knows the user ID can compute the corresponding . Similarly, users do not store directly, thereby reducing storage requirements. On the other hand, the determinants and should be small. Otherwise, it will affect the correctness of the proposed scheme. Since and need to be small, the difficulty for an adversary to compute an effective private key is equivalent to solving the ISIS problem. - )With , the user can compute the re-encryption key by the following steps:
- Compute .
- Set .
- Compute .
- Set .
- Compute .
- Perform SampleD() defined in Section 2.5 to get such that .
- Set .
The concept of re-encryption is to compute a matrix so that the matrix multiplied by will be equal to the matrix . Moreover, the determinant should be small, so it can be ignored in the search results or the decryption results. Otherwise, it will affect the correctness of those results. Since needs to be small, the difficulty for an adversary to compute an effective re-encryption key is equivalent to solving the ISIS problem. - Enc()Taking a one-bit message and a keyword set , DO encrypts with its by the following steps:
- Compute .
- Set .
- Sample noises and .
- Choose two secret vectors .
- Compute .
- Compute .
- Set the ciphertext .
- Compute .
- For to l,
- (a)
- if the keyword ,
- generate a random matrix .
- (b)
- if , perform the following steps:
- Compute .
- Compute .
- Set the index .
- Choose DUs’ identities s.
- Send (, , ), s) to PS.
To reduce the computation and transmission costs of DO by outsourced computing, DO encrypts the message with its public key. Then, DO sends the ciphertext, index, and DUs’ IDs to PS. When the number of DUs increases, DO only needs to increase the list of receivers without any other cost. Therefore, when the number of DUs is large, the proposed scheme can effectively reduce the burden on DO. - Re-Enc()Given the ciphertext , the index , DO’s identity , DU’s identity , and a re-encryption key , PS can transfer to by the following steps:
- Sample noises .
- Set .
- Compute .
- Set .
- Set .
- For to l, compute .
- Set .
- Upload () to CS.
PS computes an independent re-encrypted ciphertext and re-encrypted index for each DU. Moreover, the difficulty for an adversary to compute the re-encryption key from the ciphertext (or index) and the re-encrypted ciphertext (or re-encrypted index) is equivalent to solving the LWE problem. - TokenGen()Taking a keyword-search policy and the private key , the user can compute the search token by the following steps:
- Compute .
- Set .
- Compute .
- According to , generate invertible matrices . The detail of how to generate is described in Section 2.6.
- For to l,
- (a)
- if , then perform the following steps:
- Compute .
- Compute the inverse matrix of , such that , where is an identity matrix.
- Perform SampleD() to get such that .
- Set the search token .
- Send to CS.
In the proposed scheme, DU can generate tokens since it has a trapdoor specific to its public key . Therefore, KGC does not need to stay online to assist in generating tokens. On the other hand, through the method mentioned in Section 2.6, if a keyword set can exactly satisfy the keyword-search policy , then . Therefore, TK generated by the TokenGen algorithm will make the following equation hold: . - orGiven , , and , CS checks whether matches by the following steps:
- According to the keyword-search policy , for any keyword set exactly satisfying , CS performs the following steps:
- (a)
- Set .
- (b)
- for to l,
- if ,
- compute .
- (c)
- Compute .
- (d)
- If , send to DU.
- Return ⊥ to DU, if there are no matching search results.
By choosing appropriate parameter values, the size of the error term should be between and . Therefore, if the search token matches the index, the search result f should be less than . - Dec()With the ciphertext and private key , the user ID can decrypt by the following steps:
- Compute .
- If , return ; otherwise return .
By choosing appropriate parameter values, the size of the error term should be between and . Therefore, if the decrypted result is less than , the plaintext should be 0. Note that while DU may compute with the trapdoor , we recommend DU to store . Because computing it requires a SampleD operation, storing can reduce the computation cost for decryption.
4.2. Correctness
- Correctness in SearchSuppose , which means that the keyword set can exactly satisfy the keyword-search policy . Note that is an identity matrix.For the correctness of the search result, the absolute value of the error term must be less than .
- Correctness in DecryptionFor the correctness of the decryption result, the absolute value of the error term must be less than .
5. Security Proofs
The proposed scheme is IND-CPA secure in ciphertext security and IND-CKA secure in keyword-search security based on the D-LWE assumption defined in Section 2.4. Proof by contradiction is used to prove that the proposed scheme achieves IND-CPA security and IND-CKA security. This section presents the details of security proofs.
5.1. Ciphertext Security
Theorem 1.
The proposed scheme is IND-CPA secure in ciphertext security based on the D-LWE assumption.
Proof.
If there exists an adversary that can win the IND-CPA game defined in Section 2.8.1 with a non-negligible advantage in polynomial time, then the simulator can break the D-LWE assumption with by simulating the following game.
- : gives a target identity to . chooses two integers and sets . Then receives samples from the D-LWE oracle , where each .
- :
- –
- chooses and runs algorithm to generate the following parameters and hash functions .
- –
- sets , , and . Note that .
- –
- computes an invertible matrix and a small matrix such that , where is a gadget matrix defined in Section 2.5.
- –
- sets , and .
- –
- Finally, sends to .
- : may adaptively issue the following queries.
- –
- query: gives an identity to .
- *
- If , computes and sends it to .
- *
- If , sets and sends to .
- –
- query: gives an identity to .
- *
- If , computes and sends it to .
- *
- If ,
- ·
- if exists, returns to .
- ·
- else, computes an invertible matrix and a small matrix such that . stores and sends it to .
- –
- KeyGen query: gives an identity to .
- *
- If ,
- ·
- if exists, returns to .
- ·
- else, runs to generate . stores and sends it to .
- *
- If , aborts it.
- –
- Re-KeyGen query: gives DO’s identity and DU’s indetiy to .
- *
- If , runs Re-KeyGen() to generate and sends it to .
- *
- If , aborts it.
- : submits two different messages to . performs the following steps:
- –
- randomly chooses .
- –
- computes .
- –
- sets .
- –
- sets the ciphertext and sends it to .
- : may do more queries as in .
- : answers a bit to . If , answers the D-LWE assumption that the samples are from the noisy pseudo-random sampler . Otherwise, answers that the samples are from the truly random sampler .
If the samples from the D-LWE assumption are generated from , the ciphertext will be:
Therefore, the ciphertext simulated by will conform to the format of the proposed scheme. If has a non-negligible advantage to win the IND-CPA game defined in Section 2.8.1, the probability that can correctly guess b is .
Otherwise, if the samples are from , then the ciphertext is uniformly random. In this case, the probability that can correctly guess b is .
Thus, the advantage for to break the D-LWE assumption is
Therefore, if has an advantage to win the IND-CPA game, then has an advantage to break the D-LWE assumption in polynomial time. Since the D-LWE assumption is a hard problem, the proposed scheme achieves IND-CPA security. □
5.2. Keyword-Search Security
Theorem 2.
The proposed scheme is IND-CKA secure in keyword-search security based on the D-LWE assumption.
Proof.
If there exists an adversary that can win the IND-CKA game defined in Section 2.8.2 with a non-negligible advantage in polynomial time, then the simulator can break the D-LWE assumption with by simulating the following game.
- : gives a target identity and two target keywords to .
- –
- randomly chooses and will use for the challenge.
- –
- chooses two integers and sets . Then receives samples from the D-LWE oracle , where each .
- :
- –
- chooses and runs algorithm to generate the following parameters and hash functions .
- –
- sets , , and . Note that .
- –
- computes and its inverse matrix . Then stores .
- –
- computes the following matrices:
- *
- ,
- *
- .
Note that , and . - –
- computes an invertible matrix and a small matrix such that , where is a gadget matrix defined in Section 2.5.
- –
- sets , and .
- –
- Finally, sends to .
- : may adaptively issue the following queries.
- –
- query: gives an identity to .
- *
- If , computes and sends it to .
- *
- If , sets . Then, computes and sends to .
- –
- query: gives an identity to .
- *
- If , computes and sends it to .
- *
- If ,
- ·
- if exists, returns to .
- ·
- else, computes an invertible matrix and a small matrix such that . sets and stores it. Finally, stores and sends it to .
- –
- KeyGen query: gives an identity to .
- *
- If ,
- ·
- if exists, returns to .
- ·
- else, runs to generate . stores and sends it to .
- *
- If , aborts it.
- –
- Re-KeyGen query: gives DO’s identity and DU’s indetiy to .
- *
- If , runs Re-KeyGen() to generate and sends it to .
- *
- If , aborts it.
- –
- TokenGen query: gives an identity and a keyword-search policy to .
- *
- If ( and ( contains or )), aborts it.
- *
- Else, runs to generate . Then sends to .
- : submits a signal to start the phase. performs the following steps:
- –
- sets .
- –
- sets .
- –
- sets the index and sends it to .
- : may do more queries as in .
- : answers a bit to . If , answers the D-LWE assumption that the samples are from the noisy pseudo-random sampler . Otherwise, answers that the samples are from the truly random sampler .
If the samples from the D-LWE assumption are generated from , the index will be:
Therefore, the index simulated by will conform to the format of the proposed scheme. If has a non-negligible advantage to win the IND-CKA game defined in Section 2.8.2, the probability that can correctly guess b is .
Otherwise, if the samples are from , then the index is uniformly random. In this case, the probability that can correctly guess b is .
Thus, the advantage for to break the D-LWE assumption is
Therefore, if has an advantage to win the IND-CKA game, then has an advantage to break the D-LWE assumption in polynomial time. Since the D-LWE assumption is a hard problem, the proposed scheme achieves IND-CKA security. □
6. Comparison
Table 2 shows the features comparison between the proposed scheme and the schemes introduced in Section 3. Moreover, this section presents a performance comparison of the proposed scheme with other lattice-based searchable encryption schemes. Because some schemes use one-bit plaintext or one recipient to illustrate their schemes, it is not easy to make a completely fair comparison. For fairness, the plaintext in all schemes is set as a one-bit message, and the number of receivers is 1. Moreover, values that do not specify the meaning of parameters in all schemes will be set to m. The notations used for comparison are shown in Table 3.

Table 2.
Features Comparison.

Table 3.
Notations for Comparison.
6.1. Transmission Cost
We compare the ciphertext size, index size, and token size with other lattice-based schemes. The transmission cost of the schemes are shown in Table 4.
- Ciphertext size: Since the proposed scheme uses DelTrap to achieve ID-based features, the ciphertext size requires bits. On the other hand, all users use the same key for decryption in [20], so its ciphertext size can be shorter than other schemes. Moreover, [19,27,29,30] do not provide or detail the decryption phase.
- Index size: The proposed scheme supports multi-keyword search, which requires a multiple of l more index sizes. Therefore, the index size of the proposed scheme is .
- Token size: The proposed scheme supports multi-keyword search, which requires a multiple of l more token sizes. Therefore, the token size of the proposed scheme is .
To compare, one can consider comparing single-keyword searches. One can set and . Then, in the proposed scheme, the ciphertext size is , the index size is , and the token size is . In this case, the proposed scheme is only slightly worse than [19,29] in the part of the token size. Therefore, the proposed scheme has a good performance in transmission cost.

Table 4.
Comparison of Transmission Cost.
Table 4.
Comparison of Transmission Cost.
| Ciphertext Size | Index Size | Token Size | |
|---|---|---|---|
| Wang et al. [27] | ✗ | ||
| Liu et al. [17] | |||
| Varri et al. [20] | |||
| Chen [21] | |||
| Wang [22] | |||
| Zhang et al. [19] | ✗ | ||
| Wang et al. [18] | |||
| Zhang et al. [29] | ✗ | ||
| Hou et al. [30] | ✗ | ||
| Ours |
✗ indicates that the scheme does not provide or detail the part.
6.2. Computation Cost
We compare the costs of “Encryption plus Index”, Decryption, TokenGen, and Search with other lattice-based schemes. The details of computation cost are shown in Table 5 and Table 6. For fairness, we compare the amount of required for matrix multiplication in each scheme, where denotes the computation cost of a multiplication operation in . denotes the cost of computing an inverse matrix. and denote the cost of running a hash function and a Flatten operation, respectively. , and denote the costs of running algorithms BasisDel, SampleD, SamplePre, and SampleLeft, respectively. denotes the decryption cost of fully homomorphic encryption. denotes the cost of computing an integer coefficient set in LSSS.

Table 5.
Comparison of Computation Cost—Part 1.

Table 6.
Comparison of Computation Cost—Part 2.
To compare, one can consider comparing single-keyword searches. One can set and . Then, in the proposed scheme, the Encryption cost is , the Decryption cost is , the TokenGen cost is , and the Search cost is . In this case, the proposed scheme has good performance in Decryption and Search costs but a higher cost in Encryption and TokenGen costs.
6.3. Summary
Compared with other schemes, the proposed scheme has good performance in transmission cost. Although the proposed scheme has a slightly higher computation cost than other schemes in the case of a single-keyword search, the proposed scheme is the first to simultaneously support multi-keyword search, identity-based encryption, proxy re-encryption, and offline KGC. Furthermore, it verifies the user’s access rights during the decryption phase and the search phase. In addition, as the number of DUs increases, the costs required for DO remain the same, and PS will handle the increased workload.
On the other hand, the type-2 trapdoor has smaller n and m than the type-1 trapdoor. Our scheme uses the type-2 trapdoor, but other schemes [19,21,22,29] use the type-1 trapdoor , which does not increase dimension when generating new basis. If they use the type-1 trapdoor, then the comparison results will change. Therefore, the efficiency of the proposed scheme will be relatively better in reality.
7. Conclusions
In this research, a multi-keyword searchable identity-based proxy re-encryption scheme from lattices has been proposed. First, based on the D-LWE assumption, the proposed scheme can resist quantum attacks. Second, it provides multi-keyword searchability with AND and OR operators, increasing the flexibility of keyword searches. Third, KGC in the proposed scheme can be offline, avoiding the risk of being attacked by adversaries through the network. Fourth, the proposed scheme supports PRE to reduce file-sharing costs of the data owner. The costs of the data owner will remain the same as the number of data users increases. Fifth, to prevent illegal access to files, the user’s access rights are verified in both the search and decryption phases. Finally, the proposed scheme is identity-based, avoiding the cost of using certificates.
Compared with other schemes, the proposed scheme has good performance in transmission cost. Although the proposed scheme has a slightly higher computation cost than other schemes in the case of a single-keyword search, the proposed scheme supports multi-keyword search, increasing the flexibility of keyword searches. In addition, the cost of the data owner does not increase with the number of data users. In the future, we will try to reduce the transmission and computation costs of the proposed scheme. Furthermore, future research will be designing a new multi-keyword mechanism that supports threshold operations.
Author Contributions
Conceptualization, all authors; methodology, E.-S.Z.; software, E.-S.Z.; validation, all authors; formal analysis, all authors; investigation, E.-S.Z.; resources, E.-S.Z.; data curation, E.-S.Z.; writing—original draft preparation, E.-S.Z.; writing—review and editing, C.-I.F.; visualization, E.-S.Z.; supervision, C.-I.F.; project administration, C.-I.F.; funding acquisition, C.-I.F. All authors have read and agreed to the published version of the manuscript.
Funding
This work was partially supported by the National Science and Technology Council (NSTC) of Taiwan under grants 112-2634-F-110-001-MBK and 110-2923-E-110-001-MY3. It also was financially supported by the Information Security Research Center at National Sun Yat-sen University in Taiwan and the Intelligent Electronic Commerce Research Center from The Featured Areas Research Center Program within the framework of the Higher Education Sprout Project by the Ministry of Education (MOE) in Taiwan.
Data Availability Statement
Not applicable.
Conflicts of Interest
The authors declare no conflict of interest.
Abbreviations
The following abbreviations are used in this manuscript:
| IBE | Identity-Based Encryption |
| ABE | Attribute-Based Encryption |
| SPE | Subset-Predicate Encryption |
| PRE | Proxy Re-Encryption |
| SE | Searchable Encryption |
| LWE | Learning With Error |
| D-LWE | Decisional Learning with Errors |
| ISIS | Inhomogeneous Short Integer Solution |
| KGC | Key Generation Center |
| DO | Data Owner |
| DU | Data User |
| PS | Proxy Server |
| CS | Cloud Server |
| IND-CPA | INDistinguishability under Chosen Plaintext Attacks |
| IND-CKA | INDistinguishability under Chosen Keyword Attacks |
| LSSS | Linear Secret Sharing Scheme |
| NIST | the National Institute of Standards and Technology |
Appendix A
Here, the proposed scheme is presented in pseudo-code to make the algorithms easier to understand.
| Algorithm A1 Setup |
| Require: A security parameter . |
| Ensure: The public parameters and the master secret key . |
|
| Algorithm A2 KeyGen |
| Require: , the user’s . |
| Ensure: The private key . |
|
| Algorithm A3 Re-KeyGen |
| Require: , the user’s , the delegate’s . |
| Ensure: The re-encryption key . |
|
| Algorithm A4 Encrypt |
| Require: , a one-bit message , a keyword set , and DO’s identity . |
| Ensure: The ciphertext , the index , , and DUs’ identities . |
|
| Algorithm A5 Re-Enc |
| Require: , , ), , and a re-encryption key |
| Ensure: The re-encrypted ciphertext , the re-encrypted index , and . |
|
| Algorithm A6 TokenGen |
| Require: , , , , and a keyword-search policy . |
| Ensure: A search token and . |
|
| Algorithm A7 Search |
| Require: , , , and . |
| Ensure: or ⊥. |
|
| Algorithm A8 Dec |
| Require: and . |
| Ensure: . |
|
References
- Shamir, A. Identity-based cryptosystems and signature schemes. In Proceedings of the Workshop on the Theory and Application of Cryptographic Techniques, Paris, France, 9–11 April 1984; Springer: Berlin/Heidelberg, Germany, 1984; pp. 47–53. [Google Scholar]
- Sahai, A.; Waters, B. Fuzzy identity-based encryption. In Proceedings of the Annual International Conference on the Theory and Applications of Cryptographic Techniques, Aarhus, Denmark, 22–26 May 2005; Springer: Berlin/Heidelberg, Germany, 2005; pp. 457–473. [Google Scholar]
- Katz, J.; Maffei, M.; Malavolta, G.; Schröder, D. Subset predicate encryption and its applications. In Proceedings of the Cryptology and Network Security: 16th International Conference, CANS 2017, Hong Kong, China, 30 November–2 December 2017; Springer: Berlin/Heidelberg, Germany, 2018; pp. 115–134. [Google Scholar]
- Blaze, M.; Bleumer, G.; Strauss, M. Divertible protocols and atomic proxy cryptography. In Proceedings of the Advances in Cryptology—EUROCRYPT’98: International Conference on the Theory and Application of Cryptographic Techniques, Espoo, Finland, 31 May–4 June 1998; Springer: Berlin/Heidelberg, Germany, 1998; pp. 127–144. [Google Scholar]
- Green, M.; Ateniese, G. Identity-based proxy re-encryption. In Proceedings of the Applied Cryptography and Network Security: 5th International Conference, ACNS 2007, Zhuhai, China, 5–8 June 2007; Springer: Berlin/Heidelberg, Germany, 2007; pp. 288–306. [Google Scholar]
- Liang, X.; Cao, Z.; Lin, H.; Shao, J. Attribute based proxy re-encryption with delegating capabilities. In Proceedings of the 4th International Symposium on Information, Computer, and Communications Security, Sydney, Australia, 10–12 March 2009; pp. 276–286. [Google Scholar]
- Song, D.X.; Wagner, D.; Perrig, A. Practical techniques for searches on encrypted data. In Proceedings of the 2000 IEEE Symposium on Security and Privacy, S&P, Berkeley, CA, USA, 14–17 May 2000; IEEE: Piscataway, NJ, USA, 2000; pp. 44–55. [Google Scholar]
- Boneh, D.; Di Crescenzo, G.; Ostrovsky, R.; Persiano, G. Public key encryption with keyword search. In Proceedings of the Advances in Cryptology-EUROCRYPT 2004: International Conference on the Theory and Applications of Cryptographic Techniques, Interlaken, Switzerland, 2–6 May 2004; Springer: Berlin/Heidelberg, Germany, 2004; pp. 506–522. [Google Scholar]
- Hwang, Y.H.; Lee, P.J. Public key encryption with conjunctive keyword search and its extension to a multi-user system. In Proceedings of the Pairing-Based Cryptography–Pairing 2007: First International Conference, Tokyo, Japan, 2–4 July 2007; Springer: Berlin/Heidelberg, Germany, 2007; pp. 2–22. [Google Scholar]
- Shor, P.W. Algorithms for quantum computation: Discrete logarithms and factoring. In Proceedings of the 35th Annual Symposium on Foundations of Computer Science, Santa Fe, NM, USA, 20–22 November 1994; IEEE: Piscataway, NJ, USA, 1994; pp. 124–134. [Google Scholar]
- Bos, J.; Ducas, L.; Kiltz, E.; Lepoint, T.; Lyubashevsky, V.; Schanck, J.M.; Schwabe, P.; Seiler, G.; Stehlé, D. CRYSTALS-Kyber: A CCA-secure module-lattice-based KEM. In Proceedings of the 2018 IEEE European Symposium on Security and Privacy (EuroS&P), London, UK, 24–26 April 2018; IEEE: Piscataway, NJ, USA, 2018; pp. 353–367. [Google Scholar]
- Ajtai, M. Generating hard instances of lattice problems. In Proceedings of the Twenty-Eighth Annual ACM Symposium on Theory of Computing, Hiladelphia, PA, USA, 22–24 May 1996; pp. 99–108. [Google Scholar]
- Hoffstein, J.; Pipher, J.; Silverman, J.H. NTRU: A ring-based public key cryptosystem. In Proceedings of the International Algorithmic Number Theory Symposium, Burlington, VT, USA, 13–18 June 2004; Springer: Berlin/Heidelberg, Germany, 1998; pp. 267–288. [Google Scholar]
- Regev, O. On lattices, learning with errors, random linear codes, and cryptography. In Proceedings of the Thirty-Seventh Annual ACM Symposium on Theory of Computing, Baltimore, MD, USA, 22–24 May 2005; pp. 84–93. [Google Scholar]
- Boyen, X. Attribute-based functional encryption on lattices. In Proceedings of the Theory of Cryptography Conference, Tokyo, Japan, 3–6 March 2013; Springer: Berlin/Heidelberg, Germany, 2013; pp. 122–142. [Google Scholar]
- Singh, K.; Rangan, C.P.; Banerjee, A. Lattice based identity based unidirectional proxy re-encryption scheme. In Proceedings of the International Conference on Security, Privacy, and Applied Cryptography Engineering, Pune, India, 18–22 October 2004; Springer: Berlin/Heidelberg, Germany, 2014; pp. 76–91. [Google Scholar]
- Liu, L.; Wang, S.; He, B.; Zhang, D. A keyword-searchable abe scheme from lattice in cloud storage environment. IEEE Access 2019, 7, 109038–109053. [Google Scholar] [CrossRef]
- Wang, P.; Chen, B.; Xiang, T.; Wang, Z. Lattice-based public key searchable encryption with fine-grained access control for edge computing. Future Gener. Comput. Syst. 2022, 127, 373–383. [Google Scholar] [CrossRef]
- Zhang, X.; Tang, Y.; Wang, H.; Xu, C.; Miao, Y.; Cheng, H. Lattice-based proxy-oriented identity-based encryption with keyword search for cloud storage. Inf. Sci. 2019, 494, 193–207. [Google Scholar] [CrossRef]
- Varri, U.S.; Pasupuleti, S.K.; Kadambari, K. CP-ABSEL: Ciphertext-policy attribute-based searchable encryption from lattice in cloud storage. Peer Peer Netw. Appl. 2021, 14, 1290–1302. [Google Scholar] [CrossRef]
- Chen, X.J. Lattice-Based Searchable Attribute-Based Encryption Supporting Dynamic Membership Management. Master’s Thesis, National Sun Yet-sen University, Kaohsiung, Taiwan, 2021. [Google Scholar]
- Wang, D.R. Multi-Keyword Searchable Attribute-Based Encryption Supporting Dynamic Membership Management from Lattices. Master’s Thesis, National Sun Yet-sen University, Kaohsiung, Taiwan, 2022. [Google Scholar]
- Regev, O. On lattices, learning with errors, random linear codes, and cryptography. J. ACM 2009, 56, 1–40. [Google Scholar] [CrossRef]
- Micciancio, D.; Peikert, C. Trapdoors for lattices: Simpler, tighter, faster, smaller. In Proceedings of the Annual International Conference on the Theory and Applications of Cryptographic Techniques, Cambridge, UK, 15–19 April 2012; Springer: Berlin/Heidelberg, Germany, 2012; pp. 700–718. [Google Scholar]
- Genise, N.; Micciancio, D. Faster Gaussian sampling for trapdoor lattices with arbitrary modulus. In Proceedings of the Advances in Cryptology–EUROCRYPT 2018: 37th Annual International Conference on the Theory and Applications of Cryptographic Techniques, Tel Aviv, Israel, 29 April–3 May 2018; Springer: Berlin/Heidelberg, Germany, 2018; pp. 174–203. [Google Scholar]
- Huang, Q.; Yan, G.; Wei, Q. Attribute-based expressive and ranked keyword search over encrypted documents in cloud computing. IEEE Trans. Serv. Comput. 2022, 16, 957–968. [Google Scholar] [CrossRef]
- Wang, P.; Xiang, T.; Li, X.; Xiang, H. Public key encryption with conjunctive keyword search on lattice. J. Inf. Secur. Appl. 2020, 51, 102433. [Google Scholar] [CrossRef]
- Wang, Y. Lattice Ciphertext Policy Attribute-based Encryption in the Standard Model. Int. J. Netw. Secur. 2014, 16, 444–451. [Google Scholar]
- Zhang, E.; Hou, Y.; Li, G. A lattice-based searchable encryption scheme with the validity period control of files. Multimed. Tools Appl. 2021, 80, 4655–4672. [Google Scholar] [CrossRef]
- Hou, Y.; Yao, W.; Li, X. A Lattice-Based Semantic Aware Multi-Keyword Searchable Encryption for Multi-User Environments. SSRN 2022. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).