Abstract
Output sequences of the cryptographic pseudo-random number generator, known as the generalized self-shrinking generator, are obtained self-decimating Pseudo-Noise (PN)-sequences with shifted versions of themselves. In this paper, we present three different representations of this family of sequences. Two of them, the p and G-representations, are based on the parameters p and G corresponding to shifts and binary vectors, respectively, used to compute the shifted versions of the original PN-sequence. In addition, such sequences can be also computed as the binary sum of diagonals of the Sierpinski’s triangle. This is called the B-representation. Characteristics and generalities of the three representations are analyzed in detail. Under such representations, we determine some properties of these cryptographic sequences. Furthermore, these sequences form a family that has a group structure with the bit-wise XOR operation.
1. Introduction
Most of the devices that form part of the Internet-of-Things (IoT) require cryptographic security features to prevent users from data losses and the risks related to an improper use of passwords. Putting into effect cryptographic security is complicated. Most of the security systems are based on true random numbers, but their generation is really a difficult task [1,2]. Many popular random “noise” algorithms, for example, algorithms that are part of IoT devices, end up to be imperfect, showing glitches that make them predictable and vulnerable. Some weaknesses are never (publicly) found out, creating a false sense of security. The devices in which flaws are detected are those with the most flagrant errors and those most popular, for example, algorithms A5 in GSM communications cryptanalyzed in [3,4], the generator RC4 for encrypting Internet traffic cryptanalyzed in [5] or the J3Gen generator for low-cost passive RFID tags cryptanalyzed in [6]. To sum up, it is hard to build a true random number generator that can provide a strong cryptographic foundation for system security, especially for IoT devices (see [7,8]).
Pseudo-Random Number Generators (PRNGs) are reproducible and deterministic algorithms [9,10] used to generate random number sequences for cryptographic applications, such as key and nonces generation, digital signatures, and IoT security. These applications require various statistical properties, such as low autocorrelation, large period and linear complexity, rich dimensional distribution of the output sequence, and uniformity of distribution for large quantities of generated numbers (see ([11], Chapter 2) for more details).
Binary sequences produced by maximal-length Linear Feedback Shift Registers (LFSRs), called Pseudo-Noise (PN)-sequences [12], have been widely used in many diverse applications such as digital broadcasting, mobile wireless communications, e-commerce or cryptography (stream ciphers) [13,14]. In order to ensure practical cryptographic stability, it is necessary to destroy the linearity inherent to PN-sequences via different non-linear procedures.
LFSRs play an important role in the design of cryptographic PRNGs [15,16]. Among the most popular families of cryptographic sequence generators based on PN-sequences we can enumerate: non-linear filters with only one LFSR, combination generators that involve several LFSRs, clock-controlled registers where one LFSR controls the clock of the others or irregular decimation-based generators [11]. We focus our attention on this latter family.
Generally speaking, the regular decimation [17] of a sequence by distance d is a new sequence obtained by taking every d-th term of , that is, . Nevertheless, it is the irregular decimation of PN-sequences [18], which can be considered as a powerful PRNG, producing sequences with good cryptographic properties, such as long periods, good distribution of zeros and ones along the sequence, large linear complexity, and two-valued autocorrelation properties.
In the literature, there are three well-known irregularly decimated generators: the shrinking generator [19], made up of two LFSRs with different lengths, the self-shrinking generator [20], based on the self-decimation of one single PN-sequence, and the generalized self-shrinking generator (GSSG) [21], which produces a family of sequences that includes the sequence produced by the self-shrinking generator [22]. Moreover, the modified self-shrinking generator [23] and the t-modified self-shrinking generator [24] are also members of such a family. These generators are fast, easy to implement and they generate good cryptographic sequences. Therefore, they seem adequate for lightweight cryptography and, in general, low-cost applications. In [25], the authors studied the randomness of the family of sequences generated by the GSSG by means of several complete and powerful batteries of statistical tests and graphical tools. In fact, they provided a useful vision of the behavior of such sequences and proved their suitability for cryptographic applications. In [24], the relationship among the generalized self-shrinking generator and the t-modified self-shrinking generator is deeply analyzed. Furthermore, in [26], the authors studied the relationship between that generator and the modified self-shrinking generator. In [27], other authors presented an extension of the self-shrinking generator to the Galois field of elements with p a prime integer, that is, the p-ary Generalized Self-Shrinking Generator (p-GSSG). Furthermore, they proved that the sequences generated by this new generator have large periods and good statistical properties.
At any rate, there exist other ways to built irregularly decimated generators, for example, irregularly decimated generators based on Feedback with Carry Shift Registers (FCSRs) instead of the traditional LFSRs [28,29]. These variants of the previous generators unify in a unique structure the non-linearity inherent to the FCSRs with the irregular decimation technique. An FCSR is the arithmetic or with carry analog of an LFSR. The main difference is the fact that the elementary additions are not modulo 2 additions but with the propagation of carries. FCSRs have been used in the design of stream ciphers [30], generating pseudo-random numbers [31], and can be efficiently implemented in parallel architectures [32].
In modern algebra, group theory is the study of groups, which are sets of elements with an operation that satisfies certain axioms. The basic structure of groups can be found in many mathematical phenomena such as symmetry and certain types of transformations. Group theory has applications in robotics, computer vision/graphics and medical image analysis, physics, chemistry, computer science, and even puzzles like Rubik’s cube can be represented using group theory [33,34,35,36,37]. As we show in this paper, group theory also has applications in cryptography, since the set of output sequences of the generalized self-shrinking generator has the structure of an additive group and some of the properties of this family of sequences can be deduced as a consequence of this fact.
In this work, we study in detail three different representations of the sequences produced by the GSSG: the G-representation (introduced in [21]), the new p-representation and the B-representation (introduced in [38]). As far as we know, there are no other known representations for this kind of generators in the literature. In addition, we introduce a new way to compute the B-representation. Such a representation relates the output sequences of our generator with shifted versions of the diagonals of the binary Sierpinski’s triangle, named binomial sequences. In terms of this representation, the structural properties of some binary sequences are easily analyzed. In brief, we give a binomial expression of these sequences, providing a relation among binomial coefficients, binary sequences and group theory.
2. Fundamentals and Basic Notation
In this section, we introduce some of the main concepts related to our work: the generalized self-shrinking generator and the binomial sequences.
2.1. PN-Sequences and GSSG
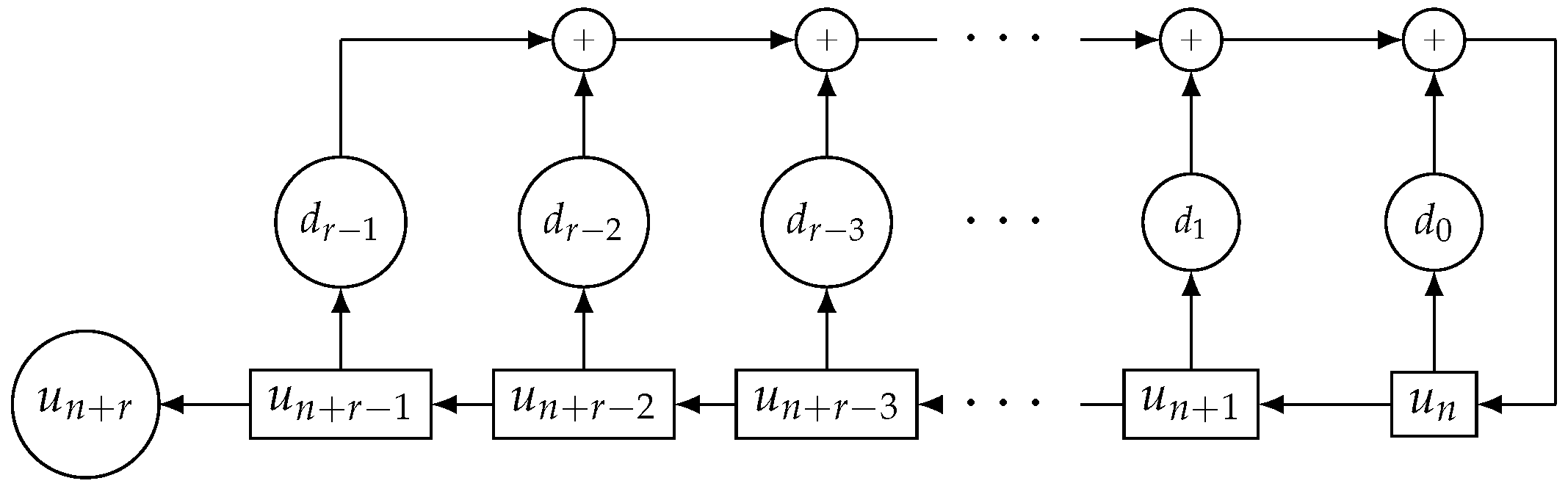
Traditionally, LFSRs implement linear recurring sequences [12]. LFSRs are electronic devices in which the information units are elements of binary field . They are made up of r interconnected memory cells (stages) that shift their contents to their next stages and a linear feedback to the empty stage. The register is shown in Figure 1.
Figure 1.
Linear Feedback Shift Registers (LFSR) of length r.
Generates the linear recurring sequence (or denoted by ) given by
If the monic polynomial
is a primitive polynomial, then the LFSR is called a maximal-length LFSR [12] and generates a PN-sequence (Pseudo Noise sequence) with maximum period with ones and zeros. This polynomial is known as the characteristic polynomial of the recurring sequence.
A common metric of the security of a sequence for its possible cryptographic application is the linear complexity [39,40,41], denoted by . Roughly speaking, the parameter determines the portion of sequence we need in order to recover the whole sequence. In fact, is the length of the shortest LFSR that generates such a sequence ([42], Chapter 5). Making use of the concept of recurrence, we can say that the of a sequence is the lowest order of its linear recurrence relationship. In cryptography, linear complexity clearly must take a large value, for example, half of the period: . Nowadays, values of T in the range seem to be enough for cryptographic purposes (see specifications of the candidates in the call of NIST for lightweight cryptography primitives [43]).
Consider a PN-sequence obtained from a maximal-length LFSR with L stages, an L-dimensional binary vector and let be the sequence defined as:
Next, we define a decimation rule to generate a new sequence as follows:
The sequence , denoted by , is called the generalized self-shrunken sequence, GSS-sequence or simply generalized sequence associated with , see [21]; and the sequence generator is called the generalized self-shrinking generator (GSSG).
Notice that when runs over we obtain all the shifted versions of (see Theorem 2). The set of sequences is called the family of generalized sequences based on the PN-sequence . This family with the addition modulo 2, that is, with the bit-wise XOR operation, is an additive group [21]. In particular, the neutral element is the sequence and the opposite of any sequence is the sequence itself. Moreover, the period of every generalized sequence is a divisor of (the number of ones in the PN-sequence) and every sequence of this family is balanced except for the sequence identically of 1 and the null sequence ([21], Theorem 1).
Example 1.

Consider the primitive polynomial and the PN-sequence generated by with initial state . As illustration of the decimation rule given in (2) consider, for instance, and the corresponding sequence . We apply the decimation rule as follows: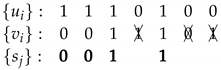 The corresponding generalized sequence is .
The corresponding generalized sequence is .
 The corresponding generalized sequence is .
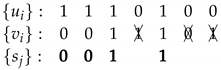
The corresponding generalized sequence is .In Table 1, we can see the family of all generalized sequences generated by the PN-sequence . Notice that the sequences are shifted versions of the PN-sequence (which appears at the bottom of the table), a fact that we will prove later in Theorem 2. The bits in bold of each sequence are the bits of the corresponding generalized sequence.

Table 1.
Generalized sequences for .
Notice that, since the number of ones in a PN-sequence of period is (see [12]), the period of the generalized sequences is a divisor of . We will see that there are always two sequences of period 1 (the identically 1 and 0 sequences), two sequences of period 2, and , and the remaining sequences have the maximum period (although there is no mathematical proof for this last statement).
Relating to the linear complexity, in [39] Blackburn introduced an upper bound for the linear complexity of the self-shrinking generator. A generalization of this bound was introduced in [40] for the linear complexity of generalized sequences, that is, . Furthermore, we know that for all generalized sequences, except for those with period 1 and 2, we have (although there is no proof for this statement either).
2.2. Binomial Sequences
The binomial number represents the coefficient corresponding to in the expansion of the polynomial . For every integer , we know that while for . Now, binomial sequences are introduced as follows.
Definition 1.
Given a fixed integer , the sequence given by
is named the -th binomial sequence.
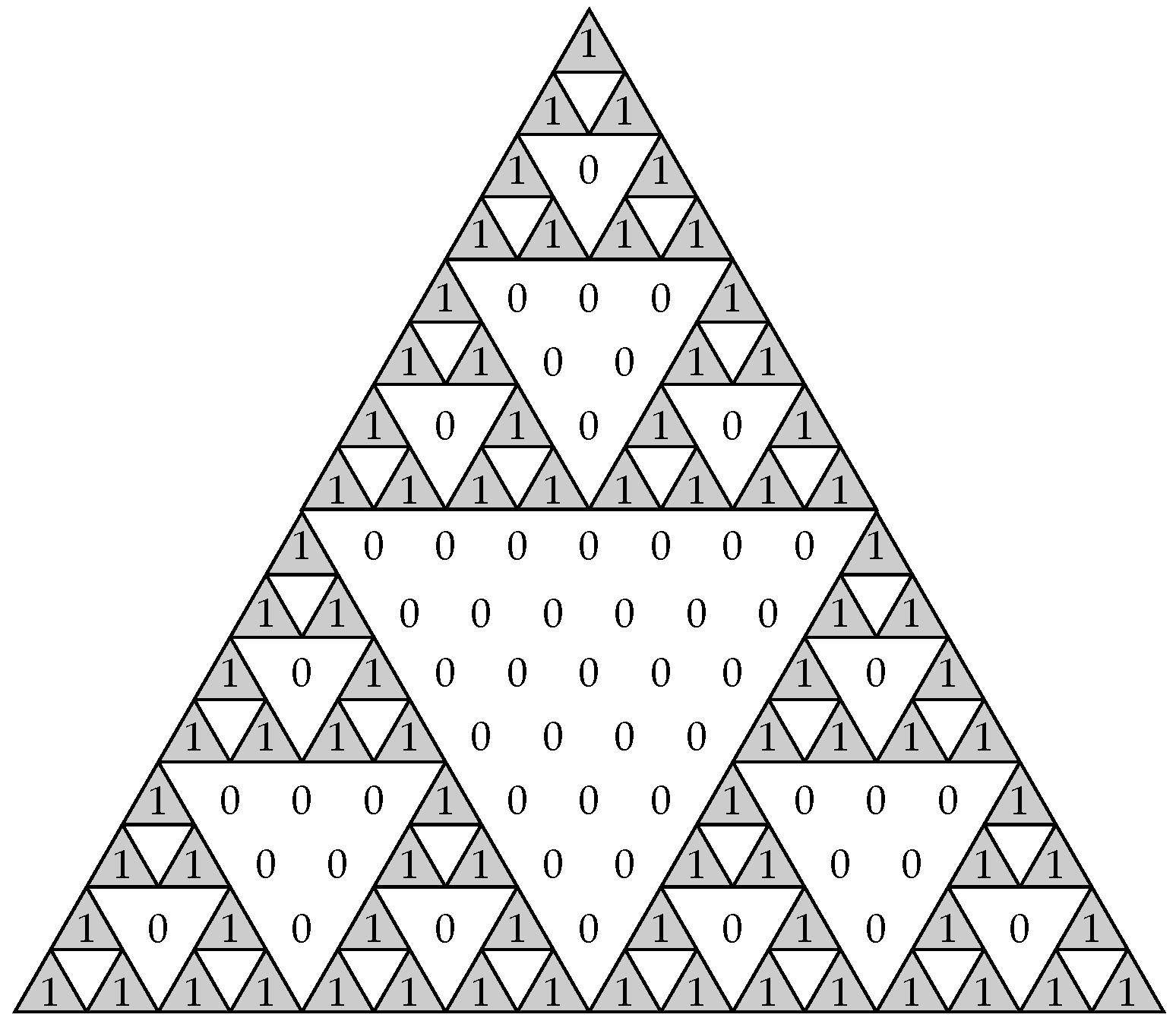
In the sequel, the sequence will be simply denoted by . Table 2 shows the first eight binomial coefficients as well as the first eight binomial sequences with their corresponding periods and linear complexities. To check the form of the first 32 binomial sequences, see reference [38]. Moreover, recall that binomial sequences are just shifted versions of the successive diagonals of the Sierpinski’s triangle depicted in Figure 2.

Table 2.
The first 8 binomial coefficients, their binomial sequences , periods and complexities.
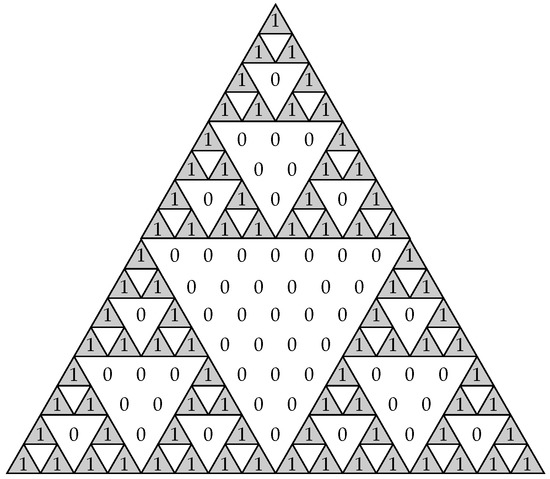
Figure 2.
Sierpinski’s triangle.
Theorem 1
([38], Proposition 3, Theorem 13). The binomial sequence with and r being a positive integer has period of value and linear complexity of value
Check [38] for more properties of binomial sequences.
3. Representation of Generalized Sequences
In this section, we present three different representations of the generalized self-shrunken sequences. From these representations we can obtain important information about the sequences. For instance, the binomial representation or B-representation of the generalized sequences allows us to examine the cryptographic parameters of these sequences and obtain their linear complexity; the p-representation and G-representation provide information about the shifted PN-sequences used in the decimation and allow us to define a partition of the family of generalized sequences.
It is worth saying that there exist certain advantages and disadvantages among these representations. On the one hand, the B-representation is more general and can be used for any binary sequence with a period of a power of two. On the other hand, the p-representation and the G-representation are specific representations for generalized sequences and, therefore, do not exist for other generators. However, both representations are related, being possible to get one from the other. In this section, we present some relations between the different representations.
3.1. The G-Representation of a Generalized Self-Shrunken Sequence
It is well known [12] that a PN-sequence generated by an LFSR with primitive polynomial of degree L can be represented by the trace map as follows
where with and is a root of , that is, a primitive element of .
From now on, we consider a PN-sequence obtained from a maximal-length LFSR with characteristic polynomial of degree L.
Next theorem proves that the sequence given in (1) is a shifted version of the PN-sequence .
Theorem 2.
Assume that is a PN-sequence obtained from a maximal-length LFSR with characteristic polynomial of degree L. If is a nonzero vector, then the sequence obtained from Expression (1) is a shifted version of . In fact, where such that
with being a root of .
Note that if in Expression (1) we consider , then is the null sequence.
From now on, we denote by G the decimal representation of the vector , i.e.
Moreover, we will use indistinctly G and . For example and .
Remark 1.
Since is the decimal representation of the binary number , we have that
that is, , where denotes the Zech logarithm of 1 with basis α.
Recall that the Zech logarithm of t with a basis of the primitive element is such that Check [44] for more properties of this discrete logarithm.
Example 2.

Consider the LFSR in which the characteristic polynomial is . For the initial state , we obtain the PN-sequence
which generates the family of generalized sequences shown in Table 3. The bits in bold in each sequence correspond to the positions of the ones of the PN-sequence , which appears at the bottom of the table. Furthermore, these bits are the digits of the corresponding sequence. Thus, in Table 3, the sequence corresponds to .

Table 3.
Generalized sequences for .
Next, we consider some properties of this representation (G-representation) of the generalized sequences.
Theorem 3.
If then is the identically 1 sequence.
Proof.
Theorem 4.
For , the sequences and are complementary sequences, in the sense that is the identically 1 sequence.
Proof.
Since the L-dimensional vector representations of G and are
and , defined by and respectively, satisfy for . Now, from the decimation rule defined in (2), in order to obtain the generalized sequences and we only consider the case when . Therefore, , which means that the sequences and are complementary. □
One can easily verify that the first 16 generalized sequences in Table 3 are the complementary sequences of the last 16 sequences. This means that if we generate the first generalized sequences using the above method, then the remaining sequences are just the complementary sequences of the previous ones. In this way, the computation of generalized sequences is half-reduced.
3.2. The B-Representation of a Generalized Self-Shrunken Sequence
Let E be the shifting operator that acts on the terms of a sequence , that is:
Let r be a positive integer. A sequence , of which the period is is, in turn, a particular solution of equation:
where its characteristic polynomial is . According to [38,45], the solutions of Equation (4) can be written as:
where the coefficients , 1 is the unique root of the polynomial with multiplicity and is a binomial coefficient reduced modulo 2. Thus, is the bit-wise XOR of T binary sequences weighted by T binary coefficients . Hence, all the solutions of the difference equation written in (4) are sums of binomial sequences. In particular, every solution can be written as:
with , , where is the greatest value i for which while for . Expression (5) is the binomial representation (or B-representation) of the sequence .
In terms of this representation, the parameters of the sequence can be easily analyzed. Indeed, the period of is the period of the binomial sequence and the linear complexity of is the linear complexity of the binomial sequence , that is (see Theorem 1).
As a consequence we can recall the following result.
Theorem 5
([38], Theorem 2). Given the binary sequence with period , where r is a positive integer, and linear complexity , such sequence can be written as a linear combination of binomial sequences, that is, , .
We will use indistinctly the notation or to denote the B-representation of the sequence . Notice that, in the B-representation, the term with the highest index is . This means that the last term provides the of the sequence. We denote by the B-representation of the null sequence.
Example 3.
Consider the sequence with period . This sequence can be also written as a linear combination of the sequences :
Since the binomial sequence (the term with highest index) is , then the linear complexity of will be . In the same way, its period coincides with the period of the sequence .
In [38], the authors proposed an algorithm to compute the B-representation of any sequence with a period of the power of two. Here, our aim is to propose another method to compute the B-representation of a generalized sequence. Next, we give a method to obtain this representation from any binary sequence of period a power of two. For this, we need to define a binary matrix called the binomial matrix, which is similar to the construction of a binary Hadamard matrix. Consider the binomial matrix for , that is, a matrix of size . We construct the binomial matrix for as follows
which has size . In general, we obtain the binomial matrix for t as
where is the binomial matrix of size and is the null matrix of the same size.
Let be a binary sequence of period . Given the binomial matrix of size , we construct the binary vector
The support of the vector B, denoted by , is the set of indices of the nonzero entries of B, considering the first position as the 0 position. Then, we define the B-representation of , denoted by , as the sequence given by the addition of the binomial sequences , for , that is
Notice that, as a consequence of Expression (6), we can only compute the B-representation of binary sequences of period . In particular, we can always obtain the B-representation of any GSS-sequence since the family of generalized sequences consists of sequences with periods power of two (see [21]).
The following example helps us to understand this construction.
Example 4.
Consider the binary sequence given in Example 3 in which the B-representation is . We check it using the method defined previously. The period of the sequence is , so we must construct the binomial matrix for , that is
From Expression (6), we have that
and, therefore, . So, from Expression (7), we have that , as we expected.
Recall that the columns of the binomial matrix (read from right to left) correspond to the successive diagonals of the Sierpinski’s triangle in Figure 2. Thus, the binary vector B in Expression (6) is just the product of by the diagonals of such a triangle.
We know that the generalized sequences have periods of the form , with . Therefore, we can express the generalized sequences as a finite sum of binomial sequences.
The following result is an immediate consequence of Theorems 4 and 3.
Theorem 6.
For , the B-representations of and are equal except for the term . Furthermore, the B-representation of is exactly .
This means that if we have the B-representations of the first generalized sequences, then the B-representations of the remaining sequences are the same ones except for the term . In this way, the computation of generalized sequences is half-reduced.
Example 5.

Consider again the generalized sequences obtained in Example 2. In Table 4, we can find the B-representation of each one of these generalized sequences. As we saw in Section 3.1, the last 16 generalized sequences in Table 3 are the complementary sequences of the first 16 sequences and then, from Theorem 6, the B-representation of them is the same except for the term . Furthermore, the B-representation of is , as expected.

Table 4.
Binomial representation for the generalized sequences of .
Some other properties of the family of generalized sequences can be deduced from the B-representation. We study these properties in detail in Section 4.
3.3. The p-Representation of a Generalized Self-Shrunken Sequence
In this subsection, we define a new representation of generalized sequences which gives us information of the shifted sequences employed in the decimation rule defined in (2).
From Theorem 2, we have that the sequence is a shifted version of the PN-sequence . Therefore, instead of considering the vector in Expression (1) to construct , we can simply consider the successive shifted versions of and apply in each case the decimation rule given in (2).
Let us consider the p-shifted version of the PN-sequence with . Applying the decimation rule given in (2), we construct the corresponding generalized sequence, which we denote by . This new representation of a generalized sequence is called p-representation.
One of the consequences of the group structure of is that the sum of two generalized sequences is another generalized sequence. The following theorem allows us to obtain the p-representation of the resulting generalized sequence from the p-representations of two generalized sequences given.
Theorem 7.
Consider that is the PN-sequence of an LFSR with primitive characteristic polynomial of degree L and is a root of . Then, the sum of two generalized sequences obtained with shifts and is another generalized sequence with shift , i.e,
where is as before the Zech logarithm with basis α.
Proof.
Assume that and are two generalized sequences obtained from the PN-sequence .
According to the decimation rule given in (2), if , then we have that and .
We have seen in Expression (3) that every element of can be expressed as
where with . Therefore, we have that:
Bit-wise XORing both sequences we get:
The sequence is the generalized sequence with shift , that is,
□
Notice that there is not any value that represents the null binary sequence . So, we denote with the p-representation of this sequence. It is worth noticing that , where and are the G-representation and the B-representation of the null sequence, respectively.
We have introduced three different notations for generalized sequences: the G-representation, , introduced in Section 3.1; the B-representation, given in Section 3.2 and the p-representation, , given in this subsection. The next theorem, which is a direct consequence of Theorem 2, provides a relation between the G-representation and the p-representation. We can get a representation from the other as follows.
Theorem 8.
Consider the family of generalized sequences denoted by , then
with such that , where is a root of the primitive polynomial of the corresponding LFSR. Equivalently, .
Example 6.

Consider again Example 2. Applying Theorem 8 to the family of generalized sequences given in Table 3, we obtain the relation between G-representation and p-representation as depicted in Table 5. For instance, if that is , we have to compute such that . According to the results in Table 5, , therefore, from Theorem 8, . It is easy to check that .

Table 5.
Generalized sequences for .
Corollary 1.
Consider the family of generalized sequences generated by the PN-sequence of period . If , with , then and or equivalently .
Example 7.
Consider again Example 2, where and . We can compute the value of p for each , where :
This result matches with the expected values for p obtained in Table 5.
| G | ||
| 1 | 0 | −4 mod 31 = 27 |
| 2 | 1 | −3 mod 31 = 28 |
| 4 | 2 | −2 mod 31 = 29 |
| 8 | 3 | −1 mod 31 = 30 |
| 16 | 4 | 0 mod 31 = 0 |
It is worth mentioning that the self-shrinking generator is another cryptographic sequence generator based on irregular decimation [20]. In this case, a PN-sequence is self-decimated producing a new sequence with good cryptographic properties. In [22], authors proved that the sequence produced by this generator can also be obtained with the generalized self-shrinking generator and the same characteristic polynomial with shift . As a consequence of this fact and the previous theorem, we can introduce the following result.
Corollary 2.
The sequence with such that is the output sequence generated by the self-shrinking generator with the same LFSR and characteristic polynomial .
Example 8.
Consider again Example 2. According to the previous corollary, the sequence generated by the self-shrinking generator is with G such that . In this case, and . Therefore and which corresponds to the sequence with shift , that is, the output sequence of the self-shrinking generator, as expected.
The following lemma proves that there exists an element such that . Later, we check that the generalized sequences associated to these values, and , are the sequences with period .
Lemma 1.
Let α be a primitive element in . Then
if and only if .
Proof.
Assume that . Then
and therefore, .
Conversely, assume that . Then
Therefore, the lemma holds. □
Let the binary representation of the value of G associated to m, and its decimal representation. Next, we introduce a theorem whose proof helps us to prove Theorem 10.
Theorem 9.
Let m be the integer defined in Lemma 1. Then
Proof.
According to Theorem 8, we can express m and as:
where and satisfy
with
From Lemma 1 and Expression (8) we deduce that:
Therefore,
As a consequence, the relation between and is
□
Theorem 10.
Consider such that , where m is the value given in Lemma 1. The generalized sequences and are the sequences of period , that is, the sequences with B-representation and .
Proof.
Let be the PN-sequence used in the GSSG. Consider the corresponding shifted versions and , where m is as in Lemma 1. According to the proof of Theorem 9, we know that:
Now, from Expression (1):
As a consequence, .
Let be the set of indices j such that . Therefore
Notice that (10) implies that, when ,
As a consequence, the resulting generalized sequences, and , are complementary (their sum is the identically 1 sequence).
Assume that . Let , according to (9), for (i.e., the integers between and ). Furthermore, since is also a shifted version of (shift ), we have , for . As a result, we obtain the following chain:
Therefore, . This means that is a shifted version of , but they are complementary. The only option is that they are the sequences and . □
For example, consider Table 5. The sequences and correspond to shifts and of the PN-sequence . From the isomorphism defined by (11), we have that the generalized sequence is associated with the element , and the generalized sequence is associated with . Therefore, we have and (see Table 5 again), in which the difference is as Theorem 9 indicated.
Theorem 11.
Consider a primitive polynomial of degree L and let m be the positive integer defined in 1, i.e., , with α a root of . Then, given β a root of , where is the reciprocal polynomial of , we have that , with .
Proof.
We know that is a root of . Then
and . As a consequence, we have that and
□
In Table 6, we study the values of m, such that , for every primitive polynomial of degree 5. Consider, for instance, . For this polynomial . The corresponding value for the reciprocal polynomial is computed as .

Table 6.
Primitive polynomials of degree 5 and m such that .
Remark 2.
Given the value of m for a primitive polynomial , we can find the value of for without computing any logarithm.
4. Partitions of the Family of Generalized Sequences
In this section, we study the family of generalized sequences as a partition of cosets of the quotient set given by and a subgroup of generalized sequences. This partition will help us in the analysis of the structure of the family of generalized sequences and their cryptographic properties. Their different representations, presented in the previous section, will facilitate us in this study.
4.1. Additive Group Structure
We know that the family of generalized sequences with the bit-wise XOR operation + is an Abelian additive group of order . Therefore, we can see it as an -vector space of dimension L. Furthermore, the additive group structure of and Theorem 7 allows us to define the following group isomorphism,
where denotes the p-representation.
Suppose that comes from an LFSR of L stages and define the set of the generalized sequences with periods 1 and 2; that is
where m is given in Lemma 1. We have that is a subgroup of of order 4; therefore, can be considered as a vector subspace of of dimension 2.
4.1.1. Subsets of of Order
From the groups and , we can define the quotient group in which the order is, by the Lagrange’s Theorem (see ([46], Section 6.8)),
For each , the set is called cosets of modulo and s is known as the representative of the coset.
Due to the properties of the cosets of a group ([47], Section 5.2) we know that any two cosets are either disjoint or identical, the union of the cosets is the own group and any subgroup is the coset defined by the neutral element. Although derived from a subgroup, cosets are not usually themselves subgroups of , only subsets. So, we have a partition of the set of generalized sequences into cosets of size 4, denoted by ; that is,
In the following example, we construct the quotient group of a family of generalized sequences and their cosets, using the p-representations.
Example 9.
Consider the set of GSS-sequences given in Table 5 and the null sequence . We have that and, as , the 8 cosets of are and
From the group isomorphism between and given in (11) and by Theorem 10, we know that
is isomorphic to ; therefore, the cosets of modulo can be written as , where is the representative of the coset. Furthermore, each coset will be isomorphic to
Example 10.
Consider Example 9 again. We know that, in this case, . Therefore, the cosets of modulo are
Next, we study the B-representation of the cosets of order 4. We focus our attention in this representation because we can obtain the of a generalized sequence directly from it (see Theorem 5).
Recalling that we denote by the B-representation of the null sequence, we have that the B-representation of is
Therefore, the B-representation of the corresponding sequences of each coset will have the following form
where , with , denotes the B-representation of the sequence associated to the representative of the coset , denoted by s. From Expression (7), we can obtain taking and the binomial matrix in Expression (6). Notice that for a sequence with linear complexity equal to , we have that and , for (see Theorem 5). As we know that for the generalized sequences [40], then we consider the coefficients , for , even though the last ones could be zeros.
Example 11.

Consider again the set of generalized sequences given in Table 5 and the cosets given in Example 9. In Table 7, we have the B-representation of each generalized sequence. Consider the coset . The B-representation of the set of generalized sequences is given by
where is the common term in the four representations.

Table 7.
Binomial representation of the generalized sequences for .
We have considered as the representative of the coset, but we could choose any element of the coset, since that . In this example, we consider the representative of the coset, and the B-representation of is denoted by .
4.1.2. Subgroups of of Order
In the previous subsection, we give a partition of the family of generalized sequences using the cosets of modulo which do not have to be subgroups. In this subsection, we give a partition of using subgroups of obtained from these cosets and the subgroup .
We can construct subgroups of of order 8, denoted by for , from the union of and the cosets of , , for any .
From the isomorphism given in Expression (11), if we assume that , then these subgroups can be expressed by
The B-representation of the corresponding sequences of each of the subgroups for will have the following form
where , with , is the binomial representation of the representative of the coset .
We observe that the subgroups can also be considered as vector subspaces of dimension three and the union of them provides the group , that is,
Notice that the Expression (13) is not a disjoint union, since the sequences represented by and are included in each subgroup. On the other hand, Expression (12) is a disjoint union of cosets. Therefore, the considered cosets form a partition of while the subgroups of order 8 do not.
Example 12.
Consider again Example 11 and Table 7. We can take the cosets and the appropriate representatives as we can see in Table 7 indicated with different colors. For instance, all the sequences that share , are represented in green or the sequences that share are represented in purple. From the cosets of order 4 and the corresponding union with the subgroup we can obtain the subgroups of order 8 with the B-representation as follows
In conclusion, from a primitive polynomial of degree L, we can obtain generalized sequences which can be divided into disjoint subsets, including the trivial group and the cosets of size four constructed by bit-wise XORing a given generalized sequence with ; or into subgroups of order eight, formed by the union of and the cosets of order four.
At this point, a question that arises in a natural way is whether it would be possible to obtain a generalized sequence from other sequences contained in other groups. Due to the additive group structure, the answer is affirmative.
4.2. Study of of Generalized Sequences
Linear complexity is a measure of unpredictability of pseudo-random sequences and it is a very important cryptographic property ([48], Section 2.3.5). Our aim in this section is to study the properties of the linear complexity of the family of generalized sequences, derived from their representations.
Cardell and Fúster-Sabater proved in [38] that we can deduce the linear complexity of any binary sequence with a period of the power of two from its B-representation.
Theorem 12
([38], Corollary 3). Given a sequence with B-representation , where are integer indexes, then the linear complexity of such a sequence is .
As a consequence, we can introduce the following result.
Theorem 13.
All the generalized sequences corresponding to a coset of order 4 have the same .
Proof.
This result is immediate using the B-representation in the cosets. The of any generalized sequence in a given coset can be determined by the B-representation of the representative, denoted by , since the rest of the sequences only differ from in the binomial terms , which will not affect the value of . □
From a high number of computational examples and as a consequence of the structure of the additive group, it is possible to observe that for a family of generalized sequences coming from a PN-sequence with a characteristic polynomial of degree L, we get different linear complexities satisfying
with , for ; apart from the trivial ones, , obtained in . There are cosets, each of them with four sequences and each sequence with linear complexity . The following example shows this fact.
Example 13.
Table 7 shows the family of generalized sequences obtained for the primitive polynomial . We distinguish with different colors the different cosets of of order 4. According to Theorem 12, we can determine the of a generalized sequence from its B-representation; and, from Theorem 13 we have that the for all the generalized sequences in a coset is the same. In this example, we obtain three different linear complexities
which allows us to classify the cosets of according to their complexities as follows
and the four trivial sequences of , the sequences of which have and .
Example 14.
Consider the 64 generalized sequences obtained from the primitive polynomial . In Appendix A we show a partition of the group of these generalized sequences into cosets of order 4. Note that we represent in bold the group and then we add the representative of each coset of . Binomial numbers, marked with different colors, provide the complexities of the sequences in each coset. Recall that the binomial number with the highest index in the B-representation is .
Next, we give a classification of the cosets of of order 4 according to the value of theirs complexities
and the four trivial sequences of .
As we can see in Table 8, each term , appears in the B-representation of eight cosets. Furthermore, for every value of , , there exist a coset, the B-representation of which only contains one of the four terms but not the others. In this example, these cosets are , , and D. Therefore, if we have four sequences, each one of them in one of the cosets above, we can obtain the 64 generalized sequences.

Table 8.
Binomial coefficients in the different subgroups.
In general, given a primitive polynomial of degree L, we generate generalized sequences which can be divided into cosets and with different linear complexities , . Each term appears times in the B-representations of the generalized sequences. As we checked previously, there are groups that have one element , , but not the others. Therefore, we only need sequences to generate the generalized sequences. We already knew this fact, since that is a vector space of dimension and thus can be generated by cosets modulo the subspace of dimension 2.
5. Conclusions
In this work, we introduce and analyze new ways to represent the generalized sequences, from which we study different properties of the sequences. We introduce the B-representation that allows us to express such sequences by means of binomial sequences, that is, shifted versions of the diagonals of the Sierpinski’s triangle. Furthermore, this representation lets us generate binary sequences with controllable parameters such as the period and the linear complexity. We have also defined the G and p-representation, both related between them. From the p-representation we can obtain the shifted version of the corresponding input PN-sequence of the GSSG and vice versa. Using this p-representation, we can define an isomorphism between the family of generalized sequences produced by a primitive polynomial of degree L and the additive group . As a consequence, we can create a partition of the sequences into subsets of cardinal 4, known as the cosets. Moreover, the B-representations of the four generalized sequences in each coset exhibit a well defined pattern and similar characteristics. This fact might be exploited in the cryptanalysis of this generator.
We still have different open problems to solve. In Section 4.2, we have analyzed the linear complexity of generalized sequences, but some results are just conjectures. The partition of generalized sequences into cosets of the quotient group and the study of the linear complexity of the sequences in each coset have brought new questions to be solved. Furthermore, we want to prove that the period of any generalized sequence obtained from a primitive polynomial of degree L, except from the sequences with period 1 and 2, is always and that is a lower bound on the linear complexity. Finally, another interesting future line would be to study the generalized shelf-shrinking generator based on FCSRs (or similar structures), analyze their cryptographic properties and adapt all three representations to this new model.
Author Contributions
All authors contributed equally. All authors have read and agreed to the published version of the manuscript.
Funding
This research is partially supported by Ministerio de Economía, Industria y Competitividad (MINECO), Agencia Estatal de Investigación (AEI), and Fondo Europeo de Desarrollo Regional (FEDER, UE) under project COPCIS, reference TIN2017-84844-C2-1-R. It is also supported by Comunidad de Madrid (Spain) under project CYNAMON (P2018/TCS-4566), co-funded by FSE and European Union FEDER funds. The first author is supported by CAPES (Brazil). Finally, the second and fourth author are partially supported by Spanish grant VIGROB-287 of the Universitat d’Alacant.
Conflicts of Interest
The authors declare no conflict of interest. The funders had no role in the design of the study; in the collection, analyses, or interpretation of data; in the writing of the manuscript, or in the decision to publish the results.
Abbreviations
The following abbreviations are used in this manuscript:
| LFSR | Linear Feedback Shift Register |
| PN-sequence | Pseudo-Noise sequence |
| LC | Linear Complexity |
| GSSG | Generalized Self-Shrinking Generator |
| GSS-sequence | Generalized Self-Shrunken Sequence |
| PRNG | Pseudo-Random Number Generator |
| FCSR | Feedback with Carry Shift Register |
Appendix A
Generalized sequences for .
References
- Fischer, V. A Closer Look at Security in Random Number Generators Design. In Constructive Side-Channel Analysis and Secure Design, COSADE 2012; Schindler, W., Huss, S., Eds.; Springer: Berlin/Heidelberg, Germany, 2012; Volume 7275, Lecture Notes in Computer Science; pp. 167–182. [Google Scholar]
- Francillon, A.; Castelluccia, C. TinyRNG: A Cryptographic Random Number Generator for Wireless Sensors Network Nodes. In Proceedings of the 2007 5th International Symposium on Modeling and Optimization in Mobile, Ad Hoc and Wireless Networks and Workshops, Limasso, Cyprus, 16–20 April 2007; pp. 1–7. [Google Scholar]
- Biryukov, A.; Shamir, A.; Wagner, D. Real Time Cryptanalysis of A5/1 on a PC. In Proceedings of Fast Software Encryption 2000; Goos, G., Hartmanis, J., Van Leeuwen, J., Schneier, B., Eds.; Springer: Berlin/Heidelberg, Germany, 2001; Volume 1978, Lecture Notes in Computer Science; pp. 1–18. [Google Scholar]
- Petrovic, S.; Fúster-Sabater, A. Cryptanalysis of the A5/2 Algorithm. IACR Cryptol. EPrint Arch. 2000, 2000, 52. [Google Scholar]
- Paul, G.; Maitra, S. RC4 Stream Cipher and its Variants; CRC Press, Taylor and Francis Group: Boca Raton, FL, USA, 2012. [Google Scholar]
- Peinado, A.; Munilla, J.; Fúster-Sabater, A. EPCGen2 Pseudorandom Number Generators: Analysis of J3Gen. Sensors 2014, 14, 6500–6515. [Google Scholar] [CrossRef] [PubMed]
- Dutta, I.K.; Ghosh, B.; Bayoumi, M. Lightweight Cryptography for Internet of Insecure Things: A Survey. In Proceedings of the 2019 IEEE 9th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, USA, 7–9 January 2019; pp. 0475–0481. [Google Scholar]
- Philip, M.A.; Vaithiyanathan. A survey on lightweight ciphers for IoT devices. In Proceedings of the 2017 International Conference on Technological Advancements in Power and Energy ( TAP Energy), Kollam, India, 21–23 December 2017; pp. 1–4. [Google Scholar]
- Dubrova, E.; Hell, M. Espresso: A stream cipher for 5G wireless communication systems. Cryptogr. Commun. 2017, 9, 273–289. [Google Scholar] [CrossRef]
- Orúe López, A.B.; Hernández Encinas, L.; Montoya Vitini, F. Trifork, a new Pseudorandom Number Generator Based on Lagged Fibonacci Maps. J. Comput. Sci. Eng. 2010, 2, 46–51. [Google Scholar]
- Paar, C.; Pelzl, J. Understanding Cryptography; Springer: Berlin, Germany, 2010. [Google Scholar]
- Golomb, S.W. Shift Register-Sequences; Aegean Park Press: Laguna Hill, CA, USA, 1982. [Google Scholar]
- Biryukov, A.; Perrin, L. State of the Art in Lightweight Symmetric Cryptography. IACR Cryptol. EPrint Arch. 2017, 2017, 511. [Google Scholar]
- Orúe López, A.B.; Hernández Encinas, L.; Martín Muñoz, A.; Montoya Vitini, F. A Lightweight Pseudorandom Number Generator for Securing the Internet of Things. IEEE Access 2017, 5, 27800–27806. [Google Scholar] [CrossRef]
- Hassan, S.; Bokhari, M.U. Design of Pseudo Random Number Generator using Linear Feedback Shift Register. Int. J. Eng. Adv. Technol. (IJEAT) 2019, 9, 1956–1965. [Google Scholar]
- Rahimov, H.; Babaei, M.; Farhadi, M. Cryptographic PRNG based on combination of LFSR and chaotic logistic map. Appl. Math. 2011, 2, 1531–1534. [Google Scholar] [CrossRef]
- Duvall, P.F.; Mortick, J.C. Decimation of Periodic Sequences. SIAM J. Appl. Math. 1971, 21, 367–372. [Google Scholar] [CrossRef]
- Díaz Cardell, S.; Fúster-Sabater, A. Cryptography with Shrinking Generators: Fundamentals and Applications of Keystream Sequence Generators Based on Irregular Decimation; Springer Briefs in Mathematics; Springer International Publishing: Cham, Switzerland, 2019. [Google Scholar]
- Coppersmith, D.; Krawczyk, H.; Mansour, Y. The shrinking generator. In Advances in Cryptology—CRYPTO ’93; Stinson, D., Ed.; Springer: Berlin/Heidelberg, Germany, 1994; Volume 773, Lecture Notes in Computer Science; pp. 22–39. [Google Scholar]
- Meier, W.; Staffelbach, O. The Self-Shrinking Generator. In Advances in Cryptology—EUROCRYPT 1994; De Santis, A., Ed.; Springer: Berlin/Heidelberg, Germany, 1995; Volume 950, Lecture Notes in Computer Science; pp. 205–214. [Google Scholar]
- Hu, Y.; Xiao, G. Generalized Self-Shrinking Generator. IEEE Trans. Inf. Theory 2004, 50, 714–719. [Google Scholar] [CrossRef]
- Zhang, B.; Feng, D. New Guess-and-Determine Attack on the Self-Shrinking Generator. In Advances in Cryptology—ASIACRYPT 2006; Lai, X., Chen, K., Eds.; Springe: Berlin/Heidelberg, Germany, 2006; Volume 4284, Lecture Notes in Computer Science; pp. 54–68. [Google Scholar]
- Kanso, A. Modified self-shrinking generator. Comput. Electr. Eng. 2010, 36, 993–1001. [Google Scholar] [CrossRef]
- Cardell, S.D.; Fúster-Sabater, A. The t-Modified Self-Shrinking Generator. In Computational Science—ICCS 2018; Shi, Y., Fu, H., Tian, Y., Krzhizhanovskaya, V.V., Lees, M.H., Dongarra, J., Sloot, P.M.A., Eds.; Springer International Publishing: Cham, Switzerland, 2018; Volume 10860, Lecture Notes in Computer Science; pp. 653–663. [Google Scholar]
- Cardell, S.D.; Requena, V.; Fúster-Sabater, A.; Orúe, A.B. Randomness Analysis for the Generalized Self-Shrinking Sequences. Symmetry 2020, 2020, 1460. [Google Scholar] [CrossRef]
- Cardell, S.D.; Fúster-Sabater, A. Discrete linear models for the generalized self-shrunken sequences. Finite Fields Their Appl. 2017, 47, 222–241. [Google Scholar] [CrossRef]
- Tasheva, A.T.; Tasheva, Z.N.; Petrov, A. Generalization of the Self-Shrinking Generator in the Galois Field GF(pn). Adv. Artif. Intell. 2011, 2011, 1–10. [Google Scholar] [CrossRef]
- Dong, L.; Zeng, Y.; Hu, Y. F-GSS: A Novel FCSR-Based Keystream Generator. In Proceedings of the 2009 First International Conference on Information Science and Engineering, Nanjing, China, 26–28 December 2009; pp. 1737–1740. [Google Scholar]
- Wang, H.; Wen, Q.; Zhang, J. The Properties of the FCSR-Based Self-Shrinking Sequence. IEICE Trans. Fundam. Electron. Commun. Comput. Sci. 2013, E96.A, 626–634. [Google Scholar] [CrossRef]
- Ali, A. Feedback with carry shift registers and (in-depth) security of ciphers based on this primitive. In Proceedings of the 2018 15th International Bhurban Conference on Applied Sciences and Technology (IBCAST), Islamabad, Pakistan, 9–13 January 2018; pp. 431–438. [Google Scholar]
- Goresky, M.; Klapper, A. Arithmetic crosscorrelations of feedback with carry shift register sequences. IEEE Trans. Inf. Theory 1997, 43, 1342–1345. [Google Scholar] [CrossRef]
- Stoyanov, B. Self-shrinking bit generation algorithm based on feedback with carry shift register. Adv. Stud. Theor. Phys. 2014, 8, 1057–1061. [Google Scholar] [CrossRef]
- Bandelow, C. Inside Rubik’s Cube and Beyond; Birkhäuser Boston: Cambridge, MA, USA, 1982. [Google Scholar]
- Jacobs, P. Group Theory with Applications in Chemical Physics; Cambridge University Press: Cambridge, UK, 2005. [Google Scholar]
- Liu, Y.; Hel-Or, H.; Kaplan, C.S.; Van Gool, L. Computational Symmetry in Computer Vision and Computer Graphics. Found. Trends Comput. Graph. Vis. 2009, 5, 1–195. [Google Scholar] [CrossRef]
- Lyubarskii, G. The Application of Group Theory in Physics; Elsevier: Pergamon, Turkey, 1960. [Google Scholar]
- Zhang, J.; Xiong, F.; Kang, J. The Application of Group Theory in Communication Operation Pipeline System. Math. Probl. Eng. 2018, 2018, 1–10. [Google Scholar] [CrossRef]
- Cardell, S.D.; Fúster-Sabater, A. Binomial Representation of Cryptographic Binary Sequences and Its Relation to Cellular Automata. Complexity 2019, 2019, 1–13. [Google Scholar] [CrossRef]
- Blackburn, S.R. The linear complexity of the self-shrinking generator. IEEE Trans. Inf. Theory 1999, 45, 2073–2077. [Google Scholar] [CrossRef]
- Fúster-Sabater, A.; Cardell, S.D. Linear complexity of generalized sequences by comparison of PN-sequences. RACSAM 2020, 2020. [Google Scholar] [CrossRef]
- Key, E.L. An Analysis of the Structure and Complexity of Nonlinear Binary Sequence Generators. IEEE Trans. Inf. Theory 1976, 22, 732–736. [Google Scholar] [CrossRef]
- Menezes, A.J.; van Oorschot, P.C.; Vanstone, S.A. Handbook of Applied Cryptography; CRC Press: Boca Raton, FL, USA, 1996. [Google Scholar]
- National Institute of Standards and Technology. NIST Lightweight Crypto Standardization Process 2019. Available online: https://csrc.nist.gov/Projects/Lightweight-Cryptography/Round-1-Candidates (accessed on 1 June 2020).
- Huber, K. Some comments on Zech’s logarithms. IEEE Trans. Inf. Theory 1990, 36, 946–950. [Google Scholar] [CrossRef]
- Fúster-Sabater, A. Generation of Cryptographic Sequences by means of Difference Equations. Appl. Math. Inf. Sci. 2014, 8, 475–484. [Google Scholar] [CrossRef]
- Birkhoff, G.; Mac Lane, S. A Survey of Modern Algebra; Macmillan: New York, NY, USA, 1996. [Google Scholar]
- Joshi, K.D. Foundations of Discrete Mathematics; Wiley: New York, NY, USA; Wiley Eastern Ltd: New Delhi, India, 1989. [Google Scholar]
- Cusick, T.W.; Ding, C.; Renvall, A. Stream Ciphers and Number Theory; North-Holland Mathematical Library: Amsterdam, Netherlands, 2004. [Google Scholar]
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).